Welcome Participants Risk Assessment in eGovernance Projects December
Welcome Participants Risk Assessment in e-Governance Projects December 18, 2019 Dr. CHARRU MALHOTRA Ph. D. (IIT-D), MCA, DCA, MCSD Associate Professor (e-Governance and ICT) Indian Institute of Public Administration NEW DELHI (1) charrumalhotra. iipa@gov. in
About the Speaker IT Consultancies with International agencies WTO, WCO, GENEVA (2018), UNCTAD (United Nations Conference on Trade and Development), GENEVA ( 2018) The Swiss Embassy-India ( 2017) The World Bank (2000 – till Now) The Economist Intelligence Unit , HK-2017) IIMD- International Institute for Management Development (Lausanne, Switzerland) (2016) ADB - Asian Development Bank (2014) Panthéon Sorbonne, PARIS (2016, 2014) Wollongong University, AUSTRALIA ( 2011) The Winrock International (1999) Generated Almost 80. 5 millions for IIPA in last 5 years Guided 20 Mphils/Ph. D National Agencies Central Universities - JNU, DU, BHU, IIT-D, Rajasthan University Central ministriesmeity, Do. PT, MHA, MEA, DST, CPWD, DARP&G STATE GOVTS – KARNATAKA, HARAYANA INDUSTRY ASSOCIATIONS - NASSCOM MEDIA/ Civil Society – The Lok. Sabha, DEF 28 years of IT Journey -From MIS/IT/ICT realm (MCA , MCSD ) to the ‘real world’ (IIT-Delhi) of 600 villages of India (2005 -2009) -NE (Sikkim, Shillong, Mizoram) -South (TN, Kerala, K’tka) -North (Punjab, Haryana, Rajasthan) -Centre (MP, 36 garh, UP) - 30 Papers/ chapters/ articles - 6 handbooks - 5 reports - Winner of several best awards
About Today’s Session First Part i) Risk Factors of e-Governance • • What are Risks What is e-Governance Why Risk Assessment of e-Gov so Unique • • • ICTs ( Present & Emerging) Governance ( Govt, Gov, GG , SDGs) Nature/ Scale of Projects The Indian Context …Contd.
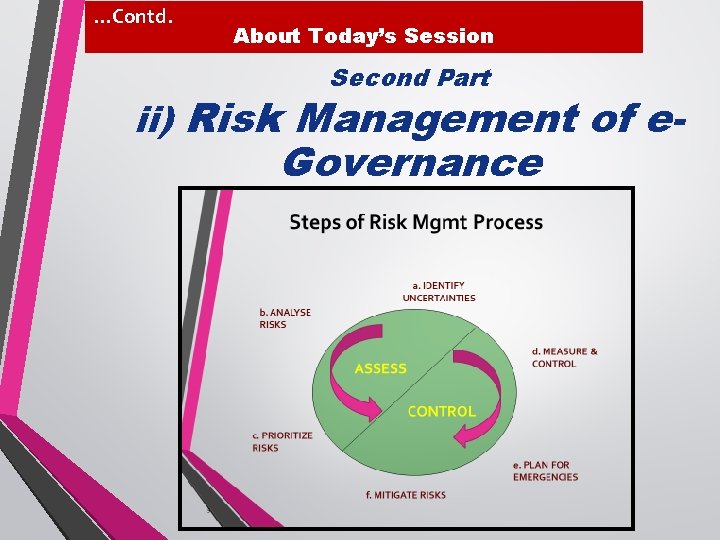
…Contd. About Today’s Session Second Part ii) Risk Management of e- Governance

About Today’s Session First Part i) Risk Factors of e-Governance
What are RISKS • DUE TO UNCERTAIN FACTORS----probabilistic events /conditions that MAY occur • • could have harmful or negative effect project’s cost , schedule (unnecessary delays), or quality. • Risks # Defects • Risks # Errors • Risks # Users’ Repeat requests for improvement/ Requirements-changes
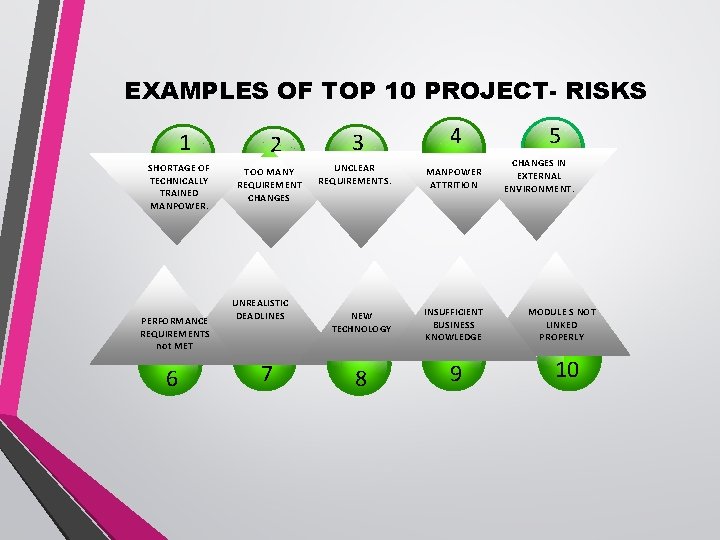
EXAMPLES OF TOP 10 PROJECT- RISKS 1 SHORTAGE OF TECHNICALLY TRAINED MANPOWER. PERFORMANCE REQUIREMENTS not MET 6 2 TOO MANY REQUIREMENT CHANGES UNREALISTIC DEADLINES 7 3 4 UNCLEAR REQUIREMENTS. MANPOWER ATTRITION NEW TECHNOLOGY INSUFFICIENT BUSINESS KNOWLEDGE 8 9 5 CHANGES IN EXTERNAL ENVIRONMENT. MODULE S NOT LINKED PROPERLY 10
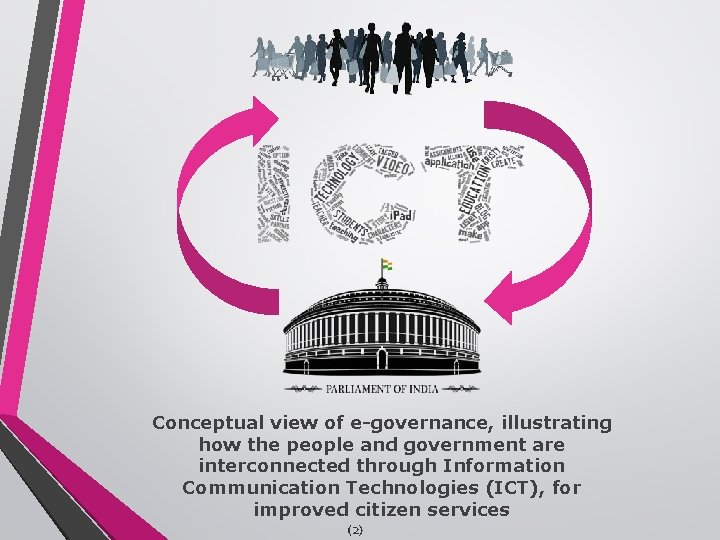
Conceptual view of e-governance, illustrating how the people and government are interconnected through Information Communication Technologies (ICT), for improved citizen services (2)

e. Governance = e Use of ICTs for Delivery of + Governance Public Services , Public Information & related Public Products e= to the Citizens/ Residents!!! ICTs
Why ? ? ? Risk Analysis of e-Gov so Different/COMPLICATED/UNIQUE A GOVERNANCE, IT , NATURE …
Citizens’ Expectations of Governance Health Safaai (Sanitation) Governance ? ? Roti (Food) Kapda (Clothing) Makaan (Shelter) Security Information Education Agriculture Employment Livelihood S a f e t y

