Web Application Security SE2840 Dr Mark L Hornick

Web Application Security SE-2840 Dr. Mark L. Hornick 1
There are three main security concerns your web apps need to address l Impersonation l l Upgrading l l A client pretends to be someone else in order to gain access to your site A client gains access to restricted aspects of your web app Eavesdropping l A third-party gains access to confidential information exchanged between your site and a valid user SE-2840 Dr. Mark L. Hornick 2
All of these can be managed via the Deployment Descriptor Tomcat incorporates a declarative security model that requires no changes to your Servlets or pages Tomcat itself handles Authentication, Authorization, and Data Encryption SE-2840 Dr. Mark L. Hornick 3
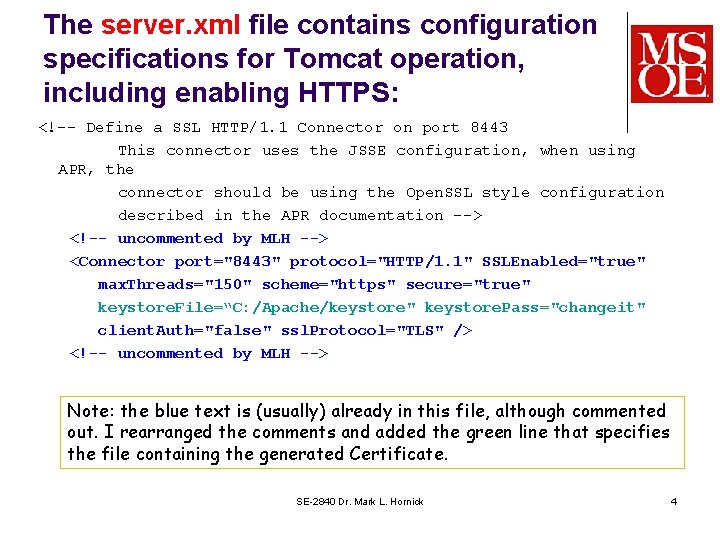
The server. xml file contains configuration specifications for Tomcat operation, including enabling HTTPS: <!-- Define a SSL HTTP/1. 1 Connector on port 8443 This connector uses the JSSE configuration, when using APR, the connector should be using the Open. SSL style configuration described in the APR documentation --> <!-- uncommented by MLH --> <Connector port="8443" protocol="HTTP/1. 1" SSLEnabled="true" max. Threads="150" scheme="https" secure="true" keystore. File=“C: /Apache/keystore" keystore. Pass="changeit" client. Auth="false" ssl. Protocol="TLS" /> <!-- uncommented by MLH --> Note: the blue text is (usually) already in this file, although commented out. I rearranged the comments and added the green line that specifies the file containing the generated Certificate. SE-2840 Dr. Mark L. Hornick 4
