Web Security Web Security Introduction Need for security
Web Security
Web Security Introduction • Need for security on the Transport Control Protocol (TCP) Layer • Uses Secure Socket Layer (SSL) and Internet standard SSL called Transport Layer Service • Allows TCP users to indentify security mechanisms • Particularly concerted with E – commerce security: Secure Electronic Transaction (SET)
Web Security Considerations • Room for nearly all levels of security in the Web • E. g. previous considerations • Nevertheless: Web presents unique challenges • All communication two way thus doubling the opportunity for attack • Web integrated into business: high losses if security compromised • Security flaws in complex software • Web Servers may provide access to local intranet • Users not aware of security risks
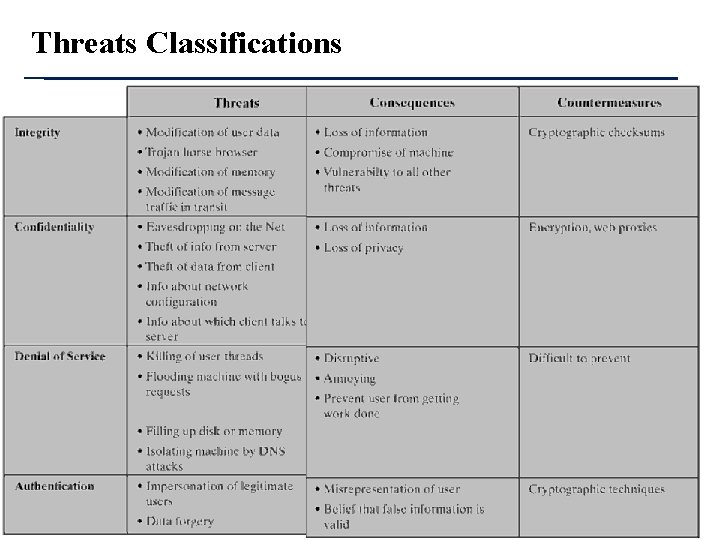
Threats Classifications
Web Security Approaches • Different ways of implementing security • Similar in services and (to an extent) mechanisms • Differ with respect to scope and location with TCP/IP stack • Simple security: Use IP Security! IPSec runs over TCP • Another solution: Run security just above TCP, below IP – Basis of SSL and TLS – Choice: Make SSL/TLS transparent or integrate into applications? (advantage: tailored to needs, disadvantage: complexity)
SSL and TLS • • • Current version is SSL v 3. TLS is essentially SSLv 3. 1 Not a “successor” exactly, just a different standard SSL Architecture Make TCP reliable/secure Higher level protocols operate (HTTP for instance) on SSL • SSL uses three protocols: Handshake Protocol, Change Cipher Spec Protocol, Alter Protocol • Also a special “record” protocol • Used in management of SSL exchanges
SSL (Secure Socket Layer) • • Transport layer security service Originally developed by netscape Version 3 designed with public input Subsequently became internet standard known as TLS (transport layer security) • Uses TCP to provide a reliable end-to-end service • SSL has two layers of protocols
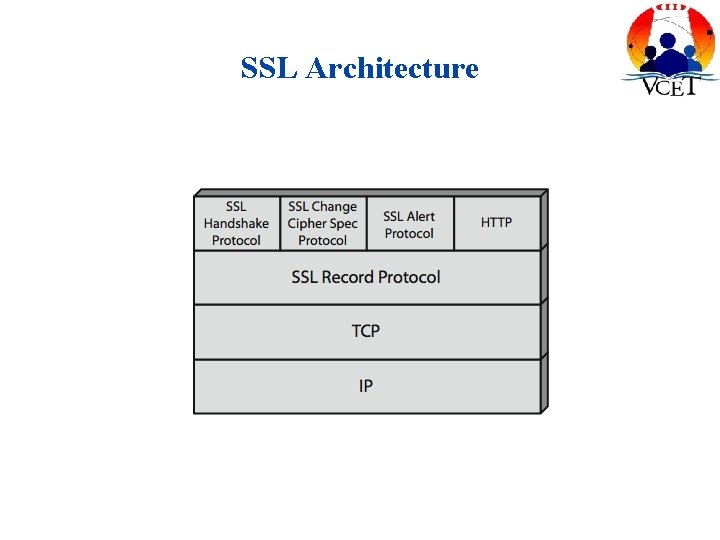
SSL Architecture
SSL Architecture • SSL connection – A transient, peer-to-peer, communications link – Associated with 1 SSL session • SSL session – An association between client & server – Created by the handshake protocol – Define a set of cryptographic parameters – May be shared by multiple SSL connections
