What is security awareness Cybersecurity awareness is awareness
What is security awareness ?
Cybersecurity awareness is awareness of threats that could compromise the information security infrastructure and allow intruders to (1) gain unauthorized access to data (data breach) and (2) interrupt our services (denial of service attack). Cybersecurity awareness also involves awareness of risks. What is the difference between risks and threats ?
Why security awareness is important?
“Research shows that if we like an activity, we tend to judge its benefits to be high and its risk to be low (Slovic 2010)” “Conversely, if we dislike the activity, we judge it as lowbenefit and high-risk. Because of this, the perception of risk by individuals and groups within an organization tends to be biased by their preferences, roles, and objectives”
Important of cyber-security awareness: “technical controls have not kept pace with the attackers. Many exploits are reaching users because technical controls, particularly those on endpoint devices, have failed to prevent them. We are therefore more reliant on the user’s ability to detect suspicious activity” “the 2015 Data Breach Investigations Report found that the percentage of users deceived by phishing actually increased from previous years, with 23% opening phishing messages and 11% clicking on attachments (Verizon 2015)” “Among CISOs surveyed recently by best-practices firm Corporate Executive Board, 50% said that insecure behaviors cause more than half of all breaches; but they also said employees are key to uncovering suspicious activity (CEB 2015)”
Important of cyber-security awareness: “Our goals include creating a more security-conscious workforce so that users are more aware of threats and vulnerabilities, and make better security decisions. Furthermore, we need to influence employees’ behavior both within the workplace and when they are home or traveling”
How to improve security awareness?
Replacing user commitment with user compliance Instead of blocking messages from being sent, display a security warning “If an employee tried to transmit a confidential document, the software displayed a message that explained the potential risks and suggested ways to protect the information, such as encryption. After all, users may have good reasons for sending confidential documents, and preventing transmission could be detrimental rather than beneficial to the business. The company found that this warning caused 70% of users to change their behavior, representing a major reduction in risk. Yet because of the way the software was configured, users didn’t complain about the security burden. The roundabout approach reduced risk without interfering with users’ productivity”
https: //www. getusecure. com/post/3 -reasons-why-youshould-phish-your-own-employees
Important of cyber-security awareness: “When an employee requested access to an application that handles sensitive information, they were automatically prompted to take training that focused on the related security and privacy concerns. We also used online training including video and other visually stimulating material as well as entertaining, interactive tools to help engage users” Cyber Security Training at Intel

How do we motivate cyber secure behavior ? “We also found we could help maintain and increase awareness by publishing security related articles on Intel’s primary employee portal. Many of these articles included a personal aspect, such as preventing identity theft, keeping children safe online, and home wireless security tips. The focus on personal concerns recognized that the way employees behave outside the office is as important to enterprise security as their behavior in the office”
