VIRTUAL PRIVATE NETWORKS VPN Traditional Connectivity From Gartner
![Traditional Connectivity [From Gartner Consulting] Traditional Connectivity [From Gartner Consulting]](https://slidetodoc.com/presentation_image/c0591b3ded45a5c0dc1ef1112da31f3d/image-2.jpg)




- Slides: 64
VIRTUAL PRIVATE NETWORKS (VPN)
![Traditional Connectivity From Gartner Consulting Traditional Connectivity [From Gartner Consulting]](https://slidetodoc.com/presentation_image/c0591b3ded45a5c0dc1ef1112da31f3d/image-2.jpg)
Traditional Connectivity [From Gartner Consulting]
What is VPN? Ø Virtual Private Network is a type of private network that uses public telecommunication, such as the Internet, instead of leased lines to communicate. Ø Became popular as more employees worked in remote locations. Ø Terminologies to understand how VPNs work.
Private Networks vs. Virtual Private Networks Employees can access the network (Intranet) from remote locations. Secured networks. The Internet is used as the backbone for VPNs Saves cost tremendously from reduction of equipment and maintenance costs. Scalability
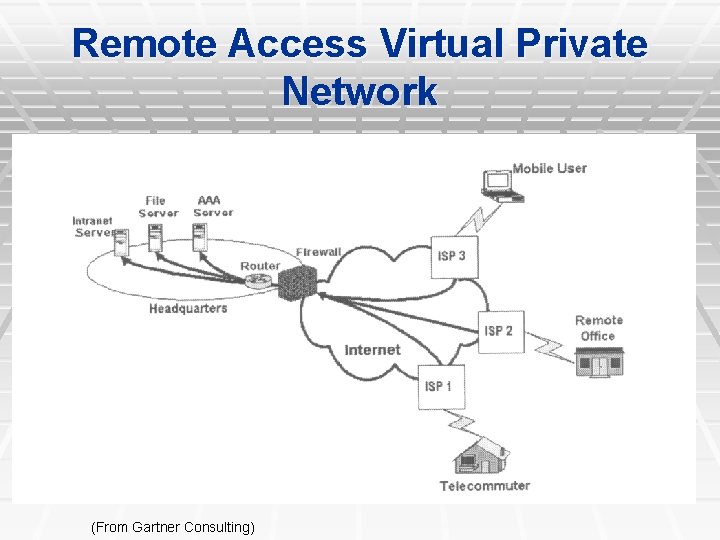
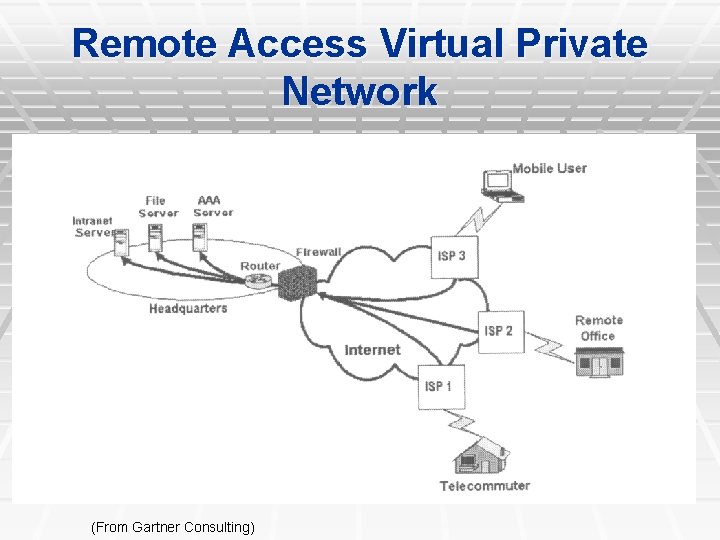
Remote Access Virtual Private Network (From Gartner Consulting)
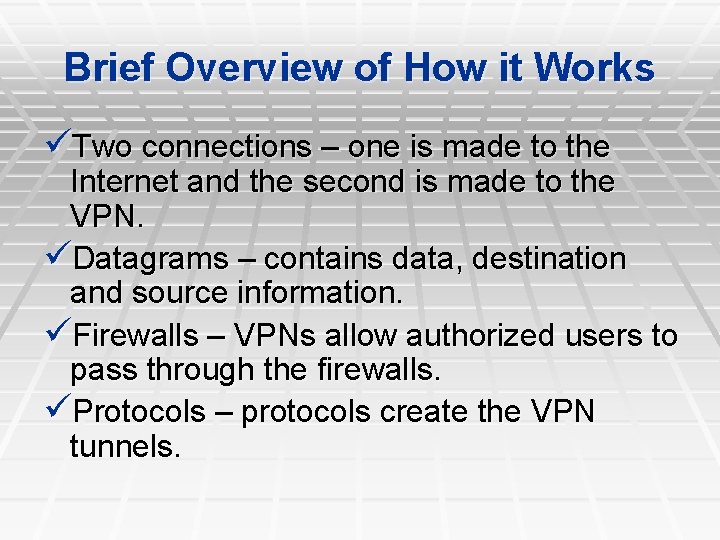
Brief Overview of How it Works Two connections – one is made to the Internet and the second is made to the VPN. Datagrams – contains data, destination and source information. Firewalls – VPNs allow authorized users to pass through the firewalls. Protocols – protocols create the VPN tunnels.
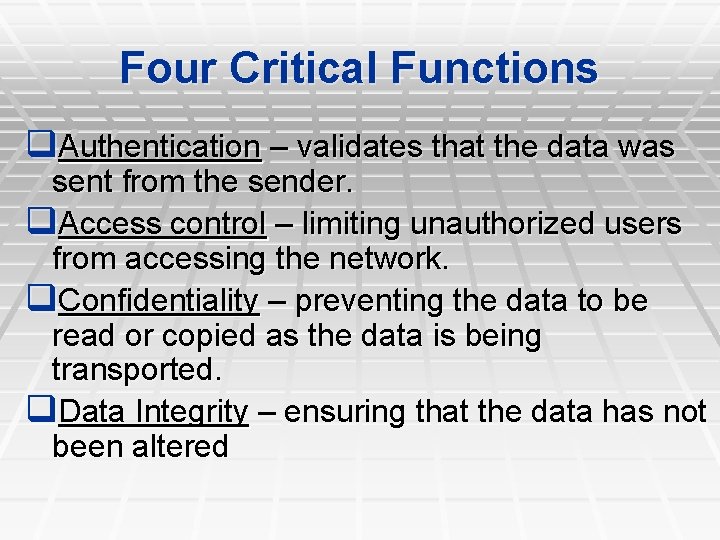
