Web Security Martin Nystrom CISSP Security Architect Cisco

Web Security Martin Nystrom, CISSP Security Architect Cisco Systems, Inc. mnystrom@cisco. com Session Number Presentation_ID © 2003 Cisco Systems, Inc. All rights reserved. 1
Who am I? • Security Architect in Cisco’s Info. Sec Responsible for consulting with application teams to secure their architecture Monitor for infrastructure vulnerabilities Infrastructure security architect • 12 years developing application architectures • Java programmer • Master of Engineering – NC State University • Bachelor’s - Iowa State University – (1990) mnystrom © 2004 Cisco Systems, Inc. All rights reserved. 2
Why worry? • Guess. com sanctioned by FTC for exposing private information “…permitting anyone able to construct a properly-crafted URL to pull down every name, credit card number and expiration date in the site's customer database. ” • U. S. Army systems hacked using Web. DAV vulnerability in IIS “…it was a disturbingly successful attack, experts say, because the intruder found and exploited a flaw that took security researchers completely by surprise. “ • Millions of credit card numbers compromised at Data Processors International "All indications are the attack on this company's (Internet) address came from the outside, and efforts continue to analyze this attack to see if it could be traced to the attacker, " the investigator said. • Utah ISP is victim of retaliation following hackers' attack on Al-Jazeera “…impersonating an Al-Jazeera employee, tricked the Web addressing company Network Solutions into making technical changes that effectively turned over temporary control of the network's Arabic and English Web sites. . . '' mnystrom © 2004 Cisco Systems, Inc. All rights reserved. 3
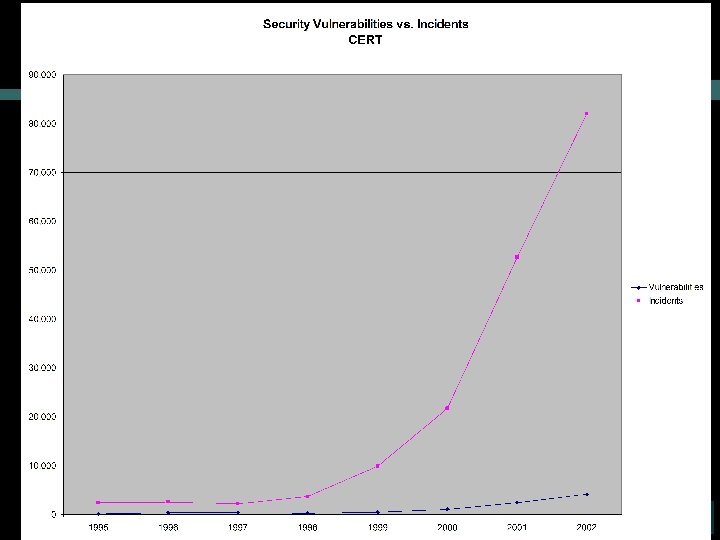
Why worry? (cont. ) mnystrom © 2004 Cisco Systems, Inc. All rights reserved. 4
The goal of an attack • Steal data • Blackmail • Beachhead for other attacks • Bragging rights • Vandalism • Demonstrate vulnerability/satisfy curiosity • Damage company reputation mnystrom © 2004 Cisco Systems, Inc. All rights reserved. 5
