Use of Fuzzing in detecting security vulnerabilities Biswajit
Use of Fuzzing in detecting security vulnerabilities Biswajit Mazumder Rohit Hooda Arpan Chowdhary
Agenda � What is Fuzzing? � Fuzzing techniques � Types of Fuzzing � Fuzzing explained � Case study and changes: SCRASHME � sys_getdomainname() � vmsplice() : Local Root Exploit � Conclusion
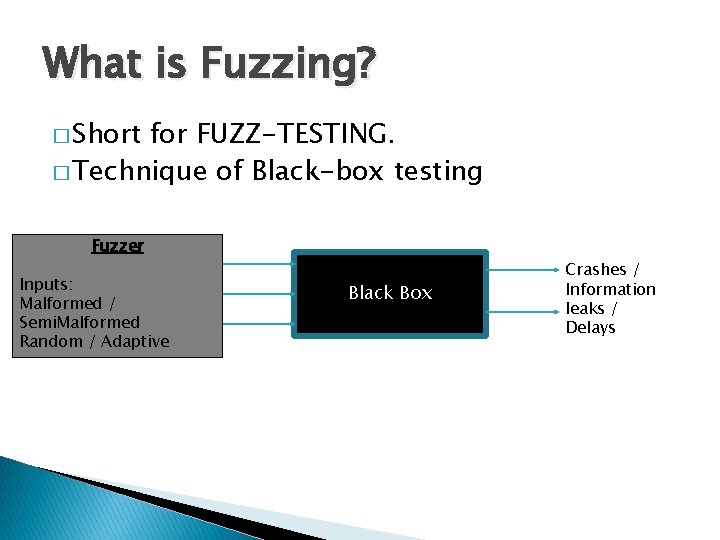
What is Fuzzing? � Short for FUZZ-TESTING. � Technique of Black-box testing Fuzzer Inputs: Malformed / Semi. Malformed Random / Adaptive Black Box Crashes / Information leaks / Delays

Fuzzing Techniques � Event-Driven Fuzz � Character-Driven Fuzz � Database Fuzz
Types of Fuzzing Based on type of Fuzzer: � Tool oriented Fuzzing � Manual Fuzzing Based on Attack Targets: � Application fuzzing. � Protocol fuzzing. � File-format fuzzing. � Operating System fuzzing.
Fuzzing Explained � Simple fuzz approach using a pseudo random number generator as input. � Validation of fuzz attempts to assure that the random input is reasonable. � A combined approach using valid test data and invalid random input interjection.
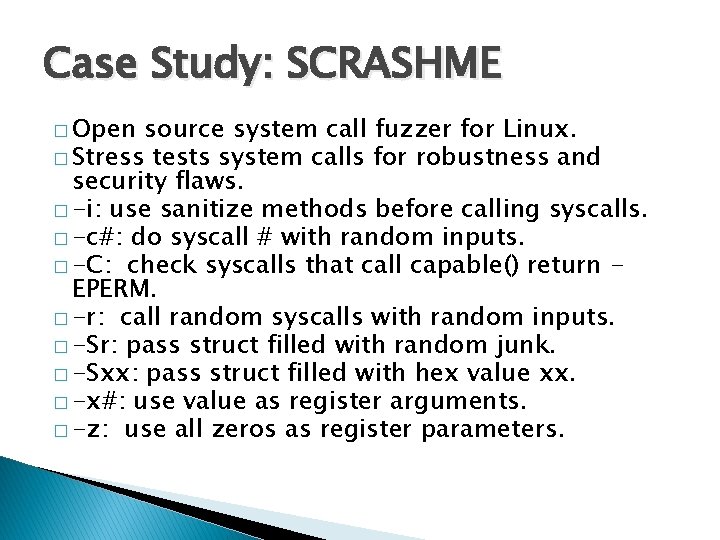
Case Study: SCRASHME � Open source system call fuzzer for Linux. � Stress tests system calls for robustness and security flaws. � -i: use sanitize methods before calling syscalls. � -c#: do syscall # with random inputs. � -C: check syscalls that call capable() return EPERM. � -r: call random syscalls with random inputs. � -Sr: pass struct filled with random junk. � -Sxx: pass struct filled with hex value xx. � -x#: use value as register arguments. � -z: use all zeros as register parameters.
SCRASHME: Changes � Support for new syscall #333 in Linux Kernel 2. 6. 27. 7 i. e. sys_getdomainname(). � Sanitize method for Local root exploit for vmsplice() syscall.
