VME 2000 USB Token The USB Token is
VME 2000 USB Token

The USB Token is a hardware device that plugs into a USB port (or a USB cable) on a laptop or PC. It can be used instead of a pass phrase (also known as a “key”) to gain access to a computer that is protected with VME 2000 Cipher. Lock.
As you’ll see, it’s a great tool for selling VME Cipher. Lock because it adds value and security to the program and because it adds a dramatic (and cool) visual dimension to the sales presentation.
HOW DOES IT WORK? The Token contains a chip with a unique 64 -bit key that can be read by VME Cipher. Lock. 2 f{kc. Kå 4 The Token makes Cipher. Lock more secure and even easier to use!
It connects to the computer via the USB port.
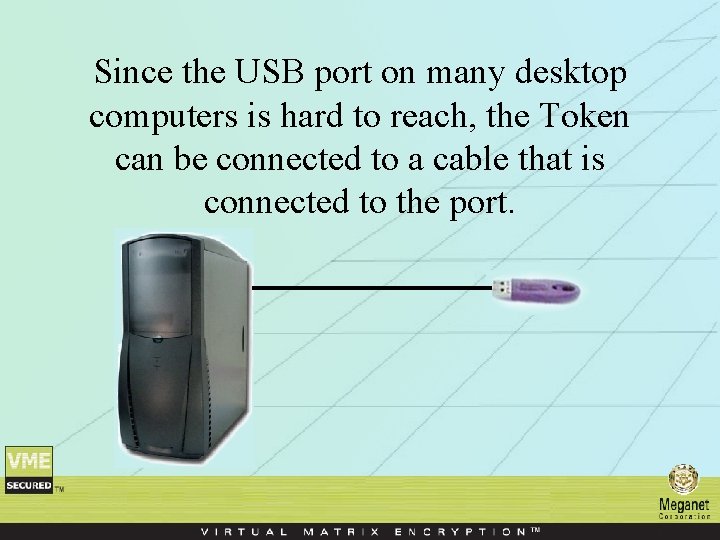
Since the USB port on many desktop computers is hard to reach, the Token can be connected to a cable that is connected to the port.

KEYS ARE USUALLY THE SINGLE LEAST SECURE ASPECT OF A DATA SECURITY SYSTEM. If they’re easy to remember: 7 -29 -51 They’re easy for a hacker to guess. If they’re hard to hack: 2 f{kc. Kåþ 4%K They’re hard to remember!
And if a key is hard to remember: Users tend to write them down and ‘hide’ them in their desks. That’s not secure! 2 f{kc. Kå 4%K
Using the USB Token with VME 2000, users don’t need to • Remember a key • Write down a key and ‘hide it’ in their desk • Waste time retrieving keys from security officers
• Users should never write down their keys, but if they don’t, they tend to forget them. Every trip to the Security Office to retrieve a forgotten key means lost productivity. In a large company, this lost time can really add up.
• With a VME 2000 USB Token, there are no keys to forget! SALES ADVANTAGE: The USB Token will save your customers MONEY.
• Good data security policy dictates that keys need to be changed, distributed and memorized every few months. This is a very expensive task, especially in a large company.

• By contrast, users need never change USB Tokens. SALES ADVANTAGE: The USB Token will save your customers MONEY.
Security is greatly increased if users don’t leave keys written down, waiting for anyone to steal. VME 2000 provides strong data security. The USB Token makes VME 2000 even stronger!
MALICIOUS CODE What is Malicious Code? • Programs that hackers hide on computers. • These programs can RECORD KEYSTROKES and send them to the hacker through the Internet. • When a user types in his key, the hacker receives it in real time.
MALICIOUS CODE How does Malicious Code get onto a computer? • Often through the ‘cute’ useless attachments that friends send each other through email. • You can prohibit users from opening such attachments, but you can’t enforce that rule all of the time!
MALICIOUS CODE With a VME 2000 USB Token the user never types in his key. The Token makes VME 2000 data security even stronger.
- Slides: 17