Use of Fieldbus in safety related systems an
Use of Fieldbus in safety related systems, an evaluation study of World. FIP according to proven-in-use concept of IEC 61508 Jean Pierre Froidevaux World. FIP Olivier Nick ALSTOM Technology Michel Suzan Bureau Veritas
Introduction to risks approach Any production operation has inherent risks in case of malfunctions l These risks may cause damages to the operators, environment, assets l Operations cannot be run if risks are unacceptable: l – Risks should be evaluated – If risks are not acceptable, they should be reduced by reliable means such as E/E/PE PN/IR/01. 0003 page 2 ©Copyright 2001 World. FIP
IEC 61508 standard PN/IR/01. 0003 page 3 Risk Reduction Concept ©Copyright 2001 World. FIP
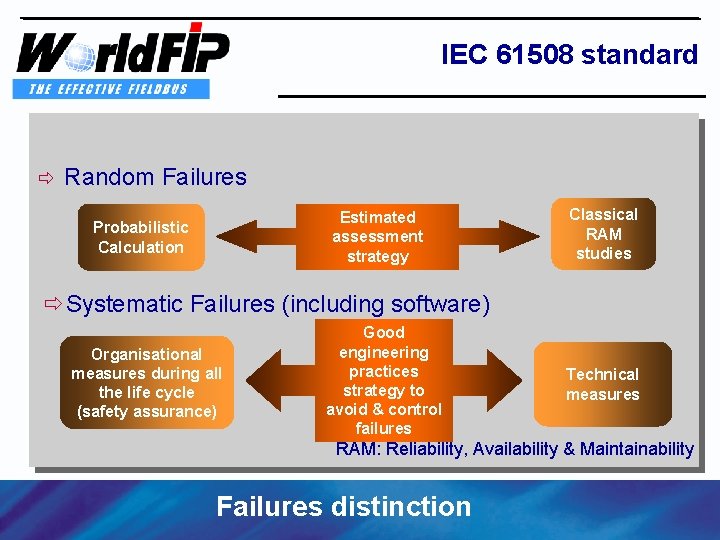
IEC 61508 standard ð Random Failures Estimated assessment strategy Probabilistic Calculation Classical RAM studies ðSystematic Failures (including software) Organisational measures during all the life cycle (safety assurance) Good engineering practices strategy to avoid & control failures Technical measures RAM: Reliability, Availability & Maintainability PN/IR/01. 0003 page 4 Failures distinction ©Copyright 2001 World. FIP
Objectives of a safety function To provide a safety related function with a given level of integrity to ensure certain risk reduction l Applicable to a function or a system, not to component l Assessments are done on application basis l A safety related function has to protect persons and environment from an identified hazard l PN/IR/01. 0003 page 5 Reliable risk reduction system ©Copyright 2001 World. FIP