A word of warning • These tools and techniques can be dangerous • The difference between a hacker and a cracker is…permission • Admins will see strange activity in logs, and come looking for you • Authorities are prosecuting even the “good guys” for using these tools mnystrom © 2004 Cisco Systems, Inc. All rights reserved. 6

Commonly attacked services • SMTP servers (port 25) sendmail: “The address parser performs insufficient bounds checking in certain conditions due to a char to int conversion, making it possible for an attacker to take control of the application” • RPC servers (port 111 & others) • Net. BIOS shares (ports 135, 139, 445) Blaster worm Sasser worm • FTP servers (ports 20, 21) wuftpd vulnerabilities • SSH servers (port 22) Open. SSH, PAM vulnerabilities • Web servers (ports 80, 443) Apache chunked encoding vulnerability mnystrom © 2004 Cisco Systems, Inc. All rights reserved. 7
Web server attack • Scan to find open ports • Find out what’s running on open ports (banner grabbing) • Profile the server Windows (look for Kerberos, Net. BIOS, AD) Unix Use TCP fingerprinting • Probe for weaknesses on interesting ports Default configuration files and settings (e. g. popular IIS ones) Buffer overflows Insecure applications • Launch attack Use exploit code from Internet… …or build your own mnystrom © 2004 Cisco Systems, Inc. All rights reserved. 8
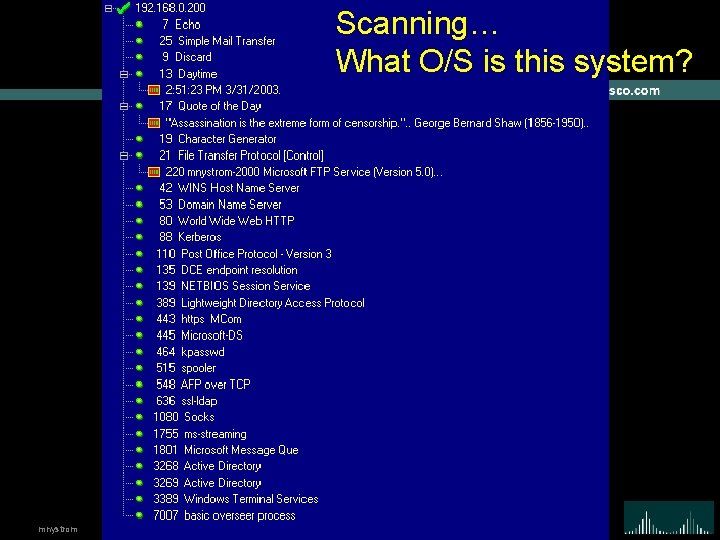
Scanning… What O/S is this system? mnystrom © 2004 Cisco Systems, Inc. All rights reserved. 9
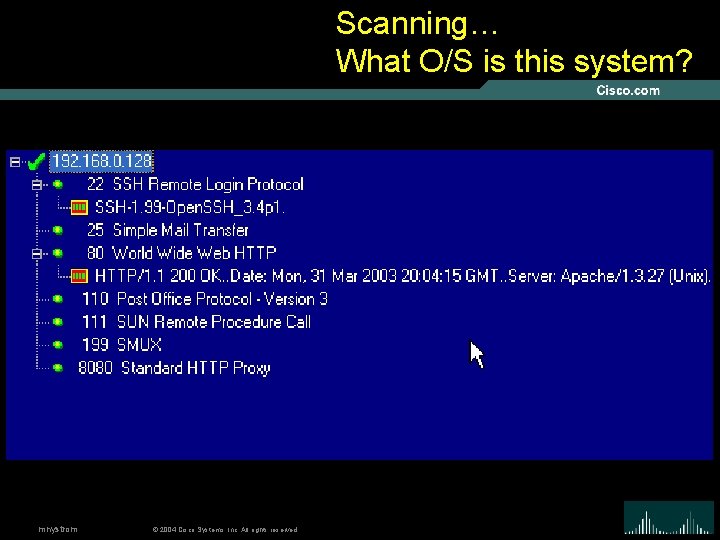
Scanning… What O/S is this system? mnystrom © 2004 Cisco Systems, Inc. All rights reserved. 10
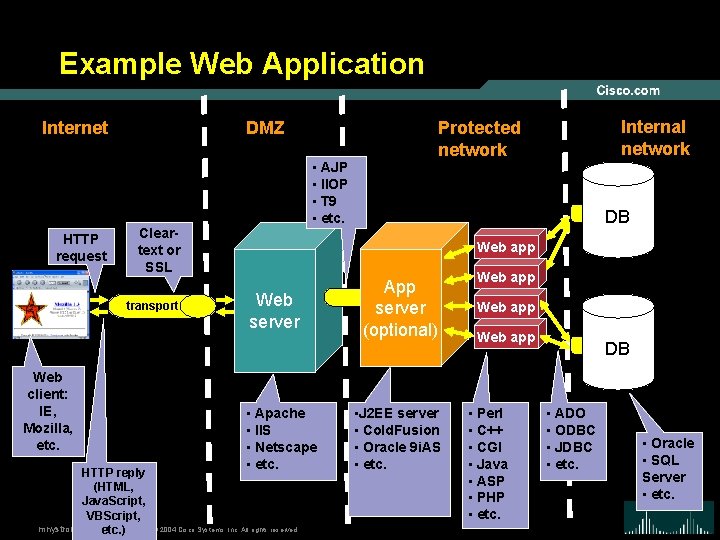
Example Web Application Internet HTTP request DMZ Cleartext or SSL transport Web client: IE, Mozilla, etc. mnystrom • AJP • IIOP • T 9 • etc. HTTP reply (HTML, Java. Script, VBScript, etc. ) Internal network Protected network DB Web app Web server • Apache • IIS • Netscape • etc. © 2004 Cisco Systems, Inc. All rights reserved. App server (optional) • J 2 EE server • Cold. Fusion • Oracle 9 i. AS • etc. Web app • Perl • C++ • CGI • Java • ASP • PHP • etc. DB • ADO • ODBC • JDBC • etc. • Oracle • SQL Server • etc. 11
