Unstructured P 2 P networks by example Gnutella
Unstructured P 2 P networks by example: Gnutella 0. 4, Gnutella 0. 6 张旭彤 杨蕊鸿 马骕 林晔
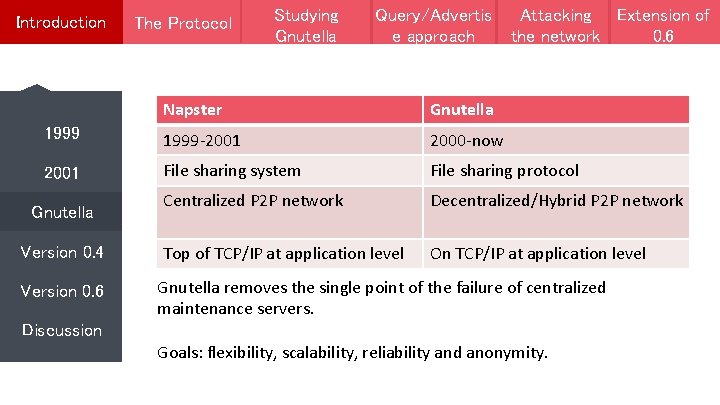
Introduction The Protocol Studying Gnutella Query/Advertis e approach Attacking Extension of the network 0. 6 Napster Gnutella 1999 -2001 2000 -now 2001 File sharing system File sharing protocol Centralized P 2 P network Decentralized/Hybrid P 2 P network Top of TCP/IP at application level On TCP/IP at application level Gnutella Version 0. 4 Version 0. 6 Gnutella removes the single point of the failure of centralized maintenance servers. Discussion Goals: flexibility, scalability, reliability and anonymity.
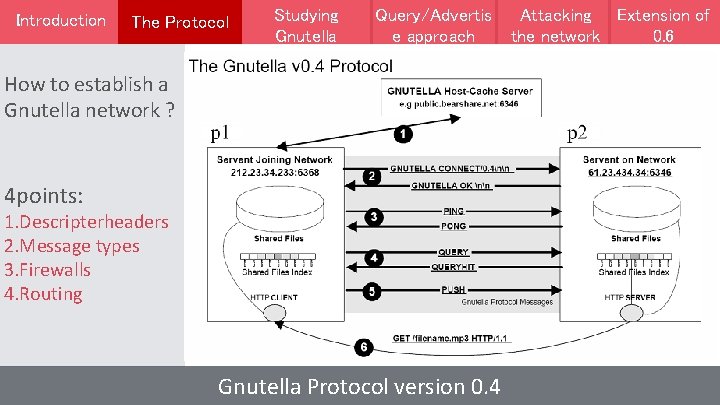
Introduction The Protocol Studying Gnutella Query/Advertis e approach How to establish a Gnutella network ? 4 points: 1. Descripterheaders 2. Message types 3. Firewalls 4. Routing Gnutella Protocol version 0. 4 Attacking Extension of the network 0. 6
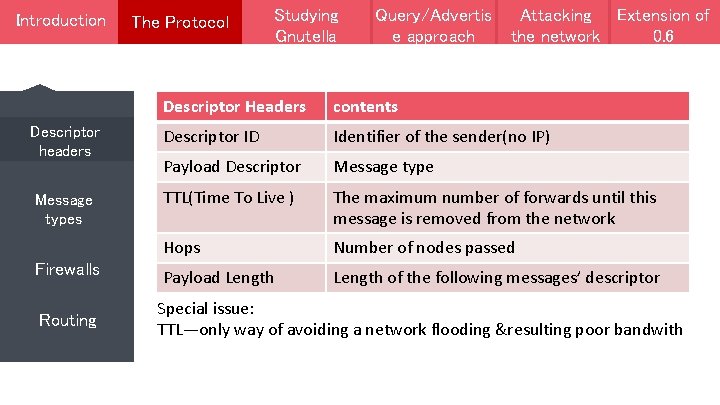
Introduction Descriptor headers Message types Firewalls Routing The Protocol Studying Gnutella Query/Advertis e approach Attacking Extension of the network 0. 6 Descriptor Headers contents Descriptor ID Identifier of the sender(no IP) Payload Descriptor Message type TTL(Time To Live ) The maximum number of forwards until this message is removed from the network Hops Number of nodes passed Payload Length of the following messages’ descriptor Special issue: TTL—only way of avoiding a network flooding &resulting poor bandwith
