Vulnerability Vectors in PDF Synthesizing PDF Attacks PDF
![Vulnerability Vectors in PDF Synthesizing PDF Attacks PDF EU-Sec-West London , UK [2008] Aditya Vulnerability Vectors in PDF Synthesizing PDF Attacks PDF EU-Sec-West London , UK [2008] Aditya](https://slidetodoc.com/presentation_image_h2/01f638914ebec2a5cffeefb8dd28918c/image-1.jpg)
Vulnerability Vectors in PDF Synthesizing PDF Attacks PDF EU-Sec-West London , UK [2008] Aditya K Sood aka 0 kn 0 ck Sec Niche Security Vulnerable Vectors in PDF EU-Sec-West 2008 , UK
![[root@0 kn 0 ck]# whoami Background = Independent Security Researcher. Founder , Sec Niche [root@0 kn 0 ck]# whoami Background = Independent Security Researcher. Founder , Sec Niche](http://slidetodoc.com/presentation_image_h2/01f638914ebec2a5cffeefb8dd28918c/image-2.jpg)
[root@0 kn 0 ck]# whoami Background = Independent Security Researcher. Founder , Sec Niche Security. [http: //www. secniche. org] Front End = Works for KPMG Consulting IS Author Hakin 9 , USENIX ; login Released Advisories : Yahoo , AOL , MSN , Google , Verisign , Microsoft etc. Projects: MLabs , CERA , Trio. Sec Rest Google Me Out ! Vulnerable Vectors in PDF EU-Sec-West 2008 , UK
Thanks to DL - PSIRT Adobe Product Security Incident Response Team For Contacting and Sharing Thoughts Over Talk. Coordinated for Responsible Disclosure and Product Security Vulnerable Vectors in PDF EU-Sec-West 2008 , UK
The Application Bug Anatomy Given Enough Eye Balls , All Bugs are Shallow. [ Eric Raymond – The Cathedral and Bazaar ] Many Eye Balls Misses the Point All Together. Bug Matrix is Hard to Diminish. Vulnerable Vectors in PDF EU-Sec-West 2008 , UK
The Realm of Application Security The Paradigm : Squared Approach Privacy Security Application Quality Reliability Vulnerable Vectors in PDF EU-Sec-West 2008 , UK
Application : Exploitation Shift 1. Understanding the Shift. Why it is Happening ? ? 2. Memory Corruptions are Hard to Exploit. 3. Diversified Infection Vectors in Application Realm. 4. Cross Referenced Matrix Technologies. 5. Development of Complex System Security Structures. 6. Applications Provide an Interface to System Insecurities. 7. System Vulnerabilities : Vendors Red Alert. 8. Application Exploitation == Feature Manipulation. Vulnerable Vectors in PDF EU-Sec-West 2008 , UK
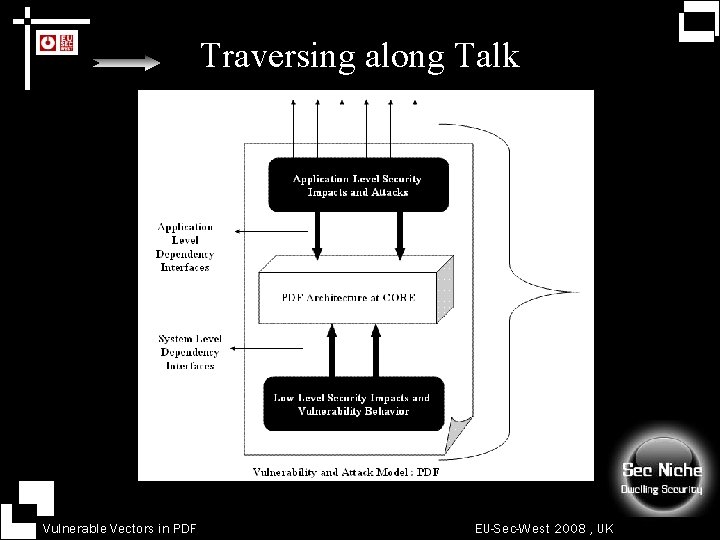
Traversing along Talk Vulnerable Vectors in PDF EU-Sec-West 2008 , UK
Dissecting PDF Internals Breaking The Hidden. Vulnerable Vectors in PDF EU-Sec-West 2008 , UK
