Web 2 0 Security James Walden Northern Kentucky
Web 2. 0 Security James Walden Northern Kentucky University
Speaker Biography Assistant Professor at NKU l Graduate certificate in Secure Software Eng. l Minors in Infosec and Forensics. l Papers & workshops in software security. Contributor to l SANS/CWE Top 25 programming flaws. l SANS GSSP secure programmer cert. l OWASP/Fortify Open Source Review.
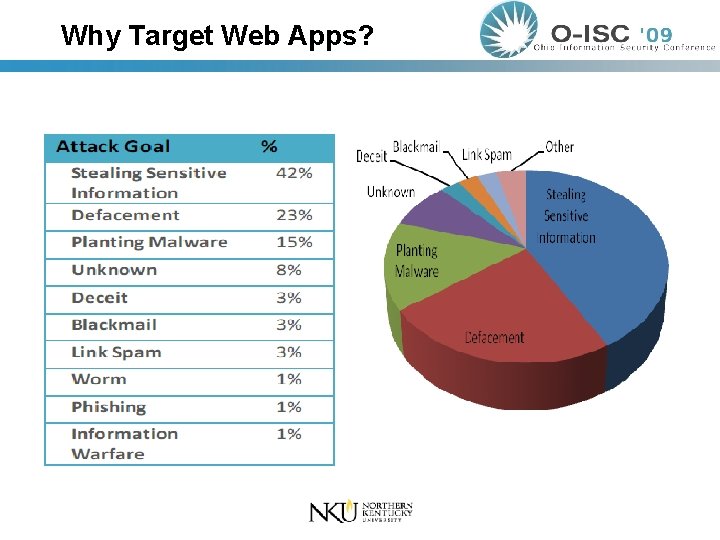
Why Target Web Apps?
Attack Surface A system’s attack surface consists of all of the ways an adversary can enter the system. Merchant’s Bank Building
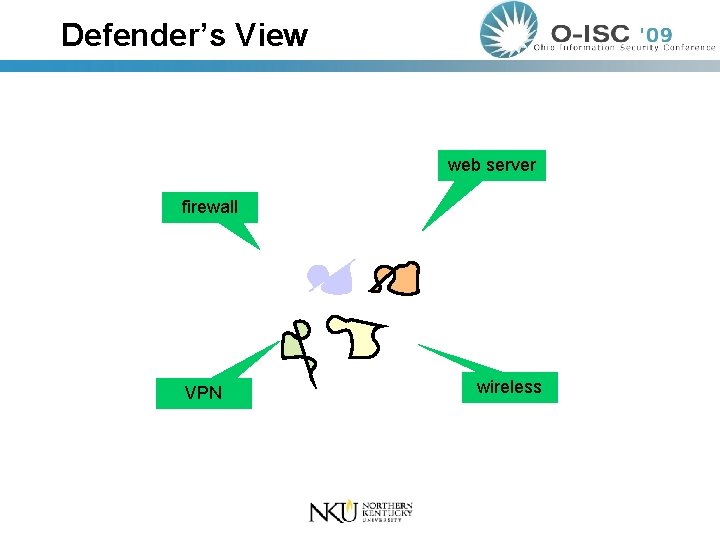
Defender’s View web server firewall VPN wireless
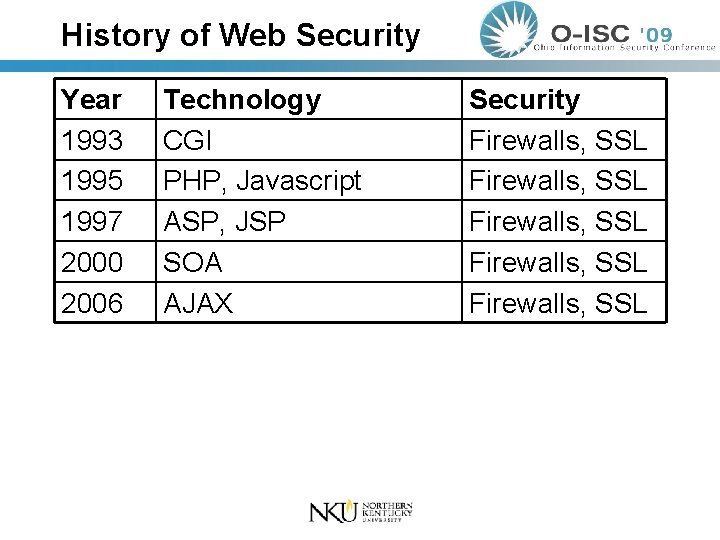
History of Web Security Year 1993 1995 1997 2000 2006 Technology CGI PHP, Javascript ASP, JSP SOA AJAX Security Firewalls, SSL Firewalls, SSL
