Universally Composable Symbolic Analysis of Security Protocols Jonathan
Universally Composable Symbolic Analysis of Security Protocols Jonathan Herzog (Joint work with Ran Canetti) 7 June 2004 The author's affiliation with The MITRE Corporation is provided for identification purposes only, and is not intended to convey or imply MITRE's concurrence with, or support for, the positions, opinions or viewpoints expressed by the author.
Introduction n n This talk: symbolic analysis can guarantee universally composable (UC) security Dolev-Yao (symbolic) model Adversary extremely limited ¨ Proofs simple, can even be automated ¨ n UC (concrete) framework Complexity- and information-theoretic approach ¨ Guarantees strong security and composability properties ¨ Requires “hand-crafted” proofs ¨ n Symbolic security proofs are sound in UC framework Traditional (symbolic) mutual-authentication definitions suffice ¨ Need strengthened notion of symbolic key-exchange ¨
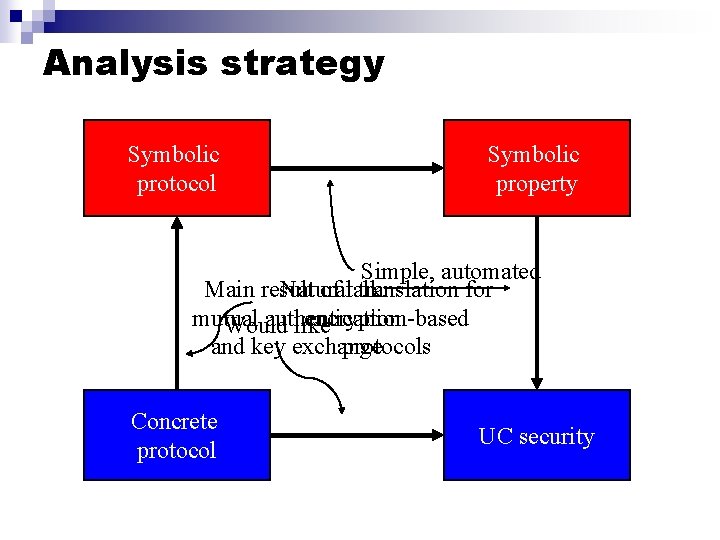
