V 4 Develop and Deploy Security Policies Enhance

- Slides: 13
V 4 Develop and Deploy Security Policies Enhance your overall security posture with a defensible and prescriptive policy suite. Info-Tech Research Group, Inc. is a global leader in providing IT research and advice. Info-Tech’s products and services combine actionable insight and relevant advice with ready-to-use tools and templates that cover the full spectrum of IT concerns. © 1997 -2017 Info-Tech Research Group Inc. Info-Tech Research Group 1
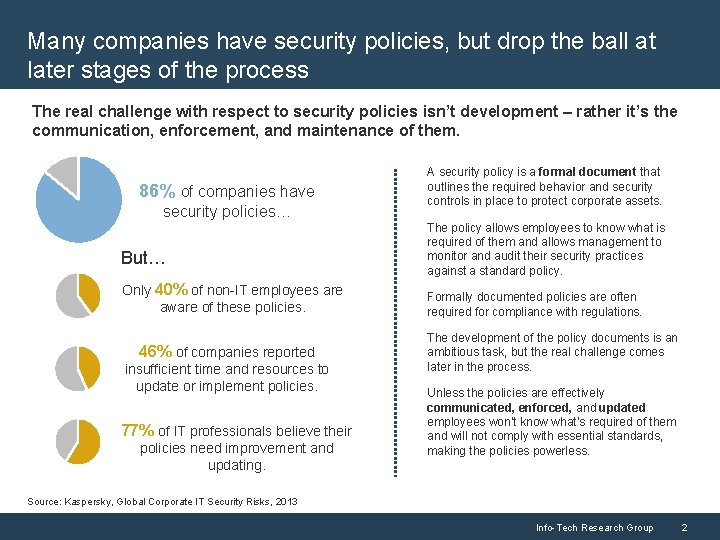
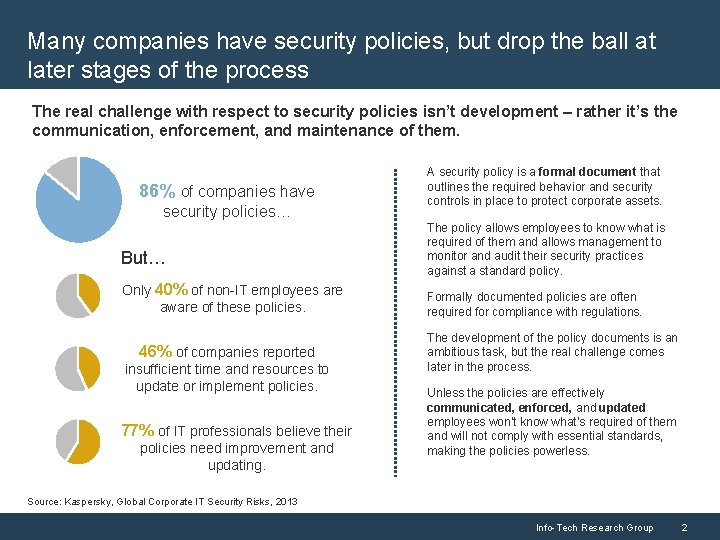
Many companies have security policies, but drop the ball at later stages of the process The real challenge with respect to security policies isn’t development – rather it’s the communication, enforcement, and maintenance of them. 86% of companies have security policies… But… Only 40% of non-IT employees are aware of these policies. 46% of companies reported insufficient time and resources to update or implement policies. 77% of IT professionals believe their policies need improvement and updating. A security policy is a formal document that outlines the required behavior and security controls in place to protect corporate assets. The policy allows employees to know what is required of them and allows management to monitor and audit their security practices against a standard policy. Formally documented policies are often required for compliance with regulations. The development of the policy documents is an ambitious task, but the real challenge comes later in the process. Unless the policies are effectively communicated, enforced, and updated employees won’t know what’s required of them and will not comply with essential standards, making the policies powerless. Source: Kaspersky, Global Corporate IT Security Risks, 2013 Info-Tech Research Group 2
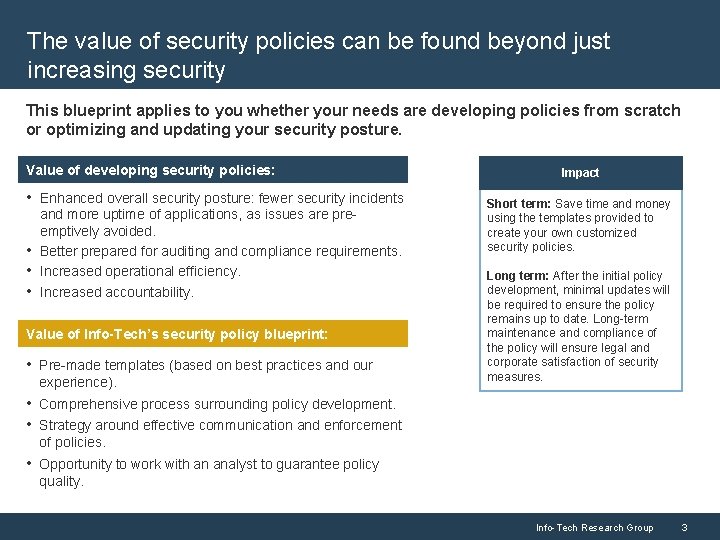
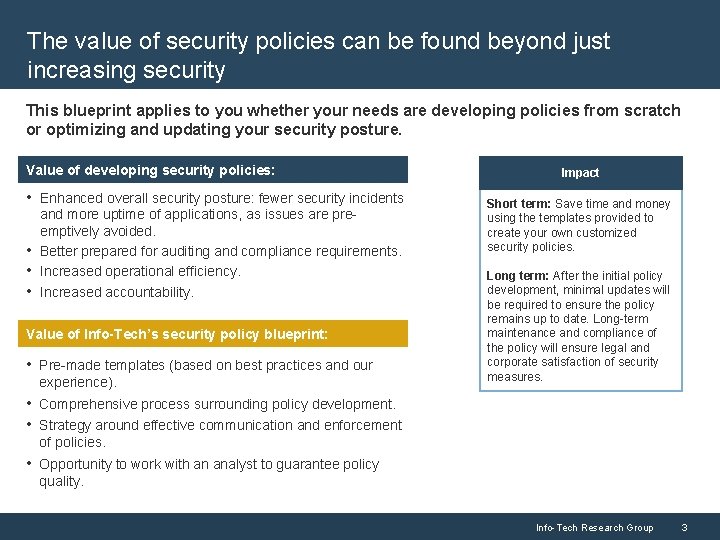