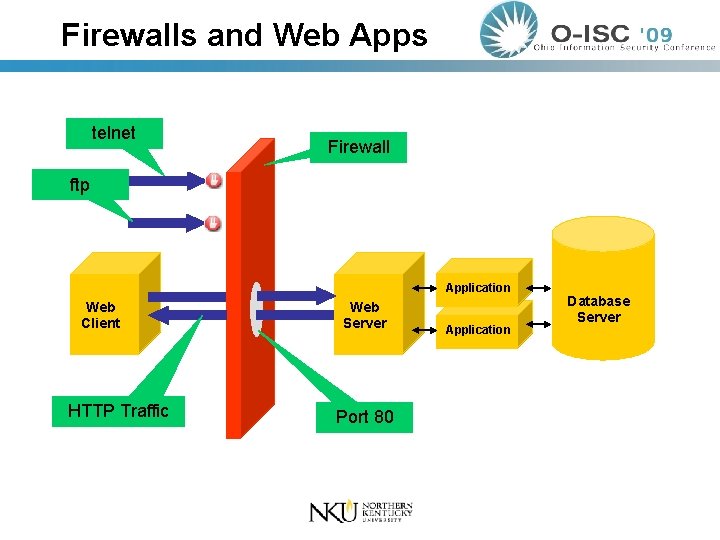
Firewalls and Web Apps telnet Firewall ftp Application Web Client HTTP Traffic Web Server Port 80 Application Database Server
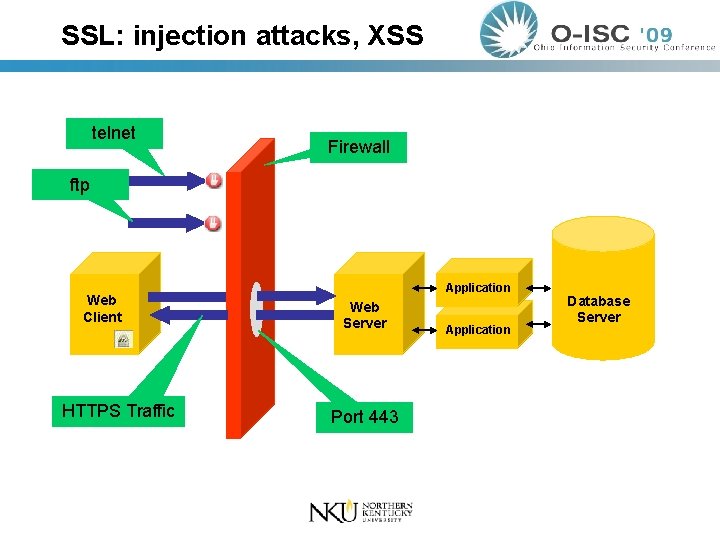
SSL: injection attacks, XSS telnet Firewall ftp Web Client HTTPS Traffic Application Web Server Port 443 Application Database Server
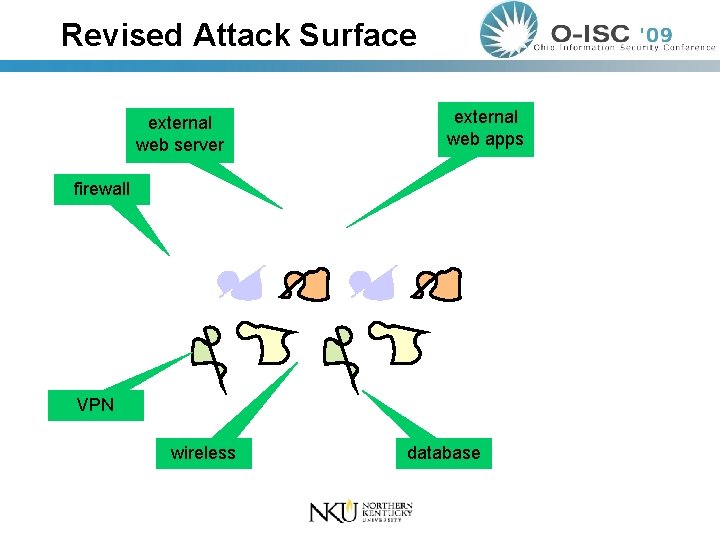
Revised Attack Surface external web server external web apps firewall VPN wireless database
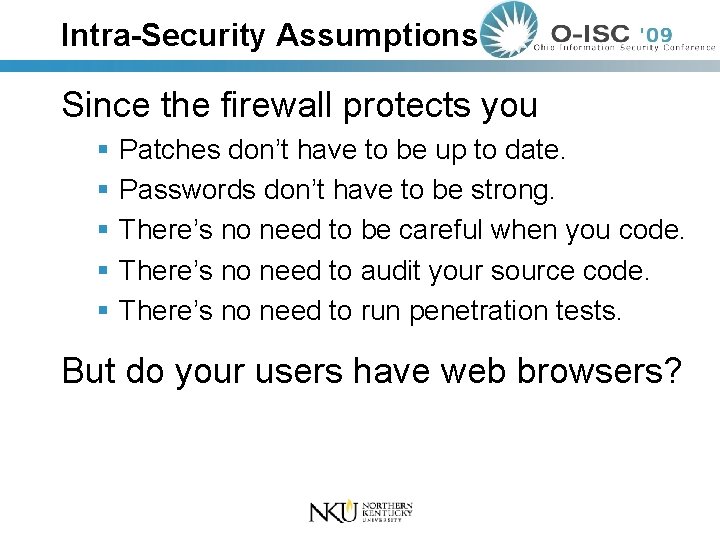
Intra-Security Assumptions Since the firewall protects you Patches don’t have to be up to date. Passwords don’t have to be strong. There’s no need to be careful when you code. There’s no need to audit your source code. There’s no need to run penetration tests. But do your users have web browsers?