Analysis strategy Symbolic protocol Symbolic property Simple, automated Main result Natural of talk: translation for mutual authentication encryption-based Would like and key exchange protocols Concrete protocol UC security
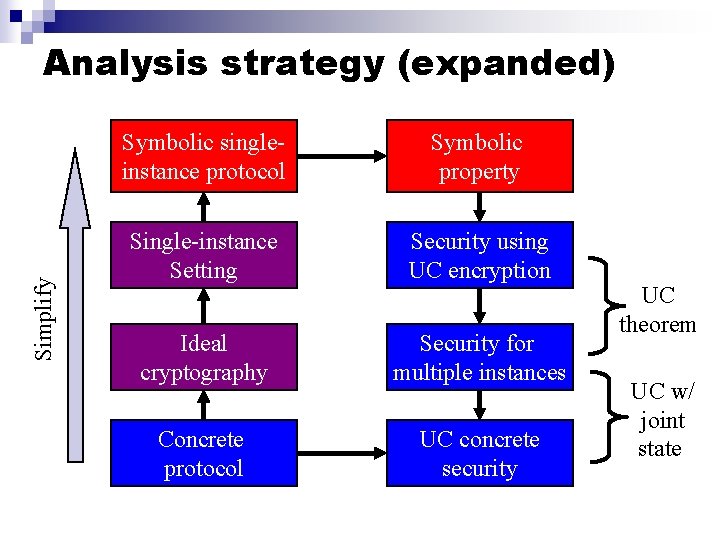
Simplify Analysis strategy (expanded) Symbolic singleinstance protocol Symbolic property Single-instance Setting Security using UC encryption Ideal cryptography Security for multiple instances Concrete protocol UC concrete security UC theorem UC w/ joint state
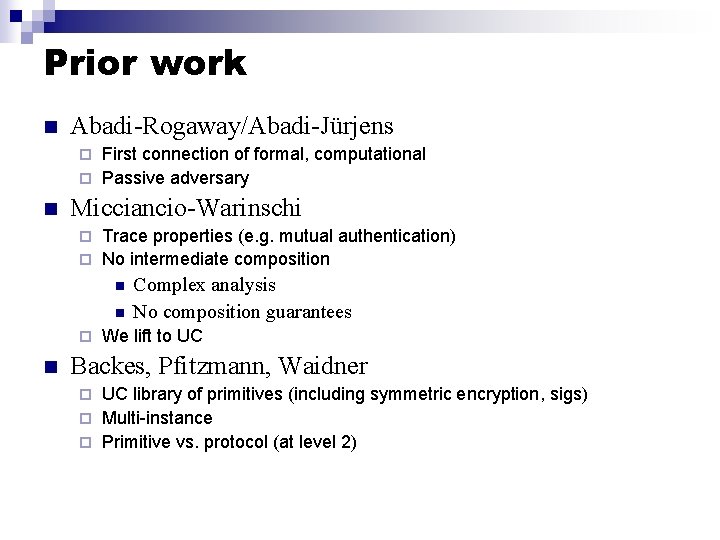
Prior work n Abadi-Rogaway/Abadi-Jürjens First connection of formal, computational ¨ Passive adversary ¨ n Micciancio-Warinschi Trace properties (e. g. mutual authentication) ¨ No intermediate composition ¨ n Complex analysis No composition guarantees We lift to UC Backes, Pfitzmann, Waidner UC library of primitives (including symmetric encryption, sigs) ¨ Multi-instance ¨ Primitive vs. protocol (at level 2) ¨
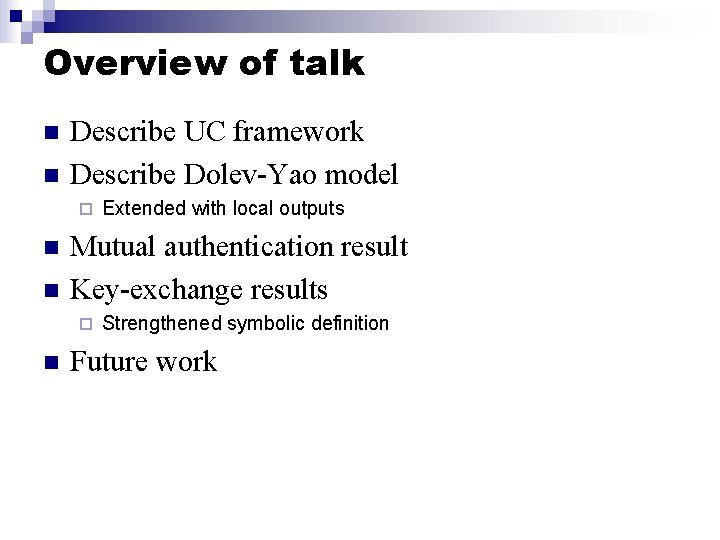
