Whitebox Security Data Governance Cybersecurity Milano 9 Aprile

Whitebox Security Data Governance Cybersecurity, Milano 9 Aprile 2014
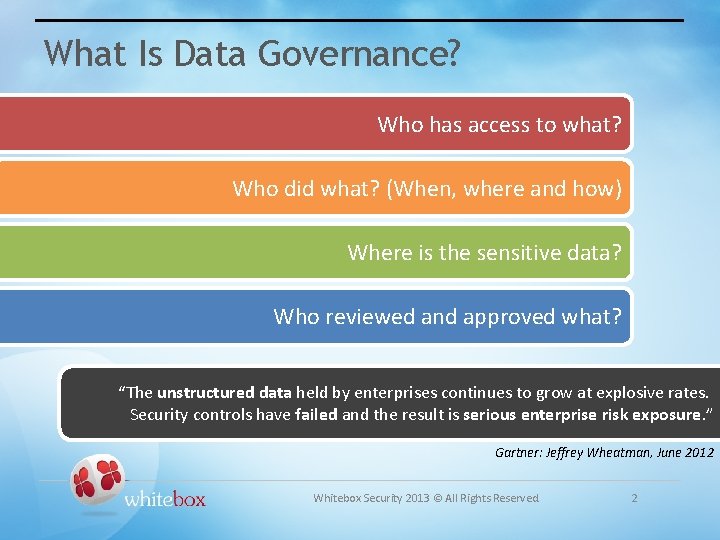
What Is Data Governance? Who has access to what? Who did what? (When, where and how) Where is the sensitive data? Who reviewed and approved what? “The unstructured data held by enterprises continues to grow at explosive rates. Security controls have failed and the result is serious enterprise risk exposure. ” Gartner: Jeffrey Wheatman, June 2012 Whitebox Security 2013 © All Rights Reserved. 2
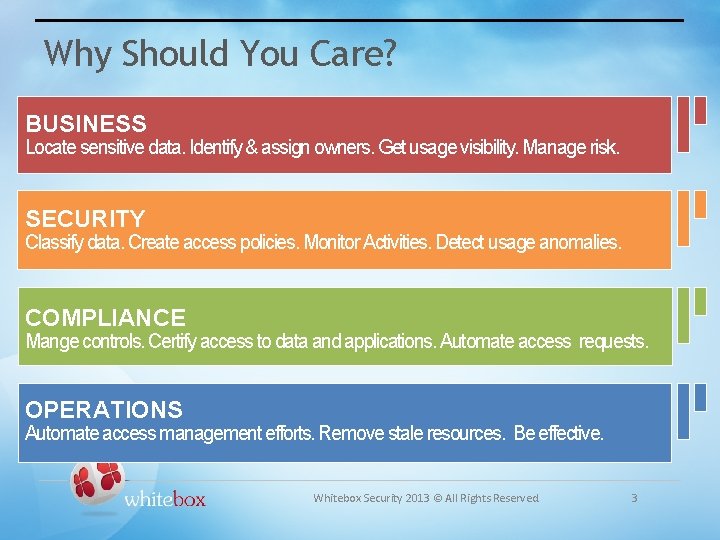
Why Should You Care? BUSINESS Locate sensitive data. Identify & assign owners. Get usage visibility. Manage risk. SECURITY Classify data. Create access policies. Monitor Activities. Detect usage anomalies. COMPLIANCE Mange controls. Certify access to data and applications. Automate access requests. OPERATIONS Automate access management efforts. Remove stale resources. Be effective. Whitebox Security 2013 © All Rights Reserved. 3
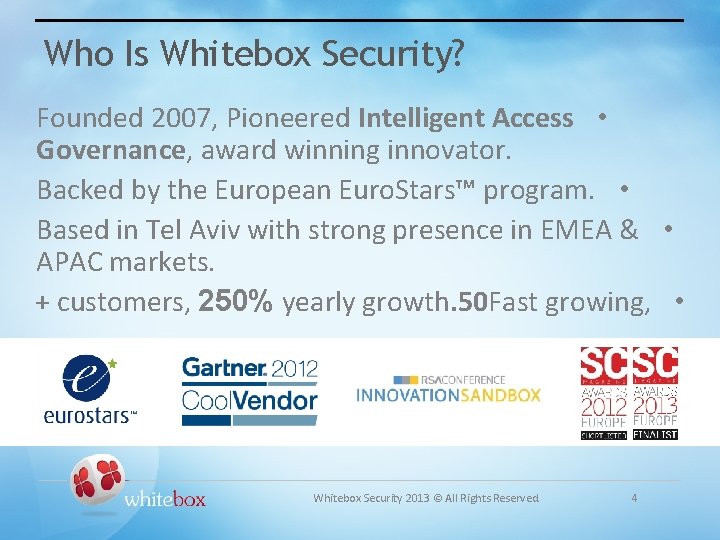
Who Is Whitebox Security? Founded 2007, Pioneered Intelligent Access • Governance, award winning innovator. Backed by the European Euro. Stars™ program. • Based in Tel Aviv with strong presence in EMEA & • APAC markets. + customers, 250% yearly growth. 50 Fast growing, • Whitebox Security 2013 © All Rights Reserved. 4
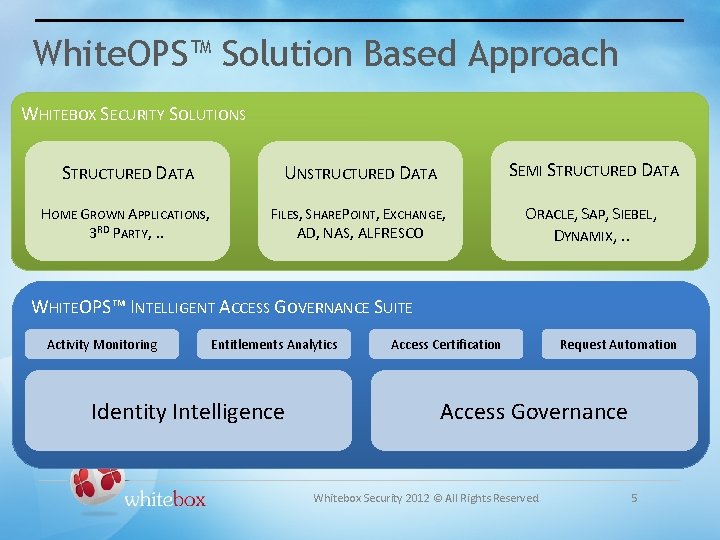
