Unit 4 Freeware Security Tools Use Freeware Tools
![IP Filter Log Format Jul 30 01: 46: 52 myhost. vt. edu ipmon[147]: [ID IP Filter Log Format Jul 30 01: 46: 52 myhost. vt. edu ipmon[147]: [ID](https://slidetodoc.com/presentation_image_h2/250a20f9582bec6e90d74168b0e49b47/image-50.jpg)
- Slides: 121
Unit 4: Freeware Security Tools Use Freeware Tools to help evaluate commercial tools OR “you have more tools than you think” Educause MARC, 2003 Copyright 2002, Marchany
The Layers of Security w Policy w Awareness w Risk Analysis w Incident Response w Free Tools Educause MARC, 2003 Copyright 2002, Marchany 2
Suggested Strategy w Use freeware tools to gain experience with your system/network environment. w Gain experience with the features provided by these tools in order to better analyze a vendor tool. w Freeware tools provide a good short-term solution. w Vendor tools may provide better long-term solution. Educause MARC, 2003 Copyright 2002, Marchany 3
The Tools w Audit/Port Scanning Tools n n n Nessus Saint Sara Nmap, strobe Tripwire, AIDE w “Personal” Firewall n n n TCP Wrappers Portsentry, ipfilters Zone. Alarm, Black. Ice, Neo. Works Educause MARC, 2003 Copyright 2002, Marchany 4
