Unit6 Ubiquitous Communication and Management Data Network The
Unit-6 Ubiquitous Communication and Management
Data Network • The early Internet in the 1960 s was based upon several innovations. -Shift from (single tasking) batch computers to (multi tasking) time shared computers. -Shift from PC hub to peer as network. -Shift from analogue to digital communication to maintain a strategic distance from signal degradation crosswise over multi-node netwok. -A network is expected to help high limit and strong network path. -Large data was split into fixed size data packets. -Shift from circuit switched to packet-switched data model.
Network Protocols • Network protocols generally define a fixed length for pieces of data to be transmitted, called the data packet size. • It makes it easier to store and forward data packets when sending and receiving and to transmit data. • Data messages that exceed the fixed length of the data packet size can be split into smaller related individual data packets. This is called data segmentation. • To send and receive content data packets, additional control packets are used such as synchronization and acknowledge data packets
Network Protocols • Each data packet is labelled with the location of an end collector PC node in specific netwok. • So it, enables packets from multiple messages to be interleaved or multiplexed to use the same piece of the network. • Each type of physical network link protocol defines its own type of data packet and multiplexing. • Data packets defined by one data protocol can be tunnelled or encapsulated in other types of data packet.
Addressing • Before starting communication between network elements like computers , they should be allocated network addresses. • In computer networks, network addresses are allocated to networks in logical ranges called subnets. • The special network computer called a router is required to transfer messages across network. • Network addresses consist of two parts: - a (sub) network address - a host computer address.
Address Space Size • IPv 4 supports 32 bit addresses. • IPv 6 supports 128 bit addresses
Routing and Internetworking • Multiple paths may be available between sender and receiver nodes located on different networks which may be interlinked to form an Internet. • Data may be too large to be transmitted. • So split data into multiple packets, that can get transmitted along multiple routes, referred to as data routing. • Routers examine the addresses of data packets to decide whether or not packets should be forwarded to another particular network
Routing and Internetworking • The information to decide where to route packets is defined in routing tables held in the routers. • Routers communicate with each other using specialized routing protocols that provide updates to the routing tables. • One of the most common used routing algorithms is Open Shortest Path First (OSPF). • Each OSPF router broadcasts its routes and in turn requests information about routes that it will connect with.
Routing and Internetworking • Dynamic routing aimed at fixed wired infrastructure networks, where senders and receivers are at fixed locations and where the routing is kept hidden. • Data networks are commonly designed to use a type of simple unreliable Packet Switched Data Network (PSDN) protocol. • e. g. , the IP or Internet Protocol. • IP data packets are mapped or encapsulated into host to network layer data packets.
Routing and Internetworking • A PSDN is unreliable because data can get lost or related data packets can be received out of order. • A PSDN protocol is often used in conjunction with an additional transport layer protocol that provides reliable and sequenced data delivery
Wireless Data Network • Several Benefits of Wireless network: -1. Anywhere: -In contrast to wired networks which can only be accessed at a fixed number of network junctions, wireless networks give users the freedom to access them anywhere. -2. Mobility: -Wireless communication networks can be accessed while moving. -The cost of installing wireless transmitters and receivers typically is much cheaper than a wired network.
Wireless Data Network • 3. Less disruptive: -Wireless networks can be used in areas where wired networks would be considered too inconvenient, disruptive or expensive to install. e. g. , in old historical buildings and in emergency situations. • 4. Adaptivity: -It has ability to expand or shrink the coverage of the network and to vary the density of coverage, installing more transmitters and capacity in high populated in contrast to more rural areas.
Wireless Data Networks • Wireless LANs (WLANs) / Wi. Fi • Wi. MAX • Blue. Tooth • Zig. Bee • Infra. Red (IR) • Ultra Wide Band (UWB) • Satellite and Microwave
Wireless LANs (WLANs) / Wi. Fi • Wireless LANs, also called WLANs are local area wireless networks that adhere to the IEEE 802. 11 set of standards. • It can operate at different frequency ranges and support different message transfer rates. • These standard 802. 11 works in the 2. 4 GHz. • It also operates to a maximum raw data rate of 54 Mbps. • A WLAN network consists of computers with WLAN cards that connect to WLAN access nodes that have a wired connection to an internet.
