Vision for Trustworthy Computing Bill Gates 15 Jan
“Vision for Trustworthy Computing”, Bill Gates, 15 Jan 2002 “…now, when we face a choice between adding features and resolving security issues, we need to choose security. ” 1
Internet Technologies An example of how the system works* Assume: FTP is our application example. Ethernet is the underlying technology at the data link layer. * Two slides of revision for some of you. 2
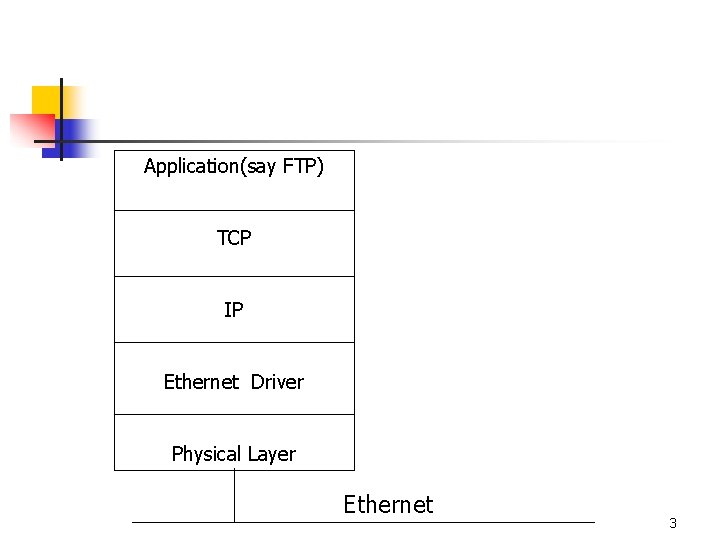
Application(say FTP) TCP IP Ethernet Driver Physical Layer Ethernet 3
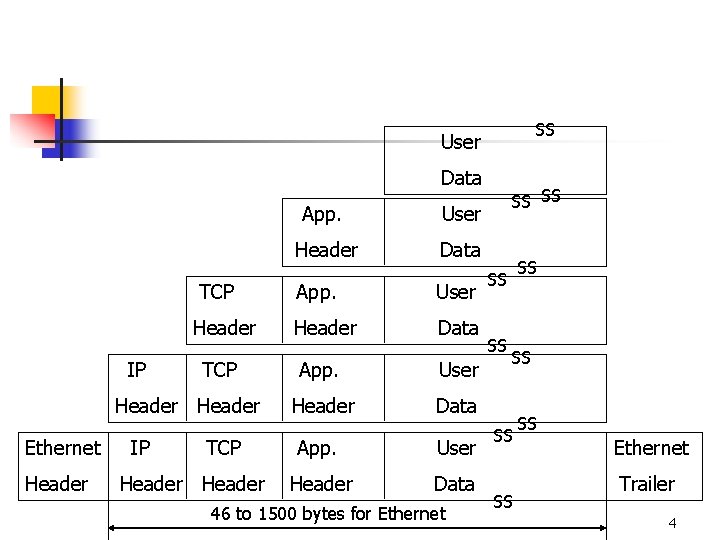
SS User Data TCP Header IP TCP Header Ethernet Header IP TCP Header App. User Header Data 46 to 1500 bytes for Ethernet SS SS SS Ethernet Trailer 4
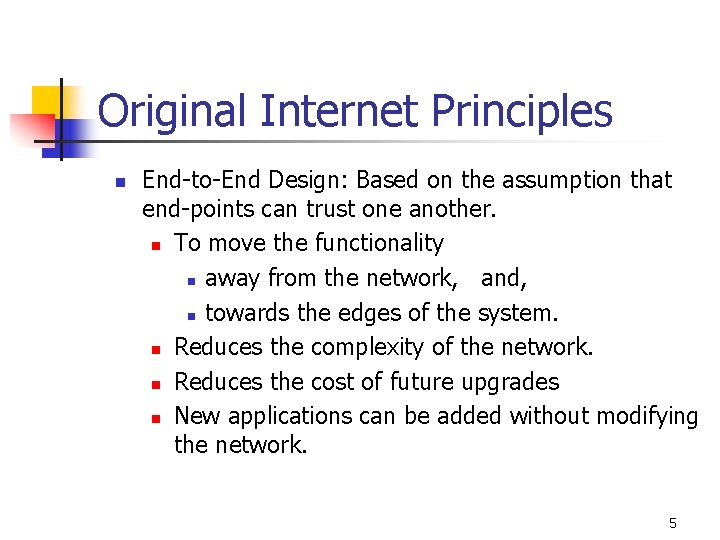
Original Internet Principles n End-to-End Design: Based on the assumption that end-points can trust one another. n To move the functionality n away from the network, and, n towards the edges of the system. n Reduces the complexity of the network. n Reduces the cost of future upgrades n New applications can be added without modifying the network. 5