The Tools w Syslog Scanners n Logcheck w Sniffers n n n Snoop, iptrace, tcpdump Netwatch (NT) Snort Educause MARC, 2003 Copyright 2002, Marchany 5
The Tools w Sysadmin Tools n n Big Brother Password Checkers l n n Crack, nt-crack, l 0 phtcrack, npasswd, passwd+ Lsof, inzider (NT) Sudo (unix) w Remote Control Tools n VNCviewer w Homegrown Tools Network Mgt Tools that can be used for Incident Response Educause MARC, 2003 Copyright 2002, Marchany n 6
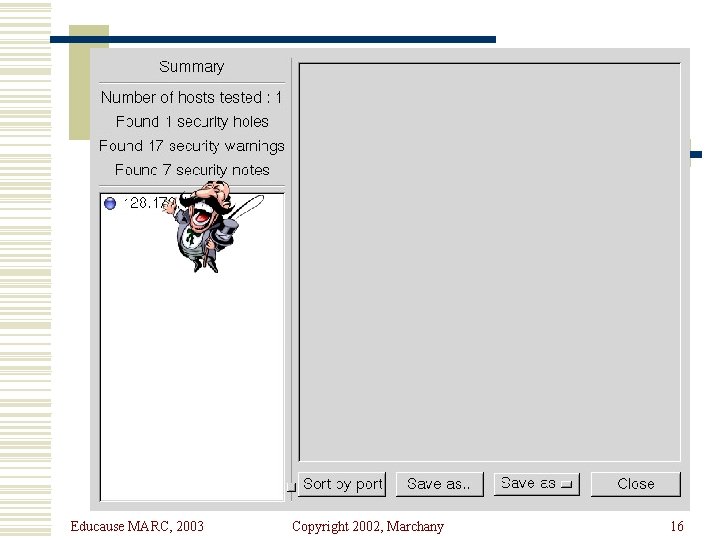
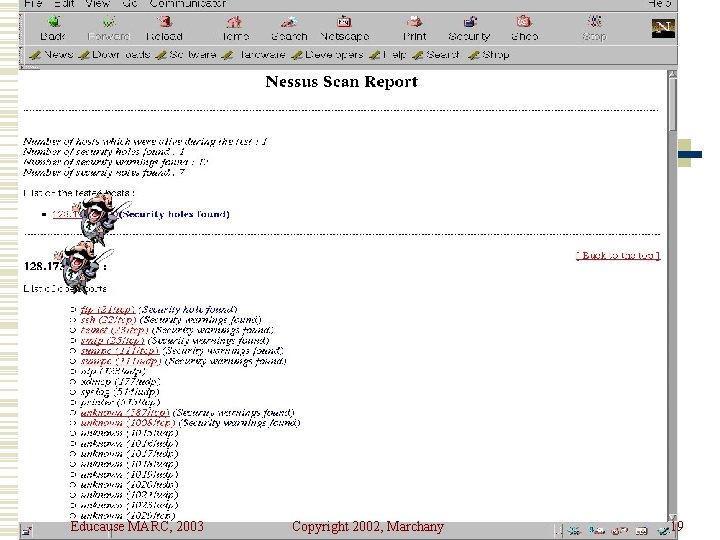
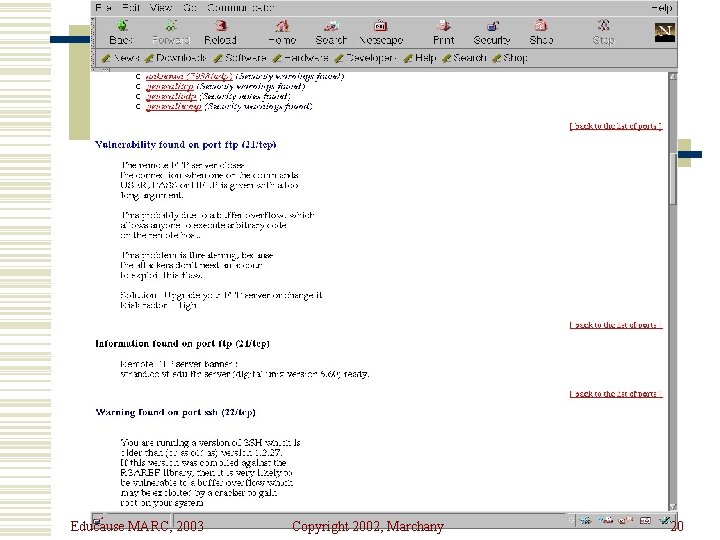
Audit/Port Scan Tools w These tools can be used to scan your systems and network for vulnerabilities. w Some tools