Welkom bij de eerste bijeenkomst van het vak
Welkom bij de eerste bijeenkomst van het vak Integratie van Sofware Systemen voor Informatiekundestudenten. Vereiste voorkennis: Gedistribueerde Software Systemen. Communicatie via: Blackboard, email, http: //www. niii. ru. nl/R. de. Vries/iss. html 2/6/2022 Integratie van Software Systemen, college 1 1
Integratie van Software Systemen n n n Informatiekunde Jan Tretmans, René de Vries Middleware, Gedistribueerd Programmeren, Java Boeken: Distributed Computing, Liu Web Services, Alonso etal. Verder aanbevolen: IT Architectures and Middleware, Strategies for Building Large, Integrated Systems, Peter Bye, Chris Britton en papers Wekelijks kleine zelfstudieopgaven Tentamen + 2 grotere practicumopgaven en hoorcollege in groepjes van 2 (voorwaarde vooraf) 2/6/2022 Integratie van Software Systemen, college 1 2
Onderwerpen Synchronization, Paradigmas for Distributed Computing, Sockets n Client-Server, Multicasting, Distributed Objects n RMI, XML, CGI, HTTP, CORBA, . NET, SOAP, Webservices, Applets, Servlets, Mobile Agents, … n Architectuur van geïntegreerde software systemen n 2/6/2022 Integratie van Software Systemen, college 1 3
Distributed computing Mei-Ling Liu Professor Department of Computer Science California Polytechnic University United States of America 2/6/2022 Integratie van Software Systemen, college 1 4
Systems en Distribution n A system is a black box that is capable of providing a service to its user by means of interaction. n A distributed system is a regularly interacting or independent group of items forming a unified system. 2/6/2022 Integratie van Software Systemen, college 1 5
Distributed system, distributed computing Early computing was performed on a single processor. Uni-processor computing can be called centralized computing. n A distributed system is a collection of independent computers or processes, interconnected via a network, capable of collaborating on a task. n Distributed computing is computing performed in a distributed system. n 2/6/2022 Integratie van Software Systemen, college 1 6
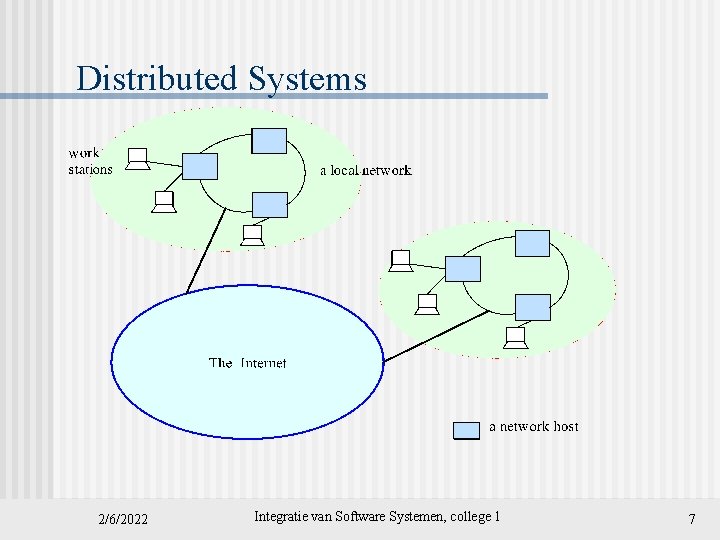
Distributed Systems 2/6/2022 Integratie van Software Systemen, college 1 7
Examples of Distributed systems Network of workstations (NOW): a group of networked personal workstations connected to one or more server machines. n The Internet n An intranet: a network of computers and workstations within an organization, segregated from the Internet via a protective device (a firewall). n 2/6/2022 Integratie van Software Systemen, college 1 8
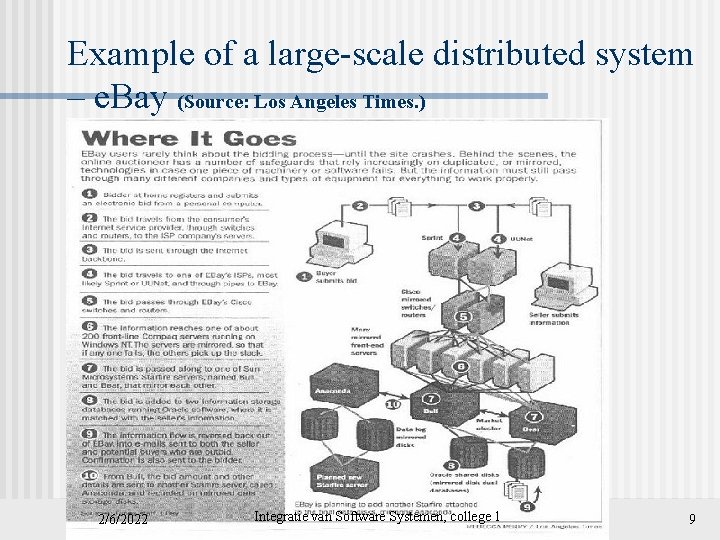
Example of a large-scale distributed system – e. Bay (Source: Los Angeles Times. ) 2/6/2022 Integratie van Software Systemen, college 1 9
Computers in a Distributed System Workstations: computers used by end-users to perform computing n Server machines: computers which provide resources and services n Personal Assistance Devices: handheld computers connected to the system via a wireless communication link. n 2/6/2022 Integratie van Software Systemen, college 1 10
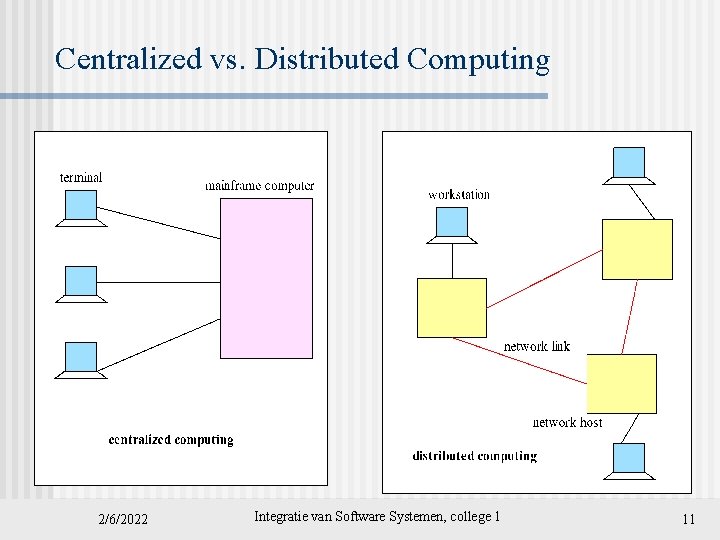
Centralized vs. Distributed Computing 2/6/2022 Integratie van Software Systemen, college 1 11
Monolithic mainframe applications vs. distributed applications n The monolithic mainframe application architecture: n n n Separate, single-function applications, such as order-entry or billing Applications cannot share data or other resources Developers must create multiple instances of the same functionality (service). Proprietary (user) interfaces The distributed application architecture: n n Integrated applications Applications can share resources A single instance of functionality (service) can be reused. Common user interfaces 2/6/2022 Integratie van Software Systemen, college 1 12
