Unleashing the Power of Digital Goods Enabling New
Unleashing the Power of Digital Goods Enabling New Business Models for the Music Industry Dimitri do B. De. Figueiredo Sept 16, 2003
Motivation • CD sales are down over 30% from 1999; music industry claims it is due to piracy. • 261 people sued by RIAA last week for copyright infringement. • It is estimated over 40 million Americans have illegally downloaded songs. All due to Technological Advances!

Facts about the Music Industry • Same model as 40 years ago. -despite very large number of P 2 P users • 5 firms: BMG, EMI, Sony, Universal and Warner have 80% of global market • Very uneven distribution of Sales and Wealth. • Very inefficient: 25 k/30 k new releases sold less than 1000 copies (2002). • Artists get less than 20% of revenues
Motivation To provide the technological tools to enable business models that: – work with the Internet; – do not require Digital Rights Management, Watermarking or other copyright enforcement technologies; – give artists a larger slice of the cake; – provide better diversity.
Outline • Related work & Economic considerations • Non-Traditional business models: • Street Performer Protocol • Distributed Patronage • Mechanisms required and in place • Magic. Thanks • Future Research Directions
The Problem… • Information goods have become: – Non-rival – Non-excludable Information goods can be analyzed as Public Goods! • Underproduction × Underconsumption
Related Work • Social Welfare Considerations. • Private Provision of Public Goods CAN be done efficiently [Bagnoli 92]. • Incentive: copies have lower values than originals [Mussa 78]. – (Musical Twist: other sources of income)
![Related Work • Social welfare [Belleflamme 02][Yoon 02] • Profit Maximization under excludability [Varian Related Work • Social welfare [Belleflamme 02][Yoon 02] • Profit Maximization under excludability [Varian](http://slidetodoc.com/presentation_image/f7e4a10619fd68434259acb8a642697c/image-8.jpg)
Related Work • Social welfare [Belleflamme 02][Yoon 02] • Profit Maximization under excludability [Varian 94] • Competition Strategies: Label × P 2 P [Duchene 01] • Concentration of Wealth [Adler 85]
Non-Traditional Business Models • Who is going to fund it? – 3 rd party sponsors – consumers • criterion: non-excludability – Efficiently avoids underconsumption 1. Street Performer Protocol 2. Distributed Patronage
The Street Performer Protocol • Description: – Producer announces goods, price & deadline. – Patrons contribute any amount. – If target price not reached, money is returned. – If target price is reached, good is produced and everyone (contributors or otherwise) can use it.
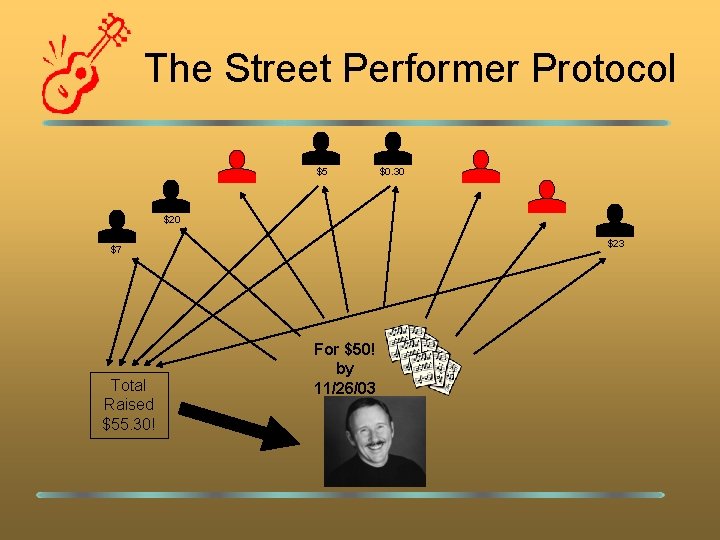
The Street Performer Protocol $5 $0. 30 $23 $7 Total Raised $55. 30! For $50! by 11/26/03
The Street Performer Protocol • Advantages: – Potentially huge profit! (due to price discrimination) – Efficient under complete information (no under production/consumption trade-off) – No copyright enforcement costs • Disadvantages: – Producer must estimate total willingness to pay – Consumers pay BEFORE getting the goods (investors) – Need for credible threat if target not reached and certainty of production otherwise – It is NOT rational to contribute. It is better to free ride.
