Universit Abderrahmane MiraBjaia Facult des Sciences Exactes Dpartement
Université Abderrahmane Mira-Béjaia Faculté des Sciences Exactes -Département d’informatique Thèse de Doctorat en Sciences Sécurité et mécanismes de gestion de confiance dans les Réseaux Mobiles Ad-Hoc Présentée par Mr. Khaled Hamouid Directeur de Thèse Pr. Kamel Adi Université du Québec en Outaouais
Outline 1 Background and motivation 2 Problem statement 3 Our original contributions q q q 4 Background & motivation Robust and adaptive threshold certification Compromise-tolerant certification scheme Efficient certificate-less web-of-trust-based model Conclusion and future work Problem statement 1 st contribution 2 ed contribution 3 ed contribution Conclusion 2
Outline 1 Background and motivation 2 Problem statement 3 Our original contributions q q q 4 Background & motivation Robust and adaptive threshold certification Compromise-tolerant certification scheme Efficient certificate-less web-of-trust model Conclusion and Future Work Problem statement 1 st contribution 2 ed contribution 3 ed contribution Conclusion 3
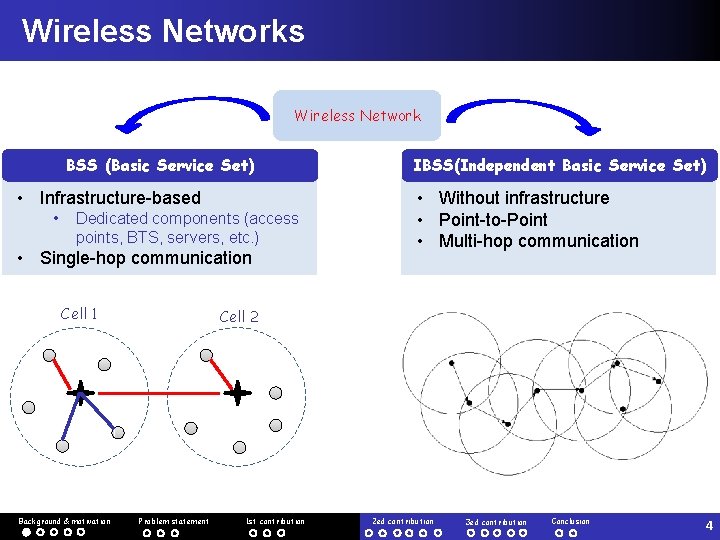
Wireless Networks Wireless Network BSS (Basic Service Set) • Infrastructure-based • Dedicated components (access points, BTS, servers, etc. ) • Single-hop communication Cell 1 Background & motivation IBSS(Independent Basic Service Set) • Without infrastructure • Point-to-Point • Multi-hop communication Cell 2 Problem statement 1 st contribution 2 ed contribution 3 ed contribution Conclusion 4
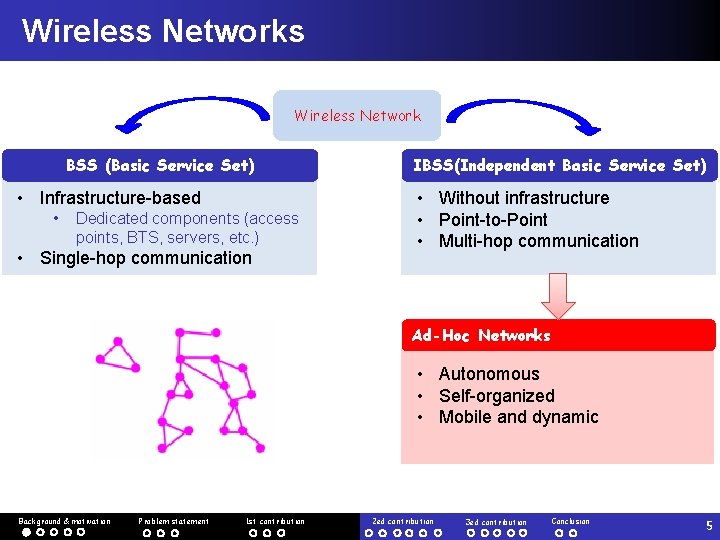
Wireless Networks Wireless Network BSS (Basic Service Set) • Infrastructure-based • Dedicated components (access points, BTS, servers, etc. ) • Single-hop communication IBSS(Independent Basic Service Set) • Without infrastructure • Point-to-Point • Multi-hop communication Ad-Hoc Networks • Autonomous • Self-organized • Mobile and dynamic Background & motivation Problem statement 1 st contribution 2 ed contribution 3 ed contribution Conclusion 5
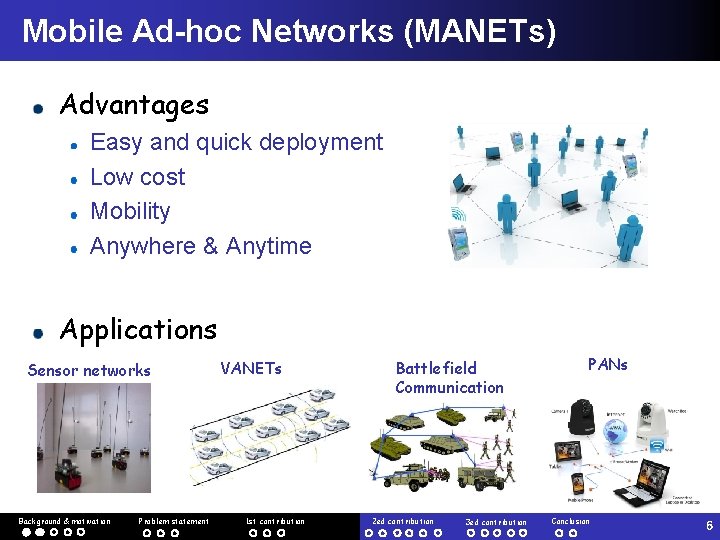
Mobile Ad-hoc Networks (MANETs) Advantages Easy and quick deployment Low cost Mobility Anywhere & Anytime Applications Sensor networks Background & motivation Problem statement VANETs 1 st contribution Battlefield Communication 2 ed contribution 3 ed contribution PANs Conclusion 6
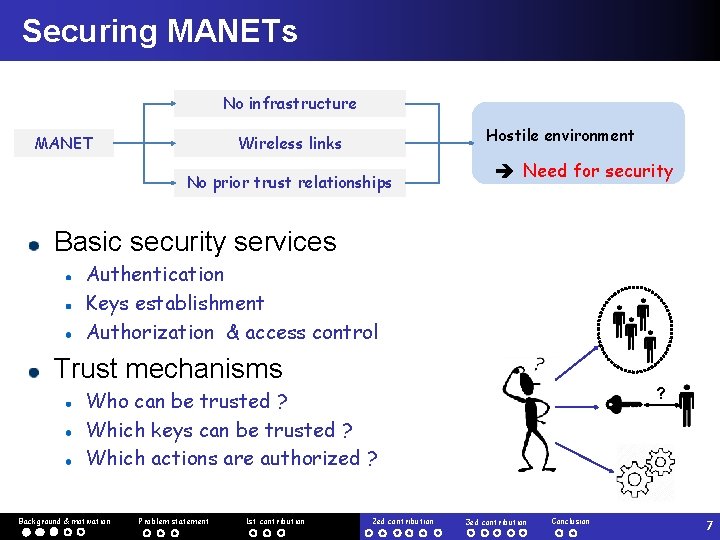
Securing MANETs No infrastructure MANET Hostile environment Wireless links No prior trust relationships Need for security Basic security services Authentication Keys establishment Authorization & access control Trust mechanisms ? Who can be trusted ? Which keys can be trusted ? Which actions are authorized ? Background & motivation Problem statement 1 st contribution 2 ed contribution 3 ed contribution Conclusion 7
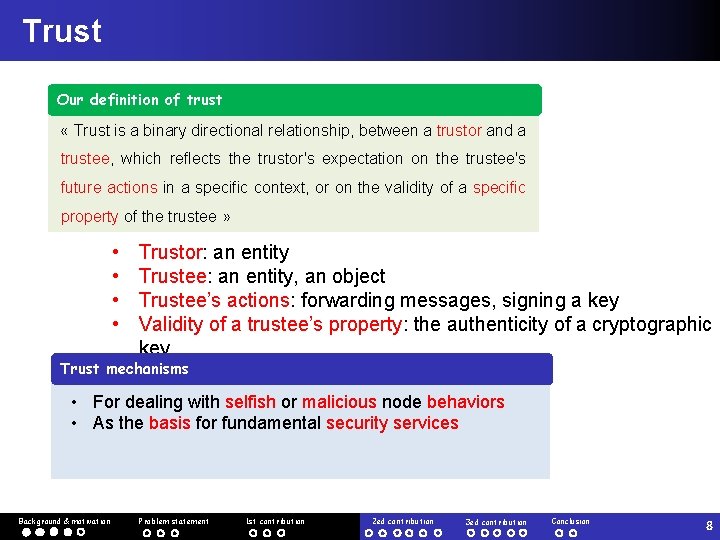