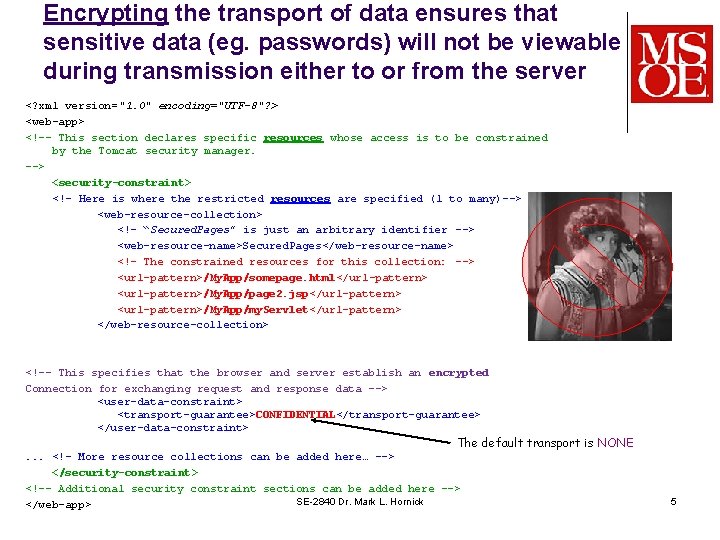
Encrypting the transport of data ensures that sensitive data (eg. passwords) will not be viewable during transmission either to or from the server <? xml version="1. 0" encoding="UTF-8"? > <web-app> <!-- This section declares specific resources whose access is to be constrained by the Tomcat security manager. --> <security-constraint> <!– Here is where the restricted resources are specified (1 to many)--> <web-resource-collection> <!– “Secured. Pages” is just an arbitrary identifier --> <web-resource-name>Secured. Pages</web-resource-name> <!– The constrained resources for this collection: --> <url-pattern>/My. App/somepage. html</url-pattern> <url-pattern>/My. App/page 2. jsp</url-pattern> <url-pattern>/My. App/my. Servlet</url-pattern> </web-resource-collection> <!-- This specifies that the browser and server establish an encrypted Connection for exchanging request and response data --> <user-data-constraint> <transport-guarantee>CONFIDENTIAL</transport-guarantee> </user-data-constraint> The default transport is NONE . . . <!– More resource collections can be added here… --> </security-constraint> <!-- Additional security constraint sections can be added here --> SE-2840 Dr. Mark L. Hornick </web-app> 5
Demo SE-2840 Dr. Mark L. Hornick 6
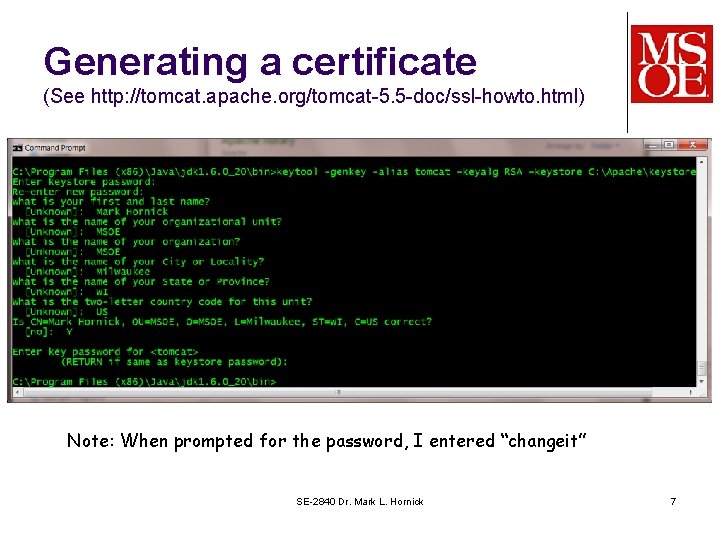
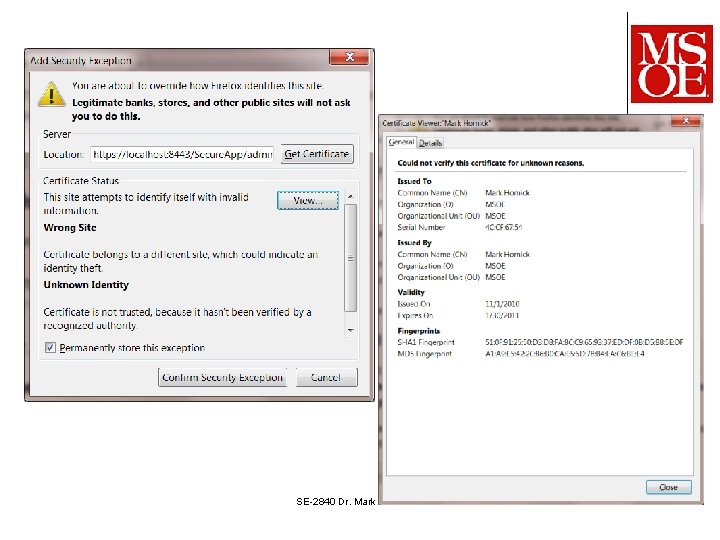
Generating a certificate (See http: //tomcat. apache. org/tomcat-5. 5 -doc/ssl-howto. html) Note: When prompted for the password, I entered “changeit” SE-2840 Dr. Mark L. Hornick 7