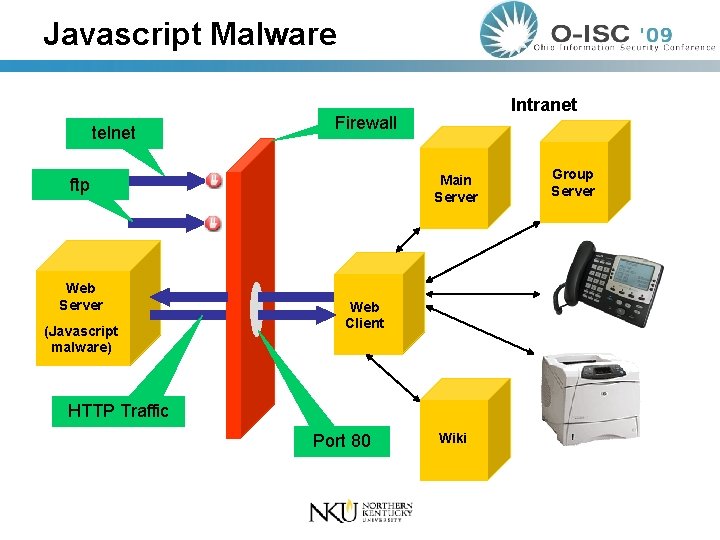
Javascript Malware telnet Firewall Main Server ftp Web Server (Javascript malware) Intranet Web Client HTTP Traffic Port 80 Wiki Group Server

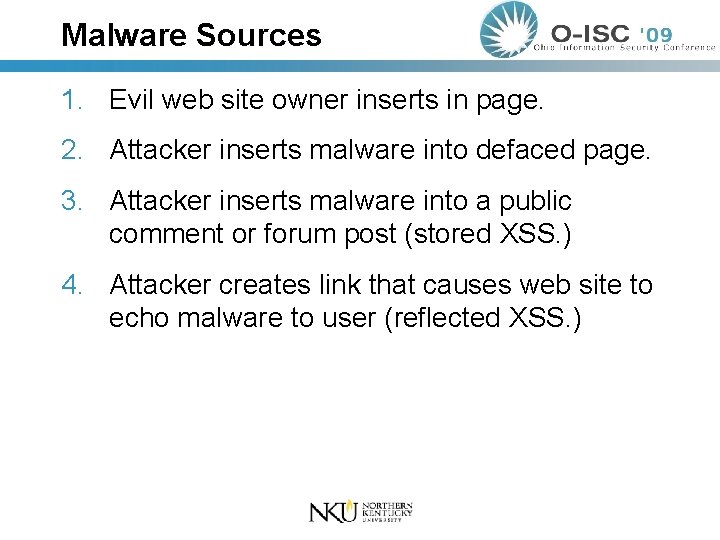
Malware Sources 1. Evil web site owner inserts in page. 2. Attacker inserts malware into defaced page. 3. Attacker inserts malware into a public comment or forum post (stored XSS. ) 4. Attacker creates link that causes web site to echo malware to user (reflected XSS. )
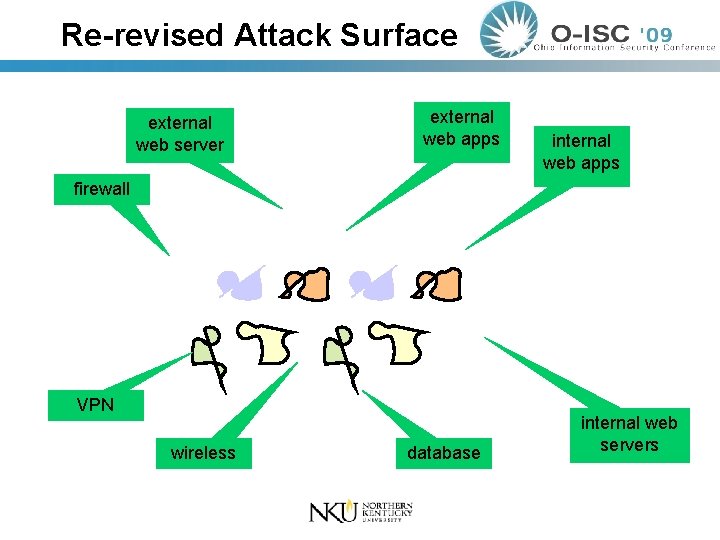
Re-revised Attack Surface external web server external web apps internal web apps firewall VPN wireless database internal web servers
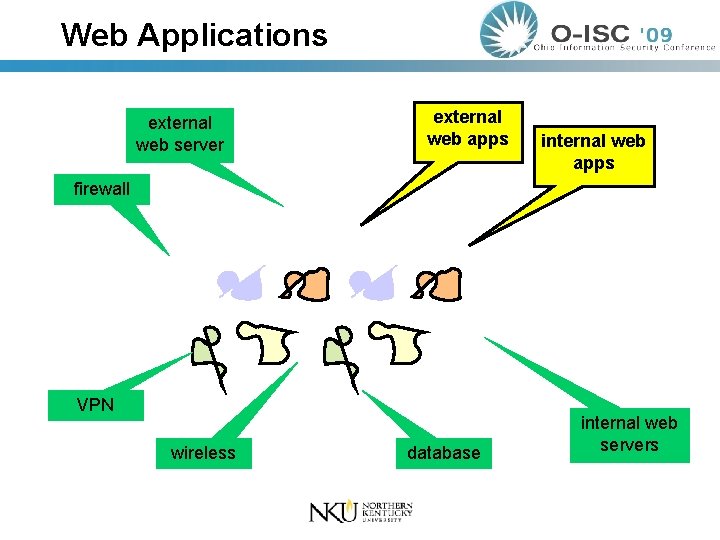
Web Applications external web server external web apps internal web apps firewall VPN wireless database internal web servers
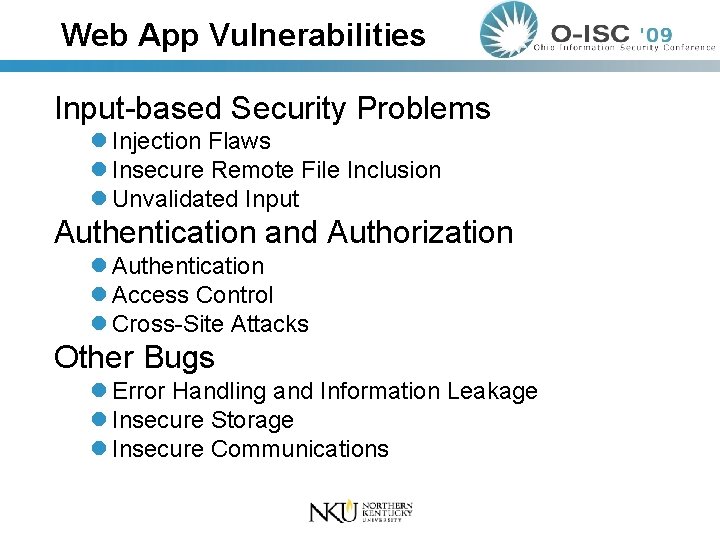
Web App Vulnerabilities Input-based Security Problems l Injection Flaws l Insecure Remote File Inclusion l Unvalidated Input Authentication and Authorization l Authentication l Access Control l Cross-Site Attacks Other Bugs l Error Handling and Information Leakage l Insecure Storage l Insecure Communications