![The Street Performer Protocol • Variations: – Rational SPP [Harisson] – Wall SPP [Rasch The Street Performer Protocol • Variations: – Rational SPP [Harisson] – Wall SPP [Rasch](http://slidetodoc.com/presentation_image/f7e4a10619fd68434259acb8a642697c/image-13.jpg)
The Street Performer Protocol • Variations: – Rational SPP [Harisson] – Wall SPP [Rasch 01] – Others: • Timed variation • Producer commits to secret amount. • Etc. • Blender success story [Neus 02]
Distributed Patronage • Similar to Shareware • Contributions for other reasons, altruism. • Advantages: – Consumption efficient – No copyright enforcement costs – Producer does not need to have a good estimate of the value of goods. – Contributors provide money AFTER using goods. • Disadvantages: – Agents bound to provide less money (musical twist helps us here: extra publicity, middlemen inefficiency)
Mechanisms • Can we use the non-traditional business models? Not Really. • What is required? At least: Distribution, promotion, payment systems. • No clear-cut solutions, e. g. : – Funding artists directly – Funding artists through songs Promotion gives Record Labels huge bargaining power!
Some P 2 P “Servents” Screenshots of Grokster, Bear. Share and Xolox
Mechanisms for SPP • Public commitment to target amount and date. • Money collection and return. • Credible threat of not releasing good • Making it rational to contribute. – Giving more information to users.
![Mechanisms for Distributed Patronage • Micropayments (if funding through songs) [Micali Rivest 02], [Jarecki Mechanisms for Distributed Patronage • Micropayments (if funding through songs) [Micali Rivest 02], [Jarecki](http://slidetodoc.com/presentation_image/f7e4a10619fd68434259acb8a642697c/image-18.jpg)
Mechanisms for Distributed Patronage • Micropayments (if funding through songs) [Micali Rivest 02], [Jarecki Odlyzko 97], etc. – Requirement: large number of small valued (revocable) donations. • Billboard refinement (public verifiable anonymous aggregation) • Payment Agent
Available Mechanisms • • Peer-to-Peer Networks Creative Commons licenses ID 3 v 2 tags in MP 3 files ISRC Freedb. org, musicbrainz. org Gracenote. com’s “Digital. Top. Ten” Openculture. org Others…
Magic. Thanks • Goal: – Provide link between author and content • shareware – Anyone can find (and maybe transfer funds to) contact address. • Characteristics: – Does not prevent, only detects fraud. – Does not require certifying authority for digital content – Works with present infrastructure: • Time stamping, e-mail certification, Paypal. – Implemented by a client that is similar to a P 2 P client
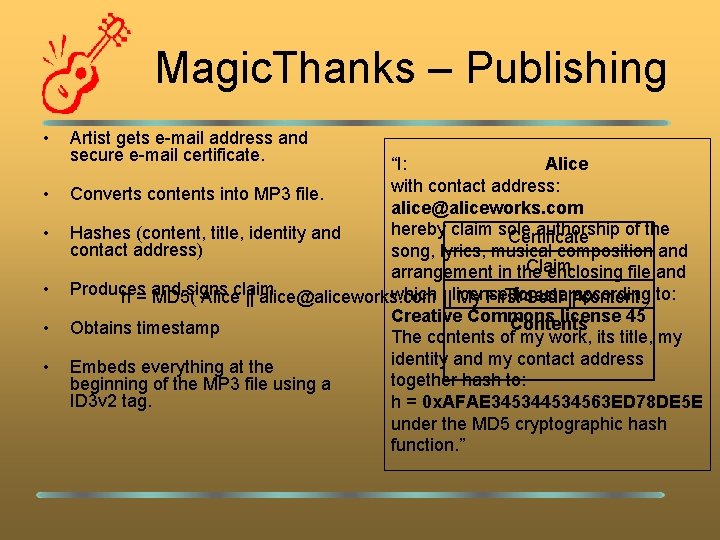
