Viceroy A scalable and dynamic emulation of the
Viceroy: A scalable and dynamic emulation of the Butterfly Presented in CS 294 -4 by Sailesh Krishnamurthy Sep 22, 2003
Viceroy n Goals: An overlay routing network with n n n Logarithmic path lengths Constant join/leave cost Balanced congestion (~ log(n)/n) Keys, servers mapped to unit ring [0, 1) In Chord: each node has all log(n) links In Viceroy: n n Each node has one log(n) link A link to 1/2 k distance points to a node with a link to 1/2(k+1) distance
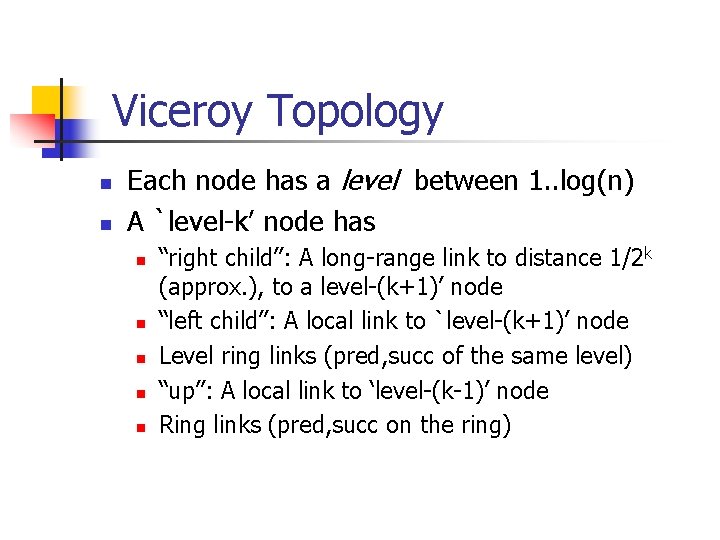
Viceroy Topology n n Each node has a level between 1. . log(n) A `level-k’ node has n n n “right child”: A long-range link to distance 1/2 k (approx. ), to a level-(k+1)’ node “left child”: A local link to `level-(k+1)’ node Level ring links (pred, succ of the same level) “up”: A local link to ‘level-(k-1)’ node Ring links (pred, succ on the ring)
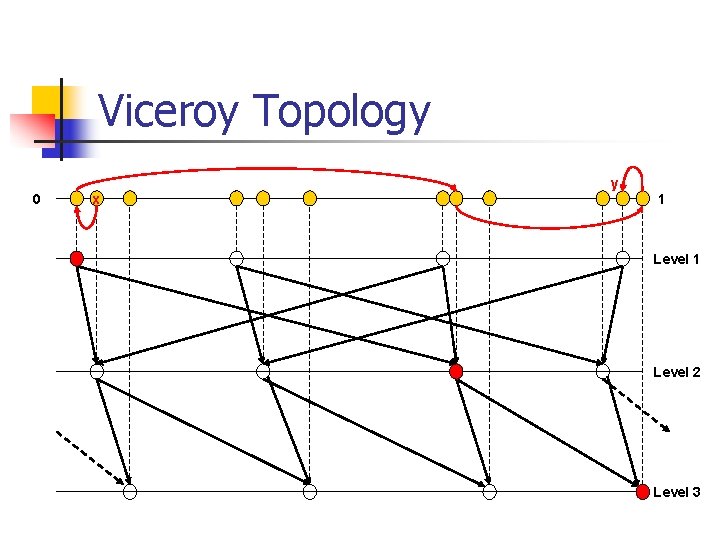
Viceroy Topology 0 x y 1 Level 2 Level 3
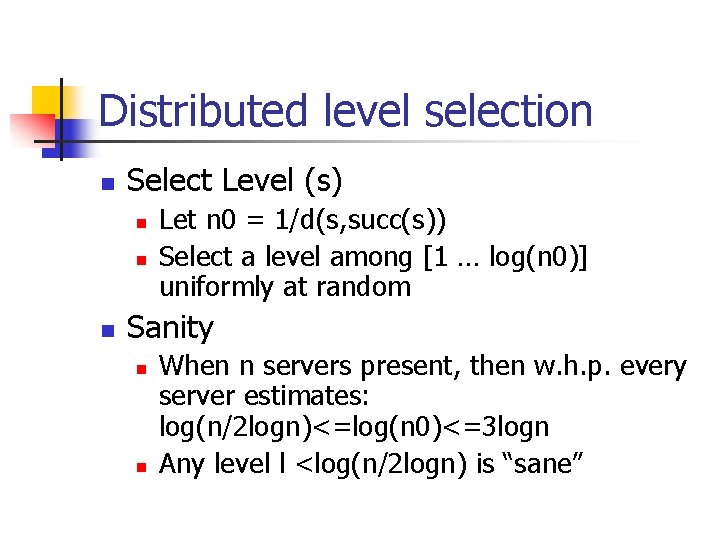
Distributed level selection n Select Level (s) n n n Let n 0 = 1/d(s, succ(s)) Select a level among [1 … log(n 0)] uniformly at random Sanity n n When n servers present, then w. h. p. every server estimates: log(n/2 logn)<=log(n 0)<=3 logn Any level l <log(n/2 logn) is “sane”
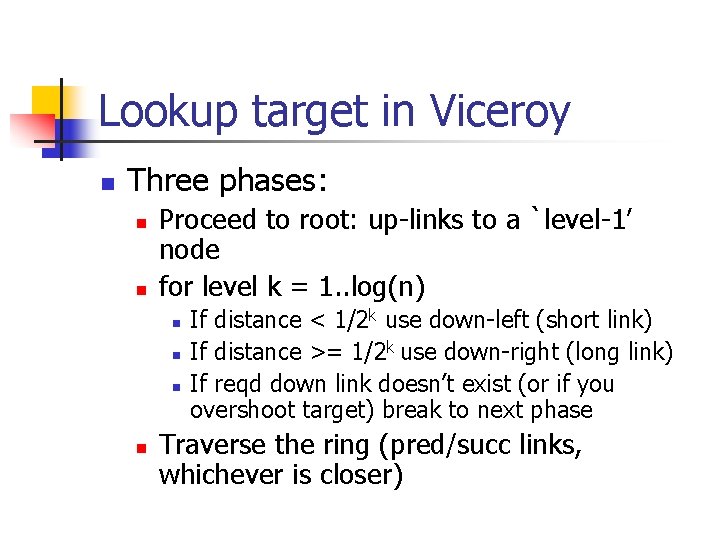
Lookup target in Viceroy n Three phases: n n Proceed to root: up-links to a `level-1’ node for level k = 1. . log(n) n n If distance < 1/2 k use down-left (short link) If distance >= 1/2 k use down-right (long link) If reqd down link doesn’t exist (or if you overshoot target) break to next phase Traverse the ring (pred/succ links, whichever is closer)
