Virtualization Security Erez Berkner Virtualization Team Manager Check
Virtualization Security Erez Berkner Virtualization Team Manager Check Point R&D May 2009 © 2009 Check Point Software Technologies Ltd. All rights reserved. [Unrestricted]—For everyone
Agenda § Virtualization overview § Virtualization security hazards § VPN-1 Virtual Edition (VE) § Common use cases § v. Switch integrated security (VMSafe) © 2009 Check Point Software Technologies Ltd. All rights reserved. [Unrestricted]—For everyone 2
![Virtualization Overview © 2009 Check Point Software Technologies Ltd. All rights reserved. [Unrestricted]—For everyone Virtualization Overview © 2009 Check Point Software Technologies Ltd. All rights reserved. [Unrestricted]—For everyone](http://slidetodoc.com/presentation_image/9a50e142967cf7a1d5c4fd3c9368f9a8/image-3.jpg)
Virtualization Overview © 2009 Check Point Software Technologies Ltd. All rights reserved. [Unrestricted]—For everyone 3
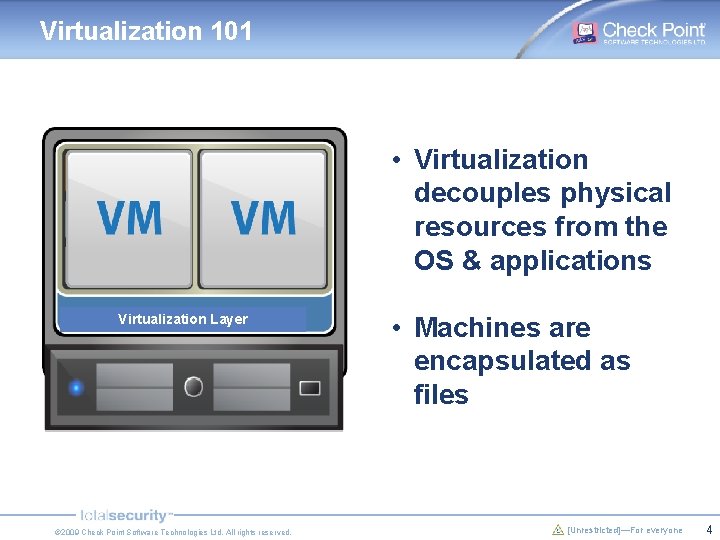
Virtualization 101 • Virtualization decouples physical resources from the OS & applications Virtualization Layer © 2009 Check Point Software Technologies Ltd. All rights reserved. • Machines are encapsulated as files [Unrestricted]—For everyone 4
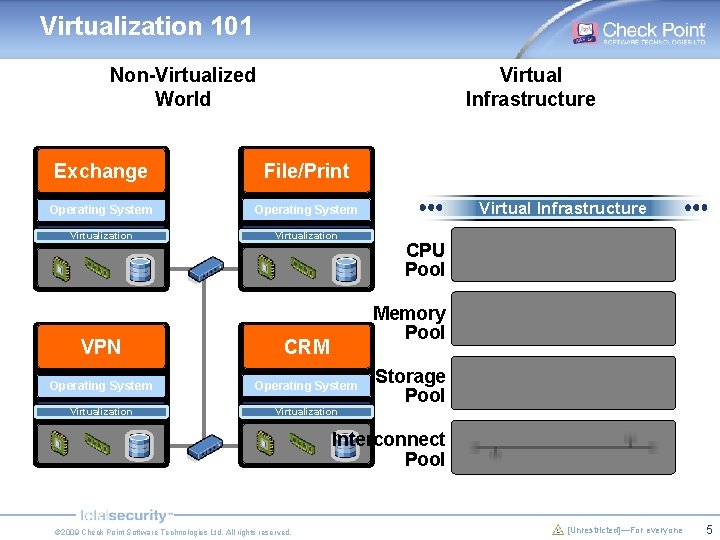