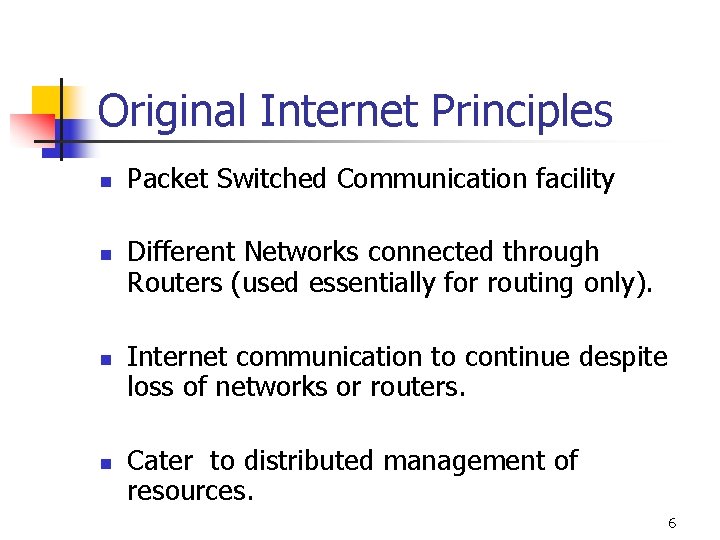
Original Internet Principles n n Packet Switched Communication facility Different Networks connected through Routers (used essentially for routing only). Internet communication to continue despite loss of networks or routers. Cater to distributed management of resources. 6
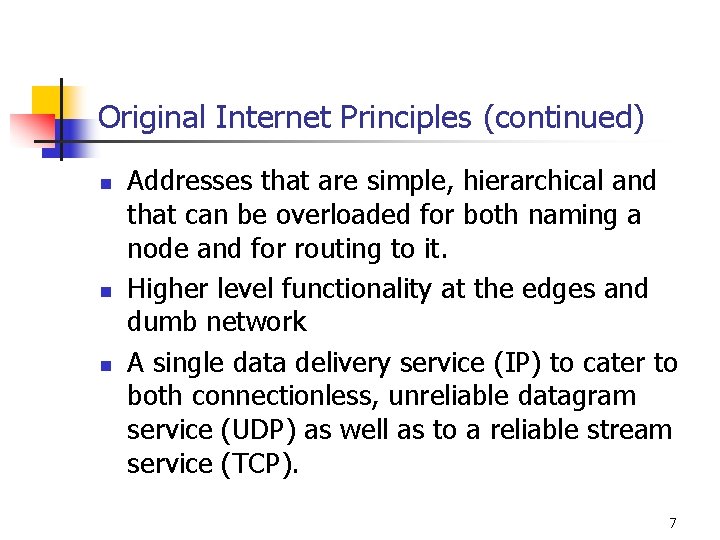
Original Internet Principles (continued) n n n Addresses that are simple, hierarchical and that can be overloaded for both naming a node and for routing to it. Higher level functionality at the edges and dumb network A single data delivery service (IP) to cater to both connectionless, unreliable datagram service (UDP) as well as to a reliable stream service (TCP). 7
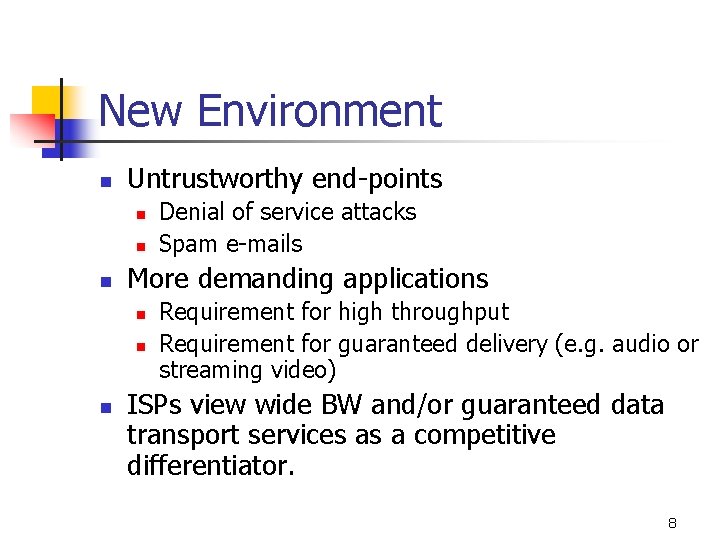