Why distributed computing? Economics: distributed systems allow the pooling of resources, including CPU cycles, data storage, input/output devices, and services. n Reliability: distributed systems allow replication of resources and/or services, thus reducing service outage due to failures. n The Internet has become a universal platform for distributed computing. n 2/6/2022 Integratie van Software Systemen, college 1 13
Distributed Computing Strengths n n The affordability of computers and availability of network access Resource sharing Scalability Fault Tolerance Weaknesses n n Multiple Points of Failure: the failure of one or more participating computers, or one or more network links, can spell trouble. Security Concerns: In a distributed system, there are more opportunities for unauthorized attack. 2/6/2022 Integratie van Software Systemen, college 1 14
Introductory Basics: three areas Some of the notations and concepts from these areas will be employed from time to time in the presentations for this course: Software engineering n Operating systems n Networks. n 2/6/2022 Integratie van Software Systemen, college 1 15
Software Engineering Basics 2/6/2022 Integratie van Software Systemen, college 1 16
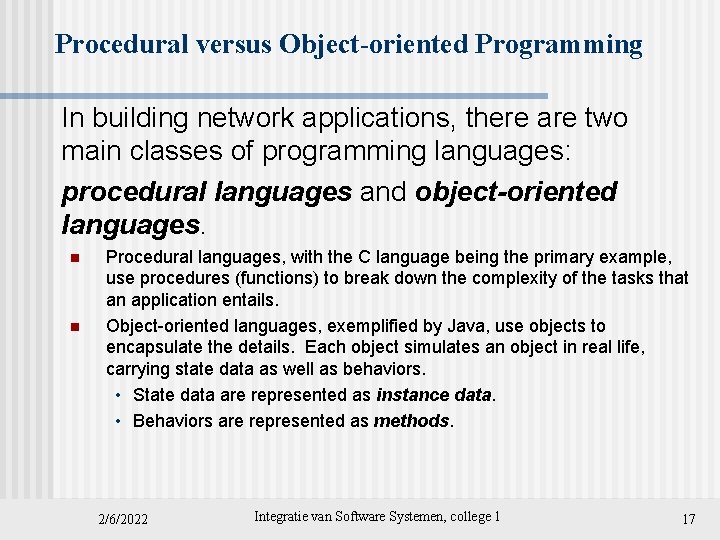
Procedural versus Object-oriented Programming In building network applications, there are two main classes of programming languages: procedural languages and object-oriented languages. n n Procedural languages, with the C language being the primary example, use procedures (functions) to break down the complexity of the tasks that an application entails. Object-oriented languages, exemplified by Java, use objects to encapsulate the details. Each object simulates an object in real life, carrying state data as well as behaviors. • State data are represented as instance data. • Behaviors are represented as methods. 2/6/2022 Integratie van Software Systemen, college 1 17
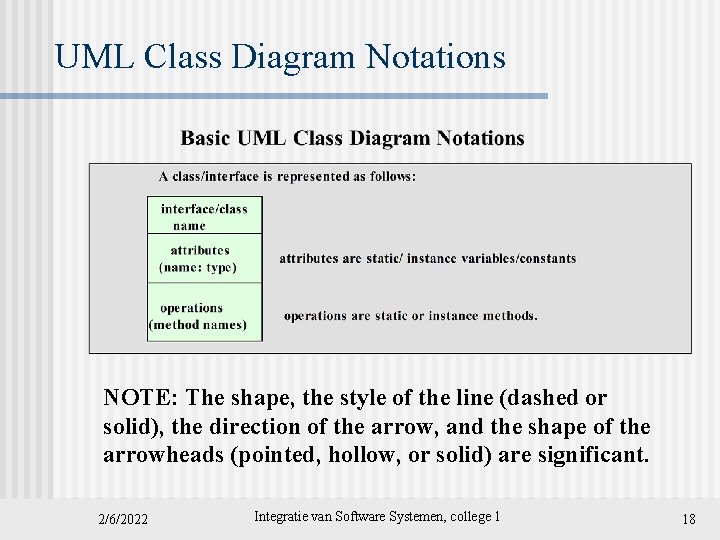
UML Class Diagram Notations NOTE: The shape, the style of the line (dashed or solid), the direction of the arrow, and the shape of the arrowheads (pointed, hollow, or solid) are significant. 2/6/2022 Integratie van Software Systemen, college 1 18
The Architecture of Distributed Applications 2/6/2022 Integratie van Software Systemen, college 1 19
Operating Systems Basics 2/6/2022 Integratie van Software Systemen, college 1 20
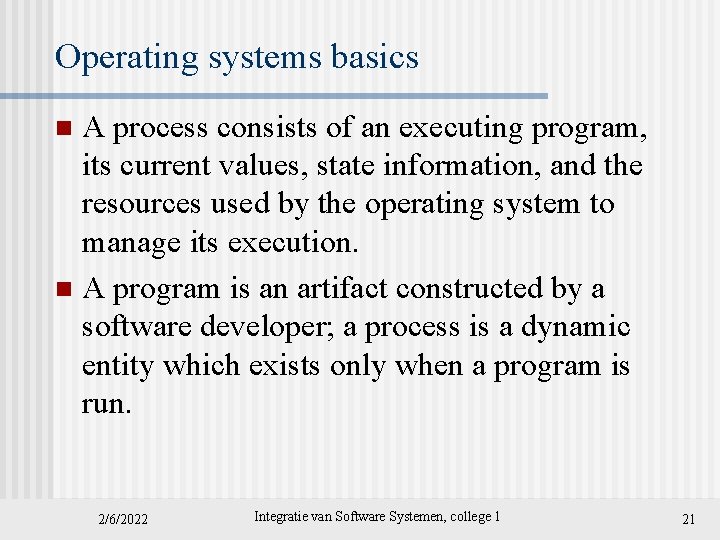
Operating systems basics A process consists of an executing program, its current values, state information, and the resources used by the operating system to manage its execution. n A program is an artifact constructed by a software developer; a process is a dynamic entity which exists only when a program is run. n 2/6/2022 Integratie van Software Systemen, college 1 21
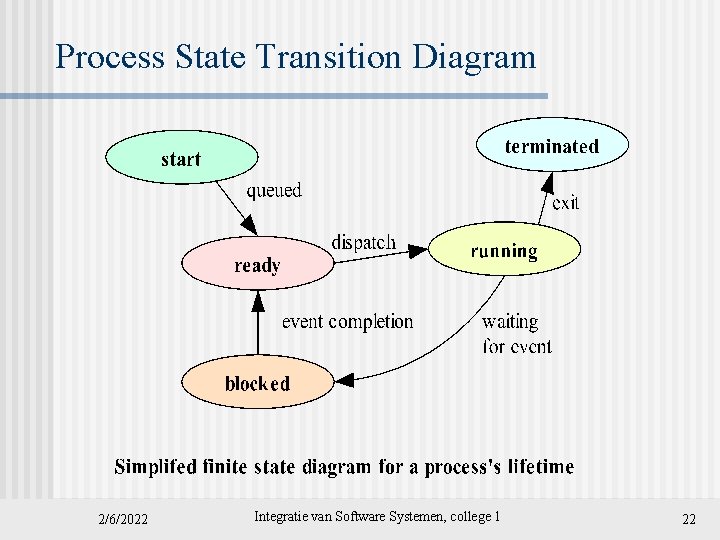
Process State Transition Diagram 2/6/2022 Integratie van Software Systemen, college 1 22
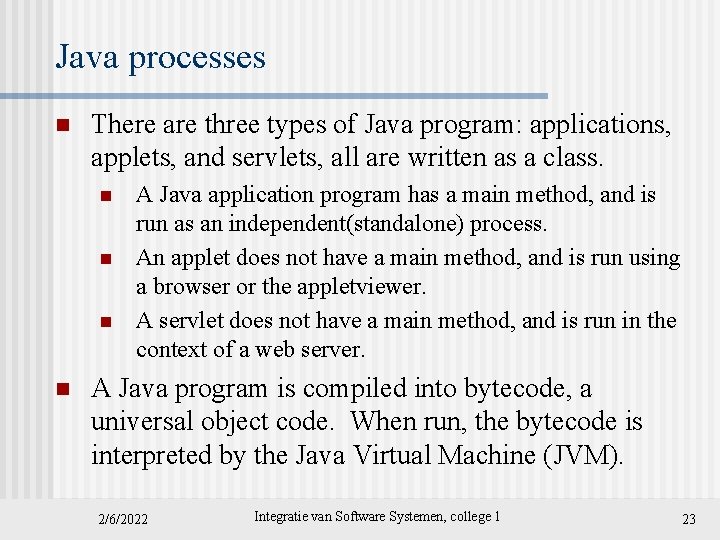
Java processes n There are three types of Java program: applications, applets, and servlets, all are written as a class. n n A Java application program has a main method, and is run as an independent(standalone) process. An applet does not have a main method, and is run using a browser or the appletviewer. A servlet does not have a main method, and is run in the context of a web server. A Java program is compiled into bytecode, a universal object code. When run, the bytecode is interpreted by the Java Virtual Machine (JVM). 2/6/2022 Integratie van Software Systemen, college 1 23