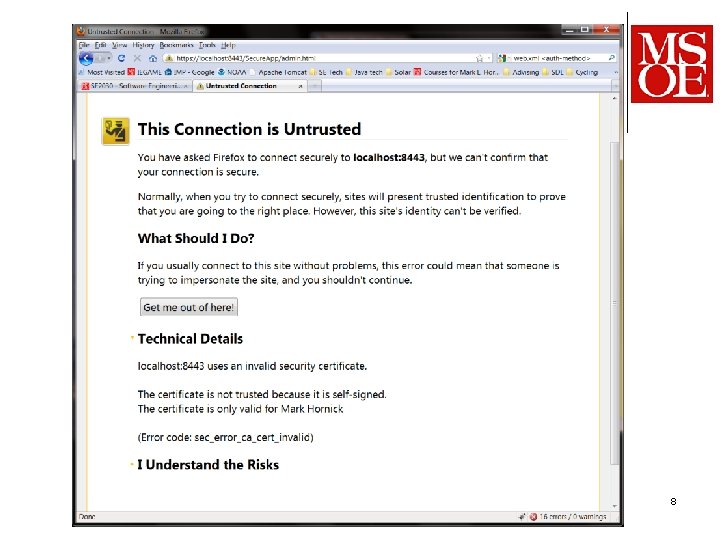
CS-4220 Dr. Mark L. Hornick 8
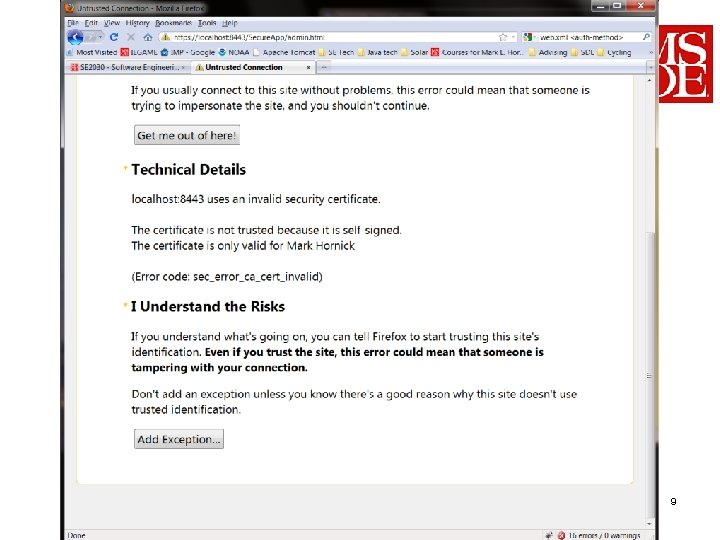
CS-4220 Dr. Mark L. Hornick 9
SE-2840 Dr. Mark L. Hornick 10
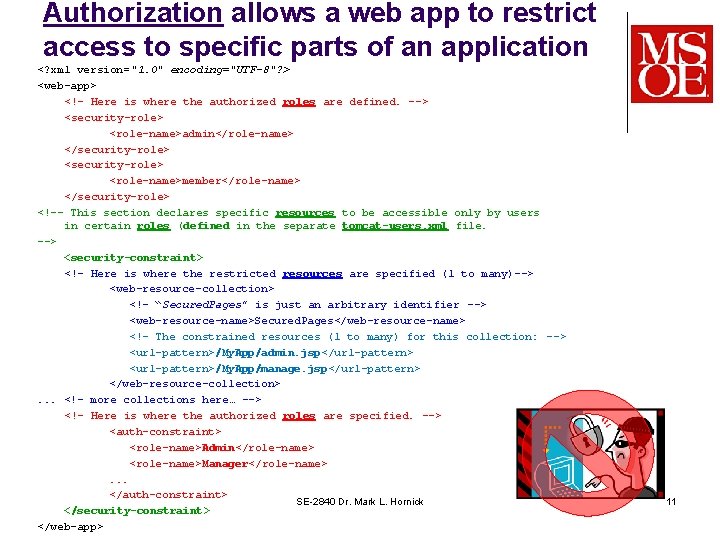
Authorization allows a web app to restrict access to specific parts of an application <? xml version="1. 0" encoding="UTF-8"? > <web-app> <!– Here is where the authorized roles are defined. --> <security-role> <role-name>admin</role-name> </security-role> <role-name>member</role-name> </security-role> <!-- This section declares specific resources to be accessible only by users in certain roles (defined in the separate tomcat-users. xml file. --> <security-constraint> <!– Here is where the restricted resources are specified (1 to many)--> <web-resource-collection> <!– “Secured. Pages” is just an arbitrary identifier --> <web-resource-name>Secured. Pages</web-resource-name> <!– The constrained resources (1 to many) for this collection: --> <url-pattern>/My. App/admin. jsp</url-pattern> <url-pattern>/My. App/manage. jsp</url-pattern> </web-resource-collection>. . . <!– more collections here… --> <!– Here is where the authorized roles are specified. --> <auth-constraint> <role-name>Admin</role-name> <role-name>Manager</role-name>. . . </auth-constraint> SE-2840 Dr. Mark L. Hornick </security-constraint> </web-app> 11
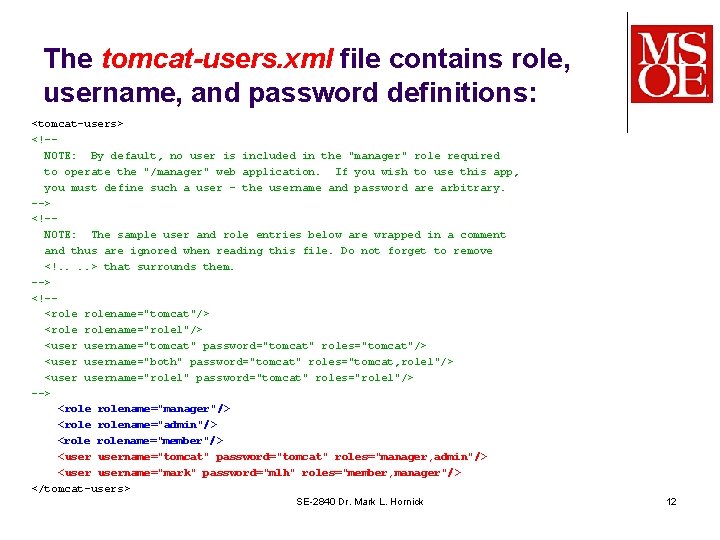
