VSEC FOR PUBLIC CLOUD Peter Marini MSP and

VSEC FOR PUBLIC CLOUD Peter Marini | MSP and Public Cloud Channel © 2017 Check Point Software Technologies Ltd. 1
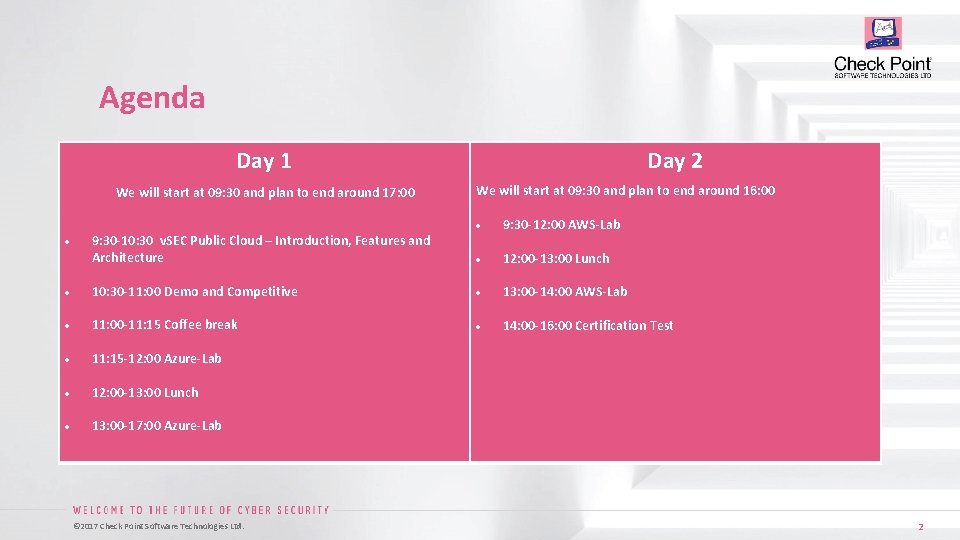
Agenda Day 1 We will start at 09: 30 and plan to end around 17: 00 Day 2 We will start at 09: 30 and plan to end around 16: 00 9: 30 -10: 30 v. SEC Public Cloud – Introduction, Features and Architecture 9: 30 -12: 00 AWS-Lab 12: 00 -13: 00 Lunch 10: 30 -11: 00 Demo and Competitive 13: 00 -14: 00 AWS-Lab 11: 00 -11: 15 Coffee break 14: 00 -16: 00 Certification Test 11: 15 -12: 00 Azure-Lab 12: 00 -13: 00 Lunch 13: 00 -17: 00 Azure-Lab © 2017 Check Point Software Technologies Ltd. 2
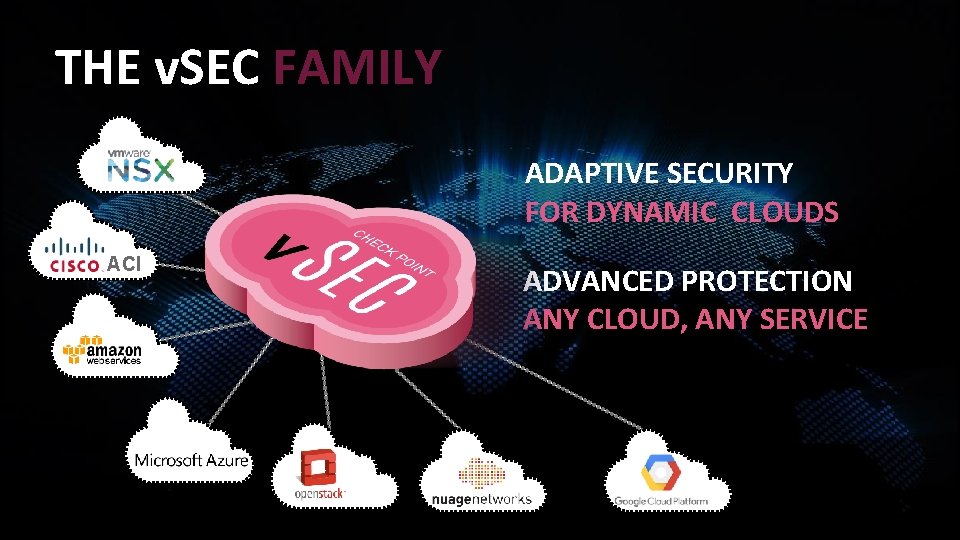
THE v. SEC FAMILY ADAPTIVE SECURITY FOR DYNAMIC CLOUDS ACI ADVANCED PROTECTION ANY CLOUD, ANY SERVICE
Datacenter Hacking Incident • Leaked account details of 32 million members • Website hosted on public cloud • Is the public cloud insecure? © 2017 Check Point Software Technologies Ltd. 4
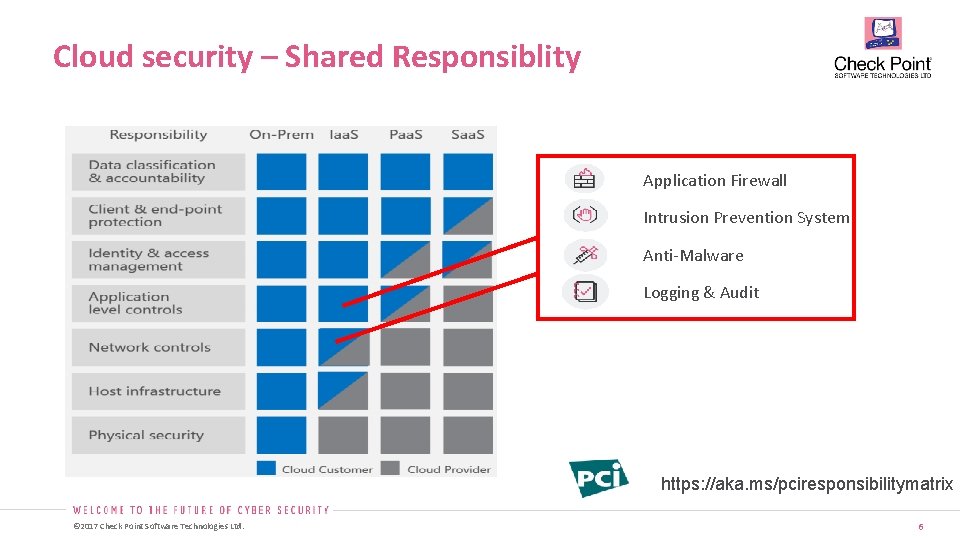
Cloud security – Shared Responsiblity Application Firewall Intrusion Prevention System Anti-Malware Logging & Audit https: //aka. ms/pciresponsibilitymatrix © 2017 Check Point Software Technologies Ltd. 6
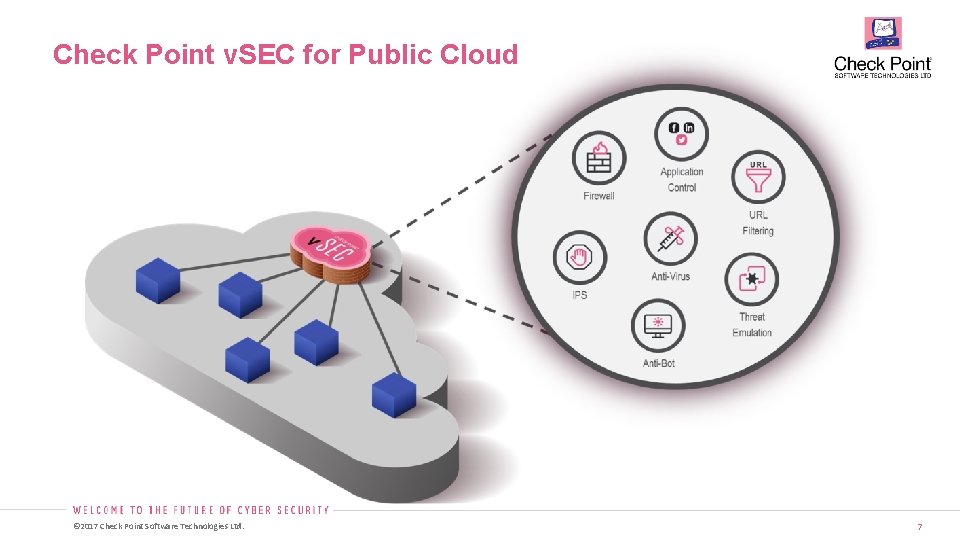
Check Point v. SEC for Public Cloud © 2017 Check Point Software Technologies Ltd. 7
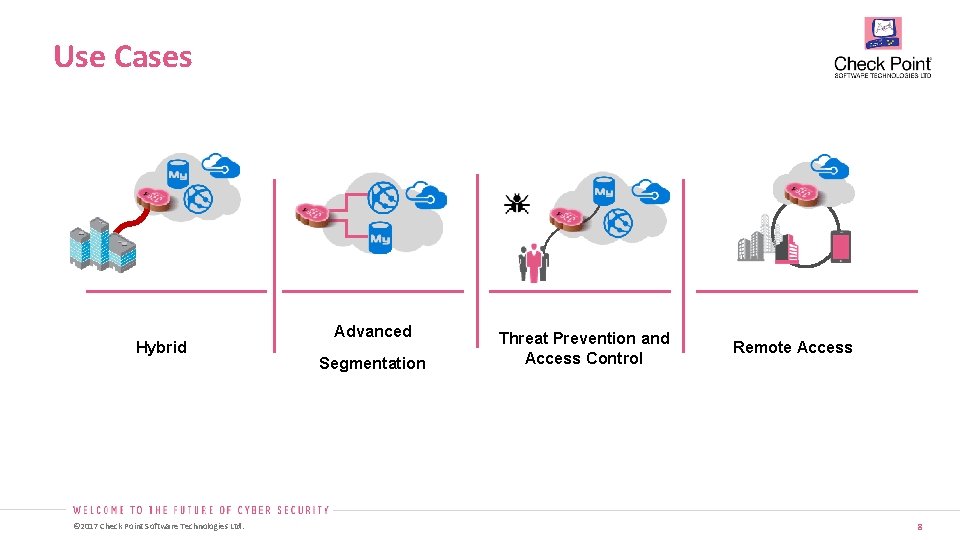
Use Cases Hybrid © 2017 Check Point Software Technologies Ltd. Advanced Segmentation Threat Prevention and Access Control Remote Access 8
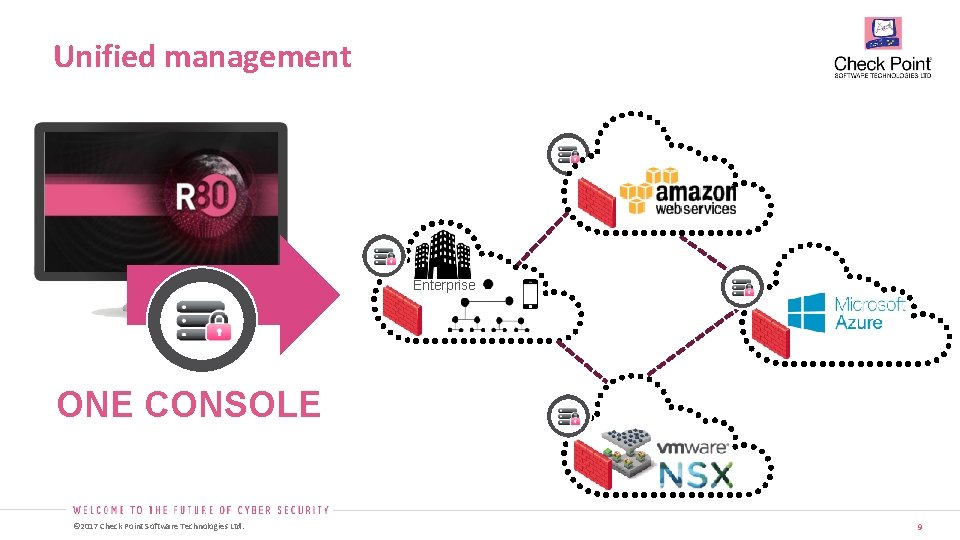
Unified management Enterprise ONE CONSOLE © 2017 Check Point Software Technologies Ltd. 9