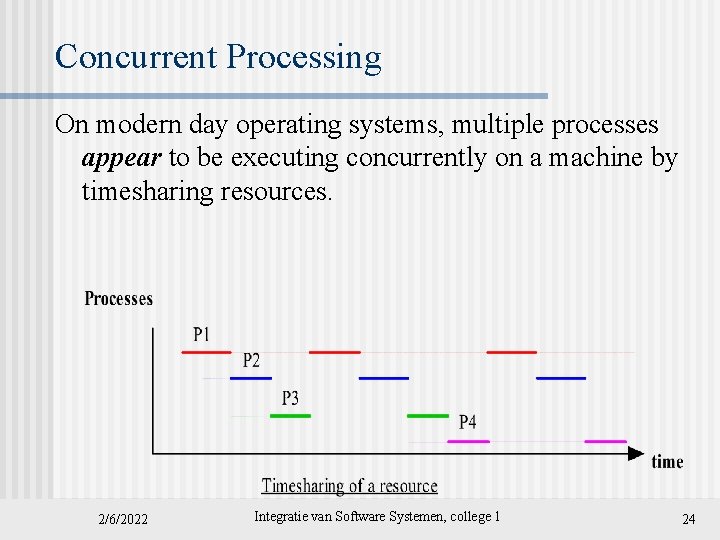
Concurrent Processing On modern day operating systems, multiple processes appear to be executing concurrently on a machine by timesharing resources. 2/6/2022 Integratie van Software Systemen, college 1 24
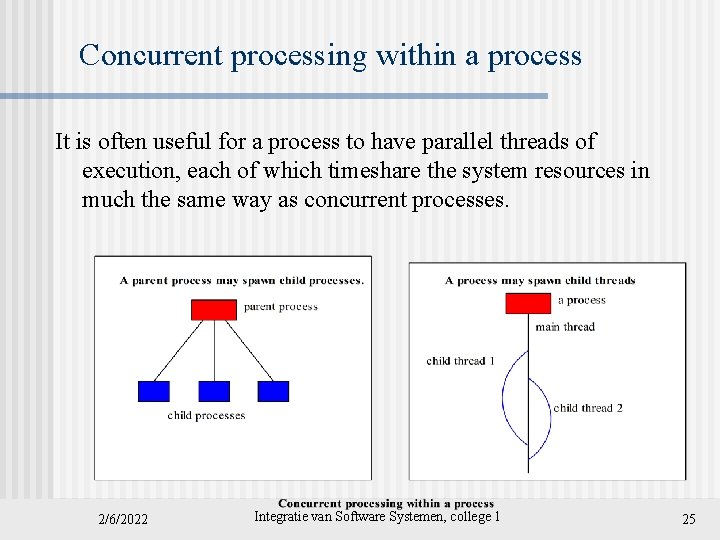
Concurrent processing within a process It is often useful for a process to have parallel threads of execution, each of which timeshare the system resources in much the same way as concurrent processes. 2/6/2022 Integratie van Software Systemen, college 1 25
Java threads n n The Java Virtual Machine allows an application to have multiple threads of execution running concurrently. Java provides a Thread class: public class Thread extends Object implements Runnable n When a Java Virtual Machine starts up, there is usually a single thread (which typically calls the method named main of some designated class). The Java Virtual Machine continues to execute threads until either of the following occurs: n n The exit method of class Runtime has been called and the security manager has permitted the exit operation to take place. All threads have terminated, either by returning from the call to the run method or by throwing an exception that propagates beyond the run method. 2/6/2022 Integratie van Software Systemen, college 1 26
Two ways to create a new thread of execution Using a subclass of the Thread class n Using a class that implements the Runnable interface n 2/6/2022 Integratie van Software Systemen, college 1 27
Thread-safe Programming n n n When two threads independently access and update the same data object, such as a counter, as part of their code, the updating needs to be synchronized. (See next slide. ) Because threads are executed concurrently, it is possible for one of the updates to be overwritten by the other due to the sequencing of the two sets of machine instructions executed in behalf of the two threads. To protect against the possibility, a synchronized method can be used to provide mutual exclusion. 2/6/2022 Integratie van Software Systemen, college 1 28
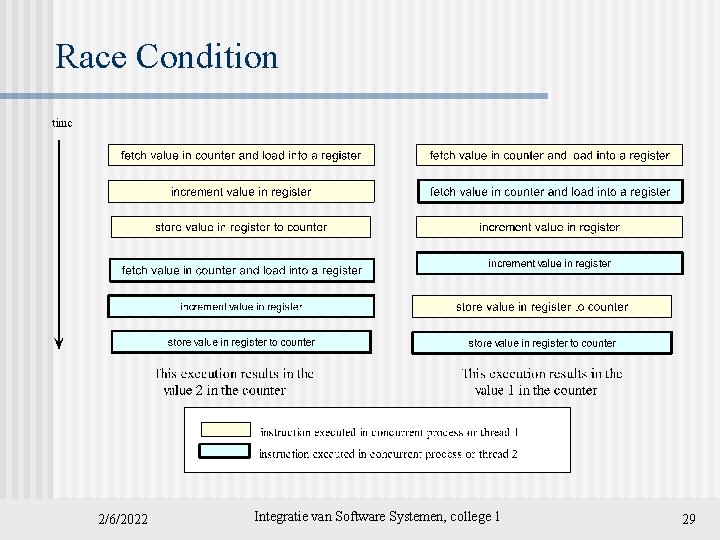
Race Condition 2/6/2022 Integratie van Software Systemen, college 1 29
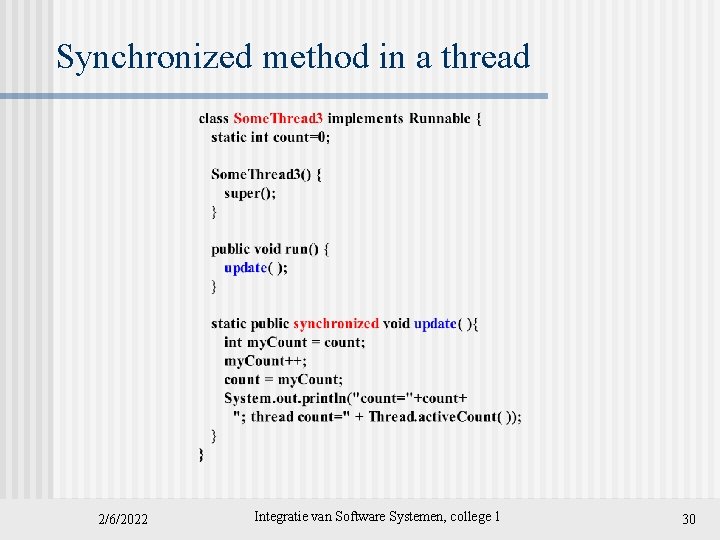
Synchronized method in a thread 2/6/2022 Integratie van Software Systemen, college 1 30
Network Basics 2/6/2022 Integratie van Software Systemen, college 1 31
Network standards and protocols n n n On public networks such as the Internet, it is necessary for a common set of rules to be specified for the exchange of data. Such rules, called protocols, specify such matters as the formatting and semantics of data, flow control, error correction. Software can share data over the network using network software which supports a common set of protocols. 2/6/2022 Integratie van Software Systemen, college 1 32
The network architecture n n Network hardware transfers electronic signals, which represent a bit stream, between two devices. Modern day network applications require an application programming interface (API) which masks the underlying complexities of data transmission. A layered network architecture allows the functionalities needed to mask the complexities to be provided incrementally, layer by layer. Actual implementation of the functionalities may not be clearly divided by layer. 2/6/2022 Integratie van Software Systemen, college 1 33