Four Critical Functions q. Authentication – validates that the data was sent from the sender. q. Access control – limiting unauthorized users from accessing the network. q. Confidentiality – preventing the data to be read or copied as the data is being transported. q. Data Integrity – ensuring that the data has not been altered
Encryption -- is a method of “scrambling” data before transmitting it onto the Internet. Public Key Encryption Technique Digital signature – for authentication
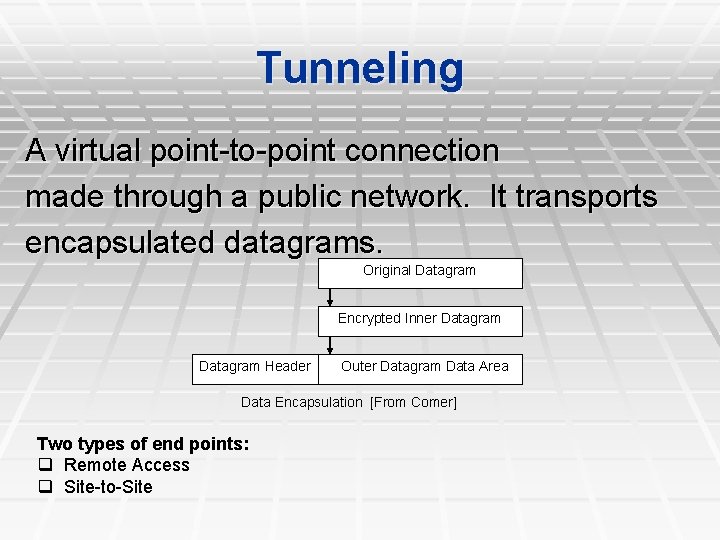
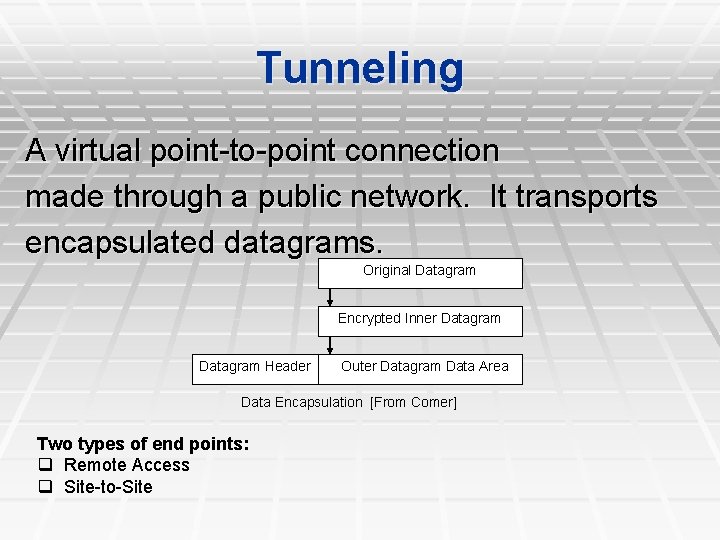
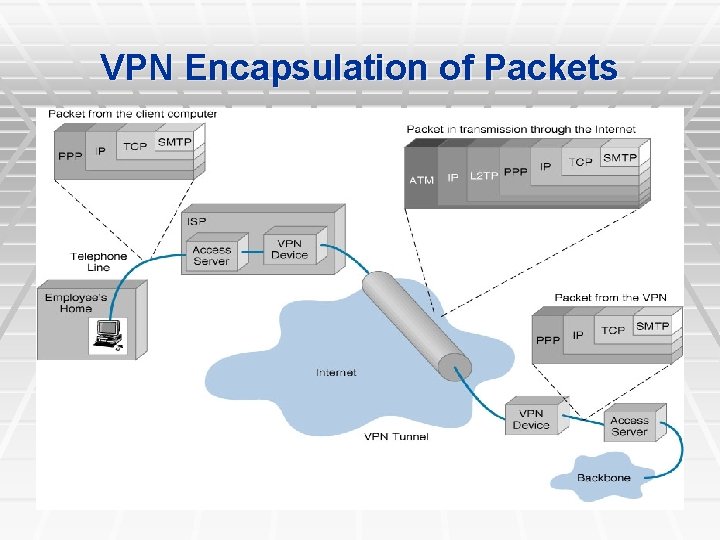
Tunneling A virtual point-to-point connection made through a public network. It transports encapsulated datagrams. Original Datagram Encrypted Inner Datagram Header Outer Datagram Data Area Data Encapsulation [From Comer] Two types of end points: q Remote Access q Site-to-Site
Four Protocols used in VPN ØPPTP -- Point-to-Point Tunneling Protocol ØL 2 TP -- Layer 2 Tunneling Protocol ØIPsec -- Internet Protocol Security ØSOCKS – is not used as much as the ones above
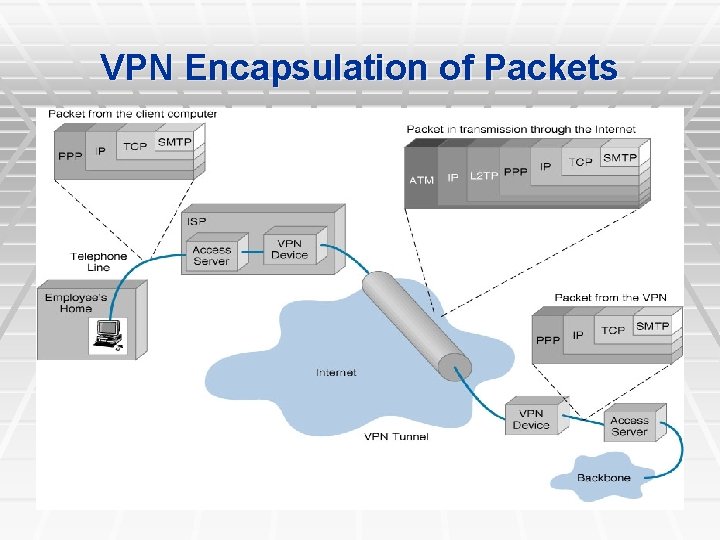
VPN Encapsulation of Packets
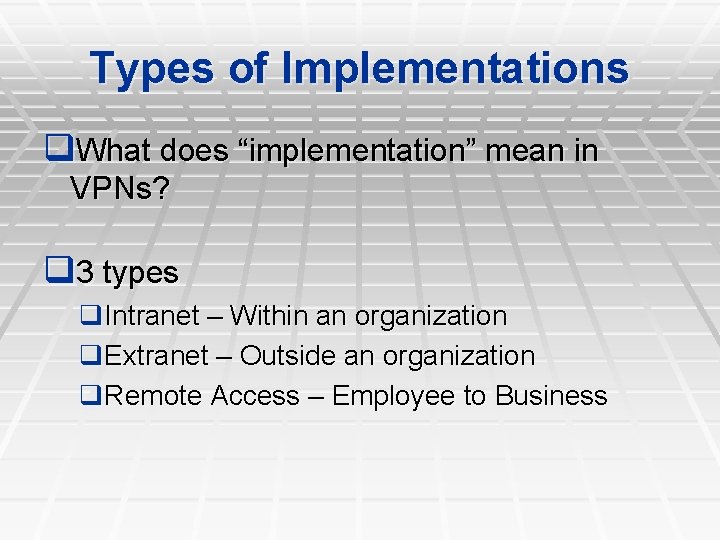
Types of Implementations q. What does “implementation” mean in VPNs? q 3 types q. Intranet – Within an organization q. Extranet – Outside an organization q. Remote Access – Employee to Business
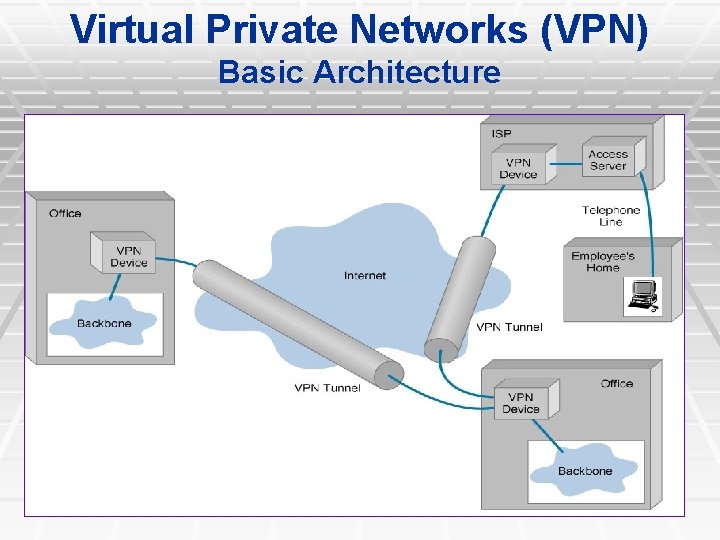
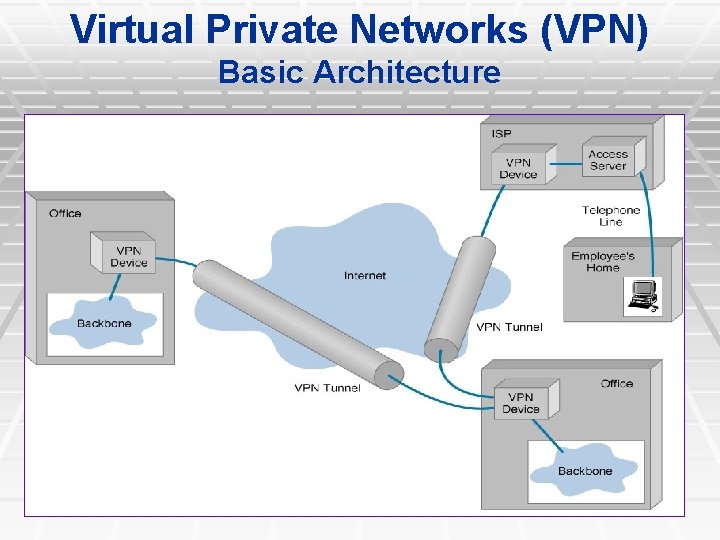
Virtual Private Networks (VPN) Basic Architecture
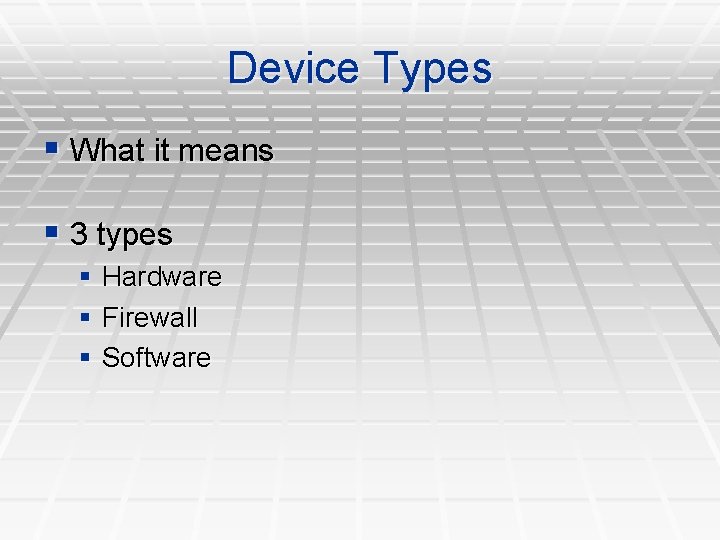
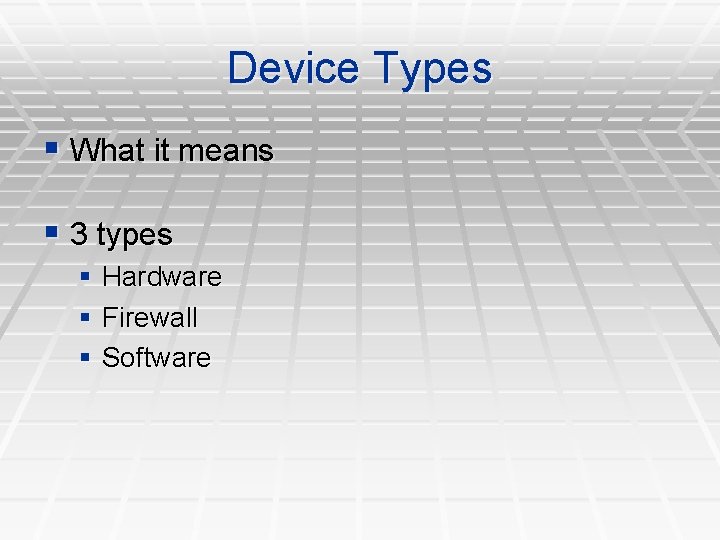
Device Types § What it means § 3 types § Hardware § Firewall § Software
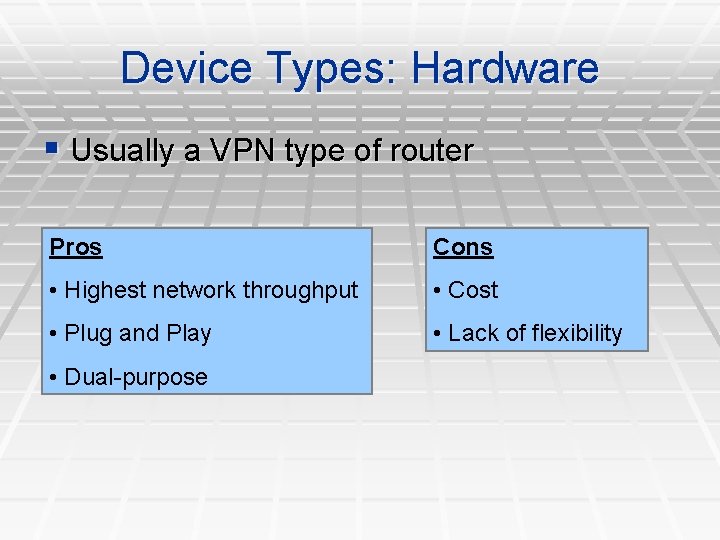