Structural Components of PDF Understanding The Crux. 1. COS – Common Object Structure Model The incore model of PDF documents. 2. The Component Design of Predefined Symbols define the component layout in the document. 3. Cross Reference Table and Object Abstraction. The cross functional dependency and object layout. Vulnerable Vectors in PDF EU-Sec-West 2008 , UK
Structural Components of PDF COS Object Model 1. Layered Based Structure with Hierarchical Layout. 2. Base Depends on Raw Data , Tree Model is Implemented. 3. Model(Tree) = Object(Child) + Object(Nodes) Objects are Applied as Child and Nodes. 4. Modelling of Objects is Undertaken from Node to Child. 5. The Tree Head Object is Document Catalog. The Tree starts from this Head Node. 6. Layers Govern the Functionality of Objects Designed. 7. Interfacial Layer Arrangement is there. Vulnerable Vectors in PDF EU-Sec-West 2008 , UK
Structural Components of PDF COS Object Model : Object Types Looking at Explicit Definition: 1. Direct Objects The Reference Vector is NULL. No Reference. 2. Indirect Objects References are Uphold in these Objects. Reference Oriented. 3. Container Objects Hold References to Other Objects. Specification is Different. 4. Notable Exceptions are Implemented. 5. Base Module is Array. Objects are Structured Over it. Vulnerable Vectors in PDF EU-Sec-West 2008 , UK
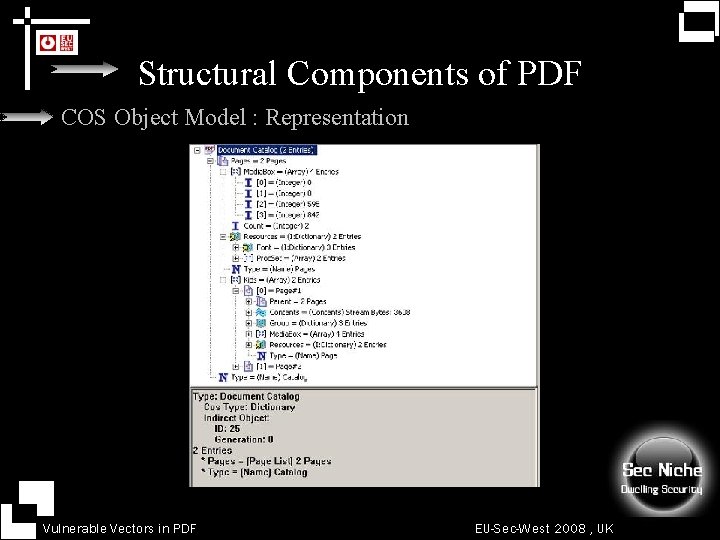
Structural Components of PDF COS Object Model : Representation Vulnerable Vectors in PDF EU-Sec-West 2008 , UK
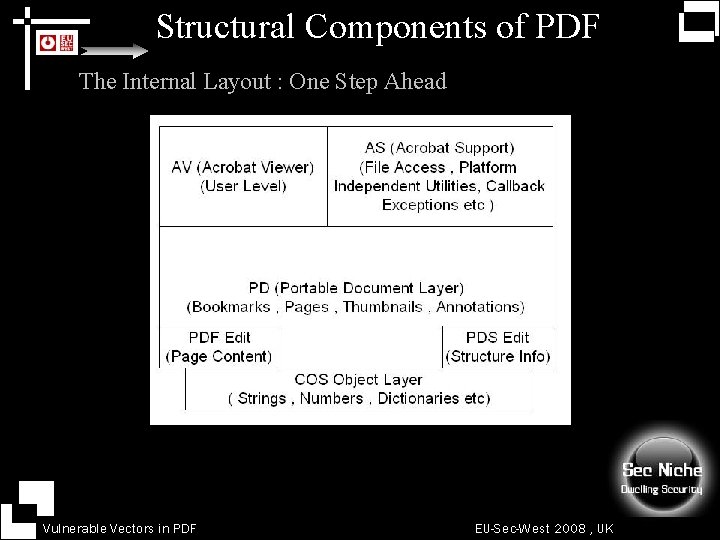
Structural Components of PDF The Internal Layout : One Step Ahead Vulnerable Vectors in PDF EU-Sec-West 2008 , UK
Structural Components of PDF The Functional Layout 1. Object Functionality = Inheriting Properties from Root. 2. Properties are Globally Applicable. 3. Versatility in Object Designing. Backward Compatibility. 4. Properties(Object) == Arrays , Strings , Dictionary etc. 5. Process( Document Designing) == Document Drafting. 6. COS Object Tree Supports Custom Object Types. Note : PDF Capabilities Can Be Altered By Anyone Following Custom Object Model. Vulnerable Vectors in PDF EU-Sec-West 2008 , UK
Structural Components of PDF The Object Symbols 1. 2. 3. 4. Symbols Comprise of Internal Entity of Root Tree. Dissects The Working Functionality Type. Reversing(PDF Doc) == Symbols Required. The Symbols 4. 1 Document Catalog. 4. 2 Annotation Objects. 4. 3 Page Object. 4. 4 Indirect Object Indication. 4. 5 Pages Object. Vulnerable Vectors in PDF EU-Sec-West 2008 , UK
