Web Security Web Application Security Concerns Introduction The

Web Security
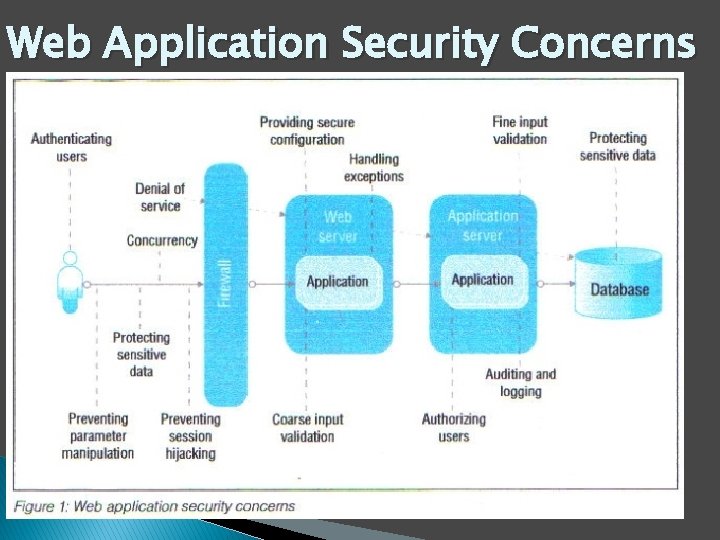
Web Application Security Concerns
Introduction “The art of war teaches us to rely not on the likelihood of the enemys’ not coming, but on our own readiness to receive him; not on the chance of his attacking, but rather on the fact that we have made our position unassailable. ” The art of war, Sun Tzu
Definitions �Computer Security – Generic name for the collection of tools designed to protect data and to thwart hackers �Network Security – Measures to protect data during their transmission �Internet Security – Measures to protect data during their transmission over a collection
Securing a Network Securing the network used to be easy when it consisted of a mainframe in a locked room and several dumb terminals. But as we embrace distributed client/server computing, corporate networks become more complex than ever. 12/12/2021
The goals of network security will depend on the enterprise, but generally include the following: • Control access to the network • Control access to specific files and applications • Protect information being transmitted • Detect any breaches in security, and take appropriate action • Prevent accidental damage from occurring • Institute a recovery plan in case of system failure • Protect against physical theft and tampering • Plan for disasters 12/12/2021
Services, Mechanisms, Attacks �Three aspects of Information Security i. Security attack ii. Security Mechanism iii. Security Service
Security Attack � Any action that compromises the security of information owned by an organization � Information security is about how to prevent attacks, or failing that, to detect attacks on information based systems 1. Passive Attacks – Eavesdropping on, monitoring of, transmission to: Obtain message contents or monitor traffic flows. Spy ware – sits & learns 2. Active Attacks – Modification of data stream to: ◦ Masquerade of one entity as some other ◦ Replay previous messages ◦ Modify messages in transit
�Masquerade: One entity pretends to be a different, legitimate entity. �Replay: Data is captured and then retransmitted. �Modification: A portion of a message is altered, delayed, or reordered. �Denial of Service: This is becoming the most prevalent form of active attack on the Internet and occurs when the network is disrupted either by overloading it with false messages or disabling the network directly. Intentionally blocking a particular internet site to prevent or hinder business activities and commerce 12/12/2021 9
� Phishing: Masquearading as a well known site such as a bank to obtain a user’s personal information, typically an account number and access code. � Address Spoofing: Faking the IP source address in a packet to trick a receiver into processing the packet. � Name Spoofing: Using a misspelling of a wellknown name or poisoning a name server with an incorrect binding � Key breaking: Automatically guessing a decryption key or a password to gain unauthorized access to data.
