UNIT 7 ORGANISATIONAL SYSTEMS SECURITY TASK 3 CYBERSECURITY
UNIT 7: ORGANISATIONAL SYSTEMS SECURITY TASK 3 – CYBERSECURITY Created by: Ma. Johann Aniya Lugue
Security Policies and Guidelines
Disaster recovery policies This policy is significant to a company so management needs to prioritise the planning process as it could give a competitive advantage to the company in times of incidents. This is needed to Disaster recovery developed and implemented that will policies help the company recover IT systems, applications, data and information. This policy is managed by the IT Management Staff, this person’s job is to make sure that the plan is implemented, tested and kept updated.
Updating of security procedures This is important as threats, virus, hacking, fraud and more are produced every day. If these malicious actions entered the company’s server it will have a big chance that the important information that is stored inside the server such as personal details and financial statements will be accessed and stolen by unknown users. However, if the company update the security procedures this will make the information stay confidential and secured.
Scheduling of security audits An audit is like a test that is done to the computers and other devices to see if they are properly working, if they aren’t the company could fix or replace them. This is also significant for better working environment as this audit are always running, if the audit stop a big chance of hidden problems inside the computers and other devices will not be resolved that will affect the performance of the company.
Codes of conduct Every company should have their code of conduct as this composed of the organisation’s mission, visions and values. The code is the main basis of the employees, as it defines the desired behavior and this could help the performance of the company as this is the central guide and an everyday guide of the employees. Email usage policy This policy sets the standard responsibility of the employees in terms of using email in their day to day work. Internet usage policy This policy provides the rules and guidelines for the employees in terms of using the equipment, network and internet access. This helps the company because this can protect the confidentiality of the company. This also can make awareness to the employees so that they will not browse sites and download files that is prohibited to the company.
Installation Policy Installation of programs including downloadable files can easily get fast-spreading security vulnerabilities. the purpose of this policy isto make sure that everyone that will use and can get an access to the devices and internet of the company should agree to follow the guidelines of this policy. Software Acqisition This is the process to select an software and put it into operation that is virtually presents problems inn an organisation, it can be as a whole organisation, department or in an individual.

Surveillance policies This policy controls the installation and operation of surveillance technologies like video surveillance cameras, facial recognition technology, fingerprint recognition and tracking systems.
Risk management This is a process of identifying, assessing and controlling threats to an organisation’s earnings. These risks could be in different sources that can include the financial uncertainty, legal liabilities, strategic management errors and natural disasters. The significance of this to the company is, if they properly implement this plan and considering the potential threats before they occur could make the organization save money, this could help the company protect its future.
Budget setting Budgeting is a process of making a plan to spend money. This is important as this plan will ensure the company will always have enough money for certain things that is to be needed.

Employment contracts and security
Hiring policies This policy is a statement on how to employ. This composed of the company’s preferred hiring practices and gives consistency within the employee hiring process.
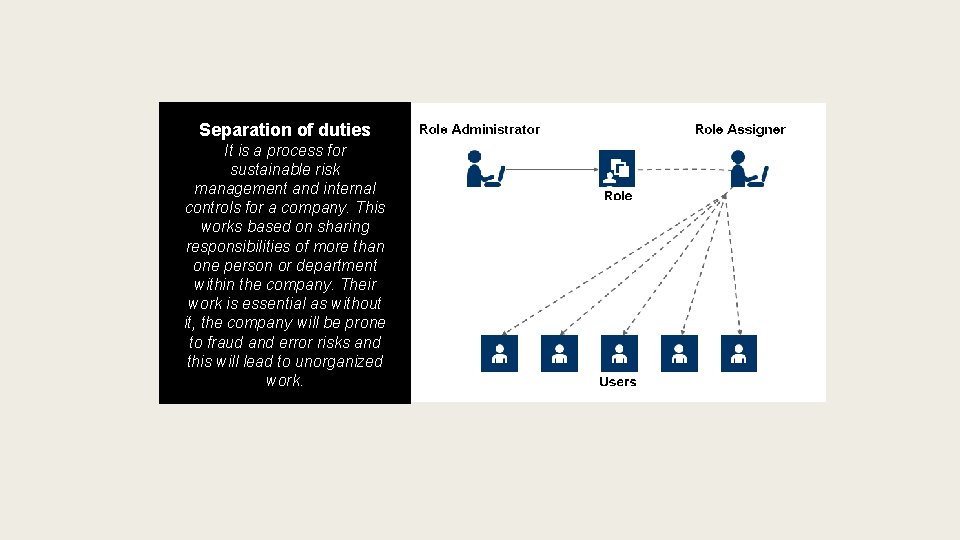
Separation of duties It is a process for sustainable risk management and internal controls for a company. This works based on sharing responsibilities of more than one person or department within the company. Their work is essential as without it, the company will be prone to fraud and error risks and this will lead to unorganized work.
Ensuring compliance Disciplinary Procedures It should say what behaviour might lead to disciplinary action and what action your employer should take. It should also include the name of someone you can speak to if you do not agree with your employer’s disciplinary decision. Your employer can also put their disciplinary procedures in your employment contract. If your employer does this and then does not follow these procedures you could sue them for breach of contract. Training and communicating with staff as to their responsibilities Within the company, employees are expected to do trainings in order to be able to perform their role to a good standard. As the employer, it is a responsibility to provide this training, whether it comes in form of a course, meeting, demonstration is purely circumstantial.

