Vocabulary Big Data Big data is a broad
Vocabulary • Big Data - “Big data is a broad term for datasets so large or complex that traditional data processing applications are inadequate. ” • Moore’s Law - The number of transistors one could fit on a chip will double every 18 months or so. Caesar Cipher - a technique for encryption that shifts the alphabet by some number of characters Cipher - the generic term for a technique (or algorithm) that performs encryption Cracking encryption - When you attempt to decode a secret message without knowing all the specifics of the cipher, you are trying to "crack" the encryption. Decryption - a process that reverses encryption, taking a secret message and reproducing the original plain text Encryption - a process of encoding messages to keep them secret, so only "authorized" parties can read it. Random Substitution Cipher - an encryption technique that maps each letter of the alphabet to a randomly chosen other letters of the alphabet. asymmetric encryption - used in public key encryption, it is scheme in which the key to encrypt data is different from the key to decrypt. modulo - a mathematical operation that returns the remainder after integer division. Example: 7 MOD 4 = 3 Private Key - In an asymmetric encryption scheme the decryption key is kept private and never shared, so only the intended recipient has the ability to decrypt a message that has been encrypted with a public key. Public Key Encryption - Used prevalently on the web, it allows for secure messages to be sent between parties without having to agree on, or share, a secret key. It uses an asymmetric encryption scheme in which the encryption key is made public, but the decryption key is kept private.
CS Principles U 4 L 7: Public Key Cryptography
U 4 L 7: Public Key Cryptography Objectives SWBAT: • Explain what the modulo operation does and how it operates as a "one-way" function • Follow an asymmetric encryption algorithm to encrypt a numerical message using the Public Key Crypto widget. • Explain the difference between symmetric and asymmetric encryption. • Describe the basic process of encrypting data using public key encryption • Explain the benefits of public key cryptography
U 4 L 7 Vocabulary asymmetric encryption - used in public key encryption, it is scheme in which the key to encrypt data is different from the key to decrypt. modulo - a mathematical operation that returns the remainder after integer division. Example: 7 MOD 4 = 3 Private Key - In an asymmetric encryption scheme the decryption key is kept private and never shared, so only the intended recipient has the ability to decrypt a message that has been encrypted with a public key. Public Key Encryption - Used prevalently on the web, it allows for secure messages to be sent between parties without having to agree on, or share, a secret key. It uses an asymmetric encryption scheme in which the encryption key is made public, but the decryption key is kept private.
U 4 L 7 Prompt: “How can two people send encrypted messages to each other if they can’t communicate, or agree on an encryption key ahead of time, and the only way they have to communicate is over the Internet? ”
U 4 L 7 Content: Public Key Cryptography • To many the fact that encrypted messages can be sent between parties who have never met before is both taken for granted and opaque. • Understanding how it works with some depth - getting to experiment with the mathematical principles that make asymmetric keys possible, and the resulting encryption hard to crack - is deeply satisfying. • The widget in the lesson mimics the RSA encryption algorithm (with smaller numbers and slightly easier mathematics). RSA is an algorithm used by modern computers to encrypt and decrypt messages. • It is an asymmetric cryptographic algorithm. Asymmetric means that there are two different keys. This is also called public key cryptography, because one of them can be given to everyone. • The other key must be kept private. • It is based on the fact that finding the factors of an integer is hard. • A user of RSA creates and then publishes the product of two large prime numbers, along with an auxiliary value, as their public key. • The prime factors must be kept secret. • Anyone can use the public key to encrypt a message, but with currently published methods, if the public key is large enough, only someone with knowledge of the prime factors can feasibly decode the message.
