What WINDOWS AZURE AND POWERSHELL POWERED MALWARE BY

What! WINDOWS AZURE AND POWERSHELL POWERED MALWARE BY KIERAN JACOBSEN
The following story is fictional and does not depict any actual person or event. Although inspired by true events, the network, people and company described are completely fictional. Whilst the source code shown today is publicly available, I hold no responsibility for any loss or damage that may arise from you using or manipulating the source code. Everyone involved in this presentation are trained IT Professionals, so please, don’t try this at home! Malware IS DANGEROUS
The Bad Guy Name: Boris Previous Title: System Administrator @ Queensland Department of Widget Management Technical Skills: Power. Shell Group Policy Windows Azure some hacking knowledge
The Malware Written in Power. Shell IT IS VERY OBVIOUS! Signed by SSL Certificate issued by 3 rd Party Root Authority A machine is considered infected when: C: Infected contains required files Drive infection scheduled task is running C&C scheduled task is running Command Control is cloud based, uses Windows Azure VM Role Windows Server 2012 with IIS and Web. DAV
The Malware: Infect-Web. PC. ps 1 Infects a client Clients download and execute script Downloads other files for infection, creates scheduled tasks to communicate with Command Control
The Malware: Invoke-Cand. C. ps 1 Runs as scheduled task Uploads “registration” file to Command Control server, file contains running processes and services Gets “Commands” from Command Control server, filters out tasks previously run, or those not destined to run on host Runs each command using invoke-expression Commands can be executable or any Power. Shell command
A Quick Note: Code Signing Authenticode/Code Signing only ensures us of the authenticity and integrity of the signed file/script/executable Does not prove good intentions Due to Crypto basis, more trusted by technically minded users Many sources of abuse: Forgery Deception Theft See Also: http: //www. f-secure. com/weblog/archives/00002437. html http: //arstechnica. com/security/2012/09/adobe-to-revoke-crypto-key-abused-to-sign 5000 -malware-apps/
The Network Simple, flat network Limited outbound protocols allowed, HTTPS, DNS Single Windows Server 2012, running DC and File and Print Windows 7 SOE All users local administrators UAC was disabled due to an application compatibility issue VNC runs on all machines, as a service account –which is a domain admin