Wi. MAX • Wi. MAX, the Worldwide Interoperability for Microwave Access, from the Wi. MAX Forum , is proposed as wireless wide area broadband access technology, based upon the IEEE 802. 16 standard, typically offering 10 Mb/s over 10 KM although speeds up to 70 Mb/s are achievable over 10 KM. • The IEEE 802. 11 and 802. 16 technologies are distinguished by their type of medium access control (MAC) whereas 802. 11 MAC uses CSMA (‘listen before talk’) and is connectionless. • The 802. 16 MAC supports full Qo. S, bandwidth on demand, is connection oriented; it supports centralised control and scheduling and offers multimedia support.
Bluetooth • Bluetooth 11 is a standard for short range wireless communication depending on the class of device and power. • Bluetooth applications include both local communication and increasingly local control. • Unlike IR, Bluetooth does not require a line of sight between the transmitter and receiver. • Current popular Bluetooth devices and applications include hands free mobile phone headsets and car kits to support hands free communication when driving and wireless controllers of game consoles.
Bluetooth • Bluetooth uses the same radio frequencies as WLAN but with higher power consumption resulting in a stronger connection. • WLAN requires more set up. • It uses access nodes and is better suited for operating full scale networks because it enables a faster connection, a better range from the base station, and better security than Bluetooth. • Unlike WLAN, Bluetooth does not require much configuration to set up shared resources, transmit files or to set up audio links • for example: headsets and hands free devices.
Zig. Bee • Zig. Bee is a specification for a suite of communication protocols from the Zig. Bee alliance formed in 2002. • It uses small, low power digital radios based on the IEEE 802. 15. 4 standard for Wireless Personal Area Networks (WPAN) • It as a technique in which a node continuously transmits small packets to advertise its presence to other mobile units. • Zig. Bee protocols are intended for use in embedded applications requiring low data rates and low power consumption and low latency. • These protocols used for industrial control, embedded sensing, medical data collection.
Zig. Bee • There are three different types of Zig. Bee device. • 1. A Zig. Bee coordinator (ZC) : -The root of the network tree is formed by ZC and can bridge to other networks. • 2. A Zig. Bee Router (ZR) : -It acts as an intermediate router, passing data from other devices. • 3. A Zig. Bee End Device (ZED): -To have talk with parent node important Functionality is given through ZED.
Infrared • Infrared (IR) is a short range low bandwidth data communication used to communicate between computers and between computer peripherals. • Remote controls and Ir. DA( Infrared Data Association)devices use infrared light emitting diodes (LEDs) to emit infrared radiation which is focused by a plastic lens into a narrow beam. • The beam is modulated, i. e. switched on and off, to encode the data. • The receiver uses a silicon photodiode to convert the infrared radiation to an electric current. • It responds only to the rapidly pulsing signal created by the transmitter, and filters out slowly changing infrared radiation from ambient light.
UWB • Ultra Wideband (UWB) is a technology for transmitting information at data rates exceeding 100 m bits/s, spread over a large bandwidth (>500 MHz) at a low power range, over short distances. • The FCC has authorised the unlicensed use of UWB in the 3. 110. 6 GHz frequency range. • In contrast to conventional wireless systems that need to use baseband signals to modulate radio frequency (RF) carrier signals. • UWB can be used to directly transmit signals at baseband frequencies. • In pulse based UWB, the transmitter only needs to operate during the pulse transmission, producing a strong duty cycle on the radio and minimising baseline power consumption.
Satellite and Microwave Communication • Satellite communication has the potential for truly ubiquitous global communication. • Commercial satellites use parts of the microwave range frequencies for transmission. • Geostationary satellites have the advantage of much simpler antennae design and configuration and a relatively small number of these satellites can be interlinked to provide global coverage. • In the 2000 s, a major use of satellite communication is for wide area TV video broadcasts although is also being challenged by cable networks. • An important use of satellite communication is to serve very large numbers of thin routes, which cannot economically be served by cable.
Audio Networks • Audio networks were the first types of pervasive communications Networks. • There are two basic types: -Audio unicast networks (PSTN). -Audio broadcast (radio) networks.