Structural Components of PDF Cross Reference Table and Object Abstraction Objects placement in XREF Table 1. The number of objects in the document. 2. The offsets that are defined for it. 3. The cross reference table is always placed at the end of file. 4. The parameter of cross reference table is XREF. 5. The table holds the object count on Zero Based Indexing ie from 0 to [N] Vulnerable Vectors in PDF EU-Sec-West 2008 , UK
Structural Components of PDF Classification of Objects in XREF Table Offset objects are called by { n, f} parameter in the cross reference table i. e. XREF of the objects. In this XREF table the : 1. [n] The parameter n is used to reference the used bytes for • object and specific offset related to it. 2. [f] The parameter f is used to reference the unused bytes related to the specific object. 3. Offsets are always picked from the staring offset of the document file for reducing complexity Vulnerable Vectors in PDF EU-Sec-West 2008 , UK
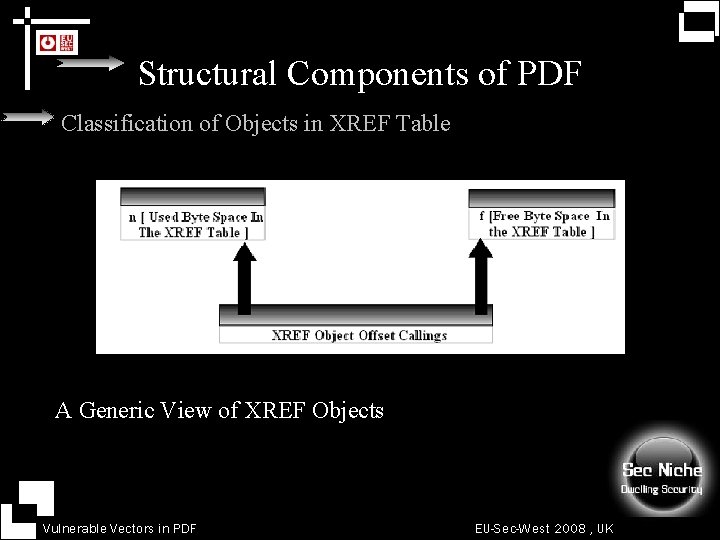
Structural Components of PDF Classification of Objects in XREF Table A Generic View of XREF Objects Vulnerable Vectors in PDF EU-Sec-West 2008 , UK
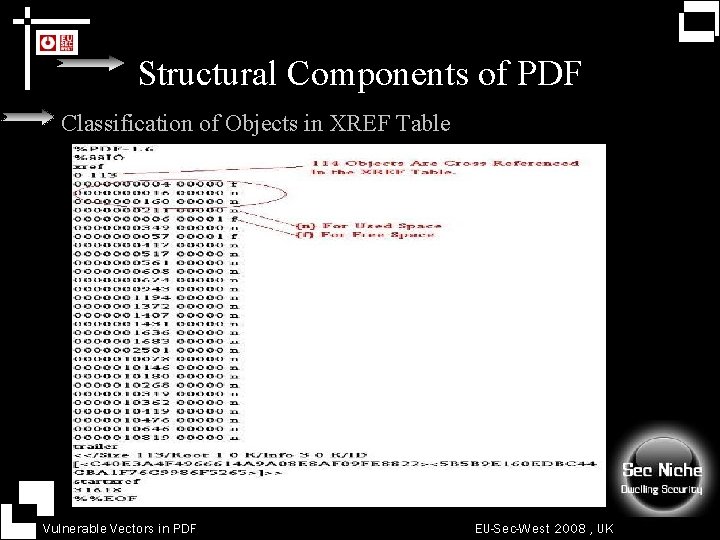
Structural Components of PDF Classification of Objects in XREF Table Vulnerable Vectors in PDF EU-Sec-West 2008 , UK
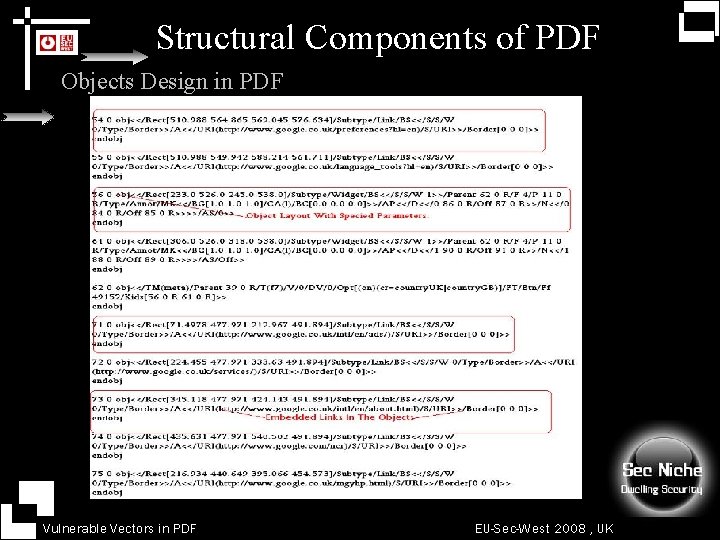
Structural Components of PDF Objects Design in PDF Vulnerable Vectors in PDF EU-Sec-West 2008 , UK
Structural Components of PDF Objects Design in PDF 1. The object starts with an object number. The 55, 56 etc are the object numbers which get cross linked for the available byte space in the table and interferes into functioning. 2. The third party linking is specified in this. The URI linking is clear in its context. 3. The other specification used like obj<<. . <<subtype is for COS Object Modelling. Vulnerable Vectors in PDF EU-Sec-West 2008 , UK
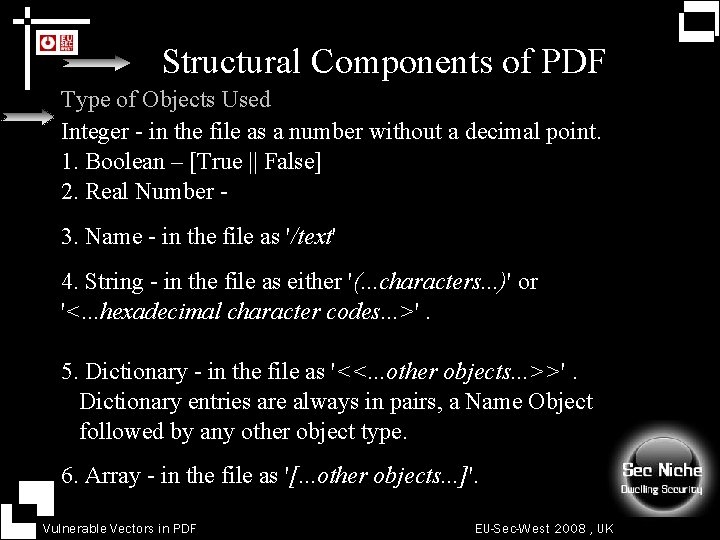
Structural Components of PDF Type of Objects Used Integer - in the file as a number without a decimal point. 1. Boolean – [True || False] 2. Real Number 3. Name - in the file as '/text' 4. String - in the file as either '(. . . characters. . . )' or '<. . . hexadecimal character codes. . . >'. 5. Dictionary - in the file as '<<. . . other objects. . . >>'. Dictionary entries are always in pairs, a Name Object followed by any other object type. 6. Array - in the file as '[. . . other objects. . . ]'. Vulnerable Vectors in PDF EU-Sec-West 2008 , UK
Structural Components of PDF Type of Objects Used 7. Stream – Object Type is complex. Streams are Indirect Objects. Stream Objects use Object References. Fused with Dictionary Objects. Dictionary Object Carry Information for Accessing Bytes. Vulnerable Vectors in PDF EU-Sec-West 2008 , UK
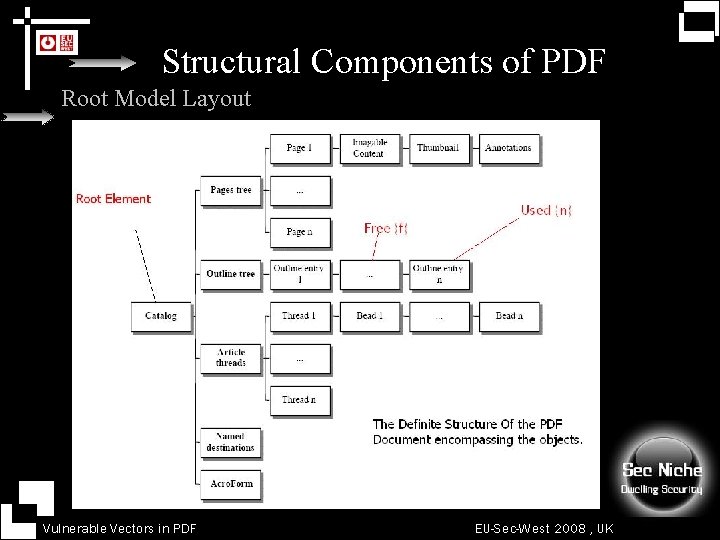