Trust Our definition of trust « Trust is a binary directional relationship, between a trustor and a trustee, which reflects the trustor's expectation on the trustee's future actions in a specific context, or on the validity of a specific property of the trustee » • • Trustor: an entity Trustee: an entity, an object Trustee’s actions: forwarding messages, signing a key Validity of a trustee’s property: the authenticity of a cryptographic key Trust mechanisms • For dealing with selfish or malicious node behaviors • As the basis for fundamental security services Background & motivation Problem statement 1 st contribution 2 ed contribution 3 ed contribution Conclusion 8
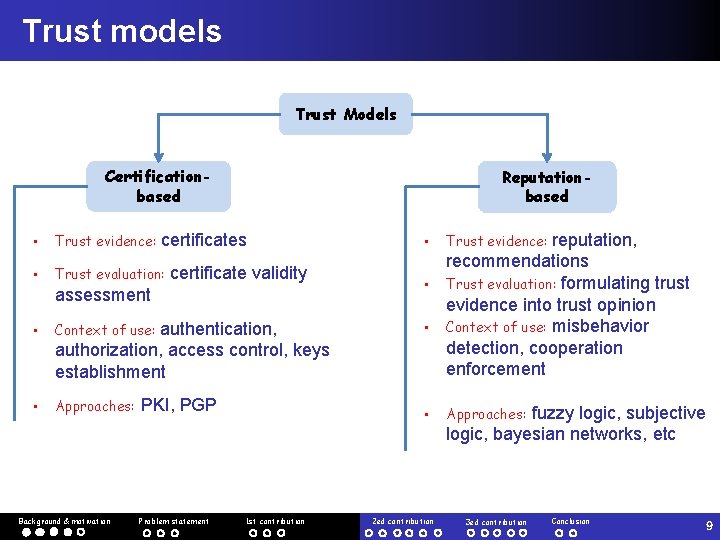
Trust models Trust Models Certificationbased Reputationbased certificates • Context of use: authentication, authorization, access control, keys establishment reputation, recommendations • Trust evaluation: formulating trust evidence into trust opinion • Context of use: misbehavior detection, cooperation enforcement • Approaches: PKI, PGP • • Trust evidence: • Trust evaluation: certificate validity assessment • Trust evidence: Approaches: fuzzy logic, subjective logic, bayesian networks, etc Background & motivation Problem statement 1 st contribution 2 ed contribution 3 ed contribution Conclusion 9
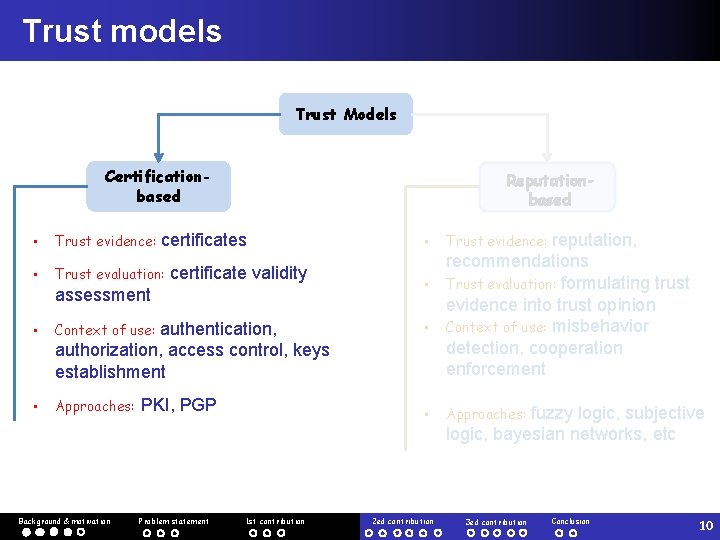
Trust models Trust Models Certificationbased Reputationbased certificates • Context of use: authentication, authorization, access control, keys establishment reputation, recommendations • Trust evaluation: formulating trust evidence into trust opinion • Context of use: misbehavior detection, cooperation enforcement • Approaches: PKI, PGP • • Trust evidence: • Trust evaluation: certificate validity assessment Background & motivation Problem statement 1 st contribution • Trust evidence: Approaches: 2 ed contribution fuzzy logic, subjective logic, bayesian networks, etc 3 ed contribution Conclusion 10
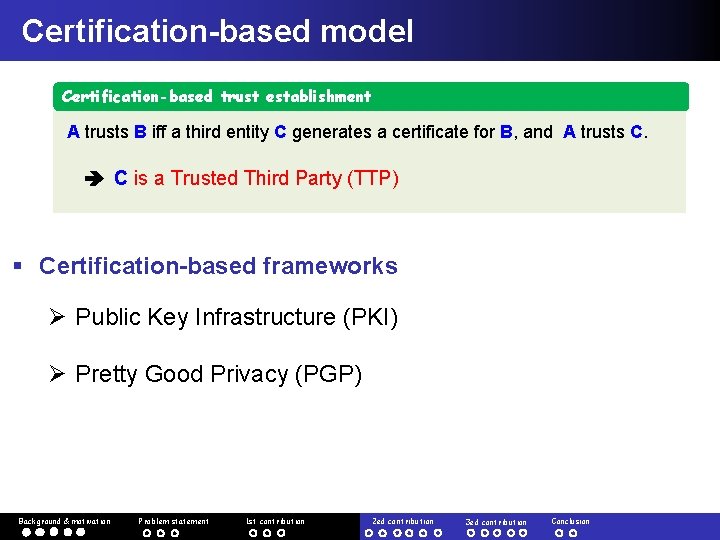
Certification-based model Certification-based trust establishment A trusts B iff a third entity C generates a certificate for B, and A trusts C. C is a Trusted Third Party (TTP) § Certification-based frameworks Ø Public Key Infrastructure (PKI) Ø Pretty Good Privacy (PGP) Background & motivation Problem statement 1 st contribution 2 ed contribution 3 ed contribution Conclusion
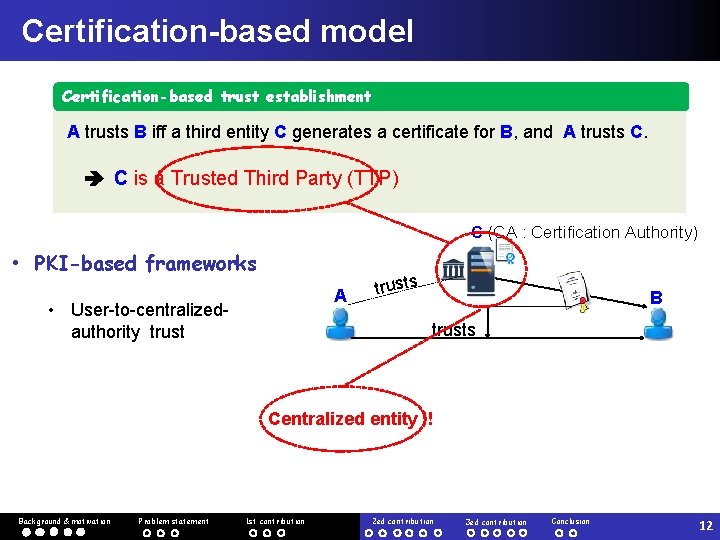
Certification-based model Certification-based trust establishment A trusts B iff a third entity C generates a certificate for B, and A trusts C. C is a Trusted Third Party (TTP) C (CA : Certification Authority) • PKI-based frameworks A • User-to-centralizedauthority trusts B trusts Centralized entity !! Background & motivation Problem statement 1 st contribution 2 ed contribution 3 ed contribution Conclusion 12
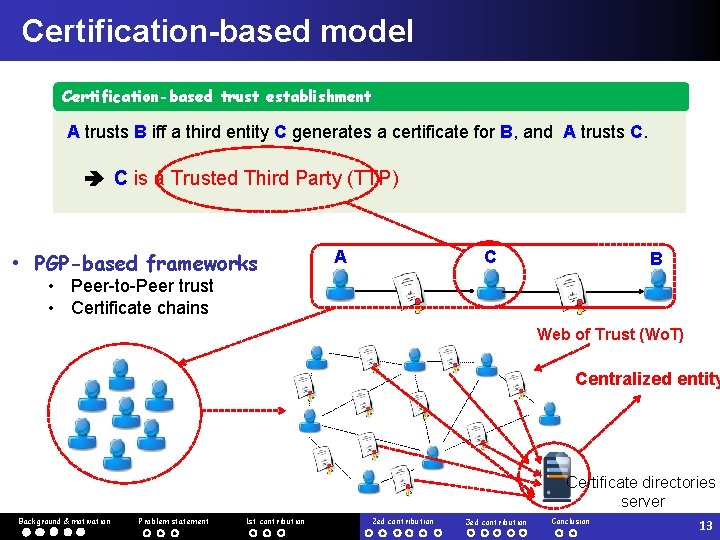
Certification-based model Certification-based trust establishment A trusts B iff a third entity C generates a certificate for B, and A trusts C. C is a Trusted Third Party (TTP) • PGP-based frameworks A C B • Peer-to-Peer trust • Certificate chains Web of Trust (Wo. T) Centralized entity Certificate directories server Background & motivation Problem statement 1 st contribution 2 ed contribution 3 ed contribution Conclusion 13