Introduction Descriptor headers Message types Firewalls Routing The Protocol Studying Gnutella Query/Advertis e approach Attacking Extension of the network 0. 6 Finding friends: PING——search for other servents PONG——respond other’s call Resource retrieval: QUERY——search for a certain data QUERY HIT——respond to QUERY Pushing data: PUSH——purpose in case of firewalled servents
Introduction Descriptor headers Message types Firewalls Routing The Protocol Studying Gnutella Query/Advertis e approach Attacking Extension of the network 0. 6 Problem: the servent wanna share a resource, but situated behind a firewall. Solution: providing a chance for requesting client to push data
Introduction Descriptor headers The Protocol Studying Gnutella Query/Advertis e approach Attacking Extension of the network 0. 6 PING & QUERY broadcast message flooded to every node until TTL is outline Message types PONG & QUERY HIT : have the same Descriptor_ID as PING &QUERY message. Firewalls PONG and Query Hit messages are routed at the same path like the incoming PING and Query messages. Routing
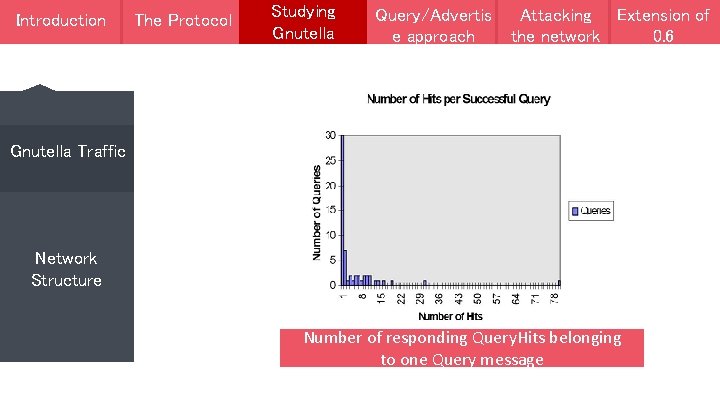
Introduction The Protocol Studying Gnutella Query/Advertis e approach Attacking Extension of the network 0. 6 Gnutella Traffic Network Structure Number Queries of with responding Query. Hits message compared belonging Gnutella network traffic in protocol version 0. 4 to one to Query all queries message
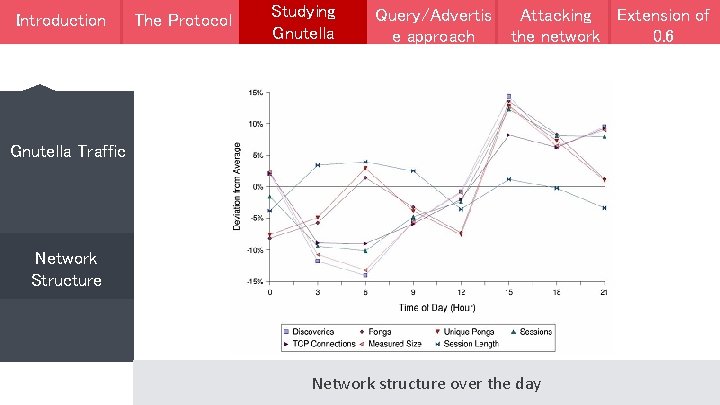
Introduction The Protocol Studying Gnutella Query/Advertis e approach Attacking Extension of the network 0. 6 Gnutella Traffic Network Structure Network structure over the day
Introduction The Protocol Studying Gnutella Query/Adverti se approach Attacking the network Flaws of the Gnutella network Using Publish/Subscribe services . . . in the end Query/Advertise approach Extension of 0. 6
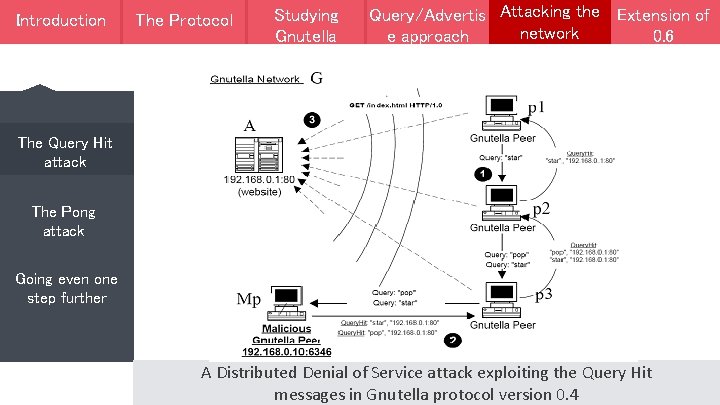