Overview of talk n n Describe UC framework Describe Dolev-Yao model ¨ n n Mutual authentication result Key-exchange results ¨ n Extended with local outputs Strengthened symbolic definition Future work
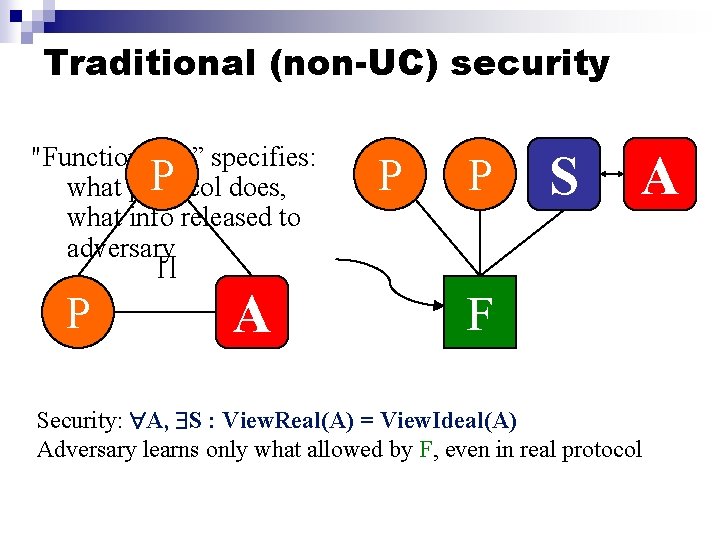
Traditional (non-UC) security "Functionality” specifies: P does, what protocol what info released to adversary P P S A ∏ P A F Security: A, S : View. Real(A) = View. Ideal(A) Adversary learns only what allowed by F, even in real protocol
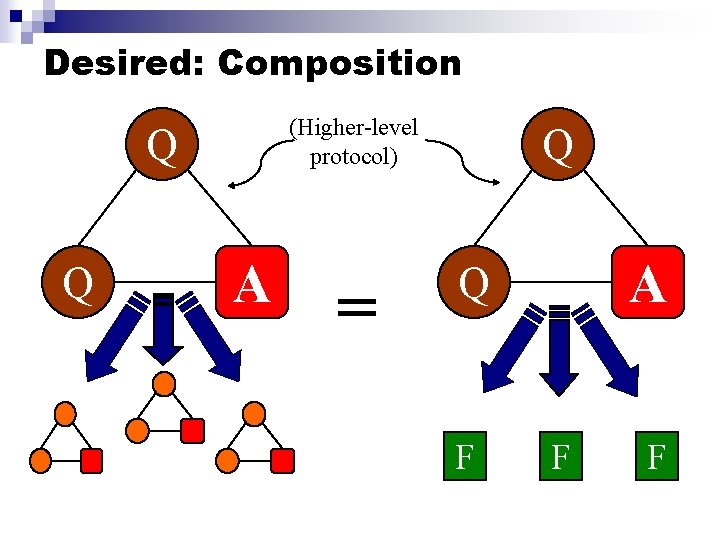
Desired: Composition (Higher-level protocol) Q Q A = Q A Q F F F
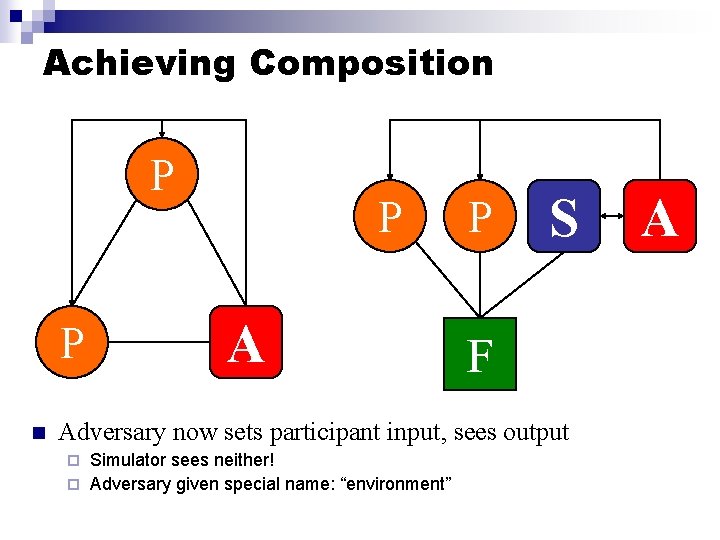
Achieving Composition P P n P A P S F Adversary now sets participant input, sees output Simulator sees neither! ¨ Adversary given special name: “environment” ¨ A
Achieving Composition n UC security: A, S : View. Real(A) = View. Ideal(A) n Enforces that protocol messages and protocol outputs are independent n Strongest known (computational) notion of protocol security
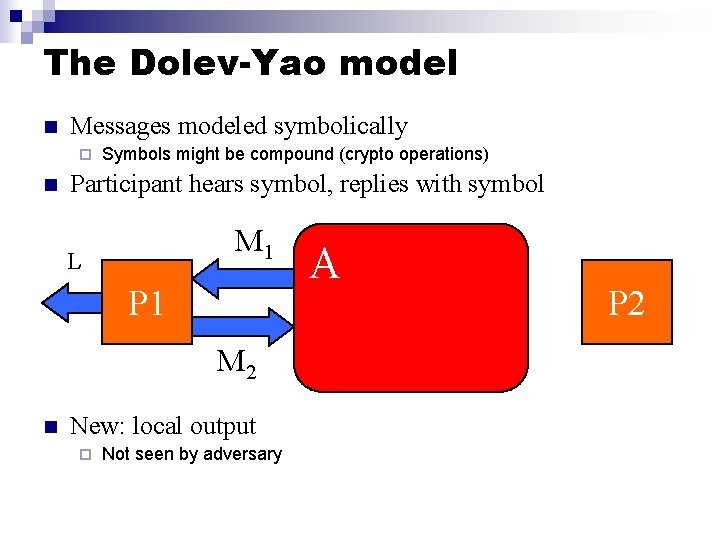