The tomcat-users. xml file contains role, username, and password definitions: <tomcat-users> <!-NOTE: By default, no user is included in the "manager" role required to operate the "/manager" web application. If you wish to use this app, you must define such a user - the username and password are arbitrary. --> <!-NOTE: The sample user and role entries below are wrapped in a comment and thus are ignored when reading this file. Do not forget to remove <!. . > that surrounds them. --> <!-<rolename="tomcat"/> <rolename="role 1"/> <username="tomcat" password="tomcat" roles="tomcat"/> <username="both" password="tomcat" roles="tomcat, role 1"/> <username="role 1" password="tomcat" roles="role 1"/> --> <rolename="manager"/> <rolename="admin"/> <rolename="member"/> <username="tomcat" password="tomcat" roles="manager, admin"/> <username="mark" password="mlh" roles="member, manager"/> </tomcat-users> SE-2840 Dr. Mark L. Hornick 12
Demo SE-2840 Dr. Mark L. Hornick 13
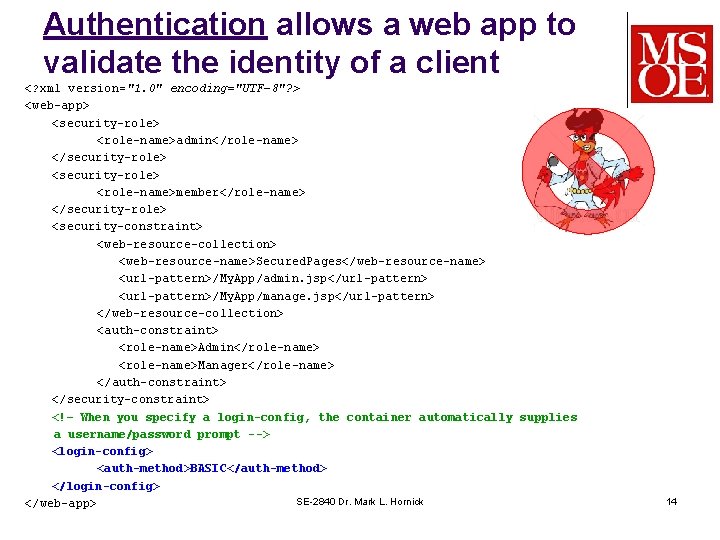
Authentication allows a web app to validate the identity of a client <? xml version="1. 0" encoding="UTF-8"? > <web-app> <security-role> <role-name>admin</role-name> </security-role> <role-name>member</role-name> </security-role> <security-constraint> <web-resource-collection> <web-resource-name>Secured. Pages</web-resource-name> <url-pattern>/My. App/admin. jsp</url-pattern> <url-pattern>/My. App/manage. jsp</url-pattern> </web-resource-collection> <auth-constraint> <role-name>Admin</role-name> <role-name>Manager</role-name> </auth-constraint> </security-constraint> <!– When you specify a login-config, the container automatically supplies a username/password prompt --> <login-config> <auth-method>BASIC</auth-method> </login-config> SE-2840 Dr. Mark L. Hornick </web-app> 14
