Universally Composable Authentication and Keyexchange with Global PKI
Universally Composable Authentication and Key-exchange with Global PKI • Ran Canetti (TAU and BU) • Daniel Shahaf (TAU) • Margarita Vald(TAU) PKC 2016 Taipei, Taiwan
• Goal: Analyze security of protocols in use. • • Need: Realistic security model Rigorous security definition Security proofs for systems in use
Modular Security Analysis 1. Split the system into smaller components 2. Separately analyze security of each component 3. Need secure composition to argue security of the system Advantages: • Essential for analysis due to protocols complexity • Security guarantee holds for any environment
Focus: security of key-exchange and authentication Our result: Modular analysis of commonly deployed key-exchange and authentication protocols.
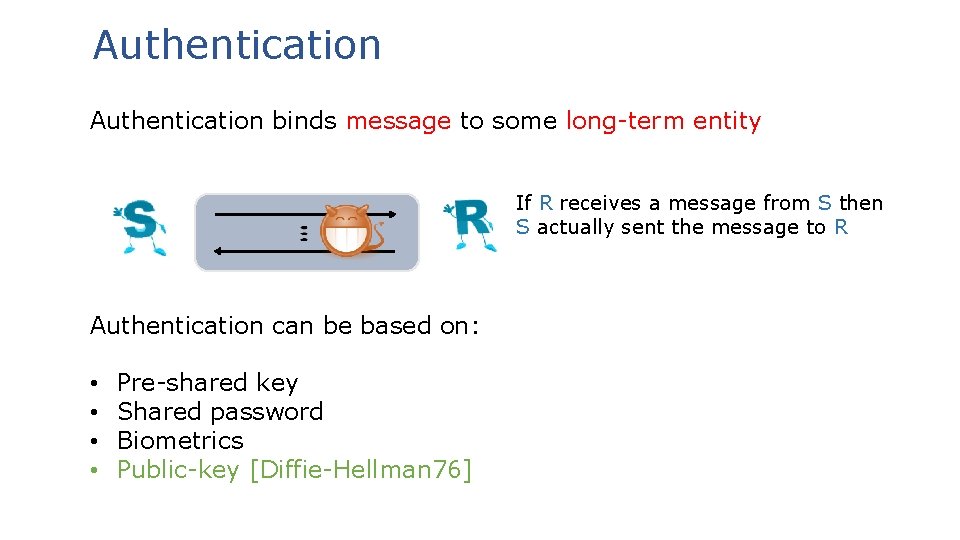
Authentication binds message to some long-term entity If R receives a message from S then S actually sent the message to R Authentication can be based on: • • Pre-shared key Shared password Biometrics Public-key [Diffie-Hellman 76]
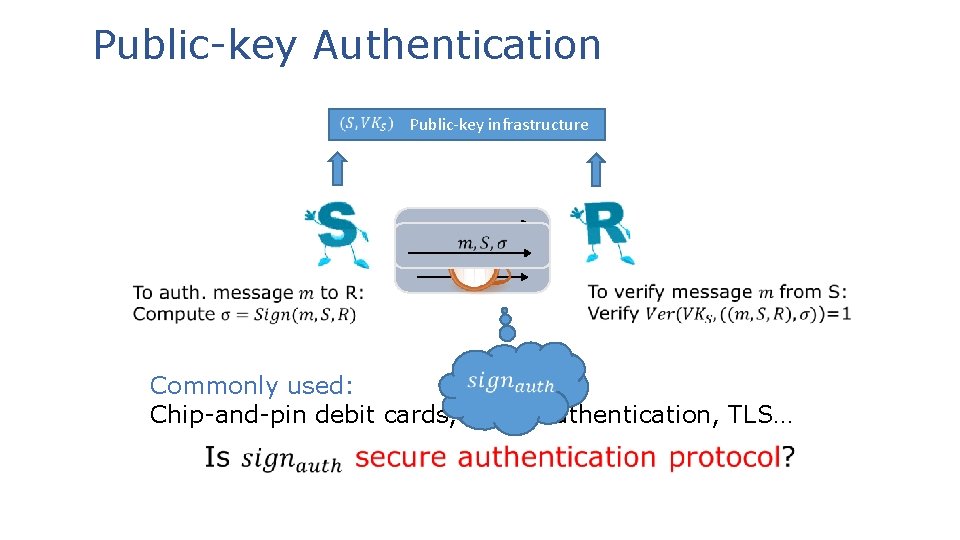
Public-key Authentication Public-key infrastructure Commonly used: Chip-and-pin debit cards, email authentication, TLS…