The Dolev-Yao model n Messages modeled symbolically ¨ n Symbols might be compound (crypto operations) Participant hears symbol, replies with symbol M 1 L P 1 M 2 n New: local output ¨ Not seen by adversary A P 2
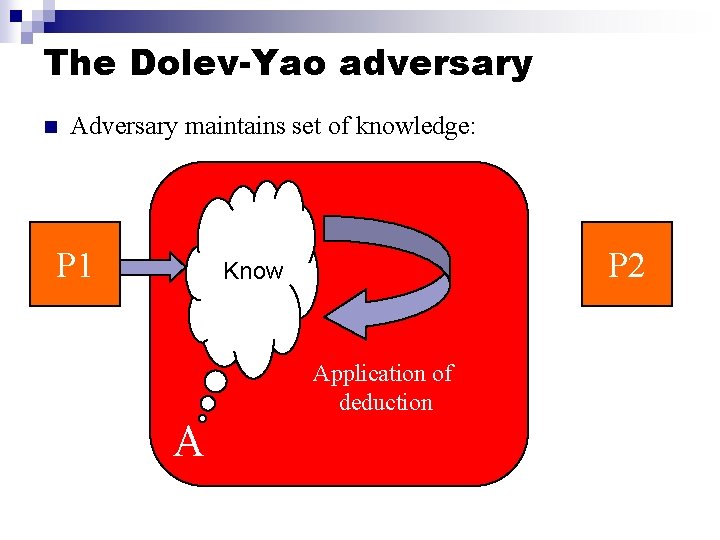
The Dolev-Yao adversary n Adversary maintains set of knowledge: P 1 P 2 Know Application of deduction A
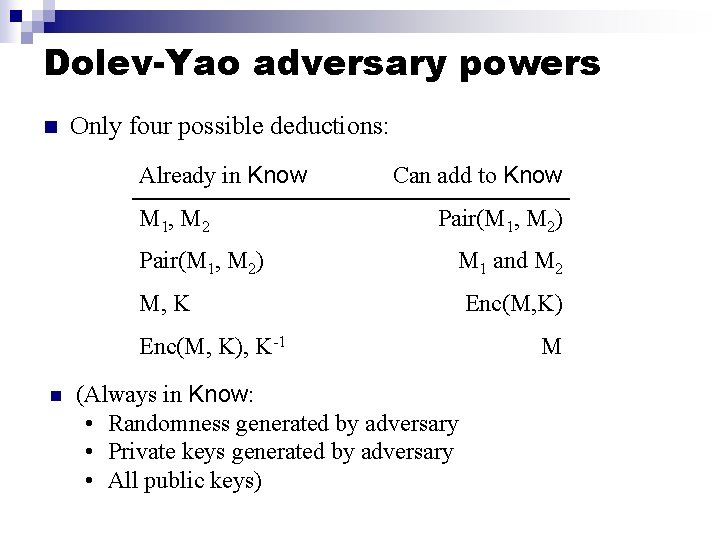
Dolev-Yao adversary powers n Only four possible deductions: Already in Know M 1, M 2 Pair(M 1, M 2) Can add to Know Pair(M 1, M 2) M 1 and M 2 M, K Enc(M, K), K-1 n (Always in Know: • Randomness generated by adversary • Private keys generated by adversary • All public keys) Enc(M, K) M
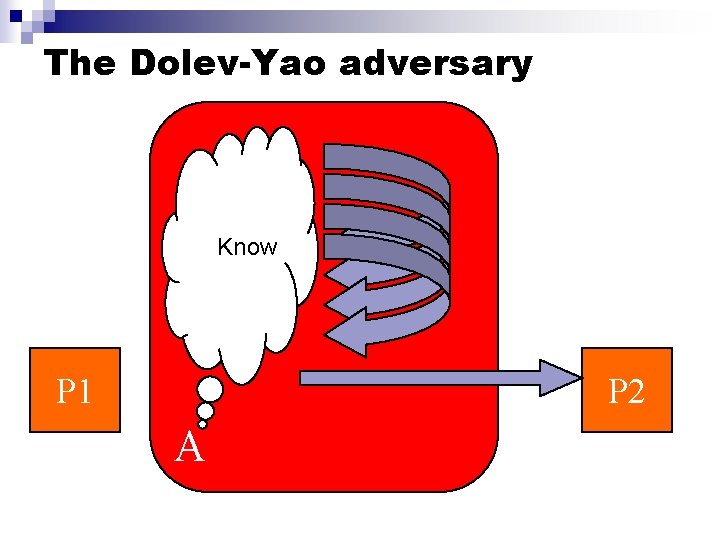
The Dolev-Yao adversary Know P 1 P 2 A
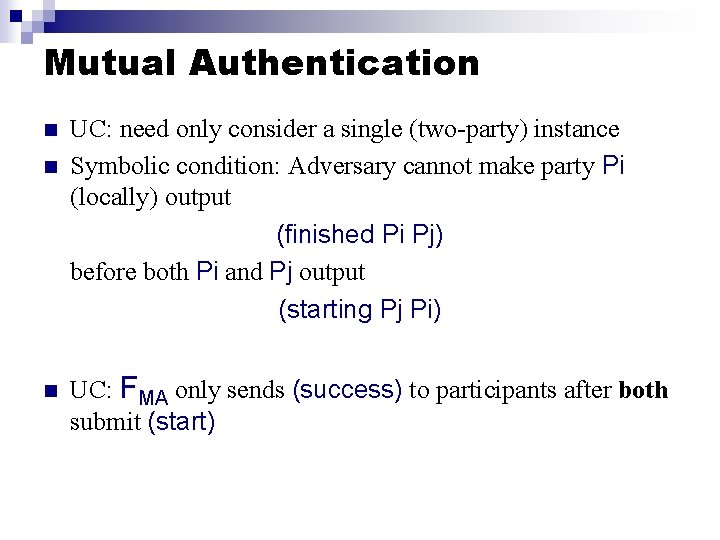
Mutual Authentication n UC: need only consider a single (two-party) instance Symbolic condition: Adversary cannot make party Pi (locally) output (finished Pi Pj) before both Pi and Pj output (starting Pj Pi) UC: FMA only sends (success) to participants after both submit (start)
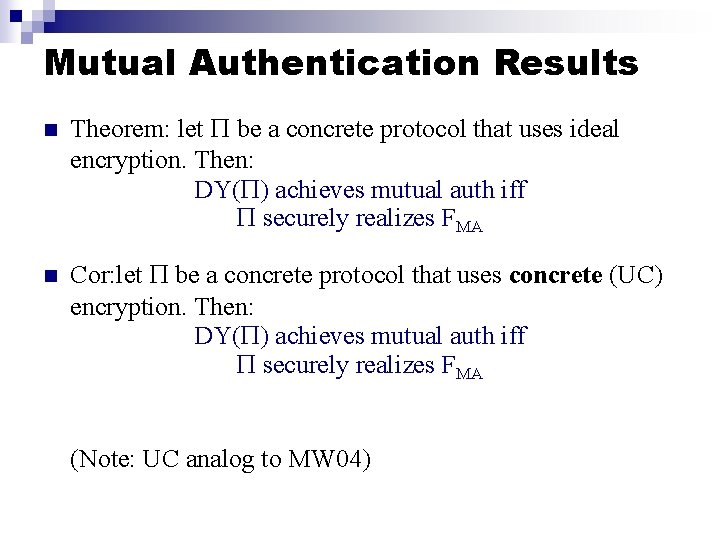