can perform integrity checks on designated files. w They have very good reporting tools usually based on HTML. Educause MARC, 2003 Copyright 2002, Marchany 7
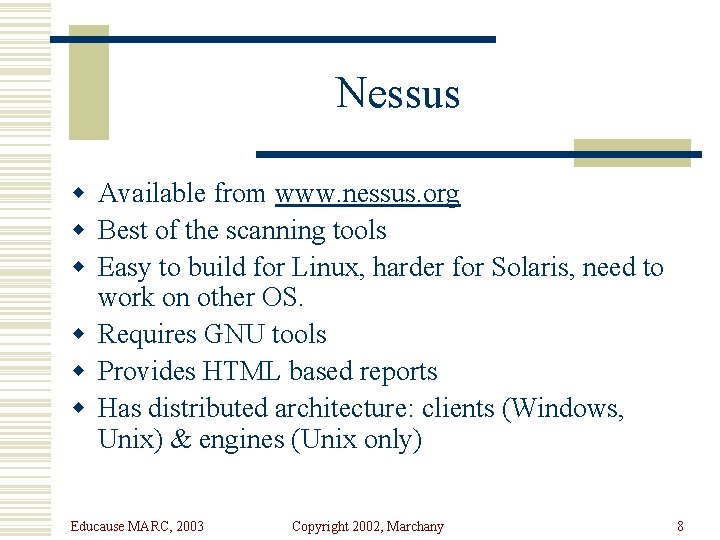
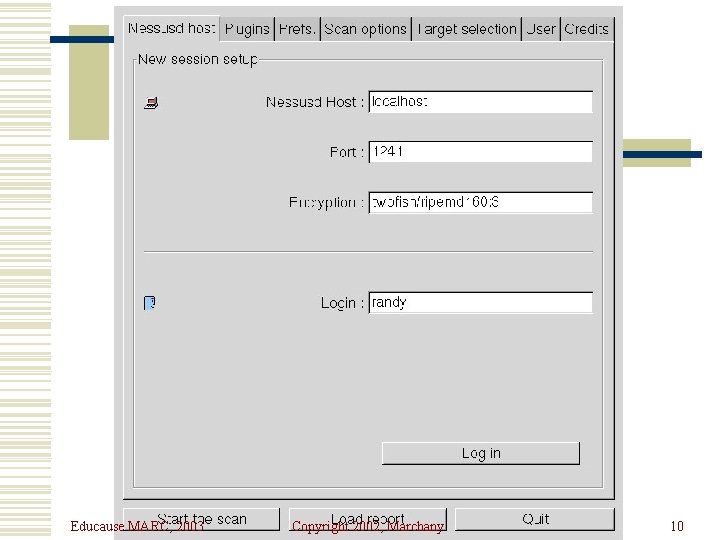
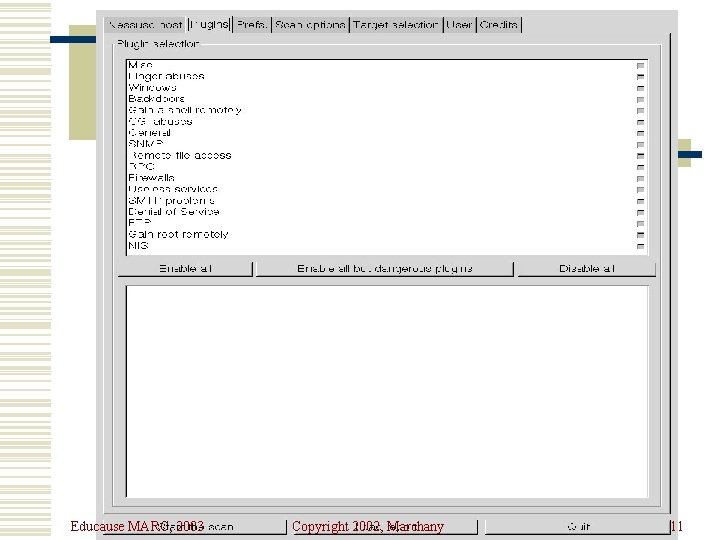
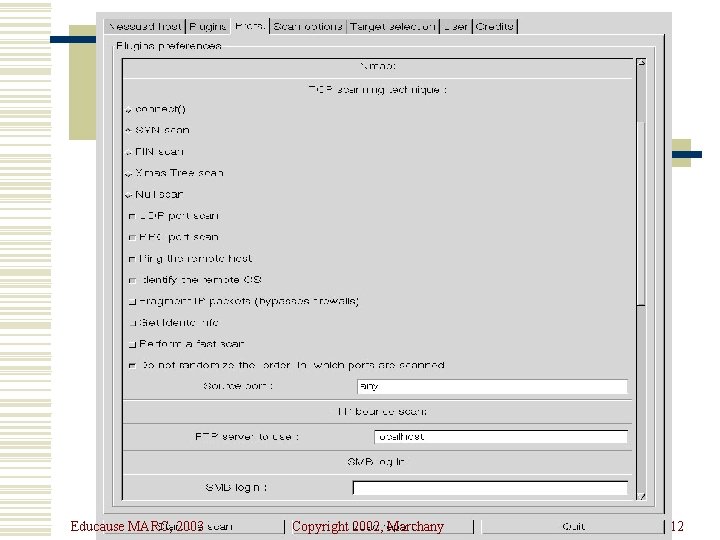
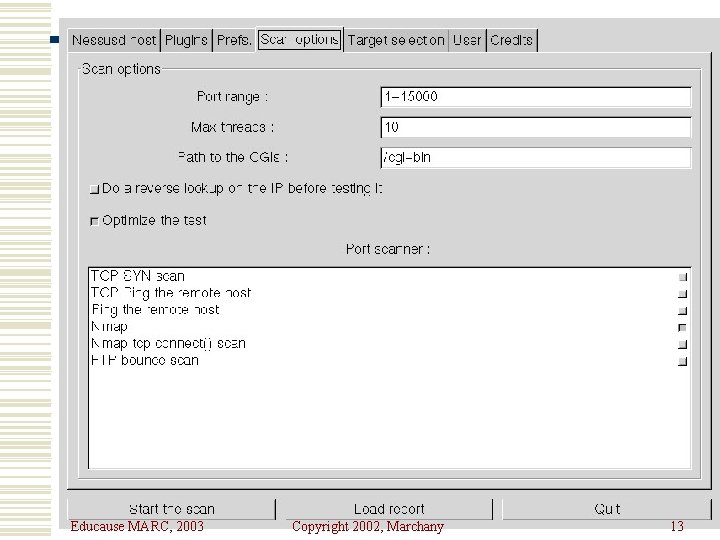
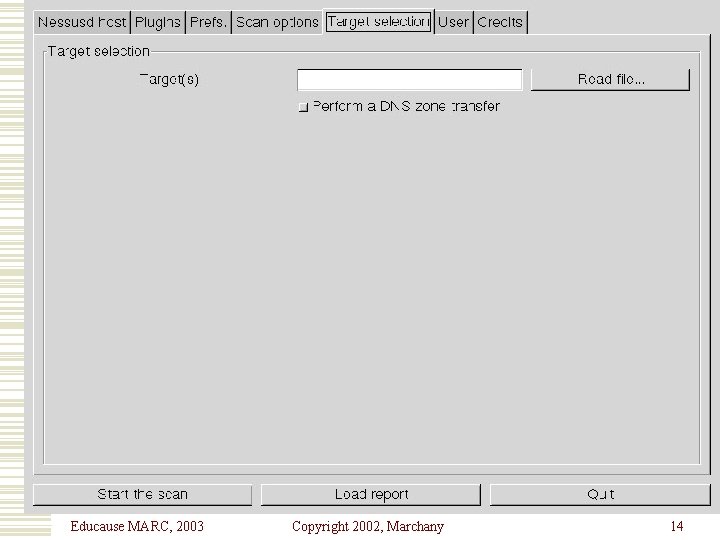
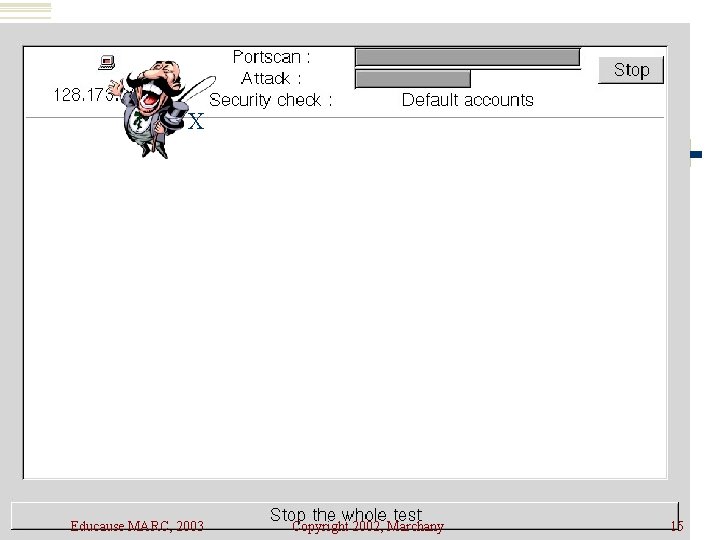
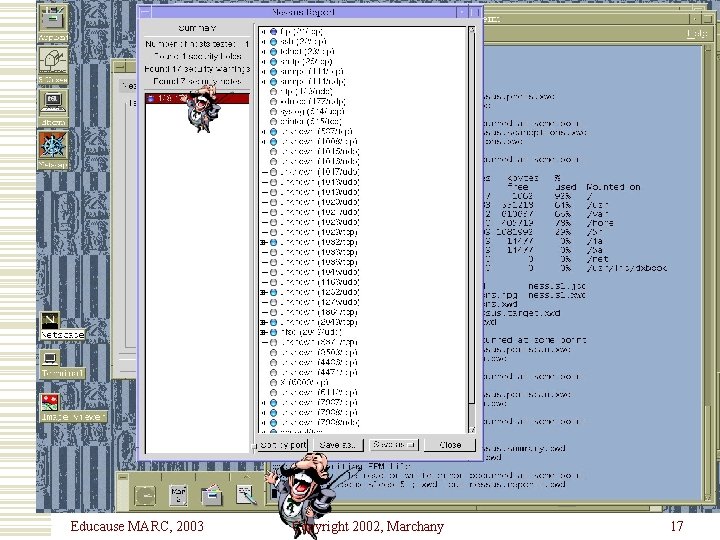
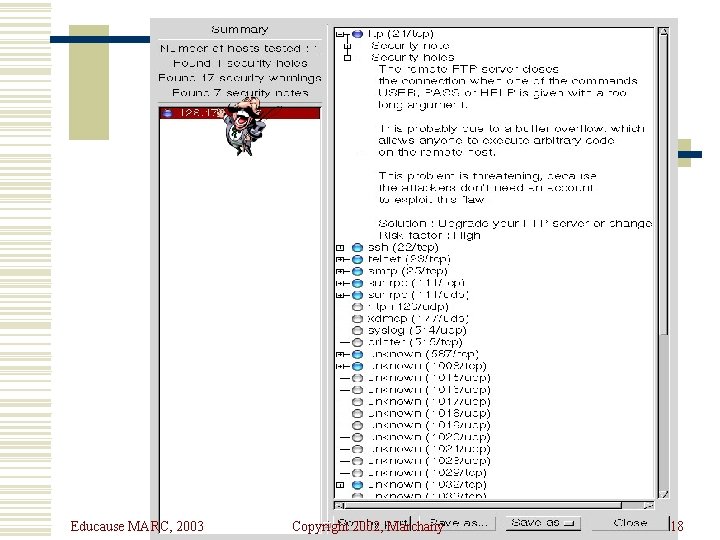
Nessus w Available from www. nessus. org w Best of the scanning tools w Easy to build for Linux, harder