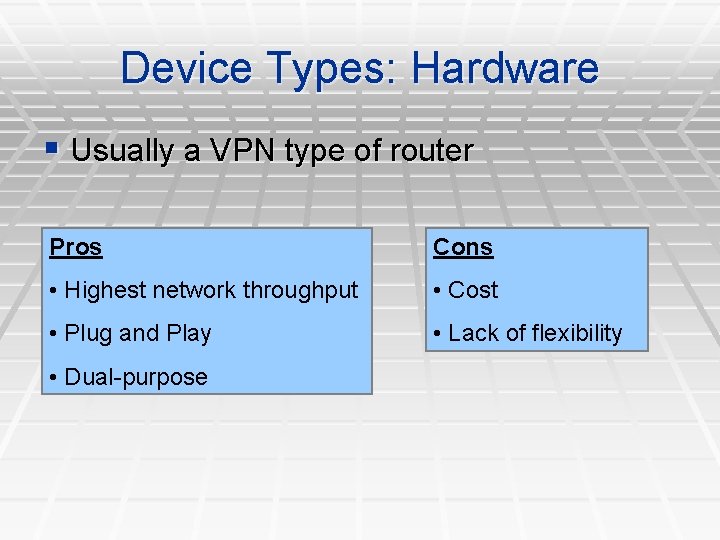
Device Types: Hardware § Usually a VPN type of router Pros Cons • Highest network throughput • Cost • Plug and Play • Lack of flexibility • Dual-purpose
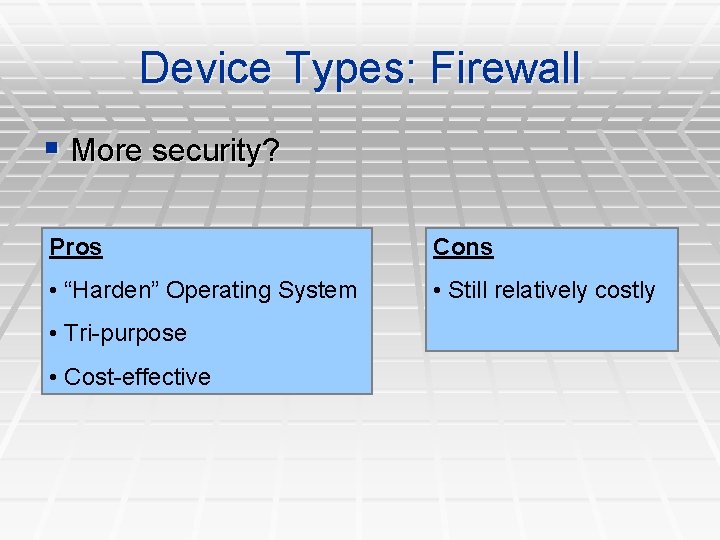
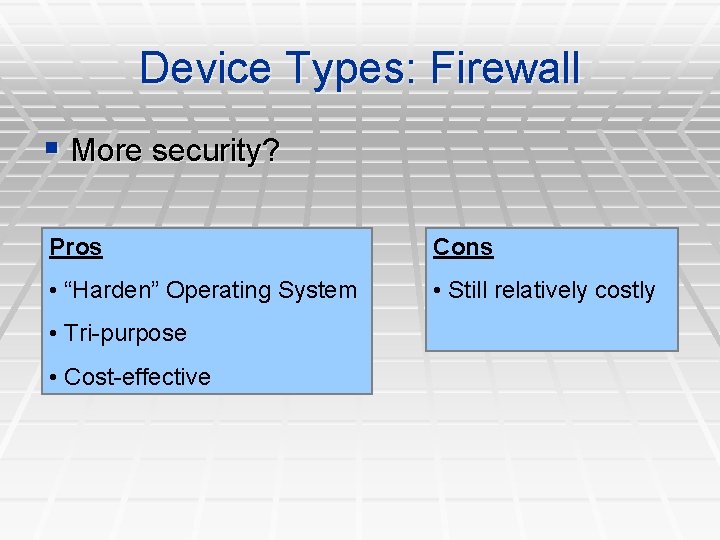
Device Types: Firewall § More security? Pros Cons • “Harden” Operating System • Still relatively costly • Tri-purpose • Cost-effective
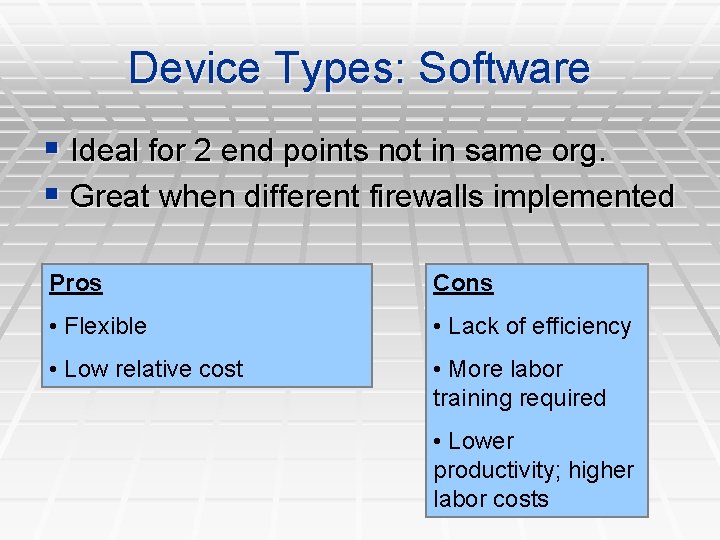
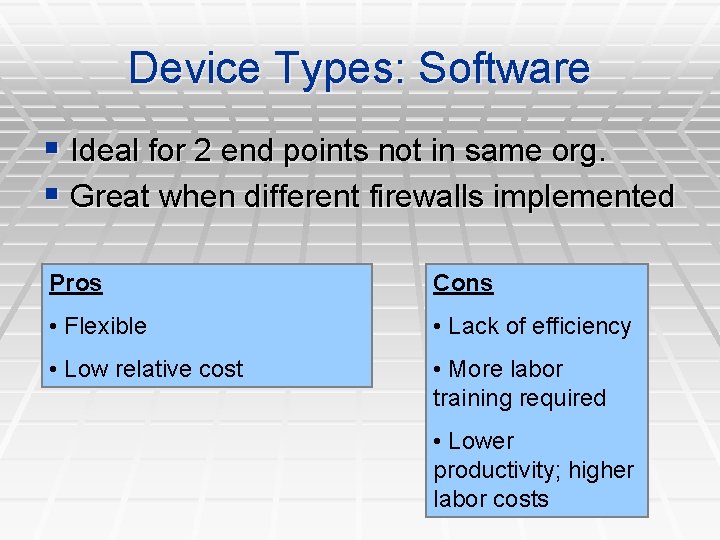
Device Types: Software § Ideal for 2 end points not in same org. § Great when different firewalls implemented Pros Cons • Flexible • Lack of efficiency • Low relative cost • More labor training required • Lower productivity; higher labor costs

Advantages VS. Disadvantages
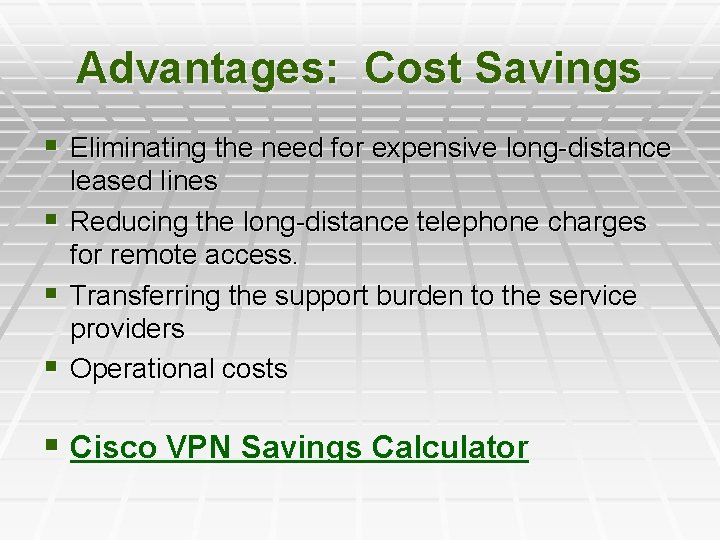
Advantages: Cost Savings § Eliminating the need for expensive long-distance leased lines § Reducing the long-distance telephone charges for remote access. § Transferring the support burden to the service providers § Operational costs § Cisco VPN Savings Calculator
Advantages: Scalability ØFlexibility of growth ØEfficiency with broadband technology
Disadvantages VPNs require an in-depth understanding of public network security issues and proper deployment of precautions Availability and performance depends on factors largely outside of their control Immature standards VPNs need to accommodate protocols other than IP and existing internal network technology
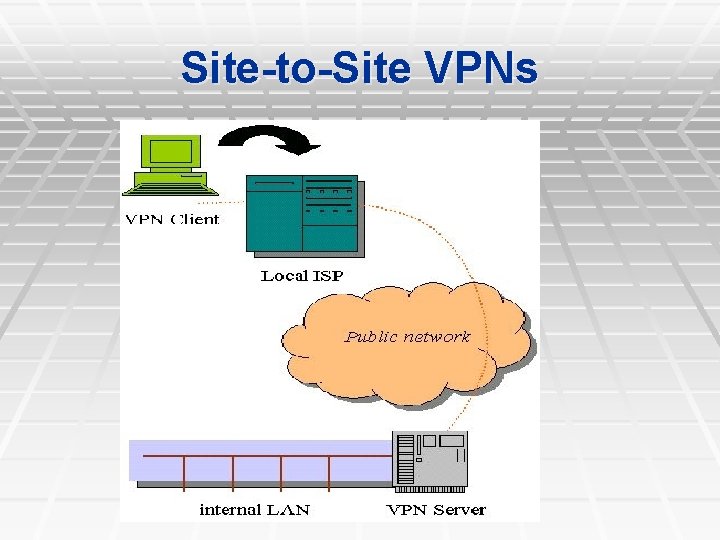
Applications: Site-to-Site VPNs Large-scale encryption between multiple fixed sites such as remote offices and central offices Network traffic is sent over the branch office Internet connection This saves the company hardware and management expenses