Structural Components of PDF Root Model Layout Vulnerable Vectors in PDF EU-Sec-West 2008 , UK
Structural Components of PDF Breaking in Internals Hit the PDF internals with PDF CAN Opener ! Vulnerable Vectors in PDF EU-Sec-West 2008 , UK
Application Attacks Anatomy Why These Attacks Persist || Supporting Factors. 1. User or Client Ignorance to technology. 1. 2. Version Compatibility Problems. 3. No Upgrade in Software's used for Working. 4. Use of OLD version of Software's. 5. Feature Manipulation for Rogue Purposes. 6. Interdependency in System and Software Functionality. 7. Complexity in Architectures. Even Adobe Acrobat Implements Security Mechanisms in all Versions 6. 0 / 7. 0 / 8. 0 Vulnerable Vectors in PDF EU-Sec-West 2008 , UK
Application Attacks Anatomy Little Java. Script Info Sheet 1. HTML Java. Script !== Acrobat Java. Script 2. ACRO JS cannot Access HTML JS Objects and Vice Versa. 3. Objects (ACRO JS) == app , doc , annotations etc. 4. Objects (HTML JS) == window , document etc. 5. Both do not have Inheritance Capabilities. 6. Objects have individualistic properties. No Cross Access. 7. ACRO JS is extracted from ECMA Script. 8. APP object is the main Information Object of ACRO JS. Critical ! Vulnerable Vectors in PDF EU-Sec-West 2008 , UK
Application Attacks Anatomy A Thought. Its not a 0 Day PDF is all about EVERDAY. Vulnerable Vectors in PDF EU-Sec-West 2008 , UK
Application Attacks in PDF 1. PDF Act as Launch Pad 2. Attacks Depend on Acrobat Versions 3. 4. 1. Easy to Manipulate for Third Party Attacks. 5. 2. Heavily Use of Java. Script for Extensible Functionality. 6. 3. Attacks Modes are Easy to Trigger. 7. 4. Client Side Attacks are Quite Easy. 8. 5. Low Level Software Vulnerabilities. 9. 6. Affecting and Hitting Browsers at Core. 10. 7. Well Defined Support for Pluggable Protocol Handlers 11. 8. Applied in a Versatile Manner. Vulnerable Vectors in PDF EU-Sec-West 2008 , UK
Application Attacks in PDF Synthesizing Application Level Attacks in PDF FUSED DEMONSTRATIONS Vulnerable Vectors in PDF EU-Sec-West 2008 , UK
Application Attacks in PDF CLIENT on the Verge What is Going to Happen to ME ? ? Vulnerable Vectors in PDF EU-Sec-West 2008 , UK
Application Attacks in PDF Implemented Security Model in Acrobat PDF Java. Script Driven 1. Execution in Privileged Mode. Methods : Console / Batch / Application etc. 2. Execution in Unprivileged Mode. Methods : Page Open / Mouse Events etc. 3. Contexts Levels = Doc / Batch / Page / Folder / Field Number of Attacks are Useless while Execution due to Implemented Security. Vulnerable Vectors in PDF EU-Sec-West 2008 , UK
