Web Single SignOn Federated Identity Dan Houser MBA
Web Single Sign-On: Federated Identity Dan Houser, MBA, CISSP, CCP Security Architect Nationwide Houserd 1@nationwide. com
Nationwide l Fortune 500 company l A leading US financial company & insurer • Life Insurance • Automobile Insurance • Property & Casualty Insurance • Liability Insurance • Annuities • Retirement Products • Investment Services • Mortgages
Objectives l How a Fortune 500 company implemented SAML for cross-company authentication (CCA) l Under the covers: how artifact and signed SAML authentication works between business partners l Building an extensible, enterprise architecture implementation with alpha and beta tools l Lessons learned, challenges, and surprises when extending authentication and authorization to 3 rd parties l Identity, cryptography, and assertions, oh my! l Web services authentication and authorization challenges
Web services l Phenomenal Business acceleration since 1990 l Transformation of business: • • • From business at the club to EDI brokering From book binding to e-books to books on demand Supply chain management l Rapid changes in business and trust models • • Outsourcing, resourcing, insourcing Hosting, co-location, managed services, ASPs Intense, cyclical Acquisition & Divestiture activity Global markets & economies
Web services (2) Generations of the Internet l 1 st Gen: Isolation Research l 2 nd Gen: Information Storefront l 3 rd Gen: Transaction e. Commerce l 4 th Gen: Integration Web Services
Quick Web services primer l Web Services • Uses open, lightweight protocols: HTTP XML WSDL UDDI SOAP • Provides a direct connection to business logic and core objects through Internet protocols • Instead of COM, DCOM and RPC, now invoke a Web service over HTTP