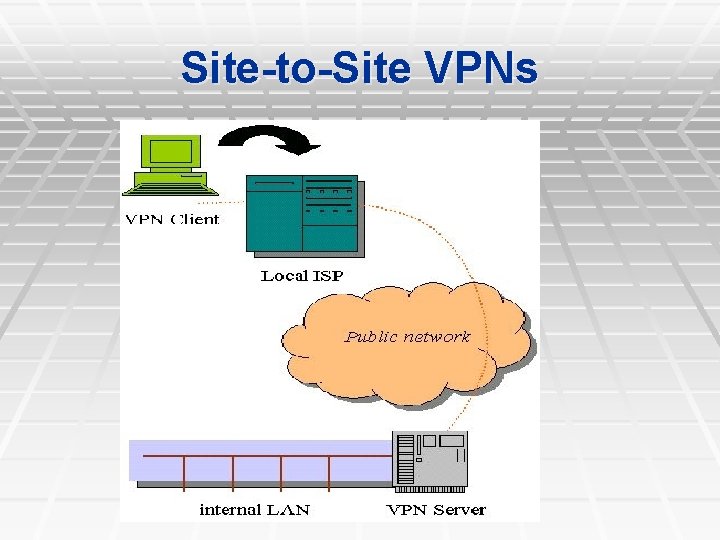
Site-to-Site VPNs
Applications: Remote Access Encrypted connections between mobile or remote users and their corporate networks Remote user can make a local call to an ISP, as opposed to a long distance call to the corporate remote access server. Ideal for a telecommuter or mobile sales people. VPN allows mobile workers & telecommuters to take advantage of broadband connectivity. i. e. DSL, Cable
Industries That May Use a VPN q Healthcare: enables the transferring of confidential patient information within the medical facilities & health care provider q Manufacturing: allow suppliers to view inventory & allow clients to purchase online safely q Retail: able to securely transfer sales data or customer info between stores & the headquarters q Banking/Financial: enables account information to be transferred safely within departments & branches q General Business: communication between remote employees can be securely exchanged
VPN Security • VPN uses encryption to provide data confidentiality. Once connected, the VPN makes use of the tunnelling mechanism to encapsulate encrypted data into a secure tunnel, with openly read headers that can cross a public network. Packets passed over a public network in this way are unreadable without proper decryption keys, thus ensuring that data is not disclosed or changed in any way during transmission. VPN can also provide a data integrity check. This is typically performed using a message digest to ensure that the data has not been tampered with during transmission.