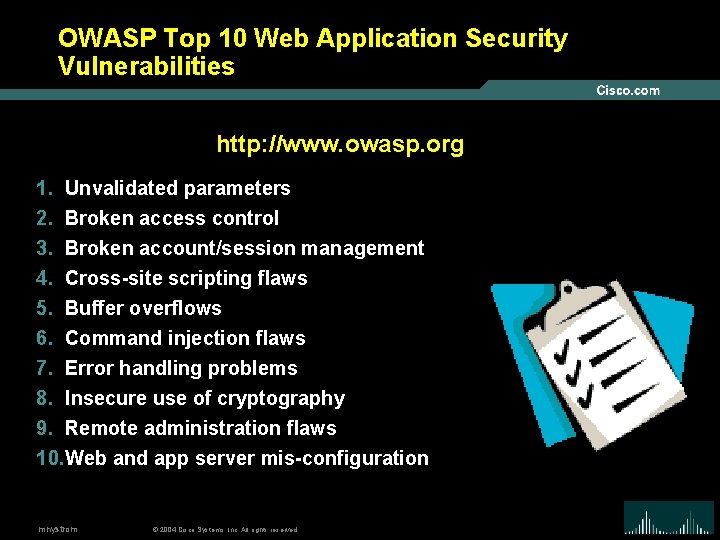
OWASP Top 10 Web Application Security Vulnerabilities http: //www. owasp. org 1. Unvalidated parameters 2. Broken access control 3. Broken account/session management 4. Cross-site scripting flaws 5. Buffer overflows 6. Command injection flaws 7. Error handling problems 8. Insecure use of cryptography 9. Remote administration flaws 10. Web and app server mis-configuration mnystrom © 2004 Cisco Systems, Inc. All rights reserved. 12
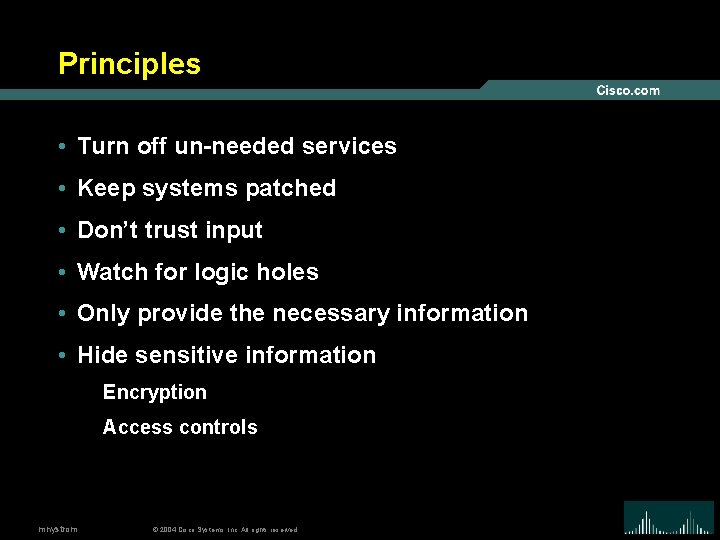
Principles • Turn off un-needed services • Keep systems patched • Don’t trust input • Watch for logic holes • Only provide the necessary information • Hide sensitive information Encryption Access controls mnystrom © 2004 Cisco Systems, Inc. All rights reserved. 13
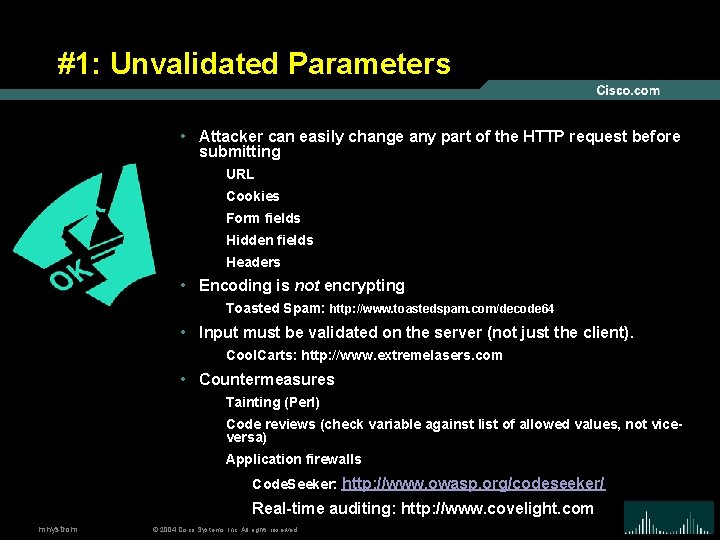
#1: Unvalidated Parameters • Attacker can easily change any part of the HTTP request before submitting URL Cookies Form fields Hidden fields Headers • Encoding is not encrypting Toasted Spam: http: //www. toastedspam. com/decode 64 • Input must be validated on the server (not just the client). Cool. Carts: http: //www. extremelasers. com • Countermeasures Tainting (Perl) Code reviews (check variable against list of allowed values, not viceversa) Application firewalls Code. Seeker: http: //www. owasp. org/codeseeker/ Real-time auditing: http: //www. covelight. com mnystrom © 2004 Cisco Systems, Inc. All rights reserved. 14
#2: Broken Access Control • Usually inconsistently defined/applied • Examples Forced browsing past access control checks Path traversal File permissions – may allow access to config/password files Client-side caching • Countermeasures Use non-programmatic controls Verify access control via central container Code reviews mnystrom © 2004 Cisco Systems, Inc. All rights reserved. 15
