Web Applications and JAAS Dan Moore Consultant Seurat
Web Applications and JAAS Dan Moore Consultant Seurat Company July 11, 2002 9/25/2020 1 © 2002, Seurat Company
Introduction • Overview of Struts • Java Authentication and Authorization Service (JAAS) • JAAS Authentication • Integration with Struts • Default JAAS Authorization • Integration with Struts • Situations where JAAS is useful/not useful • About my experience 9/25/2020 2 © 2002, Seurat Company
What do you want? • How many are building web applications • Using Struts or other lightweight framework • Using ATG Dynamo, Websphere or other heavy framework • Heard of Struts • Played with Struts • Heard of JAAS • Played with JAAS • Questions please 9/25/2020 3 © 2002, Seurat Company
Motivation • Authentication and Authorization are plumbing • Re-invent or re-learn the wheel • Re-learn once or many times • Concepts from bright people • Future integration with app servers • Resume 9/25/2020 4 © 2002, Seurat Company

Struts • • What is Struts Architecture Sample Struts-config. xml Example application 9/25/2020 5 © 2002, Seurat Company
What is Struts • Web application framework • MVC (almost) • Lightweight • Few services provided • Open Source jakarta project • Apache license 9/25/2020 6 © 2002, Seurat Company
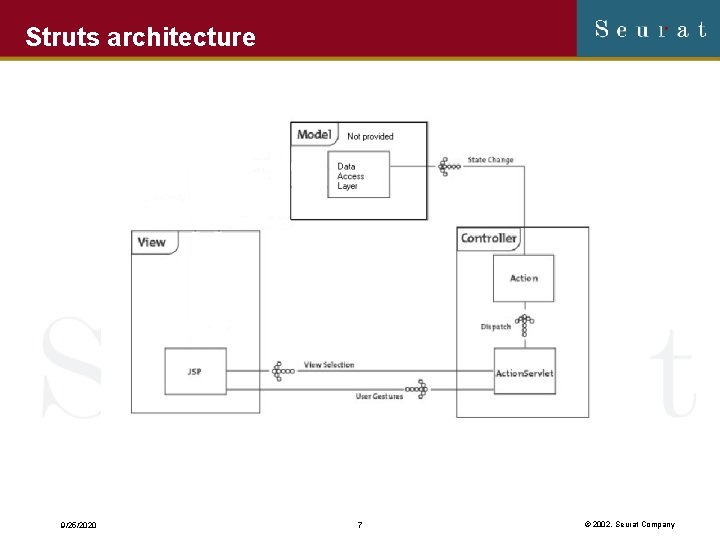
Struts architecture 9/25/2020 7 © 2002, Seurat Company
Show Struts-config. xml 9/25/2020 8 © 2002, Seurat Company
Demo Untouched Example Application 9/25/2020 9 © 2002, Seurat Company
What is JAAS • Interfaces and classes for standard authentication and authorization • Lightweight & Pluggable • Really two separate APIs • Authentication • Authorization • Which depends on Authentication • JDK 1. 3. x supplemental jar and now part of 1. 4 JDK 9/25/2020 10 © 2002, Seurat Company
Authentication • • • Definitions Configuration Typical use Integration with example application Code 9/25/2020 11 © 2002, Seurat Company
Definitions • • • User Subject Principal Login module set 9/25/2020 12 © 2002, Seurat Company
Show Authentication Configuration File 9/25/2020 13 © 2002, Seurat Company
Show Authentication Password File 9/25/2020 14 © 2002, Seurat Company
Configuration of Authentication • Configuration file • Tokens in configuration file • Required/optional/sufficient/necessary • Can replace class that reads this file • Tagish Login Module • File based • GPL • Could write your own, see resources • JVM awareness • 1. 3 class loader issues • System property: java. security. auth. login. config • java. security file 9/25/2020 15 © 2002, Seurat Company
Typical Use • Create Login. Context • Login module set name • Callbackhandler • Interact with User • Try to login • May repeat if need be • If login successful, Subject is an attribute of Login. Context • If login unsuccessful, exception thrown 9/25/2020 16 © 2002, Seurat Company
Integration of Authentication with Example application • Struts defers to adapter • Converts exceptions to boolean • Callbackhandler weirdness • Struts caches Subject in session • 377 bytes in size 9/25/2020 17 © 2002, Seurat Company
Show Struts calling Adapter and Adapter 9/25/2020 18 © 2002, Seurat Company
Authorization • • Caveat Definitions Java security Configuration Typical Use Integration with example application Code 9/25/2020 19 © 2002, Seurat Company
Caveat • This is the default authorization scheme • It has blemishes • Can plug in your own via java. security file, see resources 9/25/2020 20 © 2002, Seurat Company
Definitions • Resource • Permission • Three components • Class, resource and action • java. io. File. Permission “/tmp” “read” • Basic permission/Permission • Principals • Security Manager 9/25/2020 21 © 2002, Seurat Company