PSTN(Public Switched Telephone Network) Voice Networks • Public Switched Telephone Network (PSTN) are designed to support voice communication. • It used analogue transmissions but this has been replaced by digital transmission. • Many workplaces use separate networks for voice and data although there is a progression towards combined voice, data and audio video networks. • Telephones act as access devices to the PSTN and are typically connected to a private circuit switched network or Private Branch Exchange (PBX). • Individual home users tend to be connected to a PSTN using a single line local loop to a local switching station
PSTN(Public Switched Telephone Network) Voice Networks • The PSTN can also be accessed using fixed or mobile phones. • Many users also use the PSTN as an access network to data exchange networks, i. e. , the Internet. • PSTNs used circuit switching to interlink different network links to form an end to end connection. • Network links were used exclusively by pairs of callers when they are online. • PSTNs were designed to be very resilient. • The circuit switching used in telecoms networks typically uses a hierarchy of about five levels of switching offices that handle particular number ranges
Intelligent Networks (IN) • The earliest types of digital telecommunication networks were designed to support specific services using specialised logic contained in specialised switching network elements. • Any new features or services proposed have to be added and implemented directly in the core switch systems which led to very long introduction times for new services. • The Intelligent 4 Networks (IN) network service model, standardised by the ITU T enables Telcos to offer new value added and customised voice services such as toll free calls, e. g. , ‘ 0800’ numbers. • This supports independent component based services in general purpose computer nodes rather in special switching nodes. • This enables service providers to drive new services rather than network providers
Information Multimedia Subsystems (IMS). • IMS was originally developed for 3 G wireless networks. • Users access IMS using IP. • A key challenge is application layer control (signalling) protocol for controlling voice/video session, multimedia conference, messaging and Presence over IP. • The multiple media transmission control can be performed using the IETF SIP (Session Initiation Protocol). • The basic entities in a typical SIP system involve: • -a series of mediators where users sign in and are authenticated. • - location servers are used to track user locations. • - presence servers detect if users are active. • - proxy servers and redirect servers assist in call forwarding. • - an MCU or multi point control unit mixes multimedia streams
Information Multimedia Subsystems (IMS). • SIP can use three different types of MCU: -1. full mesh: In a full mesh, every participant builds a signalling path with every other participant and sends an individual copy of the media stream to the others this only scales to very small groups. -2. Mixer: A mixer or bridge takes several media streams and replicates them to all participants. -3. Multicast: Neither full mesh nor mixers scale to large conferences, hence a network layer multicast is used to support this.
ADLS Broadband • Asynchronous Digital Subscriber Line (ADSL) transmission technology can be used to increase the transmission capability over existing physical. • e. g: copper wire PSTN type, access networks. • It does this by exploiting the fact that audio telephony signals require only about a 3 k. Hz bandwidth but a typical line can transmit usable signals up to approximately 1 MHz. • The signal to noise ratio for transmissions is more dependent on distance. • However, Digital Signal Processing (DSP) can be used to support signal modulation commonly based upon Discrete Multi Tone (DMT) an international standard, and Carrierless Amplitude modulation Phase modulation (CAP) to encode signals for improved transmission and then to recover the original signals
Wireless Telecoms Networks • To support access anywhere for mobile or cell phone users, wide area wireless telecoms networks have been established. • Different networks depending on geographic region and on the Generation (G) of the wireless network such as 1 G analogue and 2 G digital. • These differ primarily in the way they are designed to share access to the wireless network among different users. • Global System for Mobile Communications (GSM) is a 2 G. • Code Division Multiple Access (CDMA) is another 2 G digital cellular network system mainly used for cell phones. • DECT(Digital Enhanced Cordless Telecommunications)is been deployed to access wireless spoken language at intervals areas.
Audio Broadcast (Radio Entertainment) Networks • Several benefits in using audio broadcasting or radio: -It supports one sender to many receivers. -It supports a multi modal interface that allows humans to listen to music and voice while engaged in many everyday physical world activities. - e. g. , driving a vehicle. - Radio (and TV) receivers are designed to handle and tune into receive a wide spectrum of RF broadcasts on multiple channels.
