When Cryptography Meets Storage Sarah Diesburg Chris Meyers
When Cryptography Meets Storage Sarah Diesburg, Chris Meyers, Lary, and An-I Andy Wang David Florida State University 1
Motivations n n Cryptographic systems used for confidential storage of data Assumptions made for other media (e. g. networks) not directly applicable to storage q Usage patterns and properties affect confidentiality guarantees, especially when keys and IVs are reused over time Introduction • Background • Cryptanalysis • Examples • Conclusion 2
Contributions n Non-contributions q q Two-time pad problem Criticisms of particular storage systems Instead, we want to demonstrate what can go wrong when cryptography and storage constraints collide. Introduction • Background • Cryptanalysis • Examples • Conclusion 3
Applying Encryption to a Network n Usage patterns and properties q q n Short-lived data streams (e. g. , messages) Write-once content (e. g. , transactions) Uniqueness of keys and IVs achieved by cycling through large IV space before changing to new key Introduction • Background • Cryptanalysis • Examples • Conclusion 4
Storage n n Similar to a communication channel through time, but… Usage patterns and properties q In-place updates - if keys and IVs are generated as a function of offsets within a file or storage medium, the uniqueness of keys and IVs is compromised n Example: using sector number as IV Introduction • Background • Cryptanalysis • Examples • Conclusion 5
Storage q q Content shifting - potentially a large quantity of original plaintext is encrypted via reusing the keys and IVs defined as a function of file and disk locations Backups – versions of backups can violate the uniqueness of IVs and keys Introduction • Background • Cryptanalysis • Examples • Conclusion 6
Legacy Storage Data Path Problems n Single generic data type - encrypted and non-encrypted data treated similarly q n Sensitive data may be cached in plaintext Poor consistency guarantees – versions of encrypted data may reside in memory and on disk q Due to OS mechanisms (e. g. , hibernation and swap) Introduction • Background • Cryptanalysis • Examples • Conclusion 7
Legacy Storage Data Path Problems n Information hiding – no physical views of the underlying storage q Old versions may still linger on raw storage, even though application can only see newest encrypted data Introduction • Background • Cryptanalysis • Examples • Conclusion 8
Two-time Pad Problem n n Occurs when cryptographic information is reused to generate new encrypted data Best explained with stream cipher example Introduction • Background • Cryptanalysis • Examples • Conclusion 9
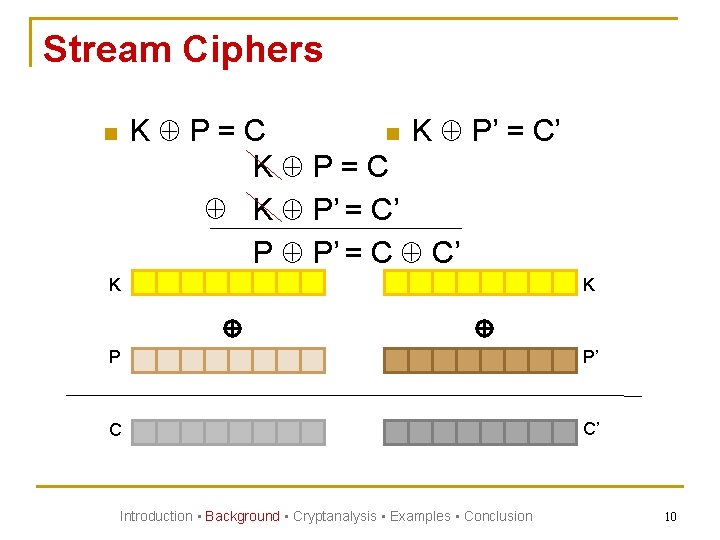
Stream Ciphers K P=C n K P’ = C’ K P=C K P’ = C’ P P’ = C C’ n K K P P’ C C’ Introduction • Background • Cryptanalysis • Examples • Conclusion 10
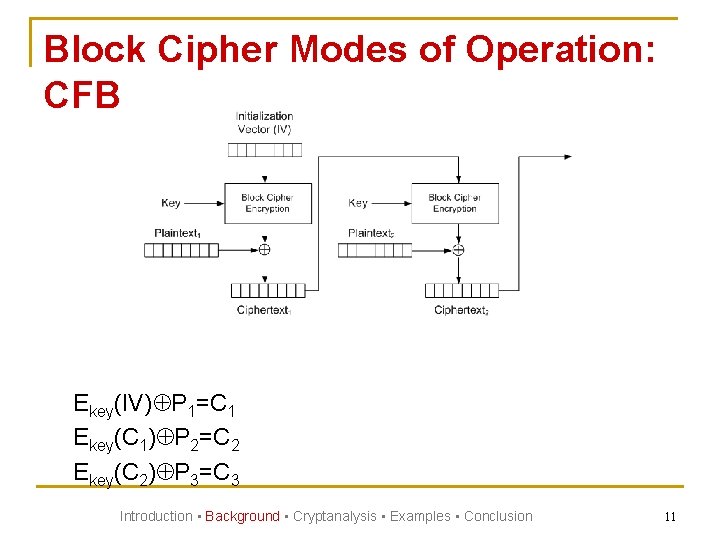