Virtualization 101 Non-Virtualized World Virtual Infrastructure Exchange File/Print Operating System Virtualization Virtual Infrastructure CPU Pool Memory Pool VPN CRM Operating System Virtualization Storage Pool Interconnect Pool © 2009 Check Point Software Technologies Ltd. All rights reserved. [Unrestricted]—For everyone 5
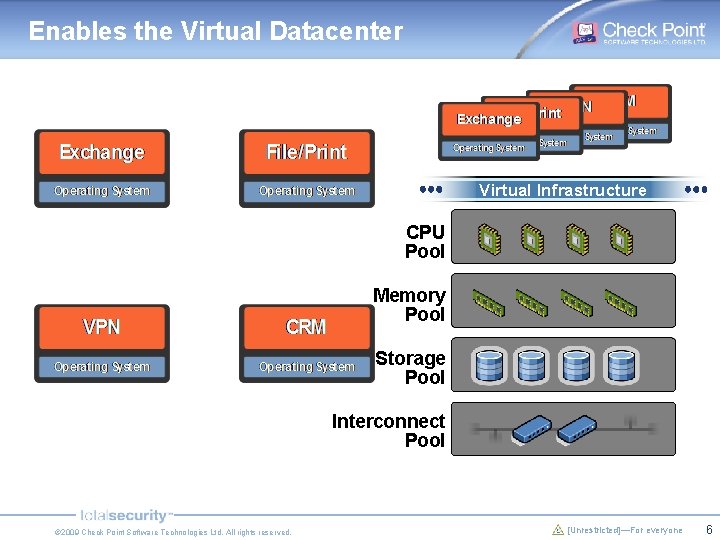
Enables the Virtual Datacenter Virtual Infrastructure CPU Pool Memory Pool Storage Pool Interconnect Pool © 2009 Check Point Software Technologies Ltd. All rights reserved. [Unrestricted]—For everyone 6
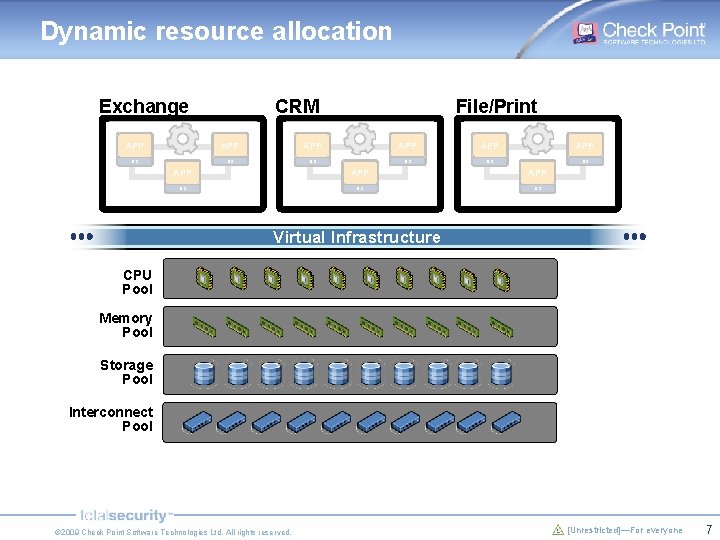
Dynamic resource allocation Exchange CRM File/Print APP APP APP OS OS OS Virtual Infrastructure CPU Pool Memory Pool Storage Pool Interconnect Pool © 2009 Check Point Software Technologies Ltd. All rights reserved. [Unrestricted]—For everyone 7
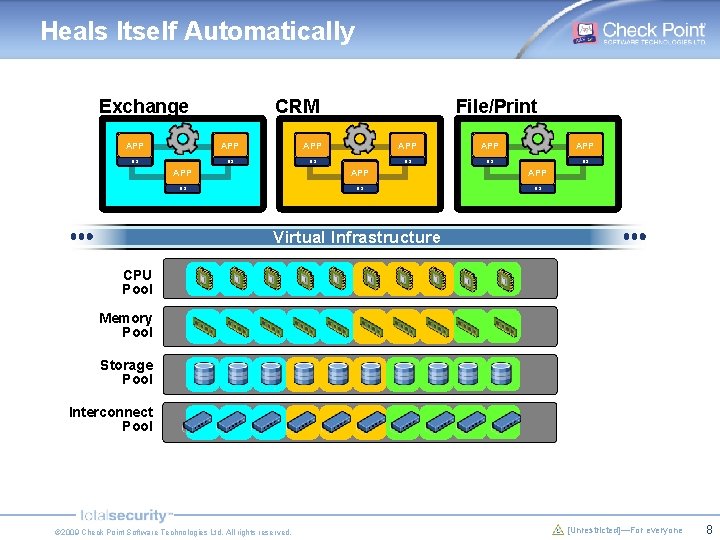
Heals Itself Automatically Exchange CRM File/Print APP APP APP OS OS OS Virtual Infrastructure CPU Pool Memory Pool Storage Pool Interconnect Pool © 2009 Check Point Software Technologies Ltd. All rights reserved. [Unrestricted]—For everyone 8
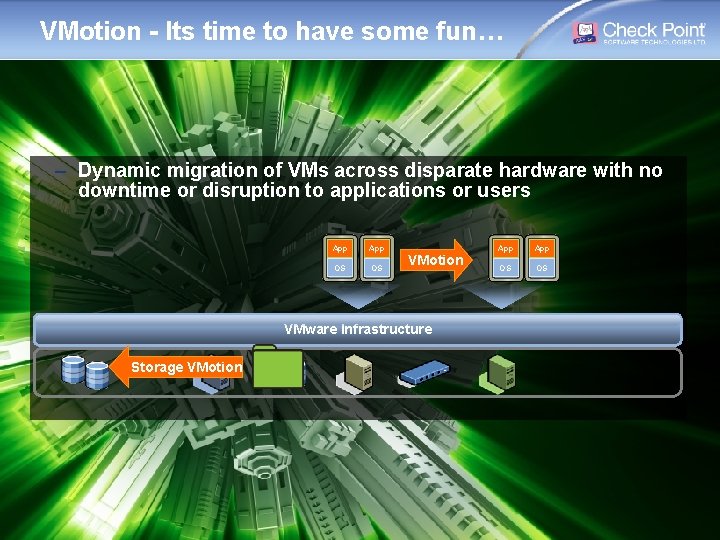
VMotion - Its time to have some fun… – Dynamic migration of VMs across disparate hardware with no downtime or disruption to applications or users App OS OS VMotion App OS OS VMware Infrastructure Storage VMotion © 2009 Check Point Software Technologies Ltd. All rights reserved. [Unrestricted]—For everyone 9