Mutual Authentication Results n Theorem: let be a concrete protocol that uses ideal encryption. Then: DY( ) achieves mutual auth iff securely realizes FMA n Cor: let be a concrete protocol that uses concrete (UC) encryption. Then: DY( ) achieves mutual auth iff securely realizes FMA (Note: UC analog to MW 04)
Key exchange n n UC: FKE creates single new key, sends to requesting participants (but not adversary) Symbolic: 1. 2. n Key Agreement: If P 1 outputs (Finished P 1 P 2 K) and P 2 outputs (Finished P 2 P 1 K’) then K = K’. Traditional Dolev-Yao secrecy: If Pi outputs (Finished Pi Pj K), then K can never be in adversary’s set Know Not strong enough!
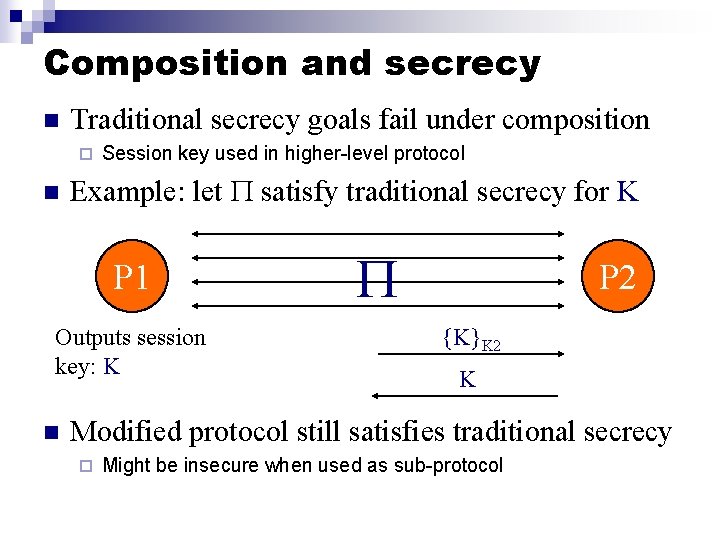
Composition and secrecy n Traditional secrecy goals fail under composition ¨ n Session key used in higher-level protocol Example: let satisfy traditional secrecy for K P 1 Outputs session key: K n P 2 {K}K 2 K Modified protocol still satisfies traditional secrecy ¨ Might be insecure when used as sub-protocol
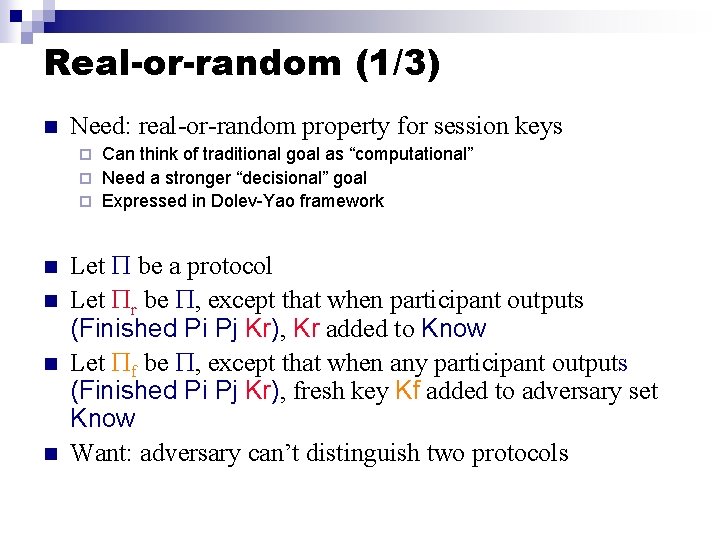