�A Security Mechanism mechanism that is designed to detect, prevent or recover from a security attack � There’s no single mechanism that will support all functions required � However, one particular element underlies many of the security mechanisms in use i. e. cryptographic techniques 1. Specific Security Mechanisms Encipherment, digital signatures, access controls, data integrity, authentication exchange, traffic padding, routing control, notarization 2. Passive Security Mechanisms Trusted functionality, security labels, event detection, security audit trails, security recovery
Cryptography and Network Security � Basic Terminology ◦ Plaintext – The original message ◦ Ciphertext – The coded Message ◦ Cipher – Algorithm for transforming plaintext into ciphertext ◦ Key – Information used in cipher known only to the sender /receiver ◦ Encipher – (Encrypt) – Converting plaintext to ciphertext ◦ Decipher – (Decrypt) – Recovering plaintext from ciphertext ◦ Cryptography – Study of encryption principles / methods ◦ Cryptanalysis – (Code breaking) – The study of encryption principles/methods ◦ Cryptology – The field of both cryptography and cryptanalysis
Two kinds of ciphers � There are two most popular encryption algorithms 1. Symmetric Ciphers �Private key / single key / common key �Sender and Receiver share a common key �Both parties have full information of the key �Remains very widely used �All classical encryption algorithms are symmetric �Assumes encryption algorithm is known �Implies a secure channel to distribute key 2. Asymmetric Ciphers �Public key ciphers �Sender and receiver have different keys
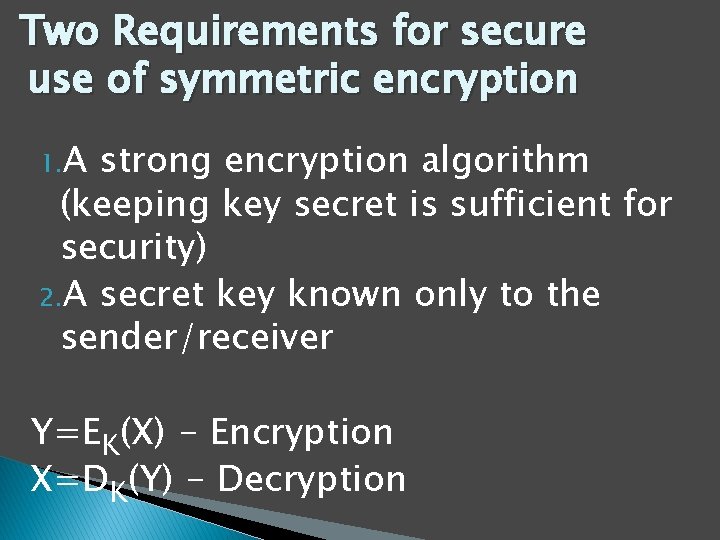
Two Requirements for secure use of symmetric encryption 1. A strong encryption algorithm (keeping key secret is sufficient for security) 2. A secret key known only to the sender/receiver Y=EK(X) - Encryption X=DK(Y) - Decryption
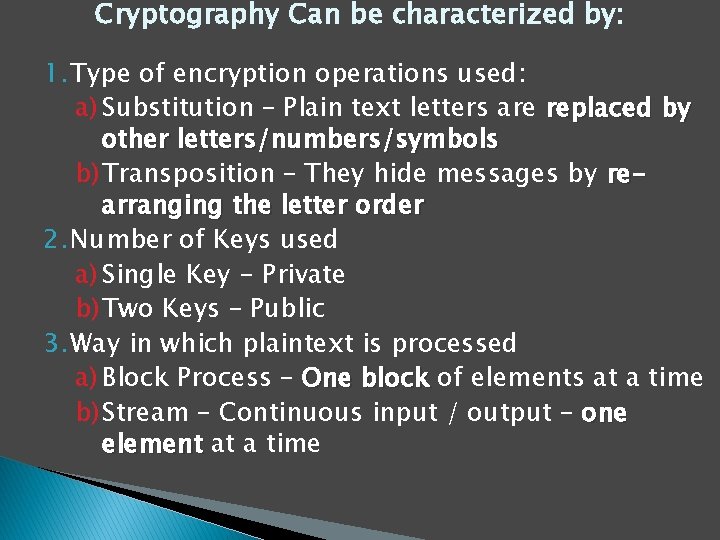
Cryptography Can be characterized by: 1. Type of encryption operations used: a) Substitution – Plain text letters are replaced by other letters/numbers/symbols b) Transposition – They hide messages by rearranging the letter order 2. Number of Keys used a) Single Key - Private b) Two Keys – Public 3. Way in which plaintext is processed a) Block Process – One block of elements at a time b) Stream – Continuous input / output – one element at a time
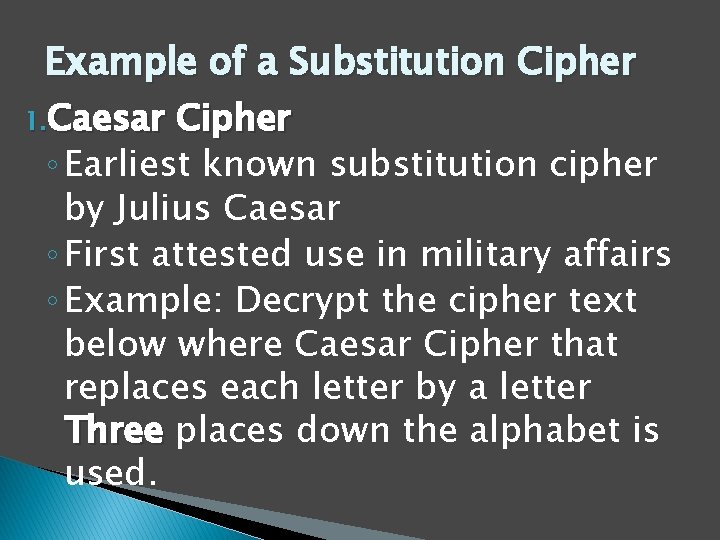
Example of a Substitution Cipher 1. Caesar Cipher ◦ Earliest known substitution cipher by Julius Caesar ◦ First attested use in military affairs ◦ Example: Decrypt the cipher text below where Caesar Cipher that replaces each letter by a letter Three places down the alphabet is used.