Outline 1 Background and motivation 2 Problem statement 3 Our original contributions q q q 4 Background & motivation Robust and adaptive threshold certification Compromise-tolerant certification scheme Efficient certificate-less web-of-trust model Conclusion and Future Work Problem statement 1 st contribution 2 ed contribution 3 ed contribution Conclusion 14
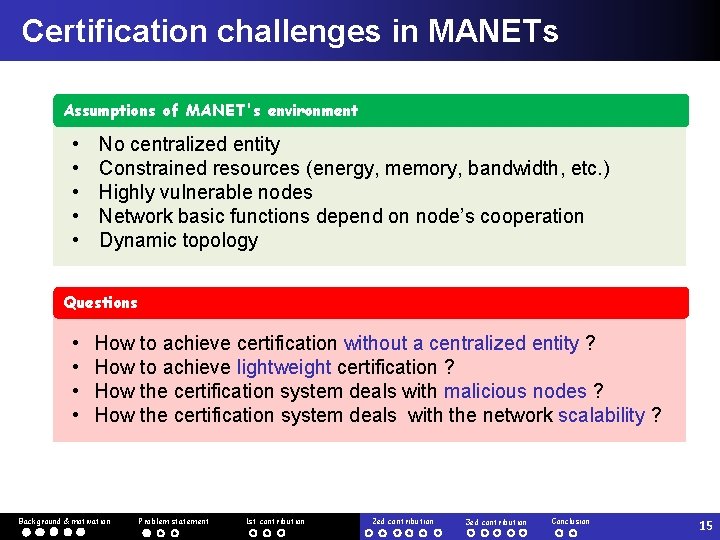
Certification challenges in MANETs Assumptions of MANET's environment • • • No centralized entity Constrained resources (energy, memory, bandwidth, etc. ) Highly vulnerable nodes Network basic functions depend on node’s cooperation Dynamic topology Questions • • How to achieve certification without a centralized entity ? How to achieve lightweight certification ? How the certification system deals with malicious nodes ? How the certification system deals with the network scalability ? Background & motivation Problem statement 1 st contribution 2 ed contribution 3 ed contribution Conclusion 15
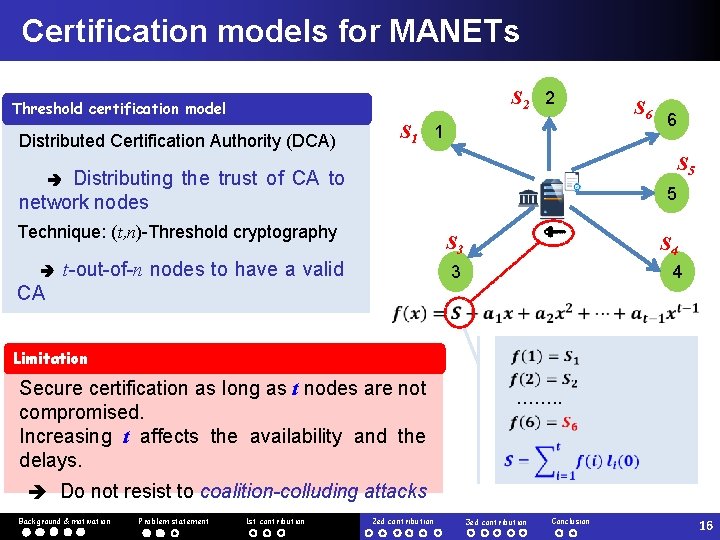
Certification models for MANETs S 2 2 Threshold certification model S 1 1 Distributed Certification Authority (DCA) Distributing the trust of CA to network nodes 5 Technique: (t, n)-Threshold cryptography t-out-of-n nodes to have a valid CA 6 S 5 S 6 S 3 S 4 3 4 Limitation Secure certification as long as t nodes are not compromised. Increasing t affects the availability and the delays. ……. . Do not resist to coalition-colluding attacks Background & motivation Problem statement 1 st contribution 2 ed contribution 3 ed contribution Conclusion 16
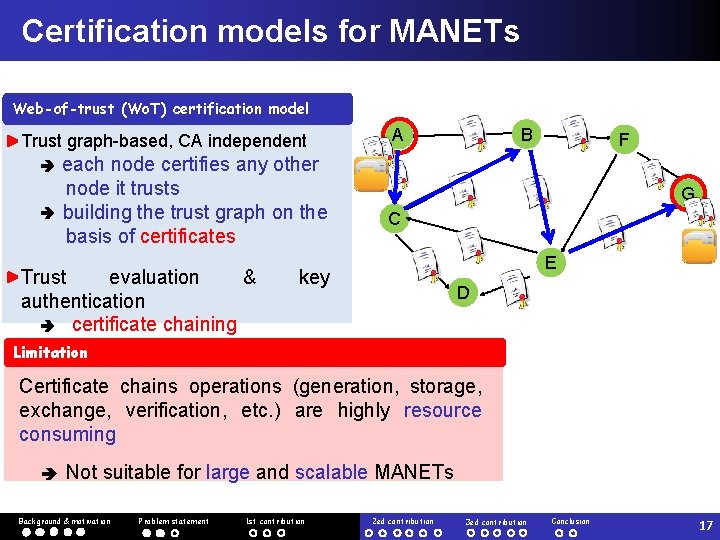
Certification models for MANETs Web-of-trust (Wo. T) certification model Trust graph-based, CA independent each node certifies any other node it trusts building the trust graph on the basis of certificates B A F Trust evaluation & authentication certificate chaining G C E key D Limitation Certificate chains operations (generation, storage, exchange, verification, etc. ) are highly resource consuming Not suitable for large and scalable MANETs Background & motivation Problem statement 1 st contribution 2 ed contribution 3 ed contribution Conclusion 17
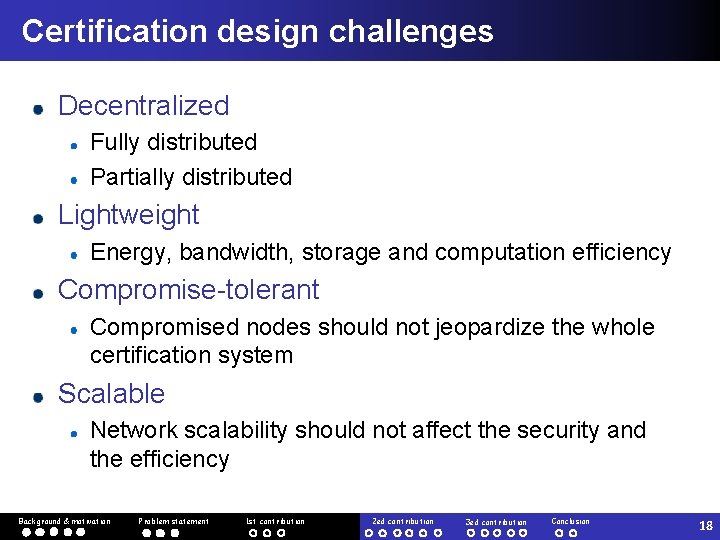
Certification design challenges Decentralized Fully distributed Partially distributed Lightweight Energy, bandwidth, storage and computation efficiency Compromise-tolerant Compromised nodes should not jeopardize the whole certification system Scalable Network scalability should not affect the security and the efficiency Background & motivation Problem statement 1 st contribution 2 ed contribution 3 ed contribution Conclusion 18
Outline 1 Background and motivation 2 Problem statement 3 Our original contributions q q q 4 Background & motivation Robust and adaptive threshold certification Compromise-tolerant certification scheme Efficient certificate-less web-of-trust model Conclusion and Future Work Problem statement 1 st contribution 2 ed contribution 3 ed contribution Conclusion 19