By default, VPN does not provide or enforce strong user authentication. Users can enter a simple username and password to gain access to an internal private network from home or via other insecure networks.
Multimedia Security Part I: Digital Watermarking § Allows users to embed some data into digital contents § When data is embedded, it is not written at header part but embedded directly into digital media itself by changing media contents data
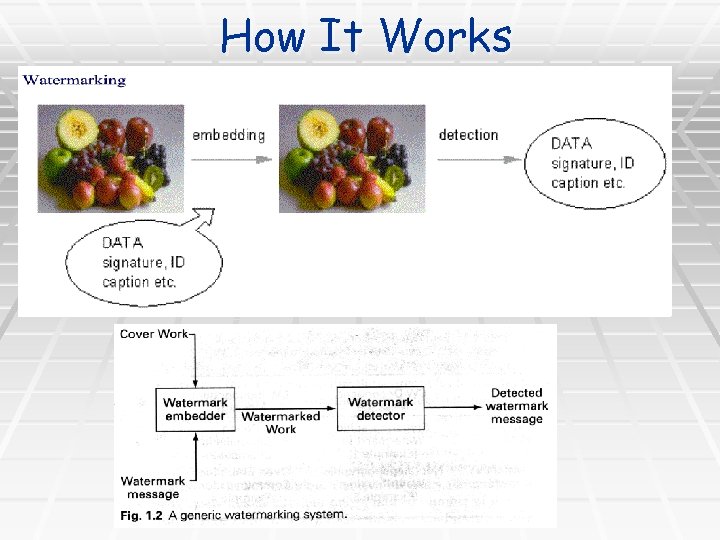
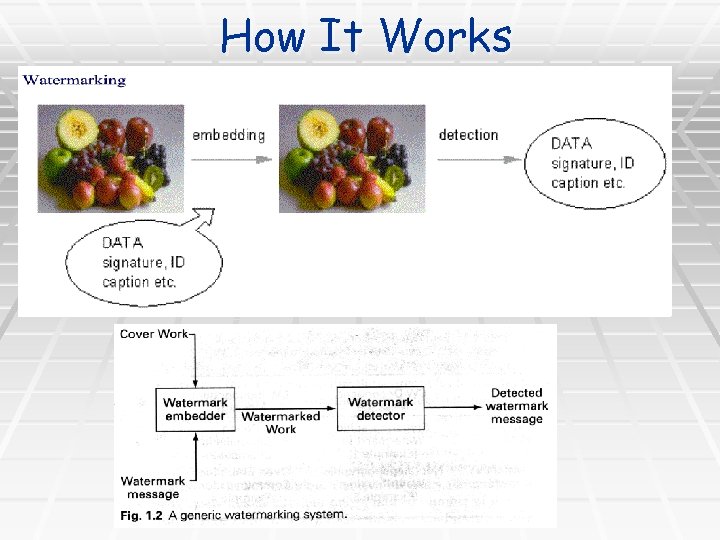
How It Works
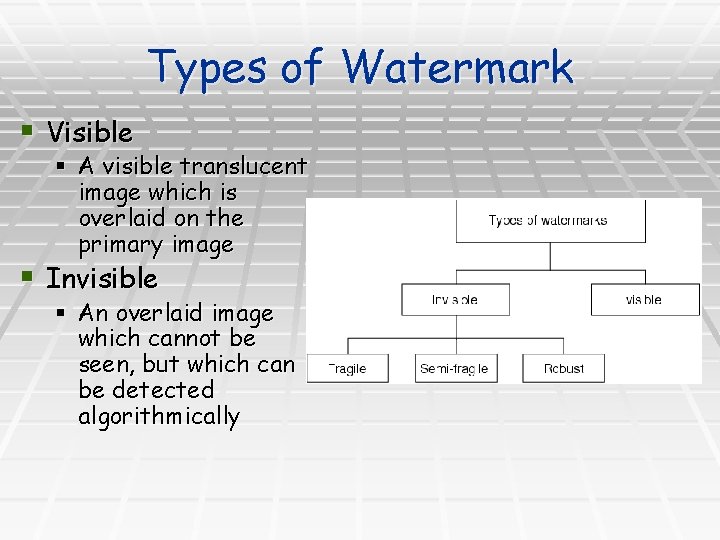
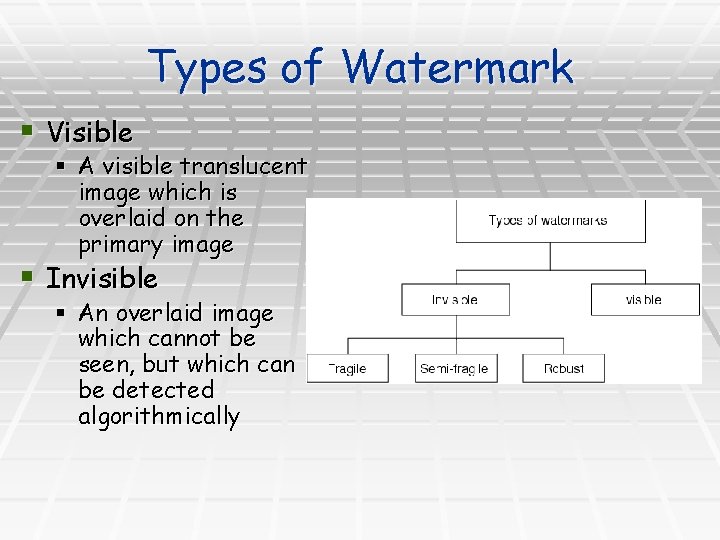
Types of Watermark § Visible § A visible translucent image which is overlaid on the primary image § Invisible § An overlaid image which cannot be seen, but which can be detected algorithmically
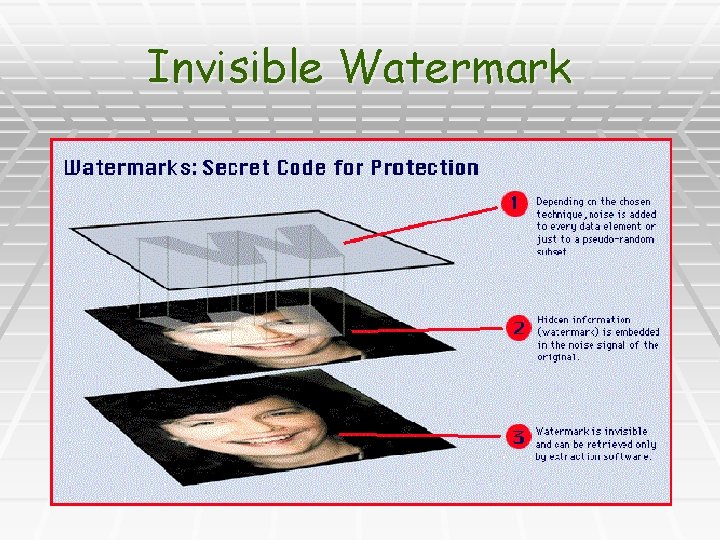
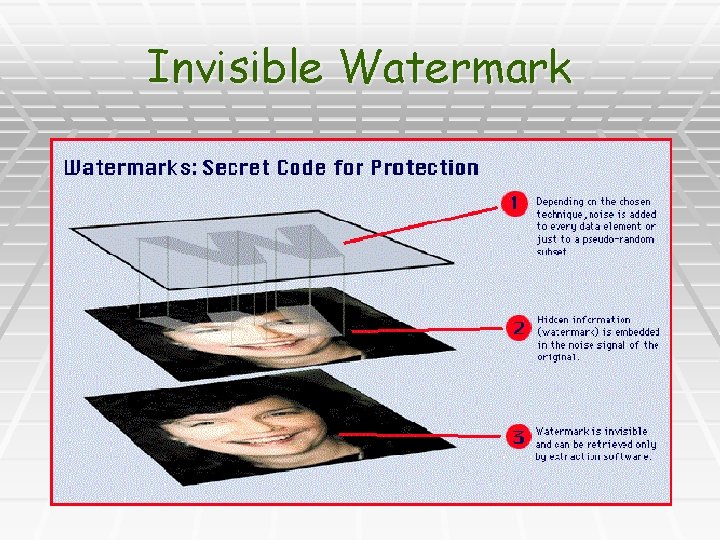
Invisible Watermark

Visible Watermark
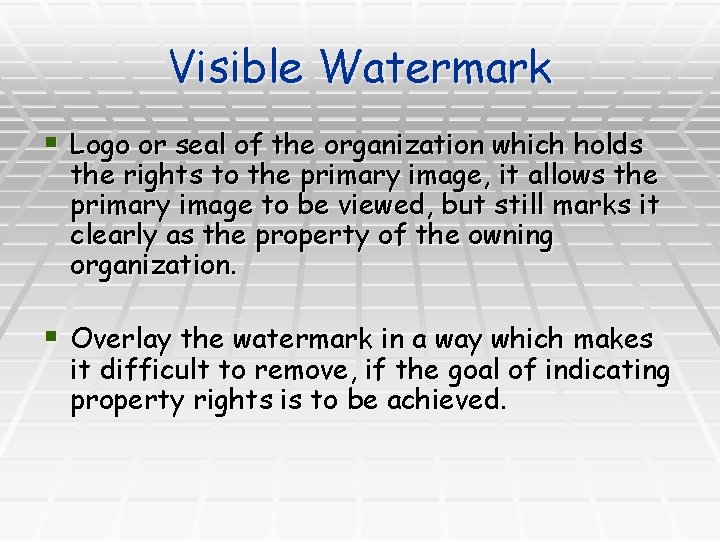
Visible Watermark § Logo or seal of the organization which holds the rights to the primary image, it allows the primary image to be viewed, but still marks it clearly as the property of the owning organization. § Overlay the watermark in a way which makes it difficult to remove, if the goal of indicating property rights is to be achieved.