Federated identity What is federated identity? • The agreements, standards and technologies that make identity and entitlements portable across § autonomous domains. Cross-company authentication (CCA) • Authentication & authorization between organizations and companies. Essentially, same thing under the covers § Source: RSA Security, http: //www. rsasecurity. com/go/google/fed_id/redirect. html
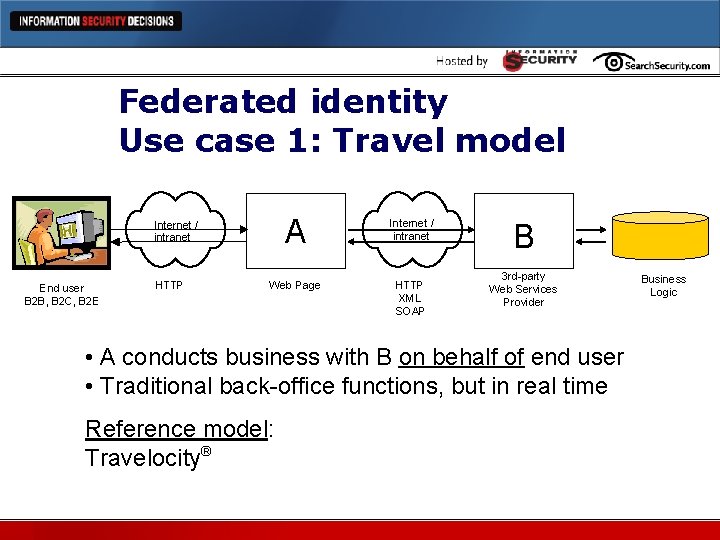
Federated identity Use case 1: Travel model A Internet / intranet Web Page HTTP XML SOAP Internet / intranet End user B 2 B, B 2 C, B 2 E HTTP B 3 rd-party Web Services Provider • A conducts business with B on behalf of end user • Traditional back-office functions, but in real time Reference model: Travelocity® Business Logic
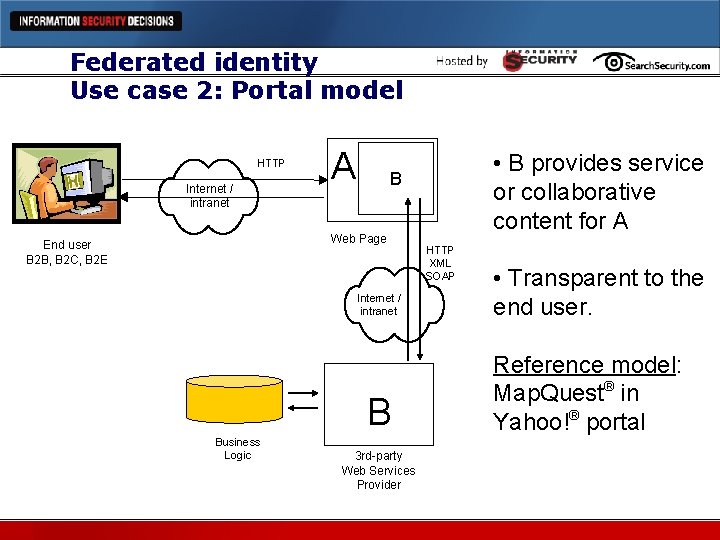
Federated identity Use case 2: Portal model HTTP Internet / intranet A B Web Page End user B 2 B, B 2 C, B 2 E Internet / intranet B Business Logic • B provides service or collaborative content for A 3 rd-party Web Services Provider HTTP XML SOAP • Transparent to the end user. Reference model: Map. Quest® in Yahoo!® portal
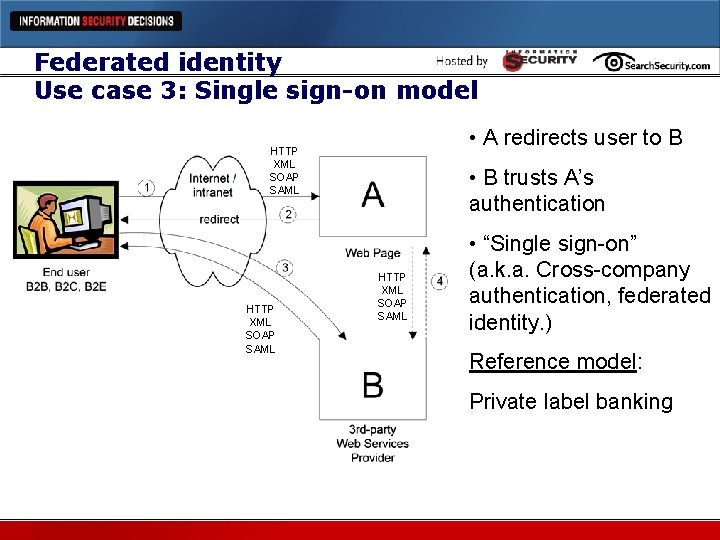
Federated identity Use case 3: Single sign-on model • A redirects user to B HTTP XML SOAP SAML • B trusts A’s authentication HTTP XML SOAP SAML • “Single sign-on” (a. k. a. Cross-company authentication, federated identity. ) Reference model: Private label banking
Web services implications l Extensible access portals for legacy business logic and processes l Ability to react to the market very quickly l Changes to core business applications are immediately available to trading partners, vendors, customers and regulators l Business velocity without roadblocks of building extensive GUI presentation layers
Web services introduces Cross-company authentication For selected interfaces: l Other business partners trust your authentications, and… l Your organization trusts the authentications provided by others.