Real-or-random (1/3) n Need: real-or-random property for session keys Can think of traditional goal as “computational” ¨ Need a stronger “decisional” goal ¨ Expressed in Dolev-Yao framework ¨ n n Let be a protocol Let r be , except that when participant outputs (Finished Pi Pj Kr), Kr added to Know Let f be , except that when any participant outputs (Finished Pi Pj Kr), fresh key Kf added to adversary set Know Want: adversary can’t distinguish two protocols
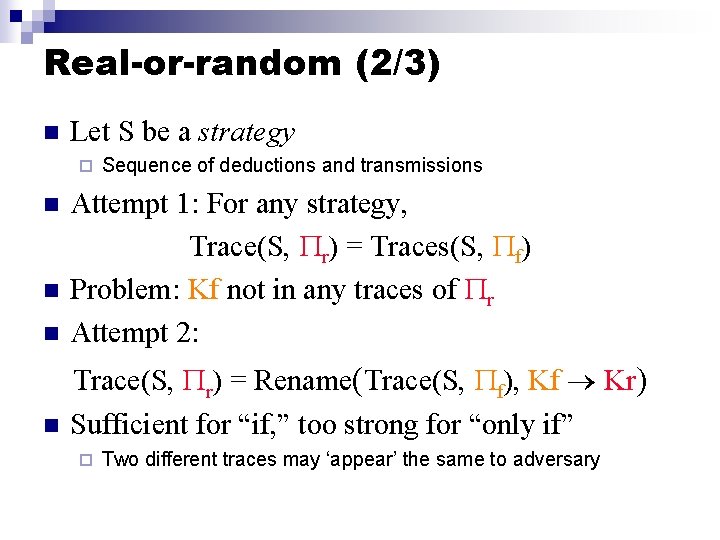
Real-or-random (2/3) n Let S be a strategy ¨ Sequence of deductions and transmissions n Attempt 1: For any strategy, Trace(S, r) = Traces(S, f) Problem: Kf not in any traces of r Attempt 2: n Trace(S, r) = Rename(Trace(S, f), Kf Kr) Sufficient for “if, ” too strong for “only if” n n ¨ Two different traces may ‘appear’ the same to adversary
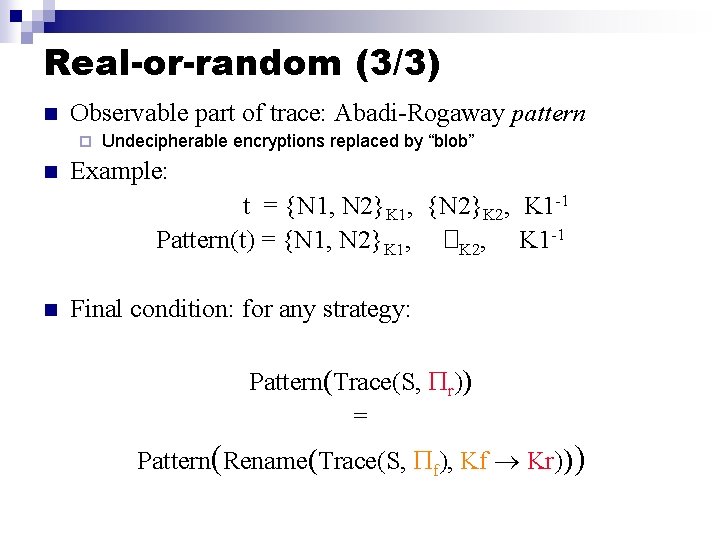
Real-or-random (3/3) n Observable part of trace: Abadi-Rogaway pattern ¨ n Undecipherable encryptions replaced by “blob” Example: t = {N 1, N 2}K 1, {N 2}K 2, K 1 -1 Pattern(t) = {N 1, N 2}K 1, �K 2, K 1 -1 n Final condition: for any strategy: Pattern(Trace(S, r)) = Pattern(Rename(Trace(S, f), Kf Kr)))