Applications of Watermarking § Rights management § Contents management § Access/copy control § Authentication
Multimedia Security Part II: Encryption
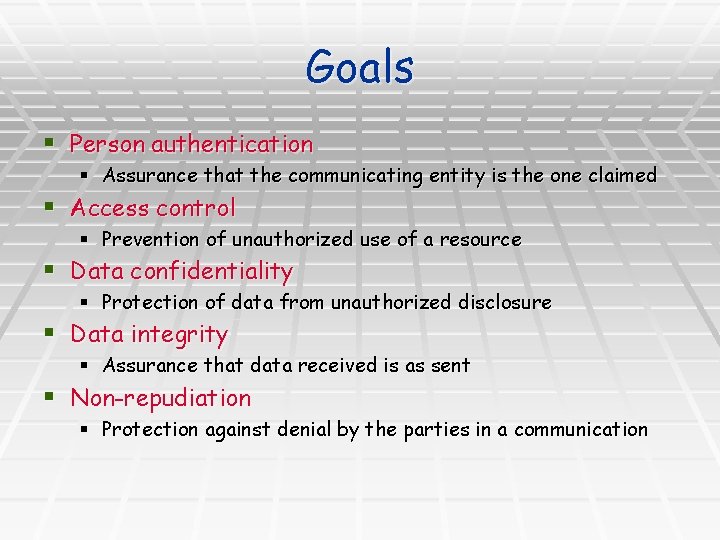
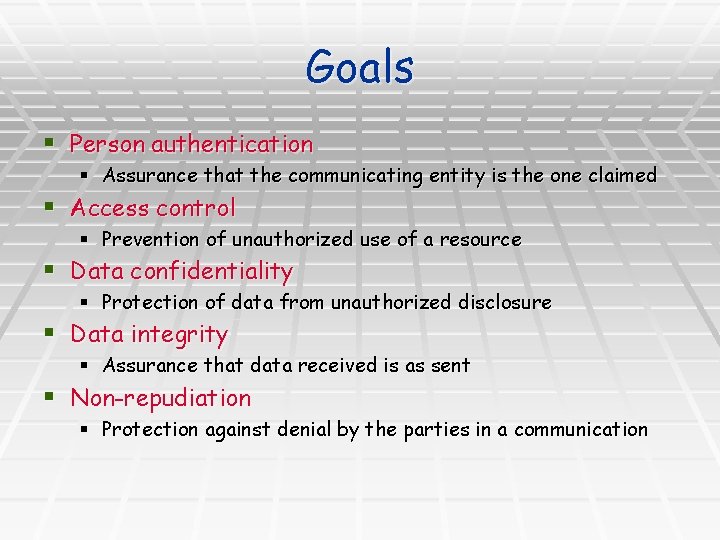
Goals § Person authentication § Assurance that the communicating entity is the one claimed § Access control § Prevention of unauthorized use of a resource § Data confidentiality § Protection of data from unauthorized disclosure § Data integrity § Assurance that data received is as sent § Non-repudiation § Protection against denial by the parties in a communication
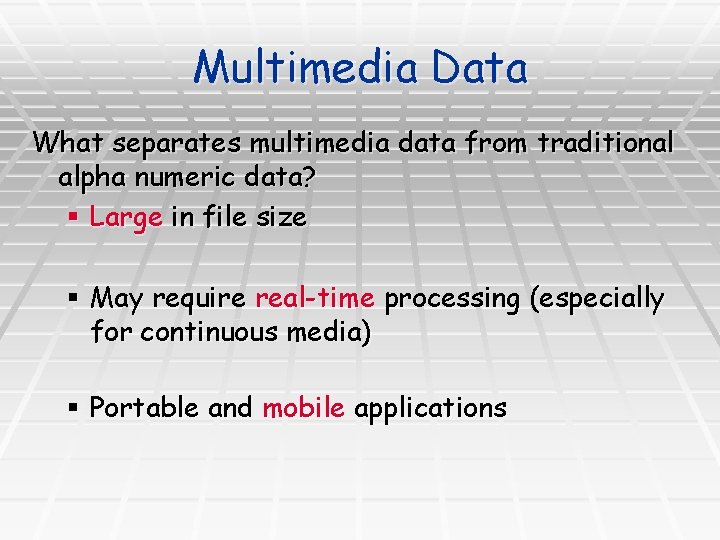
Multimedia Data What separates multimedia data from traditional alpha numeric data? § Large in file size § May require real-time processing (especially for continuous media) § Portable and mobile applications
Multimedia Encryption Approach § Signal scrambling § § § Historical approach Not compatible with modern multimedia compression Fast speed but low security § Total encryption with cryptographic ciphers § Trivial solution § High security but slow speed § Selective encryption § Most popular approach today § Limited in its range of application § Integrating encryption into entropy coding § Complementary to selective encryption § Very fast computation speed
Various Computing Platforms : 1)HPC, 2)Cluster 3)Computing Grid
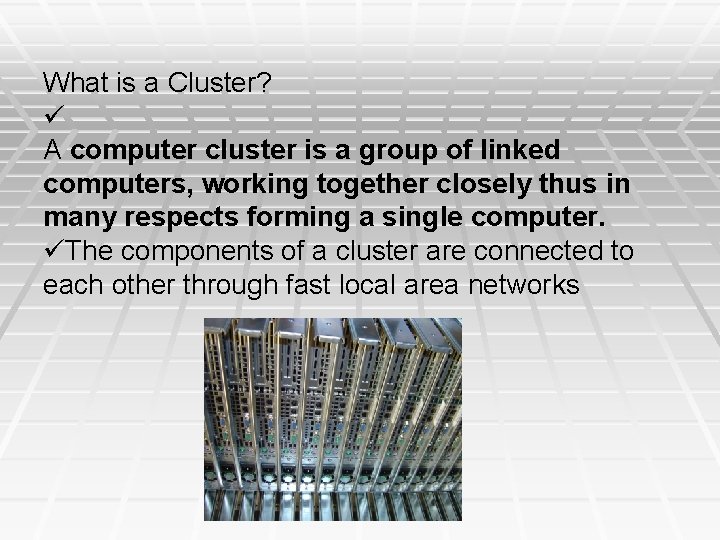
What is a Cluster? A computer cluster is a group of linked computers, working together closely thus in many respects forming a single computer. The components of a cluster are connected to each other through fast local area networks
Need for a Cluster Requirements for computing increasing fast. More data to process. compute intensive algorithms available. Approaches to supply demand Qualitative: Optimized algorithms, faster processors, more memory. Quantitative: Cluster computing, grid computing, etc.