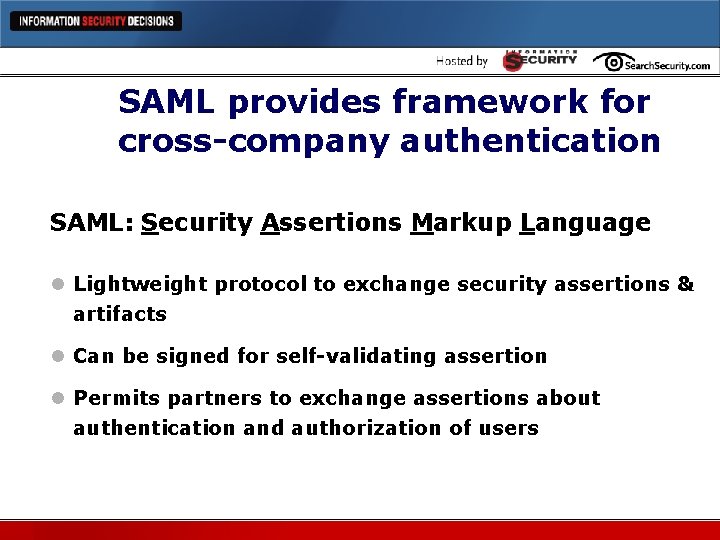
SAML provides framework for cross-company authentication SAML: Security Assertions Markup Language l Lightweight protocol to exchange security assertions & artifacts l Can be signed for self-validating assertion l Permits partners to exchange assertions about authentication and authorization of users
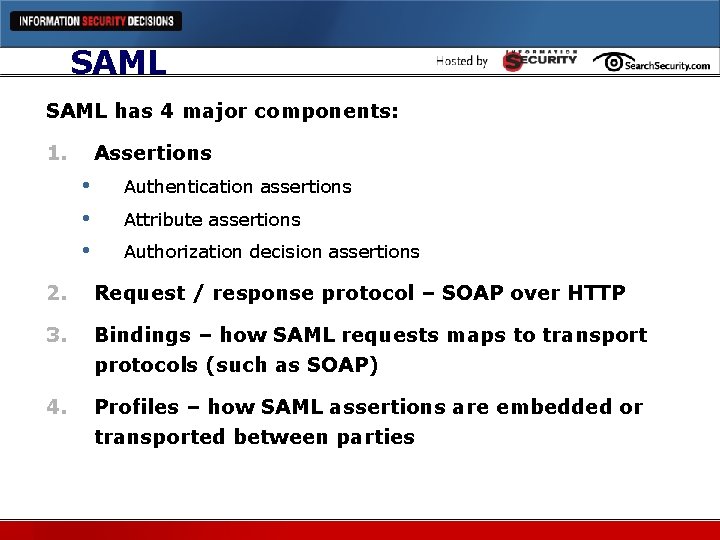
SAML has 4 major components: 1. Assertions • • • Authentication assertions Attribute assertions Authorization decision assertions 2. Request / response protocol – SOAP over HTTP 3. Bindings – how SAML requests maps to transport protocols (such as SOAP) 4. Profiles – how SAML assertions are embedded or transported between parties
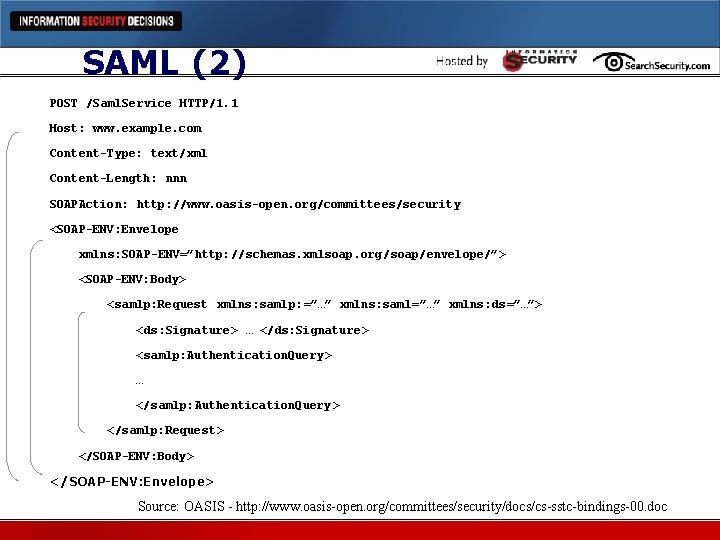
SAML (2) POST /Saml. Service HTTP/1. 1 Host: www. example. com Content-Type: text/xml Content-Length: nnn SOAPAction: http: //www. oasis-open. org/committees/security <SOAP-ENV: Envelope xmlns: SOAP-ENV=”http: //schemas. xmlsoap. org/soap/envelope/”> <SOAP-ENV: Body> <samlp: Request xmlns: samlp: =”…” xmlns: saml=”…” xmlns: ds=”…”> <ds: Signature> … </ds: Signature> <samlp: Authentication. Query > … </samlp: Authentication. Query > </samlp: Request> </SOAP-ENV: Body> </SOAP-ENV: Envelope> Source: OASIS - http: //www. oasis-open. org/committees/security/docs/cs-sstc-bindings-00. doc
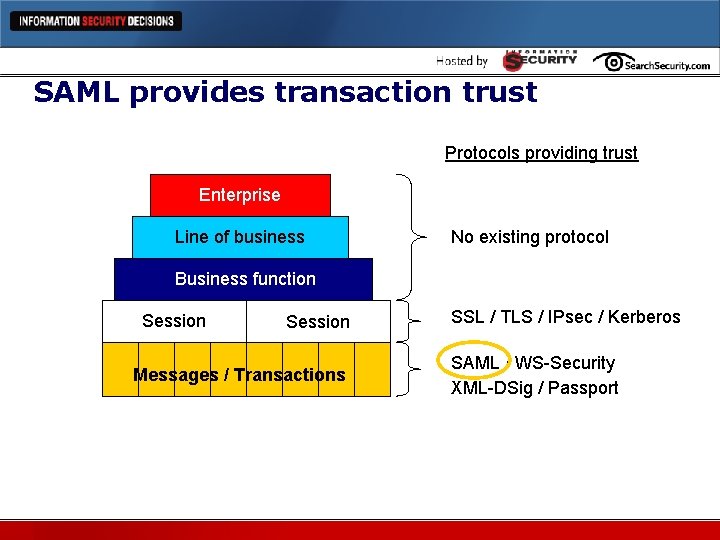
SAML provides transaction trust Protocols providing trust Enterprise Line of business No existing protocol Business function Session Messages / Transactions SSL / TLS / IPsec / Kerberos SAML / WS-Security XML-DSig / Passport