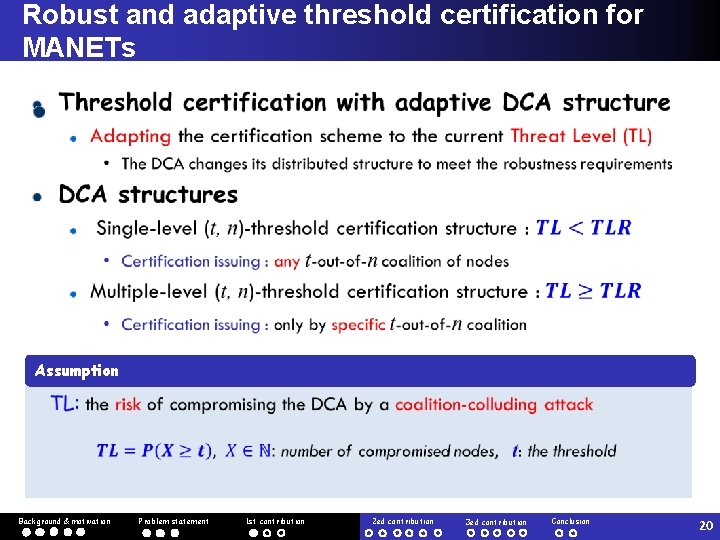
Robust and adaptive threshold certification for MANETs Assumption Background & motivation Problem statement 1 st contribution 2 ed contribution 3 ed contribution Conclusion 20
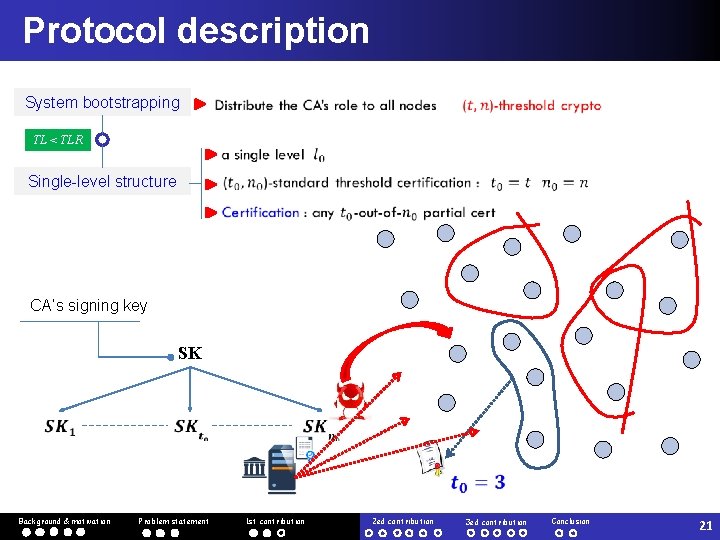
Protocol description System bootstrapping TL < TLR Single-level structure CA’s signing key SK Background & motivation Problem statement 1 st contribution 2 ed contribution 3 ed contribution Conclusion 21
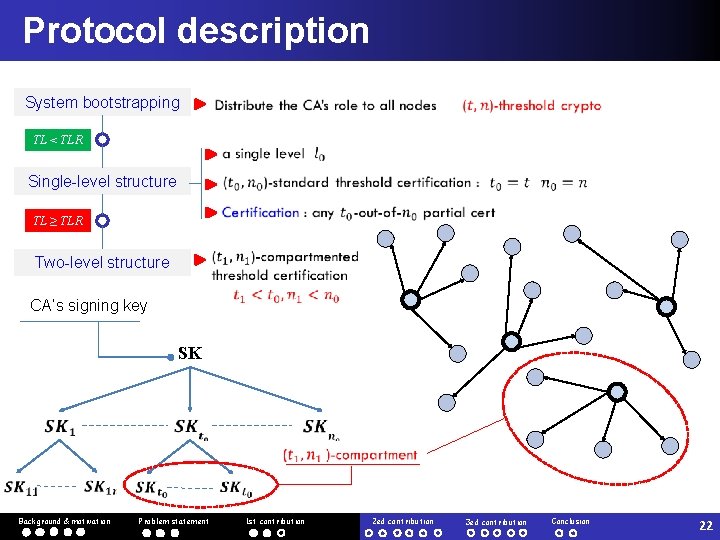
Protocol description System bootstrapping TL < TLR Single-level structure TL ≥ TLR Two-level structure CA’s signing key SK Background & motivation Problem statement 1 st contribution 2 ed contribution 3 ed contribution Conclusion 22
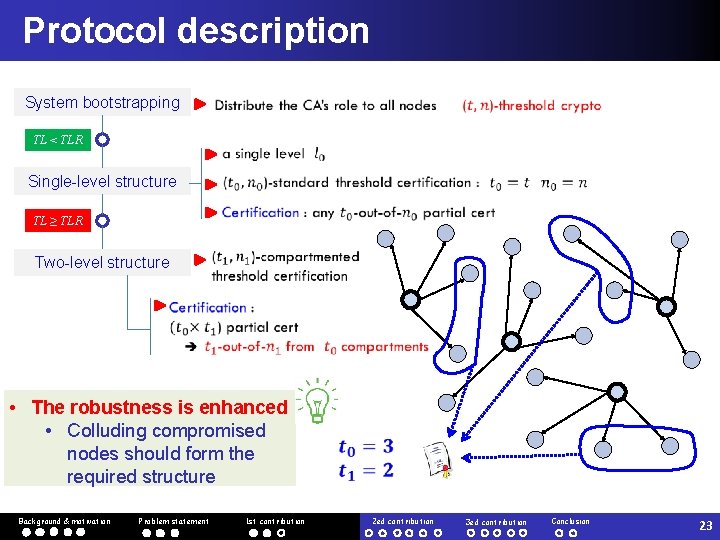
Protocol description System bootstrapping TL < TLR Single-level structure TL ≥ TLR Two-level structure • The robustness is enhanced • Colluding compromised nodes should form the required structure Background & motivation Problem statement 1 st contribution 2 ed contribution 3 ed contribution Conclusion 23
Simulation results Impact of compromised nodes on the availability Background & motivation Problem statement 1 st contribution 2 ed contribution 3 ed contribution Conclusion 24
Simulation results Impact of compromised nodes on the system robustness Background & motivation Problem statement 1 st contribution 2 ed contribution 3 ed contribution Conclusion 25
Outline 1 Background and motivation 2 Problem statement 3 Our original contributions q q q 4 Background & motivation Robust and adaptive threshold certification Compromise-tolerant certification scheme Efficient certificate-less web-of-trust model Conclusion and Future Work Problem statement 1 st contribution 2 ed contribution 3 ed contribution Conclusion 26
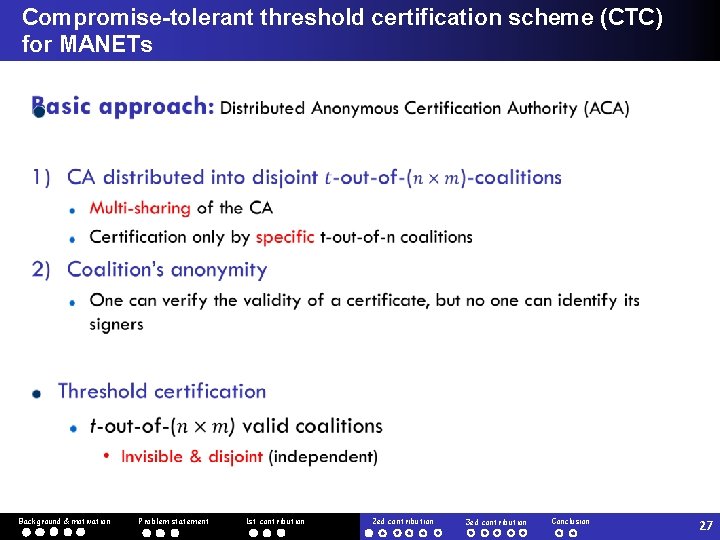
Compromise-tolerant threshold certification scheme (CTC) for MANETs Background & motivation Problem statement 1 st contribution 2 ed contribution 3 ed contribution Conclusion 27
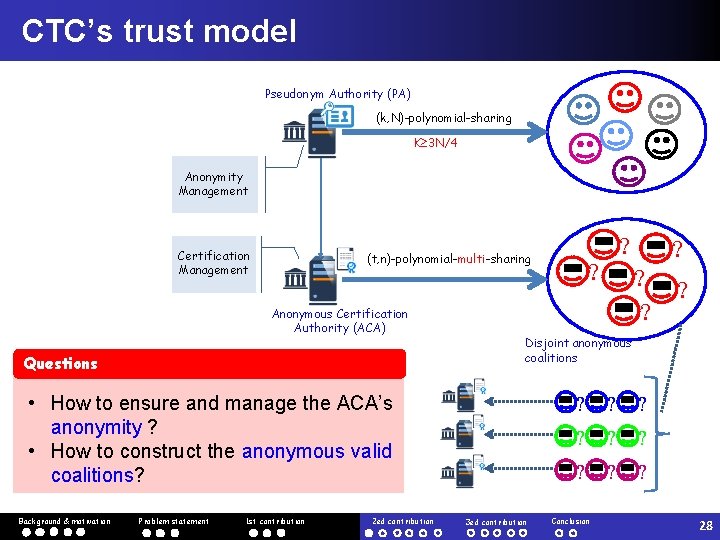
CTC’s trust model Pseudonym Authority (PA) (k, N)-polynomial-sharing K 3 N/4 Anonymity Management Certification Management (t, n)-polynomial-multi-sharing Anonymous Certification Authority (ACA) Questions Problem statement 1 st contribution 2 ed contribution ? ? ? Disjoint anonymous coalitions • How to ensure and manage the ACA’s anonymity ? • How to construct the anonymous valid coalitions? Background & motivation ? 3 ed contribution ? ? ? Conclusion 28
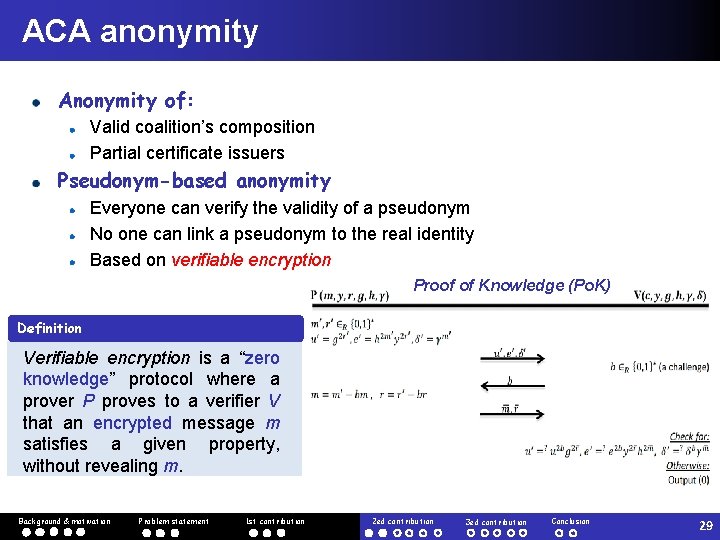
ACA anonymity Anonymity of: Valid coalition’s composition Partial certificate issuers Pseudonym-based anonymity Everyone can verify the validity of a pseudonym No one can link a pseudonym to the real identity Based on verifiable encryption Proof of Knowledge (Po. K) Definition Verifiable encryption is a “zero knowledge” protocol where a prover P proves to a verifier V that an encrypted message m satisfies a given property, without revealing m. Background & motivation Problem statement 1 st contribution 2 ed contribution 3 ed contribution Conclusion 29