The OSI seven-layer network architecture 2/6/2022 Integratie van Software Systemen, college 1 34
Network Architecture The division of the layers is conceptual: the implementation of the functionalities need not be clearly divided as such in the hardware and software that implements the architecture. The conceptual division serves at least two useful purposes : Systematic specification of protocols it allows protocols to be specified systematically 2. Conceptual Data Flow: it allows programs to be written in terms of logical data flow. 1. 2/6/2022 Integratie van Software Systemen, college 1 35
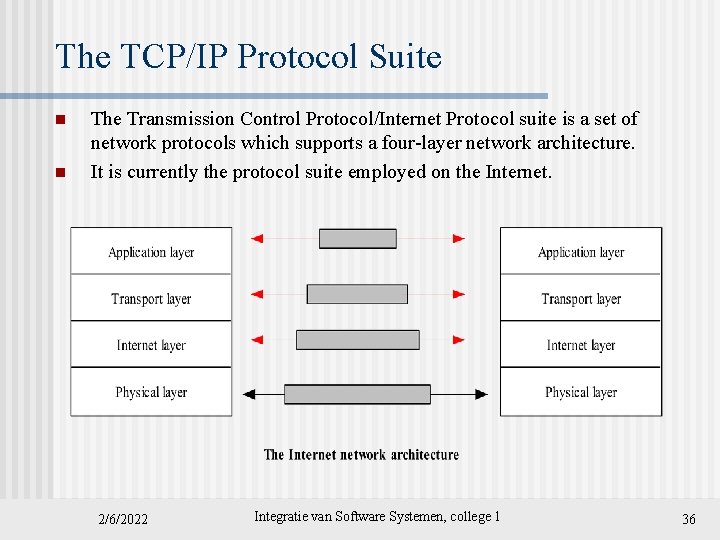
The TCP/IP Protocol Suite n n The Transmission Control Protocol/Internet Protocol suite is a set of network protocols which supports a four-layer network architecture. It is currently the protocol suite employed on the Internet. 2/6/2022 Integratie van Software Systemen, college 1 36
The TCP/IP Protocol Suite -2 n n n The Internet layer implements the Internet Protocol, which provides the functionalities for allowing data to be transmitted between any two hosts on the Internet. The Transport layer delivers the transmitted data to a specific process running on an Internet host. The Application layer supports the programming interface used for building a program. 2/6/2022 Integratie van Software Systemen, college 1 37
Network Resources n n n Network resources are resources available to the participants of a distributed computing community. Network resources include hardware such as computers and equipment, and software such as processes, emailboxes, files, web documents. An important class of network resources is network services such as the World Wide Web and file transfer (FTP), which are provided by specific processes running on computers. 2/6/2022 Integratie van Software Systemen, college 1 38
Identification of Network Resources One of the key challenges in distributed computing is the unique identification of resources available on the network, such as emailboxes, and web documents. Addressing an Internet Host n Addressing a process running on a host n Email Addresses n Addressing web contents: URL n 2/6/2022 Integratie van Software Systemen, college 1 39
Addressing an Internet Host 2/6/2022 Integratie van Software Systemen, college 1 40
The Internet Topology 2/6/2022 Integratie van Software Systemen, college 1 41
The Internet Topology n n The internet consists of an hierarchy of networks, interconnected via a network backbone. Each network has a unique network address. Computers, or hosts, are connected to a network. Each host has a unique ID within its network. Each process running on a host is associated with zero or more ports. A port is a logical entity for data transmission. 2/6/2022 Integratie van Software Systemen, college 1 42
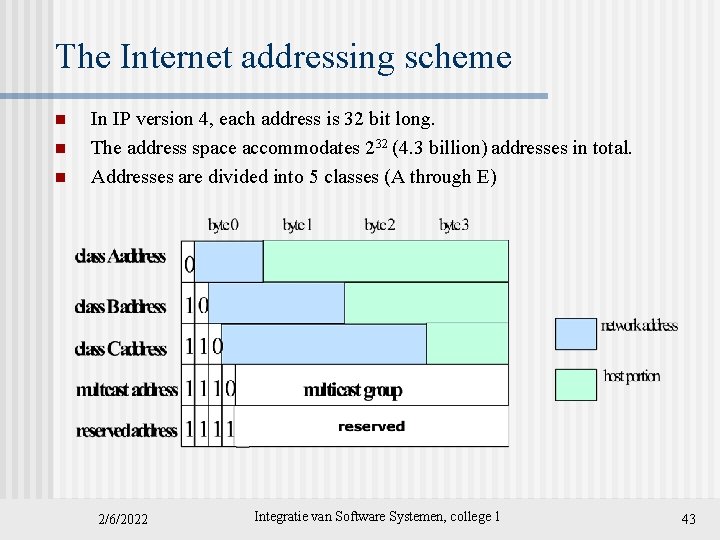
The Internet addressing scheme n n n In IP version 4, each address is 32 bit long. The address space accommodates 232 (4. 3 billion) addresses in total. Addresses are divided into 5 classes (A through E) 2/6/2022 Integratie van Software Systemen, college 1 43
The Internet Address Scheme - 3 n For human readability, Internet addresses are written in a dotted decimal notation: nnn, where each nnn group is a decimal value in the range of 0 through 255 # Internet host table (found in /etc/hosts file) 127. 0. 0. 1 localhost 129. 65. 242. 5 falcon. csc. calpoly. edu falcon loghost 129. 65. 241. 9 falcon-srv. csc. calpoly. edu falcon-srv 129. 65. 242. 4 hornet. csc. calpoly. edu hornet 129. 65. 241. 8 hornet-srv. csc. calpoly. edu hornet-srv 129. 65. 54. 9 onion. csc. calpoly. edu onion 129. 65. 241. 3 hercules. csc. calpoly. edu hercules 2/6/2022 Integratie van Software Systemen, college 1 44