Mission of a safety function Keep the process under control within its operating limits l To achieve this the safety function can either: l – develop counter actions to avoid crossing a constraint (ex: anti-surge) – stop the process either gracefully or in emergency l Actions should be defined in accordance to the gravity of consequences PN/IR/01. 0003 page 6 ©Copyright 2001 World. FIP
What is the role of communication ? Communication is a set of hardware and software allowing information to be transferred between two or more devices l It should not propagate or create a fault that may induce a dangerous situation for the process under control: l – Data corruption should be detected – time constraints should be enforced for real time data – delivery should be ordered to avoid out of sequence PN/IR/01. 0003 page 7 ©Copyright 2001 World. FIP
Behaviour on faults should be known l Consequences may be either: l – A communication fault triggers a safety action and stop the process – The communication is robust to faults and permit to continue operation even in presence of faults l the criteria is the criticity analysis of fault consequences and the need to avoid non justified safety actions (credibility) PN/IR/01. 0003 page 8 Are a stopped systems the only safe systems? ? ? ©Copyright 2001 World. FIP
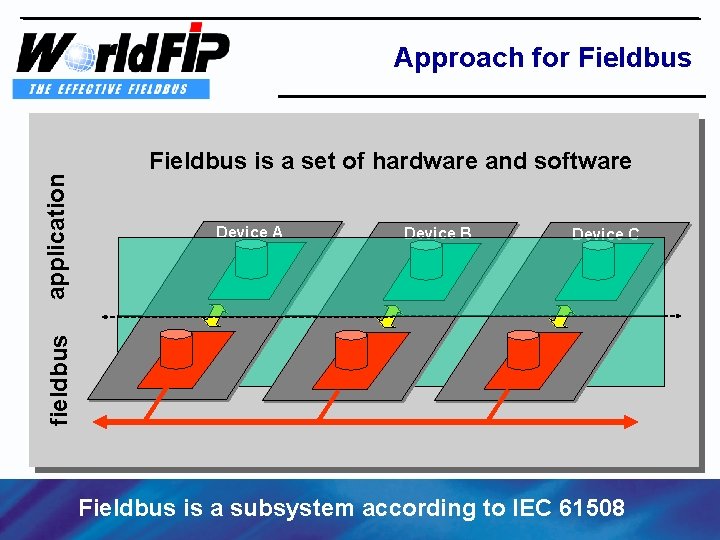
Approach for Fieldbus application Fieldbus is a set of hardware and software Device B Device C fieldbus Device A Fieldbus is a subsystem according to IEC 61508 PN/IR/01. 0003 page 9 ©Copyright 2001 World. FIP
Fieldbus approach l Trusted approach – The Fieldbus subsystem should comply with the provisions of 61508: • Proven in use concept • Fully designed for safety purpose l Non trusted approach – The integrity of a transmitted information is ensured by external means (additional coding) PN/IR/01. 0003 page 10 ©Copyright 2001 World. FIP