Application Attacks in PDF 1. PDF Act as Launch Pad : Attack Vectors 1. XSS Checks in PDF and Alerts. [Input Checks] 2. Java. Script Infection Model. [Interim Attack Base ] 3. Malicious SOAP Access. 4. PDF Backdoor Anatomy. 5. PHISHING. 6. Attack comprising Pluggable Protocol Handlers. 7. PDF Spamming 8. Local Area Network Infections through PDF. 9. Rogue PDF Designing through SDK Vulnerable Vectors in PDF EU-Sec-West 2008 , UK
Application Attacks in PDF Testing Application Strategy : PDF 1. Direct Java. Script Insertion JS Files are Globally executable at Folder Access 2. Binding Java. Script to a Control in PDF. [ c. Exec = “” ] Dynamically Execution through a Control in PDF 3. Both Strategies are Equally Driven. 4. Output Can be Seen When PDF is Opened at System Level. Vulnerable Vectors in PDF EU-Sec-West 2008 , UK
Application Attacks in PDF 1. XSS Checks in PDF 2. 3. 4. 5. 6. 7. 8. 1. Prone to XSS Attacks. 2. Interim use of ALERT Object through Java. Script. 3. OPEN PDF Parameters. 4. Universal XSS at Core. Globally Applicable in PDF. 5. Java. Script (PDF) != Java. Script (HTML) Different in Specifications and Usage 6. Triggered through Input Parameters mainly. Vulnerable Vectors in PDF EU-Sec-West 2008 , UK
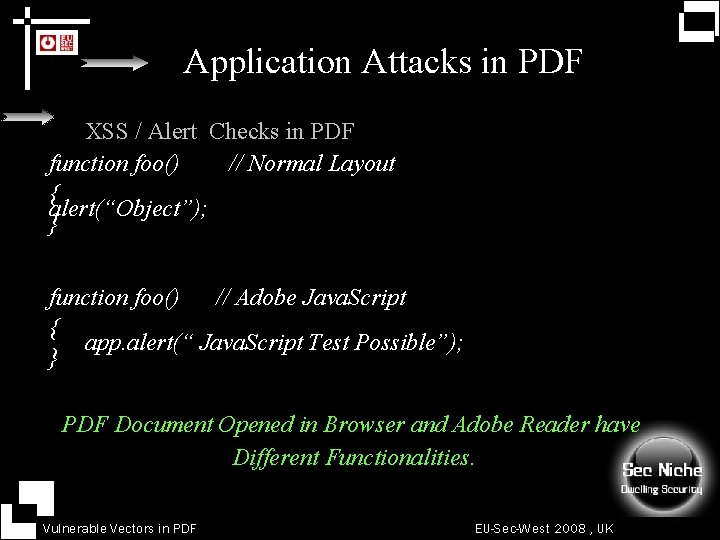
Application Attacks in PDF 1. XSS / Alert Checks in PDF function foo() // Normal Layout { alert(“Object”); } function foo() // Adobe Java. Script { app. alert(“ Java. Script Test Possible”); } 1. PDF Document Opened in Browser and Adobe Reader have Different Functionalities. Vulnerable Vectors in PDF EU-Sec-West 2008 , UK
Application Attacks in PDF 1. Open PDF Parameters 2. 1. Command Line Control to Users. 3. 2. Arguments are Passed through URL Directly. 4. Two Ways: 5. 1. Passing Parameters Directly. 6. 2. Passing Parameters through URL. 7. URL Delimiters: 8. 1. [ # ] http: //www. target. org/doc. pdf #tag =1 2. | & | http: //www. target. org/doc. pdf #tag =1 & arg = 2 Vulnerable Vectors in PDF EU-Sec-West 2008 , UK
Application Attacks in PDF Open PDF Parameters FDF option is used often by attackers. It specifies a FDF file to be used to populate form fields in the PDF file being opened. It is used with same pattern Example: # fdf =[Target URL] Vulnerable Vectors in PDF EU-Sec-West 2008 , UK
Application Attacks in PDF 1. Open PDF Parameters 2. Referenced from Advisory Release on PDF http: //[Target]/[File]. pdf##### http: //[Site Name]/[File]. pdf#fdf=[Target] http: //[Site. Name]/[File]. pdf#FDF=javascript: document. write() 1. Acrobat 7. 0 Issue. 2. Attacks Feasible for running in Older Versions. 3. Not work effectively on Latest Versions. 4. Browser Dependency is there. Interpretation of URL Vulnerable Vectors in PDF EU-Sec-West 2008 , UK