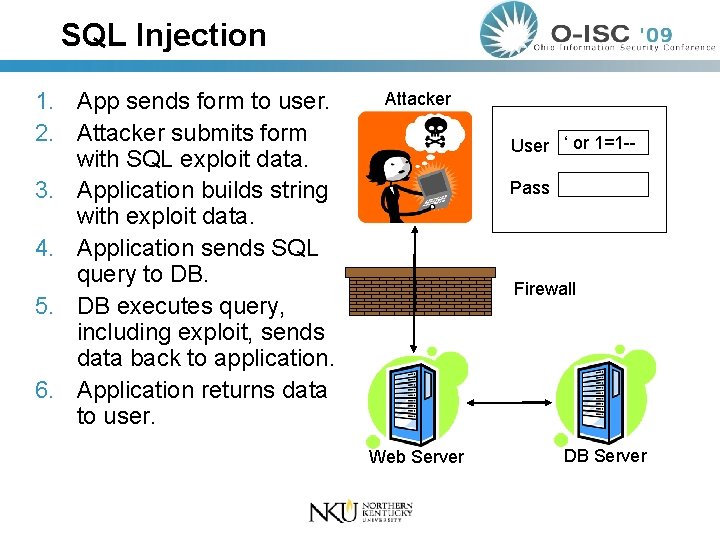
SQL Injection 1. App sends form to user. 2. Attacker submits form with SQL exploit data. 3. Application builds string with exploit data. 4. Application sends SQL query to DB. 5. DB executes query, including exploit, sends data back to application. 6. Application returns data to user. Attacker User ‘ or 1=1 -Pass Firewall Web Server DB Server
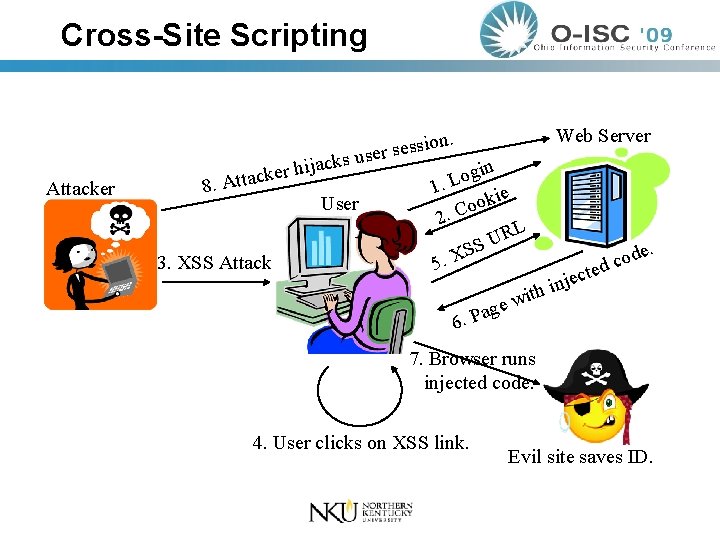
Cross-Site Scripting Attacker ijac h r e k c tta 8. A ks User 3. XSS Attack Web Server ion. s s e s r use gin o L 1. ie k o o 2. C RL U SS X. 5 te jec n i th . de o c d i 6. ew g a P 7. Browser runs injected code. 4. User clicks on XSS link. Evil site saves ID.
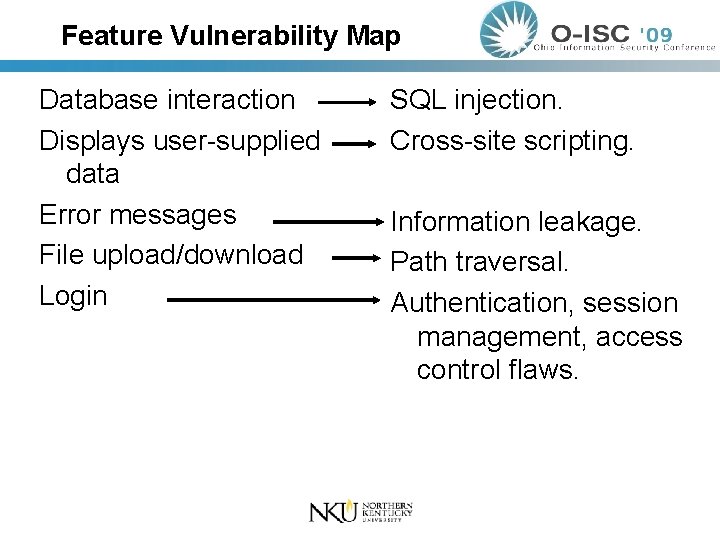
Feature Vulnerability Map Database interaction Displays user-supplied data Error messages File upload/download Login SQL injection. Cross-site scripting. Information leakage. Path traversal. Authentication, session management, access control flaws.