Java security model • How many are familiar? • Based on permissions and resources • Code based • Permissions granted to code based on • a given location (jar, URL) • Signer of code • Permission stack • Class A calls class B calls class C… • JAAS extends to include Subject executing code 9/25/2020 22 © 2002, Seurat Company
Show Authorization Configuration File 9/25/2020 23 © 2002, Seurat Company
Configuration of Authorization • In some respects, similar to authentication • Configuration file • Based on java security model. • Subject must have every principal to access resource • Wild cards possible • But not null subjects • Can replace class which reads this file • Tell JVM where security configuration file lives • java. security • Multiple, unioned • Command line: java. security. auth. policy 9/25/2020 24 © 2002, Seurat Company
Typical Use • Install/get security manager • Before allowing access to resource, check with security manager • All java classes that guard resources do this • Subject. do. As. Privileged(subject, object wrapper of access, access context) 9/25/2020 25 © 2002, Seurat Company
Integration with example application • Treat URLs as resources • Basic permission, but in real app would want real Permission • Subclass Action. Servlet • Only resources Action. Servlet controls are protected • Alternative—servlet filters • Call off to utility class • Special handling of login page 9/25/2020 26 © 2002, Seurat Company
Show Struts calling Authorization Utility 9/25/2020 27 © 2002, Seurat Company
Places to extend Authorization • Protect not only URLs but content as well • taglib • Increase configuration file scalability • Permission class that “understands” URLs • HTTP/HTTPS delineation • Would love an Open Source jar • Code emphasis not repairable 9/25/2020 28 © 2002, Seurat Company
Demo Modified Application 9/25/2020 29 © 2002, Seurat Company
Conclusion • On pluggability • Situations where JAAS is a good fit • Situations where JAAS is not 9/25/2020 30 © 2002, Seurat Company
Pluggability • Overused term • 2 kinds of pluggability • Class which reads configuration • Configuration file itself • Login modules • Permissions 9/25/2020 31 © 2002, Seurat Company
Where JAAS looks useful • You have different authentication systems that need to look the same • Lightweight framework • You have complex authentication systems • Authorization is something you have time to rework 9/25/2020 32 © 2002, Seurat Company
Where JAAS should be avoided • Pre JDK 1. 3 projects • If there’s already a heavyweight framework available • Unless you want to tackle the integration issues • If authorization is problematic and you don’t have time to fix it. 9/25/2020 33 © 2002, Seurat Company
Finally • For web applications, I feel • Authentication is ready • Authorization is not • JAAS may not be good fit • Doesn’t integrate with application servers out there presently • Similar to servlet specification • Should be implemented by vendors 9/25/2020 34 © 2002, Seurat Company
Resources • • Struts: • http: //jakarta. apache. org/struts Write your own login module: • http: //java. sun. com/security/jaas/doc/module. html Pick up some free ones • http: //free. tagish. net/jaas/doc. html Java security • Java Security by Scott Oaks Write your own authentication system: • http: //www-106. ibm. com/developerworks/library/j-jaas/? n-j-442 Paper this talk is based upon: • http: //mooreds. com/jaas. html Sample code that works with struts • http: //mooreds. com/jaas-example. tar. gz 9/25/2020 35 © 2002, Seurat Company
Thanks • Seurat nee XOR • Reviewers • Tom Malaher • Dion Almaer • Brian Pontarelli • Kris Thompson • Steven Sweeting, Clive Jones, and Aaron Rustad • Basis of struts arch diagram 9/25/2020 36 © 2002, Seurat Company
- Slides: 36