The value of security policies can be found beyond just increasing security This blueprint applies to you whether your needs are developing policies from scratch or optimizing and updating your security posture. Value of developing security policies: • Enhanced overall security posture: fewer security incidents • • • and more uptime of applications, as issues are preemptively avoided. Better prepared for auditing and compliance requirements. Increased operational efficiency. Increased accountability. Value of Info-Tech’s security policy blueprint: • Pre-made templates (based on best practices and our experience). Impact Short term: Save time and money using the templates provided to create your own customized security policies. Long term: After the initial policy development, minimal updates will be required to ensure the policy remains up to date. Long-term maintenance and compliance of the policy will ensure legal and corporate satisfaction of security measures. • Comprehensive process surrounding policy development. • Strategy around effective communication and enforcement of policies. • Opportunity to work with an analyst to guarantee policy quality. Info-Tech Research Group 3
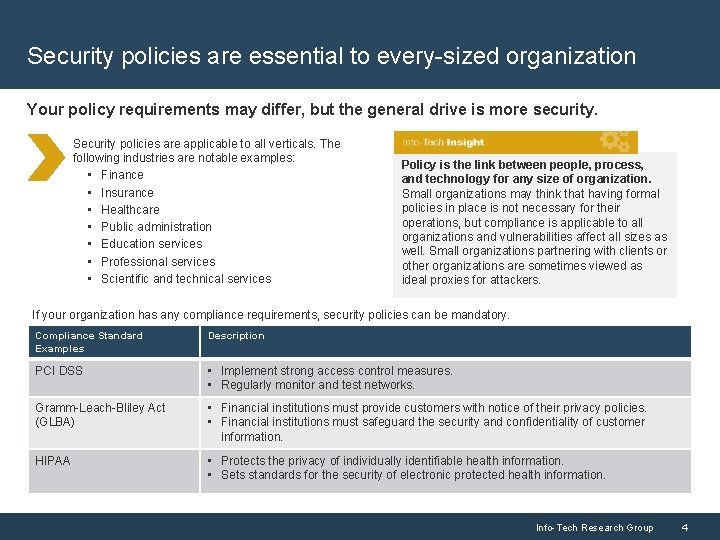
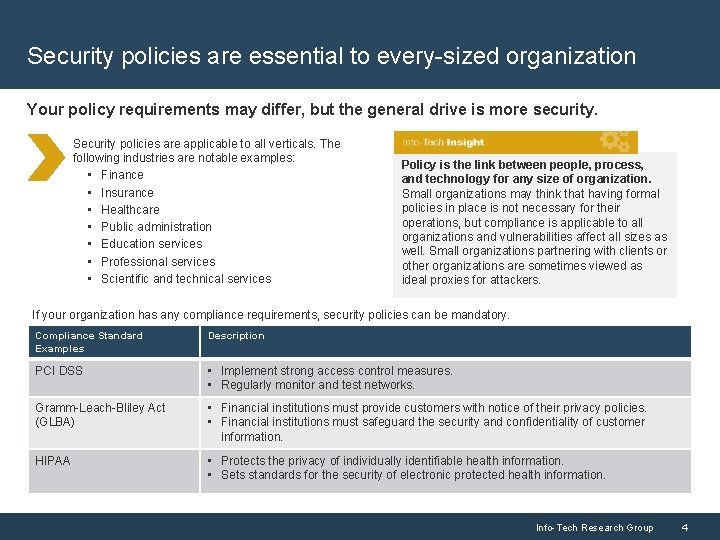
Security policies are essential to every-sized organization Your policy requirements may differ, but the general drive is more security. Security policies are applicable to all verticals. The following industries are notable examples: • Finance • Insurance • Healthcare • Public administration • Education services • Professional services • Scientific and technical services Policy is the link between people, process, and technology for any size of organization. Small organizations may think that having formal policies in place is not necessary for their operations, but compliance is applicable to all organizations and vulnerabilities affect all sizes as well. Small organizations partnering with clients or other organizations are sometimes viewed as ideal proxies for attackers. If your organization has any compliance requirements, security policies can be mandatory. Compliance Standard Examples Description PCI DSS • Implement strong access control measures. • Regularly monitor and test networks. Gramm-Leach-Bliley Act (GLBA) • Financial institutions must provide customers with notice of their privacy policies. • Financial institutions must safeguard the security and confidentiality of customer information. HIPAA • Protects the privacy of individually identifiable health information. • Sets standards for the security of electronic protected health information. Info-Tech Research Group 4