Why trusted approach l Conserve initial properties – real time features – robustness to faults – high throughput Permit use of standard hardware and software l facilitate system engineering l use high integrity control across network for better process safe operation l PN/IR/01. 0003 page 11 Fieldbus native integrity ©Copyright 2001 World. FIP
Open communication is needed To ensure high integrity of a system over time efficient diagnostic and maintenance should implemented l On-line maintenance needs communication with l end devices l These exchanges (event driven) should be isolated from safe exchanges PN/IR/01. 0003 page 12 Fieldbus should prove the quality of isolation ©Copyright 2001 World. FIP
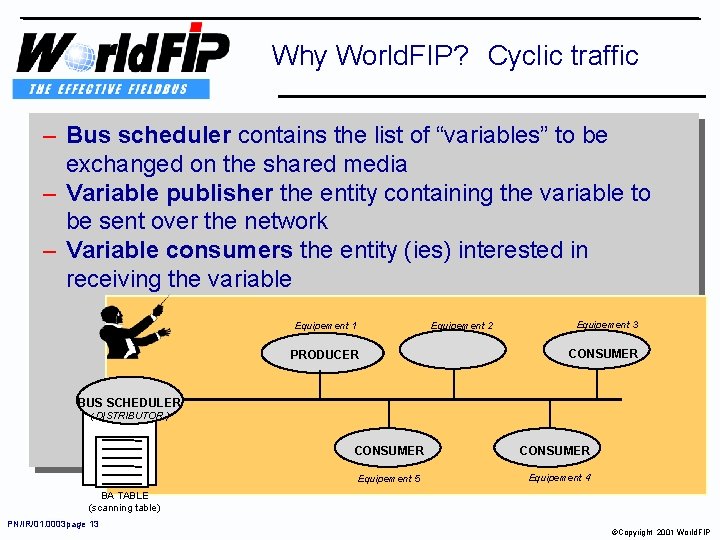
Why World. FIP? Cyclic traffic – Bus scheduler contains the list of “variables” to be exchanged on the shared media – Variable publisher the entity containing the variable to be sent over the network – Variable consumers the entity (ies) interested in receiving the variable Equipement 2 Equipement 1 PRODUCER Equipement 3 CONSUMER BUS SCHEDULER ( DISTRIBUTOR ) CONSUMER Equipement 5 CONSUMER Equipement 4 BA TABLE (scanning table) PN/IR/01. 0003 page 13 ©Copyright 2001 World. FIP
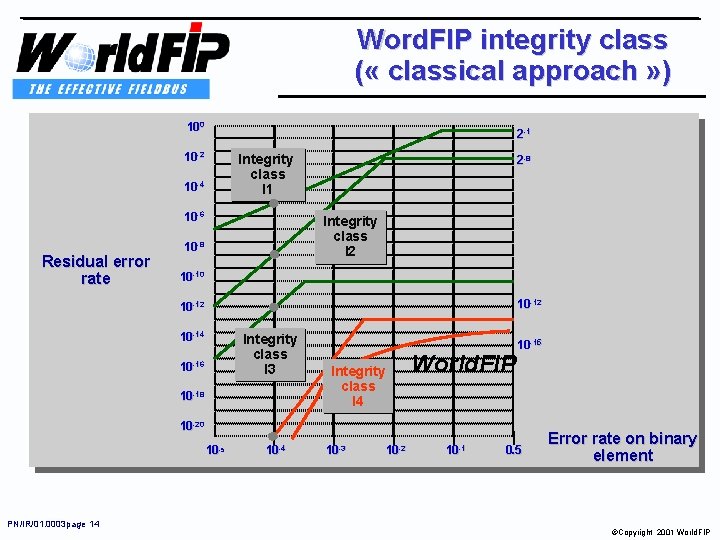
Word. FIP integrity class ( « classical approach » ) 100 2 -1 10 -2 Integrity class I 1 10 -4 10 -6 Residual error rate 2 -8 Integrity class I 2 10 -8 10 -10 10 -12 10 -14 Integrity class I 3 10 -16 10 -18 Integrity class I 4 World. FIP 10 -15 10 -20 10 -5 PN/IR/01. 0003 page 14 10 -3 10 -2 10 -1 0. 5 Error rate on binary element ©Copyright 2001 World. FIP