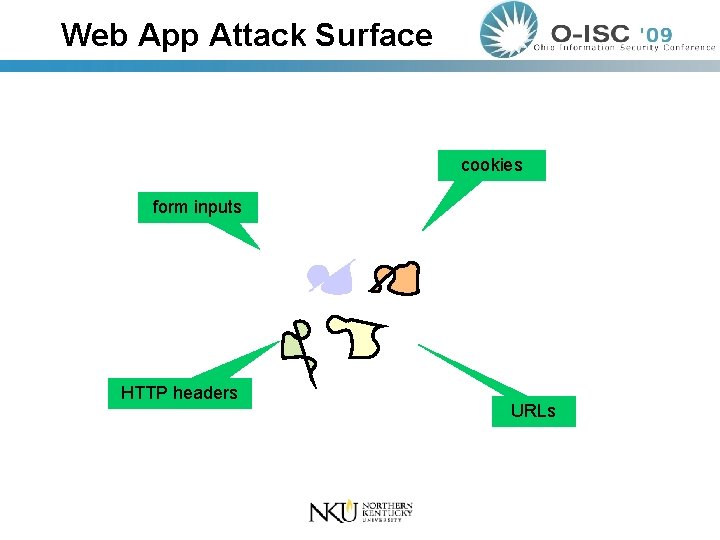
Web App Attack Surface cookies form inputs HTTP headers URLs
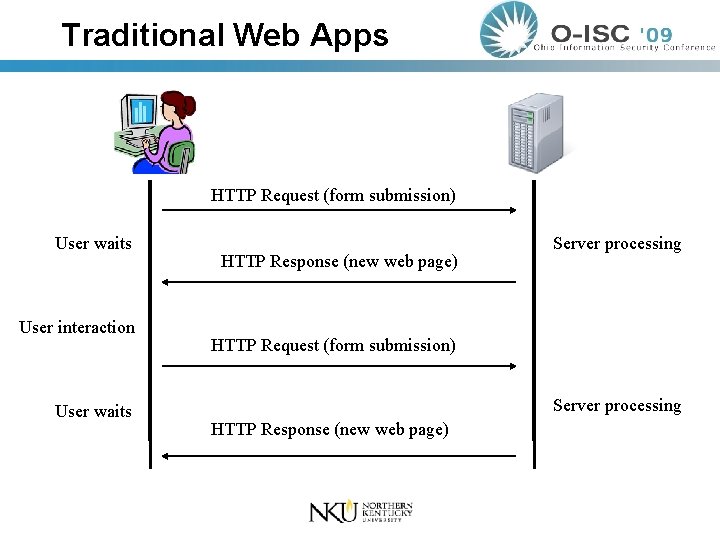
Traditional Web Apps HTTP Request (form submission) User waits User interaction User waits HTTP Response (new web page) Server processing HTTP Request (form submission) Server processing HTTP Response (new web page)
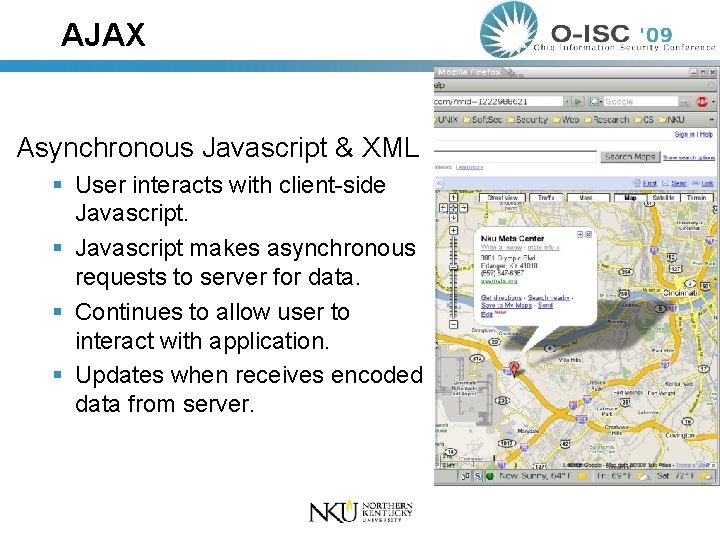
AJAX Asynchronous Javascript & XML User interacts with client-side Javascript makes asynchronous requests to server for data. Continues to allow user to interact with application. Updates when receives encoded data from server.