What Boris Knows Usernames, computer names, IP addressing… Security and Firewall policies That passwords have all been changed Group Policy restrictions – Power. Shell Execution Policies Personal details of those remaining Email addresses Pets and favourite animals Hobbies and interests
The Plan of Attack 1. Infect previous co-workers 1. Alice: His former Boss 2. Bob: The co-worker he didn’t like 3. Eve: The paranoid security administrator 4. Jane: The C-Level exec 2. Get a Domain Admin account username and password 3. ? 4. Profit!
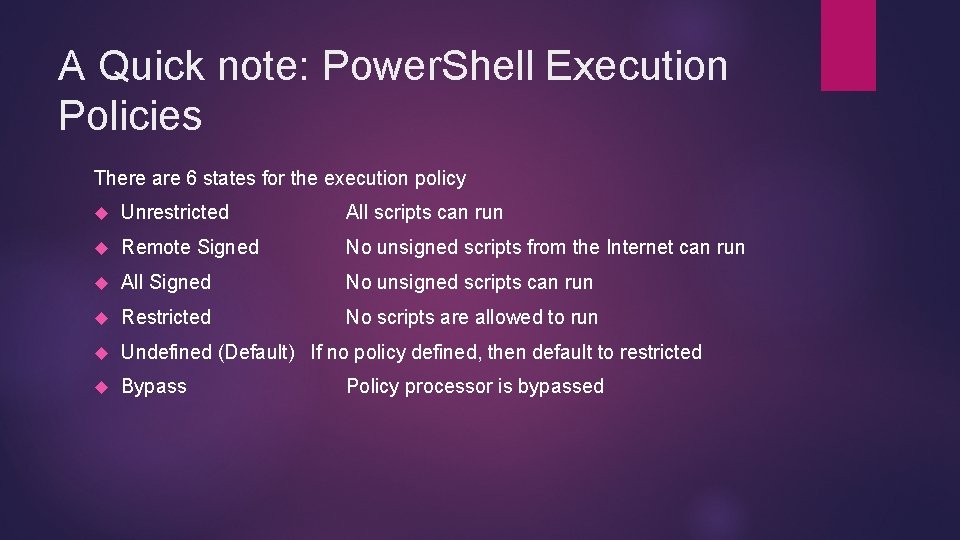
A Quick note: Power. Shell Execution Policies There are 6 states for the execution policy Unrestricted All scripts can run Remote Signed No unsigned scripts from the Internet can run All Signed No unsigned scripts can run Restricted No scripts are allowed to run Undefined (Default) If no policy defined, then default to restricted Bypass Policy processor is bypassed
Demo: Boris infects Alice’s PC
Demo: Boris infects Bob’s PC
Demo: Boris infects Eve’s PC
Code: Bypassing Restricted Execution Policy
Demo: Boris gets a domain admin username and password
Demo: Demo infects the server
Demo: Boris cracks open AD
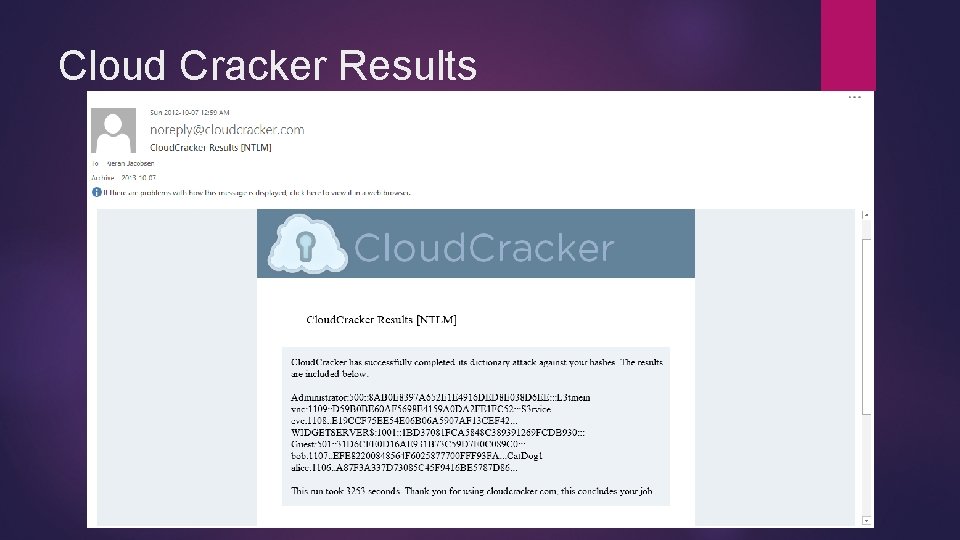
Cloud Cracker Results
Malicious HID Devices HID: Human Interface Device, examples generally include mice keyboards, fingerprint readers, joysticks, webcams, gamepads Device shown today: Hak 5 USB Rubber Duckie Retails for: USD 60 Contains Micro SD storage card and 60 MHz CPU When placed in plastic case, will appear like any other USB device Appears as a HID Keyboard – Bypassing USB Storage controls Simple programming language, can do anything you could do with a keyboard Cross Platform
Demo: Boris goes for complete domination, infects Jane’s PC
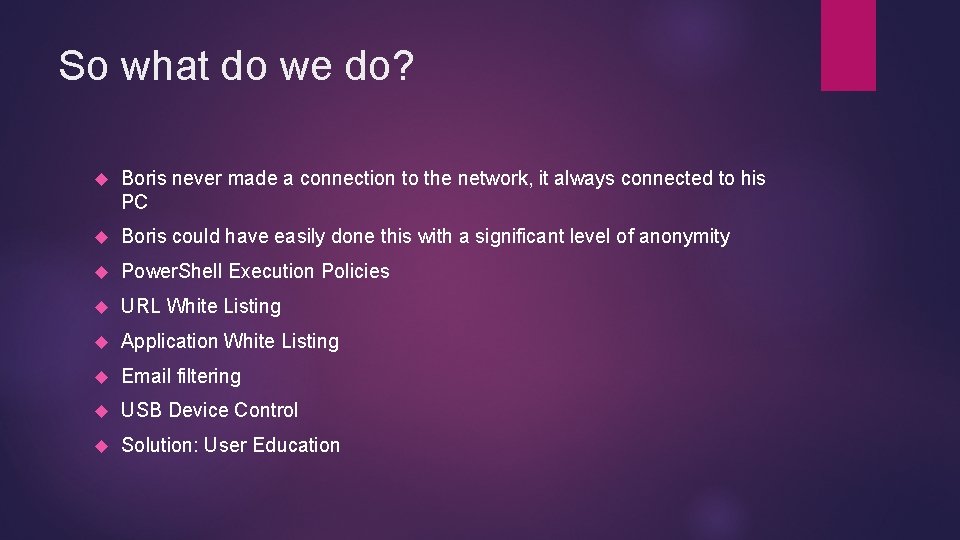
So what do we do? Boris never made a connection to the network, it always connected to his PC Boris could have easily done this with a significant level of anonymity Power. Shell Execution Policies URL White Listing Application White Listing Email filtering USB Device Control Solution: User Education
Questions? More Info… Website: http: //aperturescience. su Twitter: @kjacobsen Email Kieran@thekgb. su Git. Hub Project: http: //bit. ly/pscandc Tools: Pwdump. X: http: //bit. ly/pwdumpx Quarks PW Dump: http: //bit. ly/quarkspwdump Cloudcracker. com: http: //bit. ly/cloudcracker Usb rubber duckie: http: //bit. ly/TFe 7 EG Hak 5: http: //hak 5. org
- Slides: 23