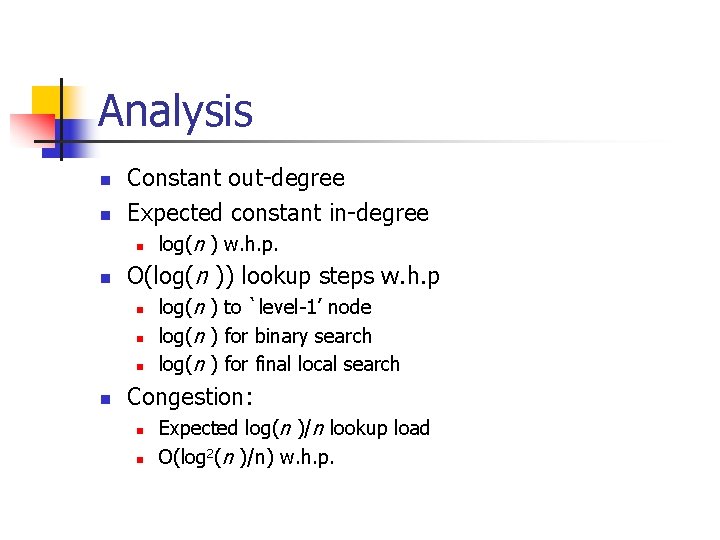
Analysis n n Constant out-degree Expected constant in-degree n n O(log(n )) lookup steps w. h. p n n log(n ) w. h. p. log(n ) to `level-1’ node log(n ) for binary search log(n ) for final local search Congestion: n n Expected log(n )/n lookup load O(log 2(n )/n) w. h. p.
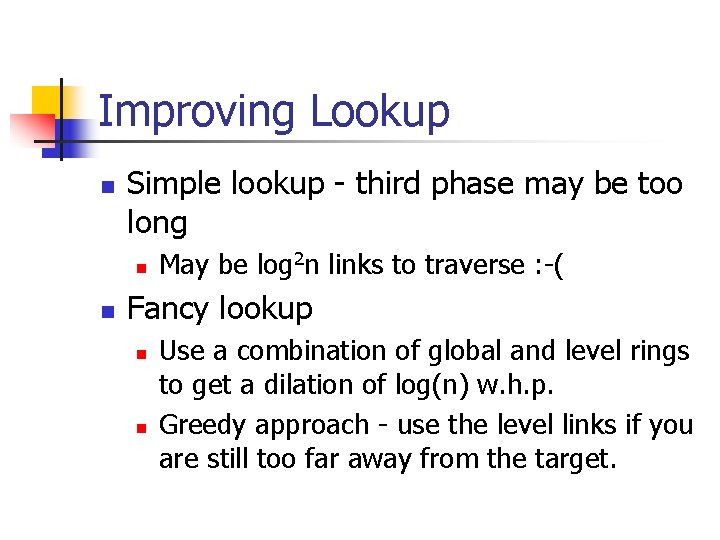
Improving Lookup n Simple lookup - third phase may be too long n n May be log 2 n links to traverse : -( Fancy lookup n n Use a combination of global and level rings to get a dilation of log(n) w. h. p. Greedy approach - use the level links if you are still too far away from the target.
What happens on node leave? n n Problem: we have constant out-degree, but even with a sparse network we could have log(n) in-degree on average Solution: “buckets” - extra background process Idea: improve identity/level-selection so that we have constant number of nodes in each stretch of (log(n)/n) nodes Maintain ~n buckets of ~log(n) contiguous non-overlapping nodes.
Bucket properties n Size: always θ(log(n)) n n n Merge with neighbouring bucket when size falls below log(n) Split bucket when size grows above clog(n) Diversity in bucket n Each level in [1. . log(n)] is represented by (1, c) nodes. Claim: this limits the indegree to 2 c - how ?
Some comparisons Skip. Nets log(n) ? ? Skip. List
Some questions n How important are const degree networks ? n n n Dilation and congestion same as chord Depends on bucket mechanism What about fault tolerance ?
- Slides: 12