Audio Broadcast (Radio Entertainment) Networks • Digital radio has been introduced as a replacement for analogue radio. • For digital radio, the Eureka 147 Digital Audio Broadcast (DAB) standard is most commonly used and is coordinated by the World DMB Forum. • DAB uses the MPEG 1 Audio Layer 2 audio (MP 2) codec for audio broadcasting while personal players use the MP 3 codec. • The main original objectives of DAB were: -1. To provide radio at CD quality; - 2. To provide better in car reception quality than using FM analogue radio; - 3. To use the spectrum more efficiently; - 4. To allow tuning by the name of the station rather than by frequency; and -5. To allow data to be transmitted.
Ubiquitous Networks • Wireless Networks • Power Line Communication(PIC). • Personal Area Networks. • Body Area Network. • Mobile Users Networks.
Power Line Communication(PIC). • Power Line Communication (PLC) is an alternative way to ubiquitously access data and audio video content. • Power line connection conducts electricity to deliver energy that can modulate electricity as a signal and be used as a channel to communicate data and audio video content. • PLC describes a range of systems for using electricity distribution wires for simultaneous distribution of data. • The carrier can communicate voice and data by superimposing a modulating signal over the standard 50 or 60 Hz alternating current (AC). • This can be used in home automation for remote control of lighting and appliances without the installation of additional control wiring. • e. g. , X 10 and the Home. Plug powerline alliance.
Personal Area Networks • Wireless Personal Area Networks (WPAN) have been specified by the IEEE P 802. 15 working group • A Personal Area Network (PAN) is normally confined to a person or object that typically extends up to 10 meters in all directions and envelops two or more objects or persons whether stationary or in motion. • The WLAN standard was initially considered for extension but was dropped because of its higher power requirements and its higher network management over head. • Bluetooth, Zigbee and IR are examples of systems that can be used to implement a PAN.
Personal Area Networks • Typical applications include: -Multi network phone depending on network access (intercom, cordless phone and cell phone). -Mobile Internet access on the move. -Interactive local conferencing to instantly exchange information. - Hands free head set to communicate and (voice) control and - Automatic synchronisation of information for mobile users.
Body Area Networks • Consists of a set of mobile and compact intercommunicating sensors that are either wearable or implanted into the human body. • A typical BAN application can monitor vital body parameters and movements • E. g. , monitor EEG, ECG, and EMG signals. • Data Management? -Either to store them in some device on the body for later upload analysis -To periodically transmit data in real-time via some external network interface
Mobile Users Networks. • Not all network access by mobile users, applications and devices need be via wireless networks and vice versa. • Wireless access devices can be static and mobile users can move in between wired or wireless hotspots such as in Internet cafes. • Mobility refers to mobile applications in which users are free to continuously move anywhere within range of a wireless network. • Portability refers to a mobile device that is stopped or suspended during the roaming itself but attached at discrete access points, intermittently. • This is useful for mobile office type scenarios when users work at multiple locations, e. g. , at a central business premises, at customer premises and at home.
Service-Oriented Networks • Different application services were coupled to specific networks because different applications need different levels of support for data transmission functions, such as latency sequencing, performance and reliability, channel sharing, data control and security. • It is simpler to design networks to support one specific set of application requirements rather than to support multiple applications that have different messaging requirements because these may conflict. • Nowadays, services are oriented to be coupled less to specific networks and to be available across heterogeneous networks. • To use a service, users must subscribe to a particular network and service configuration on the network. • e. g. , voice calls via a telecoms network and audio video content via an audio video wireless broadcast network
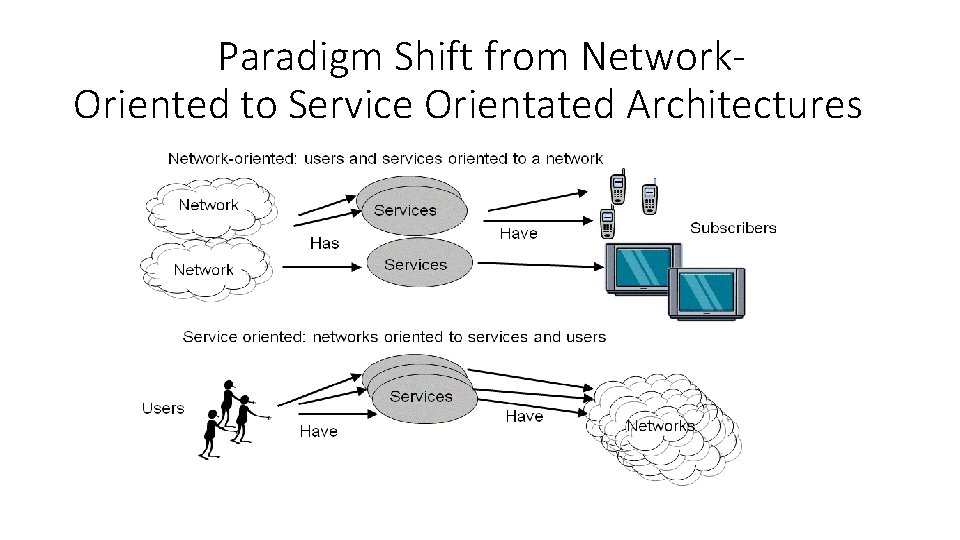
Paradigm Shift from Network. Oriented to Service Orientated Architectures
Service-Orientation: in Edge Network • A simple abstraction of a network topology to support universality is to partition a communications network into two parts: -an access network or edge network -a core network. • Access networks, is the network that users and application use to access the network. • The core network comprises the interlinked networks that then link to the access networks.