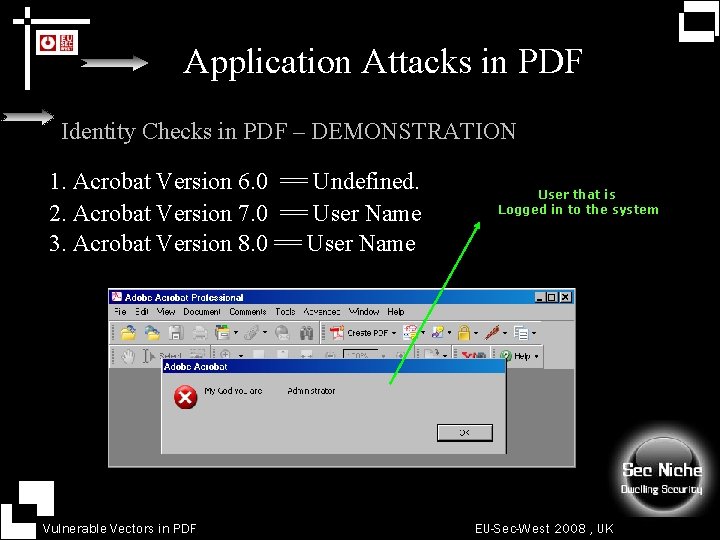
Application Attacks in PDF Identity Checks in PDF – DEMONSTRATION 1. Acrobat Version 6. 0 == Undefined. 2. Acrobat Version 7. 0 == User Name 3. Acrobat Version 8. 0 == User Name Vulnerable Vectors in PDF User that is Logged in to the system EU-Sec-West 2008 , UK
Application Attacks in PDF Backdoor Designing 1. PDF perform stringent functions when opened. 2. Used Adobe Based Malicious Java. Script's. 3. Designing PDF with Embedded Rogue Links. 4. PDF SDK is used for Crafting a Malicious PDF File. 5. Direct Interpreting in Text Editor. 6. Manipulating Objects in PDF File Directly. 7. Binding Java. Script’s to the Various Objects i. e. Buttons. 8. Form Type Submissions / Content Downloading / Links. Vulnerable Vectors in PDF EU-Sec-West 2008 , UK
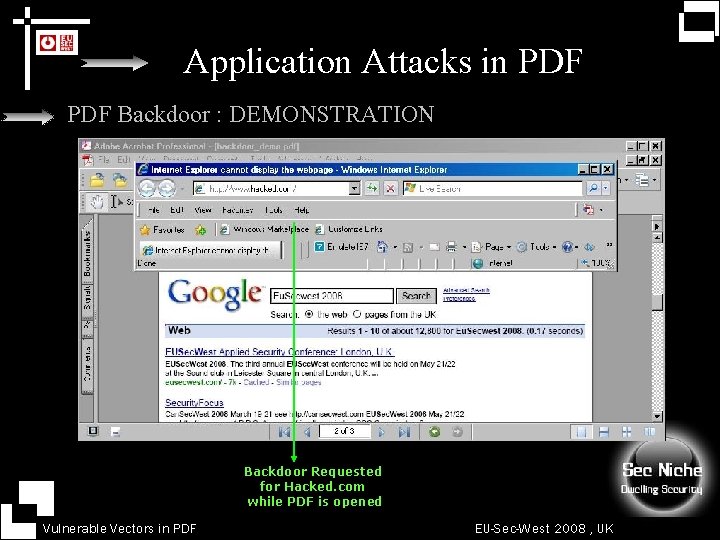
Application Attacks in PDF Backdoor : DEMONSTRATION Backdoor Requested for Hacked. com while PDF is opened Vulnerable Vectors in PDF EU-Sec-West 2008 , UK
Application Attacks in PDF Triggering Events through Pluggable Protocol Handlers. 1. Affected Browsers at Core. 2. Third Party Event Generation through PDF. 3. Prime Source of Number of Attacks. 4. Working Dependency between Two Software's. 5. Base for PHISHING Attacks. mailto: / file: / ftp: / telnet: / view-source: /chrome: gopher: / https: / Java. Script: / news: / res: Security Restrictions are Applied ! Version Specific. Vulnerable Vectors in PDF EU-Sec-West 2008 , UK
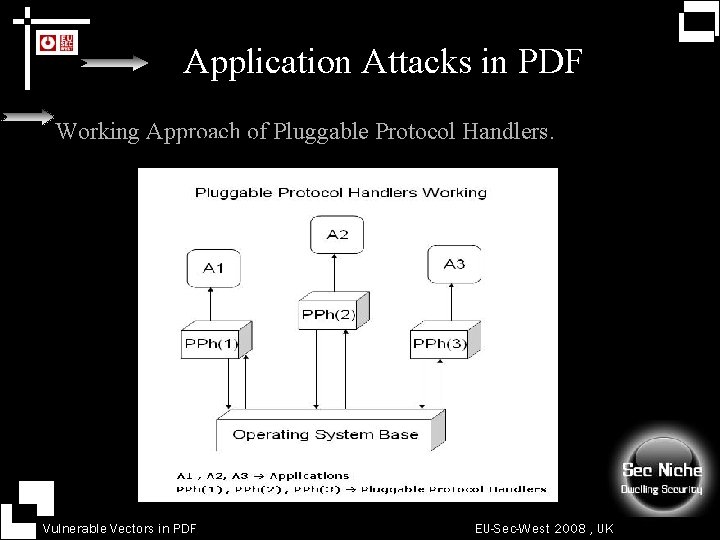
Application Attacks in PDF Working Approach of Pluggable Protocol Handlers. Vulnerable Vectors in PDF EU-Sec-West 2008 , UK
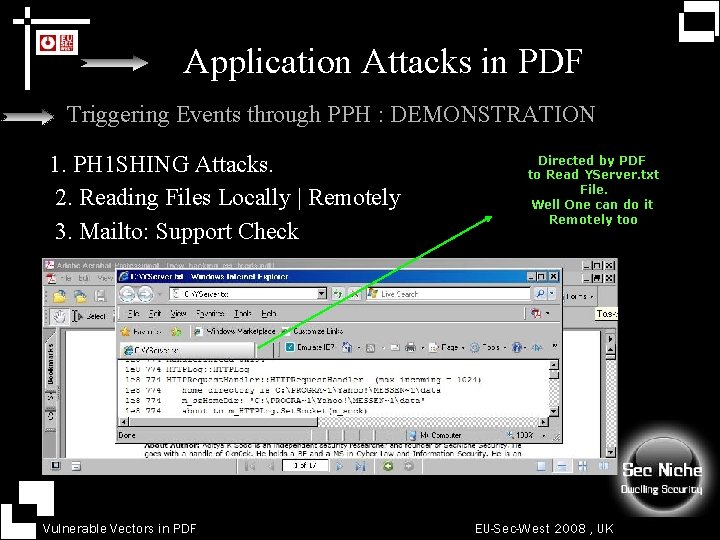
Application Attacks in PDF Triggering Events through PPH : DEMONSTRATION 1. PH 1 SHING Attacks. 2. Reading Files Locally | Remotely 3. Mailto: Support Check Vulnerable Vectors in PDF Directed by PDF to Read YServer. txt File. Well One can do it Remotely too EU-Sec-West 2008 , UK
Application Attacks in PDF Memory Exhaustion - PDF : NO DEMONSTRATION 1. PDF Can be used as Memory Exhaustion Base. Attack Vector is Direct. 2. PDF can Direct Browser to exhaust Memory. Attack Vector is Indirect The Target Base is PDF Vulnerable Vectors in PDF EU-Sec-West 2008 , UK
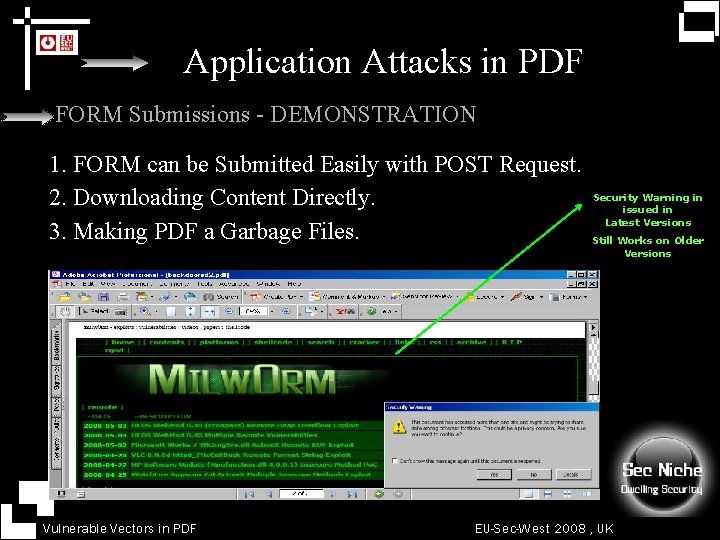
Application Attacks in PDF FORM Submissions - DEMONSTRATION 1. FORM can be Submitted Easily with POST Request. 2. Downloading Content Directly. 3. Making PDF a Garbage Files. Vulnerable Vectors in PDF Security Warning in issued in Latest Versions Still Works on Older Versions EU-Sec-West 2008 , UK