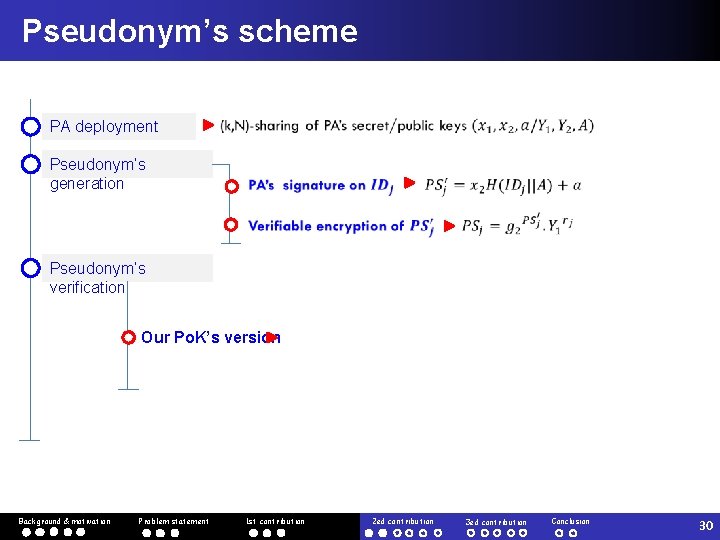
Pseudonym’s scheme PA deployment Pseudonym’s generation Pseudonym’s verification Our Po. K’s version Background & motivation Problem statement 1 st contribution 2 ed contribution 3 ed contribution Conclusion 30
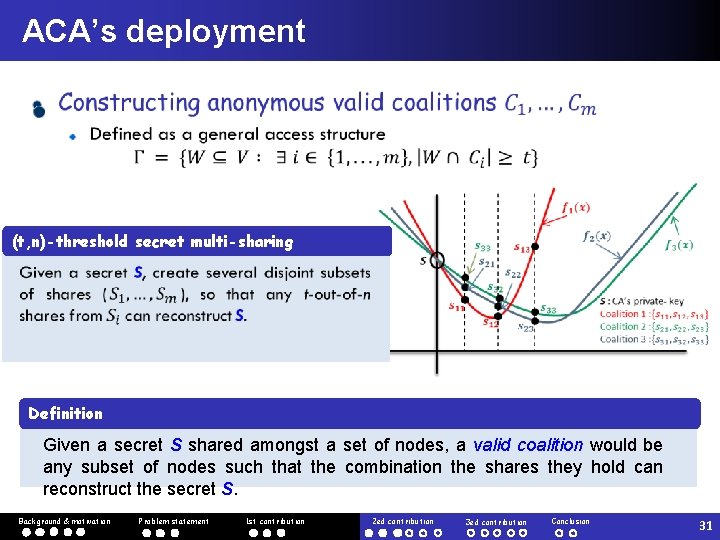
ACA’s deployment (t, n)-threshold secret multi-sharing Definition Given a secret S shared amongst a set of nodes, a valid coalition would be any subset of nodes such that the combination the shares they hold can reconstruct the secret S. Background & motivation Problem statement 1 st contribution 2 ed contribution 3 ed contribution Conclusion 31
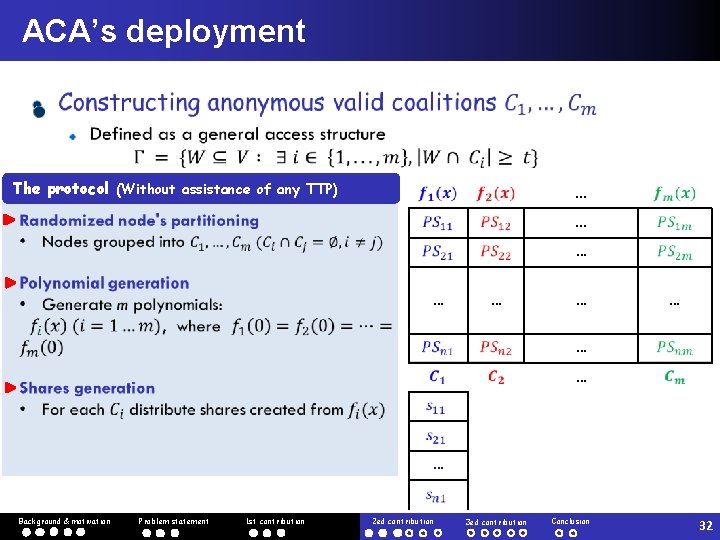
ACA’s deployment The protocol (Without assistance of any TTP) . . . … … … … Background & motivation Problem statement 1 st contribution 2 ed contribution 3 ed contribution Conclusion 32
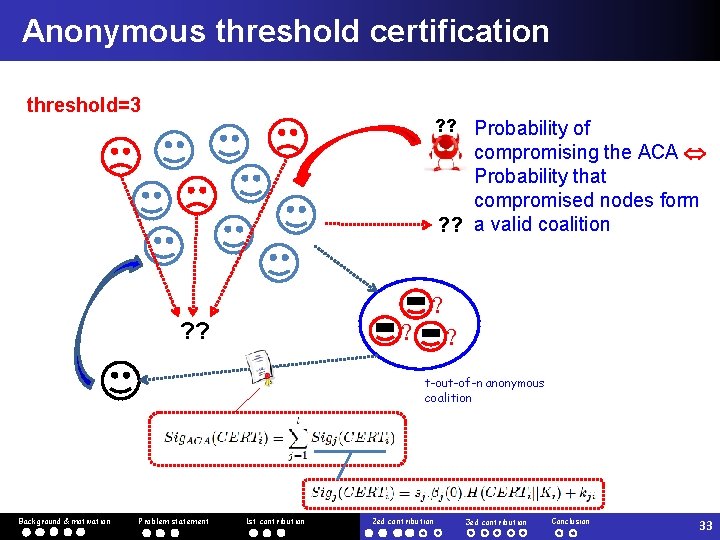
Anonymous threshold certification threshold=3 ? ? Probability of compromising the ACA Probability that compromised nodes form ? ? a valid coalition ? ? ? t-out-of-n anonymous coalition Background & motivation Problem statement 1 st contribution 2 ed contribution 3 ed contribution Conclusion 33
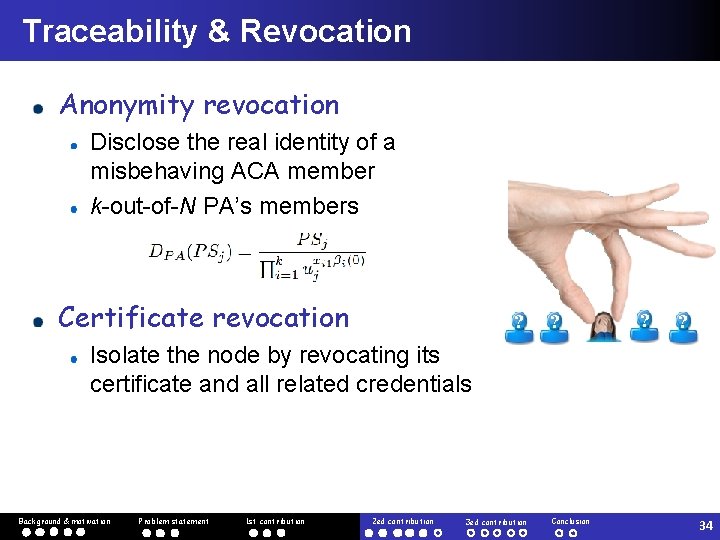
Traceability & Revocation Anonymity revocation Disclose the real identity of a misbehaving ACA member k-out-of-N PA’s members Certificate revocation ? ? Isolate the node by revocating its certificate and all related credentials Background & motivation Problem statement 1 st contribution 2 ed contribution 3 ed contribution Conclusion 34
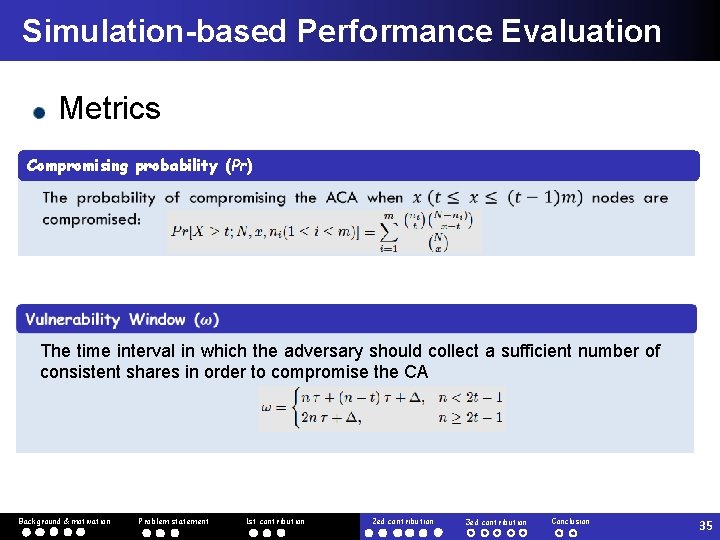
Simulation-based Performance Evaluation Metrics Compromising probability (Pr) The time interval in which the adversary should collect a sufficient number of consistent shares in order to compromise the CA Background & motivation Problem statement 1 st contribution 2 ed contribution 3 ed contribution Conclusion 35
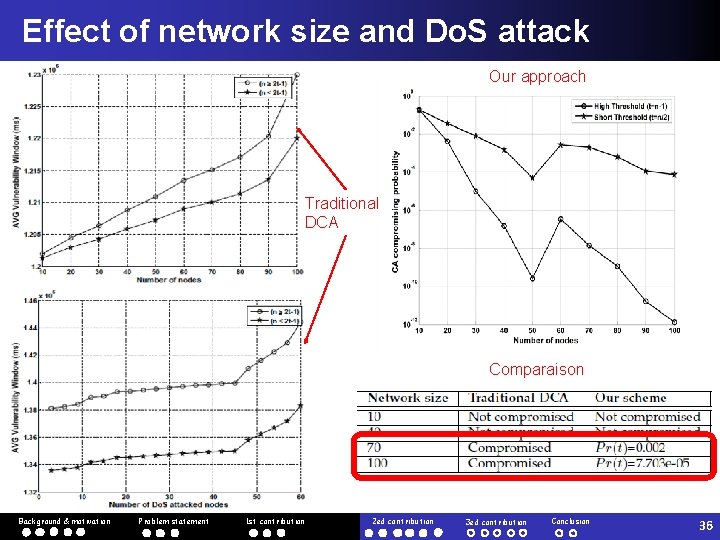
Effect of network size and Do. S attack Our approach Traditional DCA Comparaison Background & motivation Problem statement 1 st contribution 2 ed contribution 3 ed contribution Conclusion 36
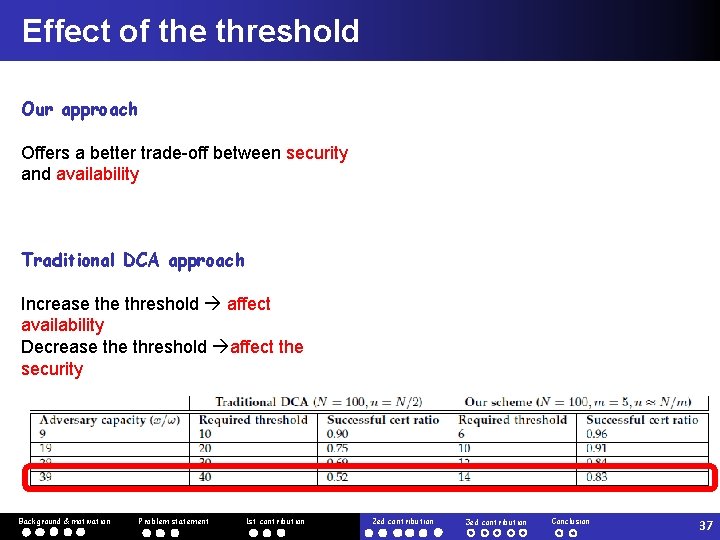
Effect of the threshold Our approach Offers a better trade-off between security and availability Traditional DCA approach Increase threshold affect availability Decrease threshold affect the security Background & motivation Problem statement 1 st contribution 2 ed contribution 3 ed contribution Conclusion 37
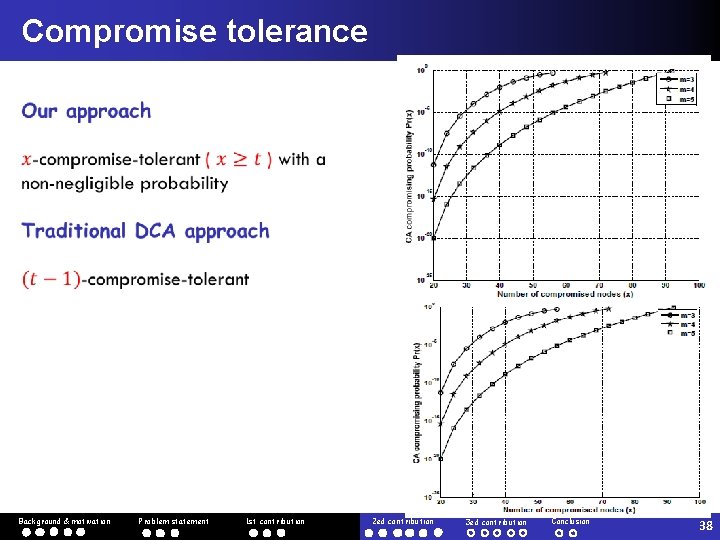
Compromise tolerance Background & motivation Problem statement 1 st contribution 2 ed contribution 3 ed contribution Conclusion 38
