Vulnerabilities of Reliable Multicast Protocols Thomas M Park
Vulnerabilities of Reliable Multicast Protocols Thomas M. Park, David A. Kassay, Clifford J. Weinstein Massachusetts Institute of Technology Lincoln Laboratory Lexinton, Massachusetts Reviewed by: Siu Fung (Andes) Chin
Vulnerabilities of Reliable Multicast Protocols n Outline n n n Introduction Types of Protocols Attacks Defenses Conclusion
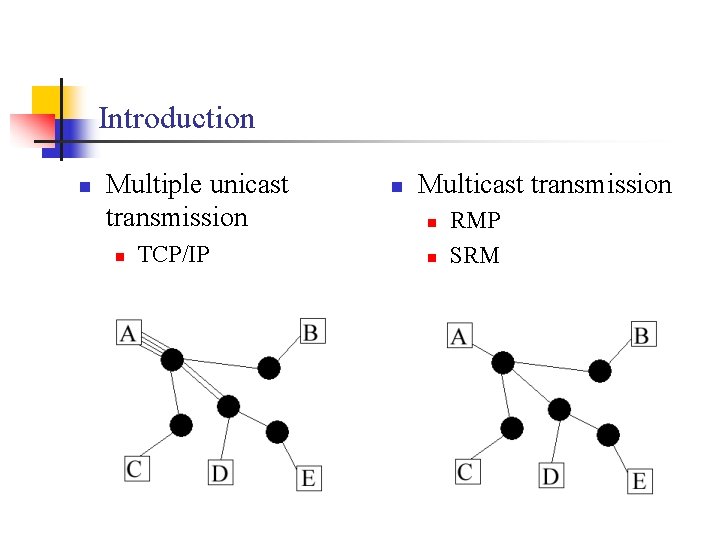
Introduction n Multiple unicast transmission n TCP/IP n Multicast transmission n n RMP SRM
Introduction (cond. ) n Why reliable multicast transmission? n n Problems? n n More efficient Lack of security Solutions? n n n Network-level security (IPSEC) Secret-key algorithm Risk management approach
Types of reliable multicast protocols n Sender-initiated reliability protocol n n n Positive acknowledgment (ACK) ACK implosion Example: RMP(Reliable Multicast Protocol) n Token around ring
Types of reliable multicast protocols (cont) n Receiver-initiated reliability protocol n n n Negative acknowledgment (NCK) NCK implosion Example: SRM(Scalable Reliable Multicast Protocol) n Suppress excess NAK
Vulnerabilities n Flooding attack n n Forged data attack n n Corruption of files transmitted (RMP) Premature ACK n n Consume network bandwidth/process time Assign incorrect sequence no. (RMP) NAK and retransmission suppression n Interfare retransmissions (SRM)
Defense n Fliter received packets n n Digitally signed messages n n Identify legitimate members Employ IGMP v 3 (Internet Group Management Protocol) n n Block attacker’s packet Prevent flooding Simple authentication protocol n Prevent spoofing
Conclusion n Different types reliable multicast protocol Different types attack Different types defense Increase protection – increase cost n Questions? n n n
- Slides: 9