#3: Broken Account and Session Management • Weak authentication Password-only Easily guessable usernames (admin, etc. ) Unencrypted secrets are sniffable • How to break in Guess/reset password Have app email you new password Sniff or crack password • Backend authentication How are database passwords stored? Trust relationships between hosts (IP address can be spoofed, etc. ) • Countermeasures Strong passwords Remove default user names mnystrom © 2004 Cisco Systems, Inc. All rights reserved. Protect sensitive files 16
#4: Cross-Site Scripting (XSS) • Attacker uses trusted application/company to reflect malicious code to end-user • Attacker can “hide” the malicious code Unicode encoding • 2 types of attacks Stored Reflected • Wide-spread problem! • Countermeasures input validation Positive Negative: “< > ( ) # &” Don’t forget these: “< > ( ) # &” User/customer education mnystrom © 2004 Cisco Systems, Inc. All rights reserved. 17
#5: Buffer Overflows • Mostly affects web/app servers • Can affect apps/libraries too • Goal: crash the target app and get a shell • Buffer overflow example echo “vrfy `perl –e ‘print “a” x 1000’`” |nc www. targetsystem. com 25 Replace all those “a”s with something like this… char shellcode[] = “xebxlfx 5 ex 89x 76x 08…” • Countermeasures Keep up with bug reports/patches Code reviews Run with limited privileges Use “safer” languages like Java mnystrom © 2004 Cisco Systems, Inc. All rights reserved. 18
#6: Command Injection • Allows attacker to relay malicious code in form variables or URL System commands SQL Interpreted code (Perl, Python, etc. ) • Many apps use calls to external programs sendmail • Examples Path traversal: “. . /” Add more commands: “; rm –r *” SQL injection: “’ OR 1=1” • Countermeasures Taint all input Avoid system calls (use libraries instead) Run with limited privileges mnystrom © 2004 Cisco Systems, Inc. All rights reserved. 19
#7: Error Handling • Examples: stack traces, DB dumps • Helps attacker know how to target the app • Inconsistencies can be revealing too “File not found” vs. “Access denied” • Fail-open errors • Need to give enough info to user w/o giving too much info to attacker • Countermeasures Code review Modify default error pages (404, 401, etc. ) mnystrom © 2004 Cisco Systems, Inc. All rights reserved. 20