Block Cipher Modes of Operation: CFB Ekey(IV) P 1=C 1 Ekey(C 1) P 2=C 2 Ekey(C 2) P 3=C 3 Introduction • Background • Cryptanalysis • Examples • Conclusion 11
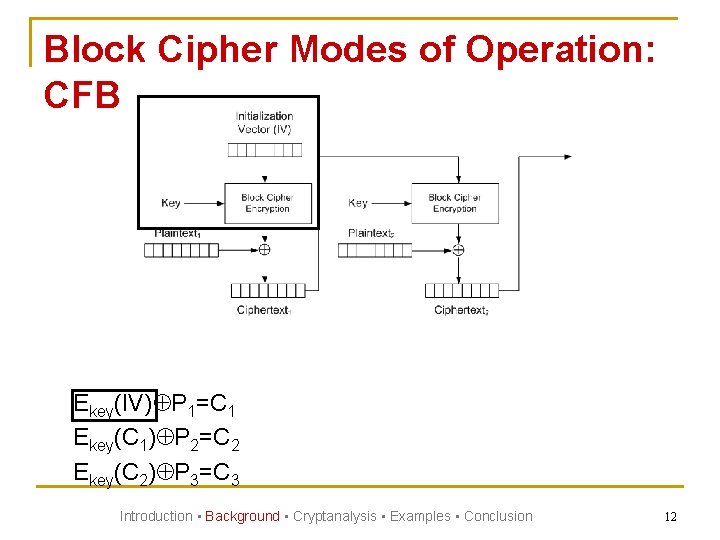
Block Cipher Modes of Operation: CFB Ekey(IV) P 1=C 1 Ekey(C 1) P 2=C 2 Ekey(C 2) P 3=C 3 Introduction • Background • Cryptanalysis • Examples • Conclusion 12
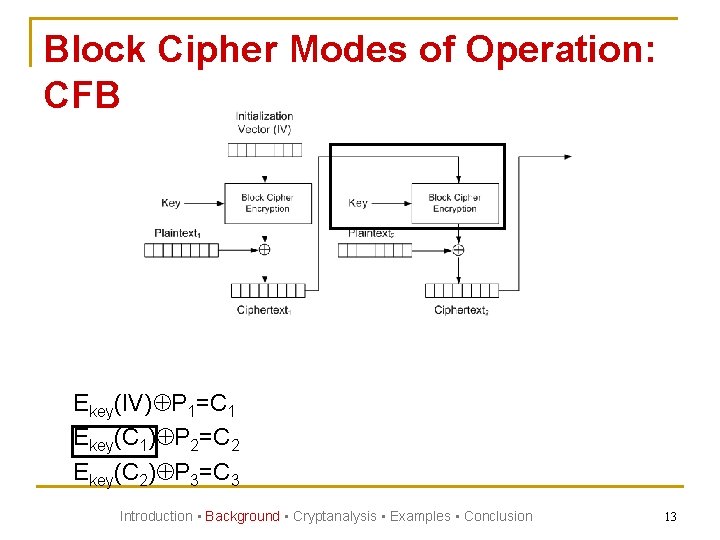
Block Cipher Modes of Operation: CFB Ekey(IV) P 1=C 1 Ekey(C 1) P 2=C 2 Ekey(C 2) P 3=C 3 Introduction • Background • Cryptanalysis • Examples • Conclusion 13
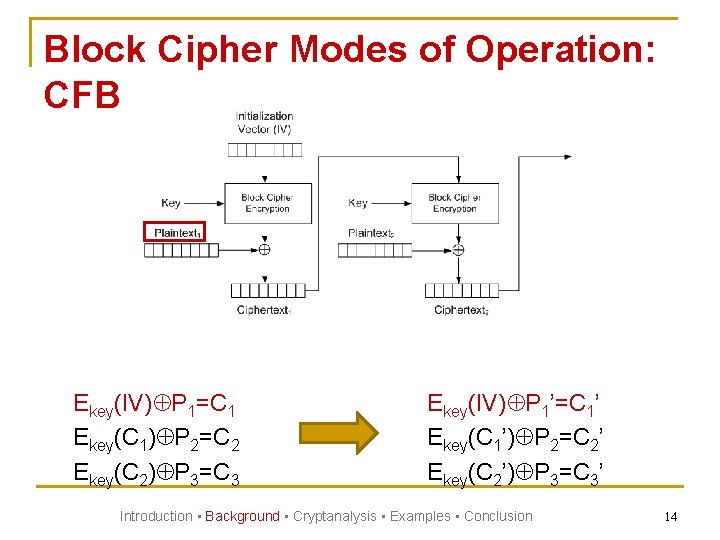
Block Cipher Modes of Operation: CFB Ekey(IV) P 1=C 1 Ekey(C 1) P 2=C 2 Ekey(C 2) P 3=C 3 Ekey(IV) P 1’=C 1’ Ekey(C 1’) P 2=C 2’ Ekey(C 2’) P 3=C 3’ Introduction • Background • Cryptanalysis • Examples • Conclusion 14
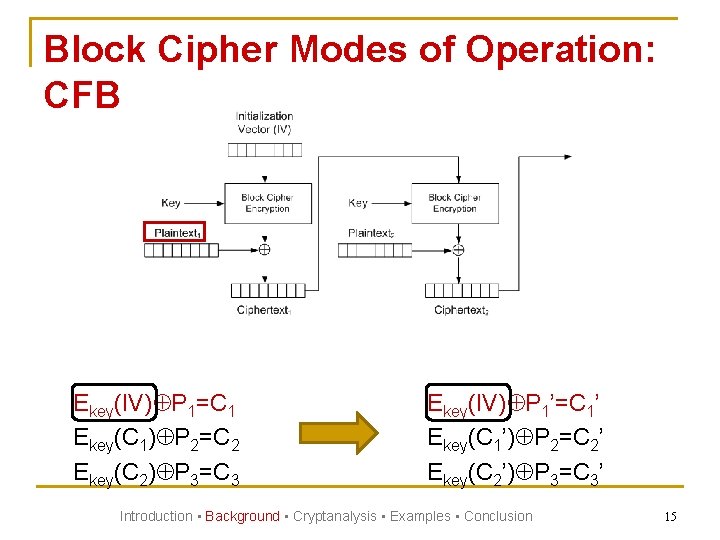
Block Cipher Modes of Operation: CFB Ekey(IV) P 1=C 1 Ekey(C 1) P 2=C 2 Ekey(C 2) P 3=C 3 Ekey(IV) P 1’=C 1’ Ekey(C 1’) P 2=C 2’ Ekey(C 2’) P 3=C 3’ Introduction • Background • Cryptanalysis • Examples • Conclusion 15
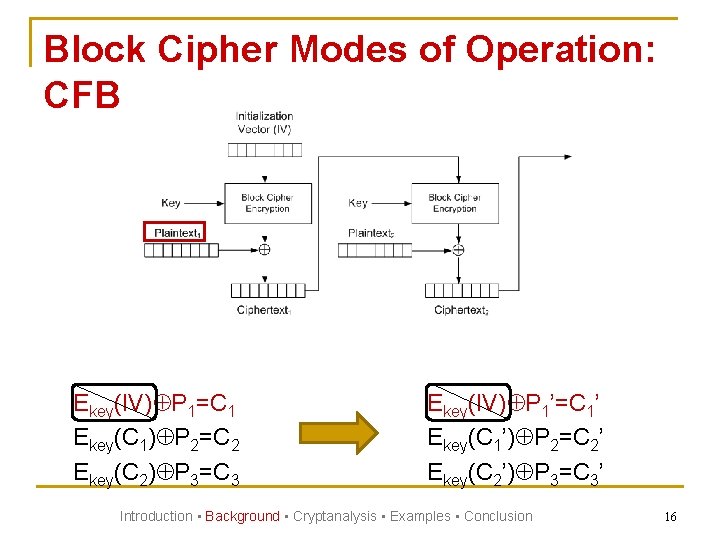
Block Cipher Modes of Operation: CFB Ekey(IV) P 1=C 1 Ekey(C 1) P 2=C 2 Ekey(C 2) P 3=C 3 Ekey(IV) P 1’=C 1’ Ekey(C 1’) P 2=C 2’ Ekey(C 2’) P 3=C 3’ Introduction • Background • Cryptanalysis • Examples • Conclusion 16
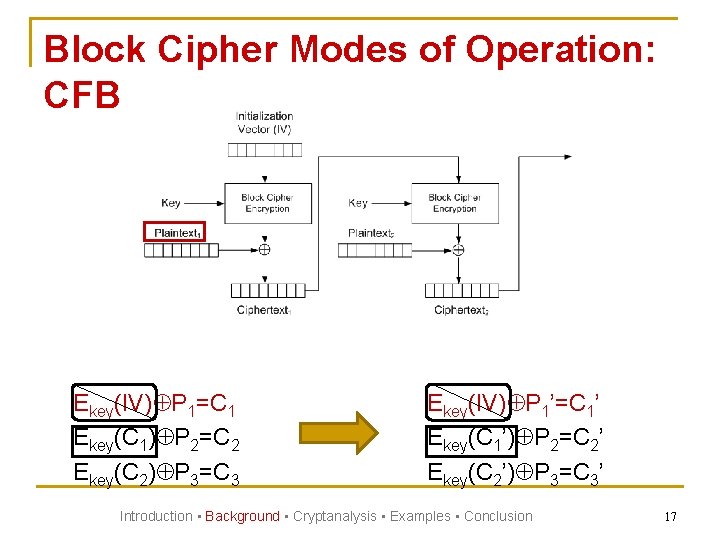
Block Cipher Modes of Operation: CFB Ekey(IV) P 1=C 1 Ekey(C 1) P 2=C 2 Ekey(C 2) P 3=C 3 Ekey(IV) P 1’=C 1’ Ekey(C 1’) P 2=C 2’ Ekey(C 2’) P 3=C 3’ Introduction • Background • Cryptanalysis • Examples • Conclusion 17
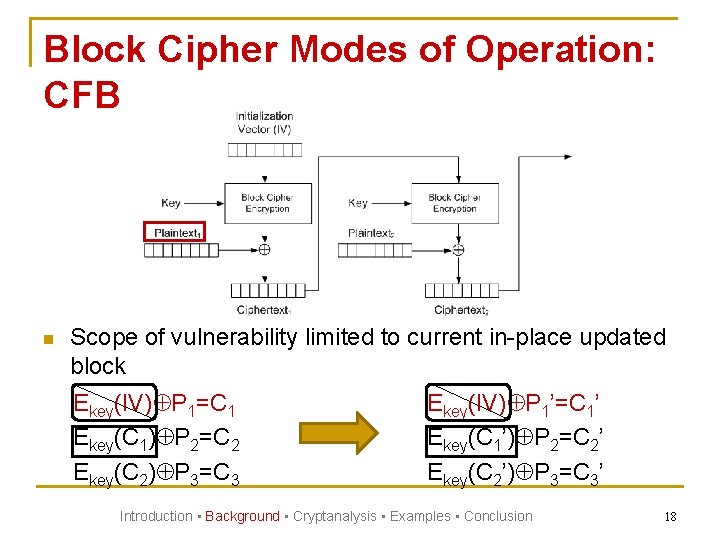
Block Cipher Modes of Operation: CFB n Scope of vulnerability limited to current in-place updated block Ekey(IV) P 1=C 1 Ekey(C 1) P 2=C 2 Ekey(C 2) P 3=C 3 Ekey(IV) P 1’=C 1’ Ekey(C 1’) P 2=C 2’ Ekey(C 2’) P 3=C 3’ Introduction • Background • Cryptanalysis • Examples • Conclusion 18
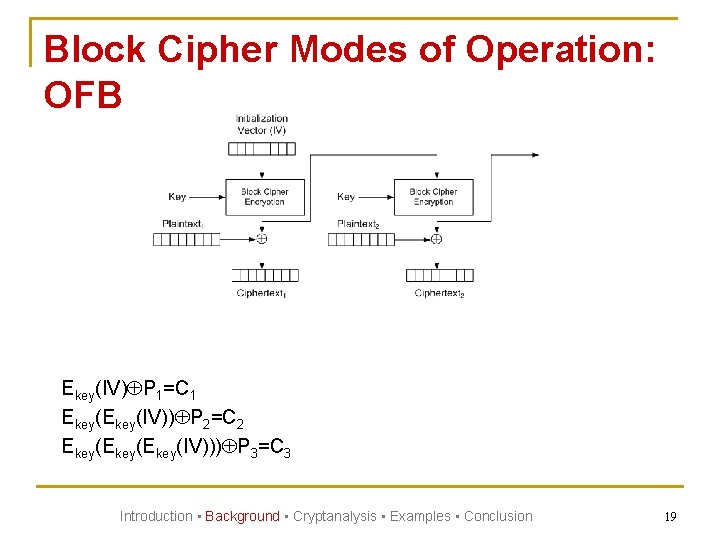
Block Cipher Modes of Operation: OFB Ekey(IV) P 1=C 1 Ekey(IV)) P 2=C 2 Ekey(Ekey(IV))) P 3=C 3 Introduction • Background • Cryptanalysis • Examples • Conclusion 19
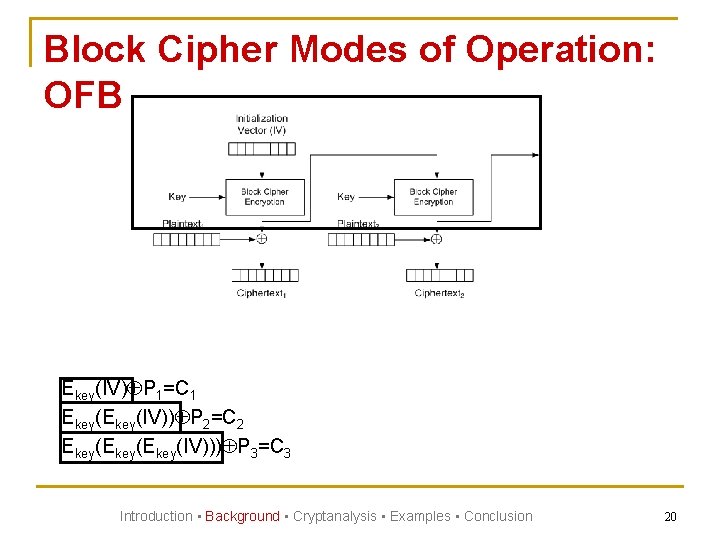
Block Cipher Modes of Operation: OFB Ekey(IV) P 1=C 1 Ekey(IV)) P 2=C 2 Ekey(Ekey(IV))) P 3=C 3 Introduction • Background • Cryptanalysis • Examples • Conclusion 20
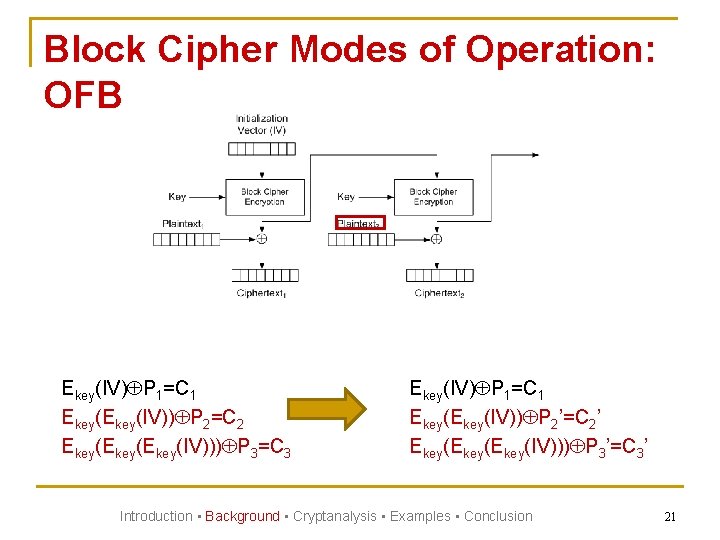
Block Cipher Modes of Operation: OFB Ekey(IV) P 1=C 1 Ekey(IV)) P 2=C 2 Ekey(Ekey(IV))) P 3=C 3 Ekey(IV) P 1=C 1 Ekey(IV)) P 2’=C 2’ Ekey(Ekey(IV))) P 3’=C 3’ Introduction • Background • Cryptanalysis • Examples • Conclusion 21
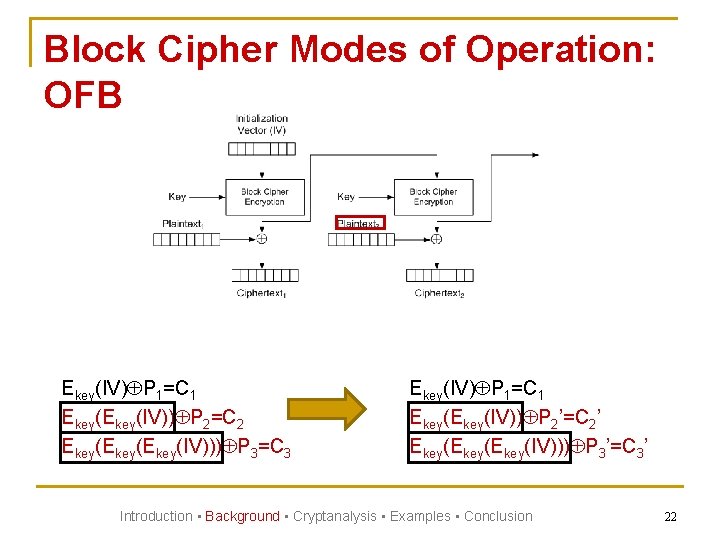
Block Cipher Modes of Operation: OFB Ekey(IV) P 1=C 1 Ekey(IV)) P 2=C 2 Ekey(Ekey(IV))) P 3=C 3 Ekey(IV) P 1=C 1 Ekey(IV)) P 2’=C 2’ Ekey(Ekey(IV))) P 3’=C 3’ Introduction • Background • Cryptanalysis • Examples • Conclusion 22