IP version 6 Addressing Scheme n n Each address is 128 -bit long. There are three types of addresses: n n n Unicast: An identifier for a single interface. Anycast: An identifier for a set of interfaces (typically belonging to different nodes). Multicast: An identifier for a set of interfaces (typically belonging to different nodes). A packet sent to a multicast address is delivered to all interfaces identified by that address. 2/6/2022 Integratie van Software Systemen, college 1 45
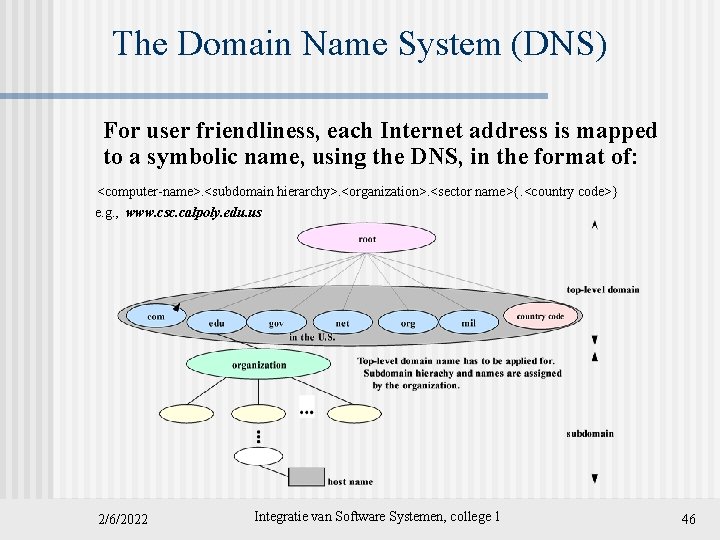
The Domain Name System (DNS) For user friendliness, each Internet address is mapped to a symbolic name, using the DNS, in the format of: <computer-name>. <subdomain hierarchy>. <organization>. <sector name>{. <country code>} e. g. , www. csc. calpoly. edu. us 2/6/2022 Integratie van Software Systemen, college 1 46
The Domain Name System n n n For network applications, a domain name must be mapped to its corresponding Internet address. Processes known as domain name system servers provide the mapping service, based on a distributed database of the mapping scheme. The mapping service is offered by thousands of DNS servers on the Internet, each responsible for a portion of the name space, called a zone. The servers that have access to the DNS information (zone file) for a zone is said to have authority for that zone. 2/6/2022 Integratie van Software Systemen, college 1 47
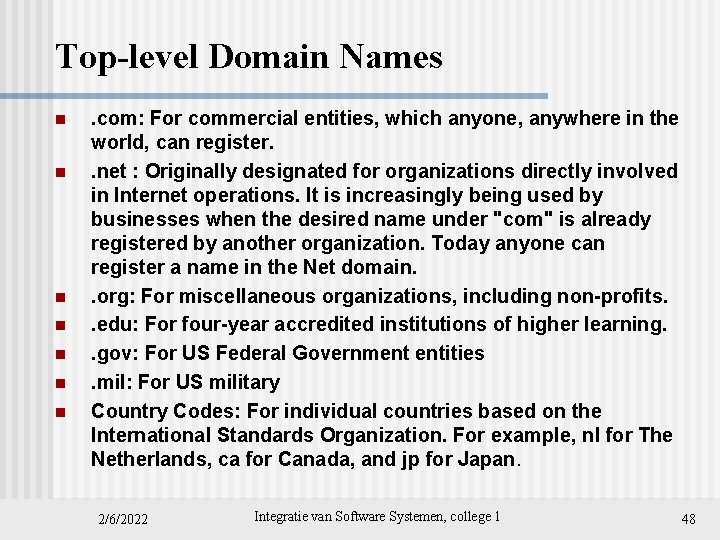
Top-level Domain Names n n n n . com: For commercial entities, which anyone, anywhere in the world, can register. . net : Originally designated for organizations directly involved in Internet operations. It is increasingly being used by businesses when the desired name under "com" is already registered by another organization. Today anyone can register a name in the Net domain. . org: For miscellaneous organizations, including non-profits. . edu: For four-year accredited institutions of higher learning. . gov: For US Federal Government entities. mil: For US military Country Codes: For individual countries based on the International Standards Organization. For example, nl for The Netherlands, ca for Canada, and jp for Japan. 2/6/2022 Integratie van Software Systemen, college 1 48
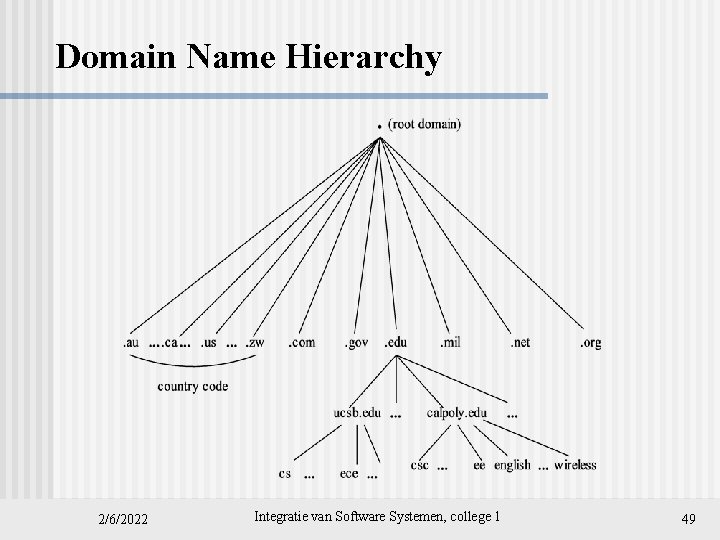
Domain Name Hierarchy 2/6/2022 Integratie van Software Systemen, college 1 49
Name lookup and resolution n If a domain name is used to address a host, its corresponding IP address must be obtained for the lower-layer network software. The mapping, or name resolution, must be maintained in some registry. For runtime name resolution, a network service is needed; a protocol must be defined for the naming scheme and for the service. Examples: The DNS service supports the DNS; the Java RMI registry supports RMI object lookup; JNDI is a network service lookup protocol. 2/6/2022 Integratie van Software Systemen, college 1 50
Addressing a process running on a host 2/6/2022 Integratie van Software Systemen, college 1 51
Logical Ports 2/6/2022 Integratie van Software Systemen, college 1 52
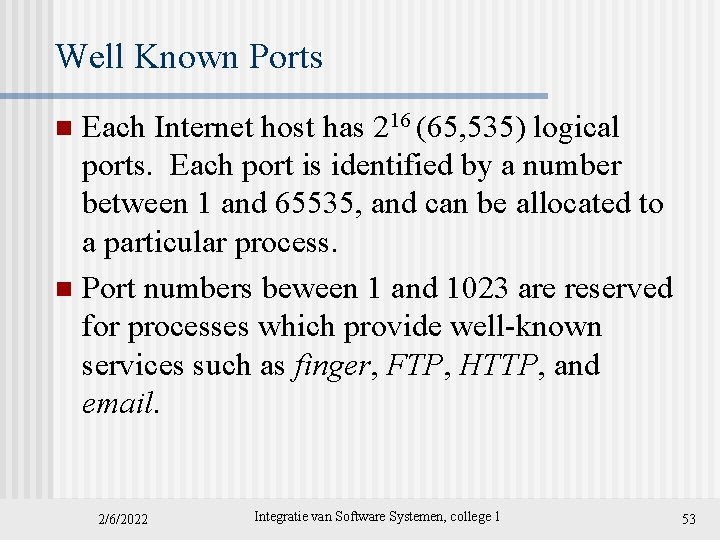
Well Known Ports Each Internet host has 216 (65, 535) logical ports. Each port is identified by a number between 1 and 65535, and can be allocated to a particular process. n Port numbers beween 1 and 1023 are reserved for processes which provide well-known services such as finger, FTP, HTTP, and email. n 2/6/2022 Integratie van Software Systemen, college 1 53
