WebMobile and API Targetted Attacks and Protection Methods
Web/Mobile and API Targetted Attacks and Protection Methods Serkan Akcan Genel Müdür
Automated Traffic on Internet Bots are 55% of all traffic on the internet
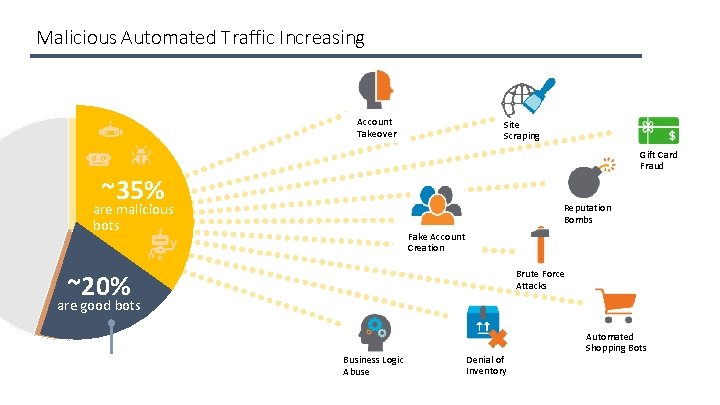
Malicious Automated Traffic Increasing Account Takeover Site Scraping Gift Card Fraud ~35% are malicious bots Reputation Bombs Fake Account Creation Brute Force Attacks ~20% are good bots Business Logic Abuse Denial of Inventory Automated Shopping Bots
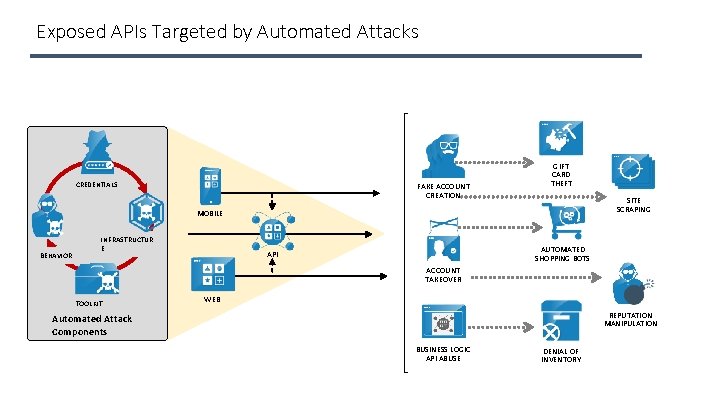
Exposed APIs Targeted by Automated Attacks CREDENTIALS FAKE ACCOUNT CREATION GIFT CARD THEFT SITE SCRAPING MOBILE BEHAVIOR INFRASTRUCTUR E AUTOMATED SHOPPING BOTS API ACCOUNT TAKEOVER TOOLKIT WEB REPUTATION MANIPULATION Automated Attack Components BUSINESS LOGIC API ABUSE DENIAL OF INVENTORY

Typical Attack Use Cases e. Commerce Credential Stuffing / Account Takeover / Account Related Fraud Malicious site scraping Fake e. Commerce Sites Banking Login Security Preventing credenial stuffing for banks that want to limit use of MFA API security – open banking Airlines / Hotels / Online Travel Credential Stuffing / Account Takeover / Account Related Fraud Fare Scraping Government Credential Stuffing / Account Takeover / Account Related Fraud