Nationwide & CCA timeline 2000 -2001 • Implemented several federated identity solutions • Used proprietary artifacts & communication session solutions • • • Worked well, but…. Unique “one-off” solutions Lacked standards for standard implementation, extensive re-work
Nationwide & CCA timeline (2) 2002 • Resolved to adopt a standards-based federated identity solution • • Investigated several federated identity standards • Joined Liberty Alliance as Associate Member SAML selected as best SSO authentication solution at the time
Nationwide & CCA Timeline (3) 2002 • Determined three viable directions: § Web Access Mgmt (WAM) middleware § Adding SAML parsing to existing application(s) § Building own assertion generator & parser • Investigated the market for vendor best suited to deliver SAML-based solution • • Established contract with WAM vendor Built first SAML implementation for SSO
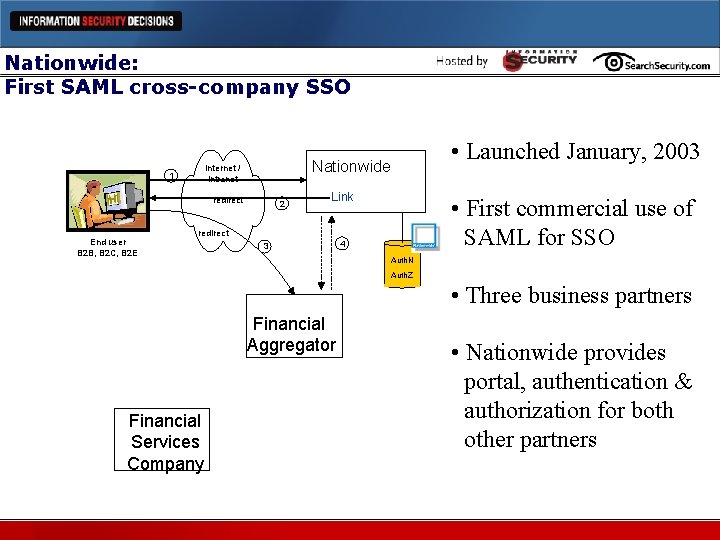
Nationwide: First SAML cross-company SSO 1 redirect End user B 2 B, B 2 C, B 2 E • Launched January, 2003 Nationwide Internet / intranet 2 Link • First commercial use of SAML for SSO redirect 3 4 Auth. N Auth. Z • Three business partners Financial Aggregator Financial Services Company • Nationwide provides portal, authentication & authorization for both other partners
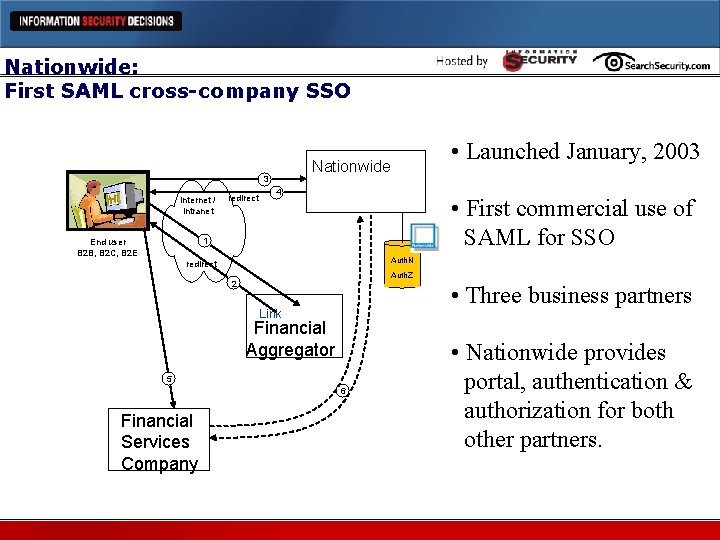