Generic method issues l l l Use of an estimated strategy assessment Reliability data can have a high level of non confidence Difficulty to quantify the safe failure fraction Difficulty to quantify common cause failure A fair method for a complete new design Mandatory conditions : stringent estimated probabilistic calculation strategy from the beginning of the design Without proven data the calculation must be conservative PN/IR/01. 0003 page 15 ©Copyright 2001 World. FIP
Field experience exploitation Use field experience from different applications to prove that the system will work in safe operation according to the specified risk reduction target. l Avoid the extensive re-validation for each new application (use similar experience). l Mandatory condition : having a rigorous record of experience and a stringent contextual risk analysis l PN/IR/01. 0003 page 16 Proven in use concept ©Copyright 2001 World. FIP
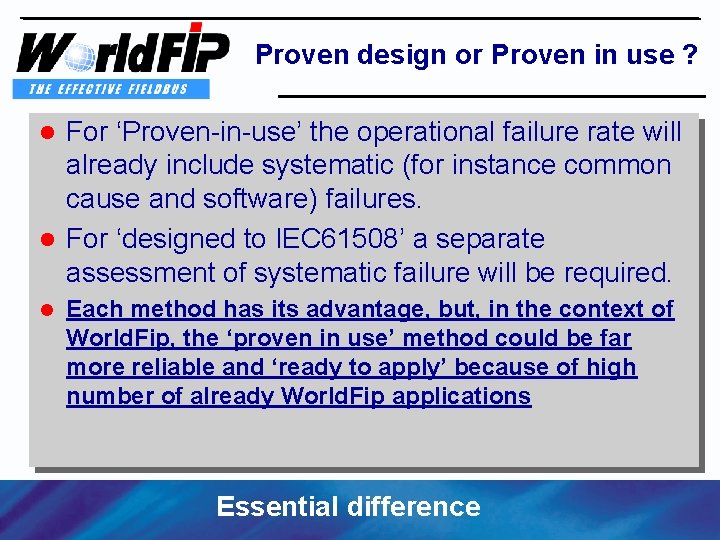
Proven design or Proven in use ? For ‘Proven-in-use’ the operational failure rate will already include systematic (for instance common cause and software) failures. l For ‘designed to IEC 61508’ a separate assessment of systematic failure will be required. l l Each method has its advantage, but, in the context of World. Fip, the ‘proven in use’ method could be far more reliable and ‘ready to apply’ because of high number of already World. Fip applications PN/IR/01. 0003 page 17 Essential difference ©Copyright 2001 World. FIP
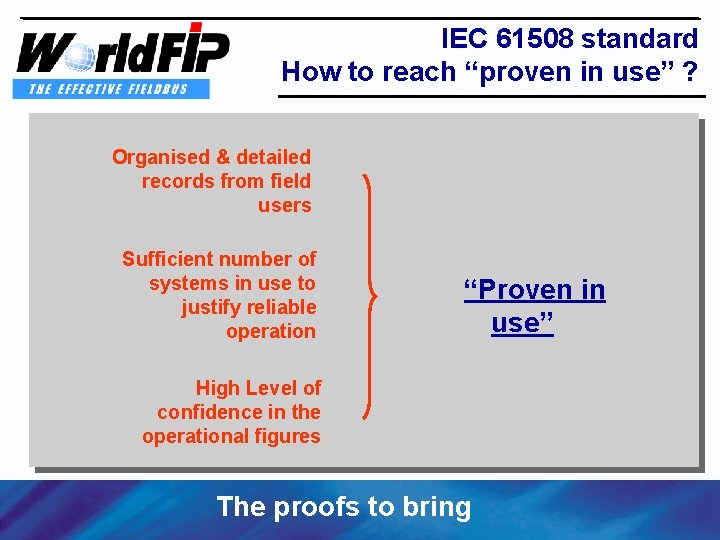
IEC 61508 standard How to reach “proven in use” ? Organised & detailed records from field users Sufficient number of systems in use to justify reliable operation “Proven in use” High Level of confidence in the operational figures PN/IR/01. 0003 page 18 The proofs to bring ©Copyright 2001 World. FIP
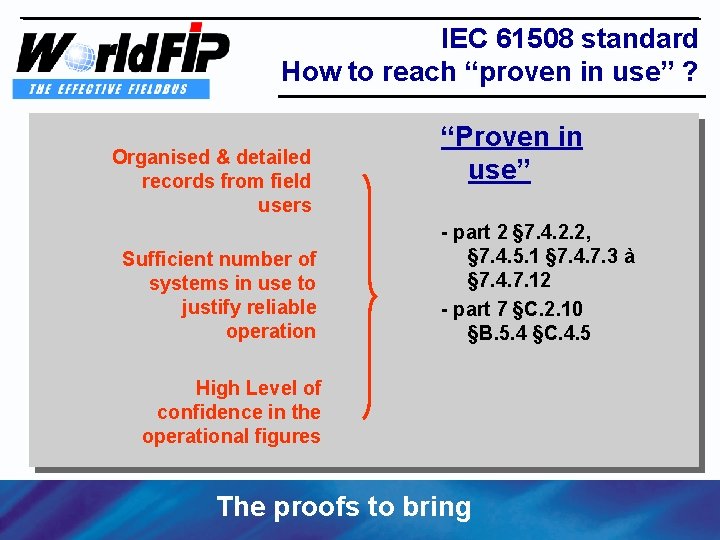