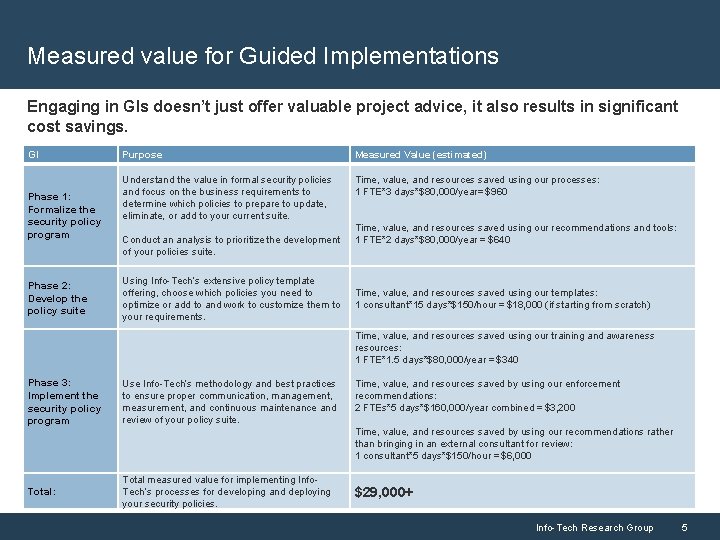
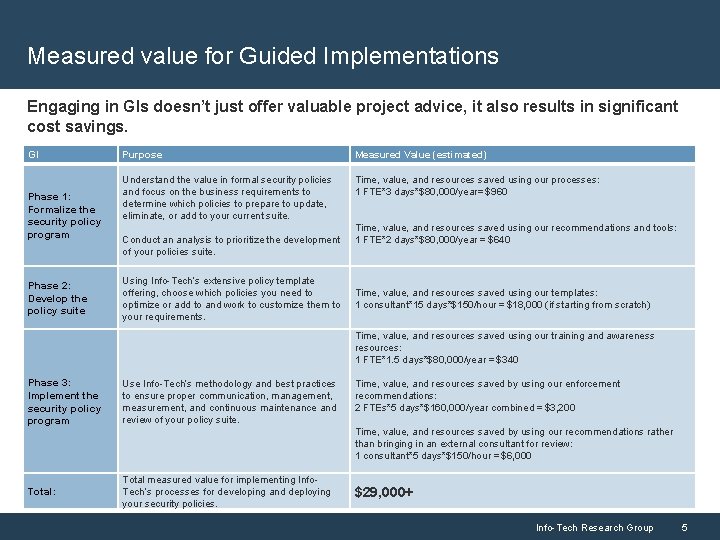
Measured value for Guided Implementations Engaging in GIs doesn’t just offer valuable project advice, it also results in significant cost savings. GI Phase 1: Formalize the security policy program Phase 2: Develop the policy suite Purpose Measured Value (estimated) Understand the value in formal security policies and focus on the business requirements to determine which policies to prepare to update, eliminate, or add to your current suite. Time, value, and resources saved using our processes: 1 FTE*3 days*$80, 000/year= $960 Conduct an analysis to prioritize the development of your policies suite. Using Info-Tech’s extensive policy template offering, choose which policies you need to optimize or add to and work to customize them to your requirements. Time, value, and resources saved using our recommendations and tools: 1 FTE*2 days*$80, 000/year = $640 Time, value, and resources saved using our templates: 1 consultant*15 days*$150/hour = $18, 000 (if starting from scratch) Time, value, and resources saved using our training and awareness resources: 1 FTE*1. 5 days*$80, 000/year = $340 Phase 3: Implement the security policy program Use Info-Tech’s methodology and best practices to ensure proper communication, management, measurement, and continuous maintenance and review of your policy suite. Total: Total measured value for implementing Info. Tech’s processes for developing and deploying your security policies. Time, value, and resources saved by using our enforcement recommendations: 2 FTEs*5 days*$160, 000/year combined = $3, 200 Time, value, and resources saved by using our recommendations rather than bringing in an external consultant for review: 1 consultant*5 days*$150/hour = $6, 000 $29, 000+ Info-Tech Research Group 5