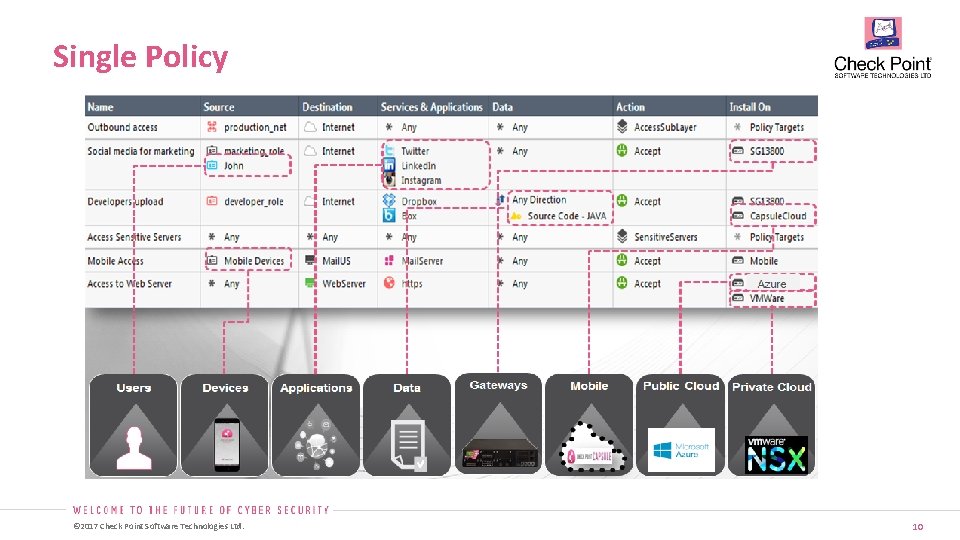
Single Policy © 2017 Check Point Software Technologies Ltd. 10
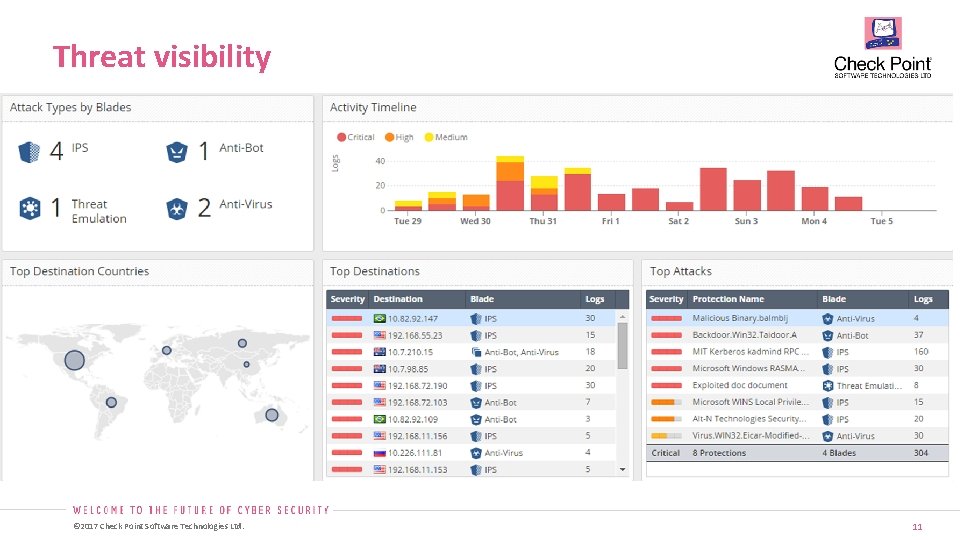
Threat visibility © 2017 Check Point Software Technologies Ltd. 11
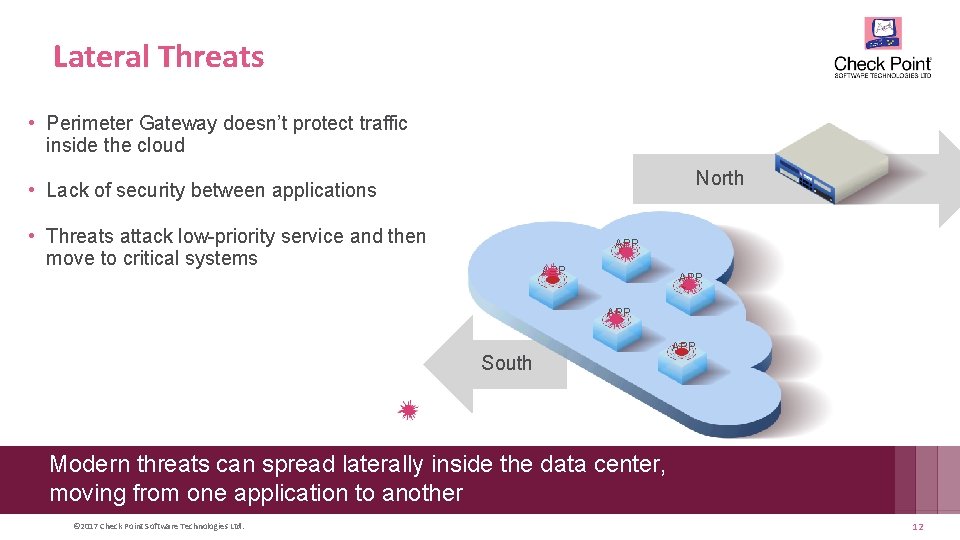
Lateral Threats • Perimeter Gateway doesn’t protect traffic inside the cloud North • Lack of security between applications • Threats attack low-priority service and then move to critical systems APP APP South APP Modern threats can spread laterally inside the data center, moving from one application to another © 2017 Check Point Software Technologies Ltd. 12
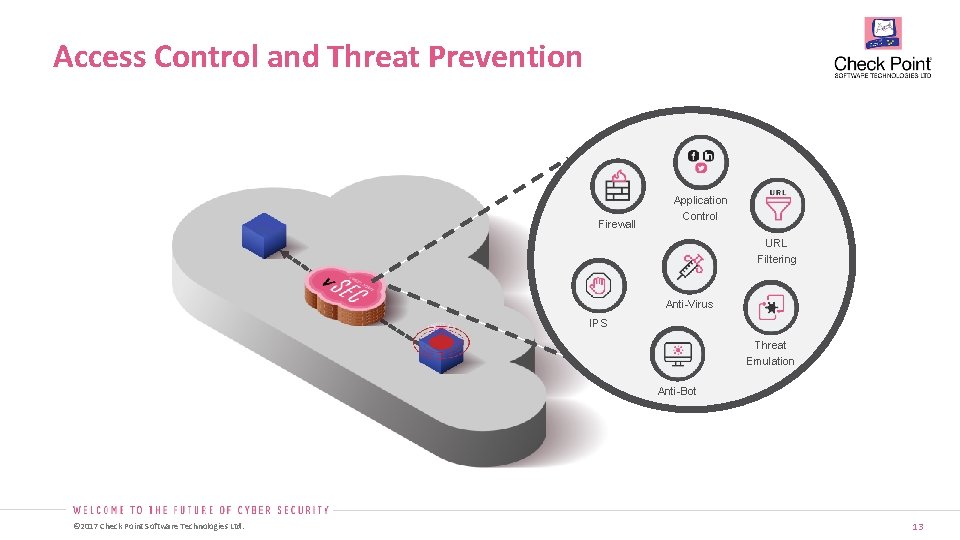
Access Control and Threat Prevention Firewall Application Control URL Filtering Anti-Virus IPS Threat Emulation Anti-Bot © 2017 Check Point Software Technologies Ltd. 13
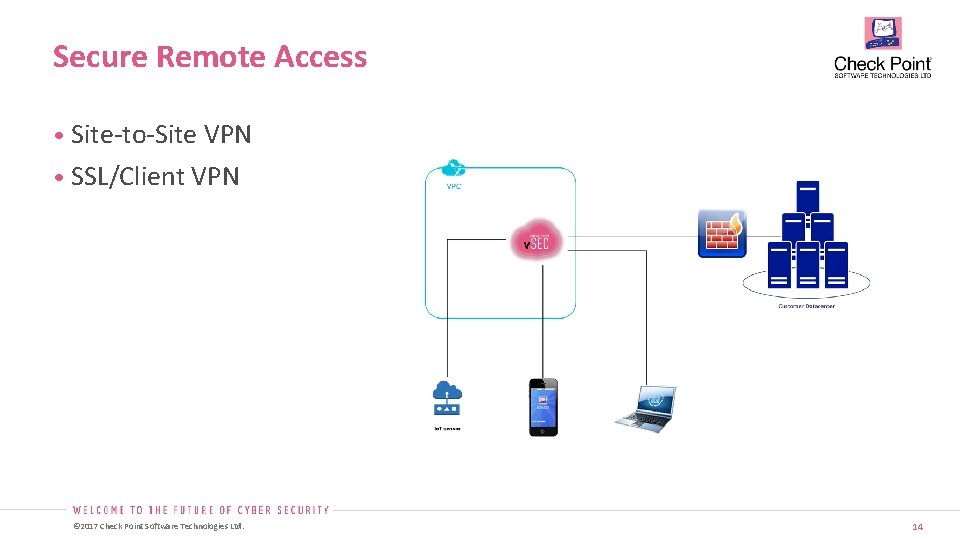
Secure Remote Access • Site-to-Site VPN • SSL/Client VPN © 2017 Check Point Software Technologies Ltd. 14
Public Cloud integrations • Marketplace • Licensing (BYOL, PAYG) • Deployment Templates (ARM, Cloud. Formation, Cloud Launcher) • Scenarios High Availability Load Balancer Support Autoscale License Pool VPN connectivity Architecture • v. SEC controller © 2017 Check Point Software Technologies Ltd. 15
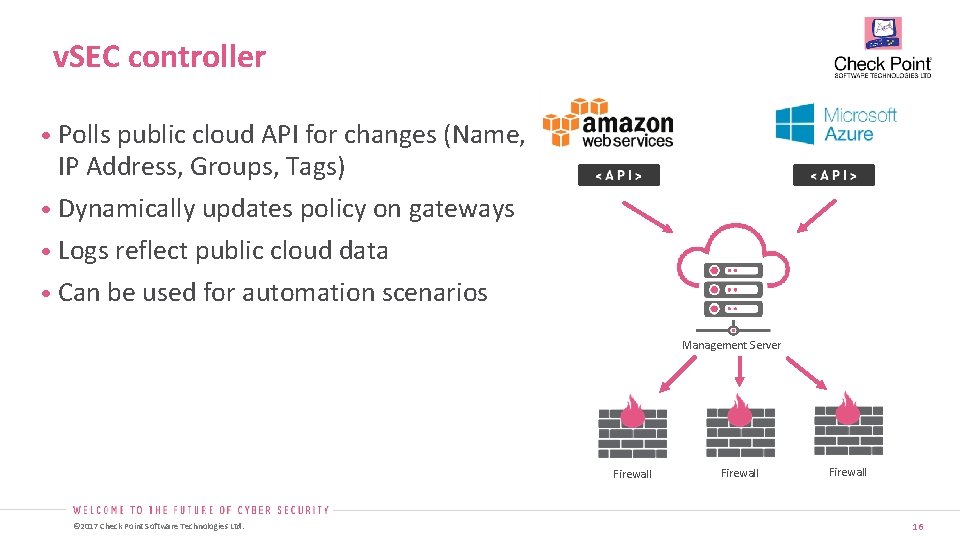
v. SEC controller • Polls public cloud API for changes (Name, IP Address, Groups, Tags) • Dynamically updates policy on gateways • Logs reflect public cloud data • Can be used for automation scenarios Management Server Firewall © 2017 Check Point Software Technologies Ltd. Firewall 16
DEMO – CONTROLLER © 2017 Check Point Software Technologies Ltd. SECURITY CHECK UP AND VSEC
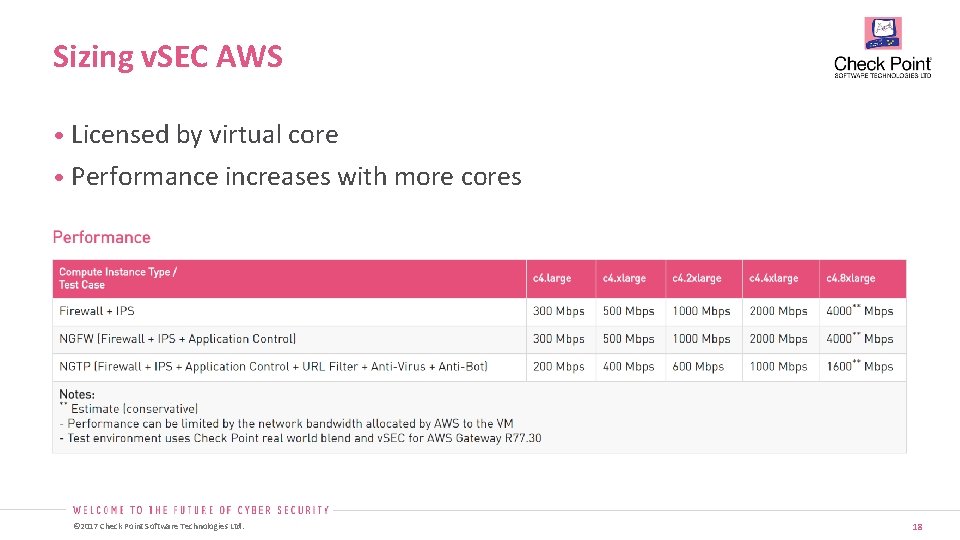