VIDEO: Public Key Cryptography https: //www. khanacademy. org/computing/computer-science/cryptography/moderncrypt/v/diffie-hellman-key-exchange-part-1
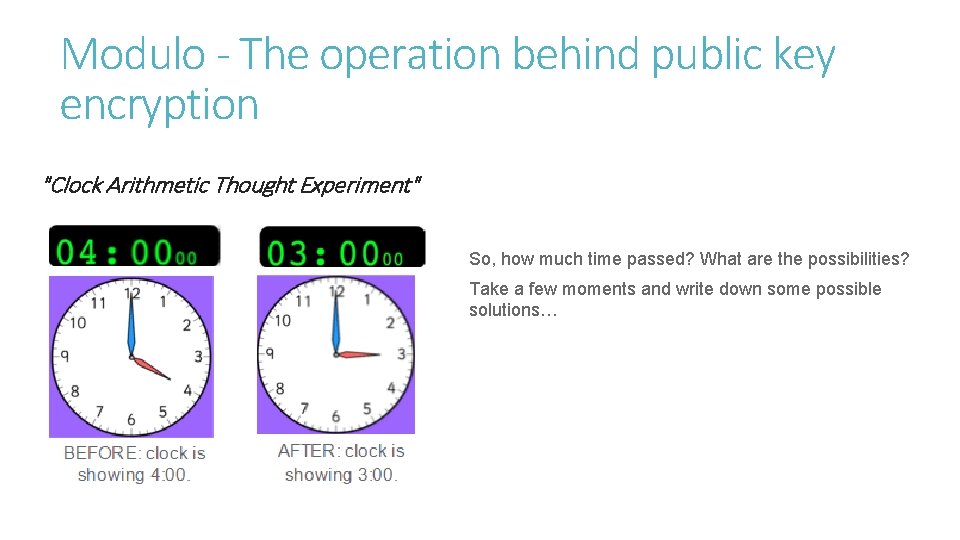
Modulo - The operation behind public key encryption "Clock Arithmetic Thought Experiment" So, how much time passed? What are the possibilities? Take a few moments and write down some possible solutions…
Clock is a metaphor for modulo Real cryptography uses this “clock” technique to obscure information, but with clocks that can have a wide range of possible values on their faces. The operation is called modulo. Modulo is a math operation that returns the remainder from dividing two integers. It is important for cryptography because it can act as a one-way function - the output obscures the input. Activity 1: Activity Guide - Multiplication + Modulo Open the activity guide, and go to Stage 5 (U 4 L 7), the modulo clock widget
The Public Key Crypto Widget Activity Real cryptography uses this “clock” technique to obscure information, but with clocks that can have a wide range of possible values on their faces. The operation is called modulo. Modulo is a math operation that returns the remainder from dividing two integers. It is important for cryptography because it can act as a one-way function - the output obscures the input. Activity 2: Activity Guide - How and Why Does the Public Key Crypto Really Work? Open the activity guide, and go to Stage 7 (U 4 L 7), the modulo clock widget
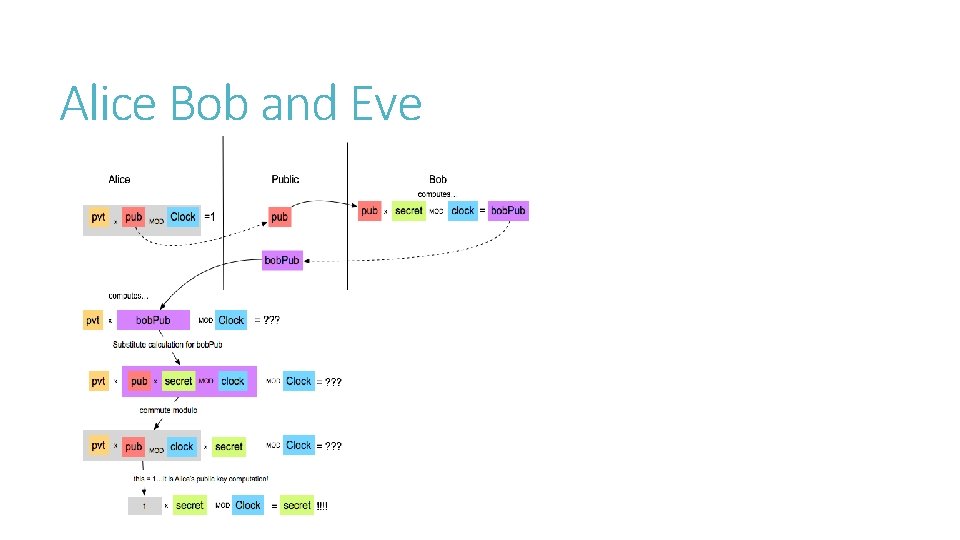
Alice Bob and Eve
U 4 L 7 Reflection Prompt: We just spent a lot of time learning about Public Key Cryptography through a bunch of different analogies, tools and activities. And what you've been exposed to mimics the real thing pretty closely. But what are the essential elements?
- Slides: 12