Application Attacks in PDF Local Denial of Service – PDF DEMONSTRATION 1. Very Easy to Trigger. 2. Specific Malicious JS file can do the Trick. 3. Affect Document Opening at Full. 4. Client Side Functionality is Lowered Down. Vulnerable Vectors in PDF EU-Sec-West 2008 , UK
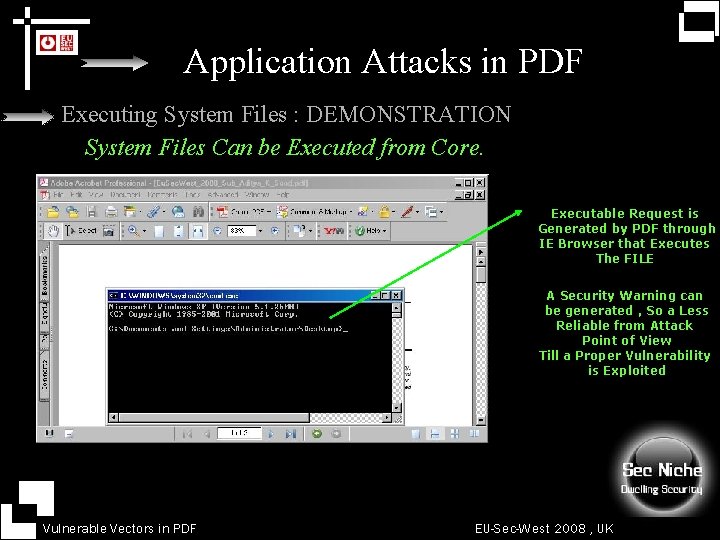
Application Attacks in PDF Executing System Files : DEMONSTRATION System Files Can be Executed from Core. Executable Request is Generated by PDF through IE Browser that Executes The FILE A Security Warning can be generated , So a Less Reliable from Attack Point of View Till a Proper Vulnerability is Exploited Vulnerable Vectors in PDF EU-Sec-West 2008 , UK
Application Attacks in PDF The Reality : 1. Number of Attacks Failed in Acrobat with diff Versions. 2. Software Version Plays Critical Role. 3. Security Restrictions Applied on Methods. 4. Game of Privileged / Non Privileged Execution. 5. Dependency on Ingrained Vulnerabilities. 6. Acrobat 8. 0 does not support Methods which Acrobat 7. 0 does The Attackers Night Mare | Security Driven Not. Allowed. Error: Security settings prevent access to this property or method. Vulnerable Vectors in PDF EU-Sec-West 2008 , UK
Application Attacks in PDF Restricted Functions in – Non Privileged Mode 1. ADBC. new. Connection. 2. app. add. Menu. Item / app. add. Sub. Menu 3. app. get. Path / app. new. Doc / app. open. Doc 4. app. launch. URL There are lot more like that. Most of the attacks use these feature to manipulate the normal functioning. Security Restrictions applied Lay off the Attacks. Vulnerable Vectors in PDF EU-Sec-West 2008 , UK
Application Attacks in PDF How to make Attacks more Sustainable : Attackers View Point 1. Finding Requisite Vulnerability : Hard Process. 2. Exploiting the Trusted Behaviour Designing Trusted Wrapper Functions with Restricted Codes. 3. PDF SDK Plays a Generic Role. 4. Dethroning the NOT ALLOWED ERROR in PDF. 5. Restricted Methods can be Called Easily. Vulnerable Vectors in PDF EU-Sec-West 2008 , UK
Application Attacks in PDF Exploiting TRUST through Java. Script Dynamically Bypassing the Security Restrictions in PDF 1. Crafting a Trusted Wrapper Function with app. Trusted() 2. Inject app. begin. Priv() and app. end. Priv(). 3. Specify the Code between these privileged contexts. trusted. Doc = app. trusted. Function( function (width , height) { app. begin. Priv(); var trusted. Doc = app. new. Doc(width, height); app. end. Priv(); return trusted. Doc; }) Vulnerable Vectors in PDF EU-Sec-West 2008 , UK