New Environment n Untrustworthy end-points n n n More demanding applications n n n Denial of service attacks Spam e-mails Requirement for high throughput Requirement for guaranteed delivery (e. g. audio or streaming video) ISPs view wide BW and/or guaranteed data transport services as a competitive differentiator. 8
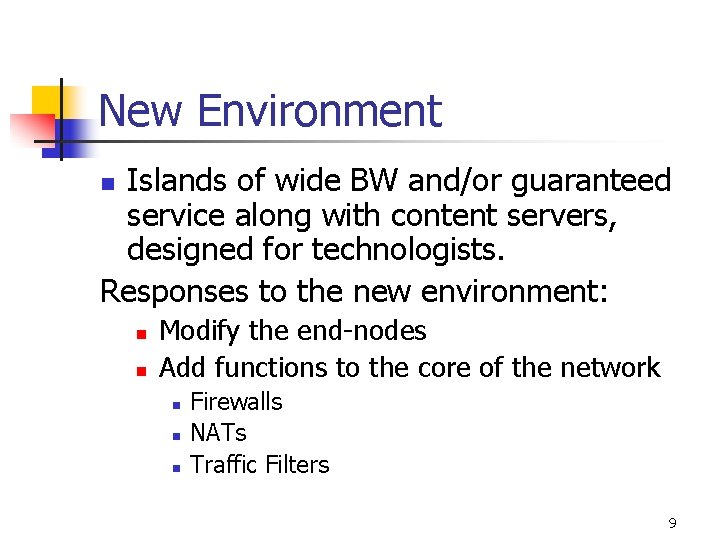
New Environment Islands of wide BW and/or guaranteed service along with content servers, designed for technologists. Responses to the new environment: n n n Modify the end-nodes Add functions to the core of the network n n n Firewalls NATs Traffic Filters 9
The Internet Characteristics & Architecture as it exists today 10
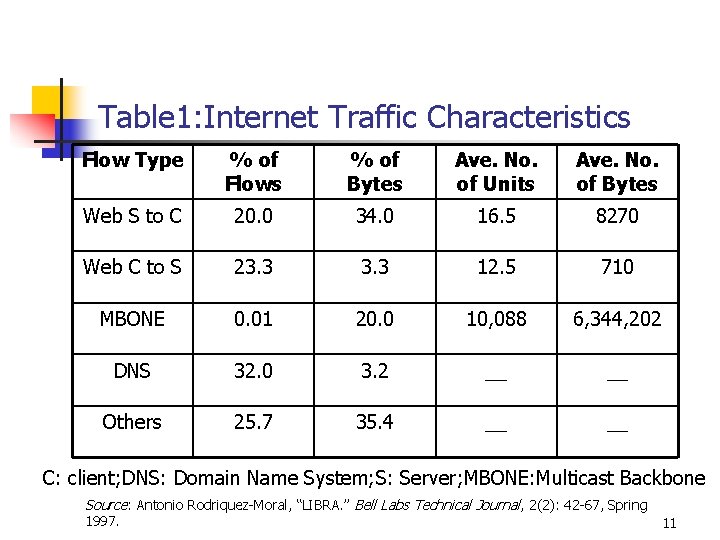
Table 1: Internet Traffic Characteristics Flow Type % of Flows % of Bytes Ave. No. of Units Ave. No. of Bytes Web S to C 20. 0 34. 0 16. 5 8270 Web C to S 23. 3 12. 5 710 MBONE 0. 01 20. 0 10, 088 6, 344, 202 DNS 32. 0 3. 2 __ __ Others 25. 7 35. 4 __ __ C: client; DNS: Domain Name System; S: Server; MBONE: Multicast Backbone Source: Antonio Rodriquez-Moral, “LIBRA. ” Bell Labs Technical Journal, 2(2): 42 -67, Spring 1997. 11