ANALYST PERSPECTIVE A poorly implemented policy can be worse than no policy at all. A policy for policy’s sake is useless if it isn’t being used to ensure proper processes are followed. A policy should exist for more than just checking a requirement box. Policies need to be quantified, qualified, and enforced for them to be relevant. Policies should be developed based on the use cases that enable the business to run securely and smoothly. Ensure they are aligned with the corporate culture and rather than introducing hindrances to daily operations they should reflect security practices that support business goals and protection. No published framework is going to be a perfect fit for any organization, so take the time to compare business operations and culture with security requirements to determine which ones apply to keep your organization secure. Céline Gravelines, Research Manager, Security, Risk & Compliance Info-Tech Research Group 6
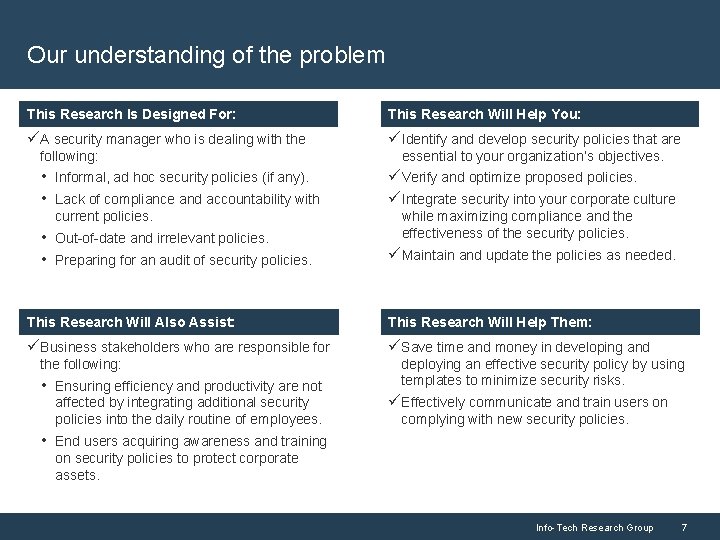
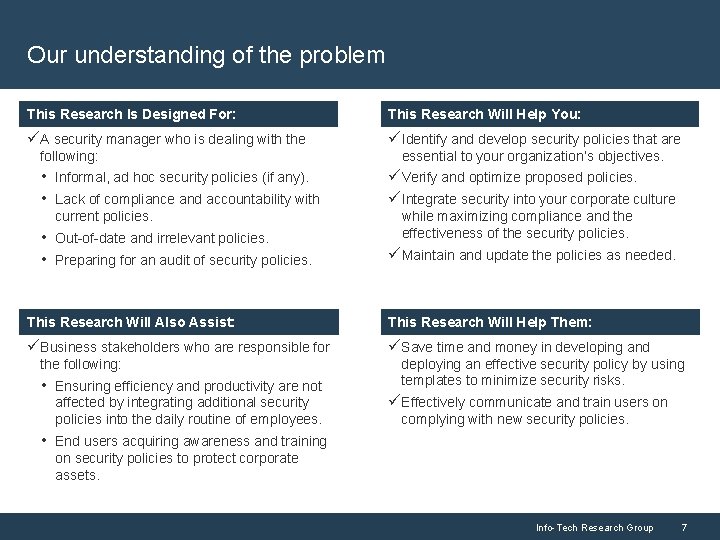
Our understanding of the problem This Research is Designed For: This Research Is Designed For: This Research Will Help You: üA security manager who is dealing with the üIdentify and develop security policies that are following: • Informal, ad hoc security policies (if any). • Lack of compliance and accountability with current policies. • Out-of-date and irrelevant policies. • Preparing for an audit of security policies. essential to your organization’s objectives. üVerify and optimize proposed policies. üIntegrate security into your corporate culture while maximizing compliance and the effectiveness of the security policies. üMaintain and update the policies as needed. This Research Will Assist: This Research Will Also Assist: This Research Will Help You: This Research Will Help Them: üBusiness stakeholders who are responsible for üSave time and money in developing and the following: • Ensuring efficiency and productivity are not affected by integrating additional security policies into the daily routine of employees. deploying an effective security policy by using templates to minimize security risks. üEffectively communicate and train users on complying with new security policies. • End users acquiring awareness and training on security policies to protect corporate assets. Info-Tech Research Group 7