Service-Orientation: in Edge Network • Important design decision is whether or not to put the complexity or intelligence for service specific communication: • into the core network, • e. g. , PSTN • Or in the edge network • Or in both • e. g. , IP networks.
Service-Orientation: in Edge Network • There is an argument for end to end or edge based complexity and to keep the core network relatively simple to optimise the core network only to forward and route data packets. • The main argument is that ‘functions placed at low levels of a system may be redundant or of little value when compared with the cost of providing them at that low level. • This implies that a simple and as neutral as possible network should be used.
Content-based Network • A content based network is a communication infrastructure in which the flow of messages through the network is driven by the content of the messages, rather than by linking specific senders to specific receivers. • With this communication pattern, receivers subscribe to the types of content that are of interest to them without regard to any specific source. • Senders simply publish information without addressing it to any specific destination. • In a content based network, nodes are not assigned unique network addresses. • Data is not addressed to any specific node or node group. • Instead, each node advertises a receiver predicate (or r predicate) that defines data of interest for that node that the node intends to receive.
Programmable Networks • Typically, service providers do not have access to the router, e. g. , the router controls environments algorithms and router states, in order to optimise network use for different applications. • This makes the deployment of new network services, which could be far more flexible than proprietary control systems, impossible due to the closed nature of network nodes. • Programmable networks allow some of the network elements to be reprogrammed dynamically: - By injecting executable codes that could support application specific services, into network elements such as routers and switches.
Programmable Networks • Drawback: Complexity increases and there is an increasing risk of instability and for malicious code to take control of core network elements. • 2 main initiatives to establish programmable networks: -1. DARAPA’s Active Networks (AN) program -2. The Open Signalling (Opensig) community. • Opensig approach seeks to establish open programmable network interfaces. • AN approach is to support injecting executable code into network elements to reprogram them.
Overlay Network • An overlay network is a virtual network built on top of a physical network that provides a (virtual) infrastructure to one or more applications. • It handles the forwarding and handling of application data in ways that can differ from or in competition with the basic underlying physical network such as the Internet or PSTN. • It can be operated in an organised and coherent way by third parties, which may include collections of end-users.
Overlay Network • Benefits: - New communication services can be introduced - Increasing costs and the need for coordination of the Internet service providers all over the world. • Another issue is that different applications may need different levels of reliability, performance and latency and security and access control. • Nodes in the overlay network are connected by virtual or logical links. • Application specific overlay networks can be incrementally deployed on end hosts running an overlay protocol
Mesh Networks • In a full mesh network topology, every network node is connected using point-topoint connections to every other one. Cons? -connecting every node to every other node is costly to wire and costly power wise to transmit to each other. • Hence, in practice, mesh networks are usually partial mesh networks, in which each node is not connected to every other node. • Partial mesh networks tend to combine ring and star based network topologies.