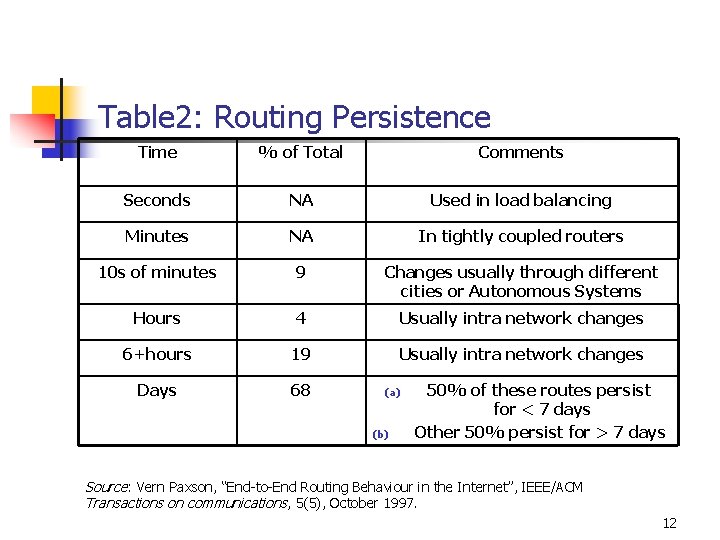
Table 2: Routing Persistence Time % of Total Comments Seconds NA Used in load balancing Minutes NA In tightly coupled routers 10 s of minutes 9 Changes usually through different cities or Autonomous Systems Hours 4 Usually intra network changes 6+hours 19 Usually intra network changes Days 68 (a) (b) 50% of these routes persist for < 7 days Other 50% persist for > 7 days Source: Vern Paxson, “End-to-End Routing Behaviour in the Internet”, IEEE/ACM Transactions on communications, 5(5), October 1997. 12
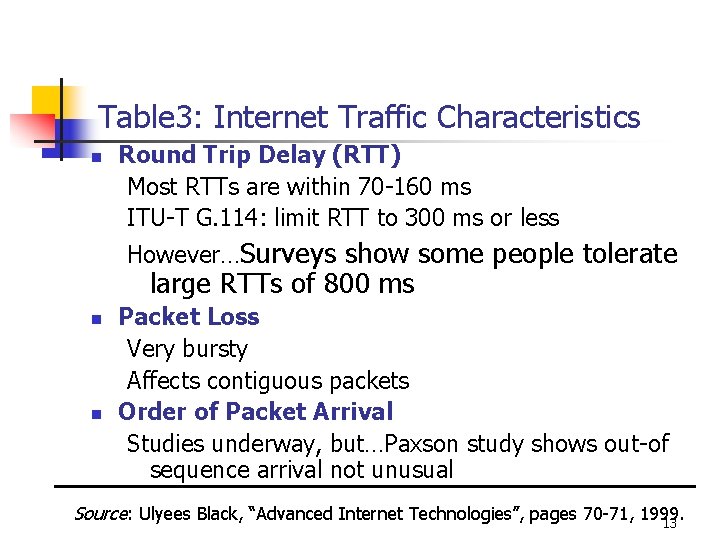
Table 3: Internet Traffic Characteristics n Round Trip Delay (RTT) Most RTTs are within 70 -160 ms ITU-T G. 114: limit RTT to 300 ms or less However…Surveys show some people tolerate large RTTs of 800 ms n n Packet Loss Very bursty Affects contiguous packets Order of Packet Arrival Studies underway, but…Paxson study shows out-of sequence arrival not unusual Source: Ulyees Black, “Advanced Internet Technologies”, pages 70 -71, 1999. 13