IEC 61508 standard How to reach “proven in use” ? Organised & detailed records from field users Sufficient number of systems in use to justify reliable operation “Proven in use” - part 2 § 7. 4. 2. 2, § 7. 4. 5. 1 § 7. 4. 7. 3 à § 7. 4. 7. 12 - part 7 §C. 2. 10 §B. 5. 4 §C. 4. 5 High Level of confidence in the operational figures PN/IR/01. 0003 page 19 The proofs to bring ©Copyright 2001 World. FIP
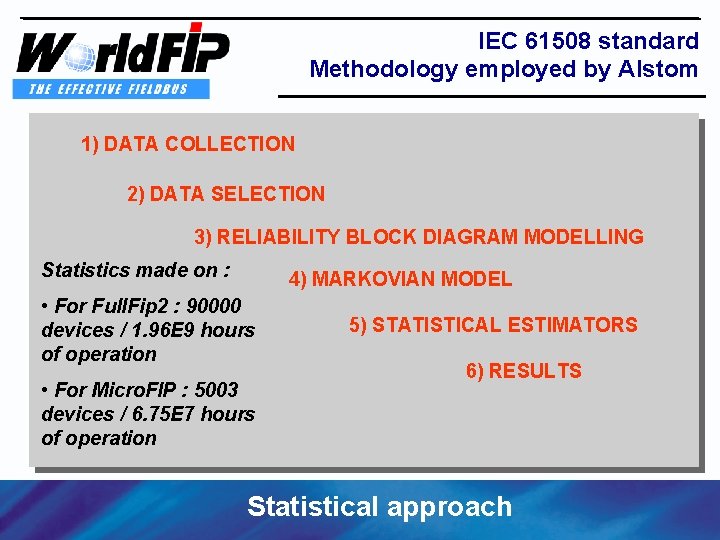
IEC 61508 standard Methodology employed by Alstom 1) DATA COLLECTION 2) DATA SELECTION 3) RELIABILITY BLOCK DIAGRAM MODELLING Statistics made on : 4) MARKOVIAN MODEL • For Full. Fip 2 : 90000 devices / 1. 96 E 9 hours of operation • For Micro. FIP : 5003 devices / 6. 75 E 7 hours of operation PN/IR/01. 0003 page 20 5) STATISTICAL ESTIMATORS 6) RESULTS Statistical approach ©Copyright 2001 World. FIP
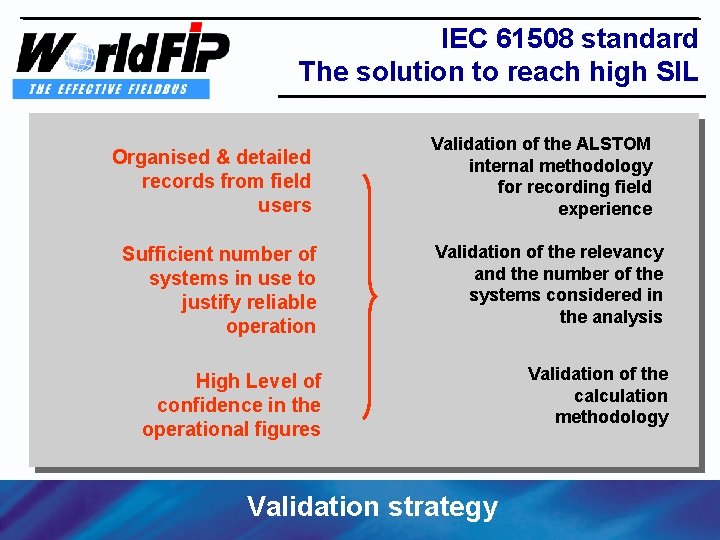
IEC 61508 standard The solution to reach high SIL Organised & detailed records from field users PN/IR/01. 0003 page 21 Validation of the ALSTOM internal methodology for recording field experience Sufficient number of systems in use to justify reliable operation Validation of the relevancy and the number of the systems considered in the analysis High Level of confidence in the operational figures Validation of the calculation methodology Validation strategy ©Copyright 2001 World. FIP
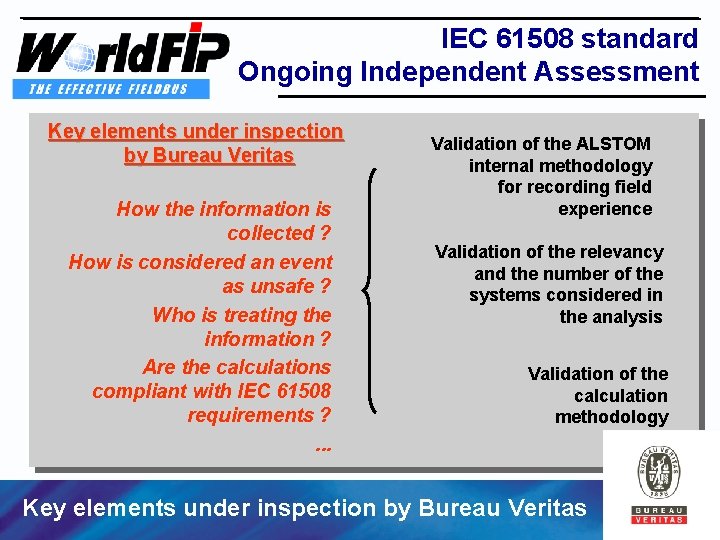
IEC 61508 standard Ongoing Independent Assessment Key elements under inspection by Bureau Veritas How the information is collected ? How is considered an event as unsafe ? Who is treating the information ? Are the calculations compliant with IEC 61508 requirements ? . . . Validation of the ALSTOM internal methodology for recording field experience Validation of the relevancy and the number of the systems considered in the analysis Validation of the calculation methodology Key elements under inspection by Bureau Veritas PN/IR/01. 0003 page 22 ©Copyright 2001 World. FIP