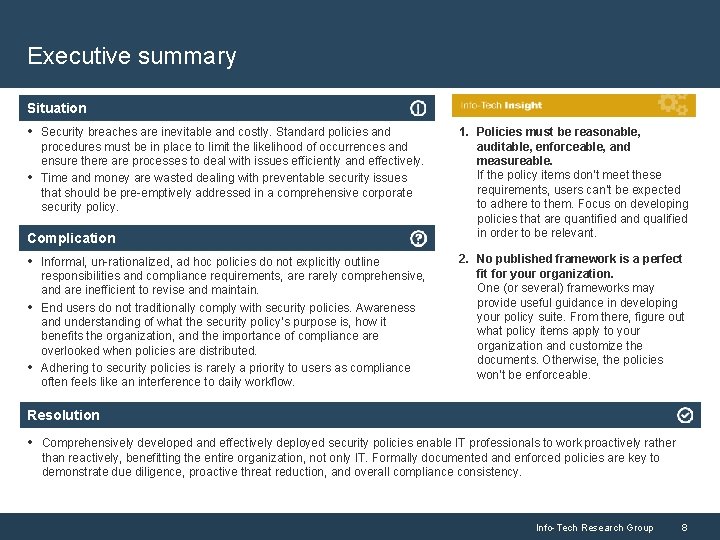
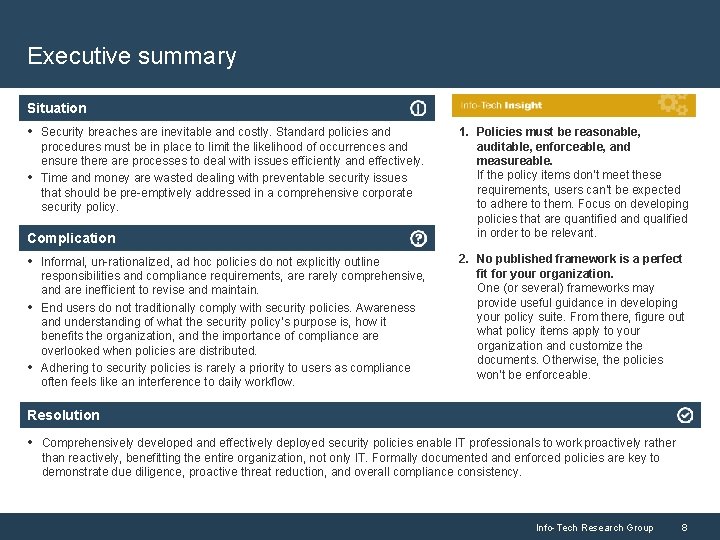
Executive summary Situation • Security breaches are inevitable and costly. Standard policies and • procedures must be in place to limit the likelihood of occurrences and ensure there are processes to deal with issues efficiently and effectively. Time and money are wasted dealing with preventable security issues that should be pre-emptively addressed in a comprehensive corporate security policy. Complication • Informal, un-rationalized, ad hoc policies do not explicitly outline • • responsibilities and compliance requirements, are rarely comprehensive, and are inefficient to revise and maintain. End users do not traditionally comply with security policies. Awareness and understanding of what the security policy’s purpose is, how it benefits the organization, and the importance of compliance are overlooked when policies are distributed. Adhering to security policies is rarely a priority to users as compliance often feels like an interference to daily workflow. 1. Policies must be reasonable, auditable, enforceable, and measureable. If the policy items don’t meet these requirements, users can’t be expected to adhere to them. Focus on developing policies that are quantified and qualified in order to be relevant. 2. No published framework is a perfect fit for your organization. One (or several) frameworks may provide useful guidance in developing your policy suite. From there, figure out what policy items apply to your organization and customize the documents. Otherwise, the policies won’t be enforceable. Resolution • Comprehensively developed and effectively deployed security policies enable IT professionals to work proactively rather than reactively, benefitting the entire organization, not only IT. Formally documented and enforced policies are key to demonstrate due diligence, proactive threat reduction, and overall compliance consistency. Info-Tech Research Group 8