![Hazards! © 2009 Check Point Software Technologies Ltd. All rights reserved. [Unrestricted]—For everyone 10 Hazards! © 2009 Check Point Software Technologies Ltd. All rights reserved. [Unrestricted]—For everyone 10](http://slidetodoc.com/presentation_image/9a50e142967cf7a1d5c4fd3c9368f9a8/image-10.jpg)
Hazards! © 2009 Check Point Software Technologies Ltd. All rights reserved. [Unrestricted]—For everyone 10
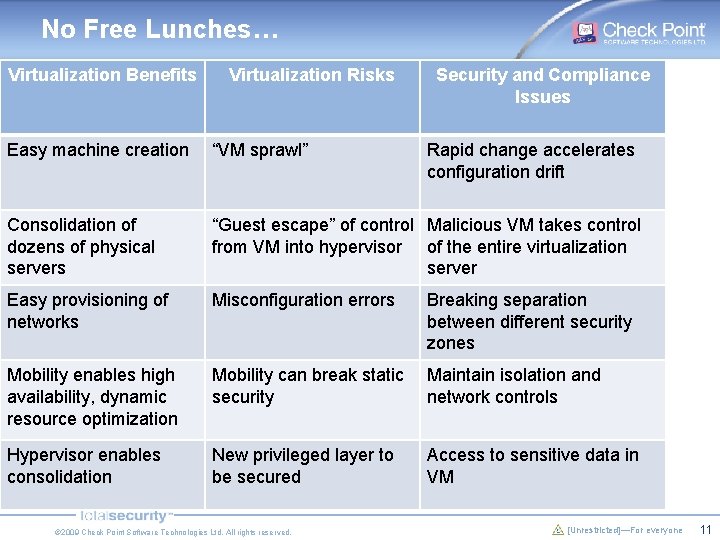
No Free Lunches… Virtualization Benefits Virtualization Risks Security and Compliance Issues Easy machine creation “VM sprawl” Consolidation of dozens of physical servers “Guest escape” of control Malicious VM takes control from VM into hypervisor of the entire virtualization server Easy provisioning of networks Misconfiguration errors Breaking separation between different security zones Mobility enables high availability, dynamic resource optimization Mobility can break static security Maintain isolation and network controls Hypervisor enables consolidation New privileged layer to be secured Access to sensitive data in VM © 2009 Check Point Software Technologies Ltd. All rights reserved. Rapid change accelerates configuration drift [Unrestricted]—For everyone 11