![Analysis of Public-key Authentication • Game based: [Canetti-Krawczyk 01, Brzuska-Fischlin-Smart-Warinschi-Williams 13] Easy and Limited Analysis of Public-key Authentication • Game based: [Canetti-Krawczyk 01, Brzuska-Fischlin-Smart-Warinschi-Williams 13] Easy and Limited](http://slidetodoc.com/presentation_image_h2/f8cff4c58947ba7acd1bf1dca9b59fc9/image-7.jpg)
Analysis of Public-key Authentication • Game based: [Canetti-Krawczyk 01, Brzuska-Fischlin-Smart-Warinschi-Williams 13] Easy and Limited natural composition definition Win/Lose • Simulation based: Universal Composability and Abstract Cryptography [Canetti-Krawczyk 02, Canetti 04, Maurer-Tackmann-Coretti 13, Kohlweiss-Maurer-Onete-Tackmann-Venturi 14] Ideal auth. General composition
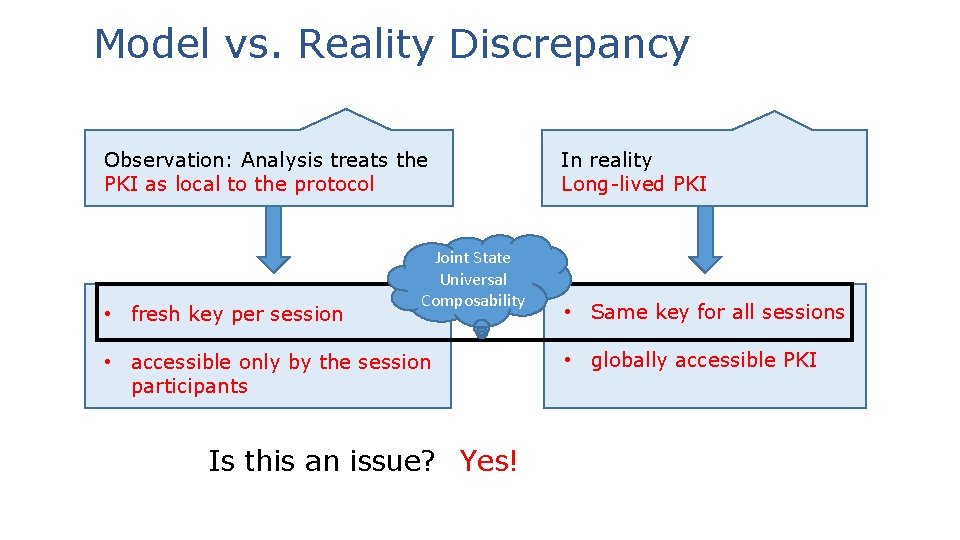
Model vs. Reality Discrepancy Observation: Analysis treats the PKI as local to the protocol • fresh key per session Joint State Universal Composability • accessible only by the session participants Is this an issue? Yes! In reality Long-lived PKI • Same key for all sessions • globally accessible PKI
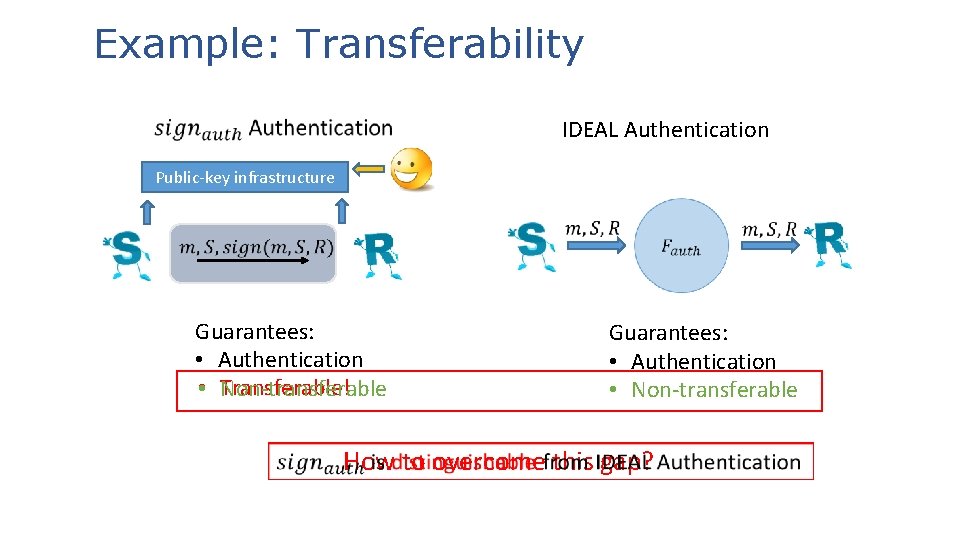
Example: Transferability IDEAL Authentication Public-key infrastructure Guarantees: • Authentication Transferable! • Non-transferable Guarantees: • Authentication • Non-transferable How to overcome this gap?