Magic. Thanks – Publishing • • • Artist gets e-mail address and secure e-mail certificate. “I: Alice with contact address: Converts contents into MP 3 file. alice@aliceworks. com hereby claim sole authorship of the Hashes (content, title, identity and Certificate contact address) song, lyrics, musical composition and Claim arrangement in the enclosing file and Produces signs which I||license for. Soul use||according Timestamp h = and MD 5( Aliceclaim || alice@aliceworks. com My First content ) to: Creative Commons license 45 Contents Obtains timestamp The contents of my work, its title, my identity and my contact address Embeds everything at the together hash to: beginning of the MP 3 file using a ID 3 v 2 tag. h = 0 x. AFAE 34534563 ED 78 DE 5 E under the MD 5 cryptographic hash function. ”
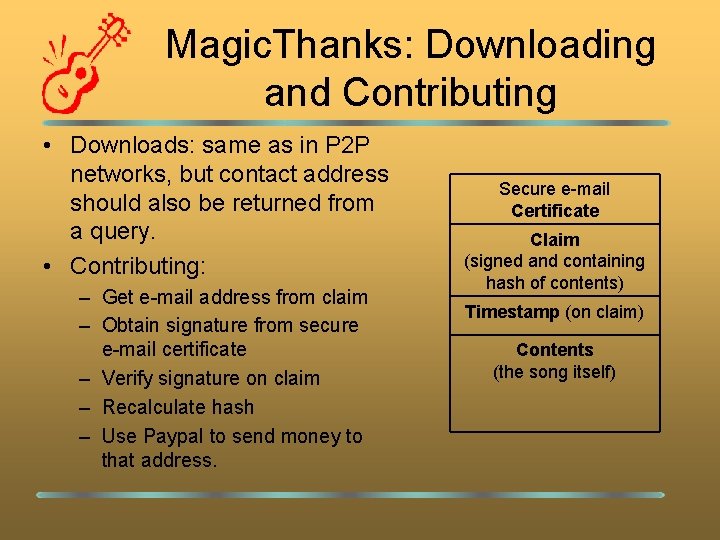
Magic. Thanks: Downloading and Contributing • Downloads: same as in P 2 P networks, but contact address should also be returned from a query. • Contributing: – Get e-mail address from claim – Obtain signature from secure e-mail certificate – Verify signature on claim – Recalculate hash – Use Paypal to send money to that address. Secure e-mail Certificate Claim (signed and containing hash of contents) Timestamp (on claim) Contents (the song itself)
Magic. Thanks: asserting authenticity • Key Idea: Asserting Authenticity implies helping to detect fraud. • • • System is able to differentiate claims based on time Only works on narrow queries, broad queries do not assert authenticity. Defrauder’s profit increases with risk of detection (smaller number of replicas and “hiding title” decreases profit) • Possible criterion for deciding between narrow and broad queries is the number of files with similar names or tags. Probabilistic line of action preferred due to the continuous nature of possible user intent. • • Hash should contain author’s own identity to prevent attacks on the time stamping service. Defrauder cannot claim his secret key has been compromised as a line of defense, if the key is compromised after the timestamp is obtained. Original claim binds author to a specific licensing agreement and prevents future changes.
Magic. Thanks: Limitations • Cannot prevent fraud, only detect it and provide evidence of its occurrence. • Assumes digitally signed fake claims must be produced by defrauder. • Need to tie key that signed claim to “real world identity” (e-mail certification may not be enough) • Hijacking threat of initial deployment • Revocation must be further addressed.
Future Research • Extending RSPP to eliminate Free-riding completely (possible? ) • Implementation of Magic. Thanks enabled P 2 P Client. • Describing Payment System for the Distributed Patronage Model • Proposing a Publicly Verifiable Aggregation System for the Street Performer Protocol • Proposing an Electronic Donations Billboard
Questions? Thank you! available at: http: //www. cs. ucdavis. edu/~defigued
- Slides: 26