2 6 OUR GOALS….
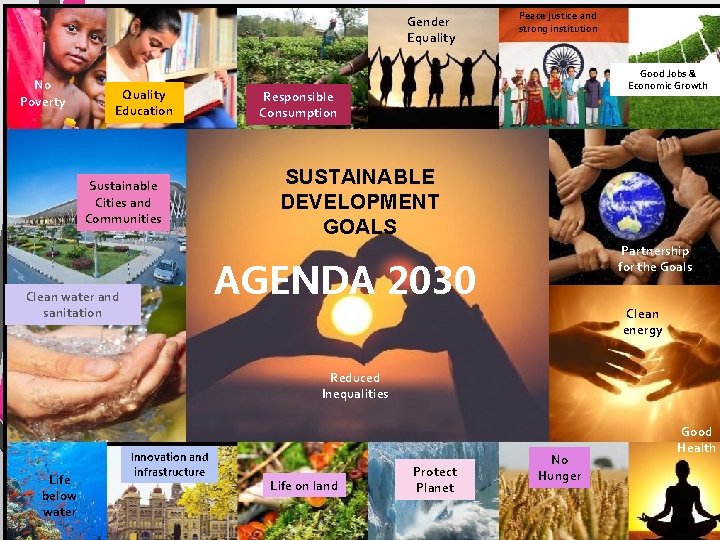
Gender Equality No Poverty Quality Education Sustainable Cities and Communities Peace justice and strong institution Good Jobs & Economic Growth Responsible Consumption SUSTAINABLE DEVELOPMENT GOALS Partnership for the Goals AGENDA 2030 Clean water and sanitation Clean energy Reduced Inequalities Life below water Innovation and infrastructure Life on land Protect Planet No Hunger Good Health
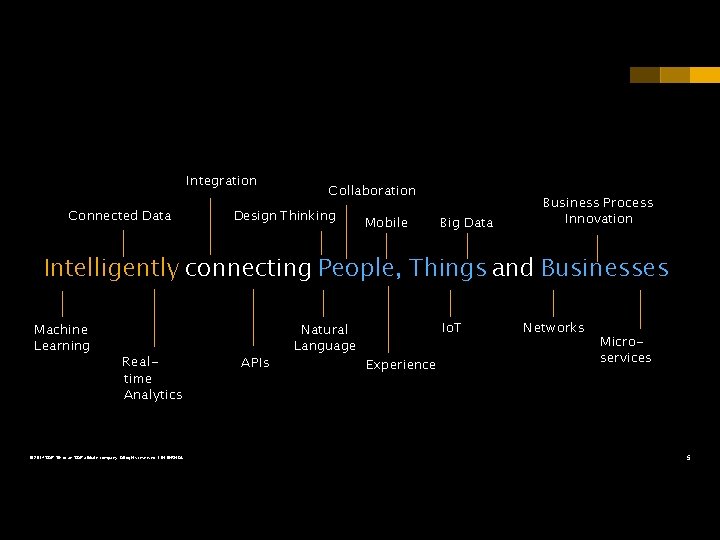
Integration Connected Data Collaboration Design Thinking Mobile Big Data Business Process Innovation Intelligently connecting People, Things and Businesses Machine Learning Realtime Analytics © 2017 SAP SE or an SAP affiliate company. All rights reserved. ǀ INTERNAL APIs Natural Language Io. T Experience Networks Microservices 5
The New Norm- Technology at our fingertips – Web Portals, e-Forums, e-News Letter, E-mail – TV, Radio, Automated calls, SMS – Social Media • Facebook, Twitter, Whatsup, 15

Our Future is already our Past!!! OUR PRESENT A …. SYSTEMS THINKING Where we are in terms of …… Our Future is already our Past!!! • • • ICTs Indian Grassroots Reality Govt to e-Governance ( Railways till Digital India) Our Future is already our Past!!! Smart-City to Smart-Villages to Smart Republic Related Cyber. Security Ecosystem : Existing Provisions & Challenges
Dreams or Reality : 1985 -Now Use of Al and Big Data Algorithms to detect Anomaly in any system to predict unexpected disasters ( To. I, Sep 27, 2017) Apps, drones likely to map infrastructure projects Dipak K Dash | TNN | Dec 6, 2017, 04: 19 IST How data analytics companies can foretell Riots/ Foreign intrusions The next intrusion is likely to happen in the wee hours of the morning, around 2 am, about 11 or 12 days after a herd of cattle meanders close to the Arunanchal border…. . …(use ) social media posts, hashtags, news articles or posts by religious group. Based on these correlation metrics, we merge all the data with the intelligence data from police agencies. Robots excavators are coming to Bengaluru soon. Bruhat Bengaluru Mahanagara Palike (BBMP) – the urban local body – has plans to procure ‘robot multi-purpose excavators’ for dredging and cleaning of drains in Bengaluru. ( Sep 5, 2017)
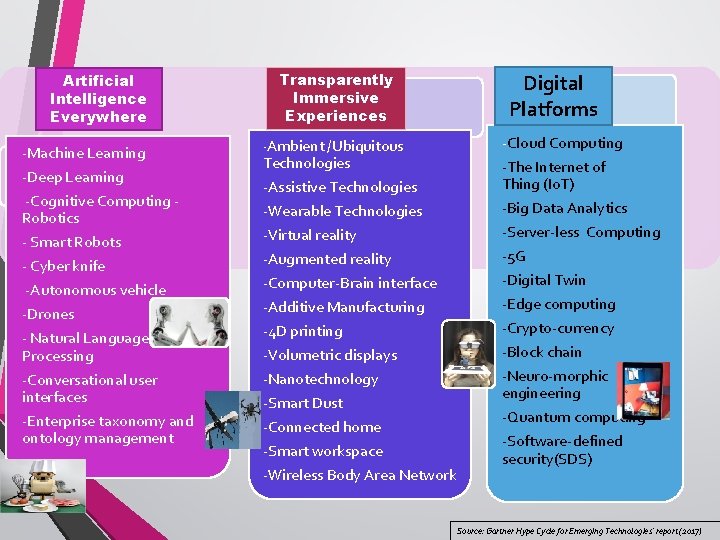
Artificial Intelligence Everywhere -Machine Learning -Deep Learning -Cognitive Computing Robotics - Smart Robots - Cyber knife -Autonomous vehicle -Drones - Natural Language Processing -Conversational user interfaces -Enterprise taxonomy and ontology management Transparently Immersive Experiences Digital Platforms -Assistive Technologies -Cloud Computing -The Internet of Thing (Io. T) -Wearable Technologies -Virtual reality -Augmented reality -Big Data Analytics -Server-less Computing -5 G -Computer-Brain interface -Additive Manufacturing -4 D printing -Volumetric displays -Nanotechnology -Smart Dust -Connected home -Smart workspace -Wireless Body Area Network -Digital Twin -Edge computing -Crypto-currency -Block chain -Neuro-morphic engineering -Quantum computing -Software-defined security(SDS) -Ambient /Ubiquitous Technologies Source: Gartner Hype Cycle for Emerging Technologies’ report (2017)
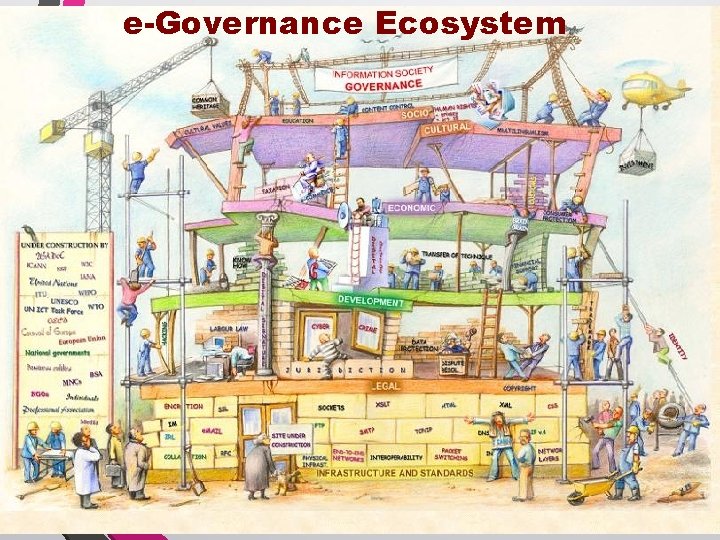
e-Governance Ecosystem
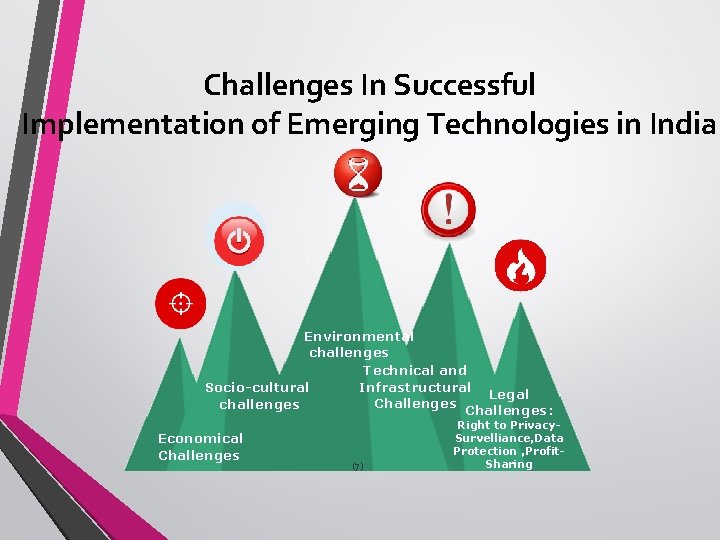
Challenges In Successful Implementation of Emerging Technologies in India Environmental challenges Technical and Infrastructural Socio-cultural Legal Challenges challenges Challenges: Economical Challenges (7) Right to Privacy. Survelliance, Data Protection , Profit. Sharing
Socio-cultural challenges (8)
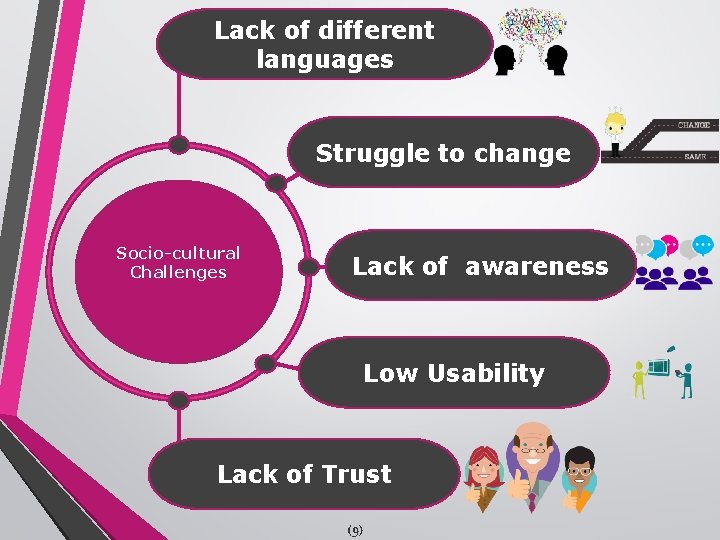
Lack of different languages Struggle to change Socio-cultural Challenges Lack of awareness Low Usability Lack of Trust (9)
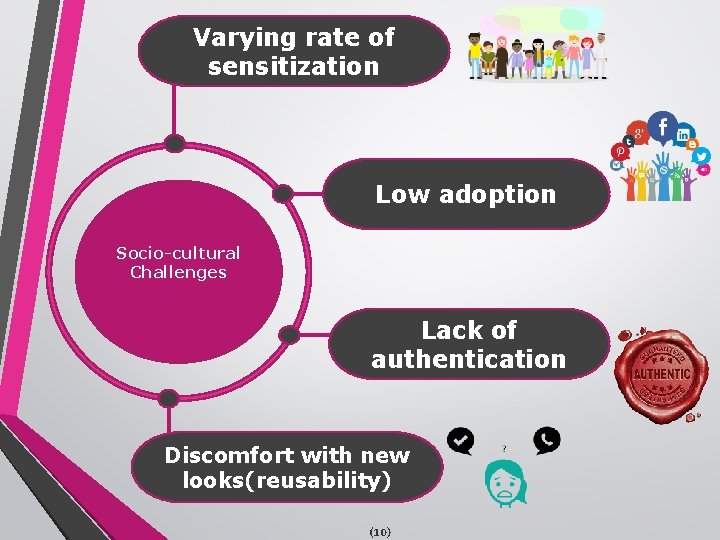
Varying rate of sensitization Low adoption Socio-cultural Challenges Lack of authentication Discomfort with new looks(reusability) (10)
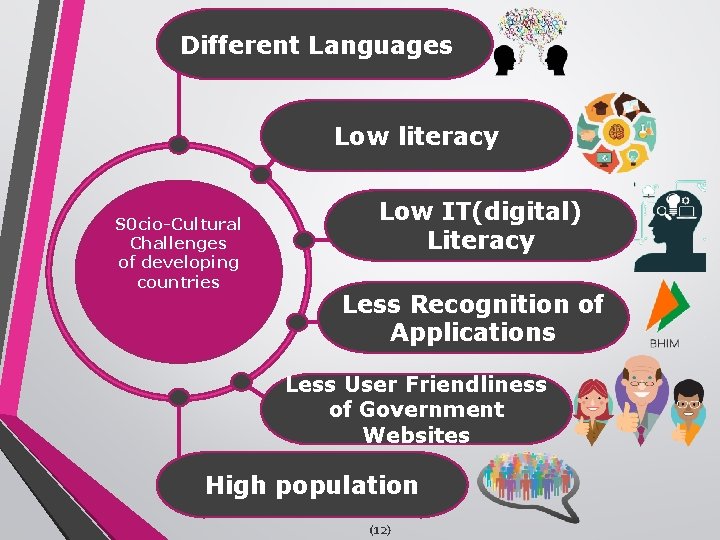
Different Languages Low literacy S 0 cio-Cultural Challenges of developing countries Low IT(digital) Literacy Less Recognition of Applications Less User Friendliness of Government Websites High population (12)
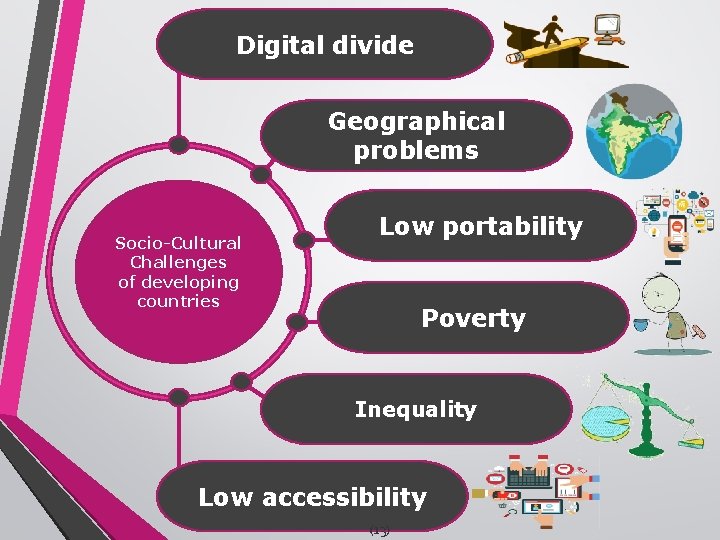
Digital divide Geographical problems Socio-Cultural Challenges of developing countries Low portability Poverty Inequality Low accessibility (13)