Well-known ports 2/6/2022 Integratie van Software Systemen, college 1 54
Choosing a port to run your program For a programming exercise: when a port is needed, choose a random number above the well known ports: 1, 024 - 65, 535. n If you are providing a network service for the community, then arrange to have a port assigned to and reserved for your service. n 2/6/2022 Integratie van Software Systemen, college 1 55
Addressing a Web Document 2/6/2022 Integratie van Software Systemen, college 1 56
The Uniform Resource Identifier (URI) n n n Resources to be shared on a network need to be uniquely identifiable. On the Internet, a URI is a character string which allows a resource to be located. There are two types of URIs: n n URL (Uniform Resource Locator) points to a specific resource at a specific location URN (Uniform Resource Name) points to a specific resource at a nonspecific location. 2/6/2022 Integratie van Software Systemen, college 1 57
![URL A URL has the format of: protocol: //host address[: port]/directory path/file name#section 2/6/2022 URL A URL has the format of: protocol: //host address[: port]/directory path/file name#section 2/6/2022](http://slidetodoc.com/presentation_image_h2/a33bbb304d8c7ffb895c23fc347210f5/image-58.jpg)
URL A URL has the format of: protocol: //host address[: port]/directory path/file name#section 2/6/2022 Integratie van Software Systemen, college 1 58
More on URL n n The path in a URL is relative to the document root of the server. Often, a user’s document root is ~/www. A URL may appear in a document in a relative form: < a href=“another. html”> and the actual URL referred to will be another. html preceded by the protocol, hostname, directory path of the document. 2/6/2022 Integratie van Software Systemen, college 1 59
n Break 2/6/2022 Integratie van Software Systemen, college 1 60
Interprocess Communications A. Process Communication Methods B. Marshalling C. Protocols 2/6/2022 Integratie van Software Systemen, college 1 61
A. Process Communication Methods - - - Operating systems provide facilities for interprocess communications (IPC), such as message queues, semaphores, and shared memory. Distributed computing systems make use of these facilities to provide application programming interface which allows IPC to be programmed at a higher level of abstraction. Distributed computing requires information to be exchanged among independent processes. 2/6/2022 Integratie van Software Systemen, college 1 62
IPC – unicast and multicast n n In distributed computing, two or more processes engage in IPC in a protocol agreed upon by the processes. A process may be a sender at some points during a protocol, a receiver at other points. When communication is from one process to a single other process, the IPC is said to be a unicast. When communication is from one process to a group of processes, the IPC is said to be a multicast, a topic that we will explore in a later chapter. 2/6/2022 Integratie van Software Systemen, college 1 63
Unicast vs. Multicast 2/6/2022 Integratie van Software Systemen, college 1 64
Interprocess Communications in Distributed Computing 2/6/2022 Integratie van Software Systemen, college 1 65
![Operations provided in an archetypal Interprocess Communications API • • Receive ( [sender], message Operations provided in an archetypal Interprocess Communications API • • Receive ( [sender], message](http://slidetodoc.com/presentation_image_h2/a33bbb304d8c7ffb895c23fc347210f5/image-66.jpg)