Packet Loss n n Data transmission: masked by TCP Audio/Video: ears and eyes catch it Audio System: G. T 23. 1 masks a loss of up to 10% if the loss is random and independent. It uses the previous packet to simulate the lost packet. But the packet loss in Internet is bursty. 14
Packet Loss n n Forward Error Correction system: uses the technology used in mobile wireless system --by sending many copies of the coded voice. If even one copy arrives safely, the operation is effective. Since UDP is used for audio/video, the out-of-sequence arrival is also a problem. 15
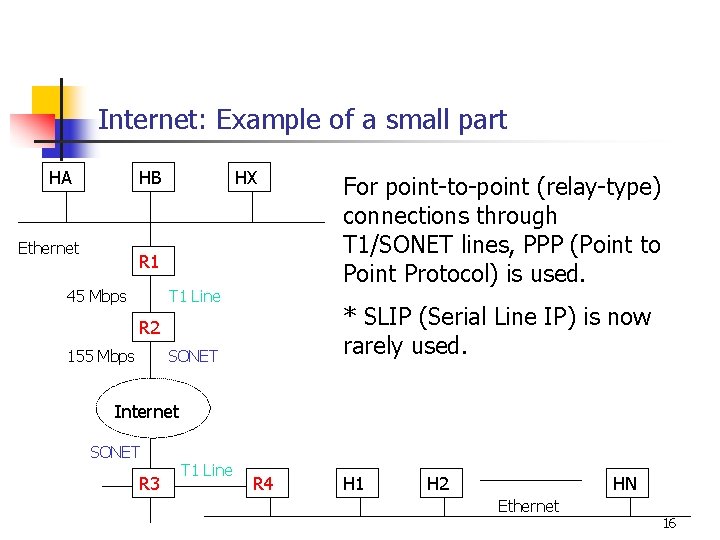
Internet: Example of a small part HA HB Ethernet HX R 1 45 Mbps T 1 Line * SLIP (Serial Line IP) is now rarely used. R 2 155 Mbps For point-to-point (relay-type) connections through T 1/SONET lines, PPP (Point to Point Protocol) is used. SONET Internet SONET R 3 T 1 Line R 4 H 1 H 2 HN Ethernet 16