Sizing v. SEC AWS • Licensed by virtual core • Performance increases with more cores © 2017 Check Point Software Technologies Ltd. 18
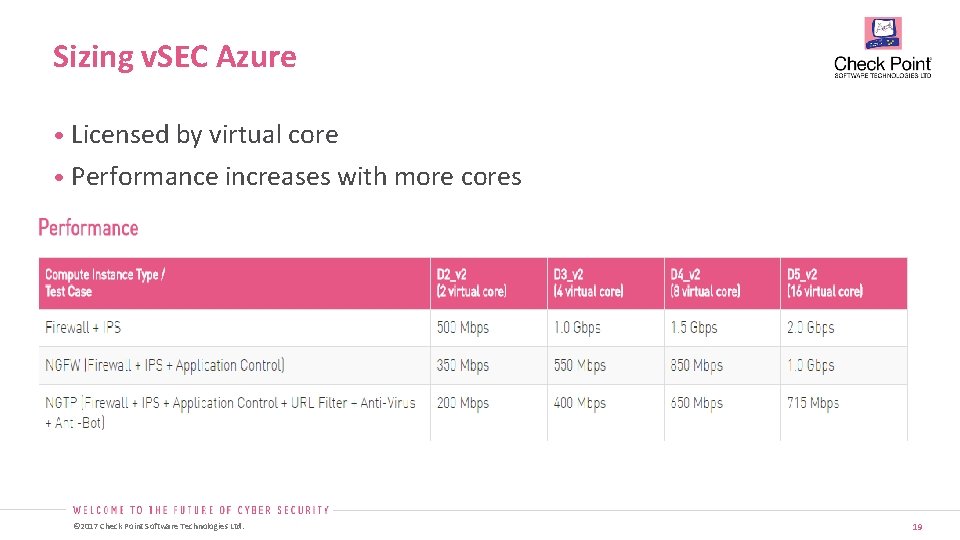
Sizing v. SEC Azure • Licensed by virtual core • Performance increases with more cores © 2017 Check Point Software Technologies Ltd. 19
ARCHITECTURE - AZURE © 2017 Check Point Software Technologies Ltd.
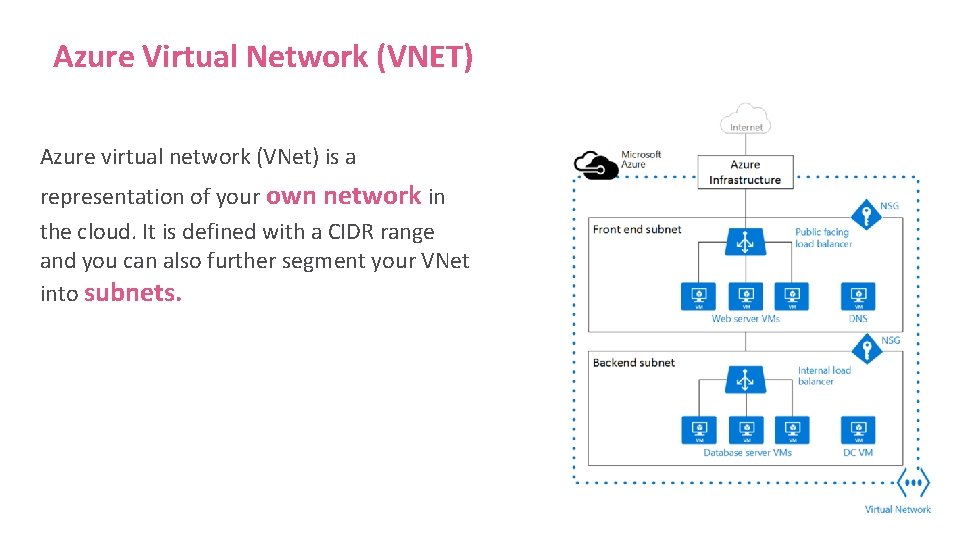
Azure Virtual Network (VNET) Azure virtual network (VNet) is a representation of your own network in the cloud. It is defined with a CIDR range and you can also further segment your VNet into subnets.
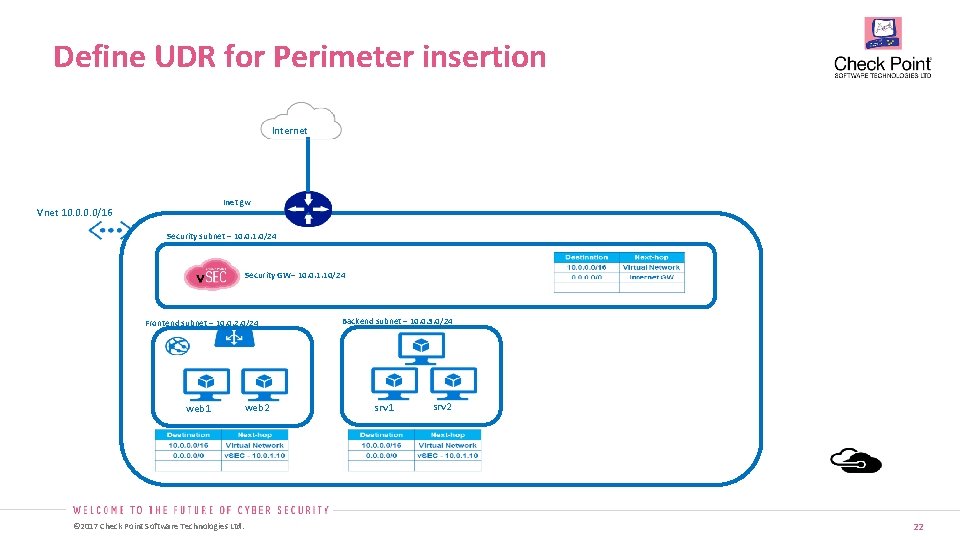
Define UDR for Perimeter insertion Internet Inet gw Vnet 10. 0/16 Security subnet – 10. 0. 1. 0/24 Security GW– 10. 0. 1. 10/24 Frontend subnet – 10. 0. 2. 0/24 web 1 web 2 © 2017 Check Point Software Technologies Ltd. Backend subnet – 10. 0. 3. 0/24 srv 1 srv 2 22
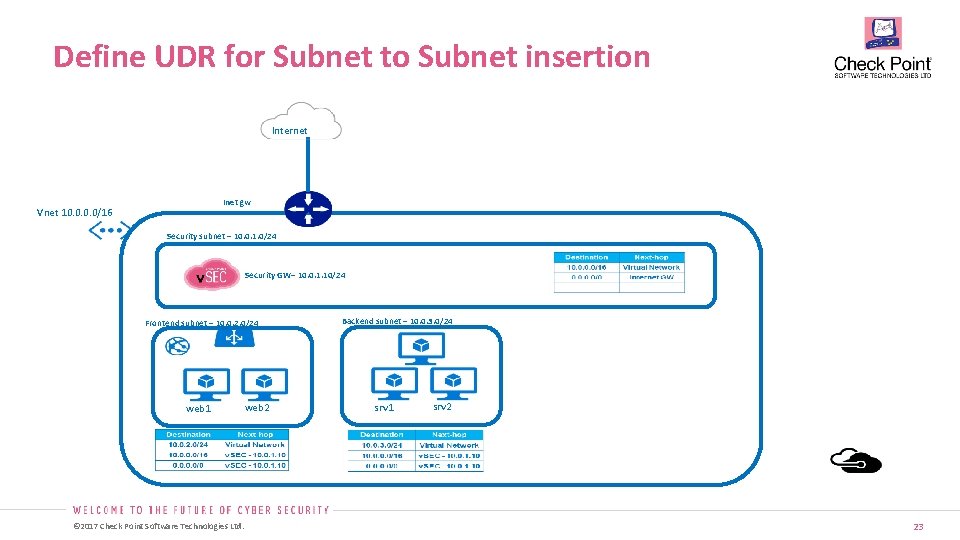
Define UDR for Subnet to Subnet insertion Internet Inet gw Vnet 10. 0/16 Security subnet – 10. 0. 1. 0/24 Security GW– 10. 0. 1. 10/24 Frontend subnet – 10. 0. 2. 0/24 web 1 web 2 © 2017 Check Point Software Technologies Ltd. Backend subnet – 10. 0. 3. 0/24 srv 1 srv 2 23
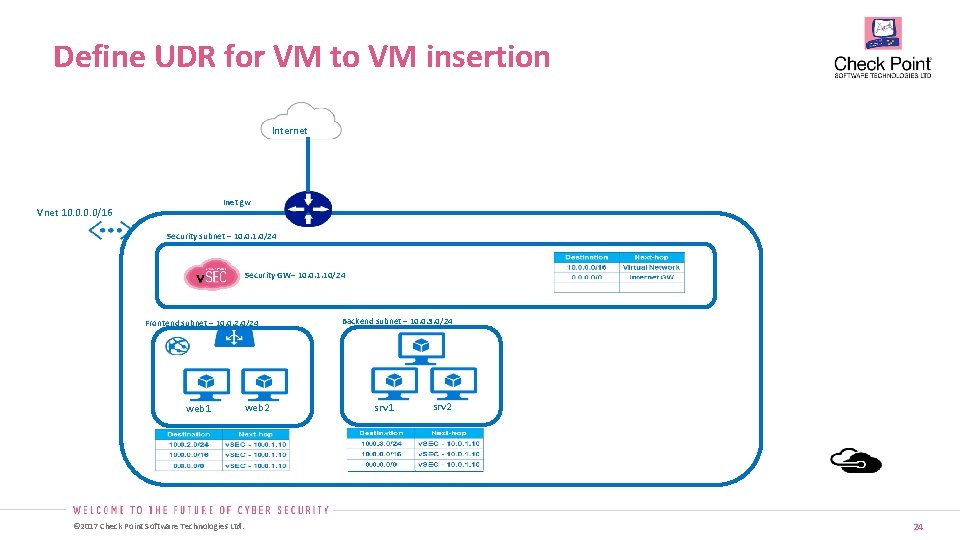
Define UDR for VM to VM insertion Internet Inet gw Vnet 10. 0/16 Security subnet – 10. 0. 1. 0/24 Security GW– 10. 0. 1. 10/24 Frontend subnet – 10. 0. 2. 0/24 web 1 web 2 © 2017 Check Point Software Technologies Ltd. Backend subnet – 10. 0. 3. 0/24 srv 1 srv 2 24
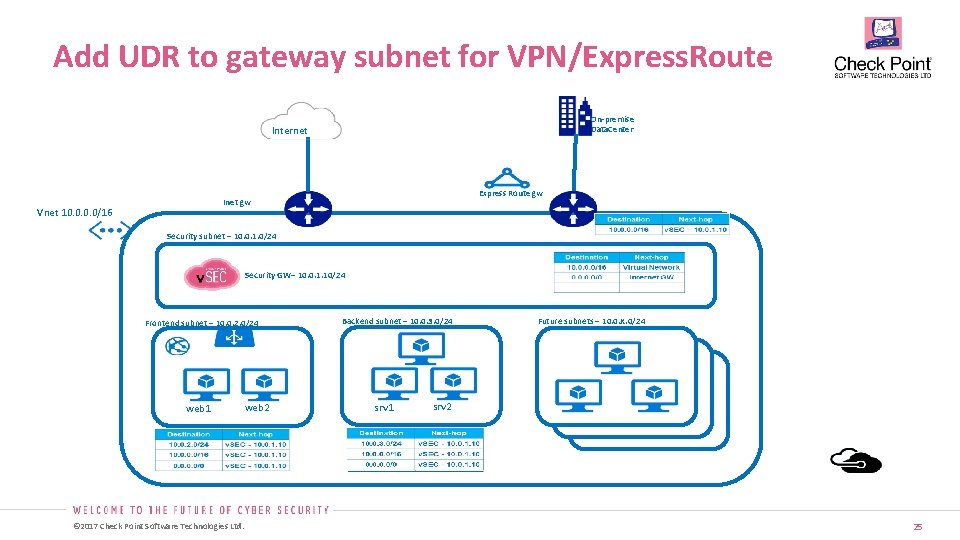