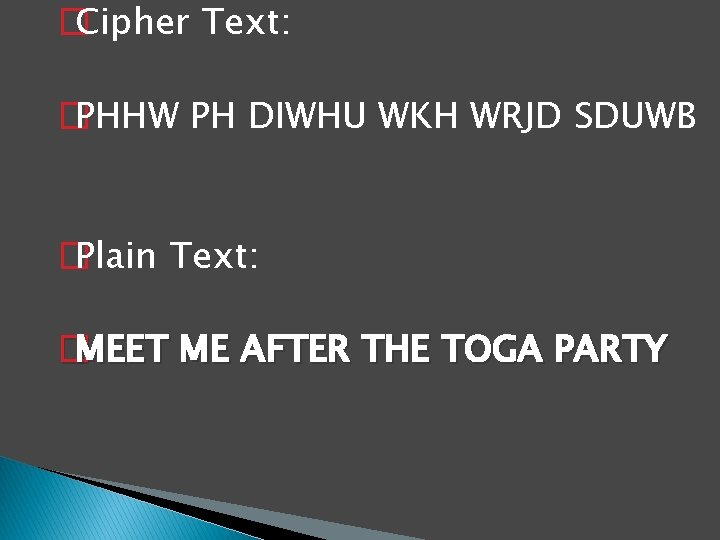
� Cipher Text: � PHHW PH DIWHU WKH WRJD SDUWB � Plain Text: � MEET ME AFTER THE TOGA PARTY
Transposition Ciphers �Also known as permutation ciphers. �They hide messages by rearranging the letter order without altering the actual letters used �We can recognize them since they have the same frequency distribution as the original text
� Plaintext is maintained as ciphertext, we only change letter positions Example: - Row Transposition Ciphers • A more complex scheme • Write letters of message out in rows over a specified number of columns
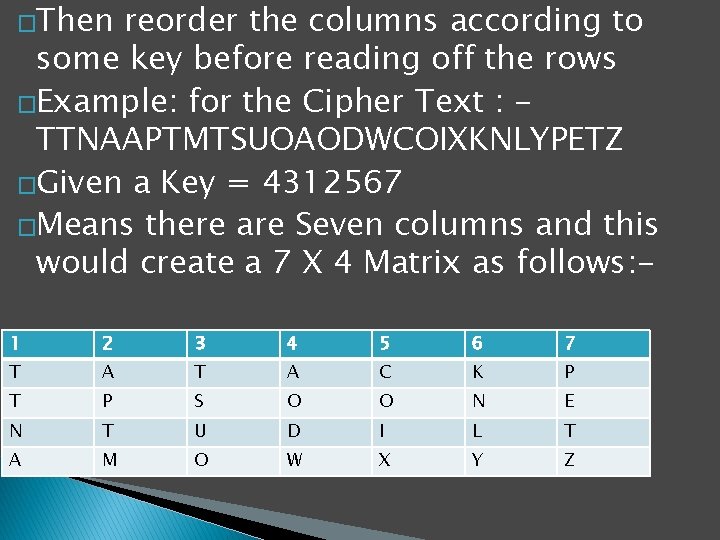
�Then reorder the columns according to some key before reading off the rows �Example: for the Cipher Text : TTNAAPTMTSUOAODWCOIXKNLYPETZ �Given a Key = 4312567 �Means there are Seven columns and this would create a 7 X 4 Matrix as follows: 1 2 3 4 5 6 7 T A C K P T P S O O N E N T U D I L T A M O W X Y Z
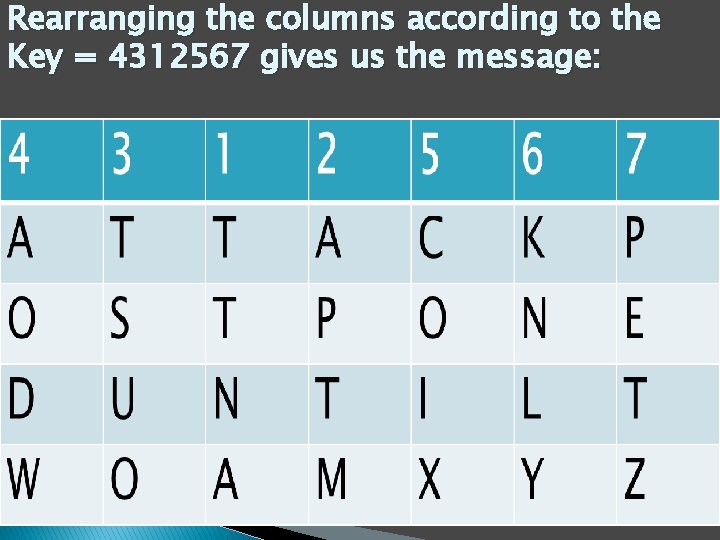
Rearranging the columns according to the Key = 4312567 gives us the message:
Security Service �Something that enhances the security of the data processing systems and the information transfers of an organization �It is intended to counter security attacks �There’s need to make use of one or more security mechanisms to provide the service �There are replicate functions normally associated with physical documents e. g. have signatures, dates, need protection from disclosure, tampering, or destruction, be notarized or witnessed, be recorded or licensed, fingerprints, Seal, Stamp
Security Services Cont… � Authentication: ◦ Assurance that the communicating entity is the one claimed ◦ Proving the identity of a person or system � Access Control: ◦ Prevention of unauthorized use of a resource ◦ Limiting who and what can gain access to: �Systems and their components �Network devices �Applications �Data
�Data Confidentiality – Protection of data from unauthorized disclosure �Data Integrity – Assurance that data received is as sent by an authorized entity �Non-Repudiation –Protection against denial by one of the parties in a communication �Encryption-transforming data in a manner such that they cannot be meaningfully read because they are garbled �Auditing and monitoring 24