Application Attack Surfaces WEB MOBILE API
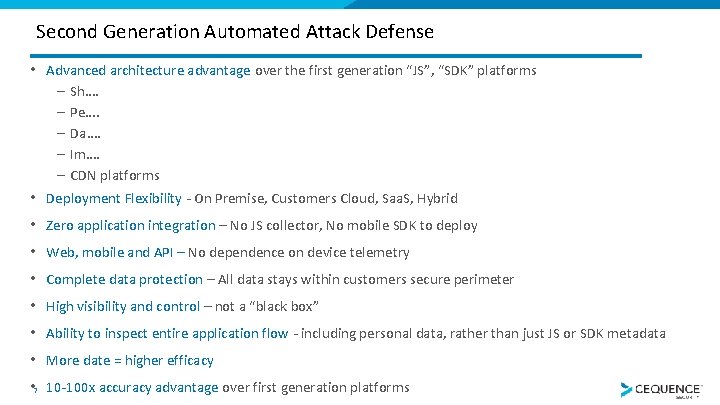
Second Generation Automated Attack Defense • Advanced architecture advantage over the first generation “JS”, “SDK” platforms – Sh…. – Pe…. – Da…. – Im…. – CDN platforms • Deployment Flexibility - On Premise, Customers Cloud, Saa. S, Hybrid • • 7 Zero application integration – No JS collector, No mobile SDK to deploy Web, mobile and API – No dependence on device telemetry Complete data protection – All data stays within customers secure perimeter High visibility and control – not a “black box” Ability to inspect entire application flow - including personal data, rather than just JS or SDK metadata More date = higher efficacy 10 -100 x accuracy advantage over first generation platforms
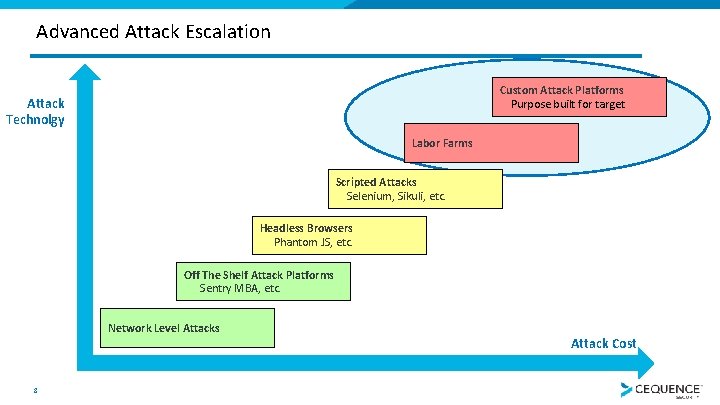
Advanced Attack Escalation Custom Attack Platforms Purpose built for target Attack Technolgy Labor Farms Scripted Attacks Selenium, Sikuli, etc. Headless Browsers Phantom JS, etc. Off The Shelf Attack Platforms Sentry MBA, etc. Network Level Attacks 8 Attack Cost
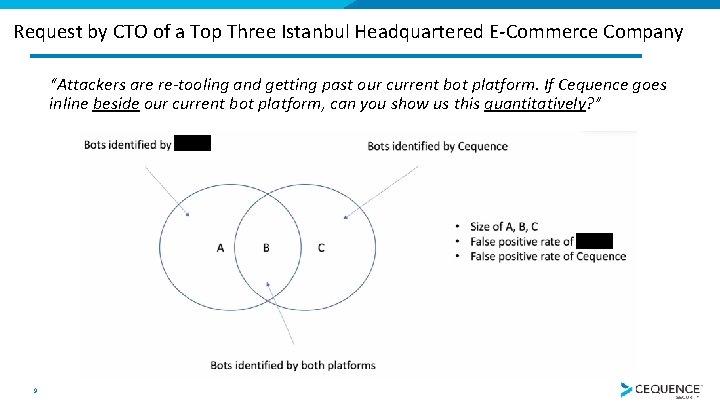
Request by CTO of a Top Three Istanbul Headquartered E-Commerce Company “Attackers are re-tooling and getting past our current bot platform. If Cequence goes inline beside our current bot platform, can you show us this quantitatively? ” 9