Add UDR to gateway subnet for VPN/Express. Route On-premise Data. Center Internet Express Route gw Inet gw Vnet 10. 0/16 Security subnet – 10. 0. 1. 0/24 Security GW– 10. 0. 1. 10/24 Frontend subnet – 10. 0. 2. 0/24 web 1 web 2 © 2017 Check Point Software Technologies Ltd. Backend subnet – 10. 0. 3. 0/24 srv 1 srv 2 Future subnets – 10. 0. X. 0/24 srv 1 srv 2 25
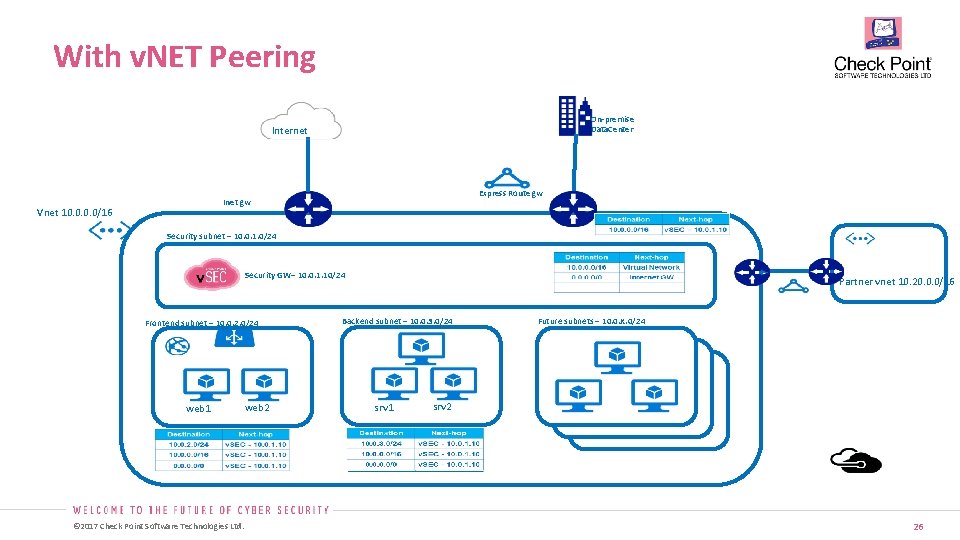
With v. NET Peering On-premise Data. Center Internet Express Route gw Inet gw Vnet 10. 0/16 Security subnet – 10. 0. 1. 0/24 Security GW– 10. 0. 1. 10/24 Frontend subnet – 10. 0. 2. 0/24 web 1 web 2 © 2017 Check Point Software Technologies Ltd. Partner vnet 10. 20. 0. 0/16 Backend subnet – 10. 0. 3. 0/24 srv 1 srv 2 Future subnets – 10. 0. X. 0/24 srv 1 srv 2 26
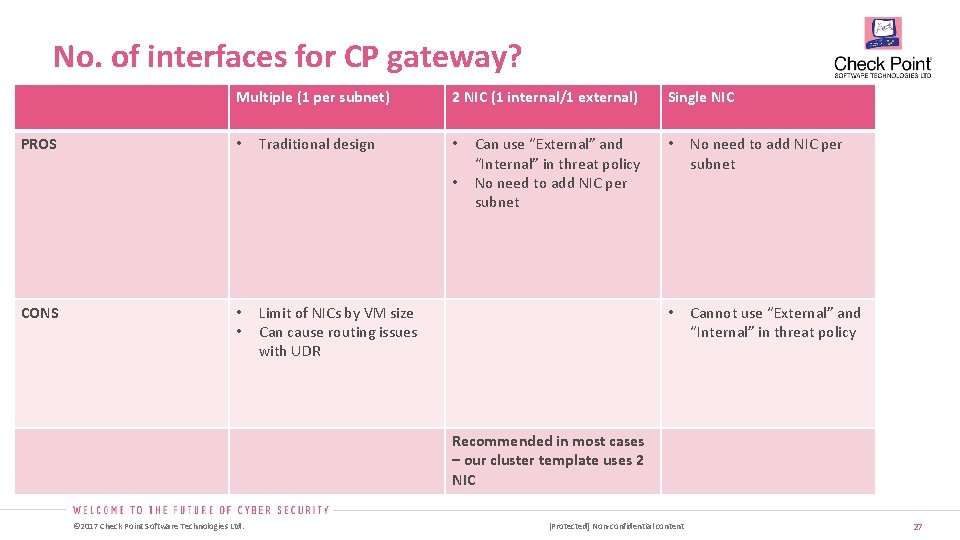
No. of interfaces for CP gateway? Multiple (1 per subnet) PROS • Traditional design 2 NIC (1 internal/1 external) • • CONS • • Can use “External” and “Internal” in threat policy No need to add NIC per subnet Limit of NICs by VM size Can cause routing issues with UDR Single NIC • No need to add NIC per subnet • Cannot use “External” and “Internal” in threat policy Recommended in most cases – our cluster template uses 2 NIC © 2017 Check Point Software Technologies Ltd. [Protected] Non-confidential content 27
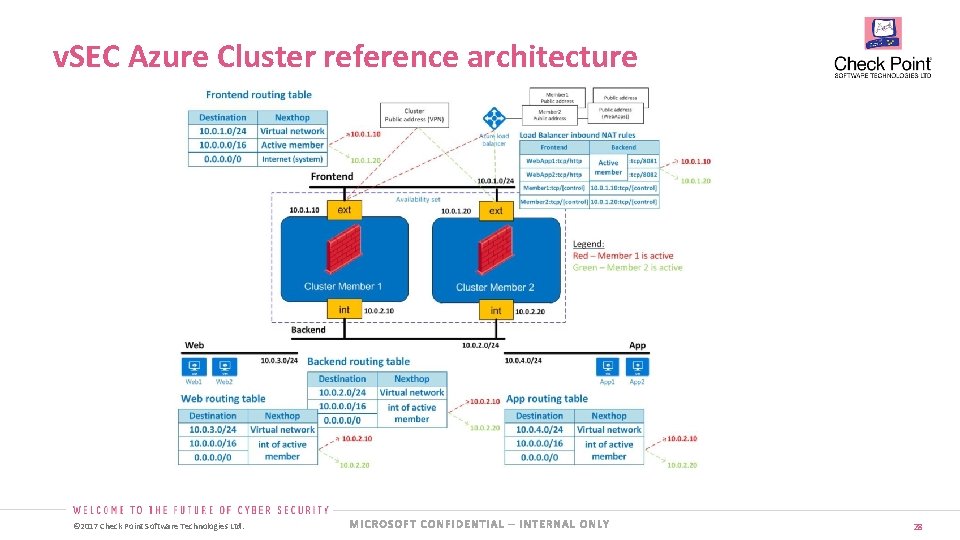
v. SEC Azure Cluster reference architecture © 2017 Check Point Software Technologies Ltd. 28
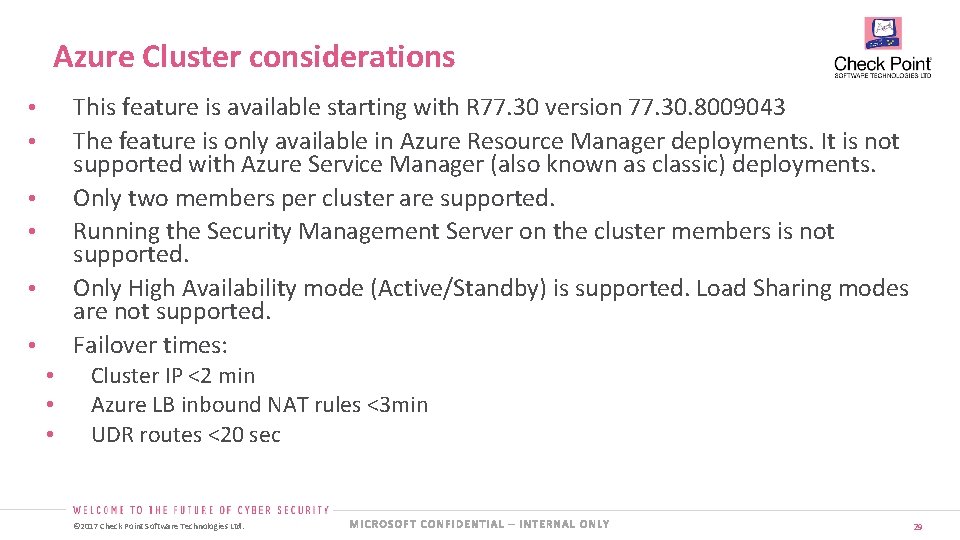
Azure Cluster considerations This feature is available starting with R 77. 30 version 77. 30. 