![Approach #1 • Find new protocols: [Dodis-Katz-Smith-Walfish 09] • Realize non-transferable authentication with globally Approach #1 • Find new protocols: [Dodis-Katz-Smith-Walfish 09] • Realize non-transferable authentication with globally](http://slidetodoc.com/presentation_image_h2/f8cff4c58947ba7acd1bf1dca9b59fc9/image-10.jpg)
Approach #1 • Find new protocols: [Dodis-Katz-Smith-Walfish 09] • Realize non-transferable authentication with globally available setup • Additional cost: assumptions, communication, rounds Is it insecure as a plain authentication protocol?
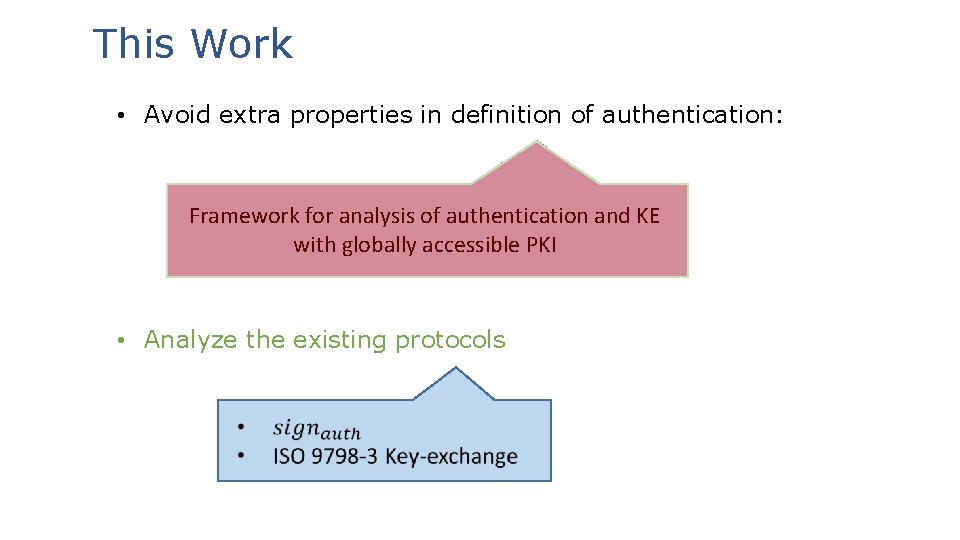
This Work • Avoid extra properties in definition of authentication: Framework for analysis of authentication and KE with globally accessible PKI • Analyze the existing protocols