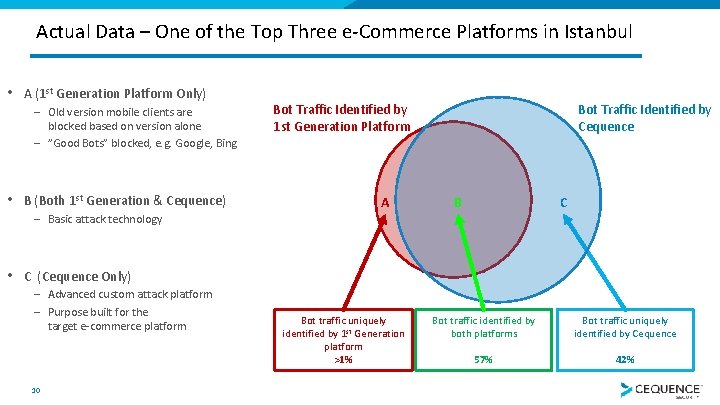
Actual Data – One of the Top Three e-Commerce Platforms in Istanbul • A (1 st Generation Platform Only) – Old version mobile clients are blocked based on version alone – ”Good Bots” blocked, e. g. Google, Bing • B (Both 1 st Generation & Cequence) Bot Traffic Identified by 1 st Generation Platform A Bot Traffic Identified by Cequence B C – Basic attack technology • C (Cequence Only) – Advanced custom attack platform – Purpose built for the target e-commerce platform 10 Bot traffic uniquely identified by 1 st Generation platform >1% Bot traffic identified by both platforms Bot traffic uniquely identified by Cequence 57% 42%
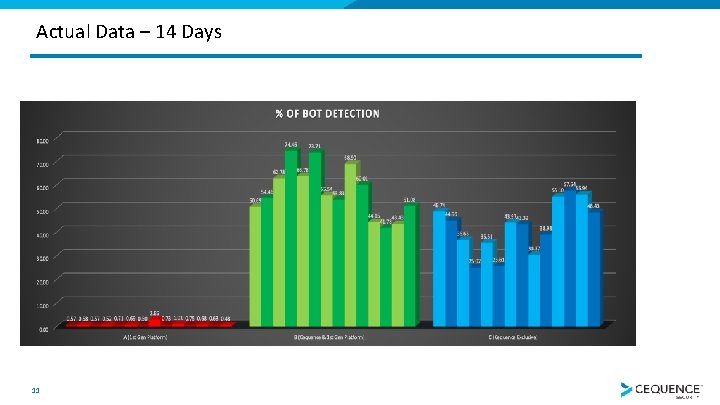
Actual Data – 14 Days 11
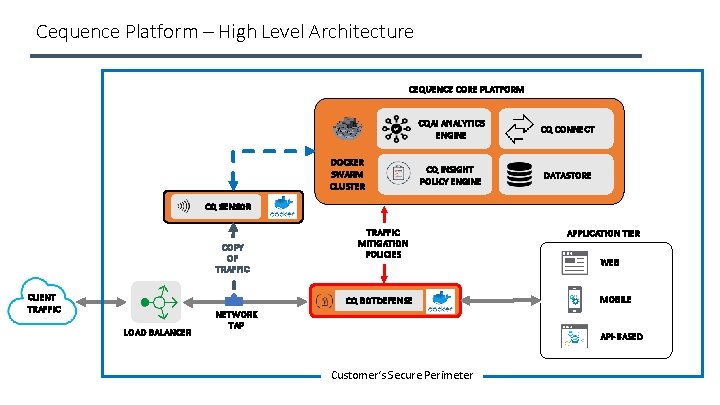
Cequence Platform – High Level Architecture CEQUENCE CORE PLATFORM DOCKER SWARM CLUSTER CQAI ANALYTICS ENGINE CQ CONNECT CQ INSIGHT POLICY ENGINE DATASTORE CQ SENSOR COPY OF TRAFFIC CLIENT TRAFFIC MITIGATION POLICIES CQ BOTDEFENSE LOAD BALANCER NETWORK TAP APPLICATION TIER WEB MOBILE API-BASED Customer‘s Secure Perimeter
www. nebulabilisim. com. tr/iletisim info@nebulabilisim. com. tr Serkan Akcan Genel Müdür
- Slides: 13