“______ are intense role-playing exercises in which employees take on the role of attackers and attempt to compromise key assets using any feasible methods. I have found ____ are particularly valuable for analyzing threats that may have major consequences but whose vulnerabilities are not well understood. ” Fill in the blanks
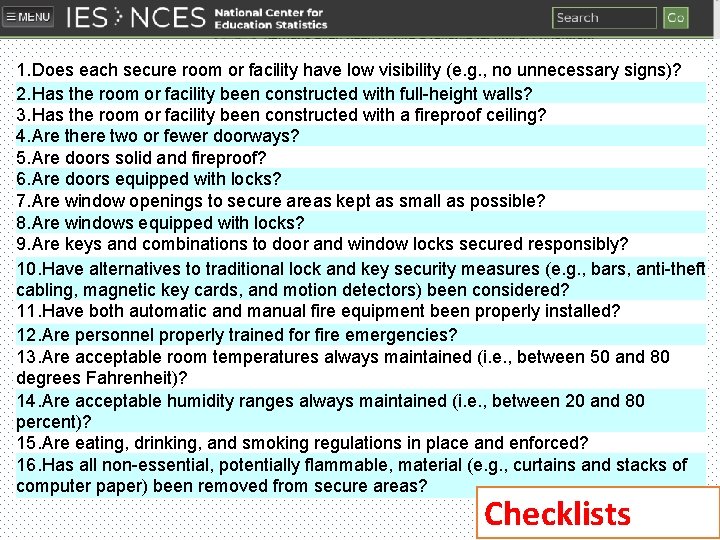
1. Does each secure room or facility have low visibility (e. g. , no unnecessary signs)? 2. Has the room or facility been constructed with full-height walls? 3. Has the room or facility been constructed with a fireproof ceiling? 4. Are there two or fewer doorways? 5. Are doors solid and fireproof? 6. Are doors equipped with locks? 7. Are window openings to secure areas kept as small as possible? 8. Are windows equipped with locks? 9. Are keys and combinations to door and window locks secured responsibly? 10. Have alternatives to traditional lock and key security measures (e. g. , bars, anti-theft cabling, magnetic key cards, and motion detectors) been considered? 11. Have both automatic and manual fire equipment been properly installed? 12. Are personnel properly trained for fire emergencies? 13. Are acceptable room temperatures always maintained (i. e. , between 50 and 80 degrees Fahrenheit)? 14. Are acceptable humidity ranges always maintained (i. e. , between 20 and 80 percent)? 15. Are eating, drinking, and smoking regulations in place and enforced? 16. Has all non-essential, potentially flammable, material (e. g. , curtains and stacks of computer paper) been removed from secure areas? Checklists
https: //www. youtube. com/watch? time_continue=226&v=q. Lgbhf. ZBwos The AAA model: Authentication • Watch the video then answer the following questions • Is asking for two passwords considered a form of 2 FA? • What is the risk of using SMS messages in 2 FA?
https: //www. youtube. com/watch? time_continue=226&v=q. Lgbhf. ZBwos The AAA model: Authentication https: //blog. dashlane. com/10 -reasonsbiometrics-wont-replace-passwords-anytimesoon/ Which reason is the most convincing ?
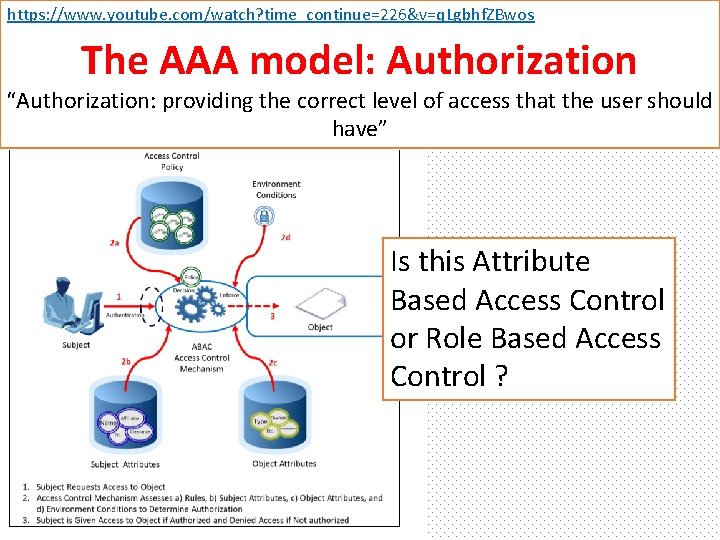
https: //www. youtube. com/watch? time_continue=226&v=q. Lgbhf. ZBwos The AAA model: Authorization “Authorization: providing the correct level of access that the user should have” Is this Attribute Based Access Control or Role Based Access Control ?
The AAA model: Accounting “Accounting: keeping track of what users do while they are logged into a system” Number of unsuccessful login attempts Time of the last login attempt IP addresse(s) Resources accessed
The AAA model: Accounting “Accounting: keeping track of what users do while they are logged into a system” “The last stage of AAA, accounting simply records which clients accessed the network, what they were granted access to, and when they disconnected from the network. Accounting has always been widely used in the Internet Service Provide (ISP) space because auditing network access is the basis for billing ISP customers. Increasingly, accounting is being used as a way to correlate client attribute information (username, IP address, etc. ) with actions and events on the network” https: //www. cisco. com/c/en/us/about/press/internet-protocol-journal/back-issues/table-contents-35/101 -aaa-part 1. html
- Slides: 19