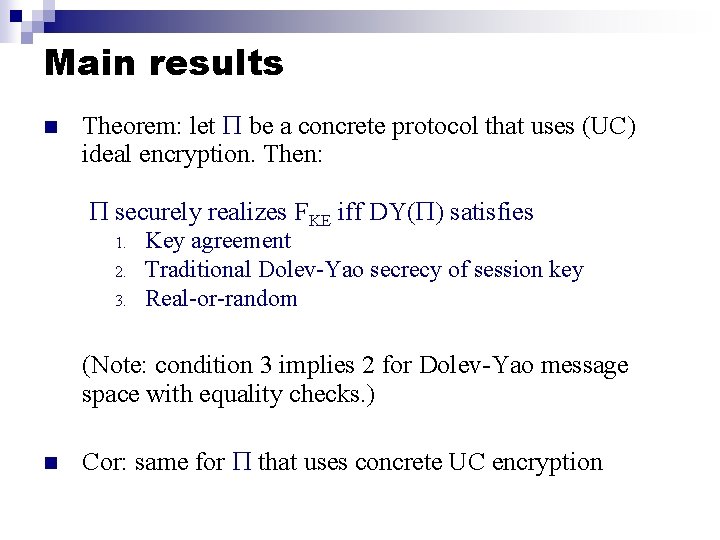
Main results n Theorem: let be a concrete protocol that uses (UC) ideal encryption. Then: securely realizes FKE iff DY( ) satisfies 1. 2. 3. Key agreement Traditional Dolev-Yao secrecy of session key Real-or-random (Note: condition 3 implies 2 for Dolev-Yao message space with equality checks. ) n Cor: same for that uses concrete UC encryption
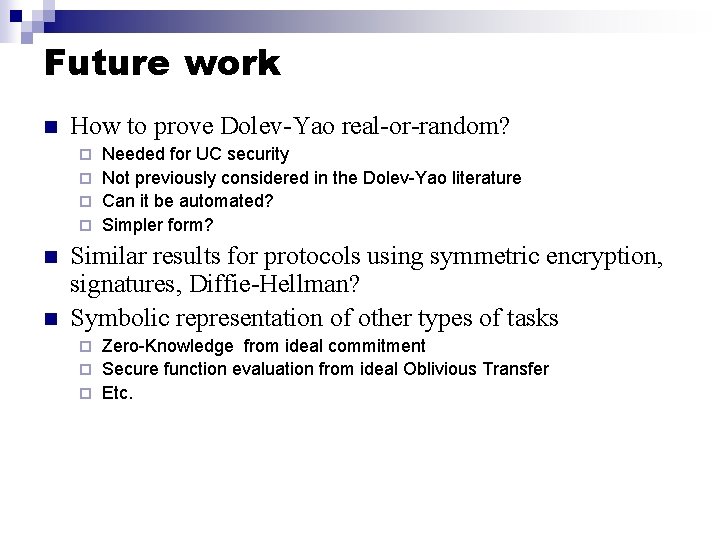
Future work n How to prove Dolev-Yao real-or-random? Needed for UC security ¨ Not previously considered in the Dolev-Yao literature ¨ Can it be automated? ¨ Simpler form? ¨ n n Similar results for protocols using symmetric encryption, signatures, Diffie-Hellman? Symbolic representation of other types of tasks Zero-Knowledge from ideal commitment ¨ Secure function evaluation from ideal Oblivious Transfer ¨ Etc. ¨
Backup-slides
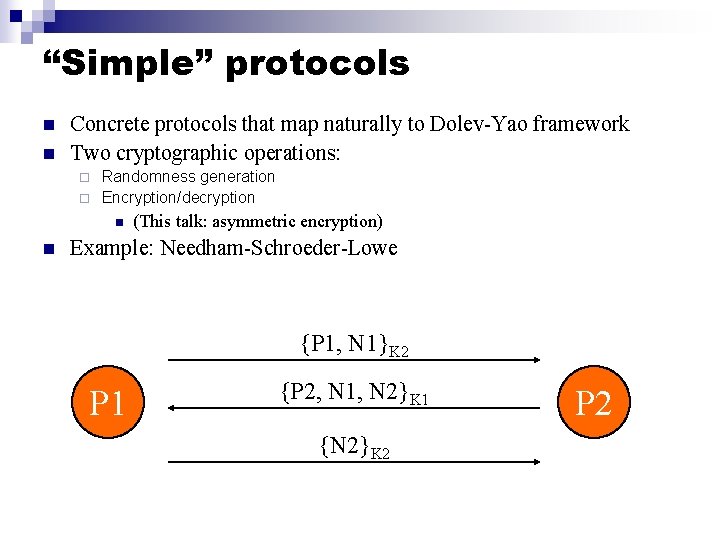