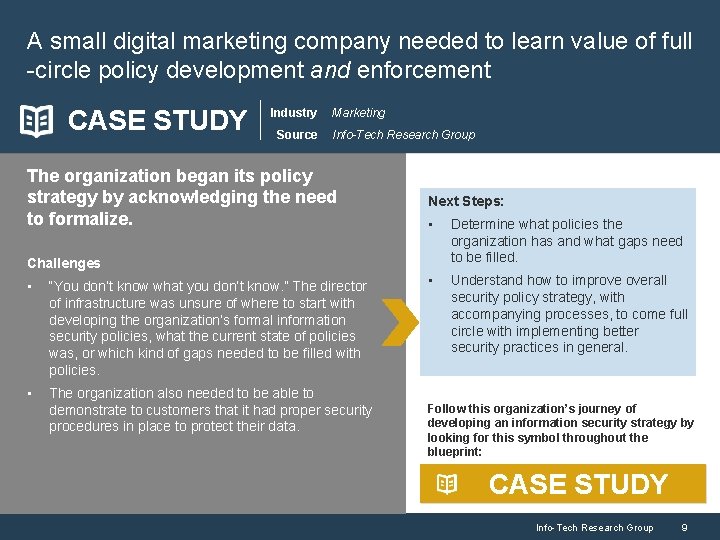
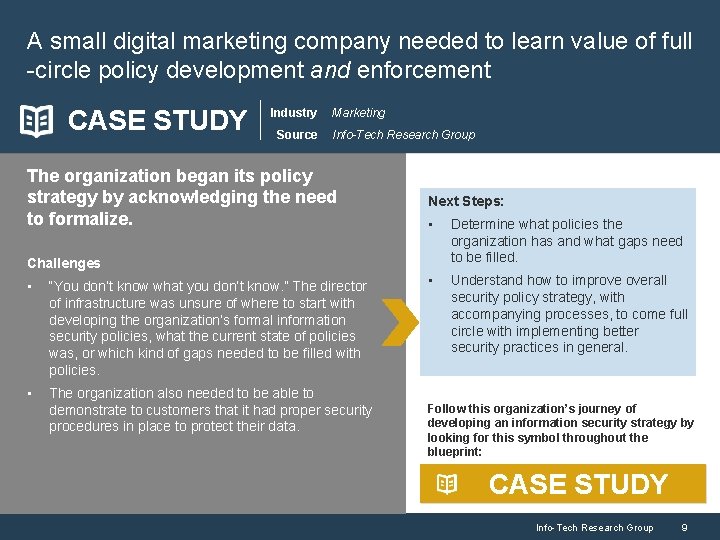
A small digital marketing company needed to learn value of full -circle policy development and enforcement CASE STUDY Industry Source Marketing Info-Tech Research Group The organization began its policy strategy by acknowledging the need to formalize. Next Steps: • Determine what policies the organization has and what gaps need to be filled. • Understand how to improve overall security policy strategy, with accompanying processes, to come full circle with implementing better security practices in general. Challenges • “You don’t know what you don’t know. ” The director of infrastructure was unsure of where to start with developing the organization’s formal information security policies, what the current state of policies was, or which kind of gaps needed to be filled with policies. • The organization also needed to be able to demonstrate to customers that it had proper security procedures in place to protect their data. Follow this organization’s journey of developing an information security strategy by looking for this symbol throughout the blueprint: CASE STUDY Info-Tech Research Group 9
Use these icons to help direct you as you navigate this research Use these icons to help guide you through each step of the blueprint and direct you to content related to the recommended activities. This icon denotes a slide where a supporting Info-Tech tool or template will help you perform the activity or step associated with the slide. Refer to the supporting tool or template to get the best results and proceed to the next step of the project. This icon denotes a slide with an associated activity. The activity can be performed either as part of your project or with the support of Info-Tech team members, who will come onsite to facilitate a workshop for your organization. Info-Tech Research Group 10