for Solaris, need to work on other OS. w Requires GNU tools w Provides HTML based reports w Has distributed architecture: clients (Windows, Unix) & engines (Unix only) Educause MARC, 2003 Copyright 2002, Marchany 8
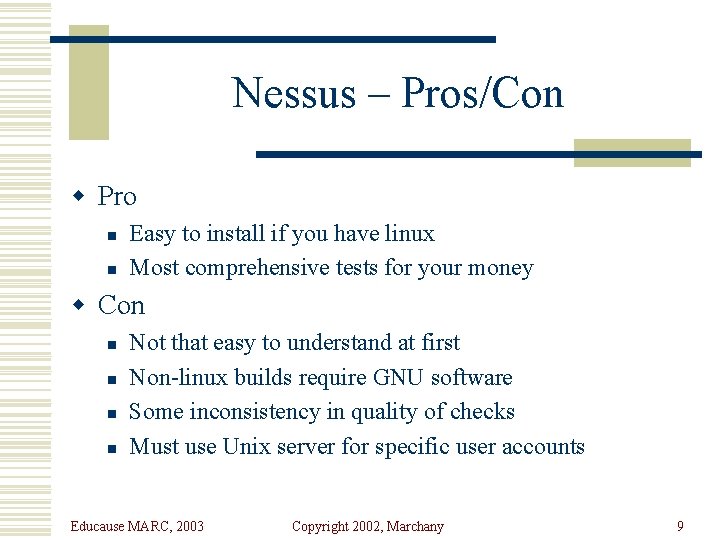
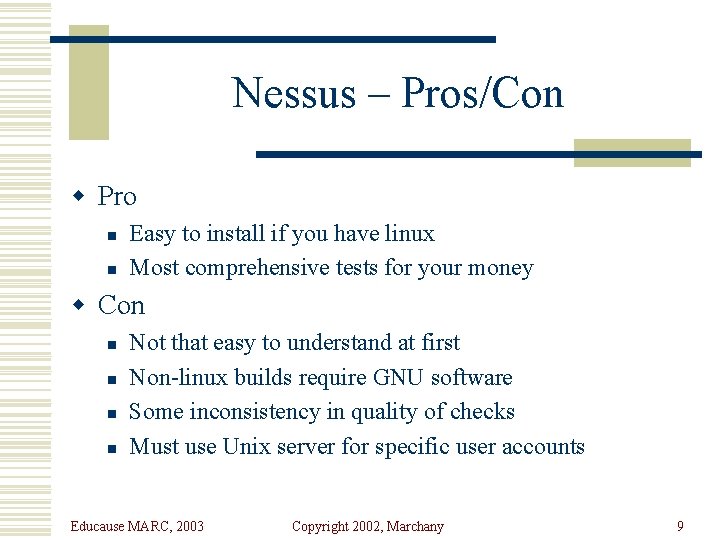
Nessus – Pros/Con w Pro n n Easy to install if you have linux Most comprehensive tests for your money w Con n n Not that easy to understand at first Non-linux builds require GNU software Some inconsistency in quality of checks Must use Unix server for specific user accounts Educause MARC, 2003 Copyright 2002, Marchany 9