Types of Cyber Attacks �Technical attack An attack perpetrated using software and systems knowledge or expertise �Nontechnical attack An attack in which a perpetrator uses persuasion to trick people into revealing sensitive information or performing actions that compromise the security of a network �Common vulnerabilities and exposures (CVEs) Publicly known computer security risks or problems; these are collected, enumerated, and shared by a board of security-related organizations.
�Denial-of-service (Do. S) attack An attack on a Web site in which an attacker uses specialized software to send a flood of data packets to the target computer with the aim of overloading its resources. �Distributed denial of service (DDo. S) attack A denial-of-service attack in which the attacker gains illegal administrative access to as many computers on the Internet as possible and uses these multiple computers to send a flood of data packets to the target computer �Malware A generic term for malicious software
� Virus A piece of software code that inserts itself into a host, including the operating systems, to propagate; it cannot run independently but requires that its host program be run to activate it � Worm A software program that runs independently, consuming the resources of its host from within in order to maintain itself and propagating a complete working version of itself onto another machine � Trojan horse A program that appears to have a useful function but that contains a hidden function that presents a security risk
Security Technologies Internet and EC security is a thriving business and several companies have come up with technologies to enhance internet security. Examples of security technologies include: � Firewall A firewall is a network node consisting of both hardware and software that isolates a private network from a public network. � Intrusion detection system (IDS) This is a special category of software that can monitor activity across a network or on a host computer, watch for suspicious activity, and take automated action based on what it sees � Security risk management A systematic process for determining the likelihood of various security attacks and for identifying the actions needed to prevent or mitigate those attacks.