Cluster categorizations § High Availability Cluster § Load Balancing Cluster § HPC Cluster
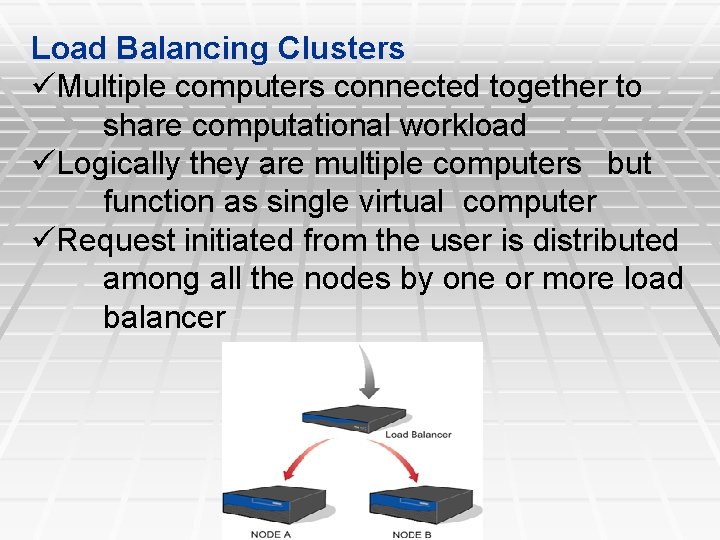
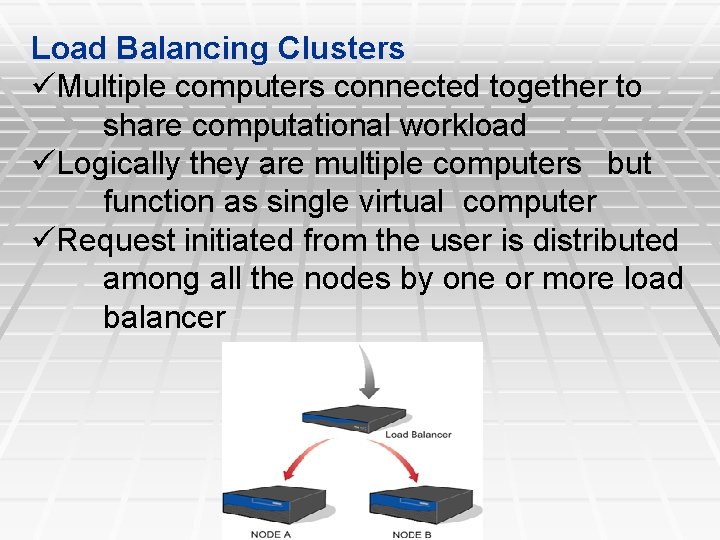
Load Balancing Clusters Multiple computers connected together to share computational workload Logically they are multiple computers but function as single virtual computer Request initiated from the user is distributed among all the nodes by one or more load balancer
HPC Clusters § HPC clusters are mainly used to increases the performance by splitting the computational task into different nodes § Mainly used in scientific computing § Popular HPC cluster implementations are nodes running with linux os and free software’s to implement the parallelism
§ The job running on the cluster nodes requires little or no inter nodes communication is called “Grid Computing” § The local Scheduling software manages the cluster nodes load balancing § Middleware such as MPI (Message Passing Interface) or PVM (Parallel Virtual Machine) permits compute clustering programs to be portable to a wide variety of clusters
What is Grid? § Definition: Grid computing is a term referring to the combination of computer resources from multiple administrative domains to reach a common goal. § Coordinates resources that are not subject to centralized control § Uses standard, open, general-purpose protocols and interfaces § Delivers nontrivial qualities of service
Grid Architecture § Grid Architecture can be described as the layers of building blocks, where each layer has a specific function, to accomplish Grid Computing Infrastructure
Grid Applications § Types : § Sequential Jobs for particular platform § Concurrent Sequential Jobs for different platforms § Homogeneous Parallel job for particular OS § Heterogeneous Parallel Jobs
§ Bio Informatics applications § High Energy Physics Applications § Weather Modelling and Predicting Ocean Currents § Disaster Management § Aerodynamic Simulations
Cloud Computing § Cloud Overview
Definition: § “A large-scale distributed computing paradigm that is driven by economies of scale, in which a pool of abstracted, virtualized, dynamically-scalable, managed computing power, storage, platforms, and services are delivered on demand to external customers over the Internet. ”
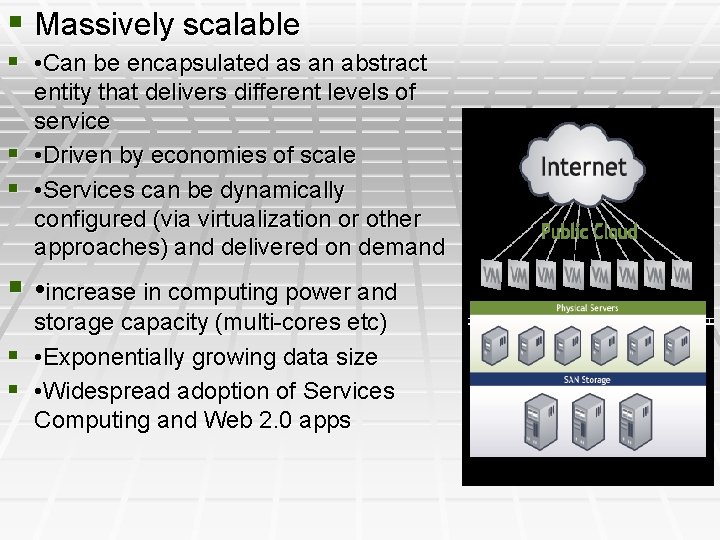
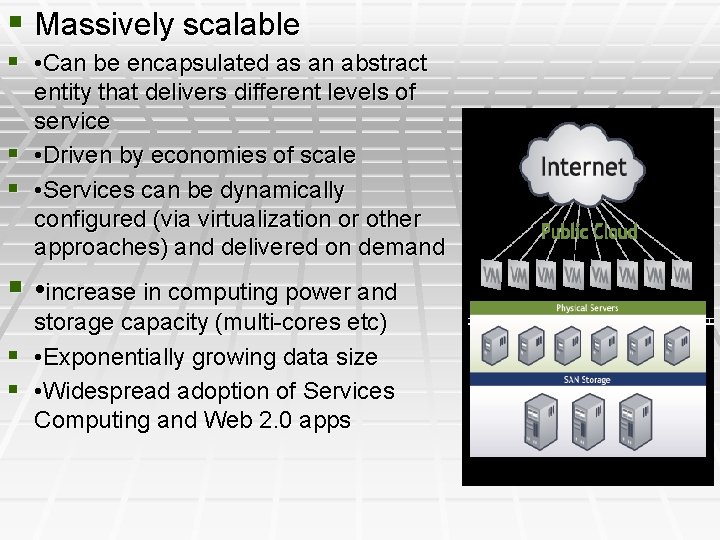
§ Massively scalable § • Can be encapsulated as an abstract entity that delivers different levels of service § • Driven by economies of scale § • Services can be dynamically configured (via virtualization or other approaches) and delivered on demand § • increase in computing power and storage capacity (multi-cores etc) § • Exponentially growing data size § • Widespread adoption of Services Computing and Web 2. 0 apps
Virtualization and Cloud Computing
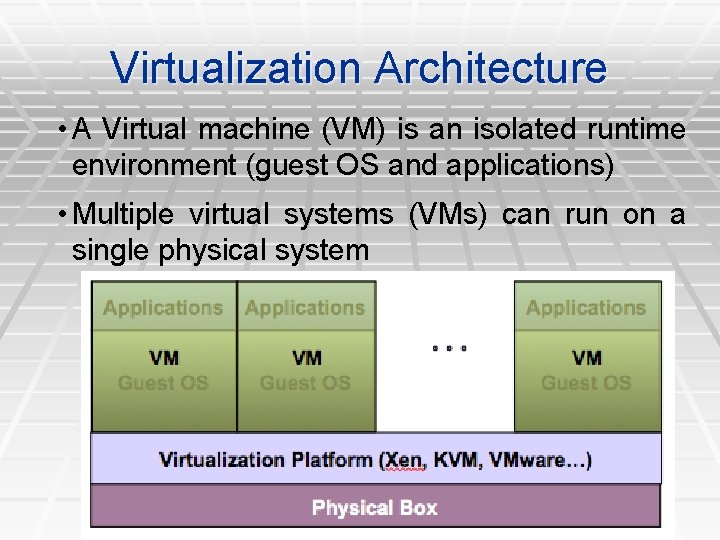
Definition § Virtualization is the ability to run multiple operating systems on a single physical system and share the underlying hardware resources* § It is the process by which one computer hosts the appearance of many computers. § Virtualization is used to improve IT throughput and costs by using physical resources as a pool from which virtual resources can be allocated.