8009043 The feature is only available in Azure Resource Manager deployments. It is not supported with Azure Service Manager (also known as classic) deployments. Only two members per cluster are supported. Running the Security Management Server on the cluster members is not supported. Only High Availability mode (Active/Standby) is supported. Load Sharing modes are not supported. Failover times: • • • Cluster IP <2 min Azure LB inbound NAT rules <3 min UDR routes <20 sec © 2017 Check Point Software Technologies Ltd. 29
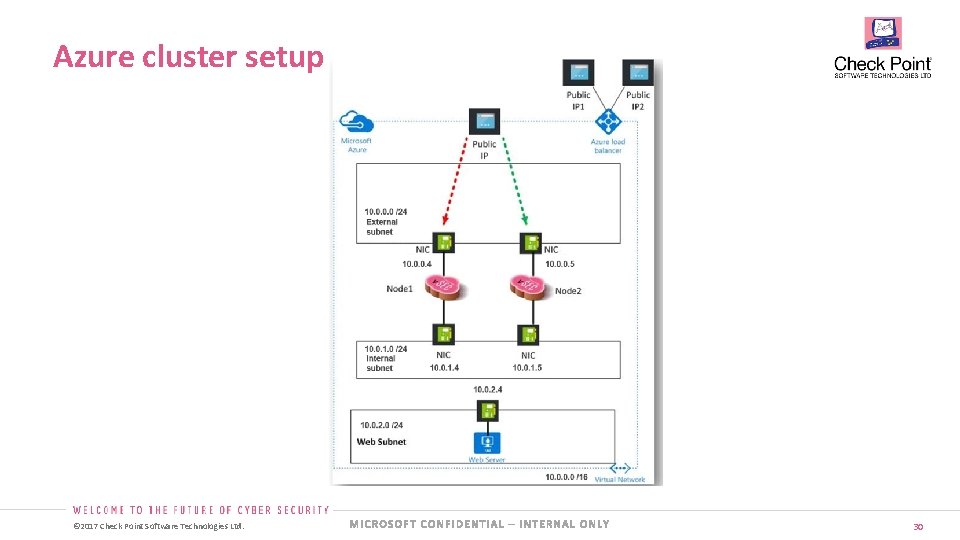
Azure cluster setup © 2017 Check Point Software Technologies Ltd. 30
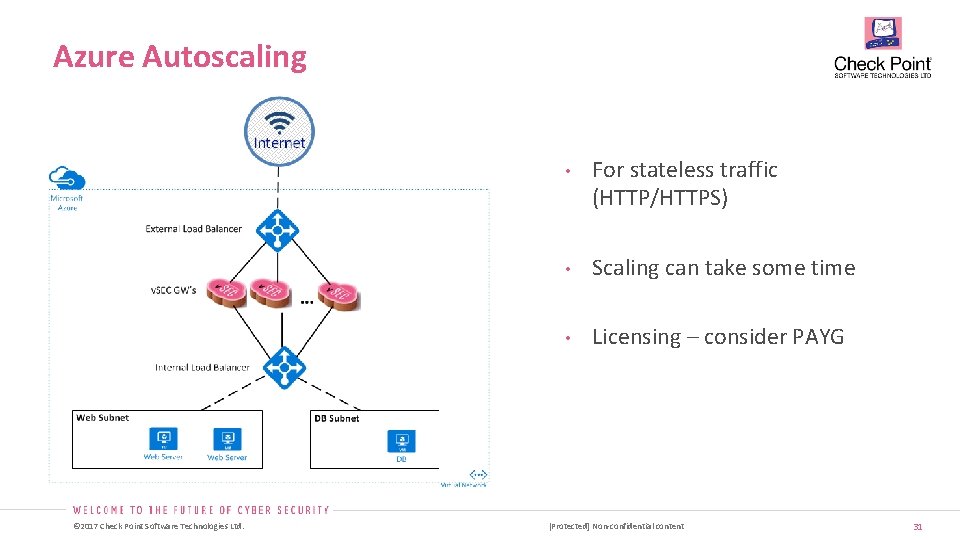
Azure Autoscaling • © 2017 Check Point Software Technologies Ltd. For stateless traffic (HTTP/HTTPS) • Scaling can take some time • Licensing – consider PAYG [Protected] Non-confidential content 31
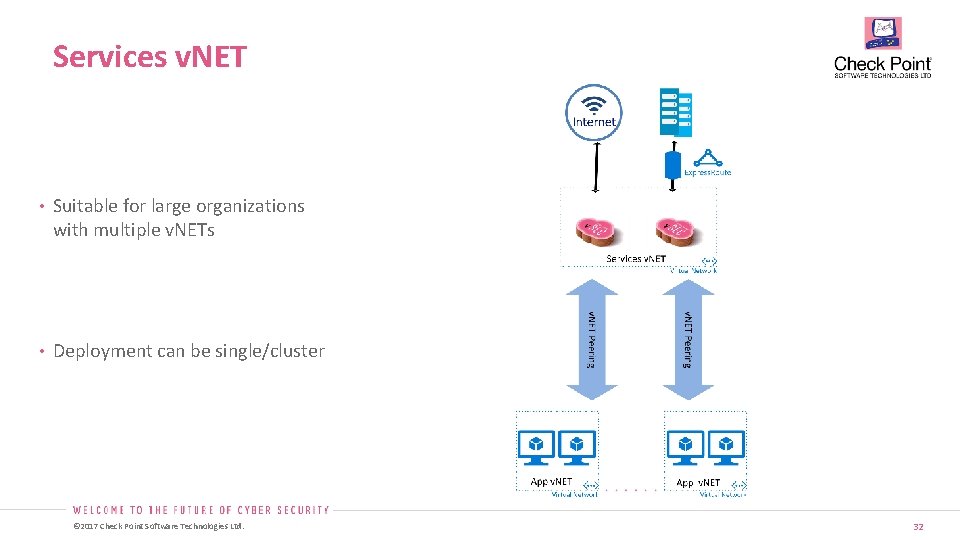
Services v. NET • Suitable for large organizations with multiple v. NETs • Deployment can be single/cluster © 2017 Check Point Software Technologies Ltd. 32
ARCHITECTURE - AWS © 2017 Check Point Software Technologies Ltd.
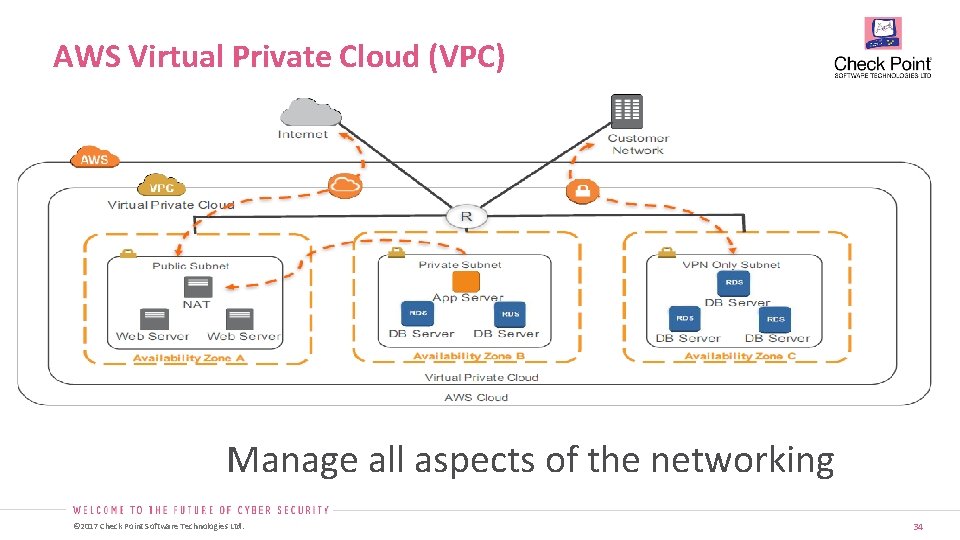
AWS Virtual Private Cloud (VPC) Manage all aspects of the networking © 2017 Check Point Software Technologies Ltd. 34
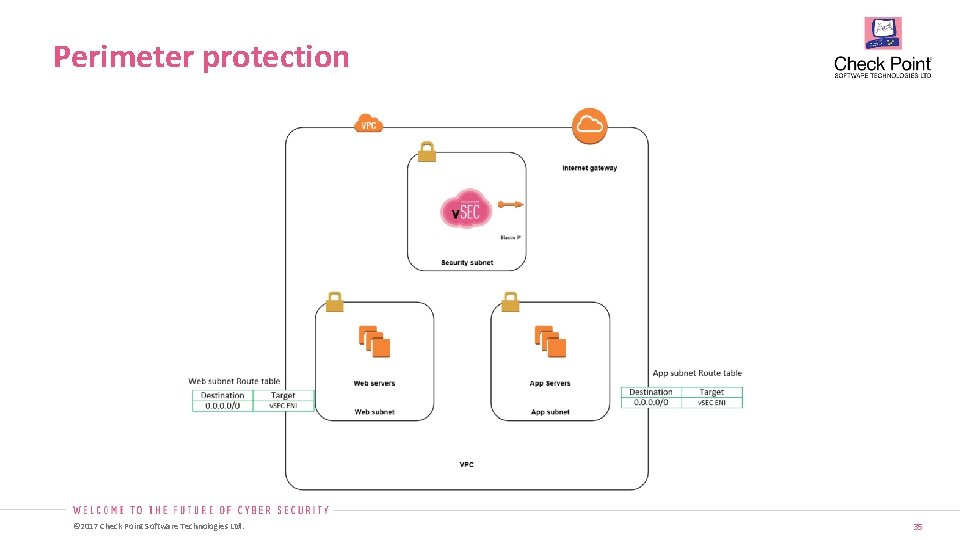
Perimeter protection © 2017 Check Point Software Technologies Ltd. 35
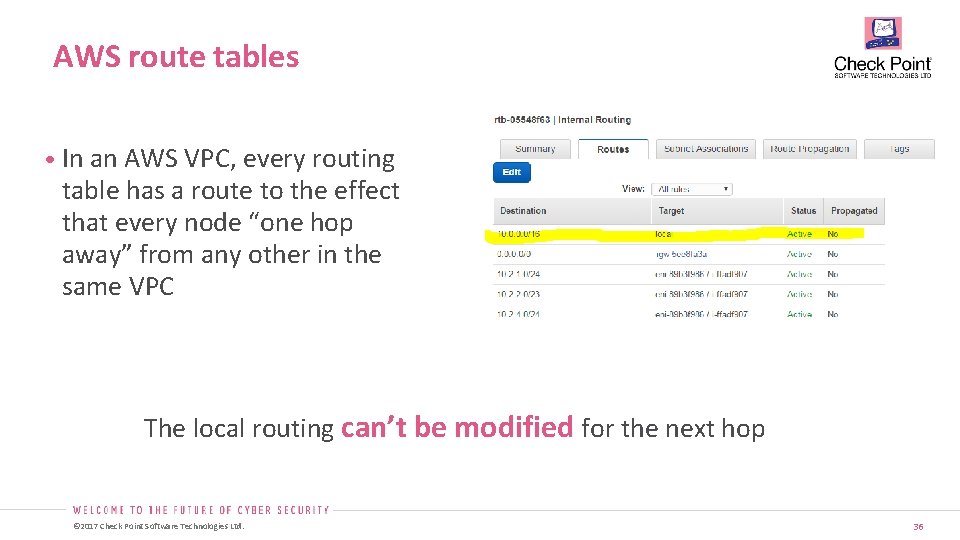
AWS route tables • In an AWS VPC, every routing table has a route to the effect that every node “one hop away” from any other in the same VPC The local routing can’t be modified for the next hop © 2017 Check Point Software Technologies Ltd. 36
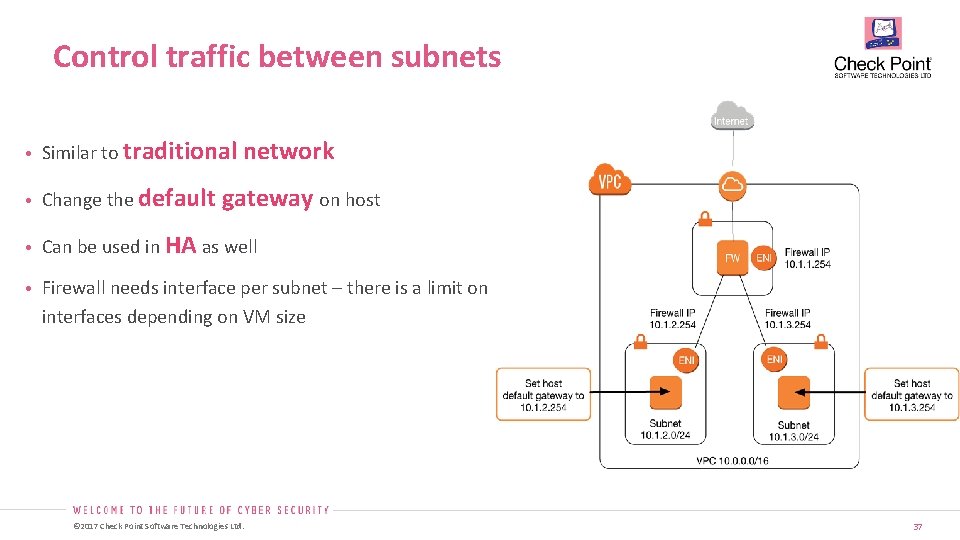
Control traffic between subnets • Similar to traditional network • Change the default gateway on host • Can be used in HA as well • Firewall needs interface per subnet – there is a limit on interfaces depending on VM size © 2017 Check Point Software Technologies Ltd. 37