Specific Challenges with Network Security § Lack of inter-VM visibility for monitoring and enforcement § Aligning static policies with fast VM sprawl and mobility § Maintaining network session state with live migration (VMotion) § Loss of SOD between server admin and network/security teams © 2009 Check Point Software Technologies Ltd. All rights reserved. [Unrestricted]—For everyone 12
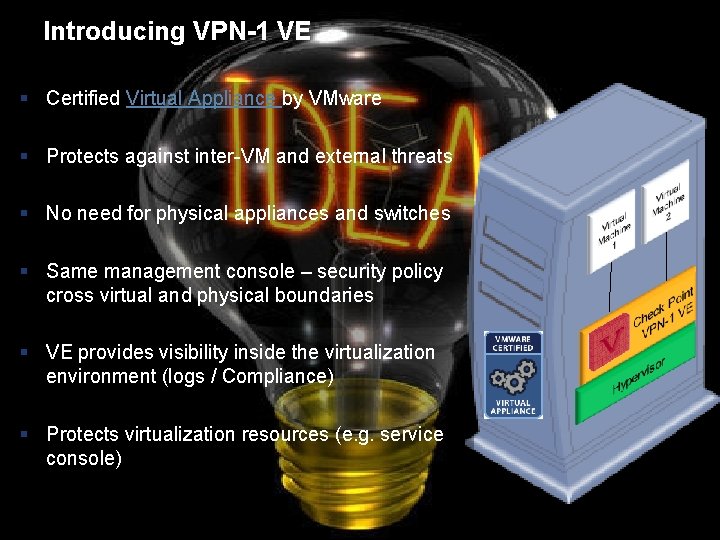
Introducing VPN-1 VE § Certified Virtual Appliance by VMware § Protects against inter-VM and external threats § No need for physical appliances and switches § Same management console – security policy cross virtual and physical boundaries § VE provides visibility inside the virtualization environment (logs / Compliance) § Protects virtualization resources (e. g. service console) © 2009 Check Point Software Technologies Ltd. All rights reserved. [Unrestricted]—For everyone 13
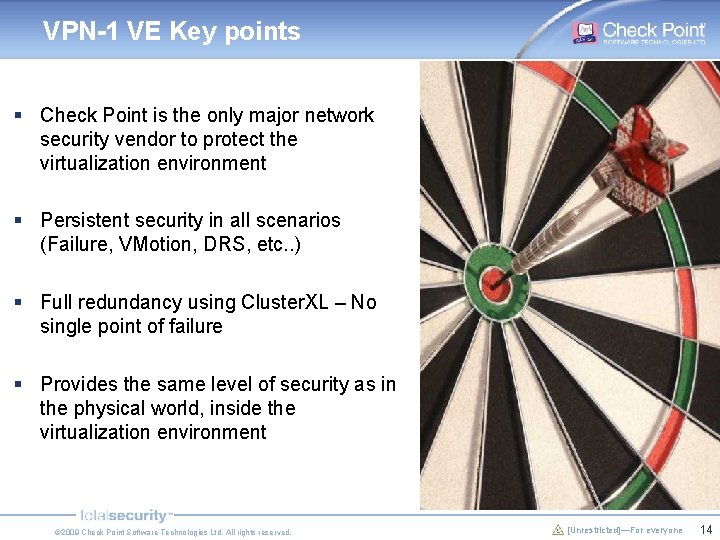
VPN-1 VE Key points § Check Point is the only major network security vendor to protect the virtualization environment § Persistent security in all scenarios (Failure, VMotion, DRS, etc. . ) § Full redundancy using Cluster. XL – No single point of failure § Provides the same level of security as in the physical world, inside the virtualization environment © 2009 Check Point Software Technologies Ltd. All rights reserved. [Unrestricted]—For everyone 14