Environmental challenges (11)
Economical Challenges (14)
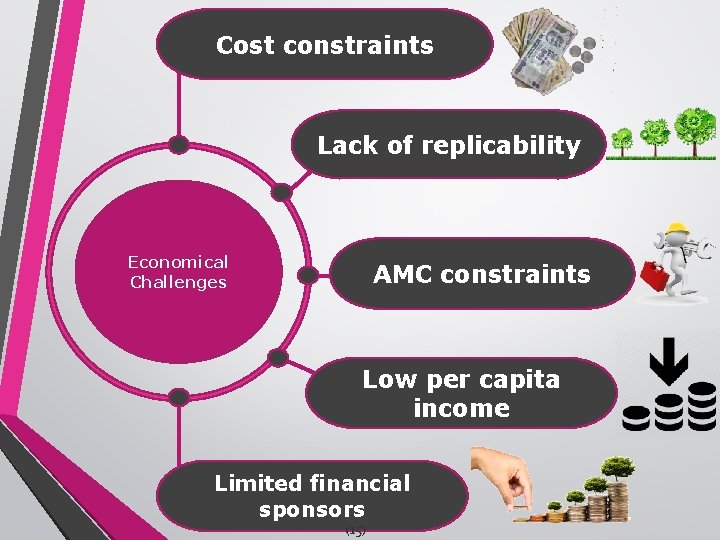
Cost constraints Lack of replicability Economical Challenges AMC constraints Low per capita income Limited financial sponsors (15)

Technical and Infrastructural Challenges (16)
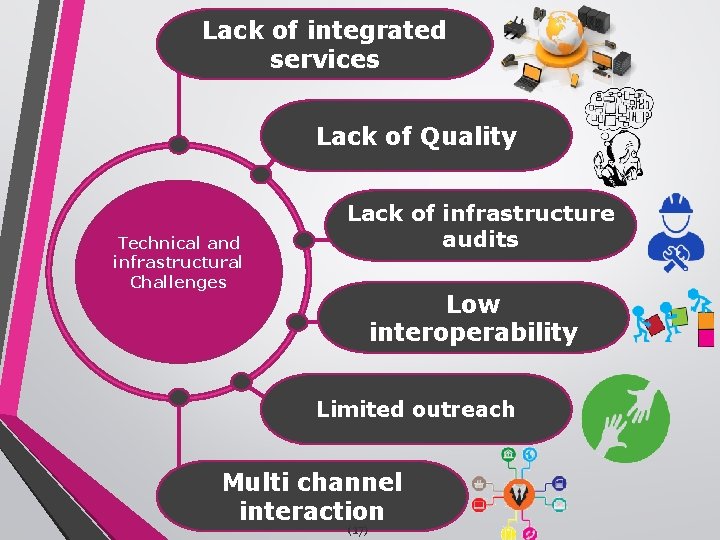
Lack of integrated services Lack of Quality Technical and infrastructural Challenges Lack of infrastructure audits Low interoperability Limited outreach Multi channel interaction (17)
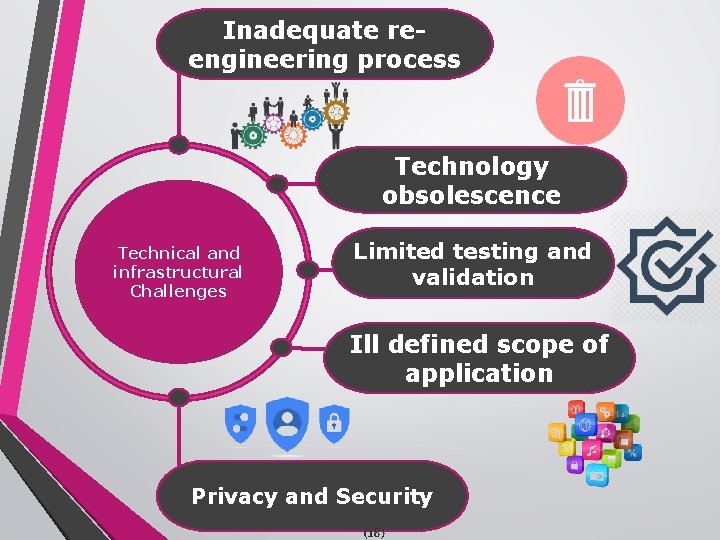
Inadequate reengineering process Technology obsolescence Technical and infrastructural Challenges Limited testing and validation Ill defined scope of application Privacy and Security (18)