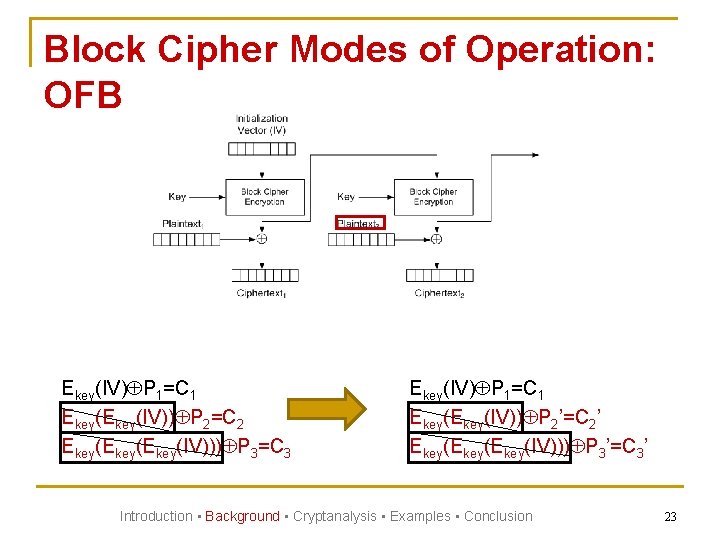
Block Cipher Modes of Operation: OFB Ekey(IV) P 1=C 1 Ekey(IV)) P 2=C 2 Ekey(Ekey(IV))) P 3=C 3 Ekey(IV) P 1=C 1 Ekey(IV)) P 2’=C 2’ Ekey(Ekey(IV))) P 3’=C 3’ Introduction • Background • Cryptanalysis • Examples • Conclusion 23
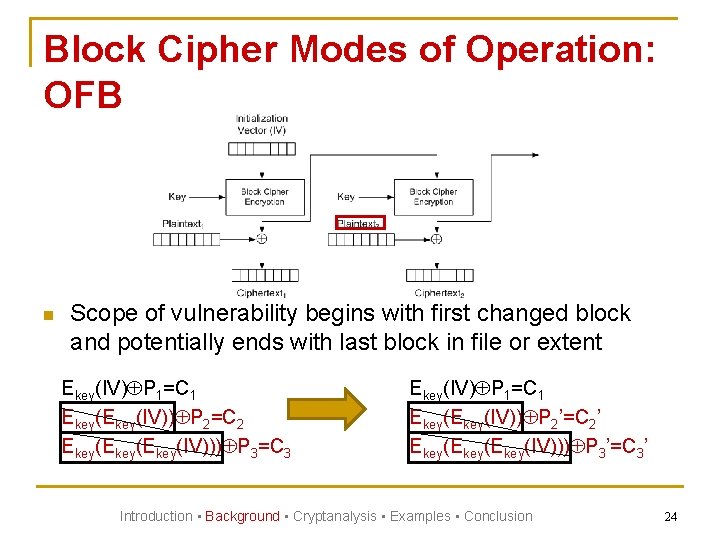
Block Cipher Modes of Operation: OFB n Scope of vulnerability begins with first changed block and potentially ends with last block in file or extent Ekey(IV) P 1=C 1 Ekey(IV)) P 2=C 2 Ekey(Ekey(IV))) P 3=C 3 Ekey(IV) P 1=C 1 Ekey(IV)) P 2’=C 2’ Ekey(Ekey(IV))) P 3’=C 3’ Introduction • Background • Cryptanalysis • Examples • Conclusion 24
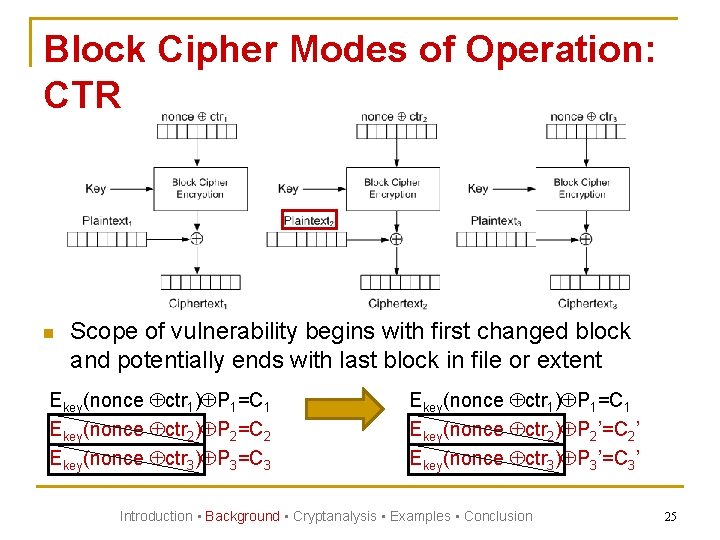
Block Cipher Modes of Operation: CTR n Scope of vulnerability begins with first changed block and potentially ends with last block in file or extent Ekey(nonce ctr 1) P 1=C 1 Ekey(nonce ctr 2) P 2=C 2 Ekey(nonce ctr 3) P 3=C 3 Ekey(nonce ctr 1) P 1=C 1 Ekey(nonce ctr 2) P 2’=C 2’ Ekey(nonce ctr 3) P 3’=C 3’ Introduction • Background • Cryptanalysis • Examples • Conclusion 25
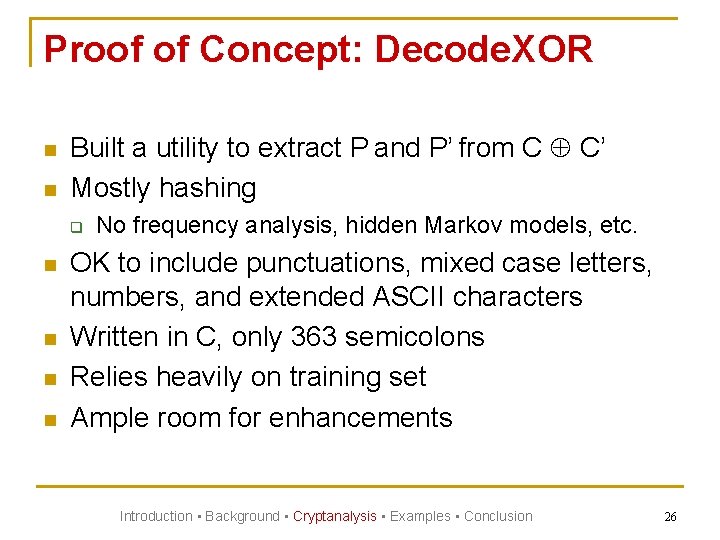
Proof of Concept: Decode. XOR n n Built a utility to extract P and P’ from C C’ Mostly hashing q n n No frequency analysis, hidden Markov models, etc. OK to include punctuations, mixed case letters, numbers, and extended ASCII characters Written in C, only 363 semicolons Relies heavily on training set Ample room for enhancements Introduction • Background • Cryptanalysis • Examples • Conclusion 26
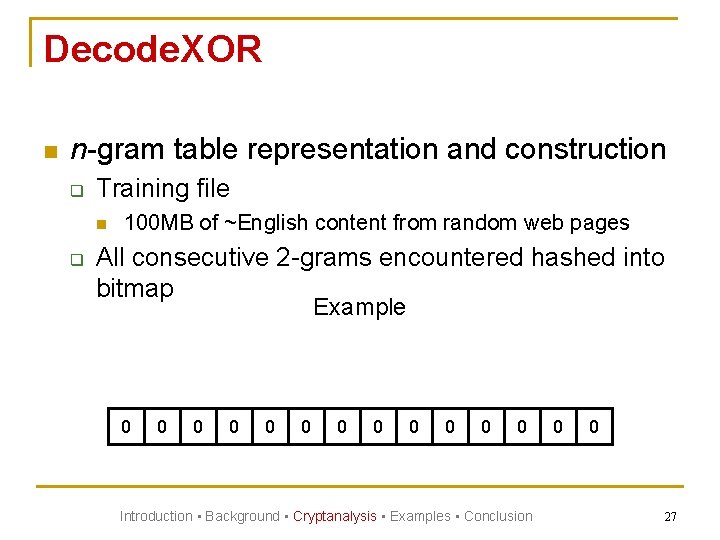
Decode. XOR n n-gram table representation and construction q Training file n q 100 MB of ~English content from random web pages All consecutive 2 -grams encountered hashed into bitmap Example 0 0 0 Introduction • Background • Cryptanalysis • Examples • Conclusion 0 0 27
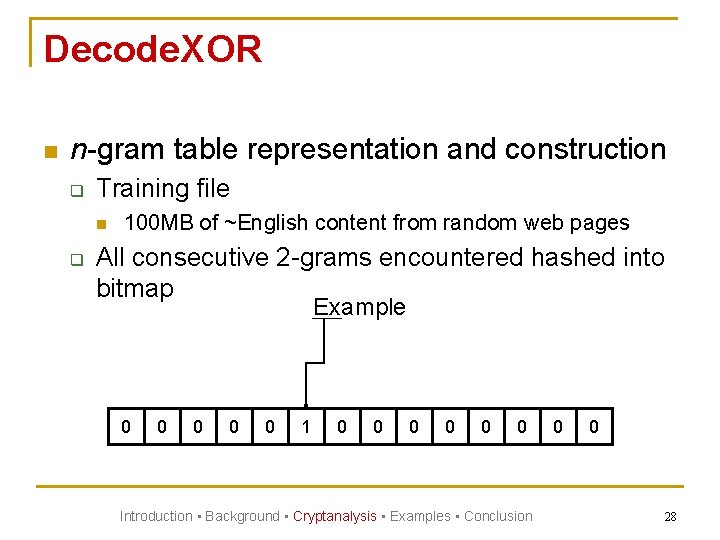
Decode. XOR n n-gram table representation and construction q Training file n q 100 MB of ~English content from random web pages All consecutive 2 -grams encountered hashed into bitmap Example 0 0 0 1 0 0 0 Introduction • Background • Cryptanalysis • Examples • Conclusion 0 0 28
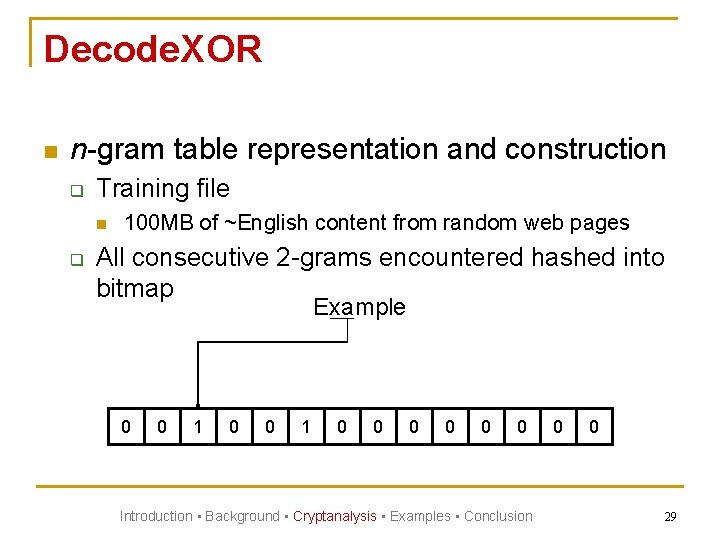
Decode. XOR n n-gram table representation and construction q Training file n q 100 MB of ~English content from random web pages All consecutive 2 -grams encountered hashed into bitmap Example 0 0 1 0 0 0 Introduction • Background • Cryptanalysis • Examples • Conclusion 0 0 29
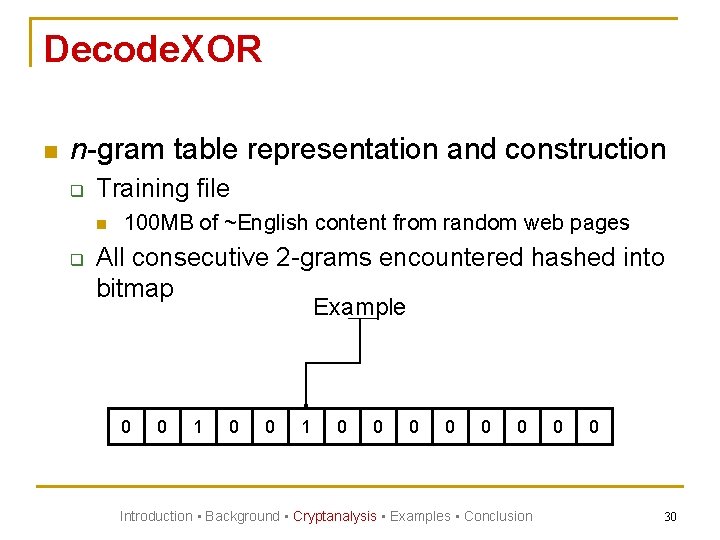
Decode. XOR n n-gram table representation and construction q Training file n q 100 MB of ~English content from random web pages All consecutive 2 -grams encountered hashed into bitmap Example 0 0 1 0 0 0 Introduction • Background • Cryptanalysis • Examples • Conclusion 0 0 30