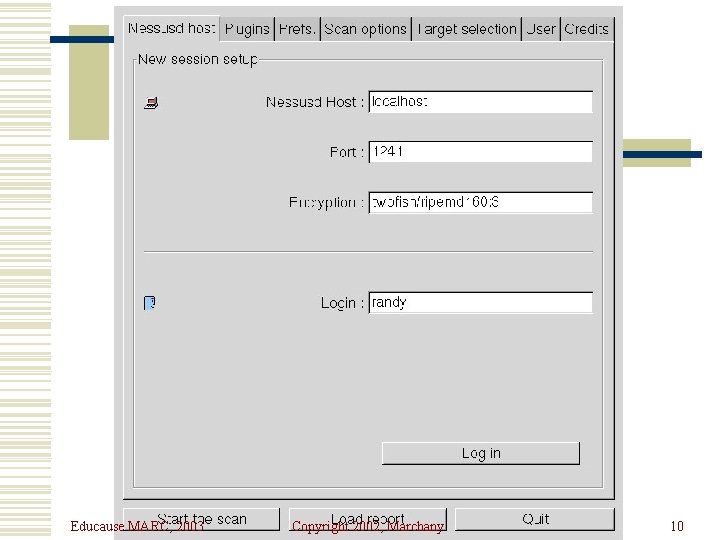
Educause MARC, 2003 Copyright 2002, Marchany 10
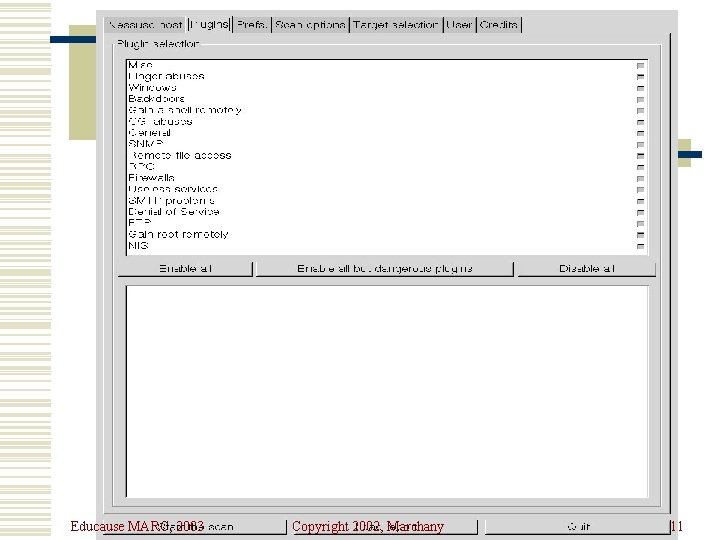
Educause MARC, 2003 Copyright 2002, Marchany 11
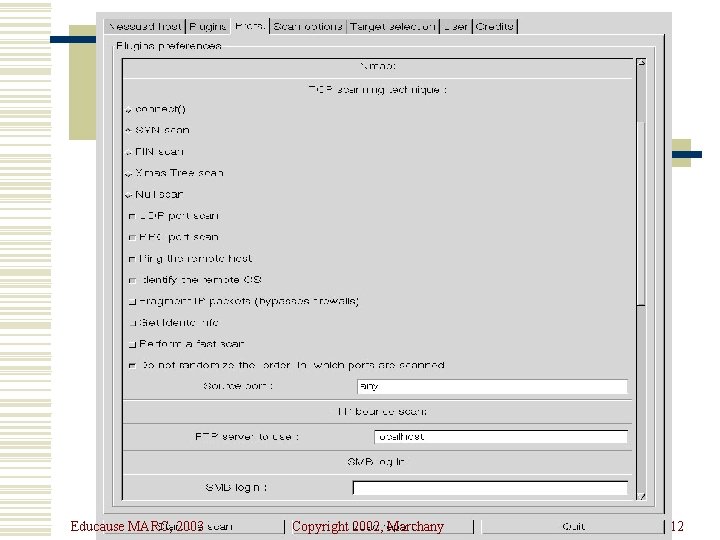
Educause MARC, 2003 Copyright 2002, Marchany 12
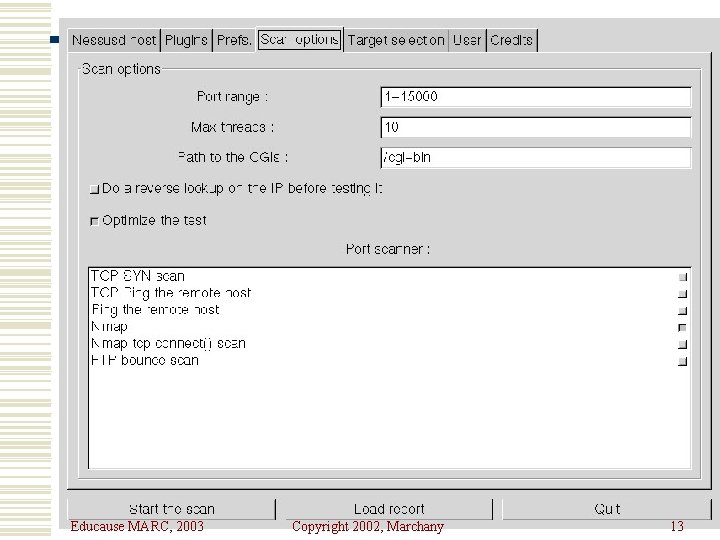
Educause MARC, 2003 Copyright 2002, Marchany 13
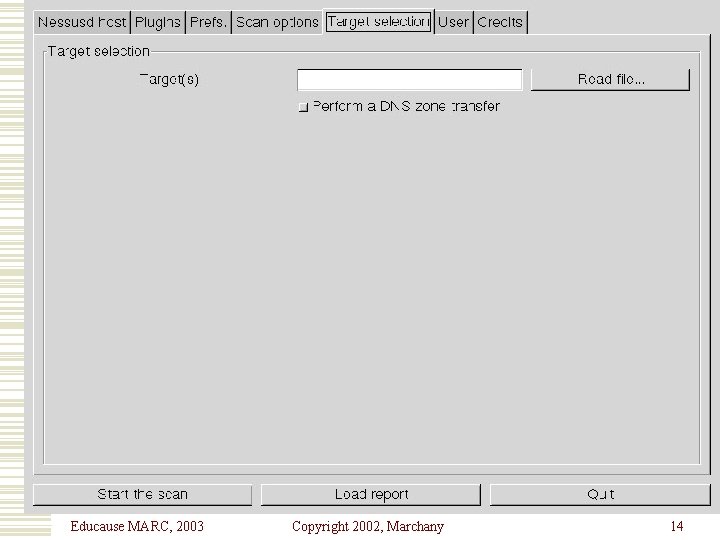
Educause MARC, 2003 Copyright 2002, Marchany 14
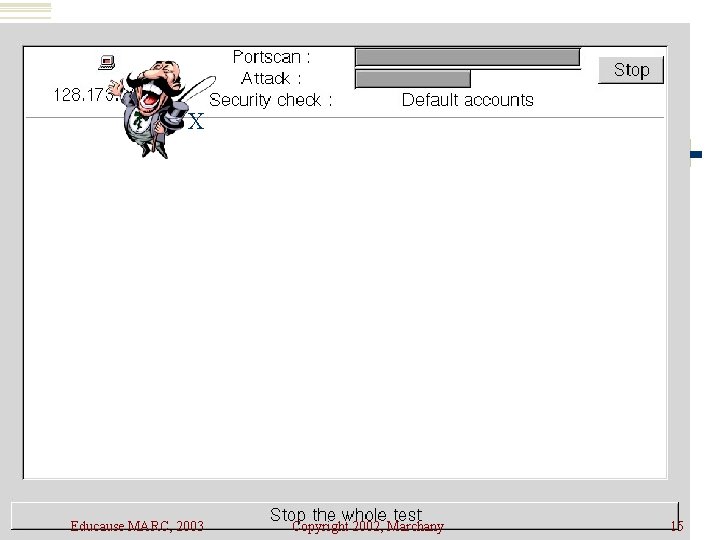
X Educause MARC, 2003 Copyright 2002, Marchany 15
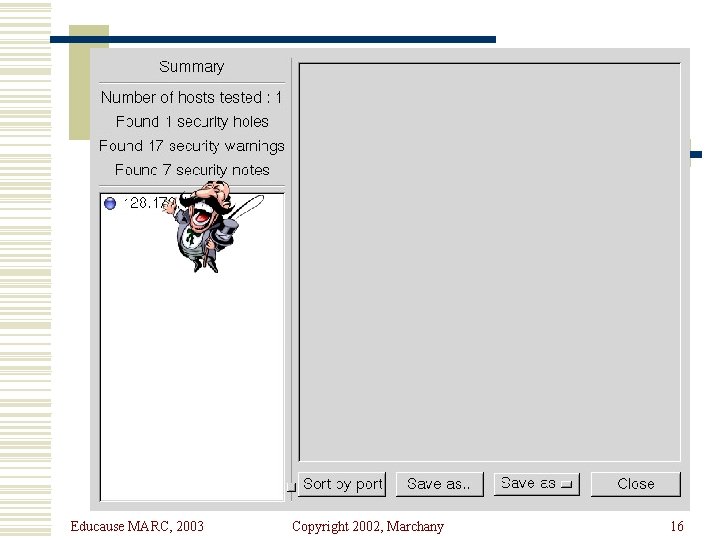
Educause MARC, 2003 Copyright 2002, Marchany 16