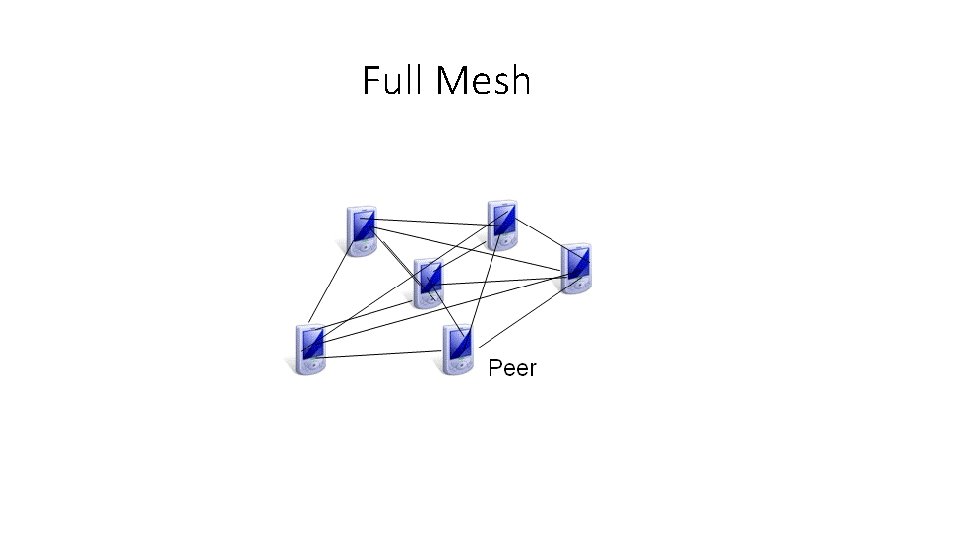
Full Mesh
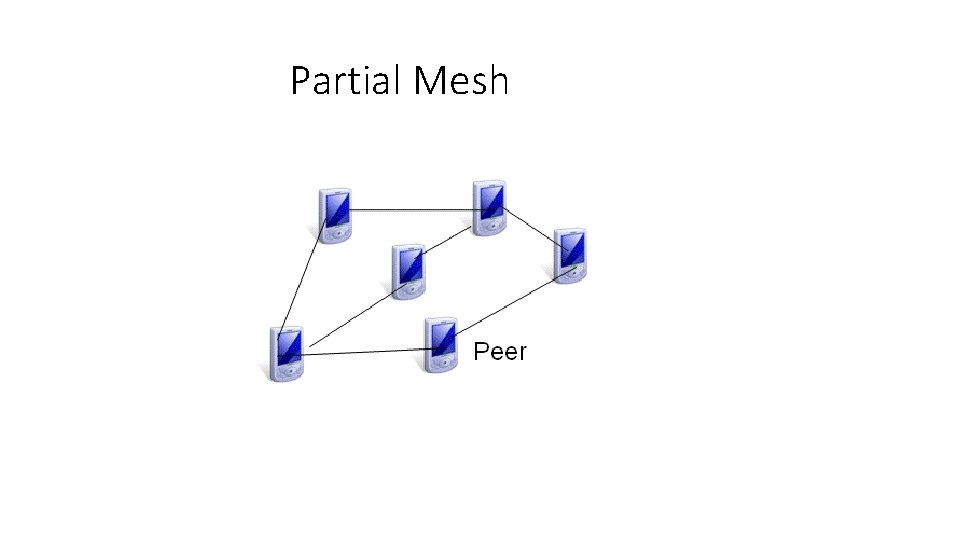
Partial Mesh
Wireless Mesh Networks (WMNs) • Wireless Mesh Networks (WMNs) are partial mesh, adhoc, networks that can significantly improve the performance, at a lower cost and at a lower power output compared to other types of WLAN. • WMN is lower power because it uses a set of lower power multi-hop transmissions rather than needing a single more powerful transmission to base-station. • It may be a suitable solution in rural areas where conventional base-station wireless type network support or DSL support maybe patchy.
Wireless Mesh Networks (WMNs) • In WMNs, each node operates not only as a host but also as a router (mesh– clients), forwarding packets on behalf of other nodes that may not be within direct wireless transmission range of their destinations. • In addition, dedicated mesh routers which contain additional routing capabilities and bridging and gateway function to other networks. • WMN can also dynamically self-organise and self-configure mesh connectivity to support ad hoc multi-hop networking.