Decode. XOR n n-gram table representation and construction q Training file n q q 100 MB of ~English content from random web pages All consecutive 2 -grams encountered hashed into bitmap Same method extended to capture n-grams of 3 to 6 characters Introduction • Background • Cryptanalysis • Examples • Conclusion 31
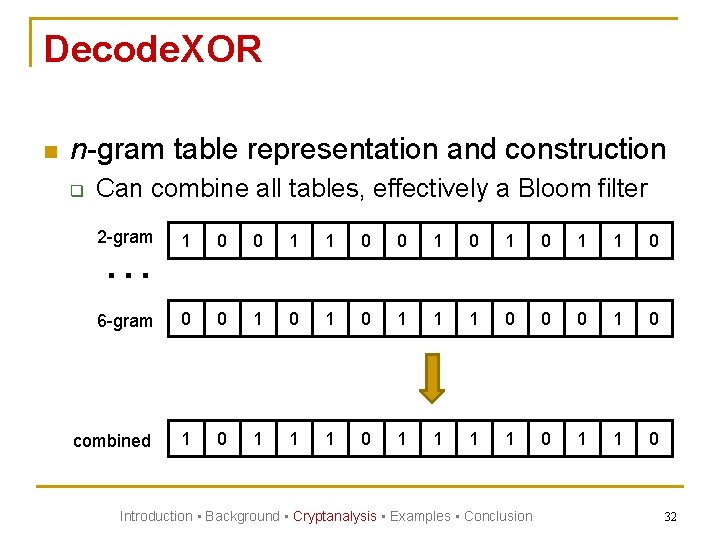
Decode. XOR n n-gram table representation and construction q Can combine all tables, effectively a Bloom filter 2 -gram … 1 0 0 1 0 1 1 0 6 -gram 0 0 1 0 1 1 1 0 0 0 1 0 combined 1 0 1 1 1 1 0 Introduction • Background • Cryptanalysis • Examples • Conclusion 32
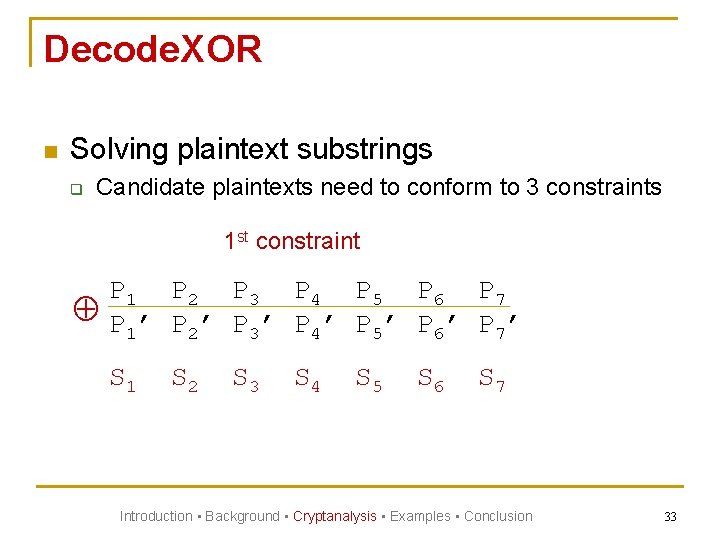
Decode. XOR n Solving plaintext substrings q Candidate plaintexts need to conform to 3 constraints 1 st constraint P 1 P 2 P 3 P 4 P 5 P 6 P 7 P 1’ P 2’ P 3’ P 4’ P 5’ P 6’ P 7’ S 1 S 2 S 3 S 4 S 5 S 6 S 7 Introduction • Background • Cryptanalysis • Examples • Conclusion 33
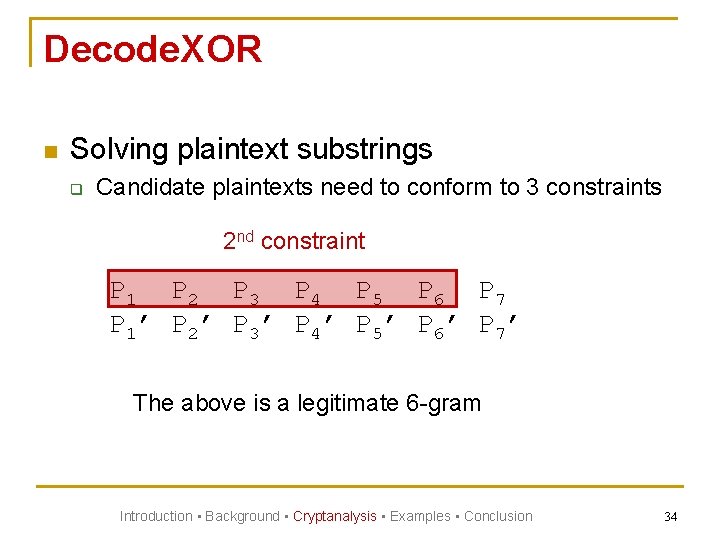
Decode. XOR n Solving plaintext substrings q Candidate plaintexts need to conform to 3 constraints 2 nd constraint P 1 P 2 P 3 P 4 P 5 P 6 P 7 P 1’ P 2’ P 3’ P 4’ P 5’ P 6’ P 7’ The above is a legitimate 6 -gram Introduction • Background • Cryptanalysis • Examples • Conclusion 34
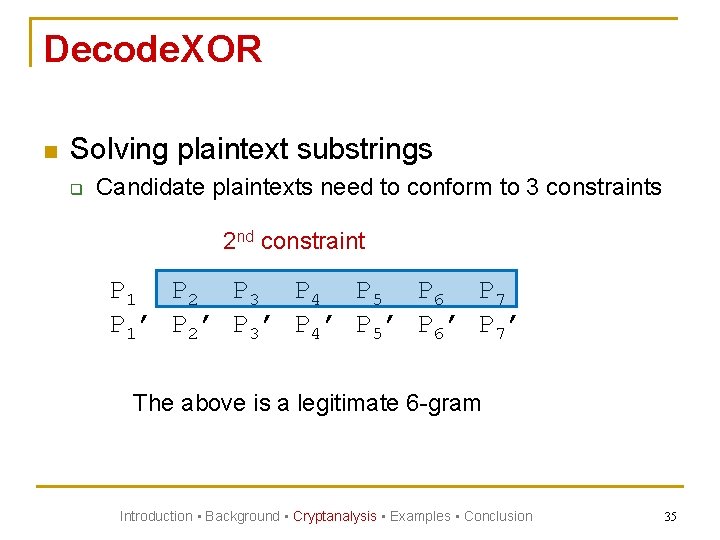
Decode. XOR n Solving plaintext substrings q Candidate plaintexts need to conform to 3 constraints 2 nd constraint P 1 P 2 P 3 P 4 P 5 P 6 P 7 P 1’ P 2’ P 3’ P 4’ P 5’ P 6’ P 7’ The above is a legitimate 6 -gram Introduction • Background • Cryptanalysis • Examples • Conclusion 35
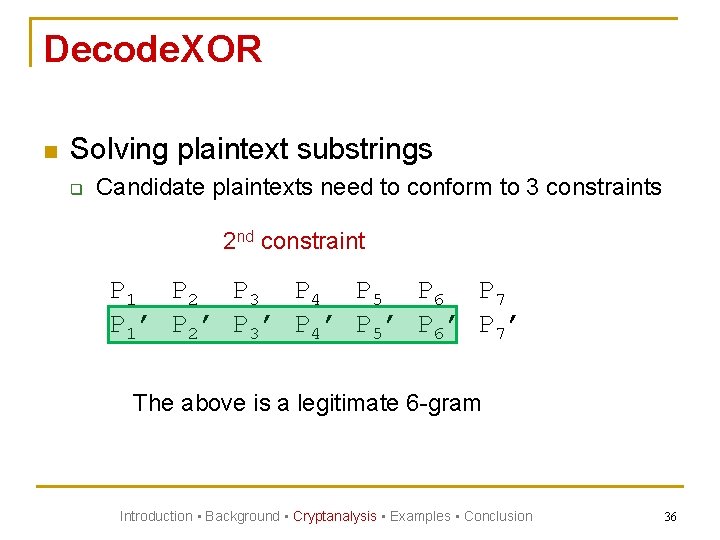
Decode. XOR n Solving plaintext substrings q Candidate plaintexts need to conform to 3 constraints 2 nd constraint P 1 P 2 P 3 P 4 P 5 P 6 P 7 P 1’ P 2’ P 3’ P 4’ P 5’ P 6’ P 7’ The above is a legitimate 6 -gram Introduction • Background • Cryptanalysis • Examples • Conclusion 36
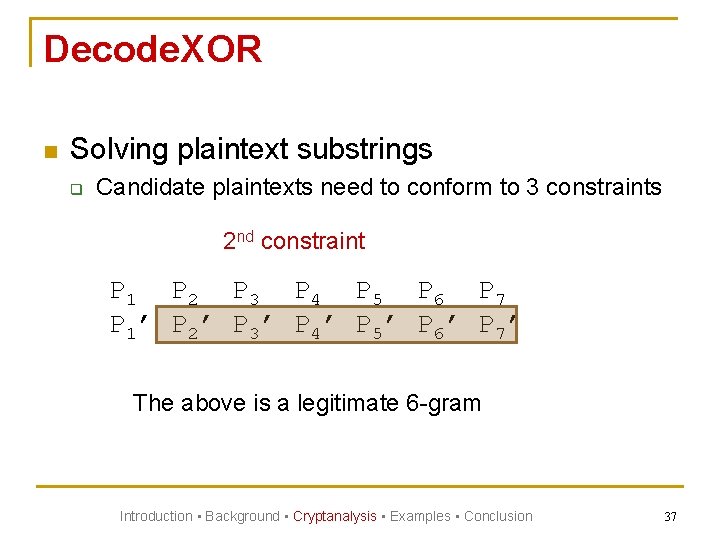
Decode. XOR n Solving plaintext substrings q Candidate plaintexts need to conform to 3 constraints 2 nd constraint P 1 P 2 P 3 P 4 P 5 P 6 P 7 P 1’ P 2’ P 3’ P 4’ P 5’ P 6’ P 7’ The above is a legitimate 6 -gram Introduction • Background • Cryptanalysis • Examples • Conclusion 37
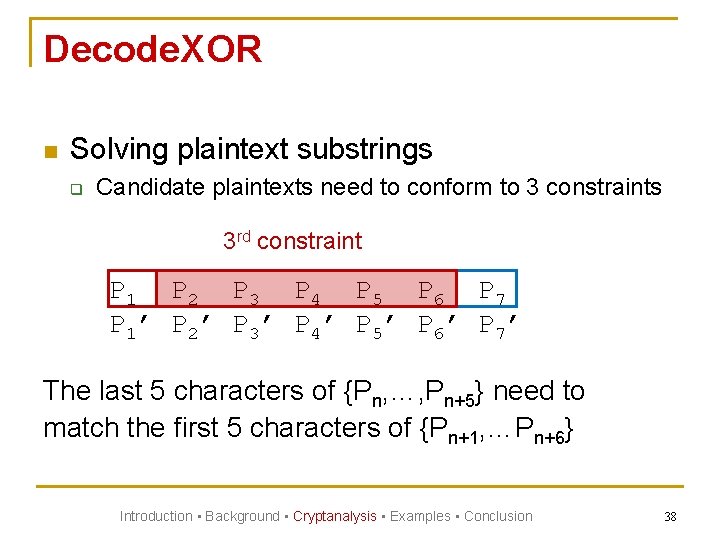
Decode. XOR n Solving plaintext substrings q Candidate plaintexts need to conform to 3 constraints 3 rd constraint P 1 P 2 P 3 P 4 P 5 P 6 P 7 P 1’ P 2’ P 3’ P 4’ P 5’ P 6’ P 7’ The last 5 characters of {Pn, …, Pn+5} need to match the first 5 characters of {Pn+1, …Pn+6} Introduction • Background • Cryptanalysis • Examples • Conclusion 38
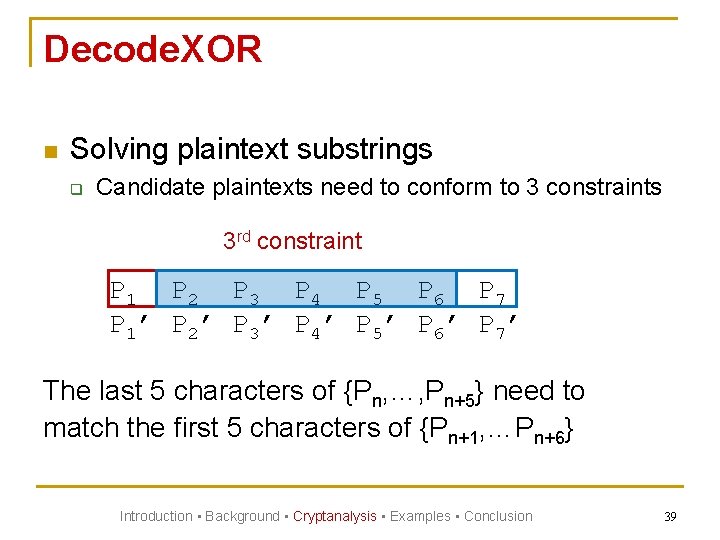
Decode. XOR n Solving plaintext substrings q Candidate plaintexts need to conform to 3 constraints 3 rd constraint P 1 P 2 P 3 P 4 P 5 P 6 P 7 P 1’ P 2’ P 3’ P 4’ P 5’ P 6’ P 7’ The last 5 characters of {Pn, …, Pn+5} need to match the first 5 characters of {Pn+1, …Pn+6} Introduction • Background • Cryptanalysis • Examples • Conclusion 39