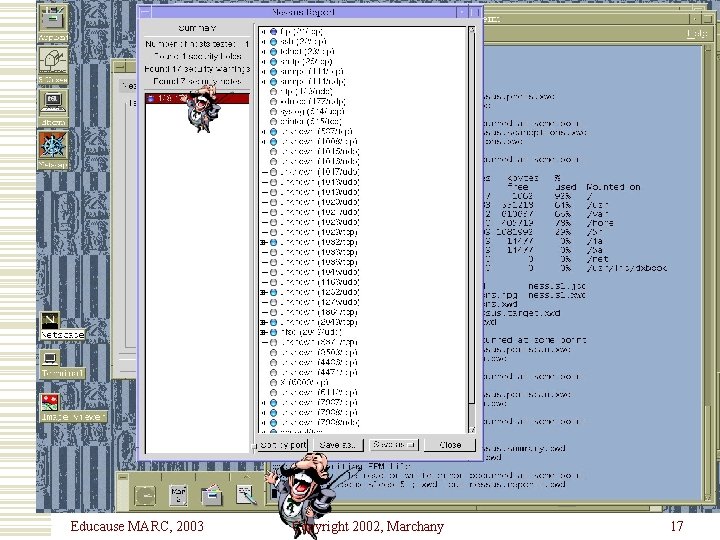
Educause MARC, 2003 Copyright 2002, Marchany 17
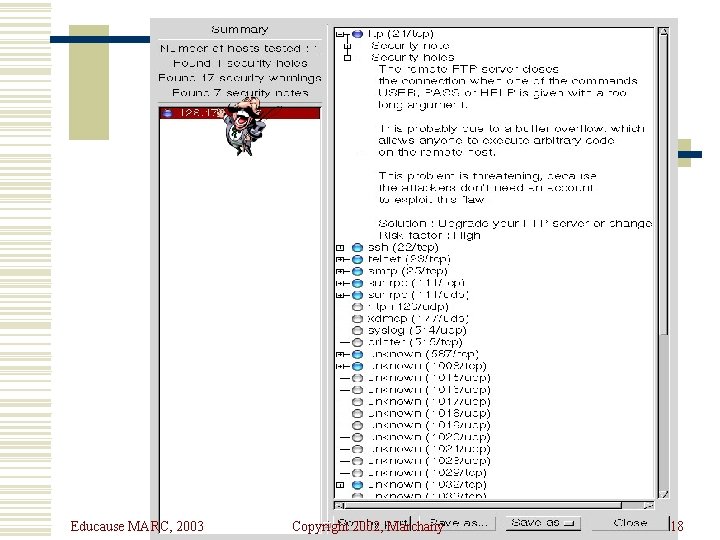
Educause MARC, 2003 Copyright 2002, Marchany 18
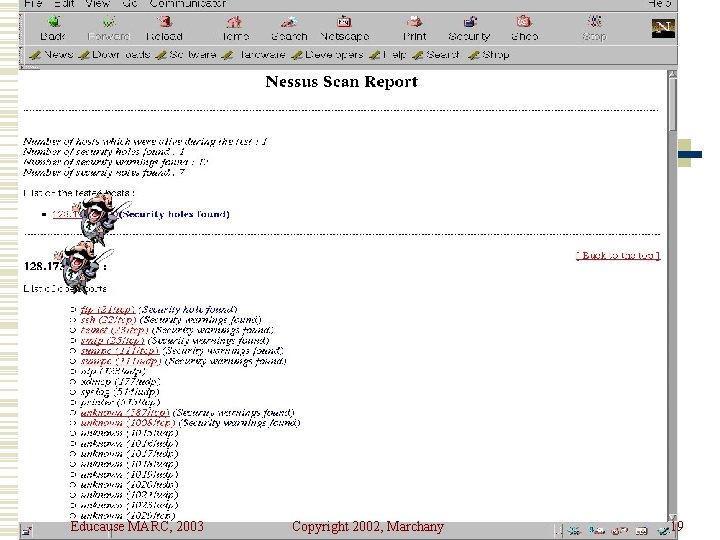
Educause MARC, 2003 Copyright 2002, Marchany 19
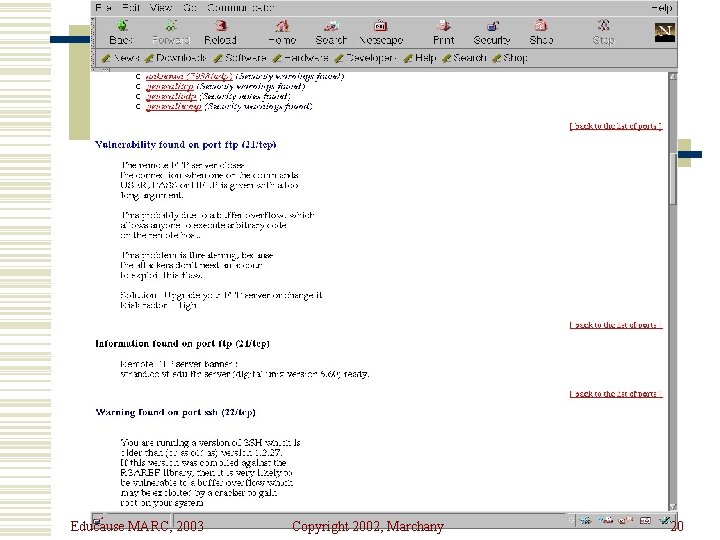
Educause MARC, 2003 Copyright 2002, Marchany 20
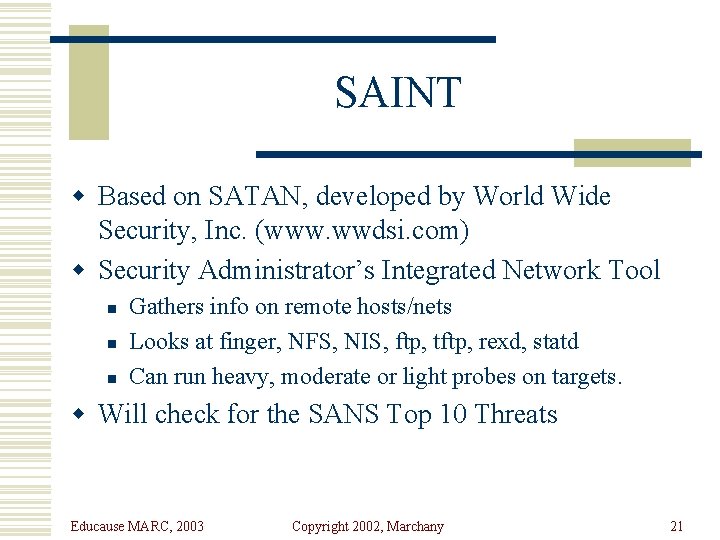
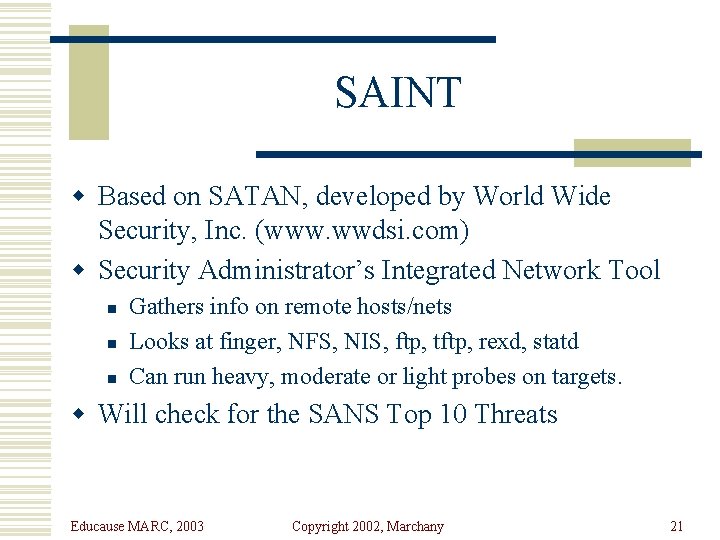
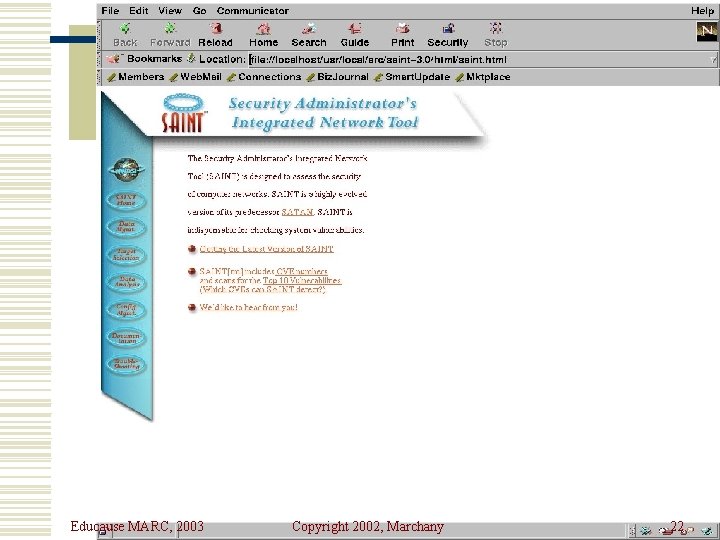
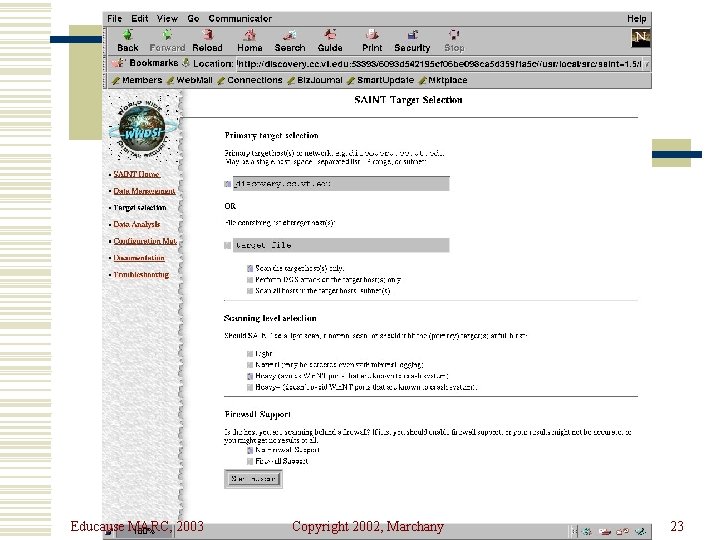
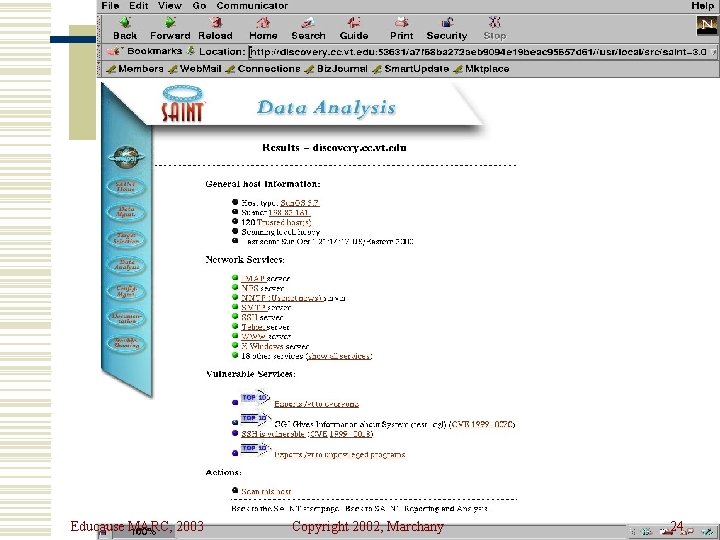