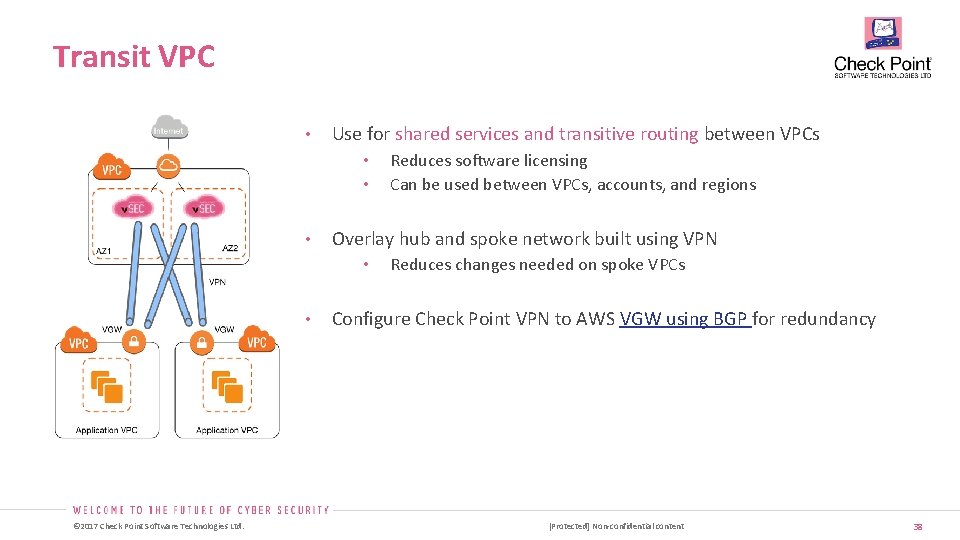
Transit VPC • Use for shared services and transitive routing between VPCs • • • Overlay hub and spoke network built using VPN • • © 2017 Check Point Software Technologies Ltd. Reduces software licensing Can be used between VPCs, accounts, and regions Reduces changes needed on spoke VPCs Configure Check Point VPN to AWS VGW using BGP for redundancy [Protected] Non-confidential content 38
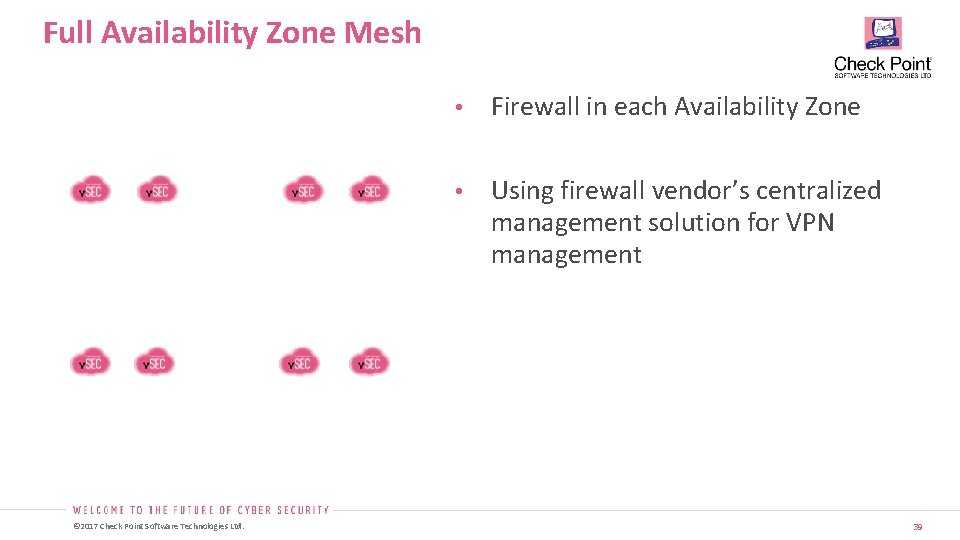
Full Availability Zone Mesh © 2017 Check Point Software Technologies Ltd. • Firewall in each Availability Zone • Using firewall vendor’s centralized management solution for VPN management 39
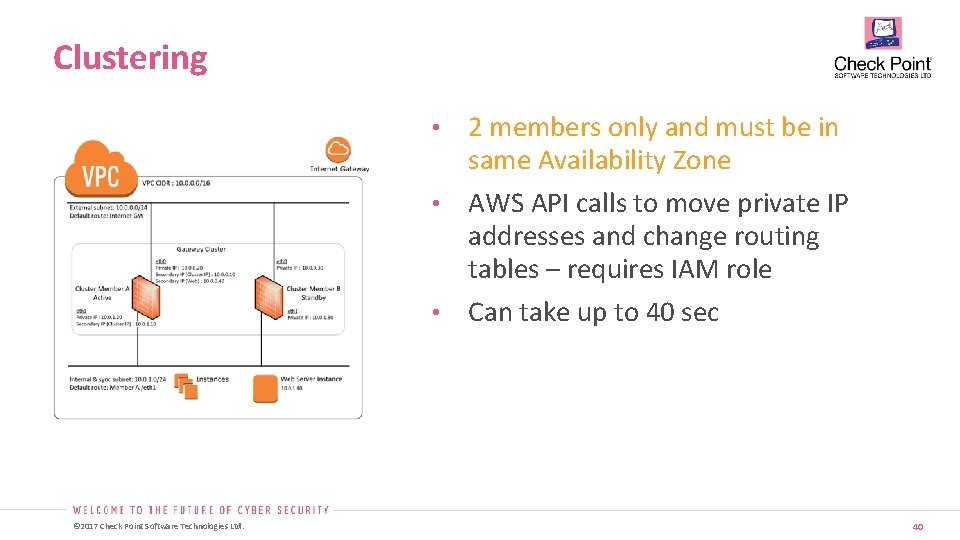
Clustering 2 members only and must be in same Availability Zone • AWS API calls to move private IP addresses and change routing tables – requires IAM role • Can take up to 40 sec • © 2017 Check Point Software Technologies Ltd. 40
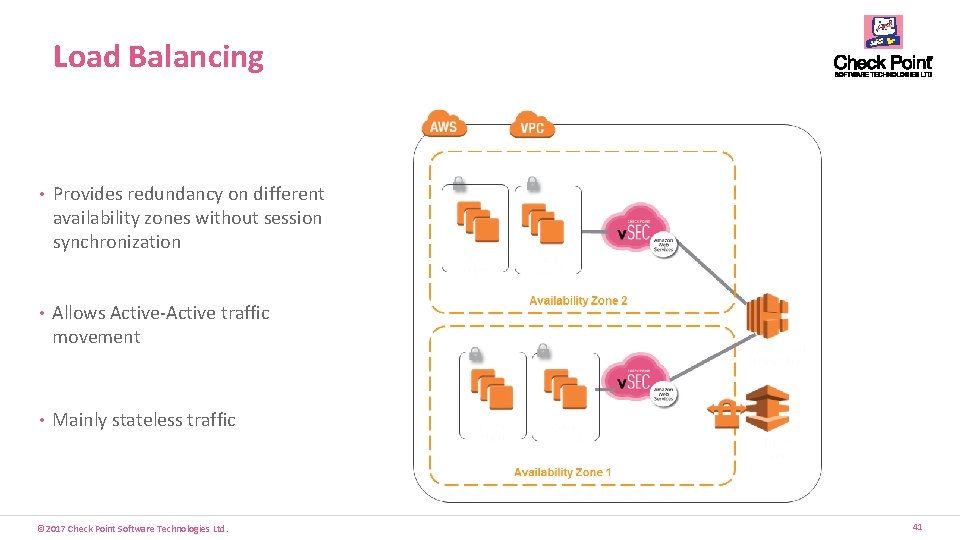
Load Balancing • Provides redundancy on different availability zones without session synchronization • Allows Active-Active traffic movement • Mainly stateless traffic © 2017 Check Point Software Technologies Ltd. 41
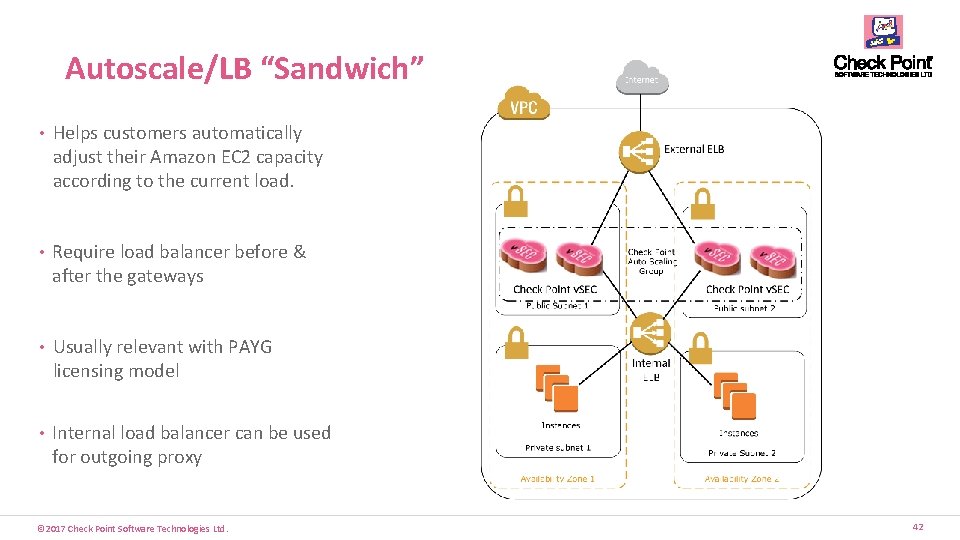
Autoscale/LB “Sandwich” • Helps customers automatically adjust their Amazon EC 2 capacity according to the current load. • Require load balancer before & after the gateways • Usually relevant with PAYG licensing model • Internal load balancer can be used for outgoing proxy © 2017 Check Point Software Technologies Ltd. 42

COMPARISONS © 2017 Check Point Software Technologies Ltd.