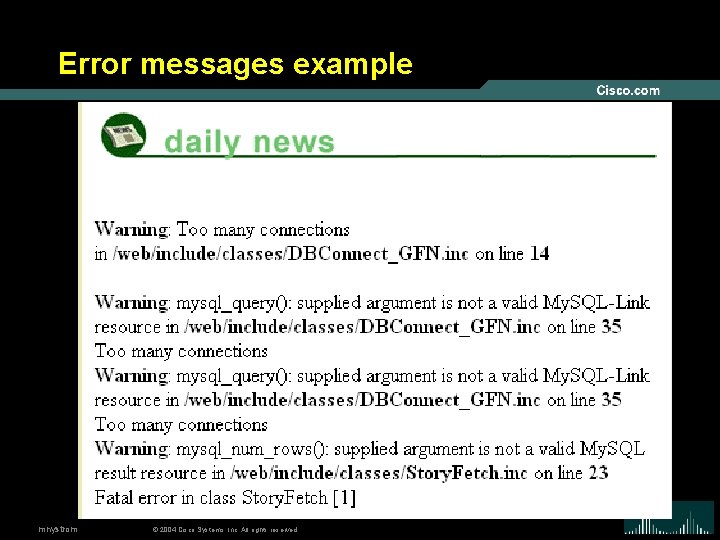
Error messages example mnystrom © 2004 Cisco Systems, Inc. All rights reserved. 21
#8: Poor Cryptography • Insecure storage of credit cards, passwords, etc. • Poor choice of algorithm (or invent your own) • Poor randomness Session IDs Tokens Cookies • Improper storage in memory • Countermeasures Store only what you must Store a hash instead of the full value (SHA-1) Use only vetted, public cryptography mnystrom © 2004 Cisco Systems, Inc. All rights reserved. 22
#9: Remote Administration Flaws • Problems Weak authentication (username=“admin”) Weak encryption • Countermeasures Don’t place admin interface on same server Use strong authentication: certificates, tokens, strong passwords, etc. Encrypt entire session (VPN or SSL) Control who has accounts IP restrictions mnystrom © 2004 Cisco Systems, Inc. All rights reserved. 23
#10: Web/App Server Misconfiguration • Tension between “work out of the box” and “use only what you need” • Developers ≠ web masters • Examples Unpatched security flaws (BID example) Misconfigurations that allow directory traversal Administrative services accessible Default accounts/passwords • Countermeasures Create and use hardening guides Turn off all unused services Set up and audit roles, permissions, and accounts Set up logging and alerts mnystrom © 2004 Cisco Systems, Inc. All rights reserved. 24
Principles • Turn off un-needed services • Keep systems patched • Don’t trust input • Watch for logic holes • Only provide the necessary information • Hide sensitive information Encryption Access controls mnystrom © 2004 Cisco Systems, Inc. All rights reserved. 25
Tools used in this preso • Web. Goat –vulnerable web applications for demonstration • VMWare – runs Linux & Windows 2000 virtual machines on demo laptop. • nmap –host/port scanning to find vulnerable hosts • Ethereal – network traffic sniffing • Metasploit Framework – exploit tool • Brutus – password cracking • Sleuth – HTTP mangling against web sites mnystrom © 2004 Cisco Systems, Inc. All rights reserved. 26
- Slides: 26