What about new RFID cards C IJET International
What about new RFID cards? (C) IJET International, Inc. All rights reserved. 1
Information Security is becoming more critical… L CONFIDENTIA (C) IJET International, Inc. All rights reserved. 2
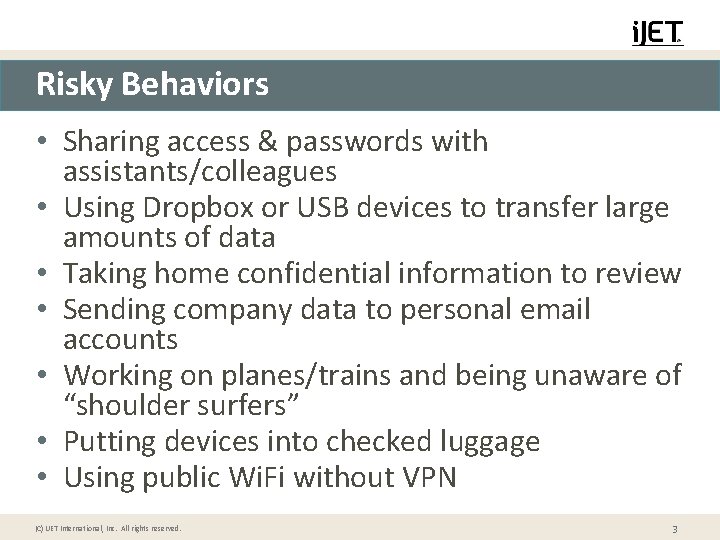
Risky Behaviors • Sharing access & passwords with assistants/colleagues • Using Dropbox or USB devices to transfer large amounts of data • Taking home confidential information to review • Sending company data to personal email accounts • Working on planes/trains and being unaware of “shoulder surfers” • Putting devices into checked luggage • Using public Wi. Fi without VPN (C) IJET International, Inc. All rights reserved. 3
Mitigating the attack • Avoid connecting to hotel Wi-Fi or any other public or untrusted networks • Use a mobile hotspot for Internet access • Better yet, use VPN for all Internet traffic Open (C) IJET International, Inc. All rights reserved. 4
Mitigating the Attack • Do not use thumb drives you get from vendors or contacts at seminars or conferences without having them scanned for Malware • Be cautious of emails received from people pretending to have met you at the conference • Be cautious of new requests for access to social media sites (C) IJET International, Inc. All rights reserved. 5
Social Media - Sharing Information • Social media provides names, phrases, dates and other information that can be fed into password crackers • Social media alerts hackers to your travel plans • Social Engineering to gain access to your information can occur virtually as well as face to face (C) IJET International, Inc. All rights reserved. 6
QUESTIONS? For additional information contact: Mark Donohue, VP Risk Management Programs i. JET International, Inc. donohuem@ijet. com www. ijet. com (C) IJET International, Inc. All rights reserved. 7
- Slides: 7