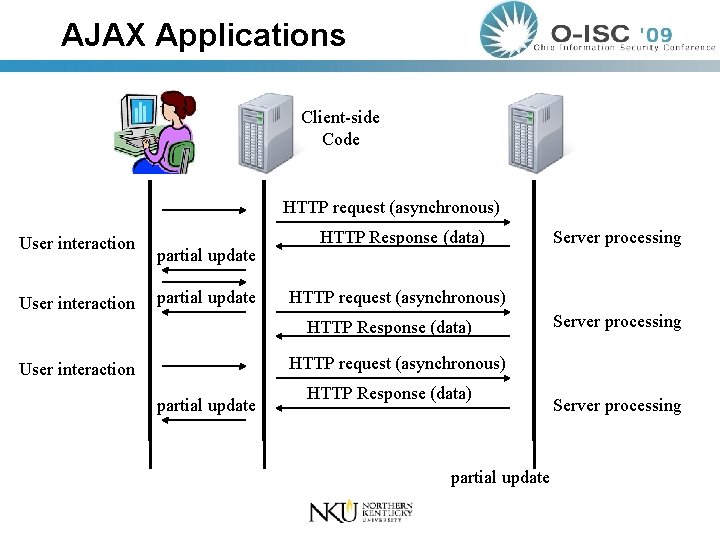
AJAX Applications Client-side Code HTTP request (asynchronous) User interaction partial update HTTP Response (data) Server processing HTTP request (asynchronous) User interaction partial update HTTP Response (data) partial update Server processing
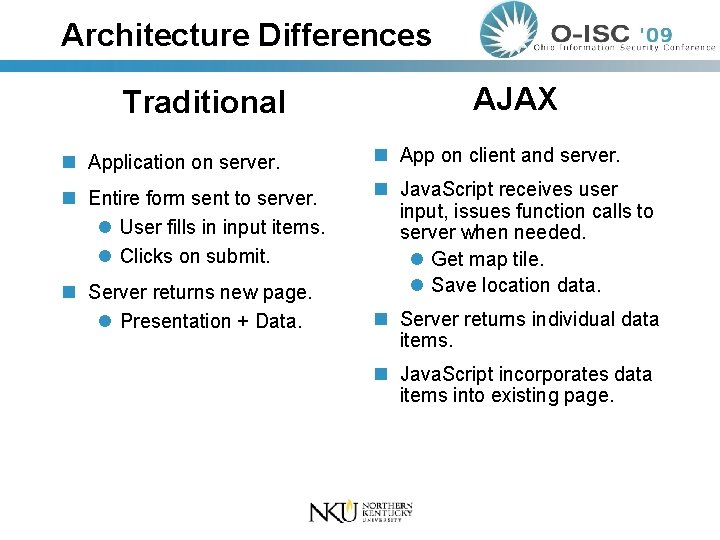
Architecture Differences Traditional AJAX n Application on server. n App on client and server. n Entire form sent to server. l User fills in input items. l Clicks on submit. n Java. Script receives user input, issues function calls to server when needed. l Get map tile. l Save location data. n Server returns new page. l Presentation + Data. n Server returns individual data items. n Java. Script incorporates data items into existing page.
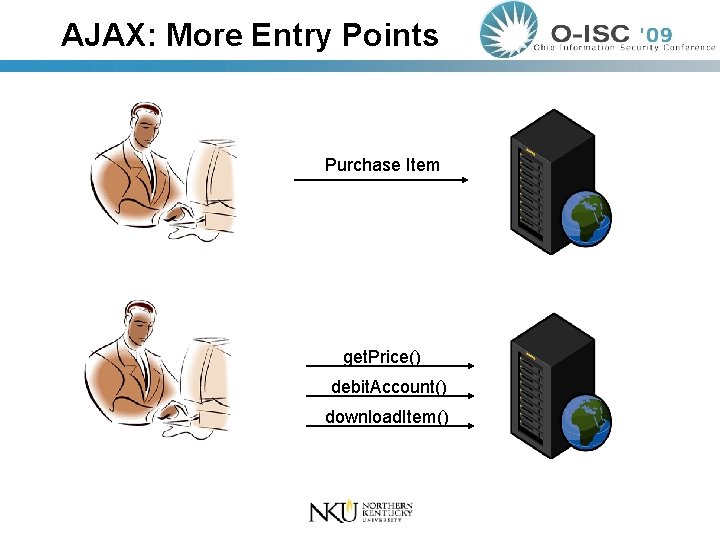
AJAX: More Entry Points Purchase Item get. Price() debit. Account() download. Item()
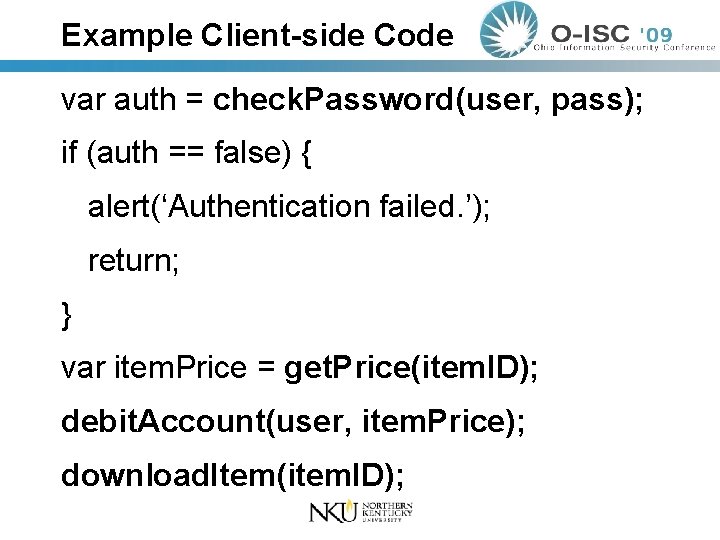
Example Client-side Code var auth = check. Password(user, pass); if (auth == false) { alert(‘Authentication failed. ’); return; } var item. Price = get. Price(item. ID); debit. Account(user, item. Price); download. Item(item. ID);
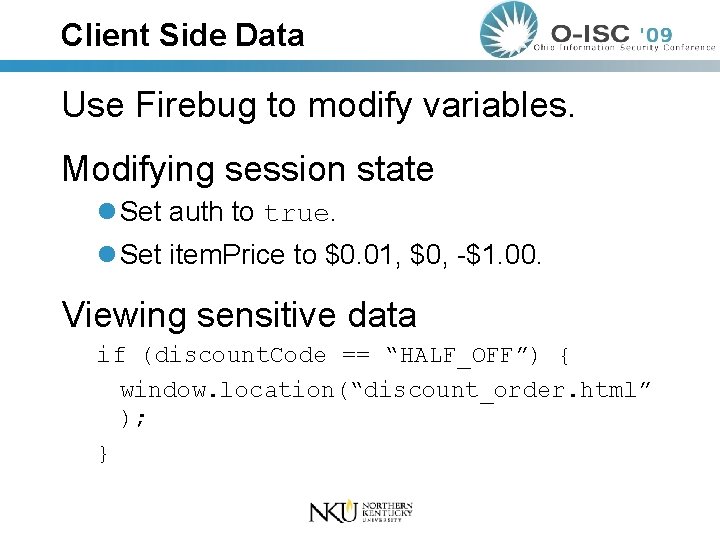
Client Side Data Use Firebug to modify variables. Modifying session state l Set auth to true. l Set item. Price to $0. 01, $0, -$1. 00. Viewing sensitive data if (discount. Code == “HALF_OFF”) { window. location(“discount_order. html” ); }
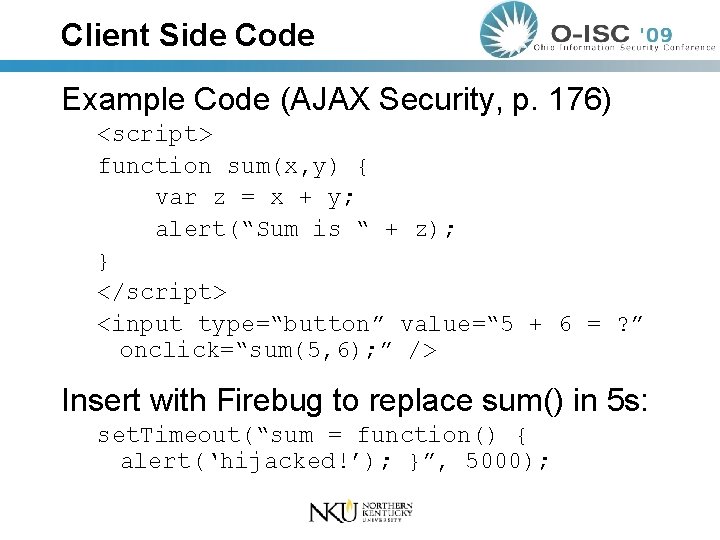
Client Side Code Example Code (AJAX Security, p. 176) <script> function sum(x, y) { var z = x + y; alert(“Sum is “ + z); } </script> <input type=“button” value=“ 5 + 6 = ? ” onclick=“sum(5, 6); ” /> Insert with Firebug to replace sum() in 5 s: set. Timeout(“sum = function() { alert(‘hijacked!’); }”, 5000);
