Vision Automated Security Validation of Mobile Apps at
Vision: Automated Security Validation of Mobile Apps at App Markets Presented by: Tom Staley
Introduction �Rising security concerns in the smartphone app community �Use of private data: �Passwords �Financial records �GPS locations �Malware attacks have been found targeting smartphones
Taint. Droid �Previous attempt by presenters to address security problems �Tracks sensitive data as it flows between apps �Raises an alert when sensitive data is transmitted off the phone �Leaks are only found after the data has been lost
Current Security Methods �Unlike PCs, the app market is highly centralized �Scan apps as they join the market �Currently applied manually, if at all �Some banned behavior still slips through the cracks
Proposed Solution �App. Inspector �Service run by market providers or by a thirdparty �Uses multiple virtual smartphones to run instances of apps before they reach the market �Entire process is automated to ensure thorough testing
Challenges �Three challenges with App. Inspector �How to track and log data �How to determine security violations using the logs �How to ensure all branches of code are covered
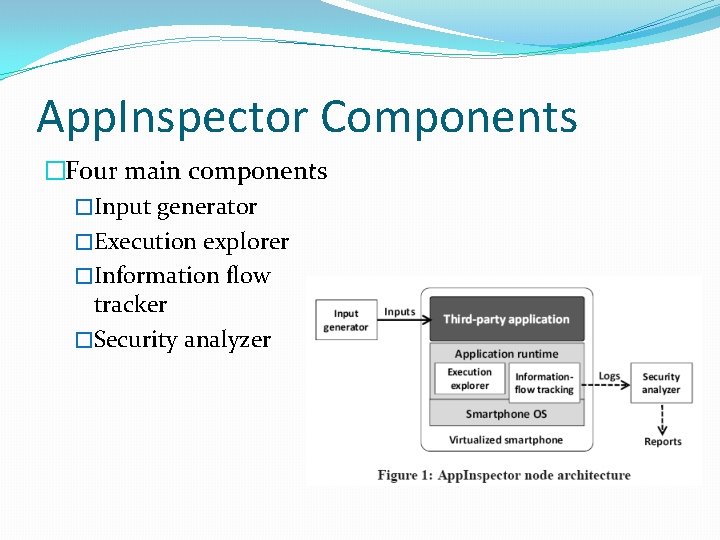
App. Inspector Components �Four main components �Input generator �Execution explorer �Information flow tracker �Security analyzer
Types of violations �Security violation - when an app accesses data without permissions to do so �Privacy violation – when an app discloses information without prompting the user �App. Inspector focuses on privacy violations
Tracking Data �Log data about explicit and implicit data flows �Various actions also logged, like methods that access disk memory or device sensors �Action logging has to be limited to reduce overhead
Data Flows �Explicit data flow – following data through use of data dependencies �Attach a “label” to data as it leaves the source of the data �Track the label through the program until it reaches a “sink” �Implicit data flow – when sensitive information can be found by looking at control flow �if (w == 0) x = y; else z = y; �If w is privacy-sensitive, looking at values of x and z can determine if w == 0;
Violation Detection �Two methods to detect privacy violations �When sensitive data is disclosed: �Use data dependency graph to trace sensitive data back to source �Check for user notifications or search license agreements for permissions
Input Generation �App are event-driven �Two types of events: �UI inputs �Callback triggers from device sensors �These inputs can be randomly generated to test apps
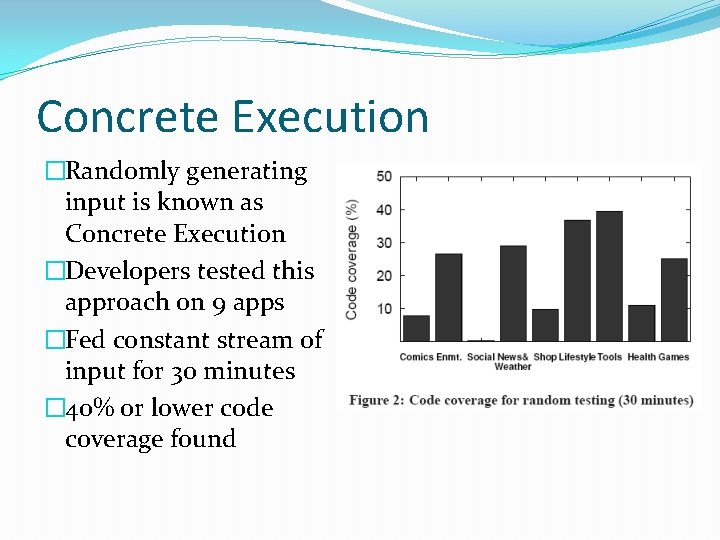
Concrete Execution �Randomly generating input is known as Concrete Execution �Developers tested this approach on 9 apps �Fed constant stream of input for 30 minutes � 40% or lower code coverage found
Symbolic Execution �Another type of input testing known as symbolic testing �Systematically tests all possible execution paths �Highly inefficient
Concolic Execution �Mix of concrete and symbolic execution �Run symbolic execution on main application code �All other code (code libraries, system code, etc. ) tested with concrete execution �Switch between the two methods as required during testing
Conclusion �The app market is at risk for security and privacy violations �App. Inspector developed to scan apps before they reach marketplace �Uses concolic execution to generate input �Tracks sensitive data as it propagates through app �Uses logs to determine if privacy violation has occurred
Bibliography Peter Gilbert, "Vision: Automated Security Validation of Mobile Apps at App Markets", MCS’ 11, June 28, 2011, Bethesda, Maryland, USA.
- Slides: 17