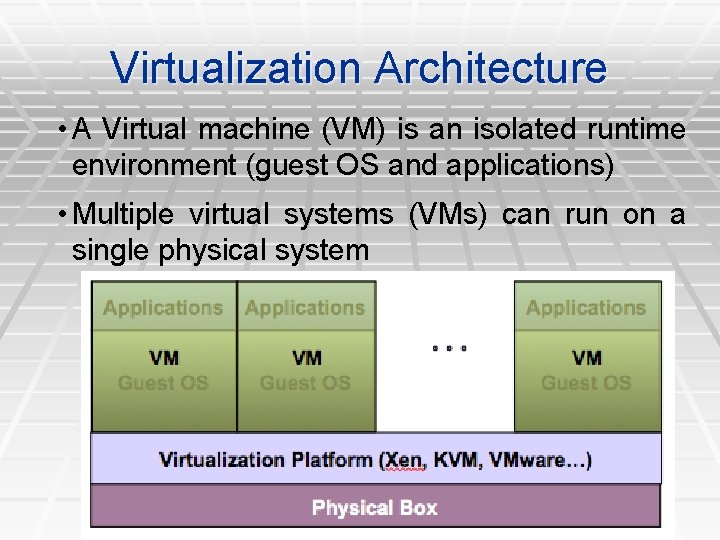
Virtualization Architecture • A Virtual machine (VM) is an isolated runtime environment (guest OS and applications) • Multiple virtual systems (VMs) can run on a single physical system
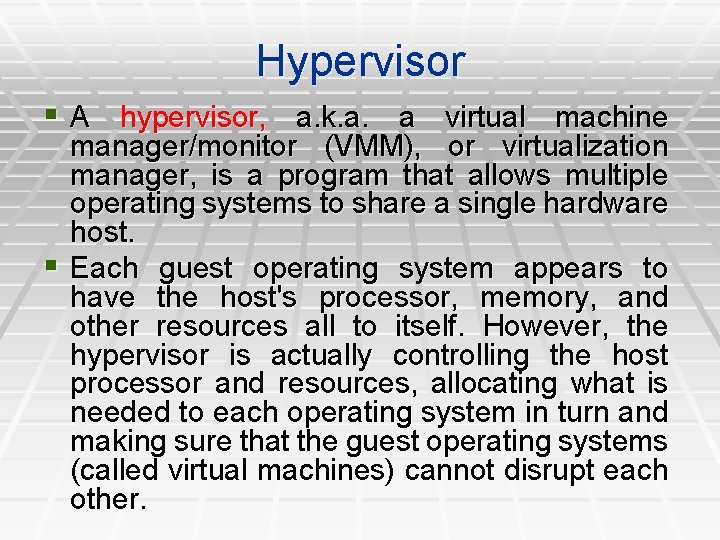
Hypervisor § A hypervisor, a. k. a. a virtual machine manager/monitor (VMM), or virtualization manager, is a program that allows multiple operating systems to share a single hardware host. § Each guest operating system appears to have the host's processor, memory, and other resources all to itself. However, the hypervisor is actually controlling the host processor and resources, allocating what is needed to each operating system in turn and making sure that the guest operating systems (called virtual machines) cannot disrupt each other.
Benefits of Virtualization § Sharing of resources helps cost reduction § Isolation: Virtual machines are isolated from § § § each other as if they are physically separated Encapsulation: Virtual machines encapsulate a complete computing environment Hardware Independence: Virtual machines run independently of underlying hardware Portability: Virtual machines can be migrated between different hosts.
Virtualization in Cloud Computing Cloud computing takes virtualization one step further: § You don’t need to own the hardware § Resources are rented as needed from a cloud § Various providers allow creating virtual servers: § Choose the OS and software each instance will have § The chosen OS will run on a large server farm § Can instantiate more virtual servers or shut down existing ones within minutes § You get billed only for what you used
Virtualization Security Challenges The trusted computing base (TCB) of a virtual machine is too large. § TCB: A small amount of software and hardware that security depends on and that we distinguish from a much larger amount that can misbehave without affecting security* § Smaller TCB more security
Virtualization Security Requirements § Scenario: A client uses the service of a cloud computing company to build a remote VM § A secure network interface § A secure secondary storage § A secure run-time environment § Build, save, restore, destroy
Virtualization Security Requirements § A secure run-time environment is the most fundamental § The first two problems already have solutions: § Network interface: Transport layer security (TLS) § Secondary storage: Network file system (NFS) § The security mechanism in the first two rely on a secure run-time environment § All the cryptographic algorithms and security protocols reside in the run-time environment
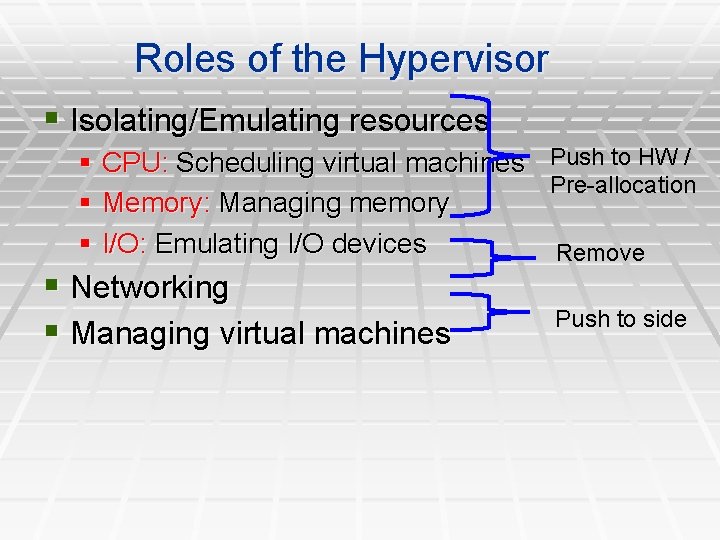
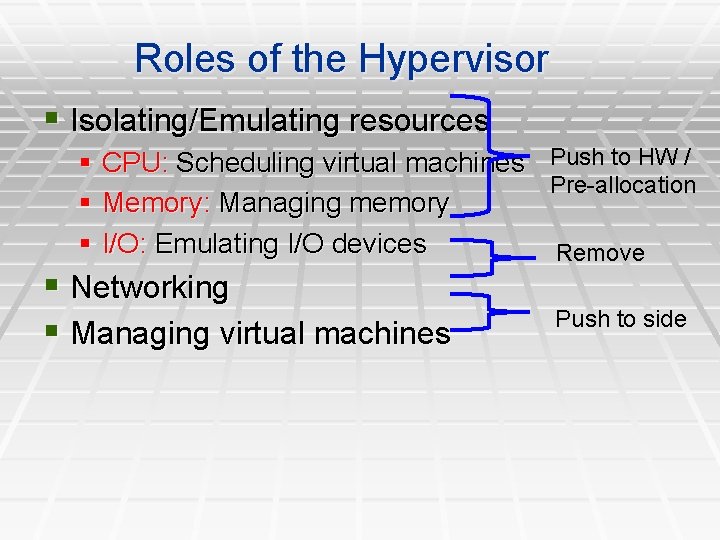
Roles of the Hypervisor § Isolating/Emulating resources § CPU: Scheduling virtual machines Push to HW / Pre-allocation § Memory: Managing memory § I/O: Emulating I/O devices Remove § Networking § Managing virtual machines Push to side
Cloud types, Cloud services types § Types of Cloud deployment § Public § Private § Hybrid § Cloud Service types § Saas § Paas § Iaas

Thank You.