Firewalls � A firewall is a hardware or software system that prevents unauthorized access to or from a network. � They can be implemented in both hardware and software, or a combination of both. � Firewalls are frequently used to prevent unauthorized Internet users from accessing private networks connected to the Internet. � All data entering or leaving the Intranet pass through the firewall, which examines and blocks data that does not meet the specified security criteria. 12/12/2021
�Authentication - A process that establishes the source of information, provides assurance of an entity’s identity or provides assurance of the integrity of communications sessions, messages, documents or stored data. �Authorization - Access privileges that are granted to an entity; conveying an “official” sanction to perform a security function or activity.
Passwords �The first line of defense in network security is the password Unfortunately, it is also the most abused. Cryptography �The basic concept if cryptography is the scrambling of messages so that only the intended parties can read them. Cryptography means hidden writing It makes use of ciphers 12/12/2021
Alarms �Physical locks can be alarmed Programmed locks can be backed up by surveillance methods to detect anyone who is attempting unauthorized entry. Risk Management Software �This refers to applications, which will gather information and then reflect situations and conditions, empowering the managers to make decisions and evolve strategies to deal with different situations. 12/12/2021
Identification Controls Personal Identification can be by: �þ Physical characteristics (Biometrics-Fingerprints, Facial Characteristics, Eye Pupil) �þ Something that could be memorized: passwords, security codes etc �þ Something that could be carried: a badge, card, key, etc. �þ Call back systems 12/12/2021
E-mail Gateways �Viruses and macros can enter your network via e-mail. Traditional e-mail is full of holes and security vulnerabilities. Usually, an enterprise should not send highly sensitive information over the Internet. 12/12/2021
Backup procedures � Managers should make data backup a top operational priority, and ensure that the backups represent sequential generations (grandfather/son) of data. 12/12/2021
� Digital signature The result of a cryptographic transformation of data that, when properly implemented with a supporting infrastructure and policy, provides the services of: ◦ 1. Origin authentication, ◦ 2. Data integrity, and ◦ 3. Signer non-repudiation
Computer security involves providing appropriate levels of assurance of: Availability of computing services and data/information stored in computing systems Confidentiality of data/information stored in computing systems Integrity of computing systems and data/information stored therein Auditability of usage of computing systems and access to data/information stored therein Non-repudiability of transactions initiated by individuals and organizations 37
�In practice, the degree of protection taken, taken and hence its cost will depend upon the assessment of potential intruders, intruders and this in turn, will depend on the sensitivity of the data and its possible value to an outsider. 12/12/2021
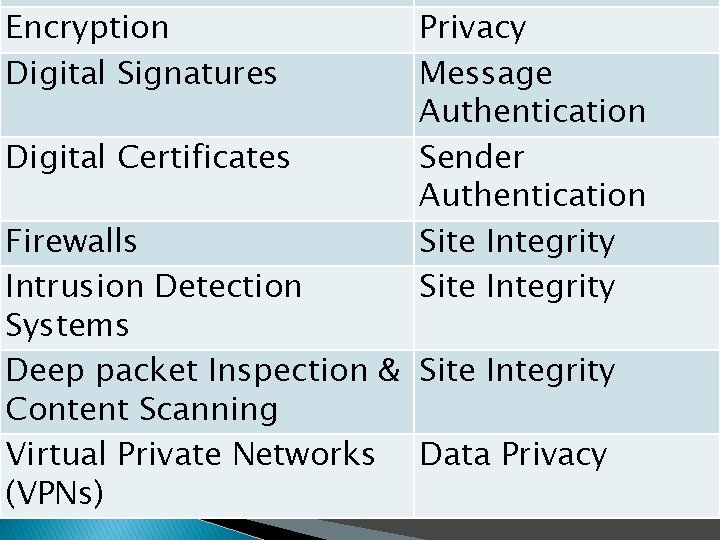
Encryption Digital Signatures Digital Certificates Privacy Message Authentication Sender Authentication Site Integrity Firewalls Intrusion Detection Systems Deep packet Inspection & Site Integrity Content Scanning Virtual Private Networks Data Privacy (VPNs)
Conclusion � Computer and information security continue to grow in importance � The gap between attackers’ capabilities and ability to defend against them is widening � Neglecting security is the worst thing you can do � Defense in depth (multi-tiered defenses) work best � Always weigh costs versus benefits when considering security measures � Nobody ever said this was going to be easy! 40

- Slides: 41