![Deploying virtualization security © 2009 Check Point Software Technologies Ltd. All rights reserved. [Unrestricted]—For Deploying virtualization security © 2009 Check Point Software Technologies Ltd. All rights reserved. [Unrestricted]—For](http://slidetodoc.com/presentation_image/9a50e142967cf7a1d5c4fd3c9368f9a8/image-15.jpg)
Deploying virtualization security © 2009 Check Point Software Technologies Ltd. All rights reserved. [Unrestricted]—For everyone 15
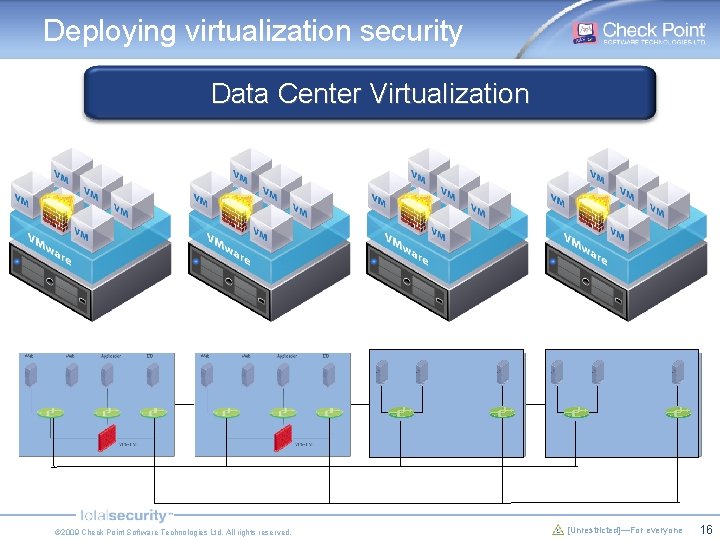
Deploying virtualization security Data Center Virtualization © 2009 Check Point Software Technologies Ltd. All rights reserved. [Unrestricted]—For everyone 16
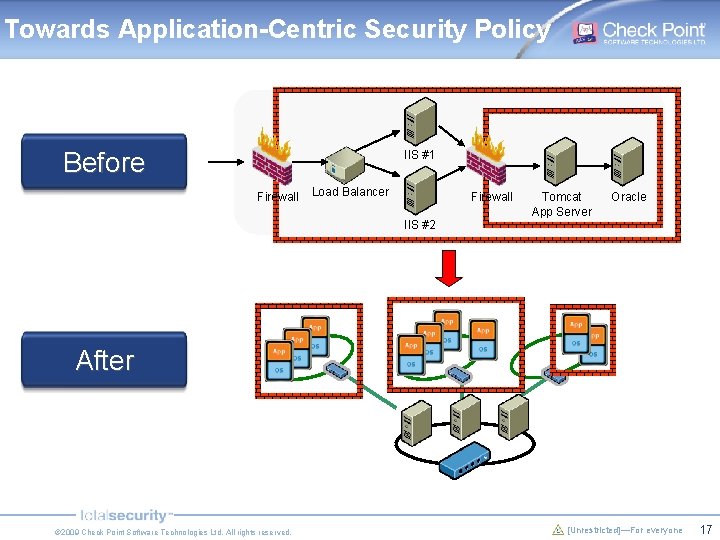
Towards Application-Centric Security Policy Before IIS #1 Firewall Load Balancer Firewall Tomcat App Server Oracle IIS #2 After © 2009 Check Point Software Technologies Ltd. All rights reserved. [Unrestricted]—For everyone 17
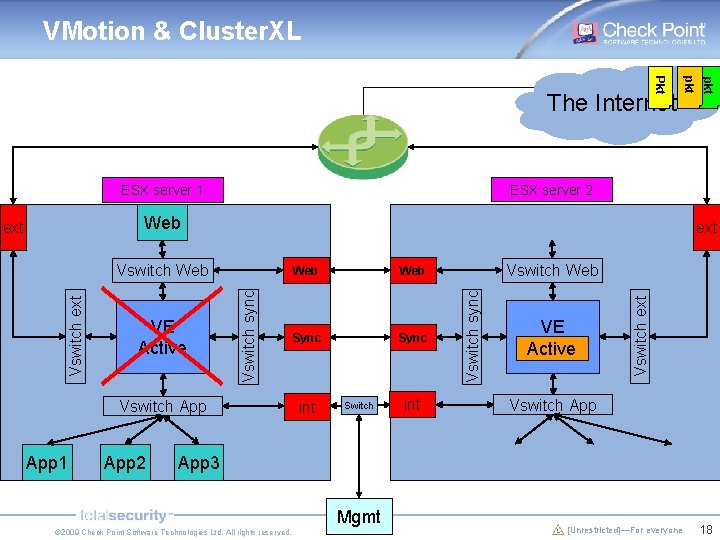
VMotion & Cluster. XL ESX server 2 ESX server 1 Web ext Vswitch App 1 App 2 Web Sync int Switch int Vswitch Web VE Standby Active Vswitch ext VE Active Vswitch sync Vswitch ext Vswitch Web Vswitch sync ext pkt Pkt The Internet Vswitch App 3 Mgmt © 2009 Check Point Software Technologies Ltd. All rights reserved. [Unrestricted]—For everyone 18
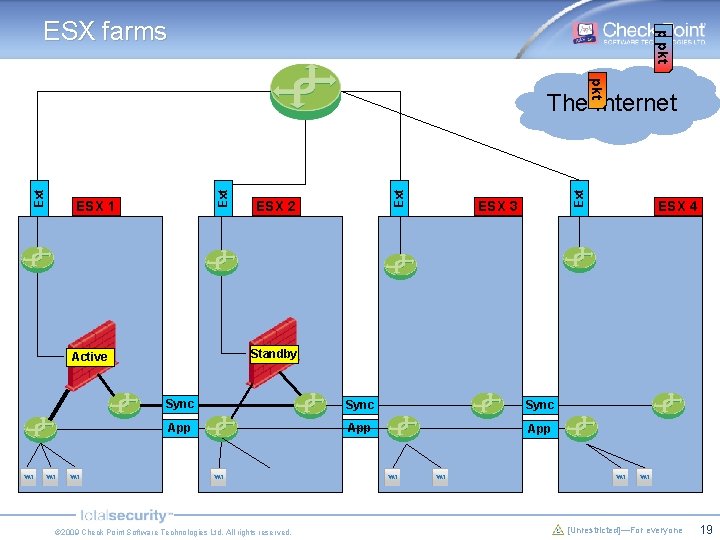
pkt ESX farms pkt ESX 2 Ext ESX 1 Ext Ext The Internet ESX 3 ESX 4 Standby Active Sync App App © 2009 Check Point Software Technologies Ltd. All rights reserved. [Unrestricted]—For everyone 19