Organisational and Project Management Challenges (19)
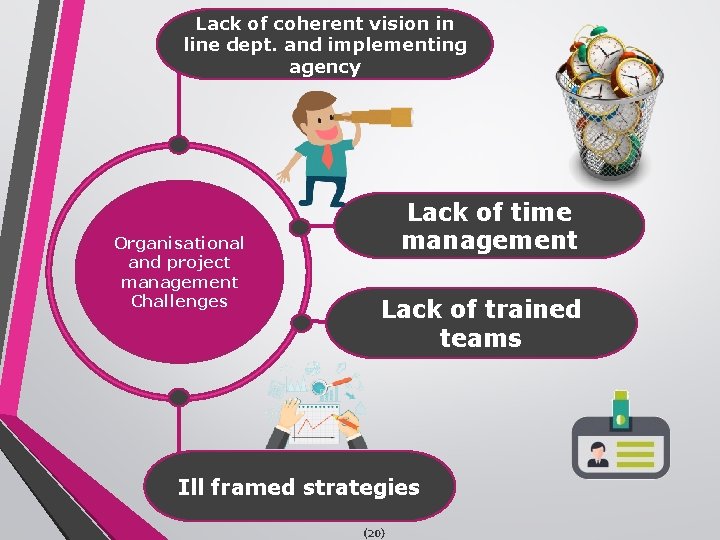
Lack of coherent vision in line dept. and implementing agency Organisational and project management Challenges Lack of time management Lack of trained teams Ill framed strategies (20)
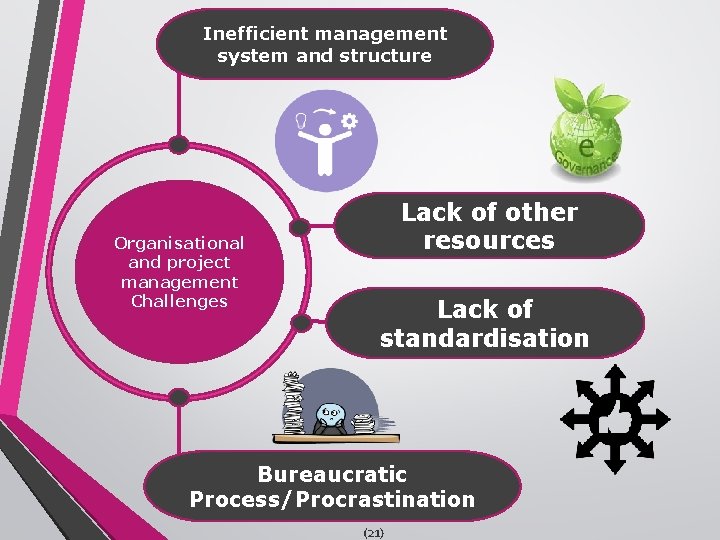
Inefficient management system and structure Organisational and project management Challenges Lack of other resources Lack of standardisation Bureaucratic Process/Procrastination (21)
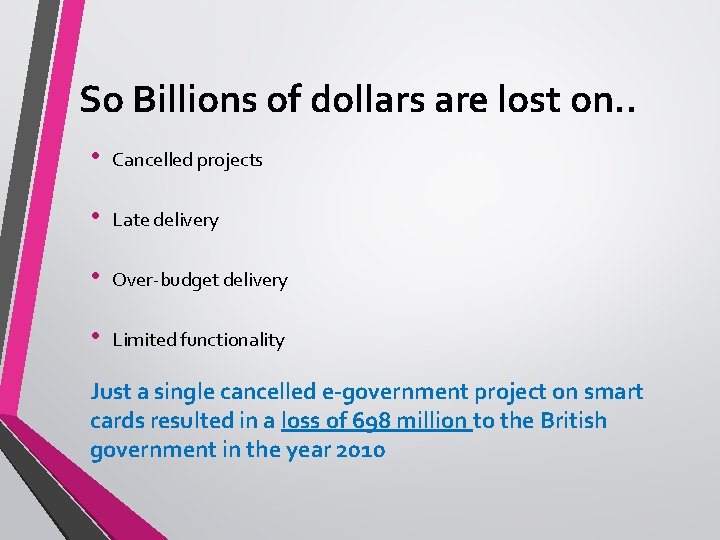
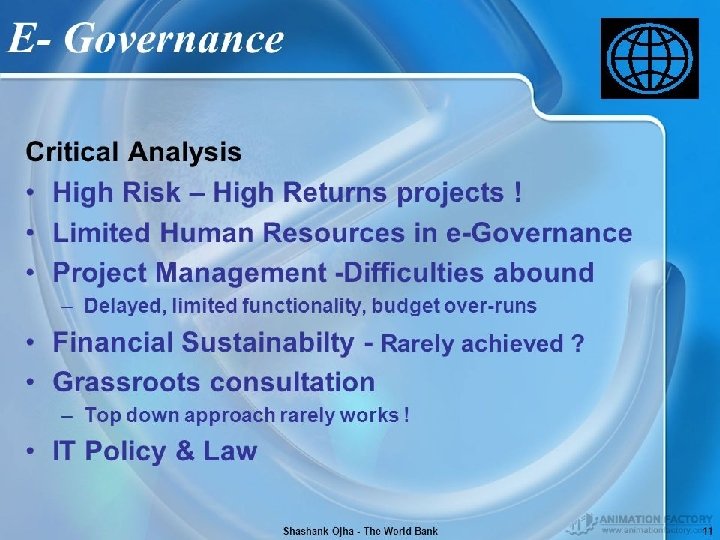
So Billions of dollars are lost on. . • Cancelled projects • Late delivery • Over-budget delivery • Limited functionality Just a single cancelled e-government project on smart cards resulted in a loss of 698 million to the British government in the year 2010
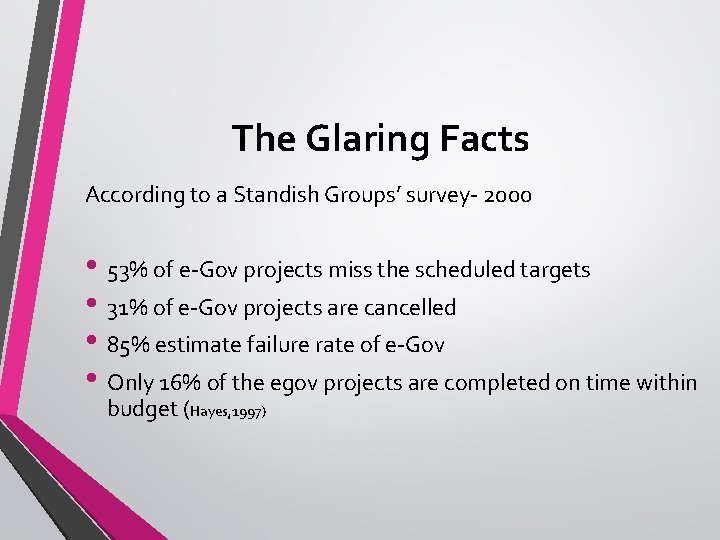
The Glaring Facts According to a Standish Groups’ survey- 2000 • 53% of e-Gov projects miss the scheduled targets • 31% of e-Gov projects are cancelled • 85% estimate failure rate of e-Gov • Only 16% of the egov projects are completed on time within budget (Hayes, 1997)
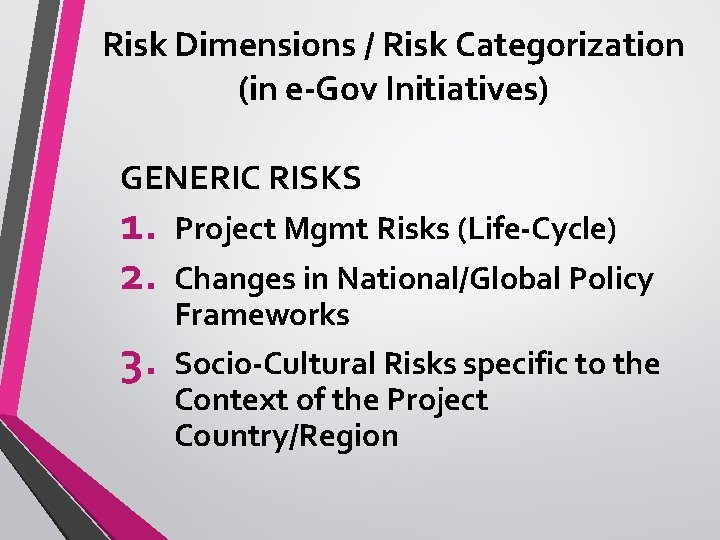
Risk Dimensions / Risk Categorization (in e-Gov Initiatives) GENERIC RISKS 1. 2. Project Mgmt Risks (Life-Cycle) 3. Socio-Cultural Risks specific to the Context of the Project Country/Region Changes in National/Global Policy Frameworks
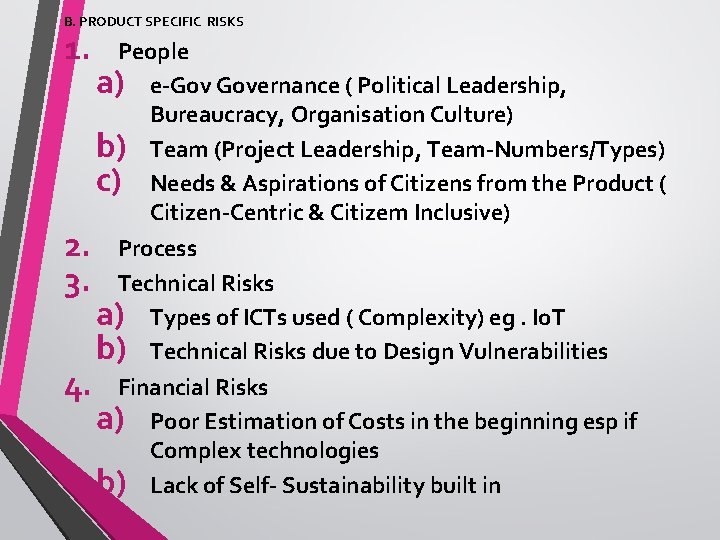
B. PRODUCT SPECIFIC RISKS 1. 2. 3. 4. People a) e-Gov Governance ( Political Leadership, Bureaucracy, Organisation Culture) b) Team (Project Leadership, Team-Numbers/Types) c) Needs & Aspirations of Citizens from the Product ( Citizen-Centric & Citizem Inclusive) Process Technical Risks a) Types of ICTs used ( Complexity) eg. Io. T b) Technical Risks due to Design Vulnerabilities Financial Risks a) Poor Estimation of Costs in the beginning esp if Complex technologies b) Lack of Self- Sustainability built in