Nationwide: First SAML cross-company SSO 3 Internet / intranet redirect • Launched January, 2003 Nationwide 4 • First commercial use of SAML for SSO 1 End user B 2 B, B 2 C, B 2 E Auth. N redirect Auth. Z 2 • Three business partners Link Financial Aggregator 5 6 Financial Services Company • Nationwide provides portal, authentication & authorization for both other partners.
Challenges l Complexity l Business issues l Federation l Weakest link l Business trust models
Complexity Corporate 3 -tier Web architectures are already complex Federated SSO adds significant complexity in coupling: Existing infrastructure Web Access Mgmt (WAM) middleware Web services interfaces New infrastructure Cross-company functionality
Complexity (2) Complexity requires technical sophistication on both sides of the relationship Developers need to understand: SAML Web services WAM Encryption Architects need to understand: Identity Management Authentication/authorization models
Complexity (3) Complexity extends to privacy and identity issues • • Privacy policy aggregation, demarcation Need to involve CPO, General Counsel Identity management issues Legal contract & business agreement: § Roles & responsibilities § Vendor management § Procedures for validating trust
Business issues The technology is moderately complex. Trust & policies are harder. Closer to a wedding than a business relationship Nationwide’s solution: l Certification & accreditation process l Reference Architecture l Strong 3 -tier infrastructure architecture l Forward-looking standards for trust governance