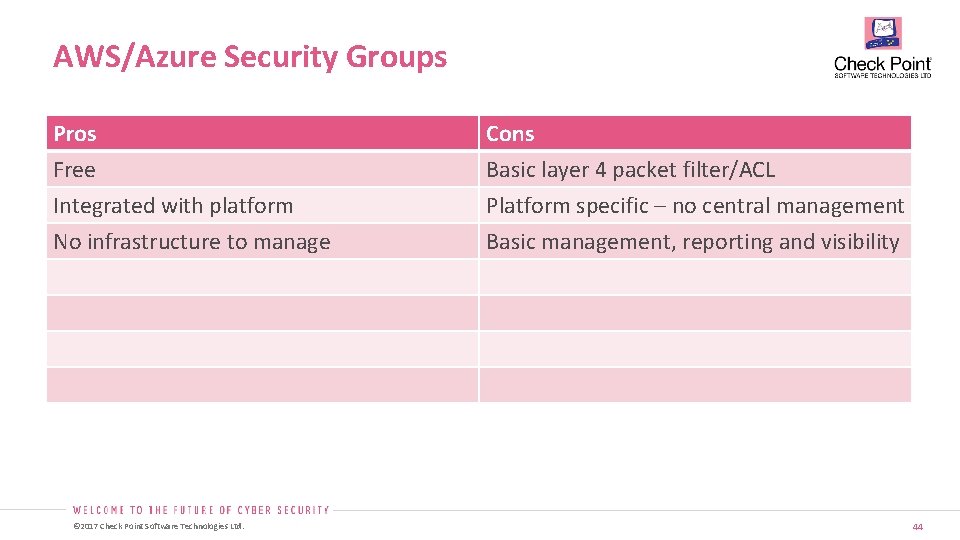
AWS/Azure Security Groups Pros Free Integrated with platform No infrastructure to manage © 2017 Check Point Software Technologies Ltd. Cons Basic layer 4 packet filter/ACL Platform specific – no central management Basic management, reporting and visibility 44
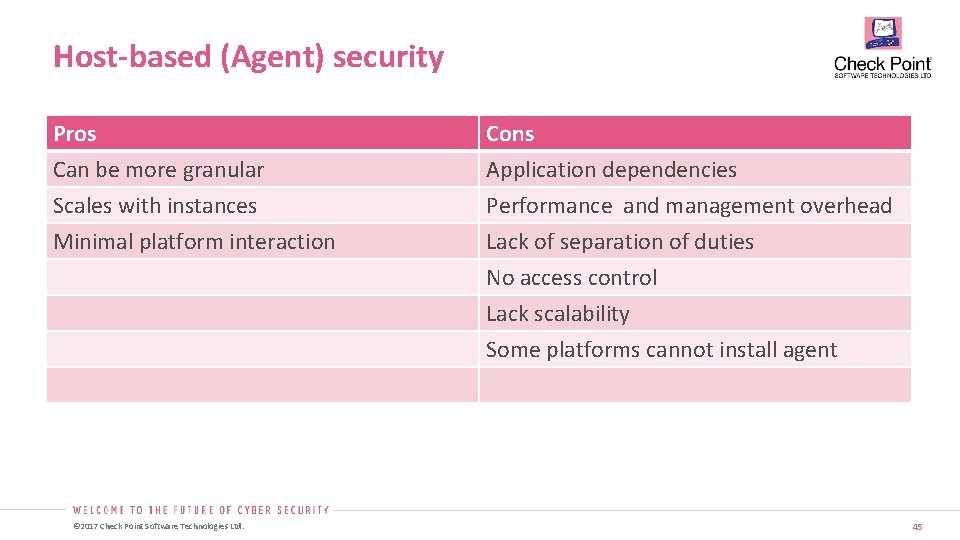
Host-based (Agent) security Pros Can be more granular Scales with instances Minimal platform interaction Cons Application dependencies Performance and management overhead Lack of separation of duties No access control Lack scalability Some platforms cannot install agent © 2017 Check Point Software Technologies Ltd. 45
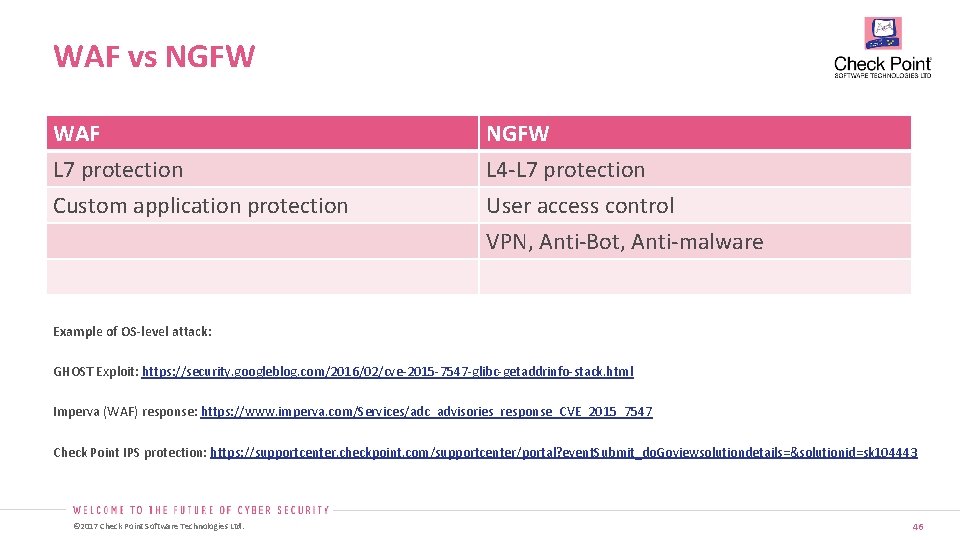
WAF vs NGFW WAF L 7 protection Custom application protection NGFW L 4 -L 7 protection User access control VPN, Anti-Bot, Anti-malware Example of OS-level attack: GHOST Exploit: https: //security. googleblog. com/2016/02/cve-2015 -7547 -glibc-getaddrinfo-stack. html Imperva (WAF) response: https: //www. imperva. com/Services/adc_advisories_response_CVE_2015_7547 Check Point IPS protection: https: //supportcenter. checkpoint. com/supportcenter/portal? event. Submit_do. Goviewsolutiondetails=&solutionid=sk 104443 © 2017 Check Point Software Technologies Ltd. 46
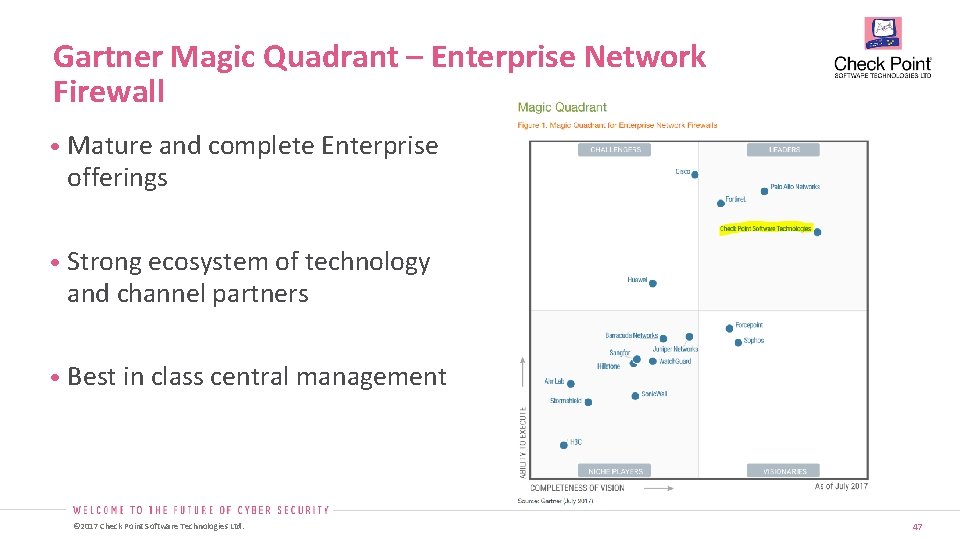
Gartner Magic Quadrant – Enterprise Network Firewall • Mature and complete Enterprise offerings • Strong ecosystem of technology and channel partners • Best in class central management © 2017 Check Point Software Technologies Ltd. 47
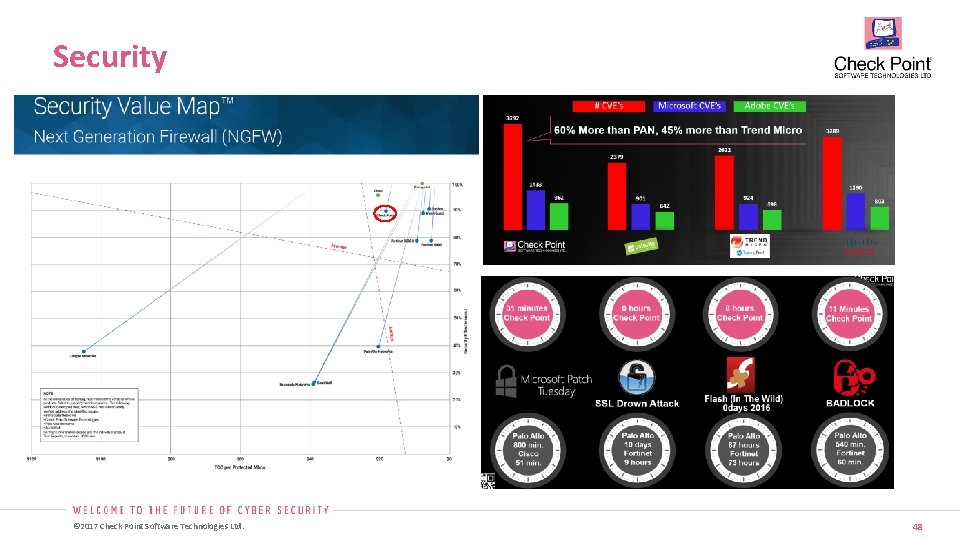
Security © 2017 Check Point Software Technologies Ltd. 48
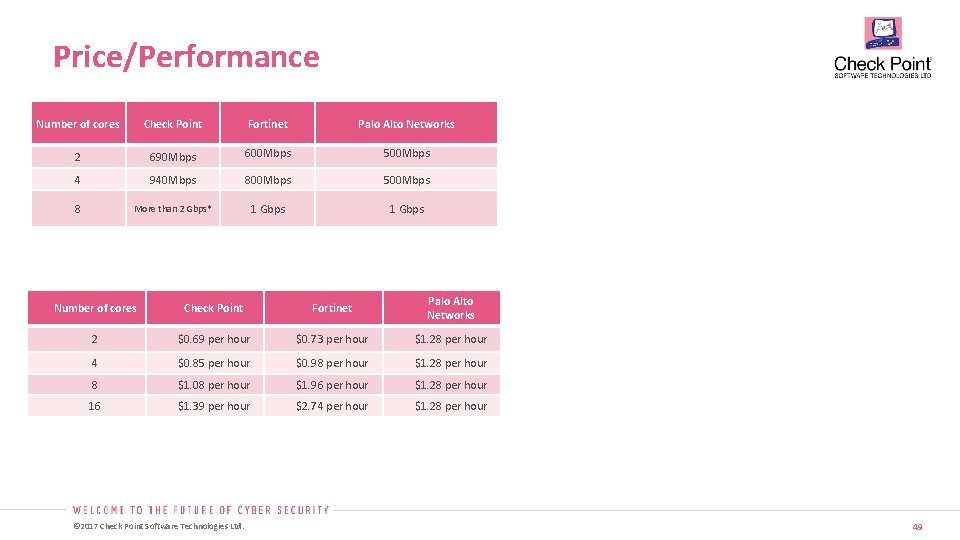
Price/Performance Number of cores Check Point Fortinet Palo Alto Networks 2 690 Mbps 600 Mbps 500 Mbps 4 940 Mbps 800 Mbps 500 Mbps 8 More than 2 Gbps* 1 Gbps Number of cores Check Point Fortinet Palo Alto Networks 2 $0. 69 per hour $0. 73 per hour $1. 28 per hour 4 $0. 85 per hour $0. 98 per hour $1. 28 per hour 8 $1. 08 per hour $1. 96 per hour $1. 28 per hour 16 $1. 39 per hour $2. 74 per hour $1. 28 per hour © 2017 Check Point Software Technologies Ltd. 49
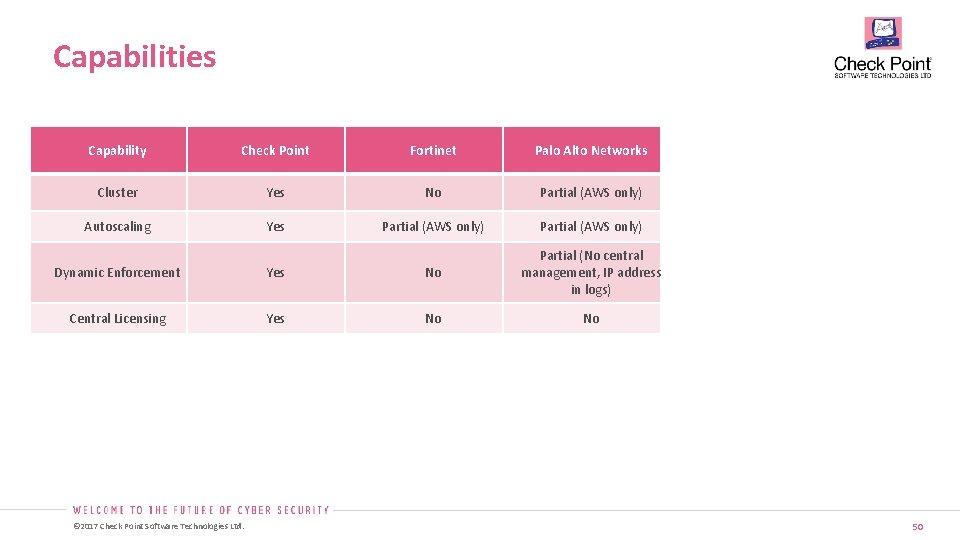
Capabilities Capability Check Point Fortinet Palo Alto Networks Cluster Yes No Partial (AWS only) Autoscaling Yes Partial (AWS only) Dynamic Enforcement Yes No Partial (No central management, IP address in logs) Central Licensing Yes No No © 2017 Check Point Software Technologies Ltd. 50