GENERIC Risk Categorization in e. Gov Initiatives 1. Project Mgmt Risks 2. Changes in Policy F/w – Global/ National 3. Socio-Cultural Risks

PROJECT MGMT RISKS
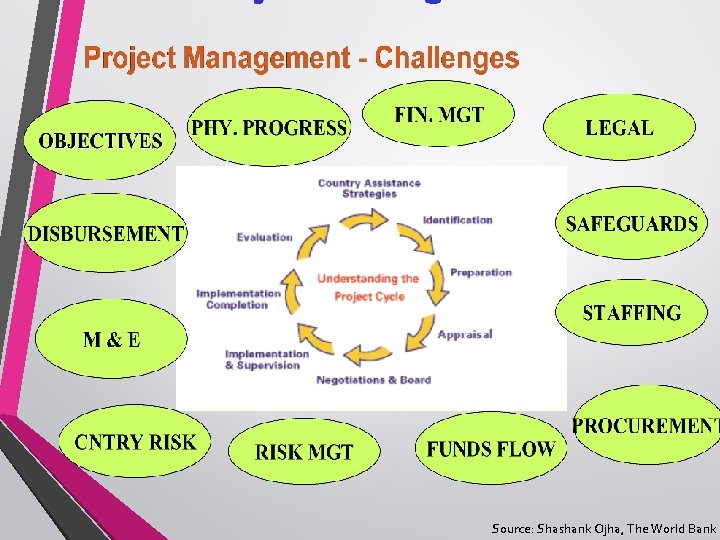
Source: Shashank Ojha, The World Bank
1. Project Planning Risks • Incorrect estimation of cost, schedule and milestones • Incorrect TELOS • Neglect of software quality assurance • Inadequate M&E • Neglect of risk assessment methodologies. • Improper Project Management Tools in use. • Wrong time scheduling for the project execution
2. HR Issues • The risks relating to change in org structure • Challenges due to changes of procedures (GPR) or may be neglecting the BPR • Disinterested leadership at political and managerial level • Too much champion led processes and not institutionalised
3. Stakeholders • Risks of resistant government employees • Stringent government policies • Fluid development team members • Neglect of needs and aspirations of citizens
Specific Issues to e-Gov • How to select and entrust a solution provider to • • • deliver any part of e-governance. To ensure that after each solution from different partners integrates seamlessly To encourage the development of replicable solutions: Avoid reinventing of wheel System Specs are tough to elicit from all Stakeholders
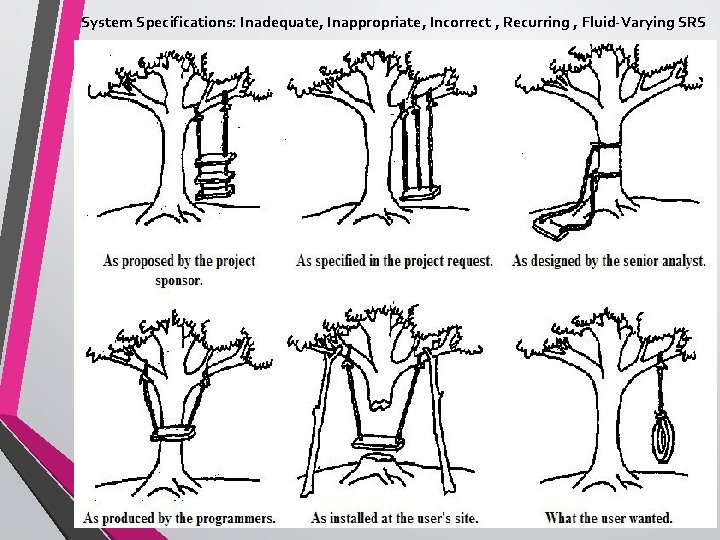
System Specifications: Inadequate, Inappropriate, Incorrect , Recurring , Fluid-Varying SRS
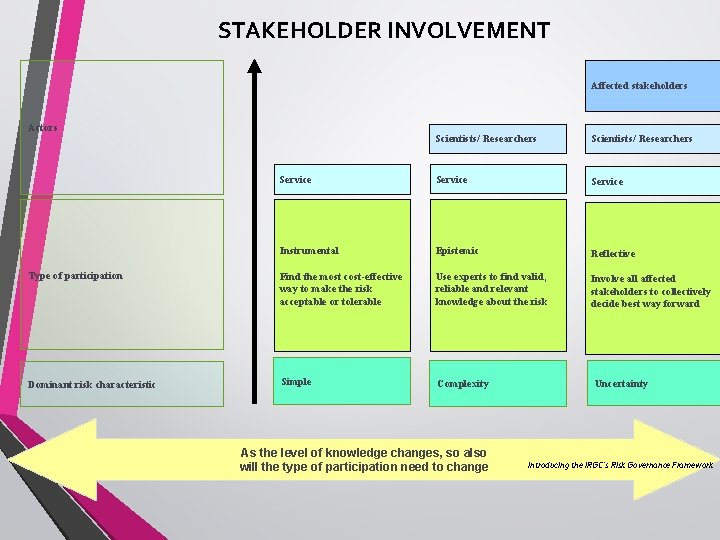
STAKEHOLDER INVOLVEMENT Affected stakeholders Actors Scientists/ Researchers Service Instrumental Epistemic Reflective Type of participation Find the most cost-effective way to make the risk acceptable or tolerable Use experts to find valid, reliable and relevant knowledge about the risk Involve all affected stakeholders to collectively decide best way forward Dominant risk characteristic Simple Complexity As the level of knowledge changes, so also will the type of participation need to change Uncertainty Introducing the IRGC’s Risk Governance Framework

TECHNICAL RISKS

1. Complex Architectural design of application s/w 2. Wrong s/w functionality 3. Poor design of software- can’t support multichannel service delivery, poor s/w engineering environment 4. Data Security challenges 5. Inappropriate selection of hardware, system software and networking technology 6. Non-accessibility and non-availability of data 7. Improper skill set of the software developers for new technology trends
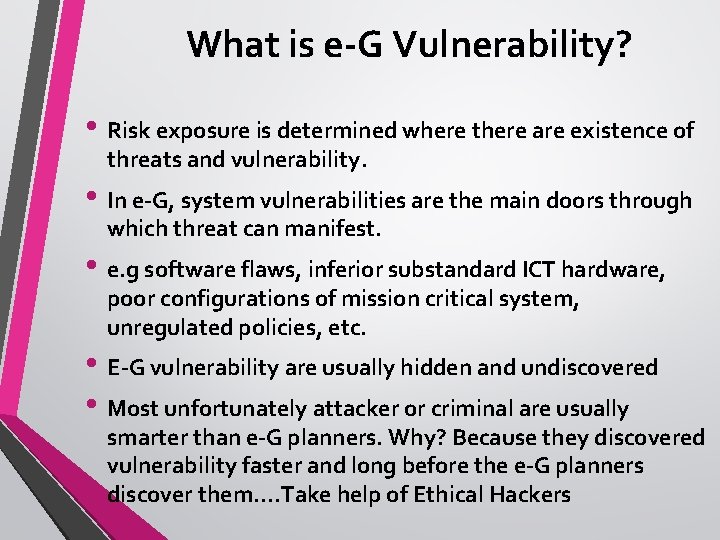
What is e-G Vulnerability? • Risk exposure is determined where there are existence of threats and vulnerability. • In e-G, system vulnerabilities are the main doors through which threat can manifest. • e. g software flaws, inferior substandard ICT hardware, poor configurations of mission critical system, unregulated policies, etc. • E-G vulnerability are usually hidden and undiscovered • Most unfortunately attacker or criminal are usually smarter than e-G planners. Why? Because they discovered vulnerability faster and long before the e-G planners discover them…. Take help of Ethical Hackers

High Risk Threats • Well-resourced, highly-motivated groups of cyber-warriors • Numerous attack vectors including email, social media, and apparent trust Why Are We Concerned About Cyber paths like those with contractor facilities Security? • Use of zero-day attacks and exploitation of weak credentials are common • Often referred to as the Advanced Persistent Threat in public media Medium Risk Threats • Criminals targeting identity and money • Varying levels of technical sophistication • Botnets and Bot Herders Low Risk Threats • Standard Internet Pollution • Threats against every user • Unsophisticated