Session and Connection States • Session state has following parameters – Session Identifier, Peer certificate (X 509, etc) – Compression Method – Cipher spec (data encryption) and hash – Master secret – Is resumable? • Connection state: – Server and client randomness – Keys: Server/Client MAC, Server/Client Write – Initialization vectors – Sequence numbers
SSL Record Protocol Services • Message integrity – Using a MAC with shared secret key – Similar to HMAC but with different padding • Confidentiality – Using symmetric encryption with a shared secret key defined by handshake protocol – AES, IDEA, RC 2 -40, DES, 3 DES, fortezza, RC 4 -40, RC 4 -128 – Message is compressed before encryption
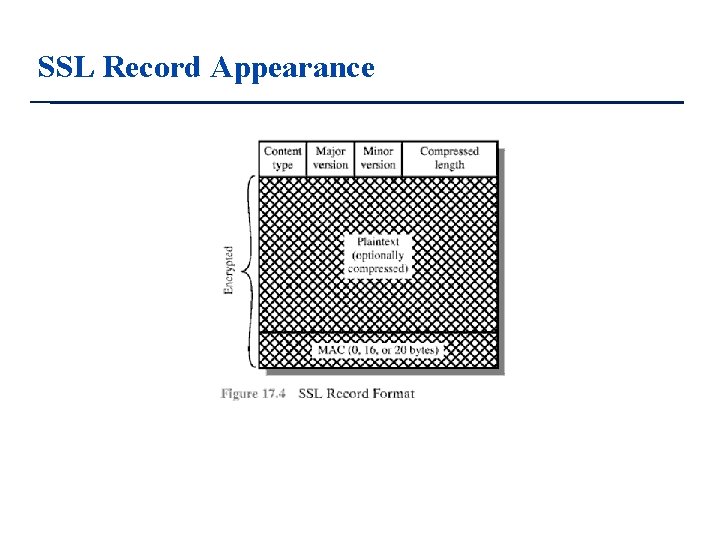
SSL Record Appearance
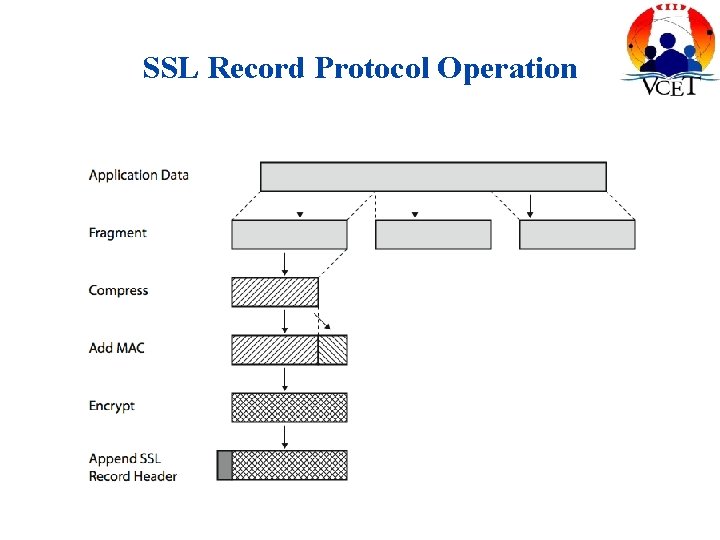
SSL Record Protocol Operation
SSL Change Cipher Spec Protocol • One of 3 SSL specific protocols which use the SSL record protocol • A single message • Causes pending state to become current • Hence updating the cipher suite in use
SSL Alert Protocol • Conveys ssl-related alerts to peer entity • Severity • Warning or fatal • Specific alert • Fatal: unexpected message, bad record mac, decompression failure, handshake failure, illegal parameter • Warning: close notify, no certificate, bad certificate, unsupported certificate, certificate revoked, certificate expired, certificate unknown • Compressed & encrypted like all SSL data
SSL Handshake Protocol • Allows server & client to: – Authenticate each other – To negotiate encryption & MAC algorithms – To negotiate cryptographic keys to be used • Comprises a series of messages in phases 1. Establish security capabilities 2. Server authentication and key exchange 3. Client authentication and key exchange 4. Finish
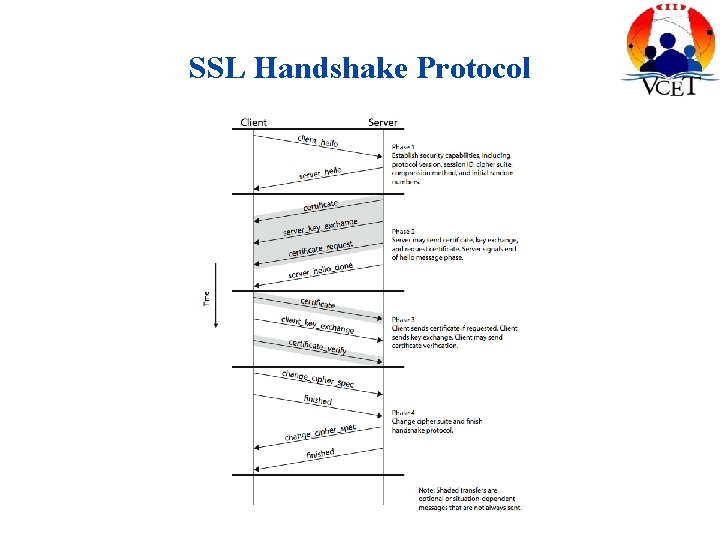
SSL Handshake Protocol
TLS (Transport Layer Security) • IETF standard RFC 2246 similar to sslv 3 • With minor differences – In record format version number – Uses HMAC for MAC – A pseudo-random function expands secrets – Has additional alert codes – Some changes in supported ciphers – Changes in certificate types & negotiations – Changes in crypto computations & padding
- Slides: 18