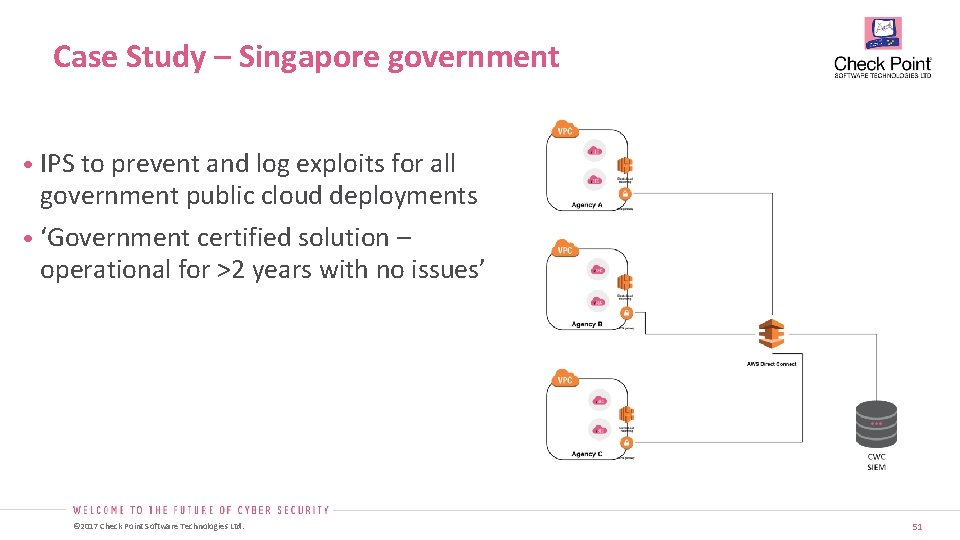
Case Study – Singapore government • IPS to prevent and log exploits for all government public cloud deployments • ‘Government certified solution – operational for >2 years with no issues’ © 2017 Check Point Software Technologies Ltd. 51

Q&A © 2017 Check Point Software Technologies Ltd.

CCVSA CERTIFICATION EXAM © 2017 Check Point Software Technologies Ltd. 53
CCVSA • What is CCVSA ? Check Point Certified v. SEC Administrator • How do I go through the exam Go through the 2 day training of CCVSA Get a voucher from your trainer Surf to this link - http: //tiny. cc/CCVSA https: //www. classmarker. com/onlinetest/start/? quiz=fnt 58 a 2 f 0 bb 363 d 7 Enter the voucher you have received Complete the personal information © 2017 Check Point Software Technologies Ltd. Good Luck 54
© 2017 Check Point Software Technologies Ltd. 55
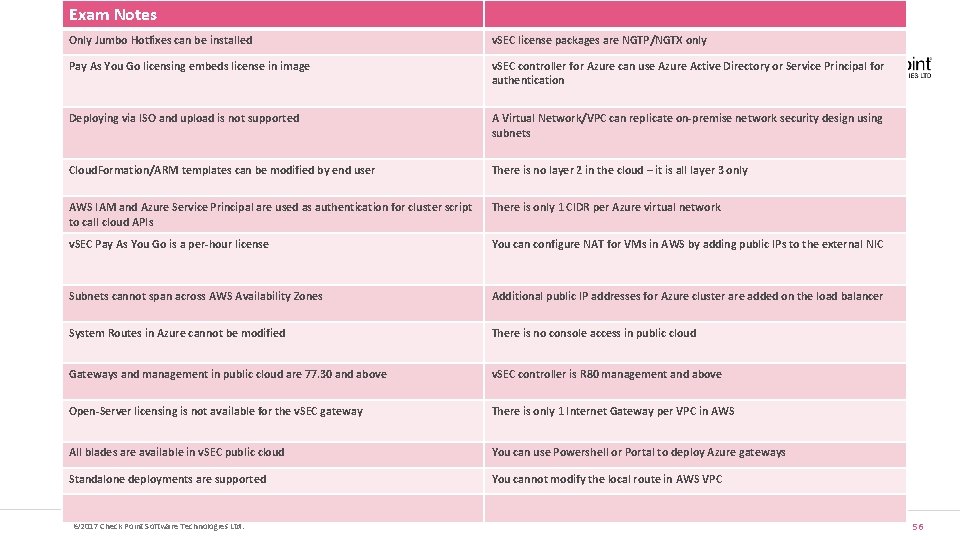
Exam Notes Only Jumbo Hotfixes can be installed v. SEC license packages are NGTP/NGTX only Pay As You Go licensing embeds license in image v. SEC controller for Azure can use Azure Active Directory or Service Principal for authentication Deploying via ISO and upload is not supported A Virtual Network/VPC can replicate on-premise network security design using subnets Cloud. Formation/ARM templates can be modified by end user There is no layer 2 in the cloud – it is all layer 3 only AWS IAM and Azure Service Principal are used as authentication for cluster script to call cloud APIs There is only 1 CIDR per Azure virtual network v. SEC Pay As You Go is a per-hour license You can configure NAT for VMs in AWS by adding public IPs to the external NIC Subnets cannot span across AWS Availability Zones Additional public IP addresses for Azure cluster are added on the load balancer System Routes in Azure cannot be modified There is no console access in public cloud Gateways and management in public cloud are 77. 30 and above v. SEC controller is R 80 management and above Open-Server licensing is not available for the v. SEC gateway There is only 1 Internet Gateway per VPC in AWS All blades are available in v. SEC public cloud You can use Powershell or Portal to deploy Azure gateways Standalone deployments are supported You cannot modify the local route in AWS VPC © 2017 Check Point Software Technologies Ltd. 56

THANK YOU © 2017 Check Point Software Technologies Ltd. 57
- Slides: 56