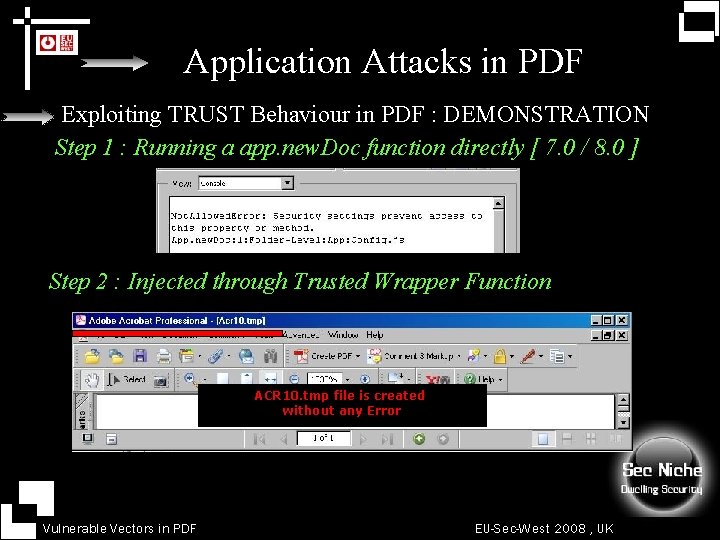
Application Attacks in PDF Exploiting TRUST Behaviour in PDF : DEMONSTRATION Step 1 : Running a app. new. Doc function directly [ 7. 0 / 8. 0 ] Step 2 : Injected through Trusted Wrapper Function ACR 10. tmp file is created without any Error Vulnerable Vectors in PDF EU-Sec-West 2008 , UK
Application Attacks in PDF SPAMMED PDF : DEMONSTRATION 1. Designed through PDF SDK for Rogue Purposes. 2. Distributed Along Mail Applications. Vulnerable Vectors in PDF EU-Sec-West 2008 , UK
Application Attacks in PDF SOAP – ADBC / ODBC Checks: 1. Querying the Local Database through System ODBC. 2. Easy to Enumerate the Running Databases. 3. Web Services Play a Crucial Part in Holding Information. 4. Holding Data at Port 80 for incoming Connection. 5. Connecting through Client to Port 80 to Access XML Data through SOAP Access. ADBC. new. Connection / ADBC. get. Data. Source. List() Follow the Trusted Wrapper Paradigm Vulnerable Vectors in PDF EU-Sec-West 2008 , UK
Software and Low Level Insecurities 1. Software Inconsistencies due to Exceptions. 2. Exceptional Behaviour in Handling Crafted JS Files. 3. Designing Call Back functions to Bypass things. 4. Memory Corruptions / Memory Exhaustions. Finding an Internal Vulnerable function. CVE 2008 – 2042 | Adobe Security Bulletins Vulnerable Vectors in PDF EU-Sec-West 2008 , UK
Digging inside PDF Further Research: 1. Storing Files inside PDF. 2. Exploiting ADBC Functionality in a Stringent Manner. 3. Java. Script for Analyzing in core PDF Software Responses. 4. PDF affect on System Optimization and Behaviour. 5. Finding Vulnerabilities and Software Issues. 6. Attaining Robustness in PDF Applications. 7. PDF Affect on Operating System Security. 8. So on && on …. Vulnerable Vectors in PDF EU-Sec-West 2008 , UK
Resources at CORE References: 1. Adobe Java. Script: http: //www. adobe. com/devnet/acrobat/javascript. html 2. Wind Jack Solution : Resources on PDF http: //www. windjack. com/ 3. Backdooring PDF Files http: //michaeldaw. org/md-hacks/backdooring-pdf-files/ 4. Security Bulletins of Adobe http: //www. adobe. com/support/security/ Vulnerable Vectors in PDF EU-Sec-West 2008 , UK
Questions / Queries Sharing the Knowledge and Research. Vulnerable Vectors in PDF EU-Sec-West 2008 , UK
![[root@0 kn 0 ck]#. /thanks Vulnerable Vectors in PDF EU-Sec-West 2008 , UK [root@0 kn 0 ck]#. /thanks Vulnerable Vectors in PDF EU-Sec-West 2008 , UK](http://slidetodoc.com/presentation_image_h2/01f638914ebec2a5cffeefb8dd28918c/image-61.jpg)
[root@0 kn 0 ck]#. /thanks Vulnerable Vectors in PDF EU-Sec-West 2008 , UK
- Slides: 61