Outline 1 Background and motivation 2 Problem statement 3 Our original contributions q q q 4 Background & motivation Robust and adaptive threshold certification Compromise-tolerant certification scheme Efficient certificate-less web-of-trust model Conclusion and Future Work Problem statement 1 st contribution 2 ed contribution 3 ed contribution Conclusion 39
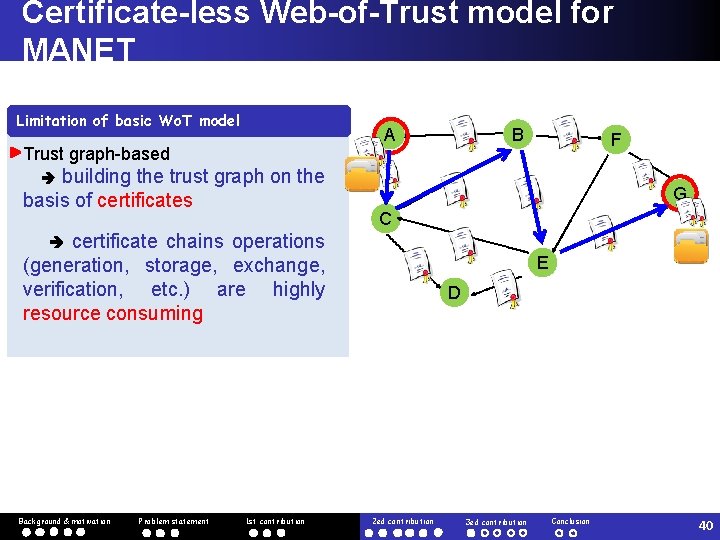
Certificate-less Web-of-Trust model for MANET Limitation of basic Wo. T model B A Trust graph-based building the trust graph on the basis of certificates F G C certificate chains operations (generation, storage, exchange, verification, etc. ) are highly resource consuming Background & motivation Problem statement 1 st contribution E D 2 ed contribution 3 ed contribution Conclusion 40
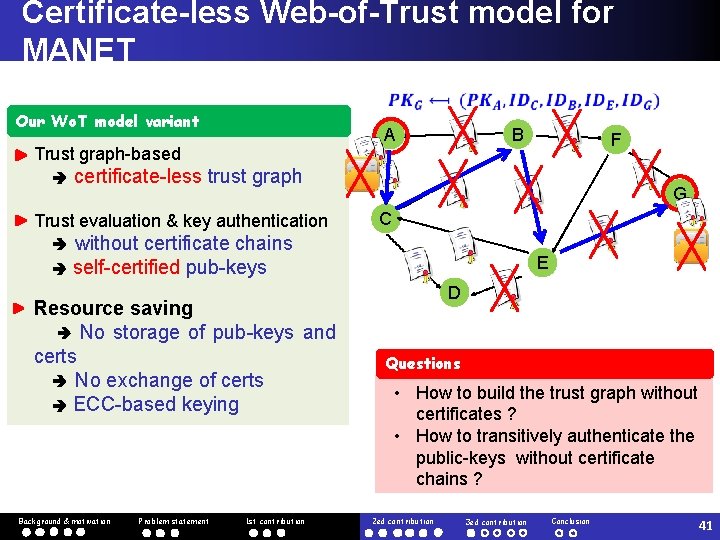
Certificate-less Web-of-Trust model for MANET Our Wo. T model variant Trust graph-based F certificate-less trust graph Trust evaluation & key authentication B A G C without certificate chains self-certified pub-keys Resource saving No storage of pub-keys and certs No exchange of certs ECC-based keying Background & motivation Problem statement 1 st contribution E D Questions • How to build the trust graph without certificates ? • How to transitively authenticate the public-keys without certificate chains ? 2 ed contribution 3 ed contribution Conclusion 41
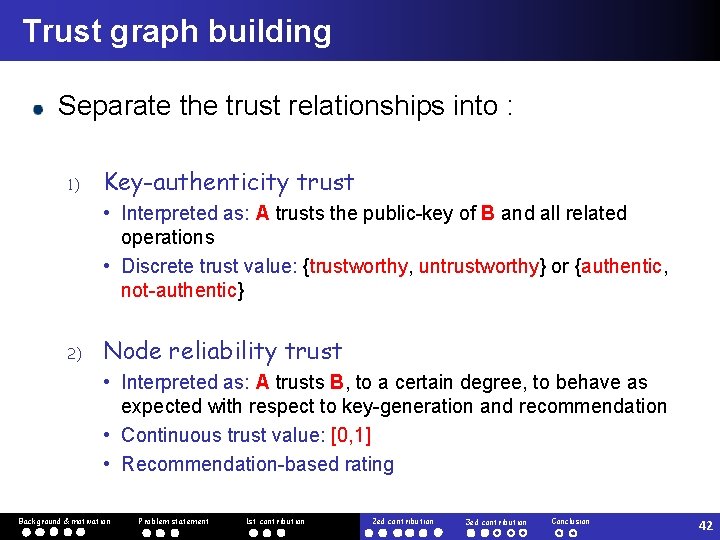
Trust graph building Separate the trust relationships into : 1) Key-authenticity trust • Interpreted as: A trusts the public-key of B and all related operations • Discrete trust value: {trustworthy, untrustworthy} or {authentic, not-authentic} 2) Node reliability trust • Interpreted as: A trusts B, to a certain degree, to behave as expected with respect to key-generation and recommendation • Continuous trust value: [0, 1] • Recommendation-based rating Background & motivation Problem statement 1 st contribution 2 ed contribution 3 ed contribution Conclusion 42
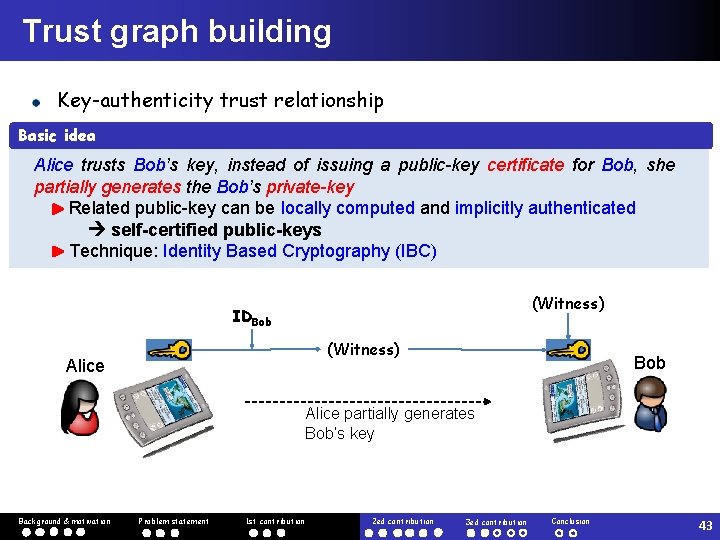
Trust graph building Key-authenticity trust relationship Basic idea Alice trusts Bob’s key, instead of issuing a public-key certificate for Bob, she partially generates the Bob’s private-key Related public-key can be locally computed and implicitly authenticated self-certified public-keys Technique: Identity Based Cryptography (IBC) (Witness) IDBob (Witness) Alice Bob Alice partially generates Bob’s key Background & motivation Problem statement 1 st contribution 2 ed contribution 3 ed contribution Conclusion 43
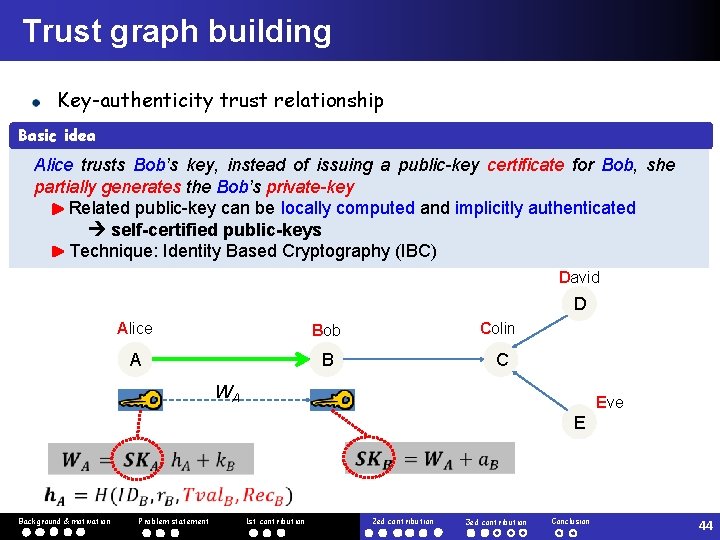
Trust graph building Key-authenticity trust relationship Basic idea Alice trusts Bob’s key, instead of issuing a public-key certificate for Bob, she partially generates the Bob’s private-key Related public-key can be locally computed and implicitly authenticated self-certified public-keys Technique: Identity Based Cryptography (IBC) David D Alice Bob Colin A B C WA Eve E Background & motivation Problem statement 1 st contribution 2 ed contribution 3 ed contribution Conclusion 44
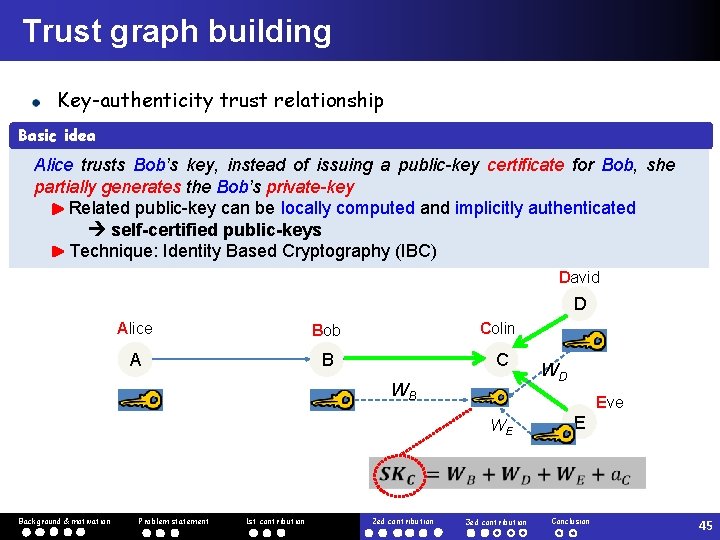