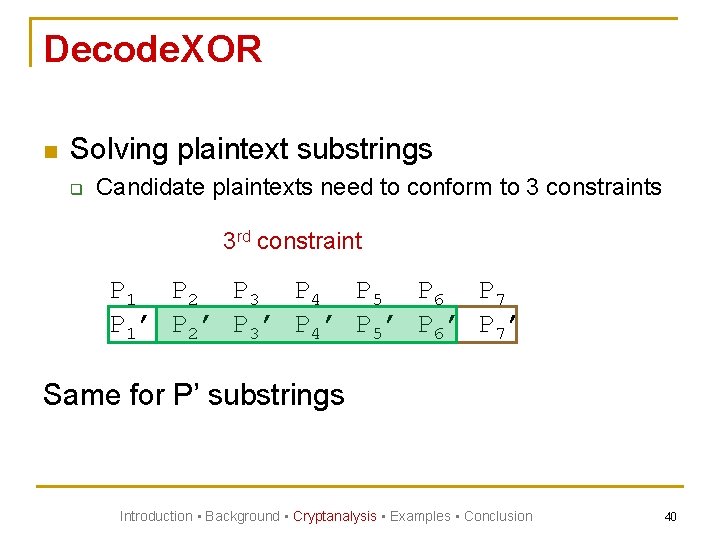
Decode. XOR n Solving plaintext substrings q Candidate plaintexts need to conform to 3 constraints 3 rd constraint P 1 P 2 P 3 P 4 P 5 P 6 P 7 P 1’ P 2’ P 3’ P 4’ P 5’ P 6’ P 7’ Same for P’ substrings Introduction • Background • Cryptanalysis • Examples • Conclusion 40
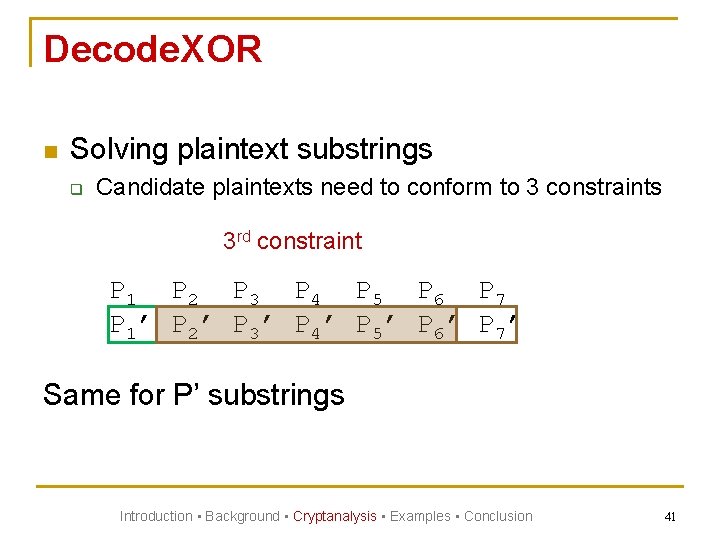
Decode. XOR n Solving plaintext substrings q Candidate plaintexts need to conform to 3 constraints 3 rd constraint P 1 P 2 P 3 P 4 P 5 P 6 P 7 P 1’ P 2’ P 3’ P 4’ P 5’ P 6’ P 7’ Same for P’ substrings Introduction • Background • Cryptanalysis • Examples • Conclusion 41
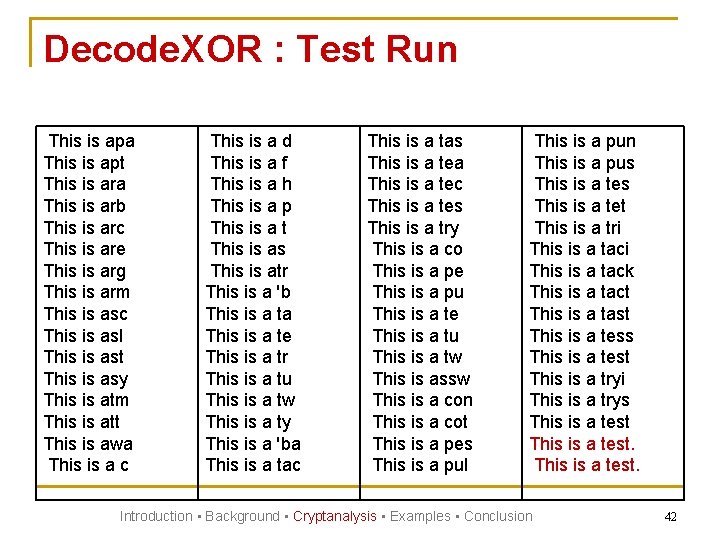
Decode. XOR : Test Run This is apa This is apt This is ara This is arb This is arc This is are This is arg This is arm This is asc This is asl This is ast This is asy This is atm This is att This is awa This is a c This is a d This is a f This is a h This is a p This is a t This is as This is atr This is a 'b This is a ta This is a te This is a tr This is a tu This is a tw This is a ty This is a 'ba This is a tac This is a tas This is a tea This is a tec This is a tes This is a try This is a co This is a pe This is a pu This is a te This is a tu This is a tw This is assw This is a con This is a cot This is a pes This is a pul This is a pun This is a pus This is a tet This is a tri This is a tack This is a tact This is a tast This is a tess This is a test This is a tryi This is a trys This is a test. Introduction • Background • Cryptanalysis • Examples • Conclusion 42
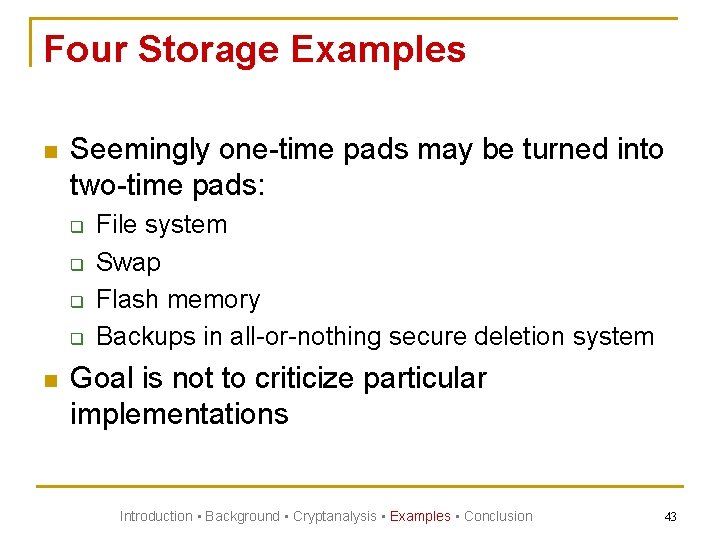
Four Storage Examples n Seemingly one-time pads may be turned into two-time pads: q q n File system Swap Flash memory Backups in all-or-nothing secure deletion system Goal is not to criticize particular implementations Introduction • Background • Cryptanalysis • Examples • Conclusion 43
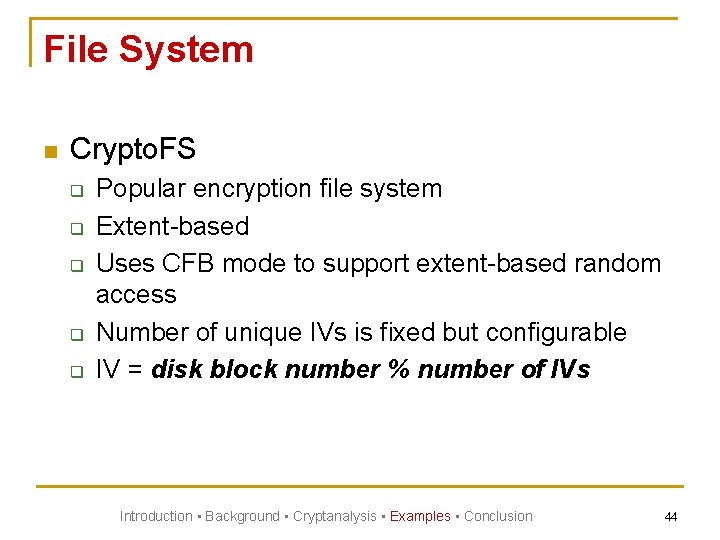
File System n Crypto. FS q q q Popular encryption file system Extent-based Uses CFB mode to support extent-based random access Number of unique IVs is fixed but configurable IV = disk block number % number of IVs Introduction • Background • Cryptanalysis • Examples • Conclusion 44
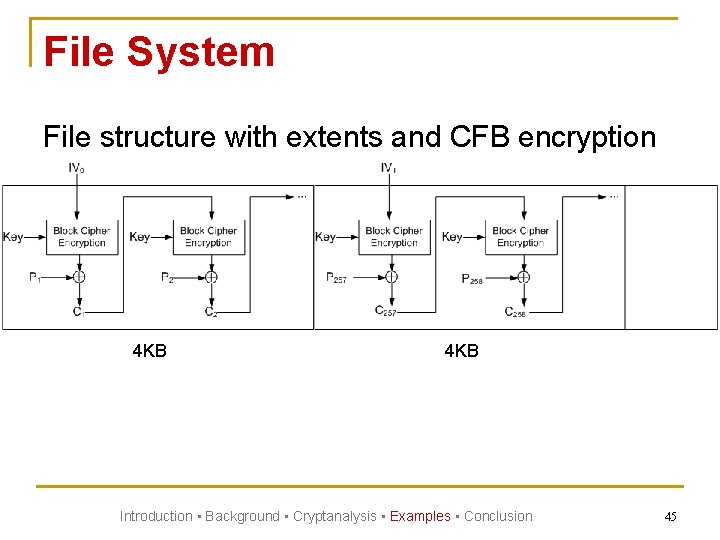
File System File structure with extents and CFB encryption 4 KB Introduction • Background • Cryptanalysis • Examples • Conclusion 45
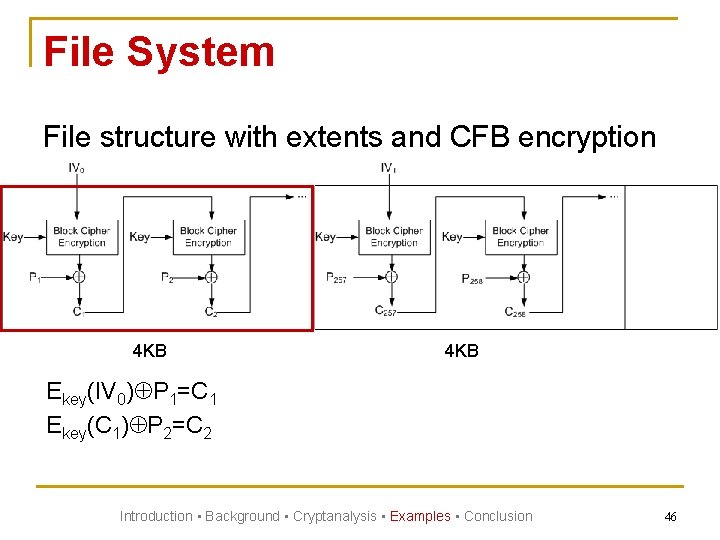
File System File structure with extents and CFB encryption 4 KB Ekey(IV 0) P 1=C 1 Ekey(C 1) P 2=C 2 Introduction • Background • Cryptanalysis • Examples • Conclusion 46
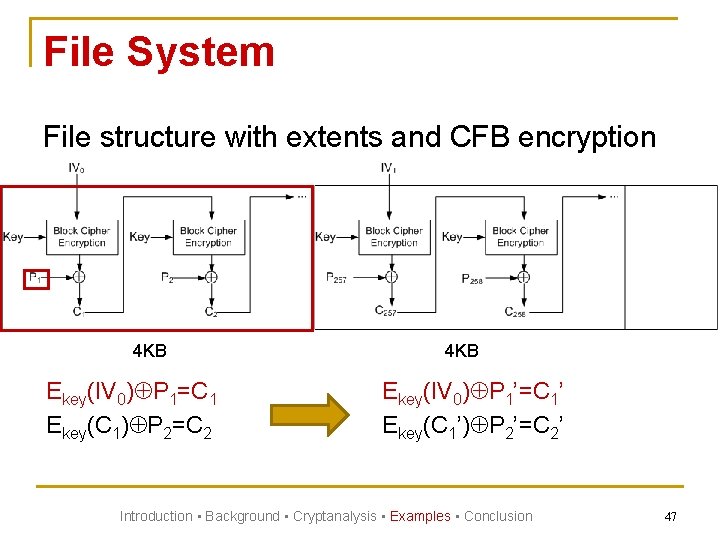
File System File structure with extents and CFB encryption 4 KB Ekey(IV 0) P 1=C 1 Ekey(C 1) P 2=C 2 4 KB Ekey(IV 0) P 1’=C 1’ Ekey(C 1’) P 2’=C 2’ Introduction • Background • Cryptanalysis • Examples • Conclusion 47