Operations provided in an archetypal Interprocess Communications API • • Receive ( [sender], message storage object) Connect (sender address, receiver address), for connection-oriented communication. Send ( [receiver], message) Disconnect (connection identifier), for connection-oriented communication. 2/6/2022 Integratie van Software Systemen, college 1 66
Interprocess Communication in basic HTTP 2/6/2022 Integratie van Software Systemen, college 1 67
Event Synchronization Interprocess communication requires that the two processes synchronize their operations: one side sends, then the other receives until all data has been sent and received. n Ideally, the send operation starts before the receive operation commences. n In practice, the synchronization requires system support. n 2/6/2022 Integratie van Software Systemen, college 1 68
Synchronous vs asynchronous communication n n The IPC operations may provide synchronous communication using blocking. A blocking operation issued by a process will block further processing of the process until the operation is fulfilled. Alternatively, IPC operations may be asynchronous or nonblocking. An asynchronous operation issued by a process will not block further processing of the process. Instead, the process is free to proceed with its processing, and may optionally be notified by the system when the operation is fulfilled. 2/6/2022 Integratie van Software Systemen, college 1 69
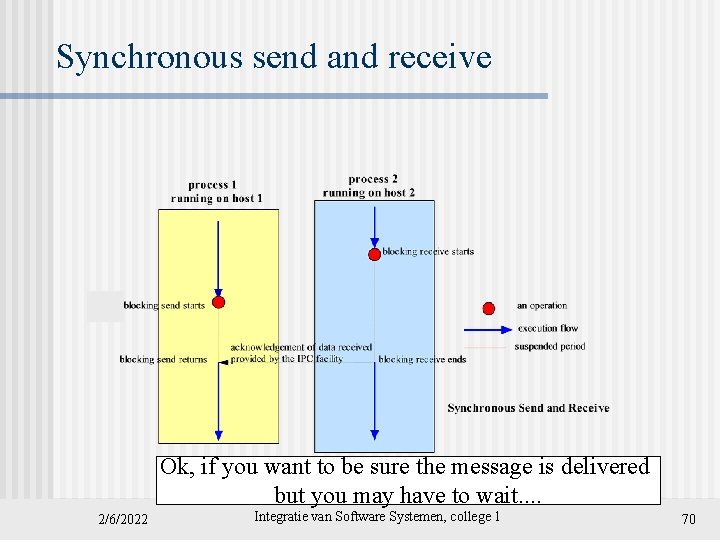
Synchronous send and receive Ok, if you want to be sure the message is delivered but you may have to wait. . 2/6/2022 Integratie van Software Systemen, college 1 70
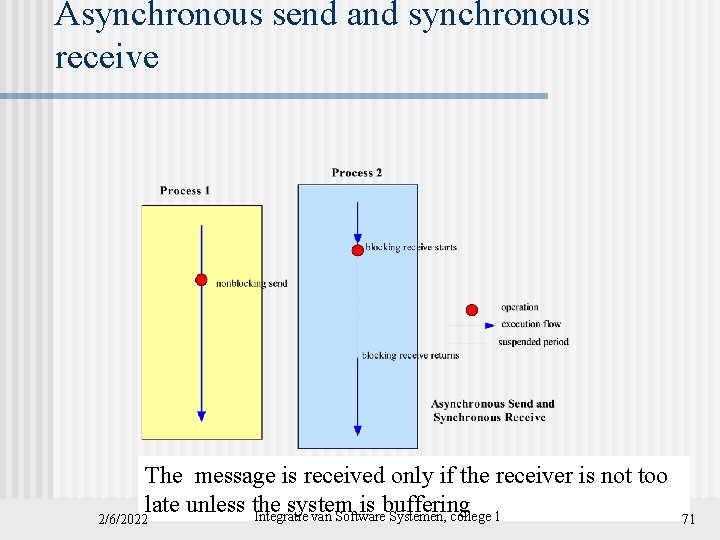
Asynchronous send and synchronous receive The message is received only if the receiver is not too late unless the system is buffering Integratie van Software Systemen, college 1 2/6/2022 71
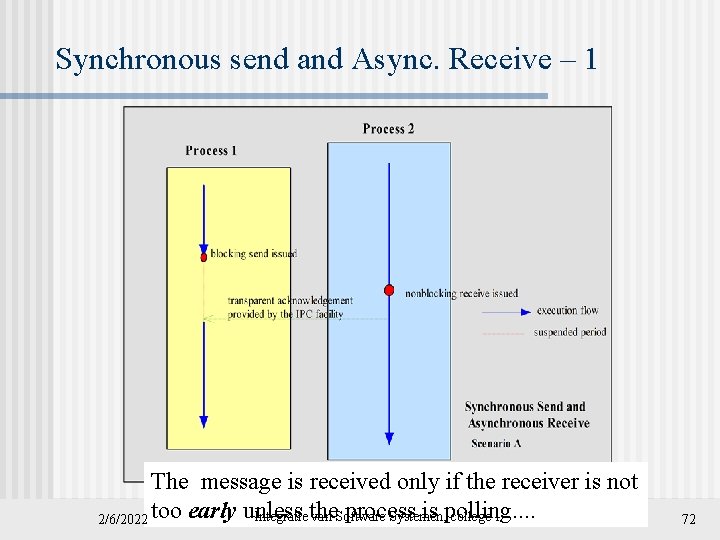
Synchronous send and Async. Receive – 1 The message is received only if the receiver is not process is polling. . Integratie the van Software Systemen, college 1 2/6/2022 too early unless 72
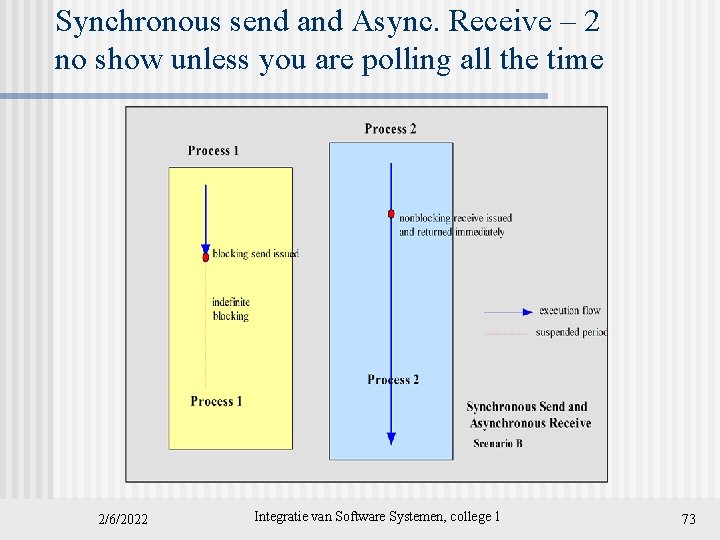
Synchronous send and Async. Receive – 2 no show unless you are polling all the time 2/6/2022 Integratie van Software Systemen, college 1 73
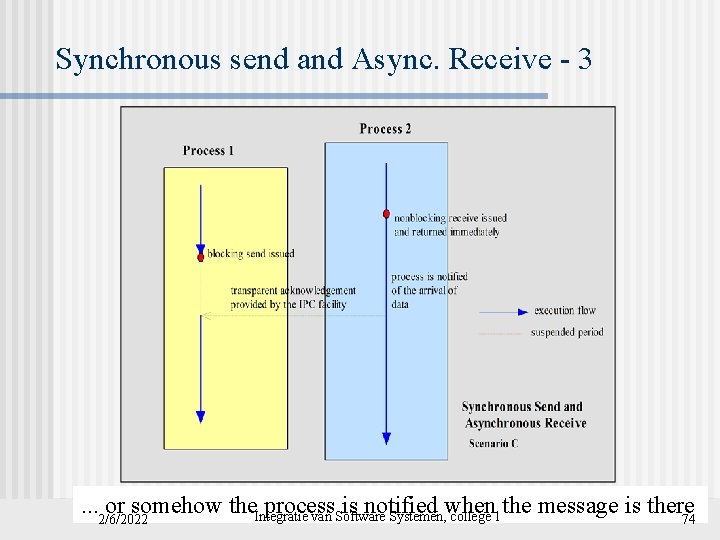
Synchronous send and Async. Receive - 3 . . . 2/6/2022 or somehow the. Integratie process is notified when the message is there van Software Systemen, college 1 74
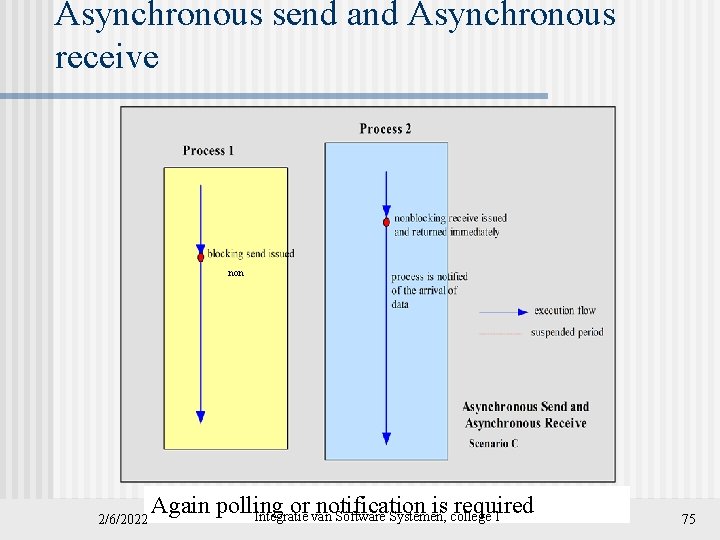
Asynchronous send and Asynchronous receive non 2/6/2022 Again polling or notification is required Integratie van Software Systemen, college 1 75
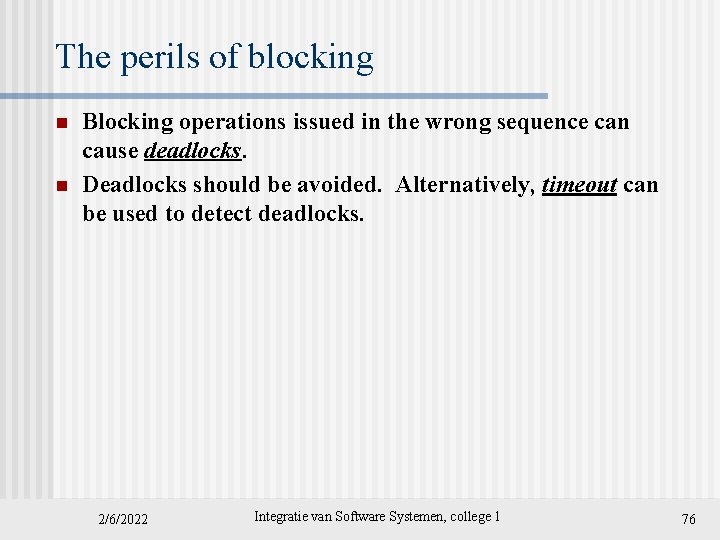
The perils of blocking n n Blocking operations issued in the wrong sequence can cause deadlocks. Deadlocks should be avoided. Alternatively, timeout can be used to detect deadlocks. 2/6/2022 Integratie van Software Systemen, college 1 76
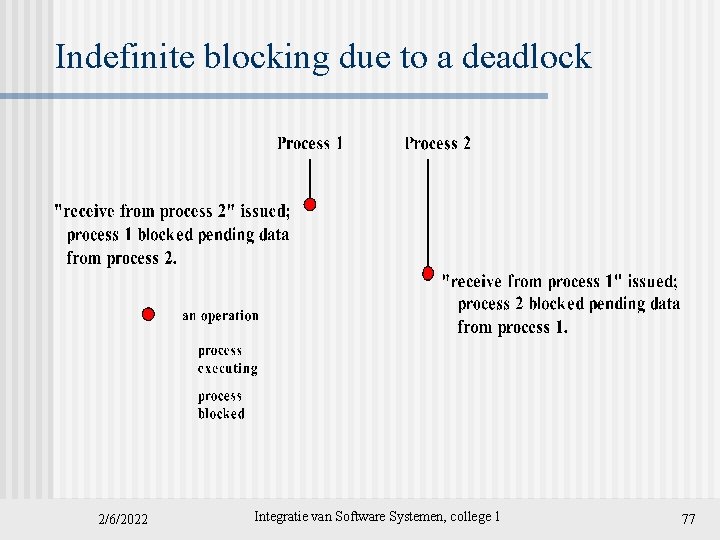
Indefinite blocking due to a deadlock 2/6/2022 Integratie van Software Systemen, college 1 77
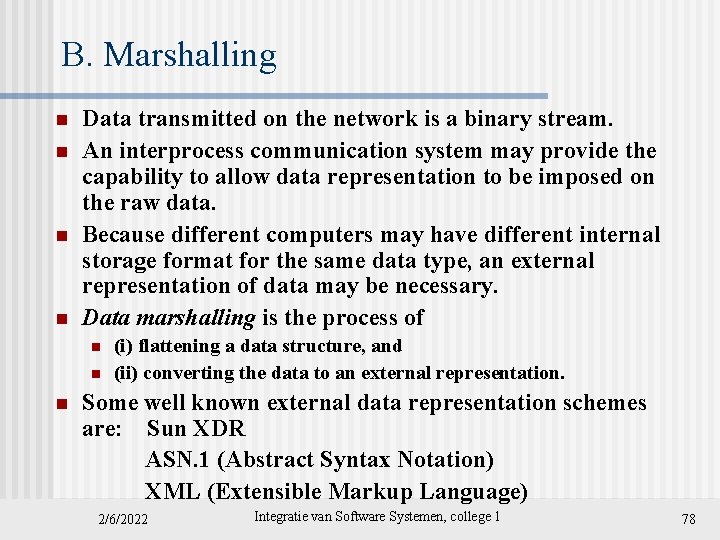
B. Marshalling n n Data transmitted on the network is a binary stream. An interprocess communication system may provide the capability to allow data representation to be imposed on the raw data. Because different computers may have different internal storage format for the same data type, an external representation of data may be necessary. Data marshalling is the process of n n n (i) flattening a data structure, and (ii) converting the data to an external representation. Some well known external data representation schemes are: Sun XDR ASN. 1 (Abstract Syntax Notation) XML (Extensible Markup Language) 2/6/2022 Integratie van Software Systemen, college 1 78