Info-Tech offers various levels of support to best suit your needs DIY Toolkit “Our team has already made this critical project a priority, and we have the time and capability, but some guidance along the way would be helpful. ” Guided Implementation Workshop Consulting “Our team knows that we need to fix a process, but we need assistance to determine where to focus. Some check-ins along the way would help keep us on track. ” “We need to hit the ground running and get this project kicked off immediately. Our team has the ability to take this over once we get a framework and strategy in place. ” “Our team does not have the time or the knowledge to take this project on. We need assistance through the entirety of this project. ” Diagnostics and consistent frameworks used throughout all four options Info-Tech Research Group 11
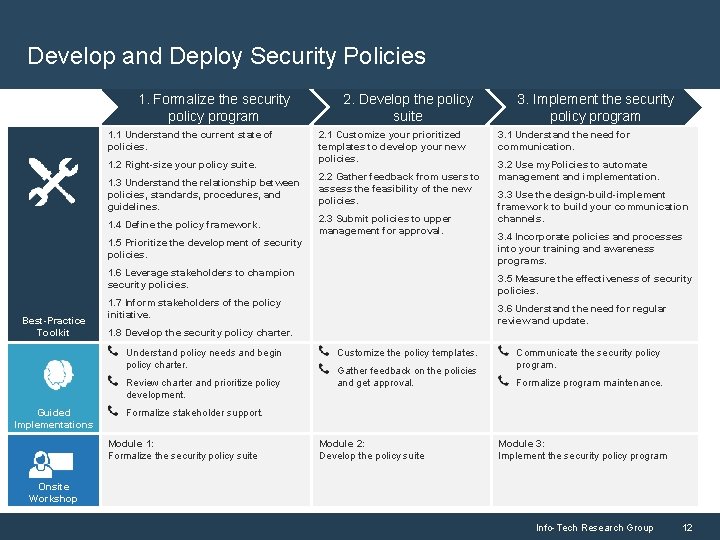
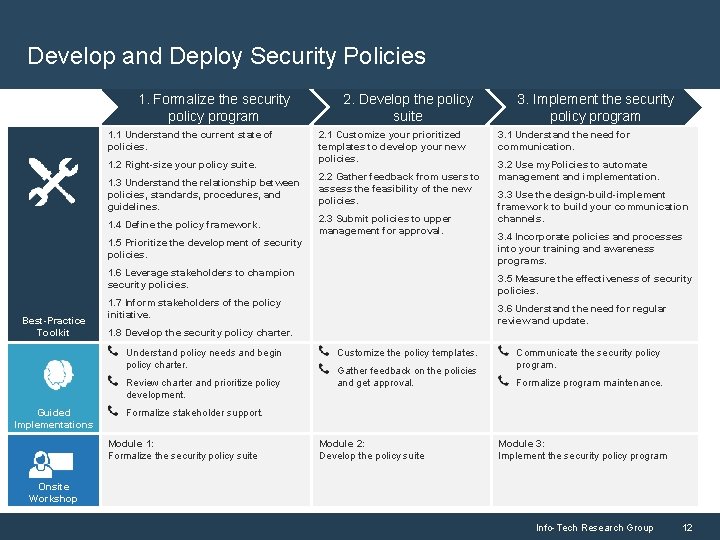
Develop and Deploy Security Policies 1. Formalize the security policy program 1. 1 Understand the current state of policies. 1. 2 Right-size your policy suite. 1. 3 Understand the relationship between policies, standards, procedures, and guidelines. 1. 4 Define the policy framework. 2. Develop the policy suite 2. 1 Customize your prioritized templates to develop your new policies. 2. 2 Gather feedback from users to assess the feasibility of the new policies. 2. 3 Submit policies to upper management for approval. 1. 5 Prioritize the development of security policies. 1. 6 Leverage stakeholders to champion security policies. Best-Practice Toolkit 3. 1 Understand the need for communication. 3. 2 Use my. Policies to automate management and implementation. 3. 3 Use the design-build-implement framework to build your communication channels. 3. 4 Incorporate policies and processes into your training and awareness programs. 3. 5 Measure the effectiveness of security policies. 1. 7 Inform stakeholders of the policy initiative. 3. 6 Understand the need for regular review and update. 1. 8 Develop the security policy charter. Understand policy needs and begin policy charter. Review charter and prioritize policy development. Guided Implementations 3. Implement the security policy program Customize the policy templates. Gather feedback on the policies and get approval. Communicate the security policy program. Formalize program maintenance. Formalize stakeholder support. Module 1: Formalize the security policy suite Module 2: Develop the policy suite Module 3: Implement the security policy program Onsite Workshop Info-Tech Research Group 12