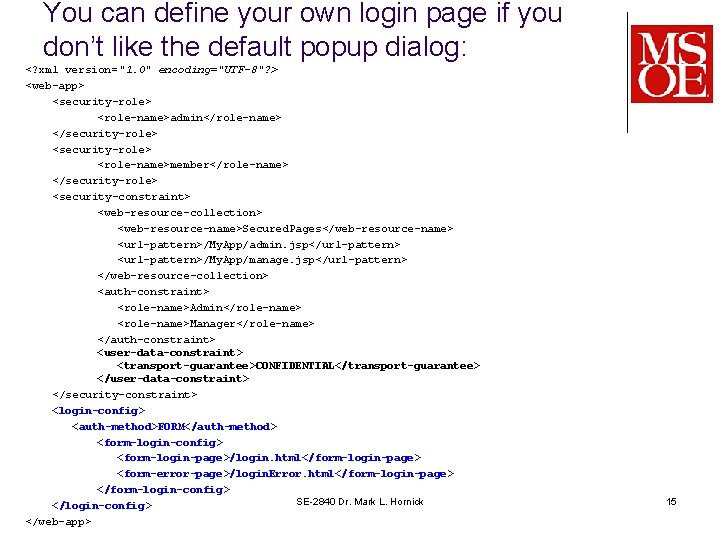
You can define your own login page if you don’t like the default popup dialog: <? xml version="1. 0" encoding="UTF-8"? > <web-app> <security-role> <role-name>admin</role-name> </security-role> <role-name>member</role-name> </security-role> <security-constraint> <web-resource-collection> <web-resource-name>Secured. Pages</web-resource-name> <url-pattern>/My. App/admin. jsp</url-pattern> <url-pattern>/My. App/manage. jsp</url-pattern> </web-resource-collection> <auth-constraint> <role-name>Admin</role-name> <role-name>Manager</role-name> </auth-constraint> <user-data-constraint> <transport-guarantee>CONFIDENTIAL</transport-guarantee> </user-data-constraint> </security-constraint> <login-config> <auth-method>FORM</auth-method> <form-login-config> <form-login-page>/login. html</form-login-page> <form-error-page>/login. Error. html</form-login-page> </form-login-config> SE-2840 Dr. Mark L. Hornick </login-config> </web-app> 15
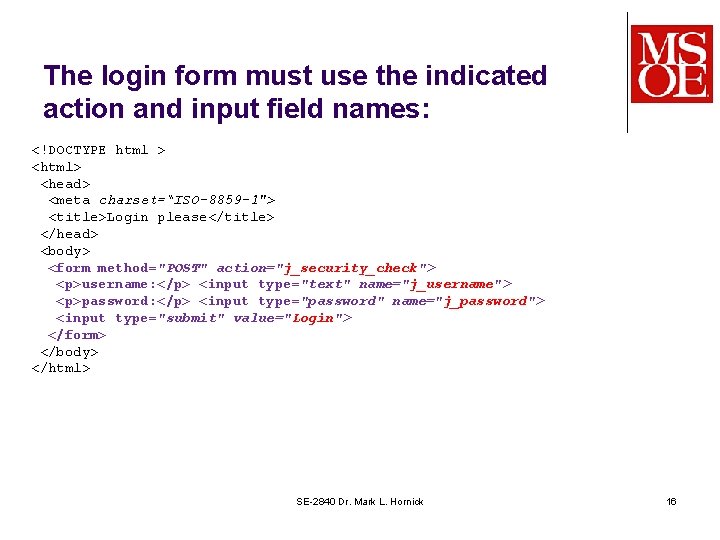
The login form must use the indicated action and input field names: <!DOCTYPE html > <html> <head> <meta charset=“ISO-8859 -1"> <title>Login please</title> </head> <body> <form method="POST" action="j_security_check"> <p>username: </p> <input type="text" name="j_username"> <p>password: </p> <input type="password" name="j_password"> <input type="submit" value="Login"> </form> </body> </html> SE-2840 Dr. Mark L. Hornick 16
- Slides: 16