Federation l Interoperability of identity frameworks l Tough to do between existing corporate legacy applications l Even tougher between disparate organizations l Deep dive on assumptions, standards, vetting l Must scale and scope to business context
Weakest link l Security posture differences must be determined & governed. • • • Alignment of reference architecture Policy & standards matrix comparison Establishment of CCA standards l SLA & performance weakest link • If your SLA is 7 x 24, and your partner’s SLA is 5 x 10, how will you provide 7 x 24?
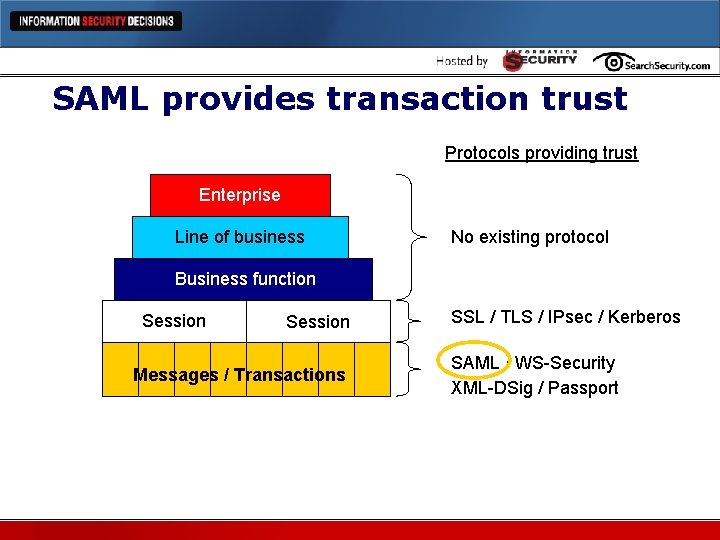
SAML provides transaction trust Protocols providing trust Enterprise Line of business No existing protocol Business function Session Messages / Transactions SSL / TLS / IPsec / Kerberos SAML / WS-Security XML-DSig / Passport
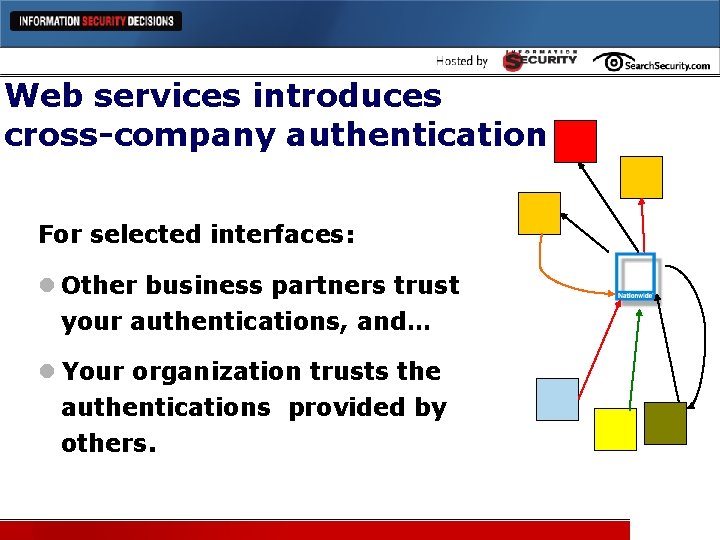
Web services introduces cross-company authentication For selected interfaces: l Other business partners trust your authentications, and… l Your organization trusts the authentications provided by others.
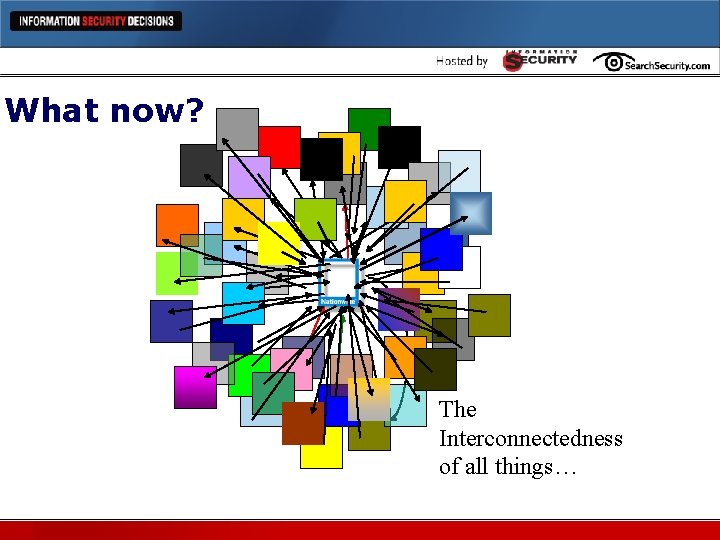
What now? The Interconnectedness of all things…
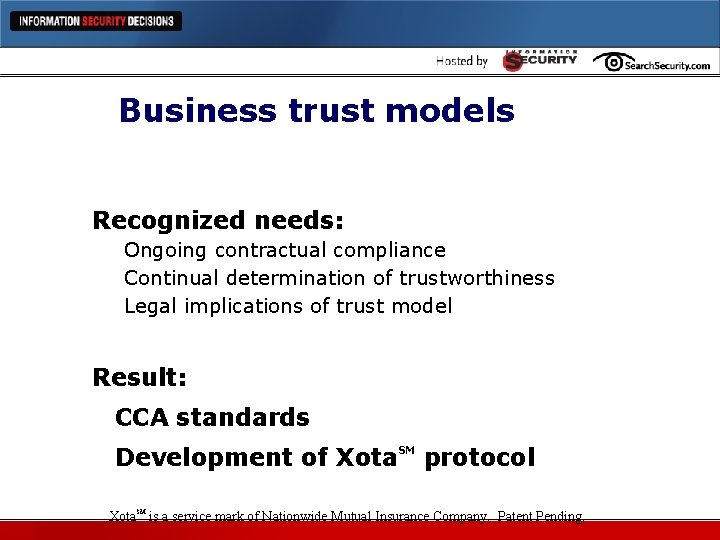
Business trust models Recognized needs: Ongoing contractual compliance Continual determination of trustworthiness Legal implications of trust model Result: CCA standards Development of Xota. SM protocol Xota. SM is a service mark of Nationwide Mutual Insurance Company. Patent Pending.