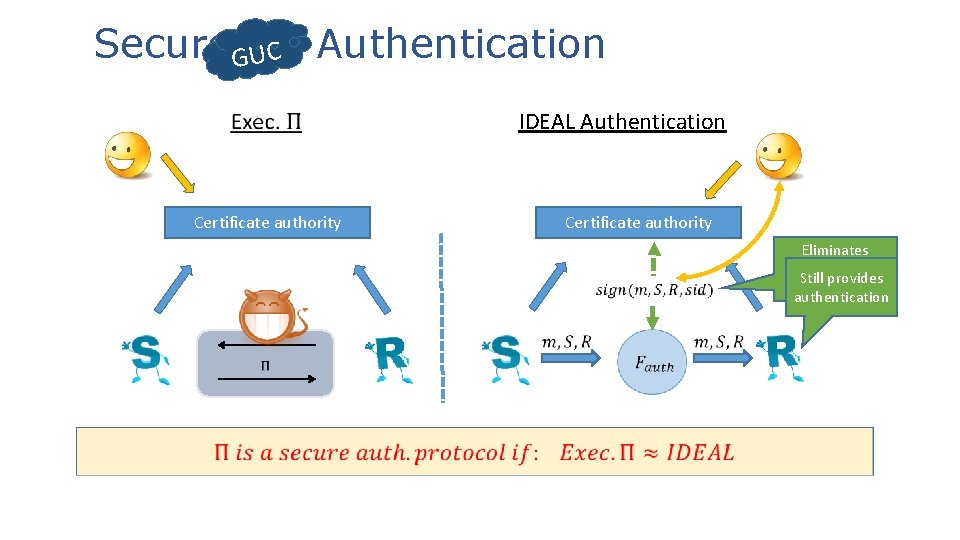
Secure GUC UC Authentication IDEAL Authentication Certificate authority Eliminates non. Still provides transferability authentication
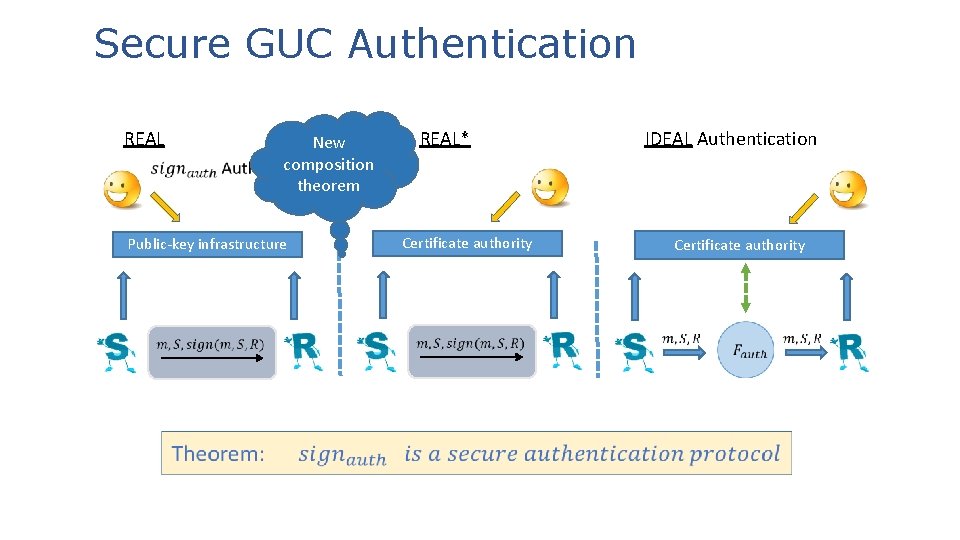
Secure GUC Authentication REAL New composition theorem Public-key infrastructure REAL* Certificate authority IDEAL Authentication Certificate authority
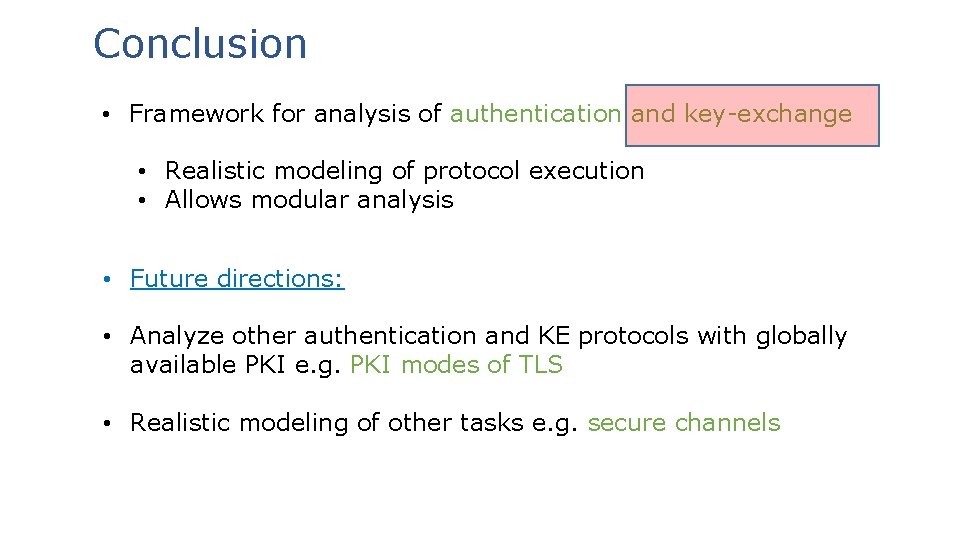
Conclusion • Framework for analysis of authentication and key-exchange • Realistic modeling of protocol execution • Allows modular analysis • Future directions: • Analyze other authentication and KE protocols with globally available PKI e. g. PKI modes of TLS • Realistic modeling of other tasks e. g. secure channels
- Slides: 15