E-Gov ORGANISATION RISKS

1. Poor management skill of Project Managers, Project Leaders and Administrators. 2. Lack of Political Commitment and Leadership 3. Lack of Bureaucratic Support 4. IPR Litigations 5. Lack of proper Contract Mgmt in PPP 6. Disinterest for timely reviews 7. No BPR 8. Lack of Stakeholder Participation – Follow ICICE Model of IAPA 2

FINANCIAL RISKS
1. Cost-benefit analysis is not properly done 2. Time/cost dependency links: Price protection risks (a rise in input costs) increase if the duration of a project is increased 3. Mismanagement of project funds 4. Exposure to changes in market prices, such as interest rates, exchange rates, and commodity prices

SOCIO-CULTURAL RISKS
1. The behavior, attitude and mindset of the stakeholders for planning, developing, 2. Lack of Ownership by Mgmt: Executing and accepting the project is a major factor of project success. 3. Behavior/Change of Political Leaders, Administrators, Vendors, Consultants, Developers, User Department and 4. Lack of Ownership by End-Beneficiary: After all the behavior of Citizens should be positive
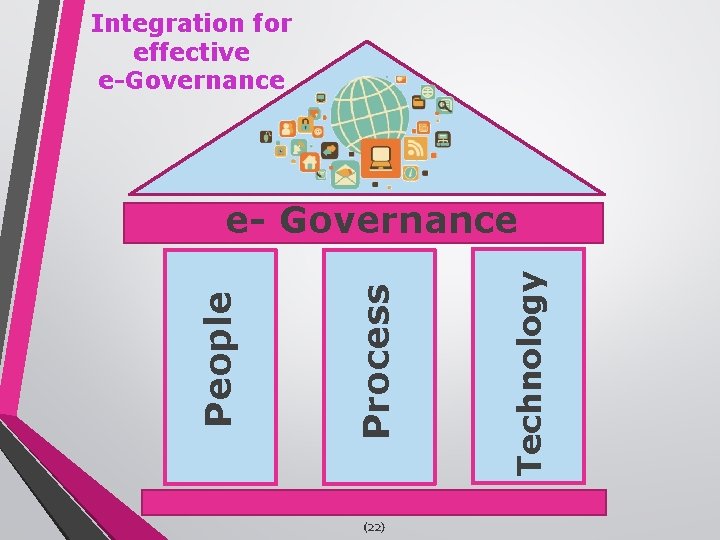
Integration for effective e-Governance (22) Technology Process People e- Governance

Solutions to e-governance
About Today’s Session Second Part ii) Risk Management of e-Governance
1. CONCEPTS OF RISKS & RISK MGMT 2. RISK ASSESSMENT 3. RISK IDENTIFICATION 4. RISK PRIORITISATION 5. RISK CONTROL • RISK MGMT PLANNING • RISK MONITORING & TRACKING Based on Infosys Case-Study of ACIC project by Mr. Pankaj
RECAP- What are RISKS are those probabilistic events or conditions that MAY occur and could have harmful or negative effect on project’s cost , schedule ( unnecessary delays), or quality. • Risks # Defects • Risks # Errors • Risks # Users’ Repeat requests for improvement/ Requirements-changes

EXAMPLES OF TOP 10 PROJECT- RISKS 4 5 1 3 2 SHORTAGE OF TECHNICALLY TRAINED MANPOWER. PERFORMANCE REQUIREMENTS not MET 6 TOO MANY REQUIREMENT CHANGES UNREALISTIC DEADLINES 7 UNCLEAR REQUIREMENTS. MANPOWER ATTRITION NEW TECHNOLOGY INSUFFICIENT BUSINESS KNOWLEDGE 8 9 CHANGES IN EXTERNAL ENVIRONMENT. MODULE S NOT LINKED PROPERLY 10
RISK MANAGEMENT-RM Aims to identify risks; prioritise; take actions to minimize their effect on the project. • When RM ? RM Cost < RM Expected Loss-Value • Why is Risk Mgmt Usually Skipped? Tough to predict risks in future; not highlighted to avoid displeasing customers; to avoid additional cost & tough to calculate risk mitigation cost; over-enthusiasm. Eg: A computer show where UPS reqd: Frequency of power failure? For how long? Generator reqd?
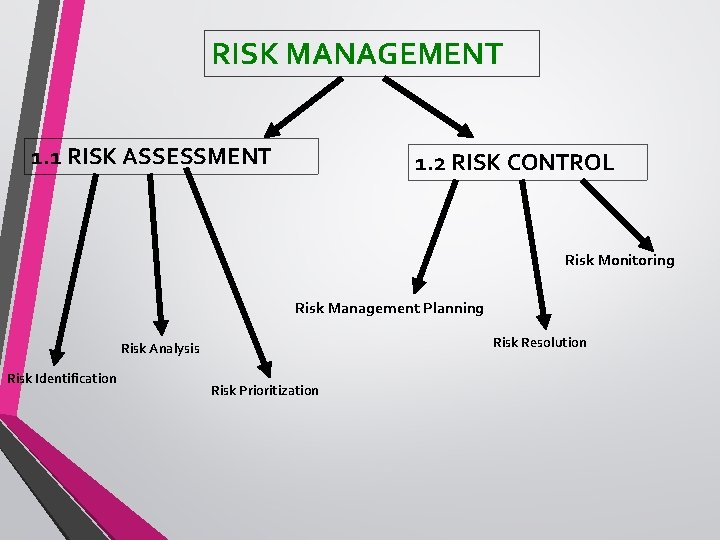
RISK MANAGEMENT 1. 1 RISK ASSESSMENT 1. 2 RISK CONTROL Risk Monitoring Risk Management Planning Risk Resolution Risk Analysis Risk Identification Risk Prioritization
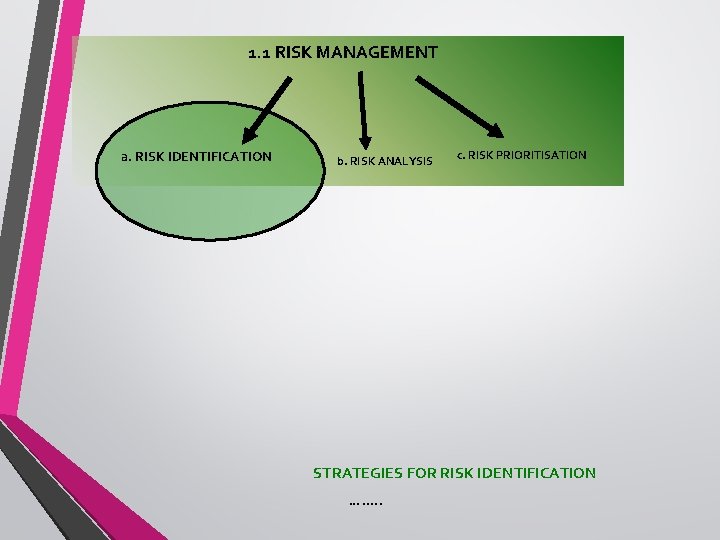
1. 1 RISK MANAGEMENT a. RISK IDENTIFICATION b. RISK ANALYSIS c. RISK PRIORITISATION STRATEGIES FOR RISK IDENTIFICATION … …. .
1. 1 RISK MANAGEMENT STRATEGIES FOR RISK IDENTIFICATION … Checklists of frequently occurring risks compiled from study of previous projects … Study process databases of previous projects of similar nature … Surveys … Brainstorming Meetings to evaluate and think about previously encountered risks … Review of Project Plans, Processes and Work Products to elicit views of all … Project managers judgment and experience
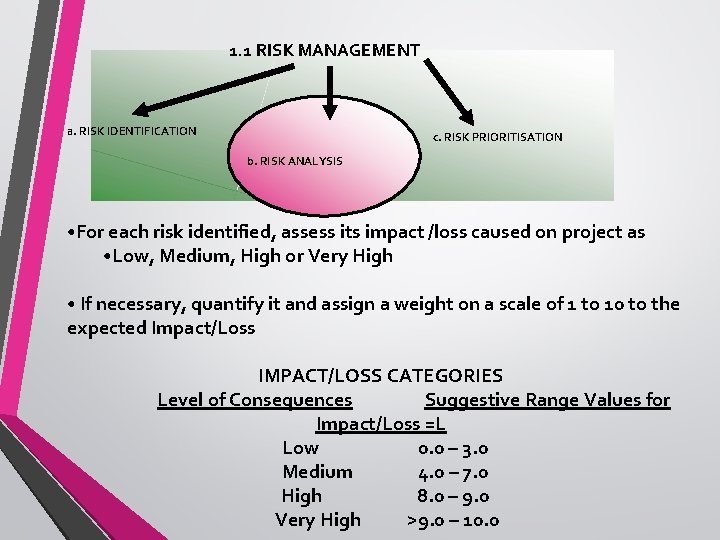
1. 1 RISK MANAGEMENT a. RISK IDENTIFICATION c. RISK PRIORITISATION b. RISK ANALYSIS • For each risk identified, assess its impact /loss caused on project as • Low, Medium, High or Very High • If necessary, quantify it and assign a weight on a scale of 1 to 10 to the expected Impact/Loss IMPACT/LOSS CATEGORIES Level of Consequences Suggestive Range Values for Impact/Loss =L Low 0. 0 – 3. 0 Medium 4. 0 – 7. 0 High 8. 0 – 9. 0 Very High >9. 0 – 10. 0
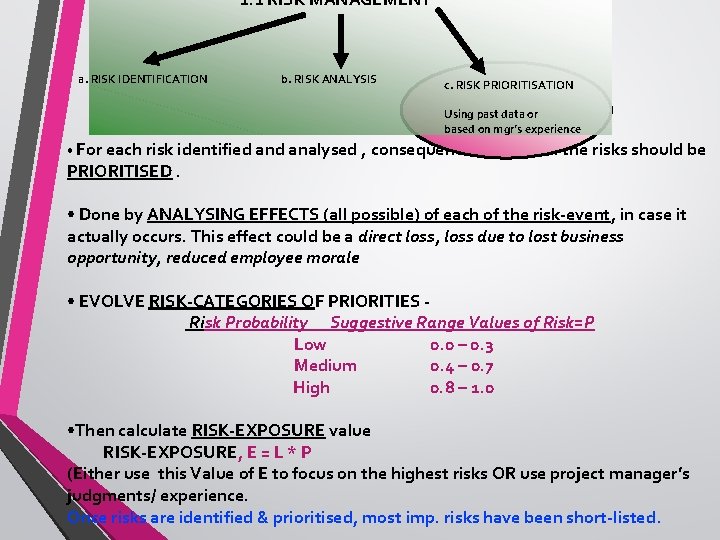
1. 1 RISK MANAGEMENT a. RISK IDENTIFICATION b. RISK ANALYSIS c. RISK PRIORITISATION Using past data or based on mgr’s experience • For each risk identified analysed , consequences of each of the risks should be PRIORITISED. • Done by ANALYSING EFFECTS (all possible) of each of the risk-event, in case it actually occurs. This effect could be a direct loss, loss due to lost business opportunity, reduced employee morale • EVOLVE RISK-CATEGORIES OF PRIORITIES Risk Probability Suggestive Range Values of Risk=P Low 0. 0 – 0. 3 Medium 0. 4 – 0. 7 High 0. 8 – 1. 0 • Then calculate RISK-EXPOSURE value RISK-EXPOSURE, E = L * P (Either use this Value of E to focus on the highest risks OR use project manager’s judgments/ experience. Once risks are identified & prioritised, most imp. risks have been short-listed.
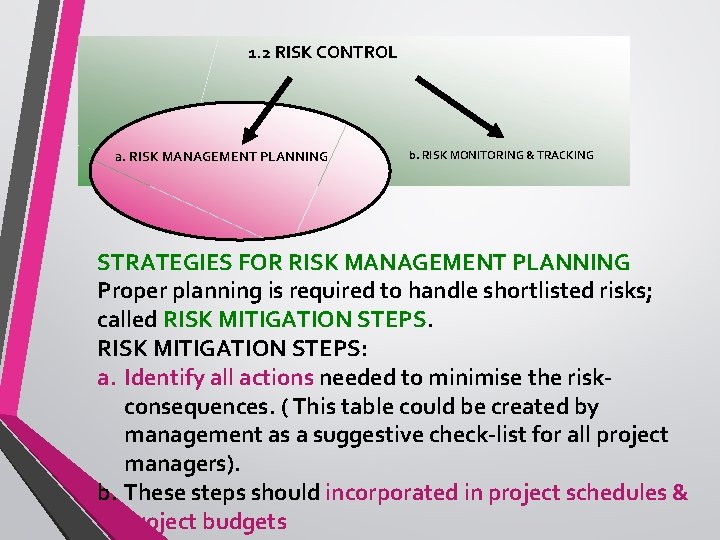
1. 2 RISK CONTROL a. RISK MANAGEMENT PLANNING b. RISK MONITORING & TRACKING STRATEGIES FOR RISK MANAGEMENT PLANNING Proper planning is required to handle shortlisted risks; called RISK MITIGATION STEPS: a. Identify all actions needed to minimise the riskconsequences. ( This table could be created by management as a suggestive check-list for all project managers). b. These steps should incorporated in project schedules & project budgets