Laws
Legislation: Computer Misuse Act 1990 This is a law that deals with the crime of unauthorised access on the stored data on the computer system. There are three offences of this law; looking at someone else’s files without their permission, an intent move like hacking to make criminal offences and writing a virus to destroy someone else’s data are considered to be a crime.
Copyright, Designs and Patents Act 1988 This gives every author or creator the exclusive right to copy or reproduce including electronic storages like downloaded files, to transmit a copy like uploading a material on the web, to adapt materials including the translation or editing and to rent or lend copies. The copyright starts the moment the work is made. Unpublished works are also protected with copyrights and the works also granted with moral rights to protect their owner’s reputation.
Privacy and compensation requirements of Data Protection Act: 1984 “An Act to regulate the use of automatically processed information relating to individuals and the provision of services in respect of such information. ” The Data Protection Act 1984 introduced basic rules of registration for users of data and rights of access to that data for the individuals to which it related. 1998 “An Act to make new provision for the regulation of the processing of information relating to individuals, including the obtaining, holding, use or disclosure of such information. ” The Data Protection Act 1984 is a governing law, the process of personal data in all organisations, can be public or private and including charities. This is also regulated the use of personal data and give the responsibilities to protect the data to the company. 2000 Our new Data Protection Act makes our data protection laws fit for the digital age in which an ever increasing amount of data is being processed. Also, to empower people to take control of their data supports UK businesses and organisations through the change ensures that the UK is prepared for the future after we have left the EU.
Copyrights
Freeware software This is a software distributed to users with no cost. The copyright holders have the right to distribute their work copies but the copyright law will not allow them to give it with a price, so in this case it will be free. However, the users of these freeware software may not be changed and sold to others.

Shareware software This is a software that is protected by the copyright law. This provides the user the chance to use the application for free before buying it or not. This can be a limited version of the real one and it is also restricted by license. The license restricts the user from changing, copying or distributing anything in the software in any way. Any of those said is done will be considered as piracy.
Commercial software This is a software that is developed for license or sale to give a commercial purpose to users for them to use it. This is the total opposite of Freeware.
Ethical Decision Making
Freedom of information versus personal privacy Freedom of information, this is the action that requires public organisations give their own public information. This affects IT security in a company as if someone request for information, the other needs must give it because of this act. This is related to ethics as in this way people can express their feelings into words that is given by the government laws. On the other hand, Personal Privacy is the action where you able to make your personal information stays hidden to yourself. The advantage of this to the company is that the personal information of the employees stay within themselves that it will not be able to be used for malicious acts like blackmail or frauds. This is related to ethics as this way personal data can be protected and it will assure the confidentiality rights of the people.
PERMISSION Use photographs or videos Photographs, illustrations and other images will generally be protected by copyright as artistic works. This means that a user will usually need the permission of the copyright owner(s) if they want to perform certain acts, such as copying the image or sharing it on the internet. Before taking any photos or films, you should ensure the people them are aware that they are being photographed, who is taking the pictures, what they will be used for, and who they will be shared with. You should also tell people who they should contact if they do not want to be photographed, or if they want their images deleted later. Display clear signs at your event which specifically explain all this. Use CCTV Footages CCTV footage is admissible as evidence in a court of law, and widely used by police in their investigations, getting hold of CCTV footage can make all the difference for those involved in legal proceedings. Under the Data Protection Act 1998, you have the right to request CCTV footage that relates to you or your property, as this may reveal personal information about you and will therefore be classed as personal data. You are able to request footage from private individuals, companies and public authorities. However, if the footage is needed for the detection and investigation of a crime, or you are concerned that a camera is being used for harassment or anti-social purposes, this can only be handled by the police.

Professional Bodies (Different Organisations)

Business Software Alliance (BSA) This is a company that advocates for the global software industry with more than 30 countries operating. The members of it are from the world’s most innovative companies and their aim is to create software solutions that will make a brighter economy and to make improvements of modern life.
Federation Against Software Theft (FAST) This company was formed in 1984 and was the world’s first organisation to promote the legal use of software and to defend the intellectual property rights of software publishers. They work to raise awareness of the value of intellectual property of the UK economy in both revenue and employment. They are known to be “the software police” because of ts anti-piracy work. The members including the law enforcement communities helps together to detect and fight the possible misuse or underlicensing of software. The Federation is a not-forprofit organisation limited by guarantee and wholly owned by its members.

British Computing Society (BCS) This company is a charity with a royal charter and the aim to support individuals who work in IT and to lead the industry through its ethical challenges. They give support and provide professional development opportunities in careers, they share expertise through knowledge-sharing and collaborations with other companies, they are improving education where they give the right computing skills and understanding to their students, they work with different industries to shape policy and practice of education and they also drive standards as they raise the levels of professionalism and performance across IT. its members cares about the professional development and work to build a great digital future for everyone.
Association of Computing Machinery (ACM) This company is employed with computing educators, researchers, and professionals to inspire dialogue, share resources, and address the field's challenges. It is the world’s largest computing society that strengthens the profession’s voice through strong leadership, promotion of the highest standards, and recognition of technical excellence. It also provides opportunities for its members with life‐long learning, career development and professional networking.
Conclusion Security policies are important in an organisation as this play a big role to protect physical and information technology assets. This gives provisions regarding the training programs to raise security information awareness, response practices when an incident happens and different requirements to protect the whole IT infrastructure. To be effective, the policies must be accurate, updated and professionally realistic. Misleading of these policies might bring a big impact to the company as it may lost costumer commitments which mean breaking the cycle of money in the company. To improve these policies, companies should always manage the people that will have the access of the policies. Identify which department or employee needs to be instructed by this laws. Always protect your most important data. Time to time, always remember to save your work and place it in a safe place in the computer and remember to make a copy of it. The policies should be updated so that It will provide better security to all the data and information.
- Slides: 31