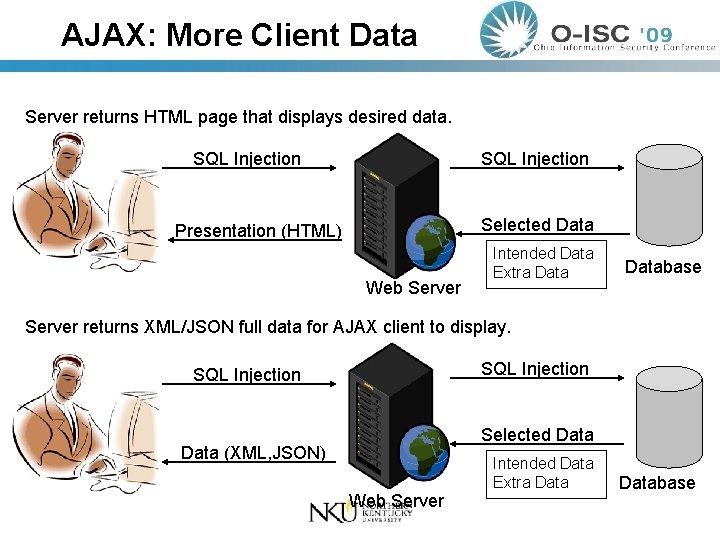
AJAX: More Client Data Server returns HTML page that displays desired data. SQL Injection Selected Data Presentation (HTML) Web Server Intended Data Extra Database Server returns XML/JSON full data for AJAX client to display. SQL Injection Selected Data (XML, JSON) Web Server Intended Data Extra Database
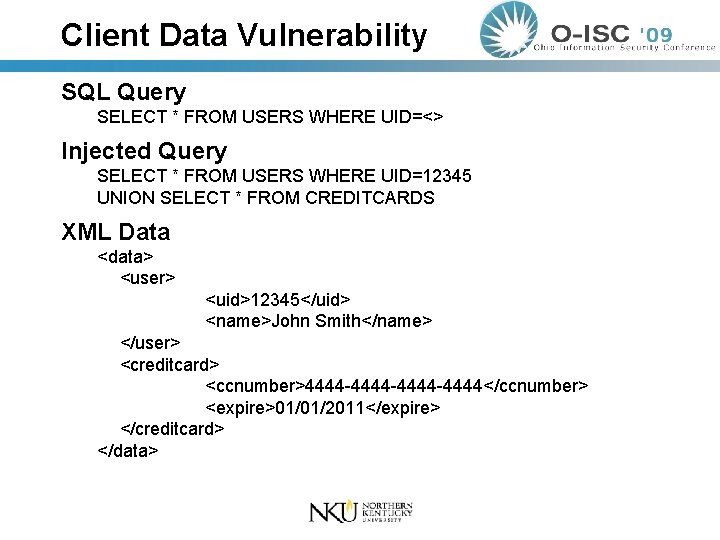
Client Data Vulnerability SQL Query SELECT * FROM USERS WHERE UID=<> Injected Query SELECT * FROM USERS WHERE UID=12345 UNION SELECT * FROM CREDITCARDS XML Data <data> <user> <uid>12345</uid> <name>John Smith</name> </user> <creditcard> <ccnumber>4444 -4444 -4444</ccnumber> <expire>01/01/2011</expire> </creditcard> </data>
![JSON var json = get. Item() // json = “[ ‘Toshiba’, 499, ‘LCD TV’]” JSON var json = get. Item() // json = “[ ‘Toshiba’, 499, ‘LCD TV’]”](http://slidetodoc.com/presentation_image_h2/02f4afd81827c14314decac1f35ac5c8/image-31.jpg)
JSON var json = get. Item() // json = “[ ‘Toshiba’, 499, ‘LCD TV’]” var item = eval(json) // item[0] = ‘Toshiba’ // item[1] = 499 // item[2] = ‘LCD TV’
![JSON Injection Evil input: ‘]; alert(‘XSS’); // var json = get. Item() // json JSON Injection Evil input: ‘]; alert(‘XSS’); // var json = get. Item() // json](http://slidetodoc.com/presentation_image_h2/02f4afd81827c14314decac1f35ac5c8/image-32.jpg)
JSON Injection Evil input: ‘]; alert(‘XSS’); // var json = get. Item() // json = “[ ‘Toshiba’, 499, ‘’]; alert(‘XSS’); //” var item = eval(json) // Alert box with ‘XSS’ appears. // Use json 2. js validation library to prevent.