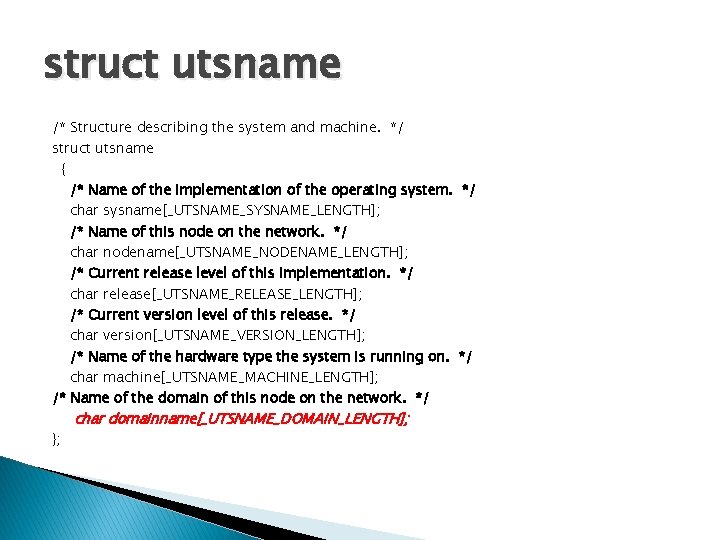
struct utsname /* Structure describing the system and machine. */ struct utsname { /* Name of the implementation of the operating system. */ char sysname[_UTSNAME_SYSNAME_LENGTH]; /* Name of this node on the network. */ char nodename[_UTSNAME_NODENAME_LENGTH]; /* Current release level of this implementation. */ char release[_UTSNAME_RELEASE_LENGTH]; /* Current version level of this release. */ char version[_UTSNAME_VERSION_LENGTH]; /* Name of the hardware type the system is running on. */ char machine[_UTSNAME_MACHINE_LENGTH]; /* Name of the domain of this node on the network. */ }; char domainname[_UTSNAME_DOMAIN_LENGTH];
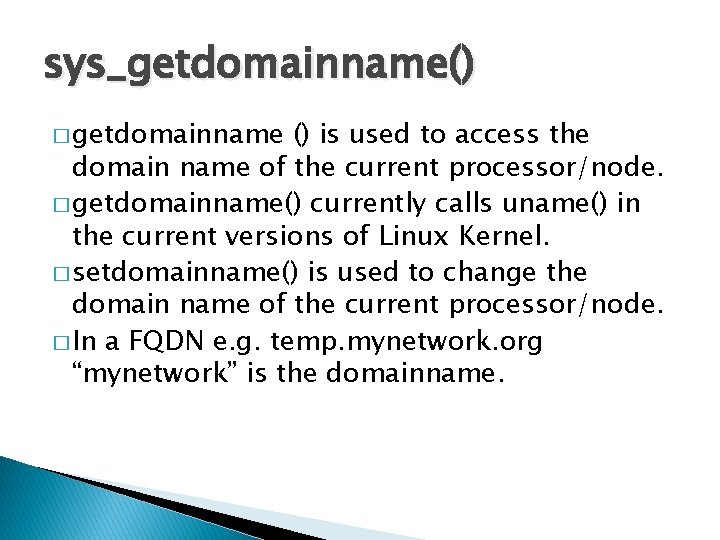
sys_getdomainname() � getdomainname () is used to access the domain name of the current processor/node. � getdomainname() currently calls uname() in the current versions of Linux Kernel. � setdomainname() is used to change the domain name of the current processor/node. � In a FQDN e. g. temp. mynetwork. org “mynetwork” is the domainname.