1 SHORTAGE OF TECHNICALLY TRAINED MANPOWER. PERFORMANCE REQUIREMENTS not MET 6 TOP TEN RISKS REVISITED 4 3 2 TOO MANY REQUIREMENT CHANGES UNREALISTIC DEADLINES 7 UNCLEAR REQUIREMENTS. MANPOWER. ATTRITION NEW TECHNOLOGY INSUFFICIENT BUSINESS KNOWLEDGE 8 9 5 CHANGES IN EXTERNAL ENVIRONMENT. MODULE S NOT LINKED PROPERLY 10
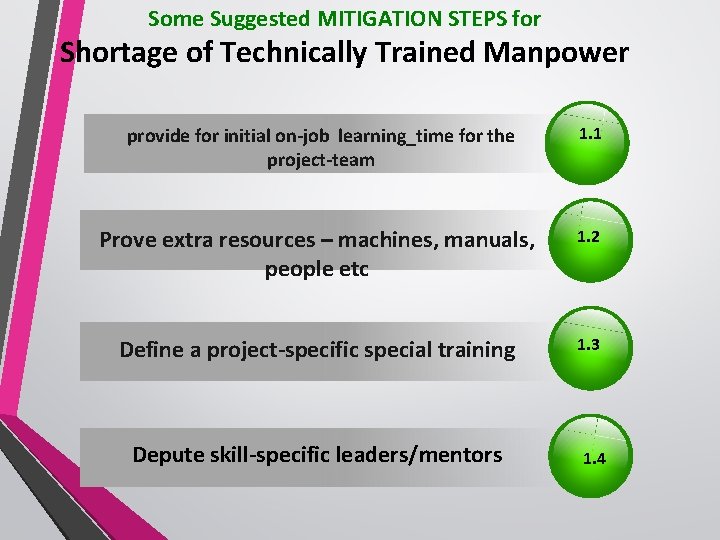
Some Suggested MITIGATION STEPS for Shortage of Technically Trained Manpower provide for initial on-job learning_time for the project-team 1. 1 Prove extra resources – machines, manuals, people etc 1. 2 Define a project-specific special training 1. 3 Depute skill-specific leaders/mentors 1. 4
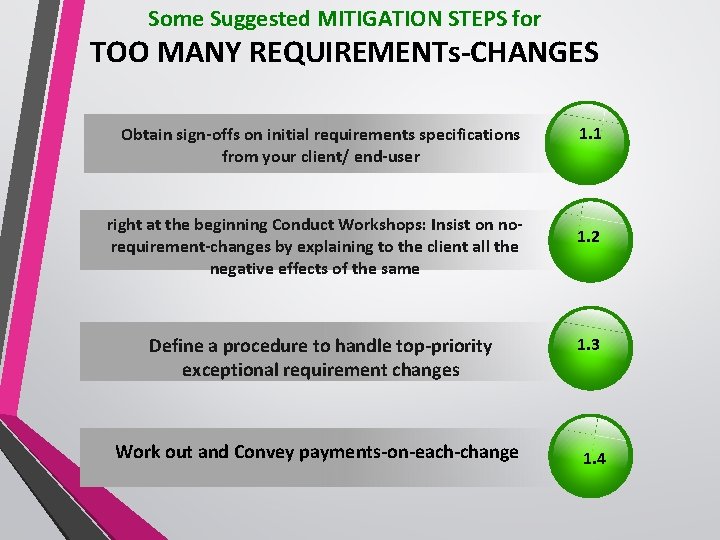
Some Suggested MITIGATION STEPS for TOO MANY REQUIREMENTs-CHANGES Obtain sign-offs on initial requirements specifications from your client/ end-user right at the beginning Conduct Workshops: Insist on norequirement-changes by explaining to the client all the negative effects of the same Define a procedure to handle top-priority exceptional requirement changes Work out and Convey payments-on-each-change 1. 1 1. 2 1. 3 1. 4
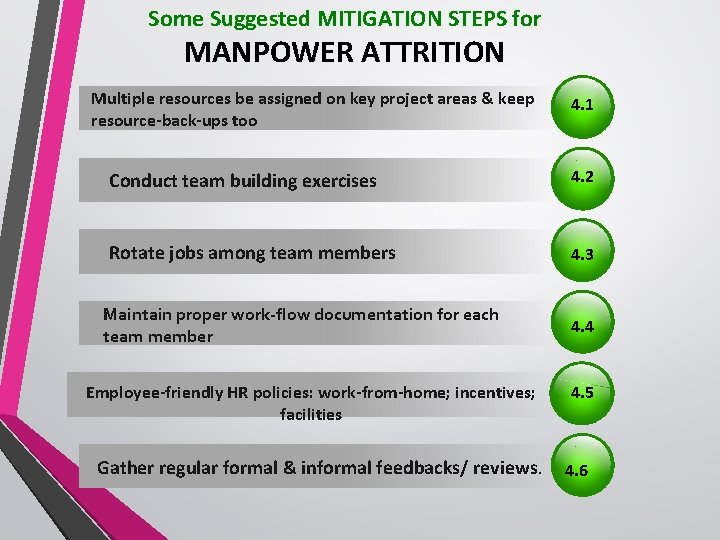
Some Suggested MITIGATION STEPS for MANPOWER ATTRITION Multiple resources be assigned on key project areas & keep resource-back-ups too 4. 1 Conduct team building exercises 4. 2 Rotate jobs among team members 4. 3 Maintain proper work-flow documentation for each team member Employee-friendly HR policies: work-from-home; incentives; facilities Gather regular formal & informal feedbacks/ reviews. 4. 4 4. 5 4. 6
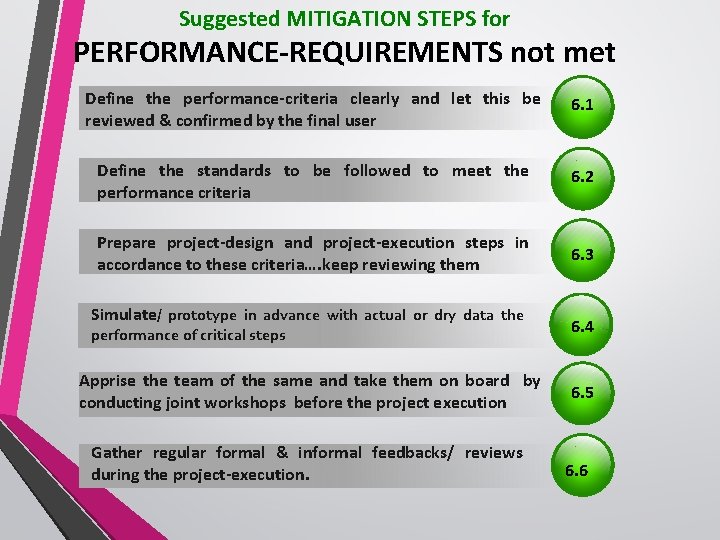
Suggested MITIGATION STEPS for PERFORMANCE-REQUIREMENTS not met Define the performance-criteria clearly and let this be reviewed & confirmed by the final user 6. 1 Define the standards to be followed to meet the performance criteria 6. 2 Prepare project-design and project-execution steps in accordance to these criteria…. keep reviewing them 6. 3 Simulate/ prototype in advance with actual or dry data the performance of critical steps Apprise the team of the same and take them on board by conducting joint workshops before the project execution Gather regular formal & informal feedbacks/ reviews during the project-execution. 6. 4 6. 5 6. 6
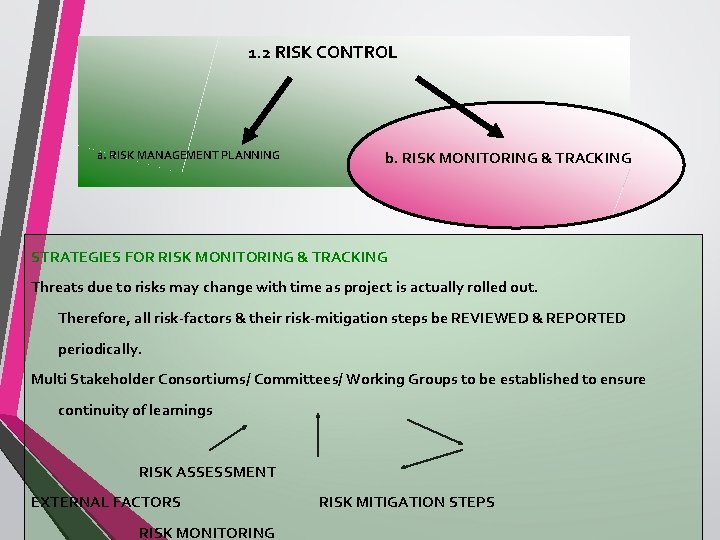
1. 2 RISK CONTROL a. RISK MANAGEMENT PLANNING b. RISK MONITORING & TRACKING STRATEGIES FOR RISK MONITORING & TRACKING Threats due to risks may change with time as project is actually rolled out. Therefore, all risk-factors & their risk-mitigation steps be REVIEWED & REPORTED periodically. Multi Stakeholder Consortiums/ Committees/ Working Groups to be established to ensure continuity of learnings RISK ASSESSMENT EXTERNAL FACTORS RISK MONITORING RISK MITIGATION STEPS
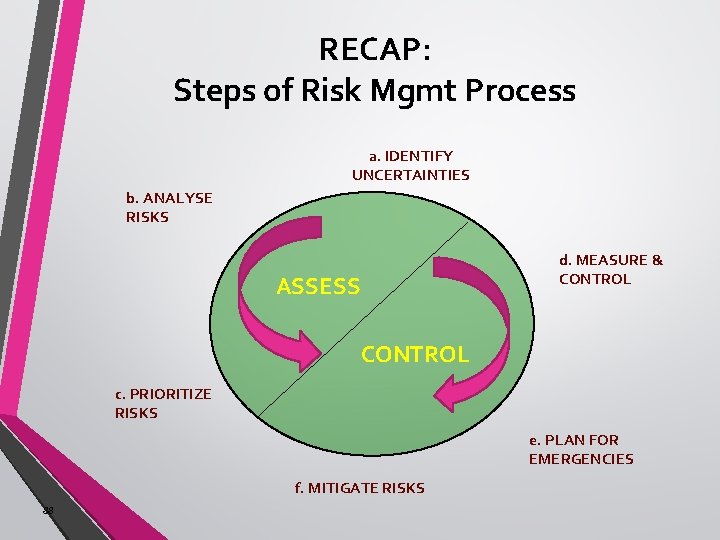
RECAP: Steps of Risk Mgmt Process a. IDENTIFY UNCERTAINTIES b. ANALYSE RISKS d. MEASURE & CONTROL ASSESS CONTROL c. PRIORITIZE RISKS e. PLAN FOR EMERGENCIES f. MITIGATE RISKS 88