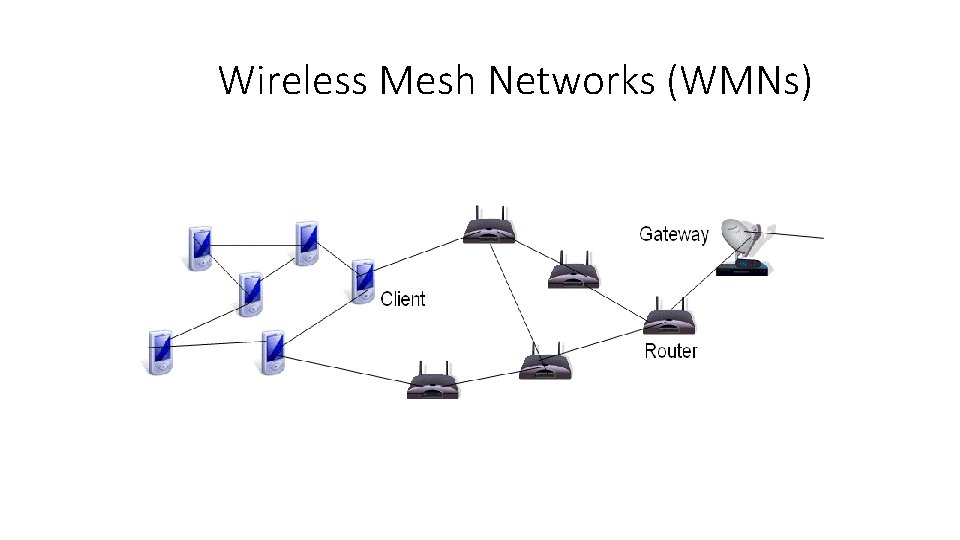
Wireless Mesh Networks (WMNs)
Characteristics and benefits of WMN • Multi hop wireless network: extends coverage range without sacrificing the channel capacity, without a direct line of sight (LOS) link. • Ad hoc networking: supports self forming, self healing, and self organisation for multipoint to multipoint communications enabling the network to grow gradually as needed. • Mobility dependence on the type of mesh nodes: mesh routers mobility, while mesh clients can be stationary or mobile nodes. usually have minimal • Multiple types of network access: both backhaul access to the Internet and peer to peer (P 2 P)communications are supported.
Characteristics and benefits of WMN • Mesh routers usually do not have strict power consumption constraints and may not be appropriate for some types of mesh clients, those that act as sensors in a sensor network where power consumption is the primary concern. • WMNs are compatible and can be integrated with multiple IEEE 802. 11 (Wifi) type networks.
Cooperative Networks • Some network access devices cannot access multiple networks in order to communicate, they just have access to one network connection. • Some other network access devices have inbuilt support for heterogeneous network access. - e. g: to Bluetooth, to Wi. Fi and to GSM networks. • Cooperative communication is designed to enable single antenna mobile access devices to reap some of the benefits of being Multiple Input Multiple Outputs (MIMO) systems. • A specific problem that cooperative communication can solve at the physical media layer concerns signal fading because thermal noise, shadowing due to fixed obstacles and due to signal attenuation can vary significantly over the course of a given transmission. .
Network Design Issues • Network Access Control. • Controlling Network Access: Firewalls, NATs and VPNs. • Group Communication: Transmissions for Multiple Receivers. • Internetworking Heterogeneous Networks. • Separating Management and Control from Usage. • Ubiquitous versus Localised Access • Global Use: Low-cost Access Networks for Rural Use.
Network Access Control. • Different networks use a range of access control techniques to handle network resource allocation problems and to allow multiple users to access network media that has a limited capacity. • GSM is designed to use Time Division Multiple Access (TDMA) to share access among multiple users. • In TDMA, several users can split the transmission time into a slot per channel. • Wireless networks such as 3 G are designed to use much more efficient multi access methods such as Wideband Code Division Multiple Access (WCDMA) that can support higher bandwidths.