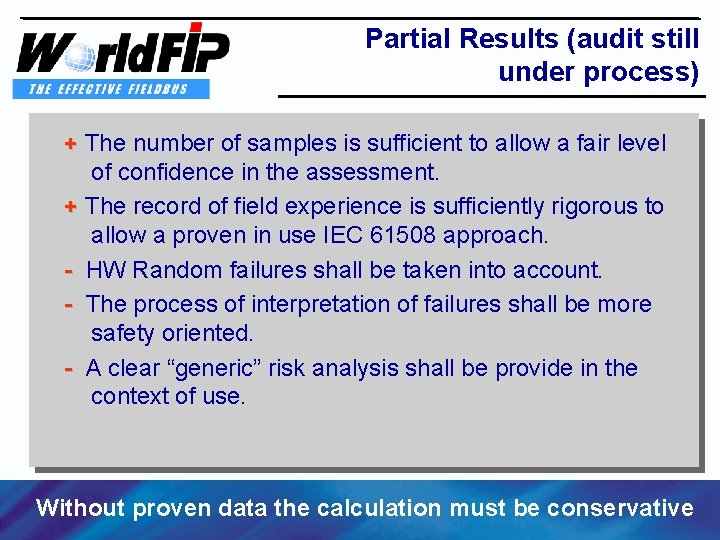
Partial Results (audit still under process) + The number of samples is sufficient to allow a fair level of confidence in the assessment. + The record of field experience is sufficiently rigorous to + allow a proven in use IEC 61508 approach. - HW Random failures shall be taken into account. - - The process of interpretation of failures shall be more - safety oriented. - A - clear “generic” risk analysis shall be provide in the context of use. Without proven data the calculation must be conservative PN/IR/01. 0003 page 23 ©Copyright 2001 World. FIP
Limits of this approach Need of a very large installed base. Need of a very stringent risk analysis in compliance with the context of use (how to adapt the risk analysis to the context and be sure the risk is still mitigated concept of generic risk analysis). Need of a close access to failure data. Need of an efficient (independence and objective recording and assessment, human factors…) Data Recording Process. PN/IR/01. 0003 page 24 The total control of the field experience ©Copyright 2001 World. FIP
Achievements Bring the evidence that World. Fip can be used in safety applications l No specific direct overcost linked to safety (it was proven in use) l If necessary adapt the field experience methodology (only quality improvement) l If necessary adapt user maintenance procedures to allow fair and relevant record of experience l A simple and operational approach of functional safety PN/IR/01. 0003 page 25 ©Copyright 2001 World. FIP
- Slides: 25