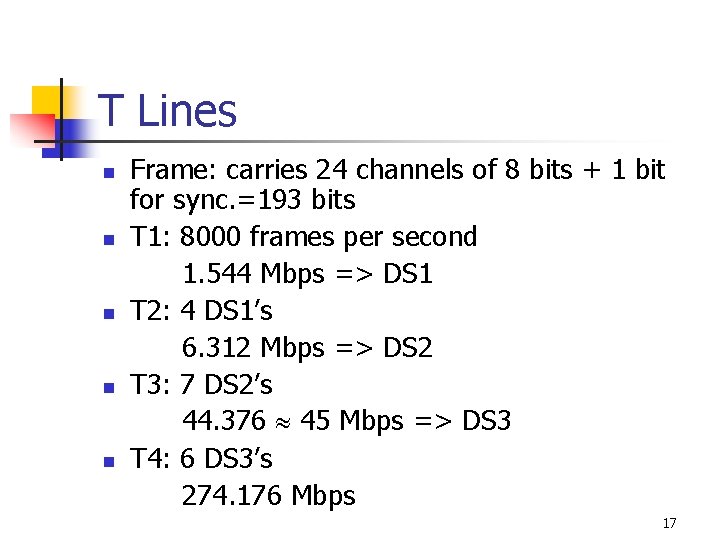
T Lines n n n Frame: carries 24 channels of 8 bits + 1 bit for sync. =193 bits T 1: 8000 frames per second 1. 544 Mbps => DS 1 T 2: 4 DS 1’s 6. 312 Mbps => DS 2 T 3: 7 DS 2’s 44. 376 45 Mbps => DS 3 T 4: 6 DS 3’s 274. 176 Mbps 17
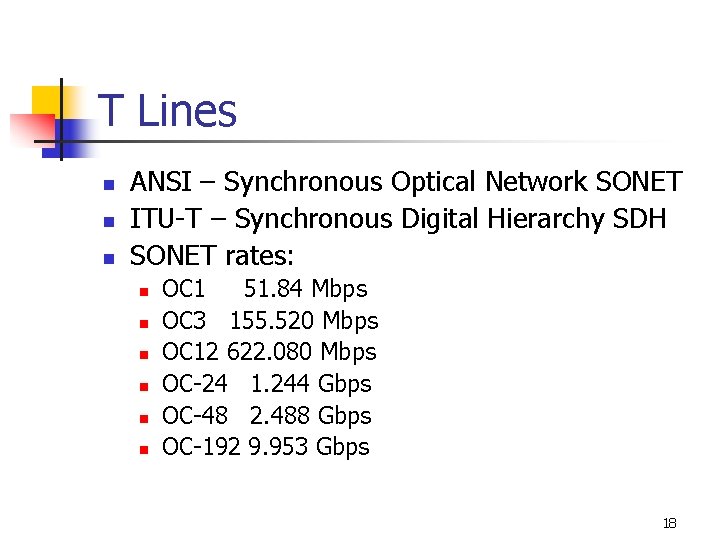
T Lines n n n ANSI – Synchronous Optical Network SONET ITU-T – Synchronous Digital Hierarchy SDH SONET rates: n n n OC 1 51. 84 Mbps OC 3 155. 520 Mbps OC 12 622. 080 Mbps OC-24 1. 244 Gbps OC-48 2. 488 Gbps OC-192 9. 953 Gbps 18
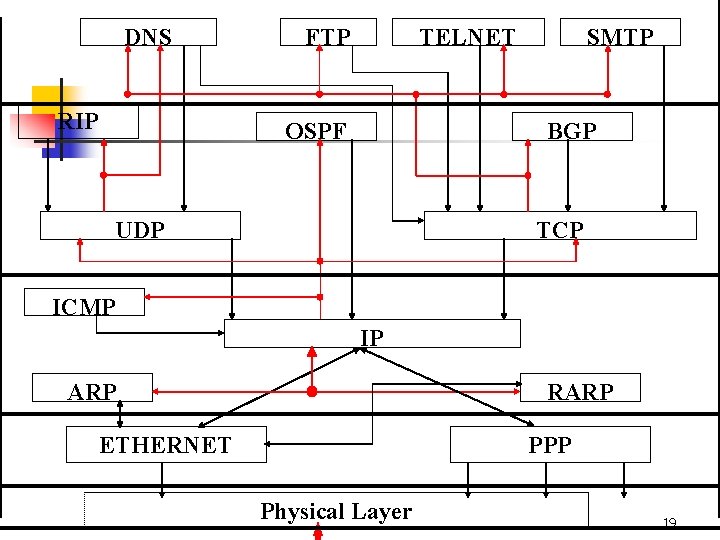
DNS RIP FTP TELNET OSPF SMTP BGP UDP TCP ICMP IP ARP RARP ETHERNET PPP Physical Layer 19
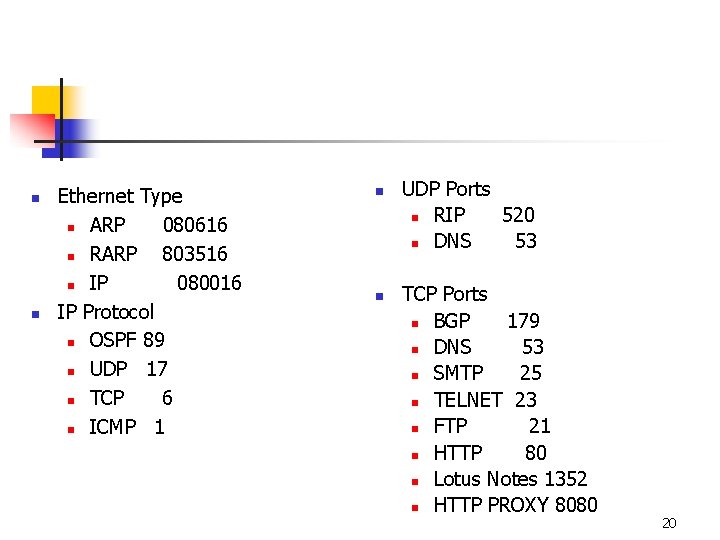
n n Ethernet Type n ARP 080616 n RARP 803516 n IP 080016 IP Protocol n OSPF 89 n UDP 17 n TCP 6 n ICMP 1 n n UDP Ports n RIP 520 n DNS 53 TCP Ports n BGP 179 n DNS 53 n SMTP 25 n TELNET 23 n FTP 21 n HTTP 80 n Lotus Notes 1352 n HTTP PROXY 8080 20
- Slides: 20