Trust graph building Key-authenticity trust relationship Basic idea Alice trusts Bob’s key, instead of issuing a public-key certificate for Bob, she partially generates the Bob’s private-key Related public-key can be locally computed and implicitly authenticated self-certified public-keys Technique: Identity Based Cryptography (IBC) David D Alice Bob Colin A B C WB WD Eve WE E Background & motivation Problem statement 1 st contribution 2 ed contribution 3 ed contribution Conclusion 45
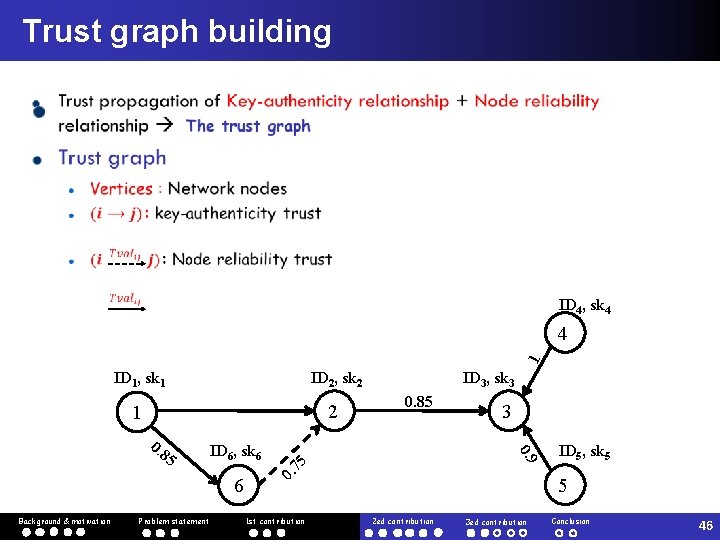
Trust graph building ID 4, sk 4 1 4 ID 1, sk 1 ID 2, sk 2 1 2 5 ID 6, sk 6 6 Background & motivation Problem statement 0. 85 75 0. 1 st contribution 3 0. 9 0. 8 ID 3, sk 3 ID 5, sk 5 5 2 ed contribution 3 ed contribution Conclusion 46
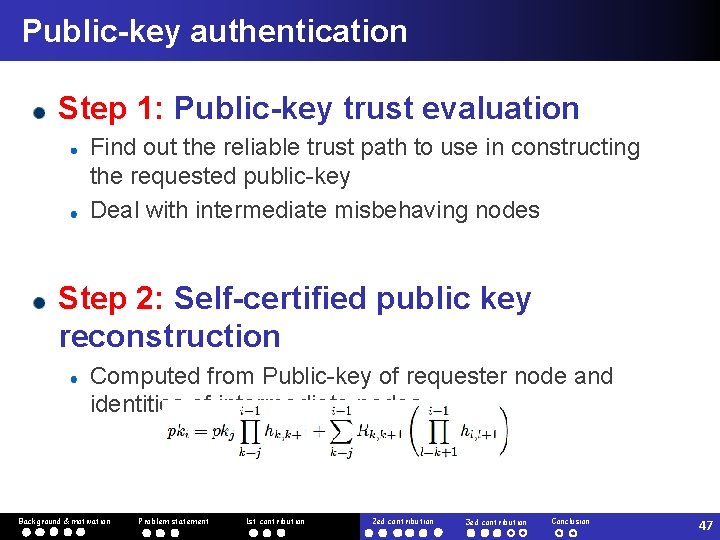
Public-key authentication Step 1: Public-key trust evaluation Find out the reliable trust path to use in constructing the requested public-key Deal with intermediate misbehaving nodes Step 2: Self-certified public key reconstruction Computed from Public-key of requester node and identities of intermediate nodes Background & motivation Problem statement 1 st contribution 2 ed contribution 3 ed contribution Conclusion 47
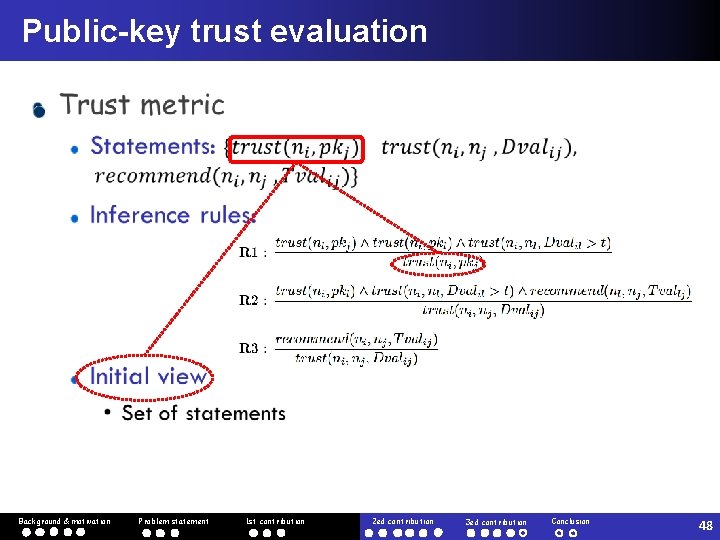
Public-key trust evaluation Background & motivation Problem statement 1 st contribution 2 ed contribution 3 ed contribution Conclusion 48
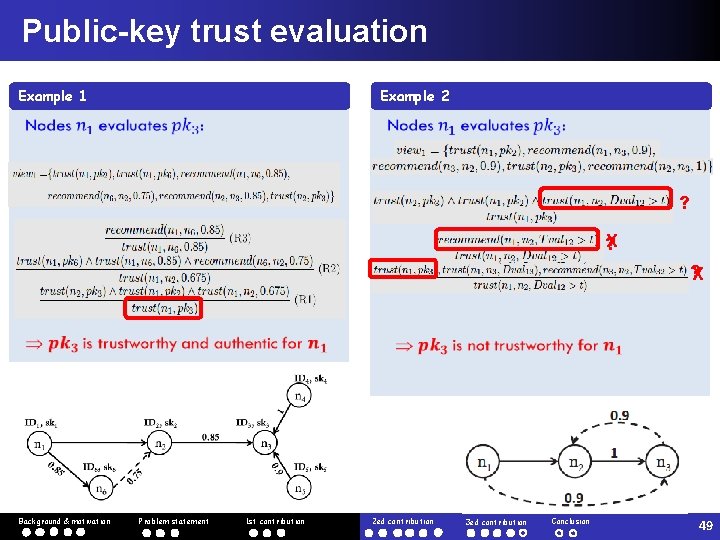
Public-key trust evaluation Example 2 Example 1 ? X ? ? X Background & motivation Problem statement 1 st contribution 2 ed contribution 3 ed contribution Conclusion 49
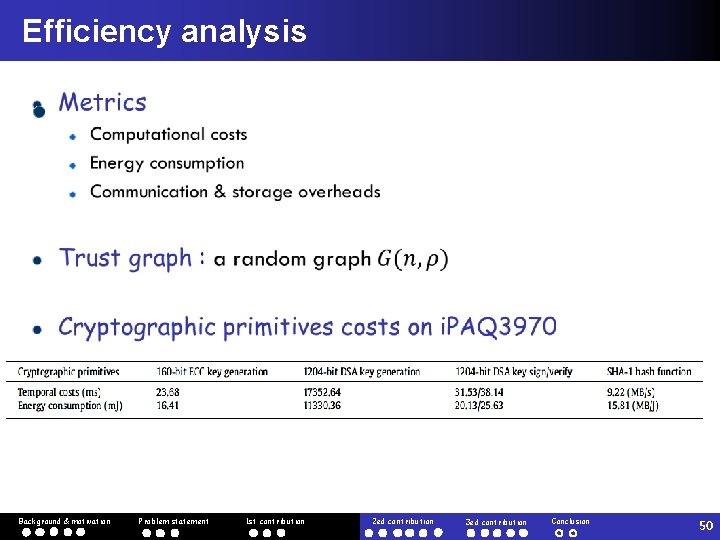
Efficiency analysis Background & motivation Problem statement 1 st contribution 2 ed contribution 3 ed contribution Conclusion 50
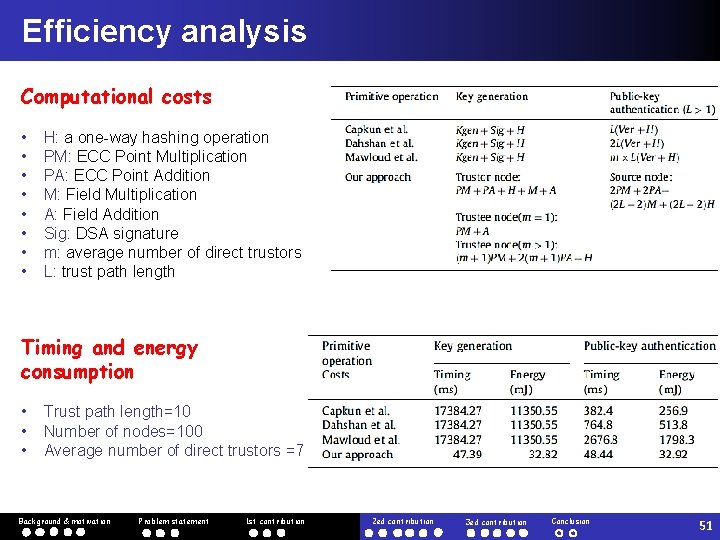
Efficiency analysis Computational costs • • H: a one-way hashing operation PM: ECC Point Multiplication PA: ECC Point Addition M: Field Multiplication A: Field Addition Sig: DSA signature m: average number of direct trustors L: trust path length Timing and energy consumption • • • Trust path length=10 Number of nodes=100 Average number of direct trustors =7 Background & motivation Problem statement 1 st contribution 2 ed contribution 3 ed contribution Conclusion 51
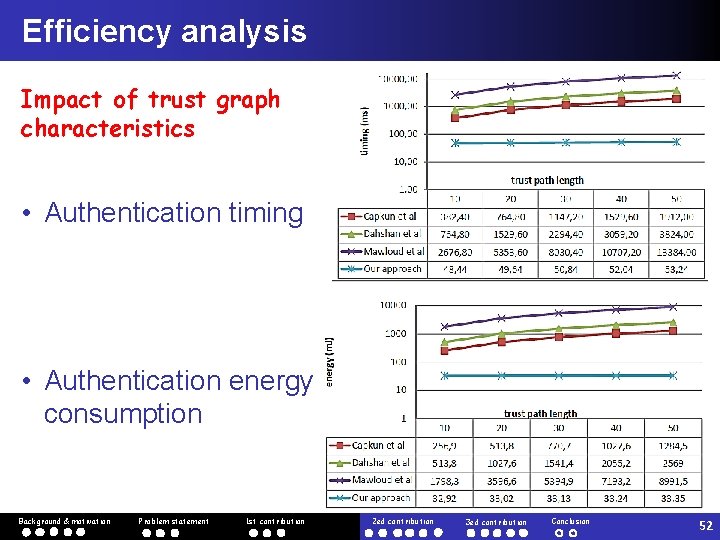
Efficiency analysis Impact of trust graph characteristics • Authentication timing • Authentication energy consumption Background & motivation Problem statement 1 st contribution 2 ed contribution 3 ed contribution Conclusion 52
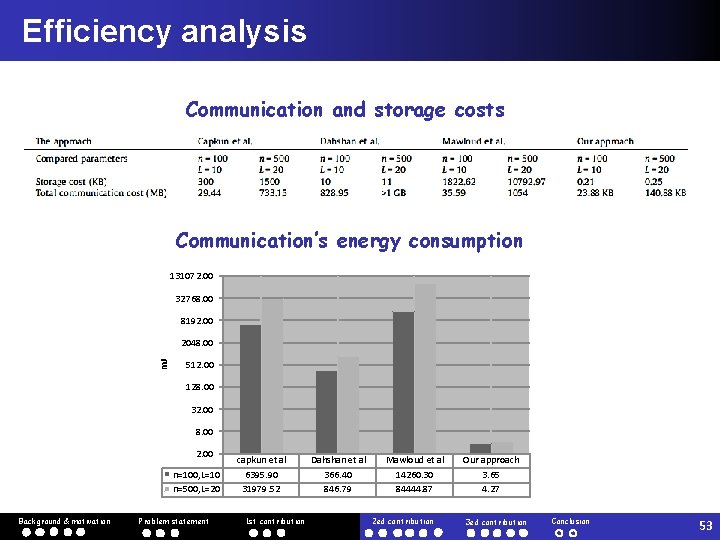
Efficiency analysis Communication and storage costs Communication’s energy consumption 131072. 00 32768. 00 8192. 00 m. J 2048. 00 512. 00 128. 00 32. 00 8. 00 2. 00 n=100, L=10 n=500, L=20 Background & motivation Problem statement capkun et al 6395. 90 31979. 52 1 st contribution Dahshan et al 366. 40 846. 79 Mawloud et al 14260. 30 84444. 87 2 ed contribution Our approach 3. 65 4. 27 3 ed contribution Conclusion 53