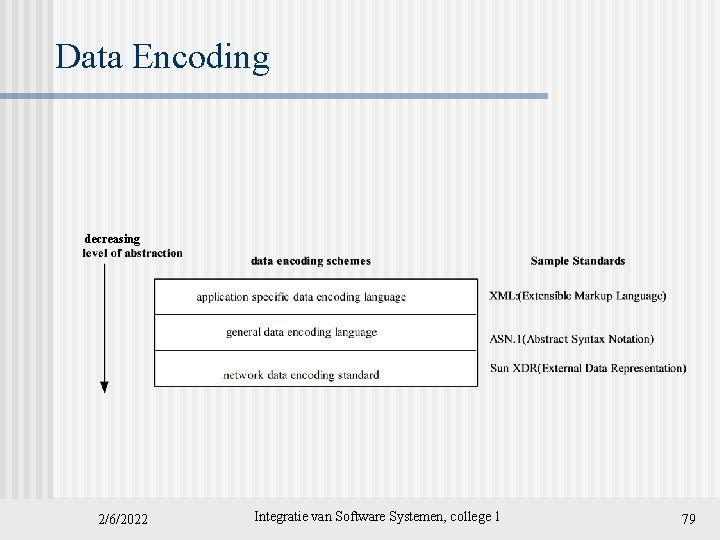
Data Encoding decreasing 2/6/2022 Integratie van Software Systemen, college 1 79
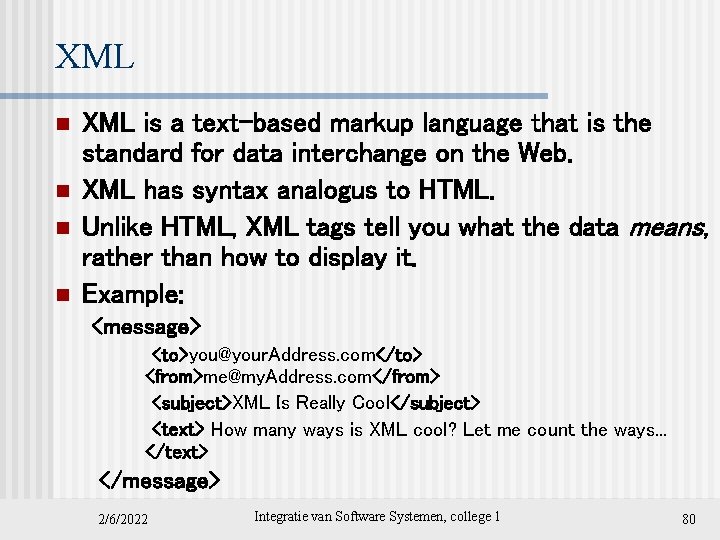
XML n n XML is a text-based markup language that is the standard for data interchange on the Web. XML has syntax analogus to HTML. Unlike HTML, XML tags tell you what the data means, rather than how to display it. Example: <message> <to>you@your. Address. com</to> <from>me@my. Address. com</from> <subject>XML Is Really Cool</subject> <text> How many ways is XML cool? Let me count the ways. . . </text> </message> 2/6/2022 Integratie van Software Systemen, college 1 80
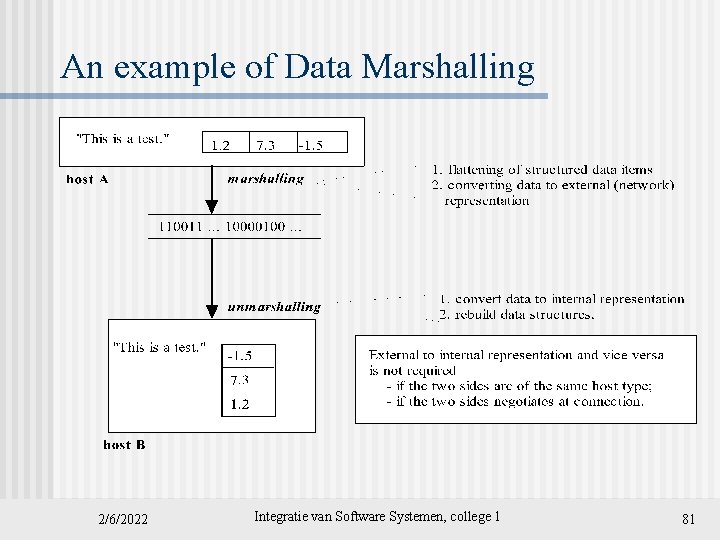
An example of Data Marshalling 2/6/2022 Integratie van Software Systemen, college 1 81
C. Protocols n n n Data marshalling is at its simplest when the data exchanged is a stream of characters, or text. Exchanging data in text has the additional advantage that the data can be easily parsed in a program and displayed for human perusal. Hence it is a popular practice for protocols to exchange requests and responses in the form of character-strings. Such protocols are said to be text-based. Many popular network protocols, including FTP (File Transfer Protocol), HTTP, and SMTP (Simple Mail Transfer Protocol), are text-based. 2/6/2022 Integratie van Software Systemen, college 1 82
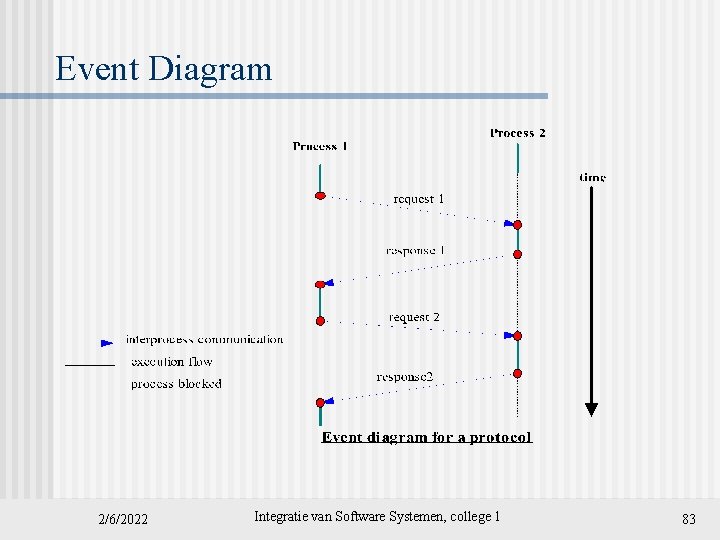
Event Diagram 2/6/2022 Integratie van Software Systemen, college 1 83
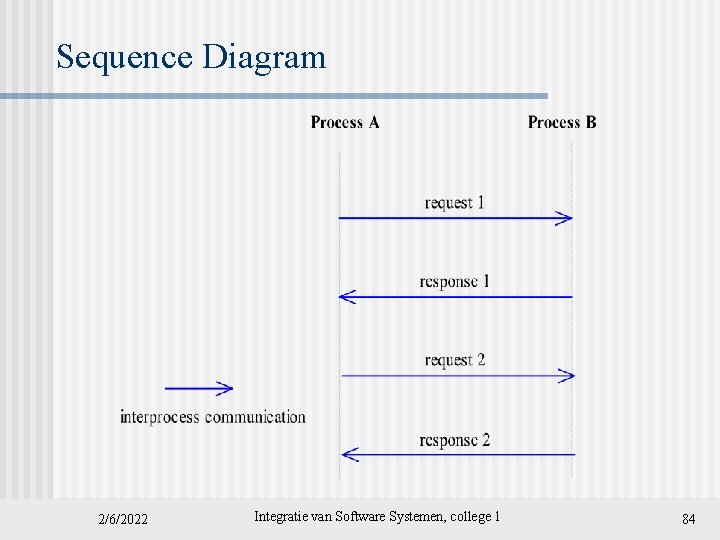
Sequence Diagram 2/6/2022 Integratie van Software Systemen, college 1 84
Protocol n n In a distributed application, two processes perform interprocess communication in a mutually agreed upon protocol. The specification of a protocol should include i. the sequence of data exchange, which can be described using an event diagram. ii. the specification of the format of the data exchanged at each step. 2/6/2022 Integratie van Software Systemen, college 1 85
HTTP: A sample protocol The Hyper. Text Transfer Protocol is a protocol for a process (the browser) to obtain a document from a web server process. n It is a request/response protocol: a browser sends a request to a web server process, which replies with a response. n 2/6/2022 Integratie van Software Systemen, college 1 86
The Basic HTTP protocol 2/6/2022 Integratie van Software Systemen, college 1 87
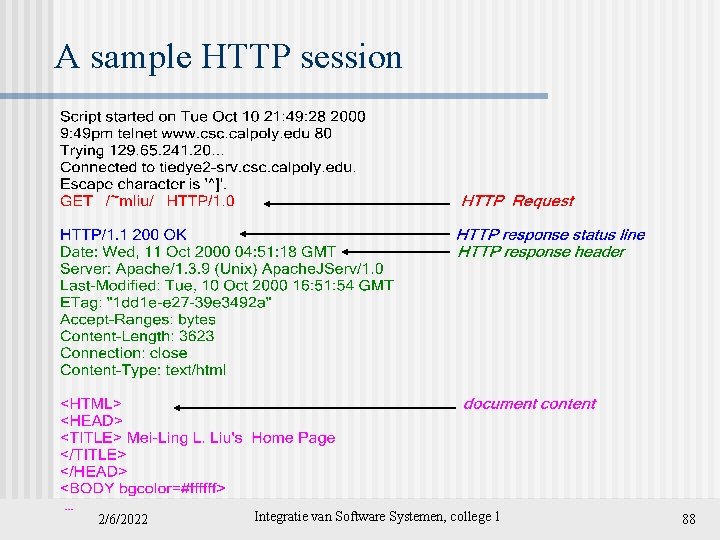
A sample HTTP session 2/6/2022 Integratie van Software Systemen, college 1 88
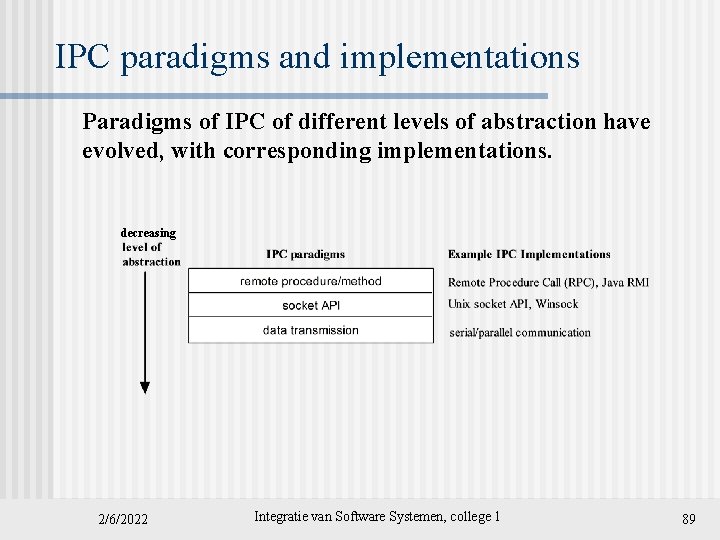
IPC paradigms and implementations Paradigms of IPC of different levels of abstraction have evolved, with corresponding implementations. decreasing 2/6/2022 Integratie van Software Systemen, college 1 89
Evolution of IPC paradigms n n n n Client-server: Socket API, remote method invocation Distributed objects Object broker: CORBA Network service: Jini Object space: Java. Spaces Mobile agents Message oriented middleware (MOM): Java Message Service Collaborative applications 2/6/2022 Integratie van Software Systemen, college 1 90
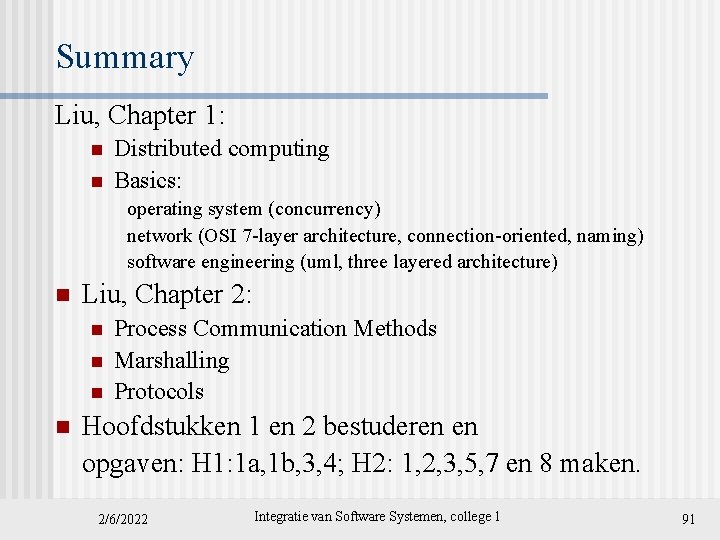
Summary Liu, Chapter 1: n n Distributed computing Basics: operating system (concurrency) network (OSI 7 -layer architecture, connection-oriented, naming) software engineering (uml, three layered architecture) n Liu, Chapter 2: n n Process Communication Methods Marshalling Protocols Hoofdstukken 1 en 2 bestuderen en opgaven: H 1: 1 a, 1 b, 3, 4; H 2: 1, 2, 3, 5, 7 en 8 maken. 2/6/2022 Integratie van Software Systemen, college 1 91
- Slides: 91