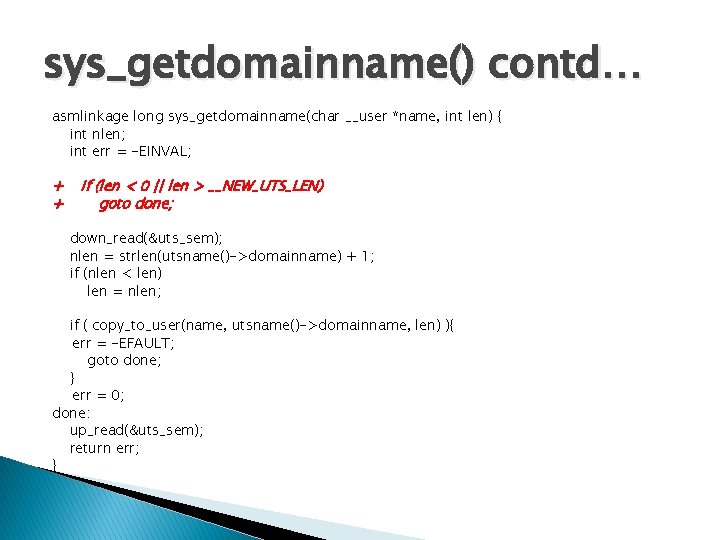
sys_getdomainname() contd… asmlinkage long sys_getdomainname(char __user *name, int len) { int nlen; int err = -EINVAL; + + if (len < 0 || len > __NEW_UTS_LEN) goto done; down_read(&uts_sem); nlen = strlen(utsname()->domainname) + 1; if (nlen < len) len = nlen; if ( copy_to_user(name, utsname()->domainname, len) ){ err = -EFAULT; goto done; } err = 0; done: up_read(&uts_sem); return err; }
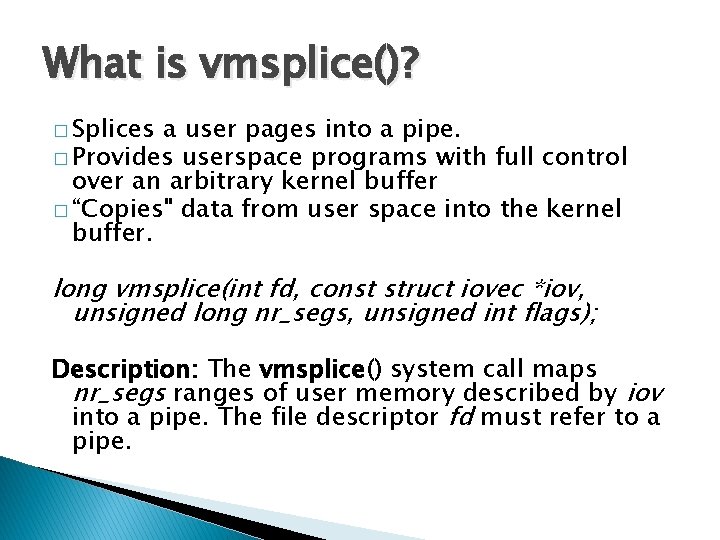
What is vmsplice()? � Splices a user pages into a pipe. � Provides userspace programs with full control over an arbitrary kernel buffer � “Copies" data from user space into the kernel buffer. long vmsplice(int fd, const struct iovec *iov, unsigned long nr_segs, unsigned int flags); Description: The vmsplice() system call maps nr_segs ranges of user memory described by iov into a pipe. The file descriptor fd must refer to a pipe.
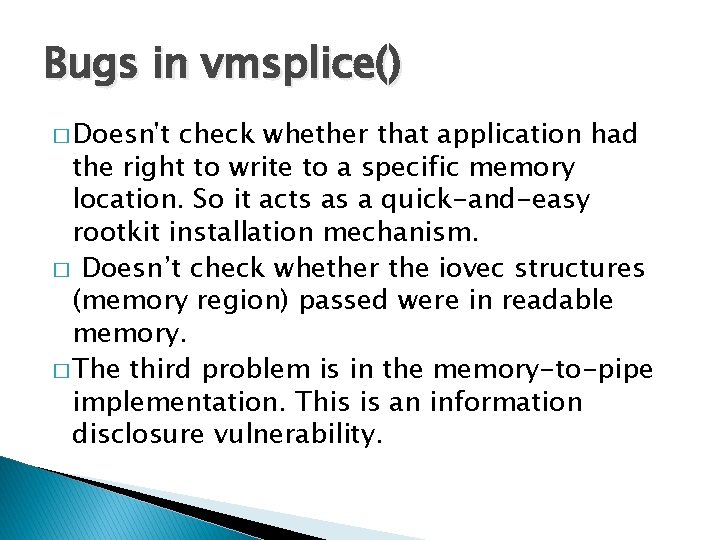
Bugs in vmsplice() � Doesn't check whether that application had the right to write to a specific memory location. So it acts as a quick-and-easy rootkit installation mechanism. � Doesn’t check whether the iovec structures (memory region) passed were in readable memory. � The third problem is in the memory-to-pipe implementation. This is an information disclosure vulnerability.
vmsplice() : Local Root Exploit � Enables non-root user to become root � Doesn’t need specific hardware Available at: � http: //www. milw 0 rm. com/exploits/5092
Conclusion � Allows detection of critical security vulnerabilities in short time periods for various applications. � Simple, efficient and can be automated. � Considerable speed up of the whole process of security vulnerabilities detection. � Downside: Not the final solution for detection of all security vulnerabilities that exist in an application.
Questions ?
- Slides: 16