Xota. SM l Combination of protocol & methodology l Permits determination of trustworthiness in real time between business partners l Trust governance at the transaction level l Continuous assessment of contractual and regulatory compliance l Nationwide is establishing a consortium Xota. SM is a service mark of Nationwide Mutual Insurance Company. Patent Pending.
Surprises l Troubleshooting with ½ the data l Missing standards & solutions l Interoperability l Human factors
Troubleshooting l SAML consists of HALF transactions: Asserting party Relying party l Troubleshooting with only half the data! l Complexity and cross-disciplinary issues l Coordinated helpdesk an issue l Log sharing, aggregation l Time synchronization an issue
Missing standards & solutions SAML has some gaps No SAML session management No support for timeout, logoff “rollup” Had to develop own session management and session timeout protocol Middleware gaps No signed SAML support in middleware Lack of 3 -tier architecture support
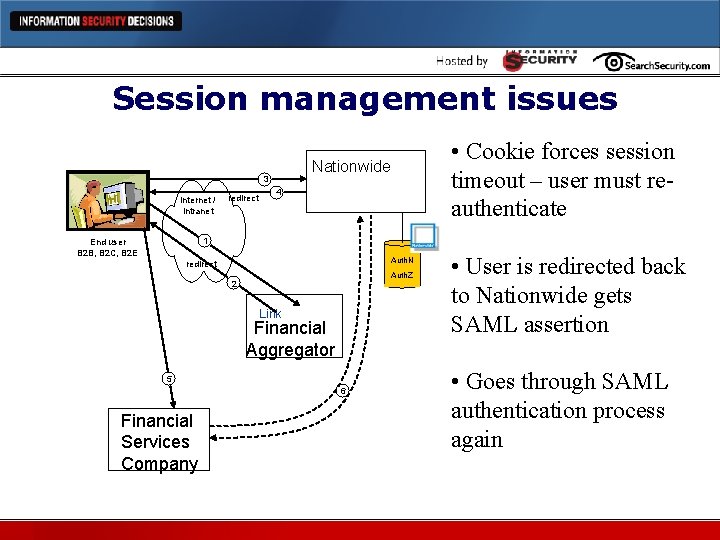
Session management issues 3 Internet / intranet redirect • Cookie forces session timeout – user must reauthenticate Nationwide 4 1 End user B 2 B, B 2 C, B 2 E Auth. N redirect Auth. Z 2 Link Financial Aggregator 5 6 Financial Services Company • User is redirected back to Nationwide gets SAML assertion • Goes through SAML authentication process again
Interoperability Authentication & authorization required for both the business partners and users SAML provides user authentication No protocol support for partner connection authentication, authorization Each partner connection model unique Bleeding-edge implementation preceded Web services protocol standards
Human factors Communications Issues Users unaware of SSO implementation: • • • Sensitive to performance lag Multiple resubmits Question lack of sign-on – “Is security broken? ” Deep bookmarking Users will bookmark relying party sites Persistent cookie that identifies user as CCA user?
Lessons learned l Have a good partner relationship with WAM vendor(s) l Business issues as significant as technology issues l Lightweight implementation toolkit required for smaller partners l Trust modeling important consideration
Benefits achieved l Federated identity provides flexible, adaptable solutions for SSO l Ability to use infrastructure for affiliates, other contexts l If you build it, they will come l Federated identity works reliably l Use of standards, such as SAML, pays off in 2 nd, 3 rd implementations
Q&A l Questions?
Further information Best resources: OASIS http: //xml. coverpages. org/saml. html Liberty Alliance http: //projectliberty. org Contact information: Dan Houser, MBA, CISSP, CCP Security Architect Nationwide (614) 249 -6639 houserd 1@nationwide. com
Thank you. Questions, comments? Mr. Houser will not be available to answer questions at the Ask-the-Experts booth in the Exhibit Hall. Please send question to jglossner@techtarget. com.
- Slides: 44