Outline 1 Background and motivation 2 Problem statement 3 Our original contributions q q q 4 Background & motivation Robust and adaptive threshold certification Compromise-tolerant certification scheme Efficient certificate-less web-of-trust model Conclusion and Future Work Problem statement 1 st contribution 2 ed contribution 3 ed contribution Conclusion 54
Conclusion Security and trust issues in MANETs Traditional trust models not suitable for MANETs • Certification-based & Reputation-based Limitations of certification-based models in MANETs Threshold certification: not robust against node compromising Wo. T-based certification: highly resource consuming, do not scale to large networks New suitable certification approaches for MANETs Robust and adaptive threshold certification scheme (ATC) • Dealing with node compromising Compromise-tolerant certification with anonymous authority (CTC) • Enhancing the compromise tolerance without affecting the service availability Efficient certificate-less web-of-trust model (Css. Wo. T) • Resource saving even in large networks Background & motivation Problem statement 1 st contribution 2 ed contribution 3 ed contribution Conclusion 55
Future Work Css. Wo. T: Solving the key-revocation Detect and remove a compromised key without affecting the whole subsequent chain Css. Wo. T: Solving the computation of trust values necessary for building the trust graph CTC: Developing a protocol for an optimized propagation of certification requests to anonymous members of a valid coalition Exploring our pseudonym’s mechanism to deal with privacy in MANETs Background & motivation Problem statement 1 st contribution 2 ed contribution 3 ed contribution Conclusion 56
List of papers Journal papers 1. K. Hamouid and K. Adi. Efficient certificate-less web-of-trust model for public-key authentication in MANET. Computer Communications journal, 63: 24 -39, Elsevier, 2015 2. K. Hamouid and K. Adi. Secure and robust threshold key management (SRKM) scheme for ad hoc networks. Security and Communication Networks journal, 3(6): 517 -534, Wiley, 2010 3. K. Hamouid and K. Adi. Compromise-tolerant certification management scheme in MANETs with anonymous distributed authority. Submitted to IEEE Transactions on Mobile Computing journal Conference papers 4. K. Hamouid and K. Adi. Self-certified based trust establishment scheme in Ad-hoc networks. 5 th IFIP International Conference on New Technologies, Mobility and Security, NTMS, IEEE, pp. 1 -7, 2012 5. K. Hamouid and K. Adi. A Key Management Scheme for Clustering based Ad hoc networks. CECS'2010 International Workshop, jointly organized by the university Backgroundof Batna and Berlin University of Technology, October, 2010 & motivation Problem statement 1 st contribution 2 ed contribution Conclusion 3 ed contribution 57
Thank You … for your attention “Tous les progrès sont précaires, et la solution d’un problème nous confronte à un autre problème” (Martin Luther King) 58
- Slides: 58