Network Access Control. • WLANs support sharing frequencies between many active users. • Many simultaneous users may cause packet collisions and waste channel bandwidth. • So the packet collisions should be avoided. • Therefore WLANs typically use a MACA (Multiple Access with collision Avoidance )type transmission protocol. • Another option is to use a Carrier Sense Multiple Access with Collision Detection (CSMA/CD) network control protocol in which a carrier sensing scheme is used. • Here if a sender detects another signal while transmitting data, it stops transmitting its data, transmits a jam signal, 24 and then waits for a random time interval before trying to send its data again.
Ubiquitous Versus Localised Access • Networks may also be designed to support only local access by organisations, to serve only particular populations of users and applications and not to be accessed remotely across a wide area. • Some services that only serve a local area, e. g. , local restaurants that only serve customers that visit it, may advertise only to local customers. • Services can be restricted to local access because they are only available on wired local networks that are situated in buildings or because they are offered on wireless local area networks and because they need to be kept internal by an organisation. • Local services can also be designed to have access control to enable them to be accessed remotely and securely by a closed group of users, operating as Virtual Private Networks or VPNs.
Ubiquitous Versus Localised Access • For networks to support ubiquitous access, it seems logical to use Wide Area Networks or WAN. • Even if these are actually constructed out of large numbers of distinct networks that are internetworked. • There at least three major types of WAN: 1. The wired and wireless based Internet, 2. Wireless satellite networks and the 3. Wired and wireless telephone networks. • These use different protocols and manage internetworking differently.
Controlling Network Access: Firewalls, NATs and VPNs • A firewall is a router or special purpose computer that monitors all packets entering and leaving network and filters packets. • Firewalls can be designed according to which level of the network they work. • 1. Packet level firewall. • 2. Application level firewall. • Packet level firewalls examine and filter data packets according to the IP or Transport layer address. • Application level firewalls require users to log on in to the firewall computer before they can access any other network elements.
Controlling Network Access: Firewalls, NATs and VPNs • Network Address Translation (NAT) is a computer that acts as a proxy to translate IP addresses inside a network, keeping them private, to other IP addresses that are visible outside the network. • VPNs essentially allow users to establish a lower layer virtual channel or virtual circuit for exchanging data packets, but hidden from, high level applications. This is called tunnelling. • Multiple heterogeneous applications may use the same tunnel. • These lower layer packets are said to be tunneled through or to overlay the public network. • Packets are usually encrypted when they are tunneled to prevent the content (data packets) from being intercepted and examined by unauthorized users.
Controlling Network Access: Firewalls, NATs and VPNs • Users normally authenticate themselves at a VPN client or access devices in order to gain access to remote resources via the VPN tunnel. • There are several types of VPN tunnel used, depending on the type of network layer packets are tunnelled through, the type of encryption used and the type of access control to the VPN used.
Group Communication: Transmissions for Multiple Receivers • Sending the same message from a single source to a defined group of multiple receivers, multicast communication or group communication can be used in order to share information within a group • e. g: a conference. • There may be hardware support for multicast so that large group messages can be sent efficiently. • In unreliable multicast, messages are transmitted to all members without acknowledgement. • In reliable multicast, the message transmission makes the best effort to deliver to all receivers in the group: it may be delivered to some but not all nodes. • In atomic multicast, a message is either received by all receivers or none of them.
Internetworking Heterogeneous Networks • Ideally, universal access means that any type of data may be accessed simultaneously anywhere over any kind of network. • Historically, many separate types of communication network exist that are not interlinked. • Networks are heterogeneous in terms of the physical media that electromagnetic signals propagate through. • e. g: signals may propagate through wired copper or optical fibre networks or through wireless or Over The Air (OTA) networks. • Networks are heterogeneous in terms of the types of content or media they exchange, such as video, audio and (alphanumeric) data.
Internetworking Heterogeneous Networks • Currently, separate networks are still predominantly used to distribute audio (voice and music), video and data. • Networks are heterogeneous in terms of the types of applications that use them, in terms of their architecture or topology and in terms of how the individual networks are interlinked and managed. • It seems useful to design and standardise specifications to interlink a heterogeneous internetwork in such a way that it acts as a universal network for applications and users. • Universal networks have been specified for Internets based upon the Transmission Control Protocol / Internet protocol suite or TCP/IP and for wireless and mobile use, Universal Mobile Transmission Service or UMTS based upon the 3 rd generation mobile phone technology.

- Slides: 69