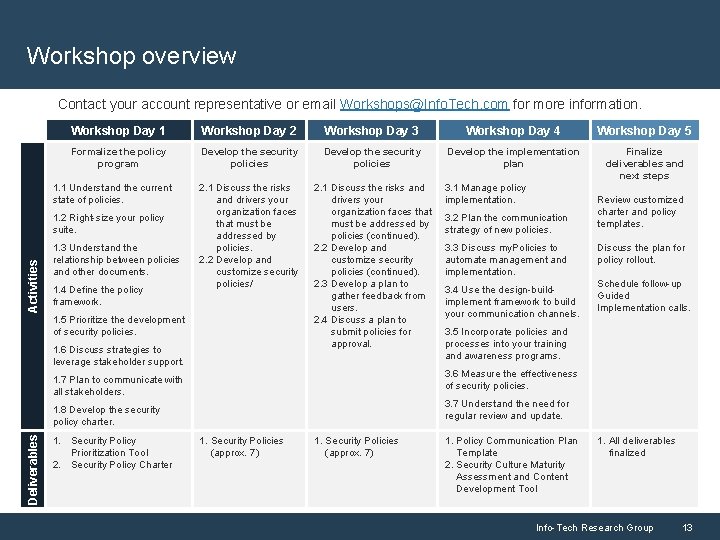
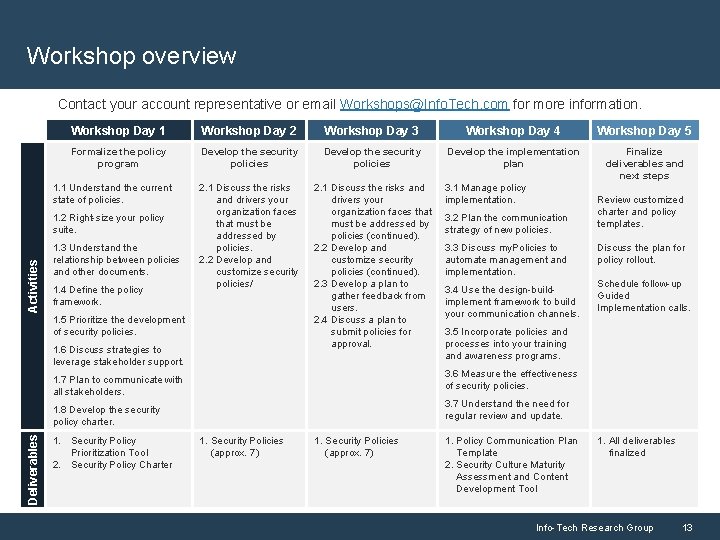
Workshop overview Contact your account representative or email Workshops@Info. Tech. com for more information. Workshop Day 1 Workshop Day 2 Workshop Day 3 Workshop Day 4 Workshop Day 5 Formalize the policy program Develop the security policies Develop the implementation plan Finalize deliverables and next steps 1. 1 Understand the current state of policies. 2. 1 Discuss the risks and drivers your organization faces that must be addressed by policies. 2. 2 Develop and customize security policies/ 2. 1 Discuss the risks and drivers your organization faces that must be addressed by policies (continued). 2. 2 Develop and customize security policies (continued). 2. 3 Develop a plan to gather feedback from users. 2. 4 Discuss a plan to submit policies for approval. Activities 1. 2 Right-size your policy suite. 1. 3 Understand the relationship between policies and other documents. 1. 4 Define the policy framework. 1. 5 Prioritize the development of security policies. 1. 6 Discuss strategies to leverage stakeholder support. 3. 3 Discuss my. Policies to automate management and implementation. 3. 4 Use the design-buildimplement framework to build your communication channels. Discuss the plan for policy rollout. Schedule follow-up Guided Implementation calls. 3. 5 Incorporate policies and processes into your training and awareness programs. 3. 7 Understand the need for regular review and update. 1. 8 Develop the security policy charter. Deliverables 3. 2 Plan the communication strategy of new policies. Review customized charter and policy templates. 3. 6 Measure the effectiveness of security policies. 1. 7 Plan to communicate with all stakeholders. 1. Security Policy Prioritization Tool 2. Security Policy Charter 3. 1 Manage policy implementation. 1. Security Policies (approx. 7) 1. Policy Communication Plan Template 2. Security Culture Maturity Assessment and Content Development Tool 1. All deliverables finalized Info-Tech Research Group 13