White. OPS™ Solution Based Approach WHITEBOX SECURITY SOLUTIONS STRUCTURED DATA UNSTRUCTURED DATA SEMI STRUCTURED DATA HOME GROWN APPLICATIONS, 3 RD PARTY, . . FILES, SHAREPOINT, EXCHANGE, AD, NAS, ALFRESCO ORACLE, SAP, SIEBEL, DYNAMIX, . . WHITEOPS™ INTELLIGENT ACCESS GOVERNANCE SUITE Activity Monitoring Entitlements Analytics Identity Intelligence Access Certification Request Automation Access Governance Whitebox Security 2012 © All Rights Reserved. 5
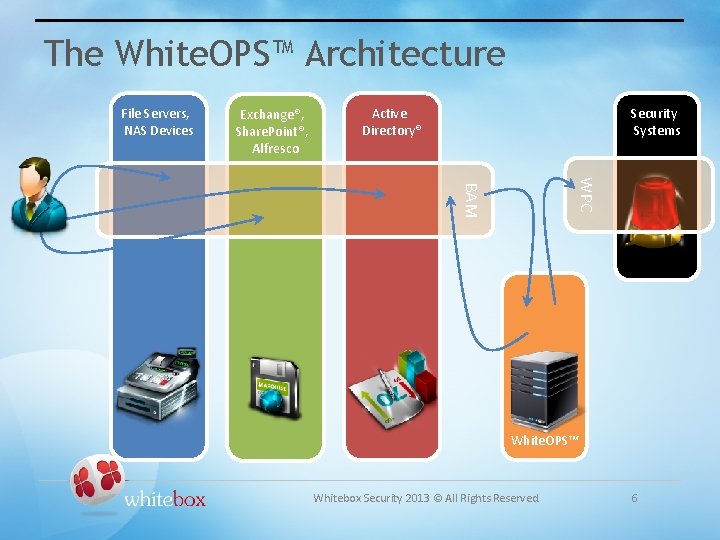
The White. OPS™ Architecture File Servers, NAS Devices Exchange®, Share. Point®, Alfresco Security Systems Active Directory® WPC BAM White. OPS™ Whitebox Security 2013 © All Rights Reserved. 6
But, Customers Are Asking Us To: BE FAST, TELL ME WHEN BAD THINGS HAPPEN, NOT A WEEK AFTER BE ELASTIC, SUPPORT UNSTRUCTURED INFORMATION & STRUCTURED INFORMATION BE HYBRID, SUPPORT ON-PREMISE &CLOUD ENVIRONMENTS Whitebox Security 2013 © All Rights Reserved. 7
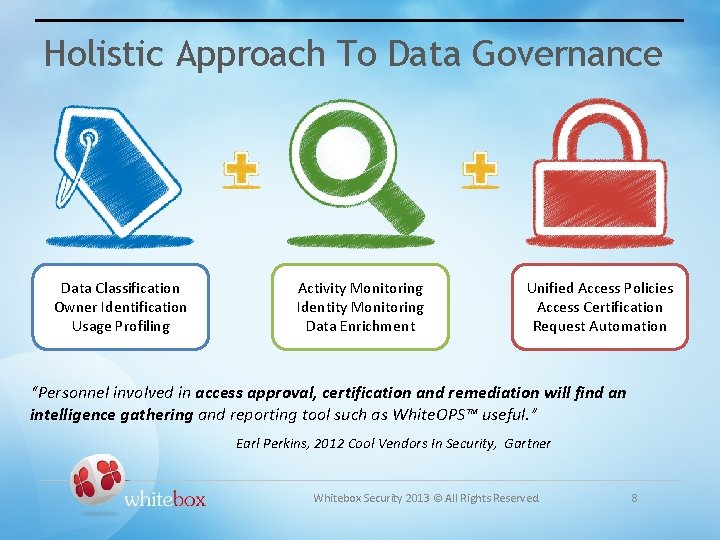
Holistic Approach To Data Governance Data Classification Owner Identification Usage Profiling Activity Monitoring Identity Monitoring Data Enrichment Unified Access Policies Access Certification Request Automation “Personnel involved in access approval, certification and remediation will find an intelligence gathering and reporting tool such as White. OPS™ useful. ” Earl Perkins, 2012 Cool Vendors In Security, Gartner Whitebox Security 2013 © All Rights Reserved. 8

The White. OPS™ Key Advantages Simplementation & quick turnover. • Real-Time monitoring of access to data. • Resource access protection using policy rules. • Support for on-premise and cloud data stores. • Support for applications (ERP, CRM, etc. ) • Address the needs of of IT and Business. • Whitebox Security 2013 © All Rights Reserved. 9

- Slides: 10