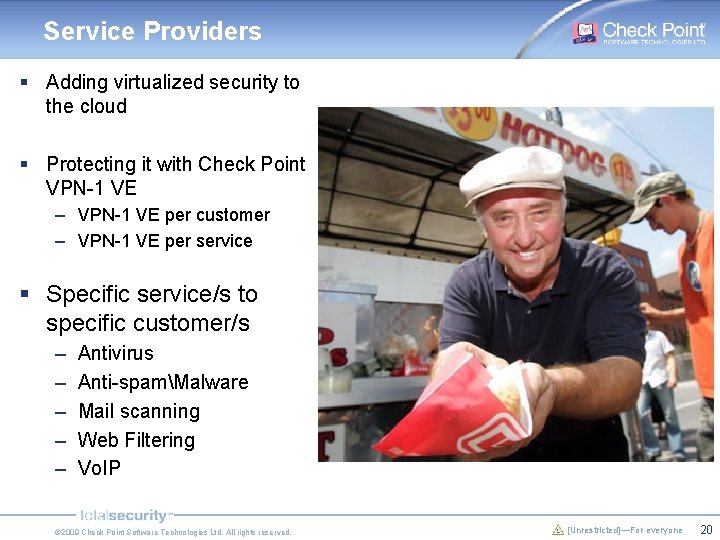
Service Providers § Adding virtualized security to the cloud § Protecting it with Check Point VPN-1 VE – VPN-1 VE per customer – VPN-1 VE per service § Specific service/s to specific customer/s – – – Antivirus Anti-spamMalware Mail scanning Web Filtering Vo. IP © 2009 Check Point Software Technologies Ltd. All rights reserved. [Unrestricted]—For everyone 20
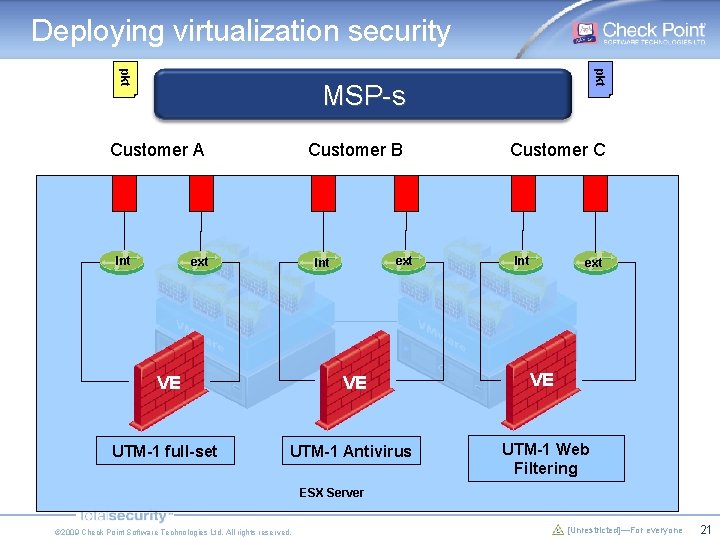
Deploying virtualization security pkt MSP-s Customer A Int Customer B ext Int Customer C Int ext VE VE VE UTM-1 full-set UTM-1 Antivirus UTM-1 Web Filtering ESX Server © 2009 Check Point Software Technologies Ltd. All rights reserved. [Unrestricted]—For everyone 21
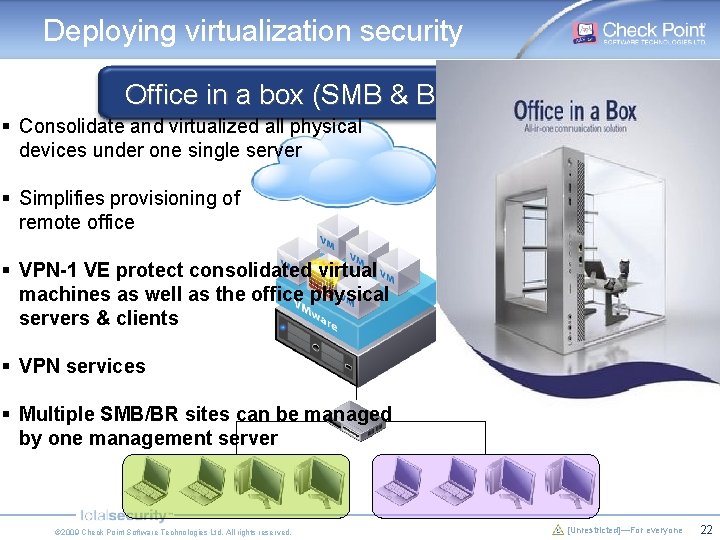
Deploying virtualization security Office in a box (SMB & Branch offices) § Consolidate and virtualized all physical devices under one single server § Simplifies provisioning of remote office § VPN-1 VE protect consolidated virtual machines as well as the office physical servers & clients § VPN services § Multiple SMB/BR sites can be managed by one management server © 2009 Check Point Software Technologies Ltd. All rights reserved. [Unrestricted]—For everyone 22
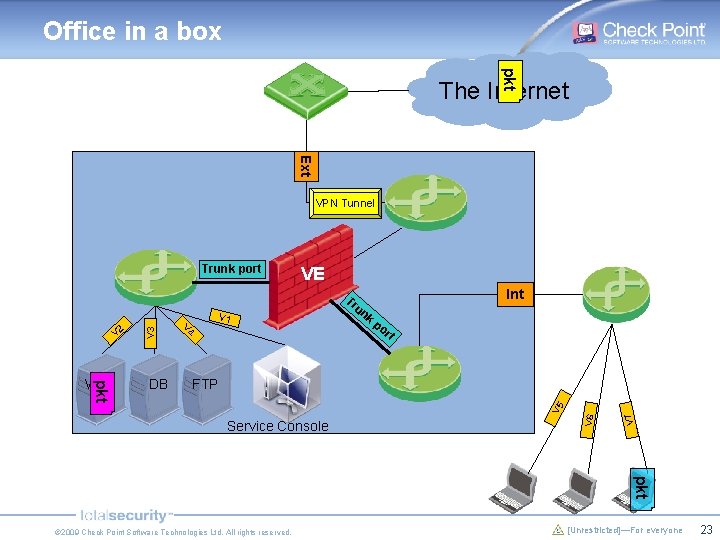