Introduction The Protocol Protpcol Studying Gnutella Query/Adverti Attacking the Extension of Attacking Query/Advertis se approach network the network e approach 0. 6 The Query Hit attack The Pong attack Going even one step further A Distributed Denial of Service attack exploiting the Query Hit messages in Gnutella protocol version 0. 4
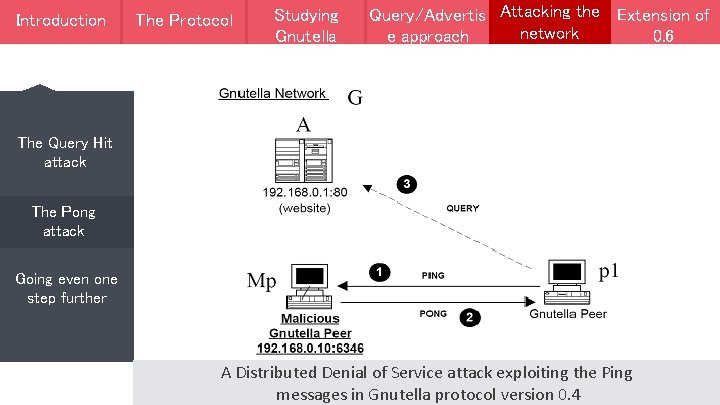
Introduction The Protocol Protpcol Studying Gnutella Query/Adverti Attacking the Extension of Attacking Query/Advertis se approach network the network e approach 0. 6 The Query Hit attack The Pong attack Going even one step further A Distributed Denial of Service attack exploiting the Ping messages in Gnutella protocol version 0. 4
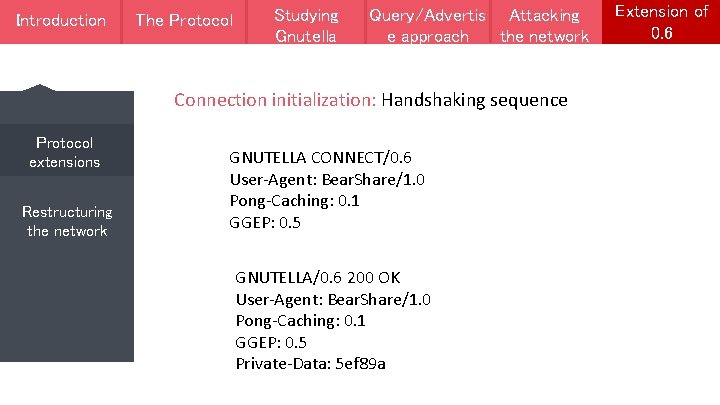
Introduction The Protocol Protpcol Studying Gnutella Query/Adverti Attacking Query/Advertis se approach thenetwork e approach Connection initialization: Handshaking sequence Protocol extensions Restructuring the network GNUTELLA CONNECT/0. 6 User-Agent: Bear. Share/1. 0 Pong-Caching: 0. 1 GGEP: 0. 5 GNUTELLA/0. 6 200 OK User-Agent: Bear. Share/1. 0 Pong-Caching: 0. 1 GGEP: 0. 5 Private-Data: 5 ef 89 a Extension of 0. 6
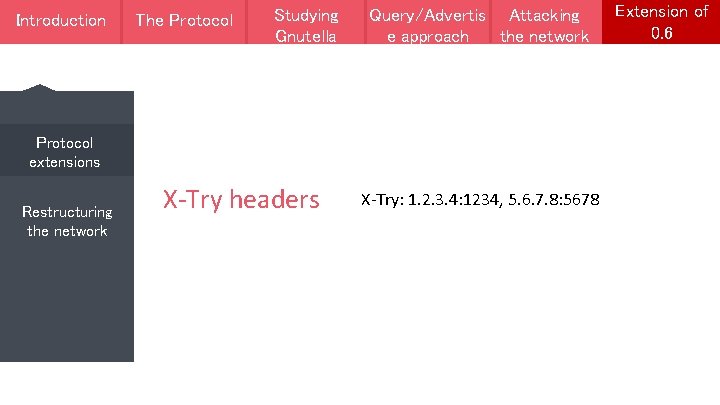
Introduction The Protocol Protpcol Studying Gnutella Query/Adverti Attacking Query/Advertis se approach thenetwork e approach Protocol extensions Restructuring the network X-Try headers X-Try: 1. 2. 3. 4: 1234, 5. 6. 7. 8: 5678 Extension of 0. 6
Introduction The Protocol Protpcol Studying Gnutella Query/Adverti Attacking Query/Advertis se approach thenetwork e approach Extension of 0. 6 Protocol extensions Restructuring the network Ultrapeer Query routing protocol

Thank You
- Slides: 16