CHARRU MALHOTRA Ph. D. (IIT-D), MCA, DCA, MCSD Associate Professor (e-Governance and ICT) Indian Institute of Public Administration charrumalhotra. iipa@gov. in charrumalhotra@gmail. com

Questions pls ? 37
§ § § BIBLIOGRAPHY A Validated Citizen-Centric Approach using Delphi Technique, For Converging Indigenous Knowledge Systems using ICT , Charru Malhotra*, V. M. Chariar, L. K. Das Krishna, Kumar, (2015), Where Does India Stand In EGovernment Readiness: Understanding The Components Of The EGovernment Development Index – Infographic, IT NEXT International Journal of Computer & Communication Technology, ISSN (PRINT): 0975 - 7449, Volume-4, Issue-3, 2013, E-Governance in India: Prospects and Challenges International Journal of Science, Engineering and Technology Research (IJSETR), Volume 3, Issue 7, July 2014, Challenges and Future Prospects for E-Governance in India Lynn Fernandes and Mrs. Annapoorna Shetty, International Journal of Latest Trends in Engineering and Technology Special Issue SACAIM 2016, pp. 499 -504 e-ISSN: 2278 -621 X , Challenges Faced by E -Governance in India Ramanjeet Kaur. , International Journal of Recent Scientific Research Vol. 7, Issue, 4, pp. 1061610620, April, 2016, E-Governance: Problems, Challenges And Prospects In India Episteme: an online interdisciplinary, multidisciplinary & multi-cultural journal Bharat College of Commerce, Badlapur, MMR, India Volume 2, Issue 2 September 2013, E-Governance : Issues and Challenges Paramashivaiah and Suresh / OIDA International Journal of Sustainable Development 09: 08 (2016), E- governance: Issues and challenges in India Kiran Yadav and Sanatan Tiwari Aditi mahavidyalaya, University of Delhi, India, Advance in Electronic and Electric Engineering. ISSN 2231 -1297, Volume 4, Number 6 (2014), E-Governance in India: Opportunities and Challenges IOSR Journal of Economics and Finance (IOSR-JEF) e-ISSN: 2321 -5933, p-ISSN: 2321 -5925. Volume 7, Issue 5 Ver. IV (Sep. - Oct. 2016), Nagaraja K. Research Scholar, Dept. of Studies in Economics Davangere University, Shivagangothri – 577002, E-Governance in India: Issues and Challenges Amandeep Kaur, Dr. Pardeep Mittal, International Journal of Advanced Research in Computer Engineering & Technology (IJARCET) Volume 2, Issue 3, March 2013 1196 All Rights Reserved © 2013 IJARCET E-Governance - A challenge for India (23)
Useful Links • http: //www. itnext. in/article/2015/10/07/where-does-india-stand-egovernmentreadiness-understanding-components-egovernment • http: //interscience. in/IJCCT_Vol 4 Iss 3/1 -5. pdf • http: //ijsetr. org/wp-content/uploads/2014/07/IJSETR-VOL-3 -ISSUE-7 -19641972. pdf • https: //www. ijltet. org/journal/148263112986. T 711 Challenges%20 Faced%20 by %20 E%20 governance. pdf • http: //www. recentscientific. com/sites/default/files/5093. pdf • http: //www. episteme. net. in/web. content/d. 73/content/511/attachments/8 -EGovernance. pdf • http: //www. oidaijsd. com/Files/09 -08 -01. pdf • https: //www. ripublication. com/aeee_spl/aeeev 4 n 6 spl_21. pdf • https: //pdfs. semanticscholar. org/b 41 a/d 7 d 1537 e 49 b 90 e 40 ec 9 b 732736 d 6 c 16 f 33 47. pdf • http: //egovstandards. gov. in/sites/default/files/IJARCET-VOL-2 -ISSUE-3 -11961199_1. pdf
- Slides: 83