“Simple” protocols n n Concrete protocols that map naturally to Dolev-Yao framework Two cryptographic operations: Randomness generation ¨ Encryption/decryption ¨ n n (This talk: asymmetric encryption) Example: Needham-Schroeder-Lowe {P 1, N 1}K 2 P 1 {P 2, N 1, N 2}K 1 {N 2}K 2 P 2
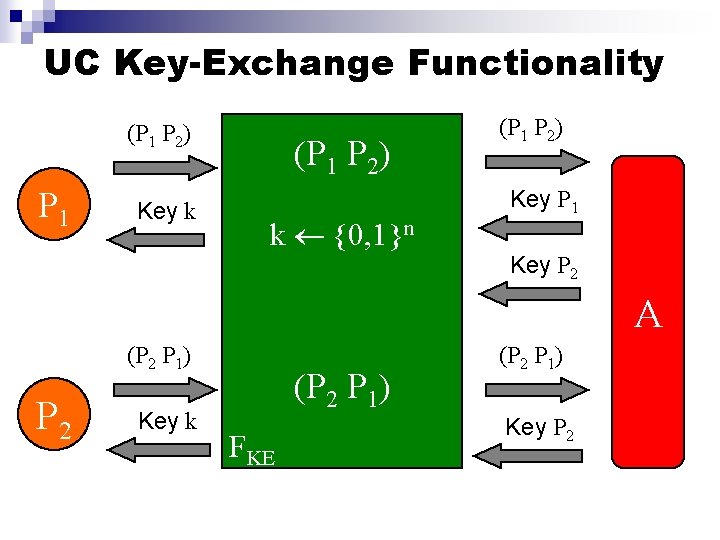
UC Key-Exchange Functionality (P 1 P 2) P 1 Key k (P 1 P 2) k {0, 1}n (P 1 P 2) Key P 1 Key P 2 A (P 2 P 1) P 2 Key k (P 2 P 1) FKE (P 2 P 1) Key P 2
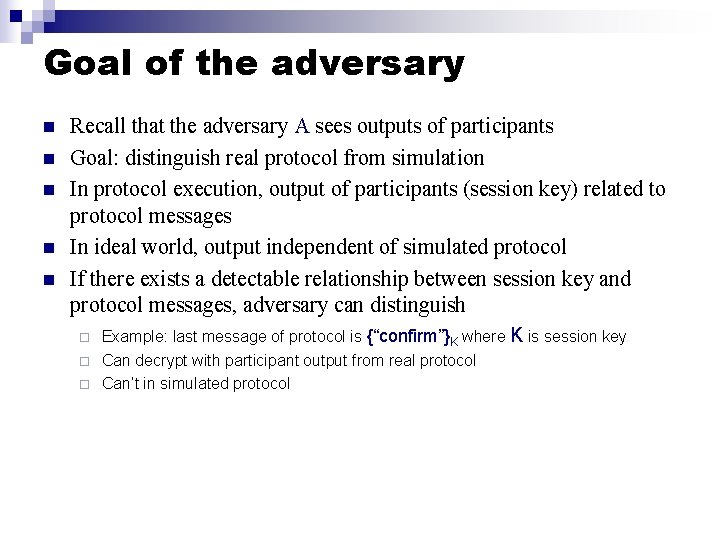
Goal of the adversary n n n Recall that the adversary A sees outputs of participants Goal: distinguish real protocol from simulation In protocol execution, output of participants (session key) related to protocol messages In ideal world, output independent of simulated protocol If there exists a detectable relationship between session key and protocol messages, adversary can distinguish Example: last message of protocol is {“confirm”}K where K is session key ¨ Can decrypt with participant output from real protocol ¨ Can’t in simulated protocol ¨
- Slides: 27