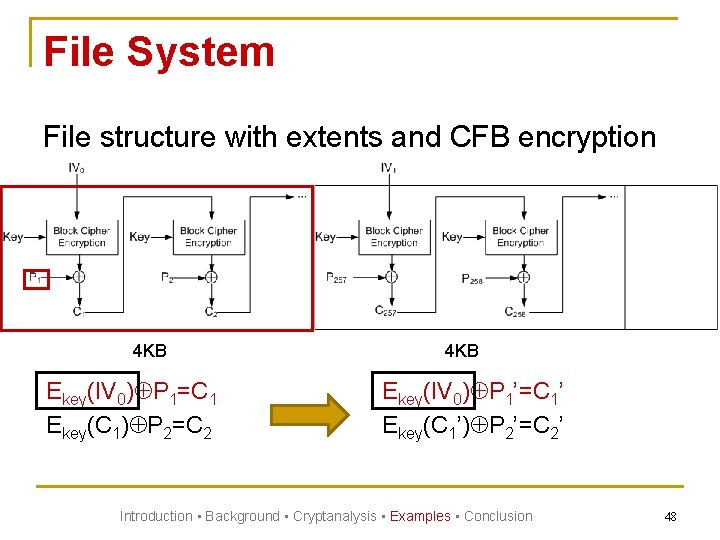
File System File structure with extents and CFB encryption 4 KB Ekey(IV 0) P 1=C 1 Ekey(C 1) P 2=C 2 4 KB Ekey(IV 0) P 1’=C 1’ Ekey(C 1’) P 2’=C 2’ Introduction • Background • Cryptanalysis • Examples • Conclusion 48
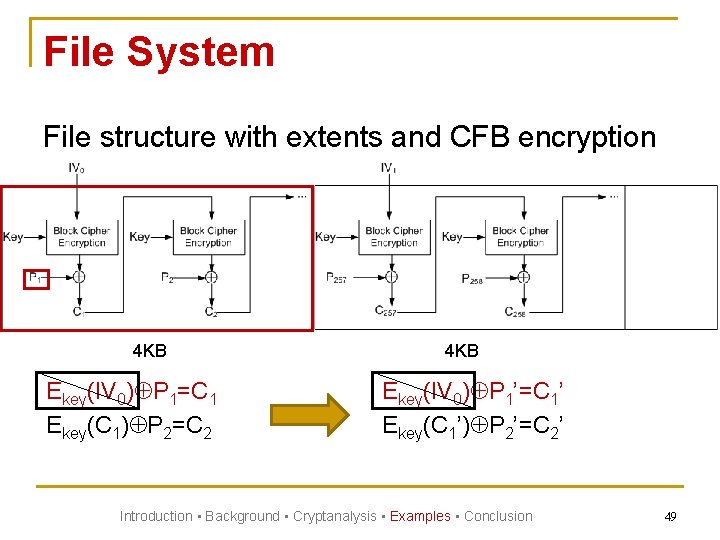
File System File structure with extents and CFB encryption 4 KB Ekey(IV 0) P 1=C 1 Ekey(C 1) P 2=C 2 4 KB Ekey(IV 0) P 1’=C 1’ Ekey(C 1’) P 2’=C 2’ Introduction • Background • Cryptanalysis • Examples • Conclusion 49
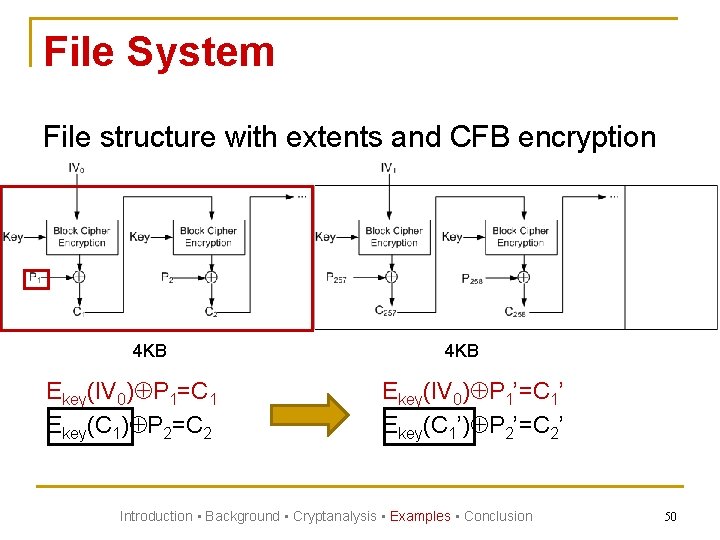
File System File structure with extents and CFB encryption 4 KB Ekey(IV 0) P 1=C 1 Ekey(C 1) P 2=C 2 4 KB Ekey(IV 0) P 1’=C 1’ Ekey(C 1’) P 2’=C 2’ Introduction • Background • Cryptanalysis • Examples • Conclusion 50
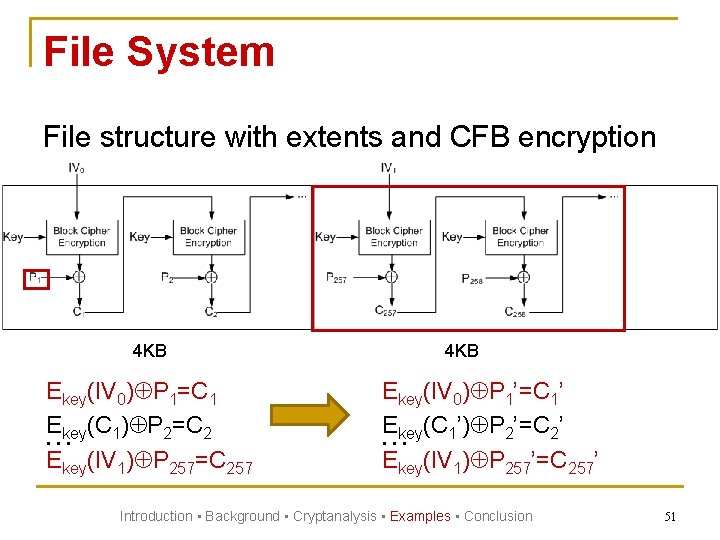
File System File structure with extents and CFB encryption 4 KB Ekey(IV 0) P 1=C 1 Ekey(C 1) P 2=C 2 … Ekey(IV 1) P 257=C 257 4 KB Ekey(IV 0) P 1’=C 1’ Ekey(C 1’) P 2’=C 2’ … Ekey(IV 1) P 257’=C 257’ Introduction • Background • Cryptanalysis • Examples • Conclusion 51
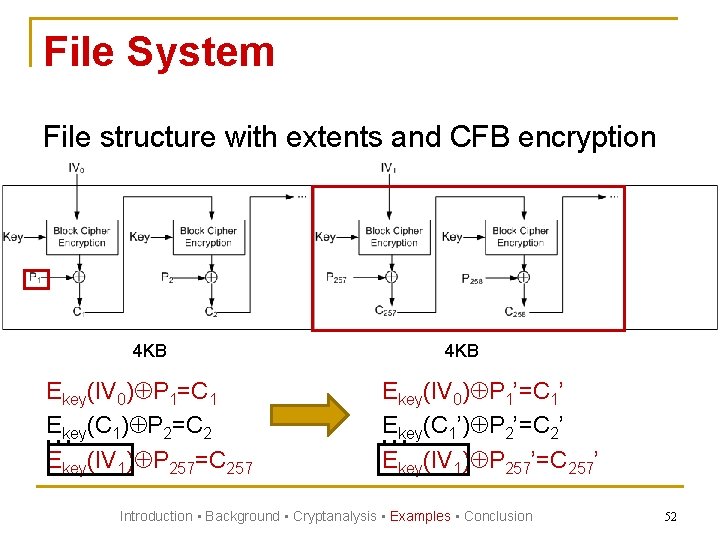
File System File structure with extents and CFB encryption 4 KB Ekey(IV 0) P 1=C 1 Ekey(C 1) P 2=C 2 … Ekey(IV 1) P 257=C 257 4 KB Ekey(IV 0) P 1’=C 1’ Ekey(C 1’) P 2’=C 2’ … Ekey(IV 1) P 257’=C 257’ Introduction • Background • Cryptanalysis • Examples • Conclusion 52
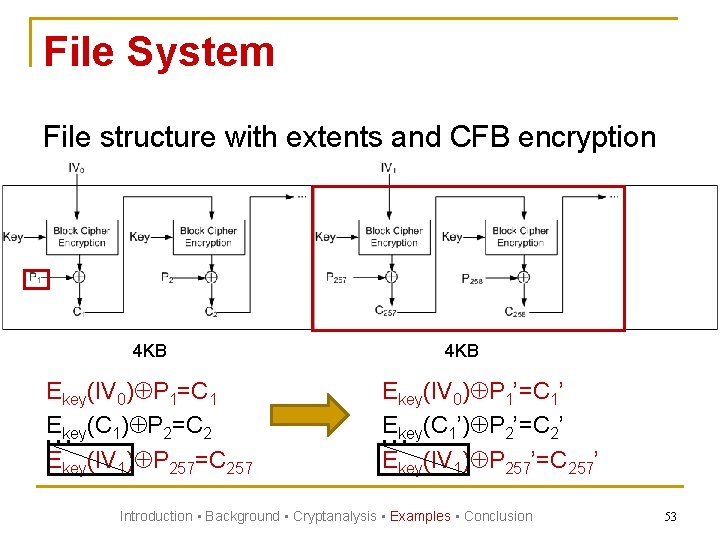
File System File structure with extents and CFB encryption 4 KB Ekey(IV 0) P 1=C 1 Ekey(C 1) P 2=C 2 … Ekey(IV 1) P 257=C 257 4 KB Ekey(IV 0) P 1’=C 1’ Ekey(C 1’) P 2’=C 2’ … Ekey(IV 1) P 257’=C 257’ Introduction • Background • Cryptanalysis • Examples • Conclusion 53
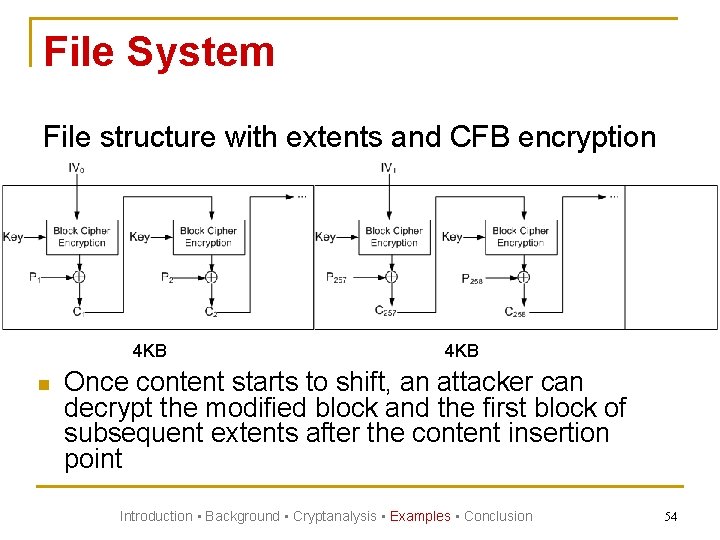
File System File structure with extents and CFB encryption 4 KB Once content starts to shift, an attacker can decrypt the modified block and the first block of subsequent extents after the content insertion point Introduction • Background • Cryptanalysis • Examples • Conclusion 54
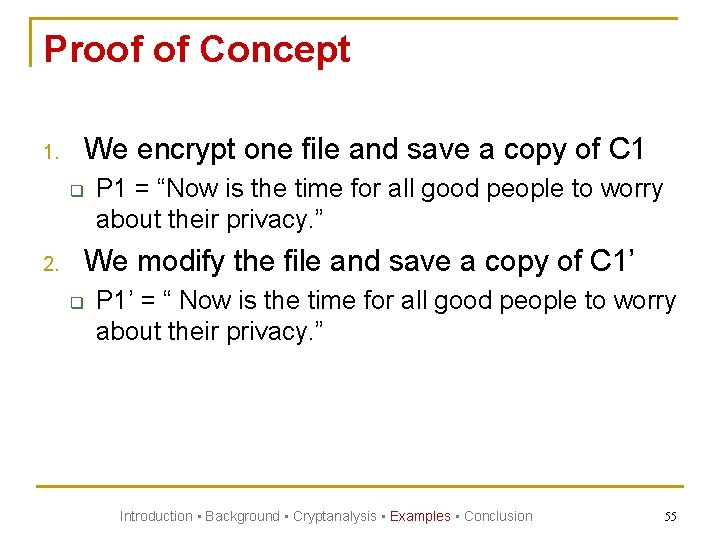
Proof of Concept 1. We encrypt one file and save a copy of C 1 q 2. P 1 = “Now is the time for all good people to worry about their privacy. ” We modify the file and save a copy of C 1’ q P 1’ = “ Now is the time for all good people to worry about their privacy. ” Introduction • Background • Cryptanalysis • Examples • Conclusion 55
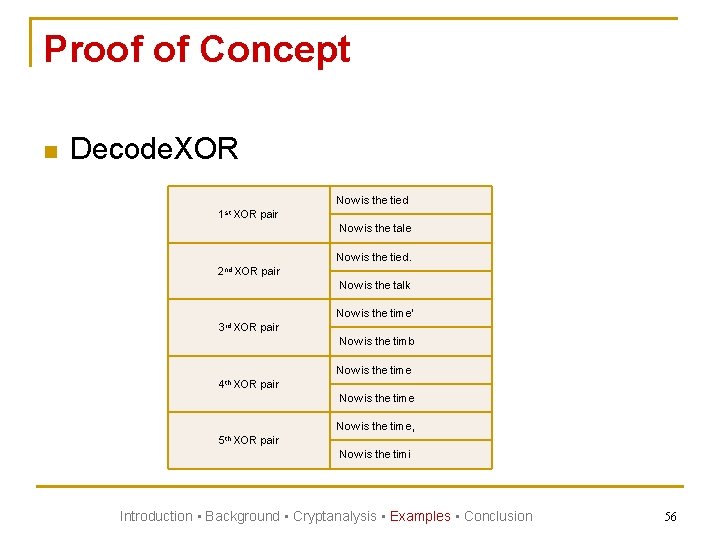
Proof of Concept n Decode. XOR Now is the tied 1 st XOR pair Now is the tale Now is the tied. 2 nd XOR pair Now is the talk Now is the time' 3 rd XOR pair Now is the timb Now is the time 4 th XOR pair Now is the time, 5 th XOR pair Now is the timi Introduction • Background • Cryptanalysis • Examples • Conclusion 56