Office in a box pkt The Internet Ext VPN Tunnel Trunk port VE Int po rt FTP Service Console V 7 DB V 1 V 5 pkt Web V 4 un k V 6 V 2 V 3 Tr pkt © 2009 Check Point Software Technologies Ltd. All rights reserved. [Unrestricted]—For everyone 23
Deploying virtualization security Disaster Recovery § Preserve security in DR scenarios § No need for additional physical Firewall on the DR site § “DR on a Disk” § Fast deployment – zero time © 2009 Check Point Software Technologies Ltd. All rights reserved. [Unrestricted]—For everyone 24
Is running VPN-1 VE on VMware is safe? § A hypervisor is at less risk of an external attack because – There is no ip on v. Switch/Hypervisor – It doesn't listen on input/output ports § The hypervisor network attack surface (the v. Switch) is very thin (think of it as a nic driver) § VE can protect the service console § Every incoming packet should go through VE security inspection before it reaches a VM § VMware has resource allocation abilities to prevent Do. S on resource by a malicious VM © 2009 Check Point Software Technologies Ltd. All rights reserved. [Unrestricted]—For everyone 25
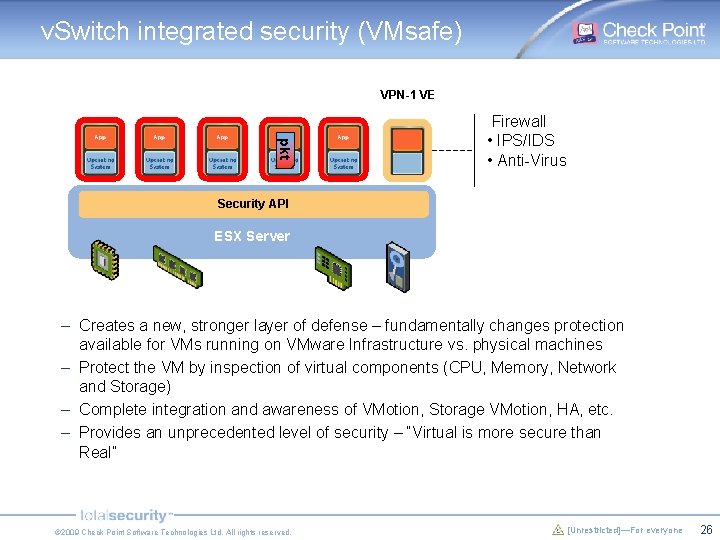
v. Switch integrated security (VMsafe) VPN-1 VE pkt Firewall • IPS/IDS • Anti-Virus Security API ESX Server – Creates a new, stronger layer of defense – fundamentally changes protection available for VMs running on VMware Infrastructure vs. physical machines – Protect the VM by inspection of virtual components (CPU, Memory, Network and Storage) – Complete integration and awareness of VMotion, Storage VMotion, HA, etc. – Provides an unprecedented level of security – “Virtual is more secure than Real” © 2009 Check Point Software Technologies Ltd. All rights reserved. [Unrestricted]—For everyone 26
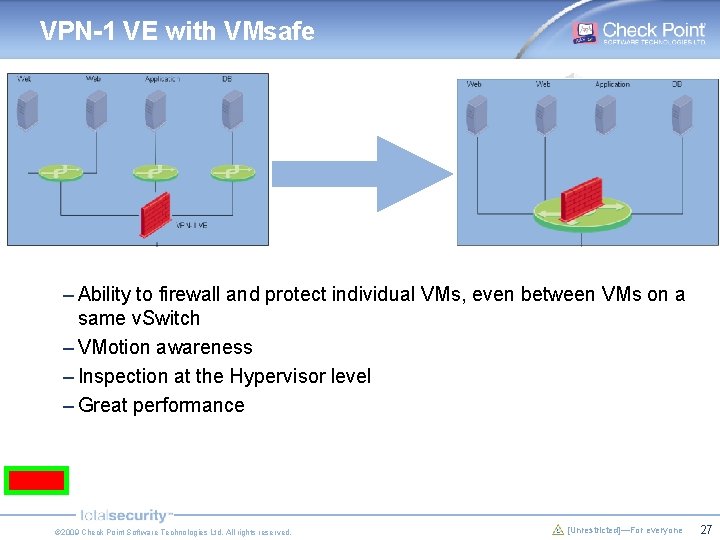
VPN-1 VE with VMsafe – Ability to firewall and protect individual VMs, even between VMs on a same v. Switch – VMotion awareness – Inspection at the Hypervisor level – Great performance © 2009 Check Point Software Technologies Ltd. All rights reserved. [Unrestricted]—For everyone 27
![© 2009 Check Point Software Technologies Ltd. All rights reserved. [Unrestricted]—For everyone 28 © 2009 Check Point Software Technologies Ltd. All rights reserved. [Unrestricted]—For everyone 28](http://slidetodoc.com/presentation_image/9a50e142967cf7a1d5c4fd3c9368f9a8/image-28.jpg)
© 2009 Check Point Software Technologies Ltd. All rights reserved. [Unrestricted]—For everyone 28
![© 2009 Check Point Software Technologies Ltd. All rights reserved. [Unrestricted]—For everyone 29 © 2009 Check Point Software Technologies Ltd. All rights reserved. [Unrestricted]—For everyone 29](http://slidetodoc.com/presentation_image/9a50e142967cf7a1d5c4fd3c9368f9a8/image-29.jpg)
© 2009 Check Point Software Technologies Ltd. All rights reserved. [Unrestricted]—For everyone 29
- Slides: 29