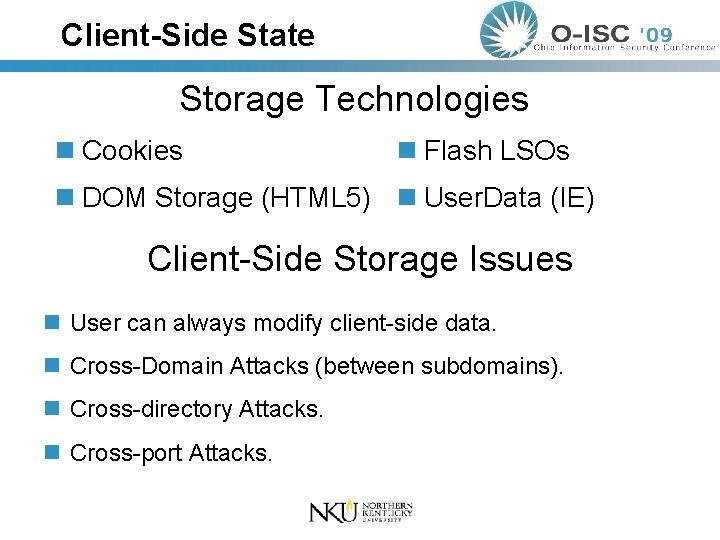
Client-Side State Storage Technologies n Cookies n Flash LSOs n DOM Storage (HTML 5) n User. Data (IE) Client-Side Storage Issues n User can always modify client-side data. n Cross-Domain Attacks (between subdomains). n Cross-directory Attacks. n Cross-port Attacks.
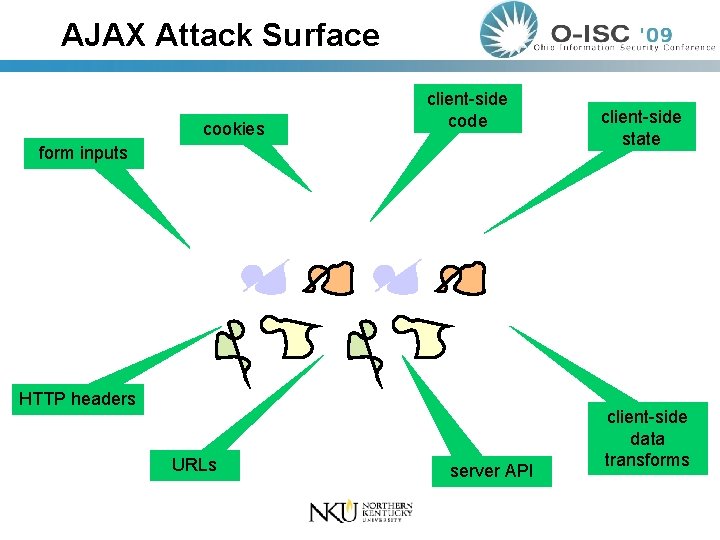
AJAX Attack Surface cookies client-side code form inputs HTTP headers URLs server API client-side state client-side data transforms
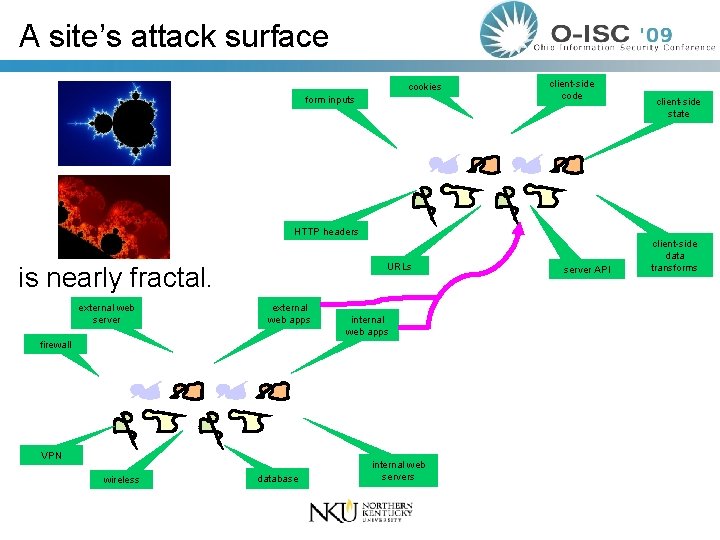
A site’s attack surface cookies form inputs client-side code client-side state HTTP headers URLs is nearly fractal. external web server external web apps internal web apps firewall VPN wireless database internal web servers server API client-side data transforms
Discussion Items n. Are organization’s security policies changing in response to Web 2. 0? n. What are people currently doing to determine their attack surface? n. How do people select which elements of the attack surface to reduce first?
- Slides: 36