Flash n n Use of flash storage is becoming ubiquitous Although popular, flash has limitations q q q Each storage location can only be erased up to 100, 000 times Erasure time is slow (in msec) An in-place update involves first erasing the target location before writing new data Introduction • Background • Cryptanalysis • Examples • Conclusion 57
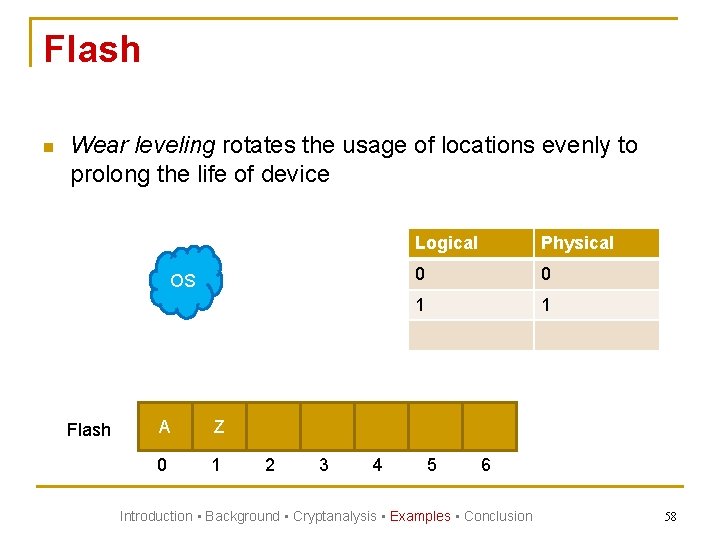
Flash n Wear leveling rotates the usage of locations evenly to prolong the life of device OS Flash A Z 0 1 2 3 4 Logical Physical 0 0 1 1 5 6 Introduction • Background • Cryptanalysis • Examples • Conclusion 58
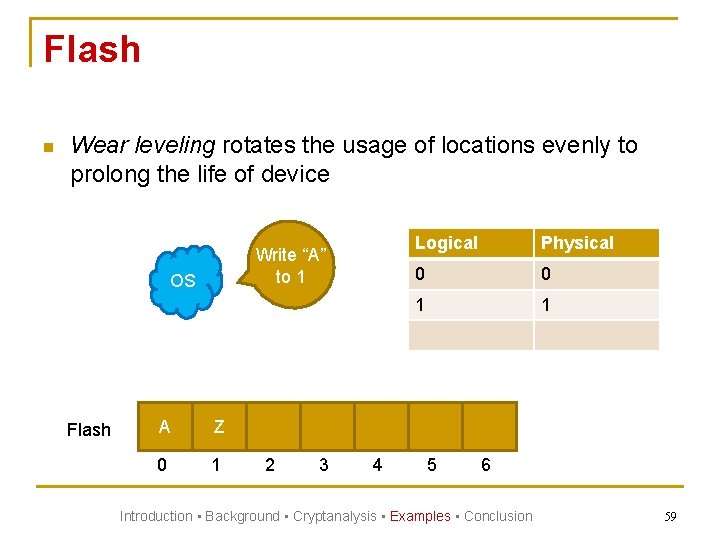
Flash n Wear leveling rotates the usage of locations evenly to prolong the life of device Write “A” to 1 OS Flash A Z 0 1 2 3 4 Logical Physical 0 0 1 1 5 6 Introduction • Background • Cryptanalysis • Examples • Conclusion 59
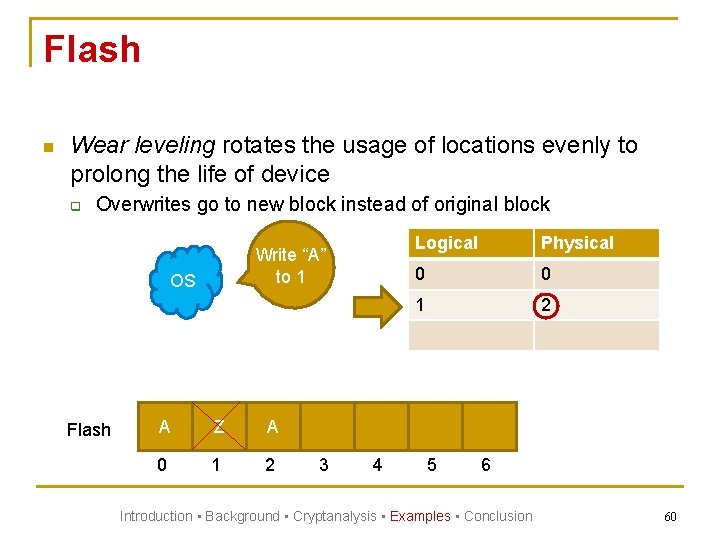
Flash n Wear leveling rotates the usage of locations evenly to prolong the life of device q Overwrites go to new block instead of original block Write “A” to 1 OS Flash A Z A 0 1 2 3 4 Logical Physical 0 0 1 2 5 6 Introduction • Background • Cryptanalysis • Examples • Conclusion 60
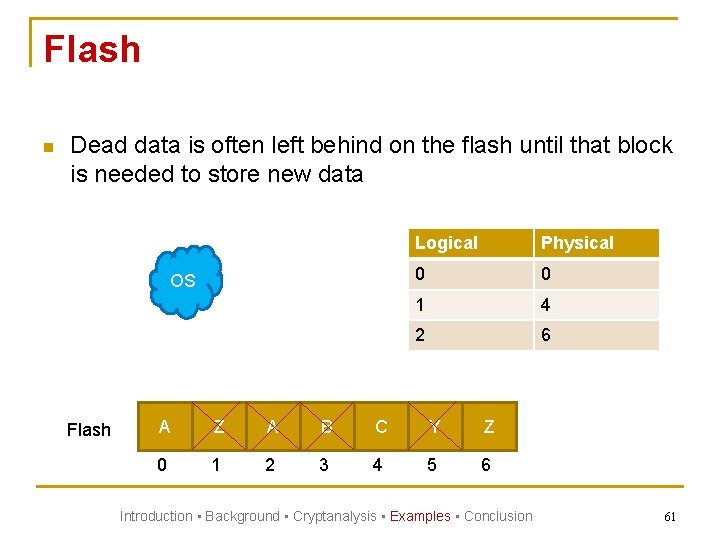
Flash n Dead data is often left behind on the flash until that block is needed to store new data OS Flash Logical Physical 0 0 1 4 2 6 A Z A B C Y Z 0 1 2 3 4 5 6 Introduction • Background • Cryptanalysis • Examples • Conclusion 61
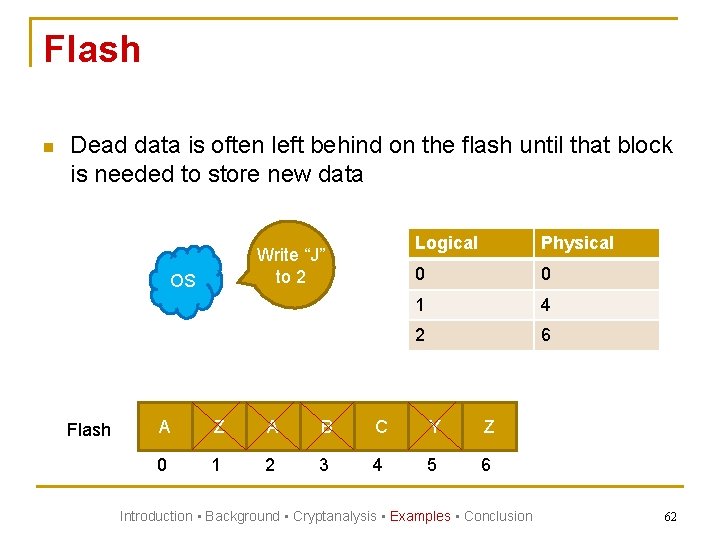
Flash n Dead data is often left behind on the flash until that block is needed to store new data Write “J” to 2 OS Flash Logical Physical 0 0 1 4 2 6 A Z A B C Y Z 0 1 2 3 4 5 6 Introduction • Background • Cryptanalysis • Examples • Conclusion 62
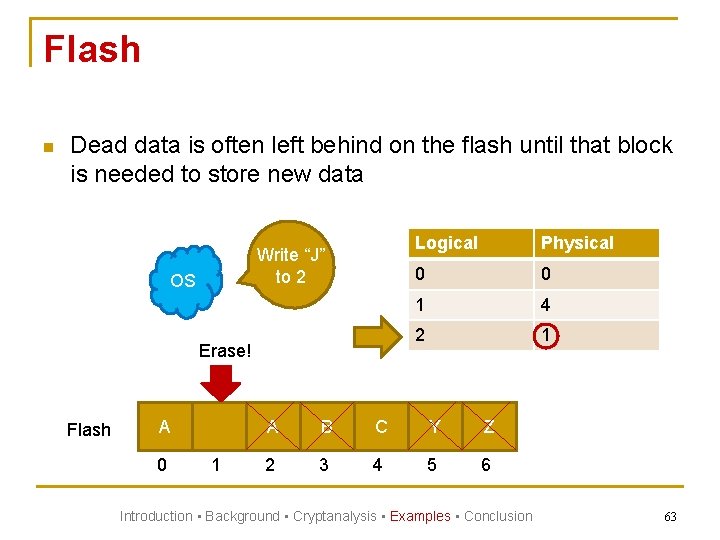
Flash n Dead data is often left behind on the flash until that block is needed to store new data Write “J” to 2 OS Erase! Flash A 0 1 Logical Physical 0 0 1 4 2 1 A B C Y Z 2 3 4 5 6 Introduction • Background • Cryptanalysis • Examples • Conclusion 63
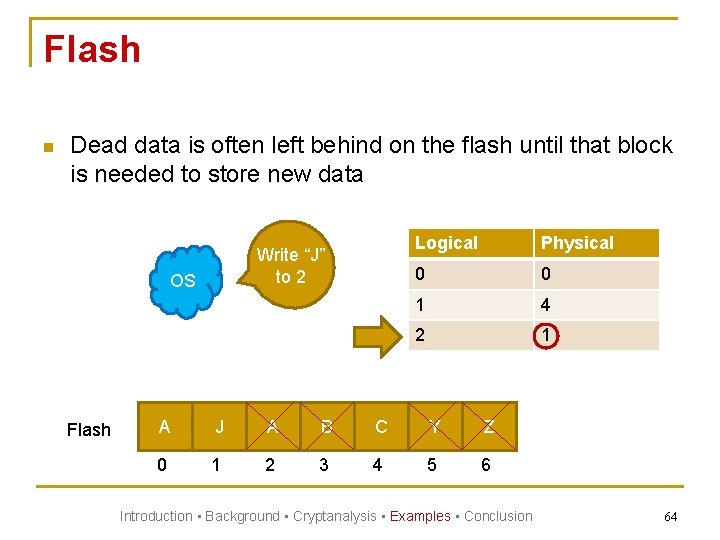
Flash n Dead data is often left behind on the flash until that block is needed to store new data Write “J” to 2 OS Flash Logical Physical 0 0 1 4 2 1 A J A B C Y Z 0 1 2 3 4 5 6 Introduction • Background • Cryptanalysis • Examples • Conclusion 64
Flash n We demonstrate that we can find old encrypted data using JFFS 2 q n Log-based file system with wear leveling for flash Experiment q Mounted jffs 2 on a disk partition using the emulation module block 2 mtd Introduction • Background • Cryptanalysis • Examples • Conclusion 65
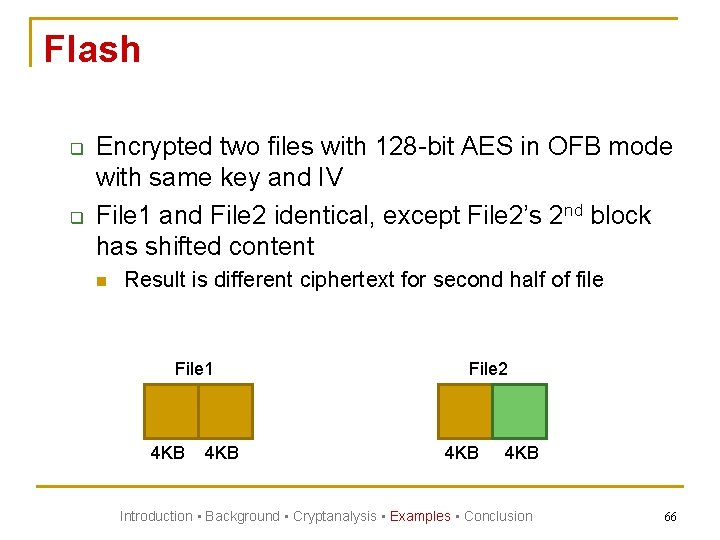
Flash q q Encrypted two files with 128 -bit AES in OFB mode with same key and IV File 1 and File 2 identical, except File 2’s 2 nd block has shifted content n Result is different ciphertext for second half of file File 1 4 KB File 2 4 KB Introduction • Background • Cryptanalysis • Examples • Conclusion 66
Flash q q Copied File 1 onto the jffs 2 flash partition Overwrote the second half of File 1 with the modified second half of File 2 n See if we could find traces of the original second half of file 1 We were able to verify large portions of the original second half of file 1! q With both second halves, we could use Decode. XOR to recover the plaintext Introduction • Background • Cryptanalysis • Examples • Conclusion 67
Lessons n n n Avoid certain encryption modes in storage Do not reuse keys and IVs when reencrypting data Be aware of the properties of legacy storage data path q q q Single generic data type Poor consistency guarantees Information hiding Introduction • Background • Cryptanalysis • Examples • Conclusion 68
Conclusion n Remember storage is different than networks q q q n n In-place updates Content shifting Backups Legacy storage usage patterns and properties threaten confidentiality Knowing what can go wrong is the first step Introduction • Background • Cryptanalysis • Examples • Conclusion 69
Questions? When Cryptography Meets Storage Sarah Diesburg, Chris Meyers, David Lary, and An-I Andy Wang Florida State University 70
Extra Slides 71
Attacks n So how can attacker get two versions of a file’s ciphertext? q Backups n q Multiuser machine n q q q Portable hard drives, flash, versioning file systems… Through root access or poor directory permission settings Email snooping / network sniffing Swap More to the imagination… Introduction • Background • Cryptanalysis • Examples • Conclusion 72
Swap via Hibernation n Memory caching may keep recently modified encrypted data in memory q n n Write-back policy Hibernation allows system to save current memory states to non-volatile storage Could result in multiple stored versions of data encrypted with same key and IV Introduction • Background • Cryptanalysis • Examples • Conclusion 73
Swap via Hibernation n Experiment q q Injected encrypted data into memory Indentified swap candidate blocks with high entropy Created XOR blocks by XORing encrypted file blocks with candidate swap blocks Used Decode. XOR to analyze XOR blocks that exhibit low, but non-zero entropy n n n C C’ = P P’ = low entropy C C = zero entropy C 1 C 2 = high entropy Introduction • Background • Cryptanalysis • Examples • Conclusion 74
Decode. XOR n Tracking and assembling candidate plaintext substrings q q Uses a hash table to track 6 -character candidate substrings that satisfy previous constraints For each 6 -character candidate substring n n Last 5 characters in substring determine storage location of the 6 -character substring First 5 characters in substring points to the hash bin location of the previous candidate substring with the last 5 characters matched Introduction • Background • Cryptanalysis • Examples • Conclusion 75
- Slides: 75