SAINT w Based on SATAN, developed by World Wide Security, Inc. (www. wwdsi. com) w Security Administrator’s Integrated Network Tool n n n Gathers info on remote hosts/nets Looks at finger, NFS, NIS, ftp, tftp, rexd, statd Can run heavy, moderate or light probes on targets. w Will check for the SANS Top 10 Threats Educause MARC, 2003 Copyright 2002, Marchany 21
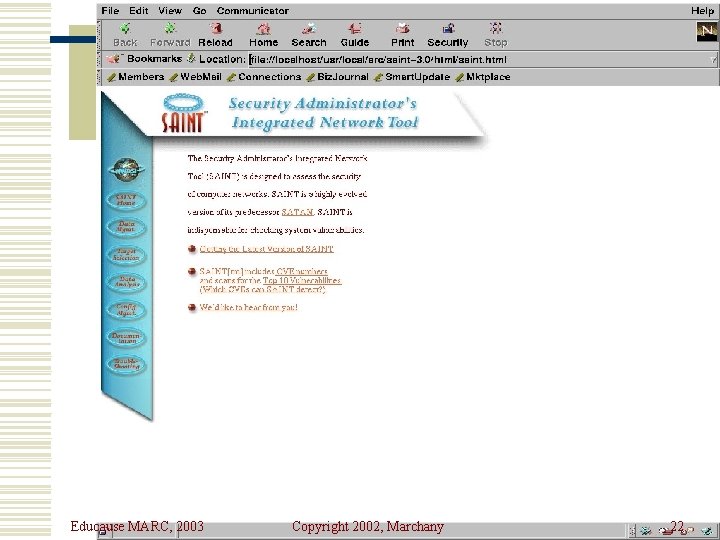
Educause MARC, 2003 Copyright 2002, Marchany 22
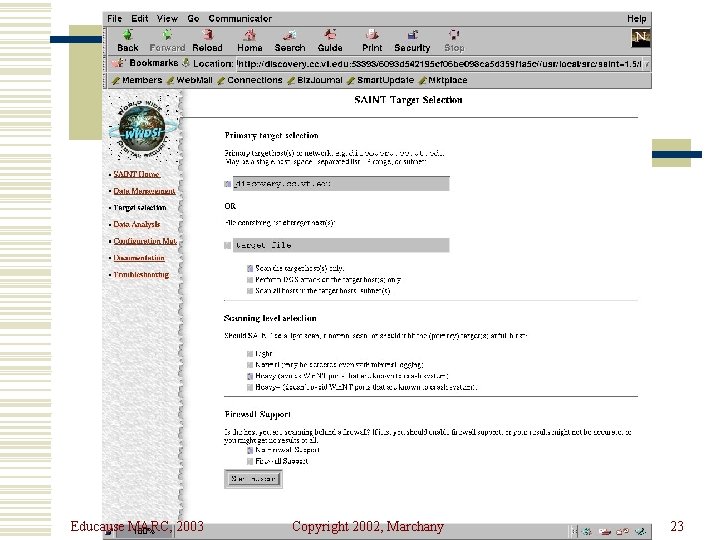
Educause MARC, 2003 Copyright 2002, Marchany 23
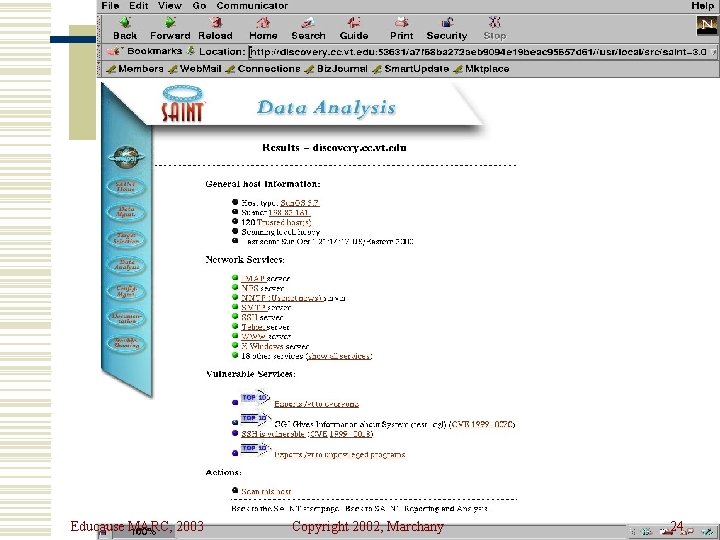
Educause MARC, 2003 Copyright 2002, Marchany 24
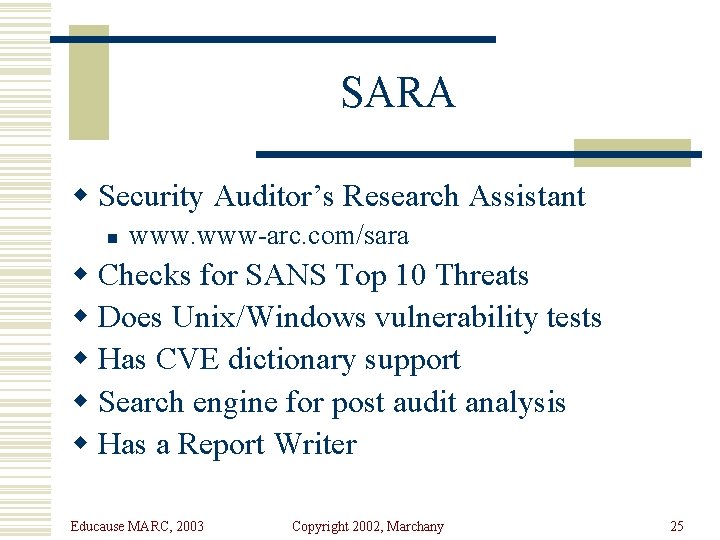
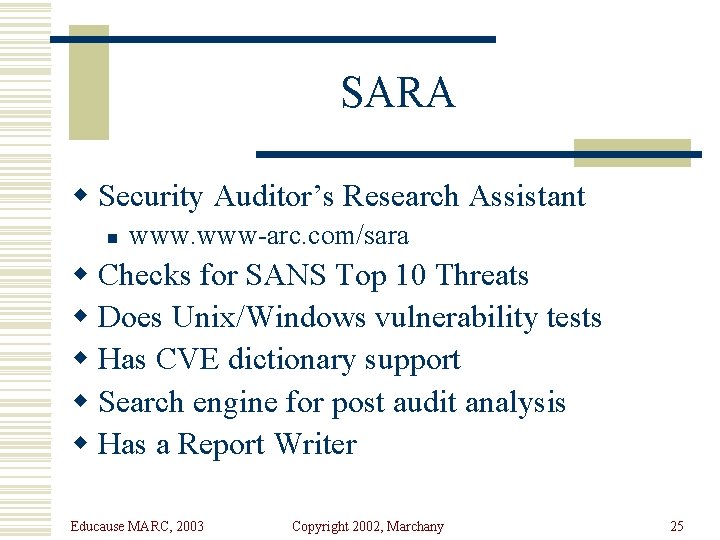
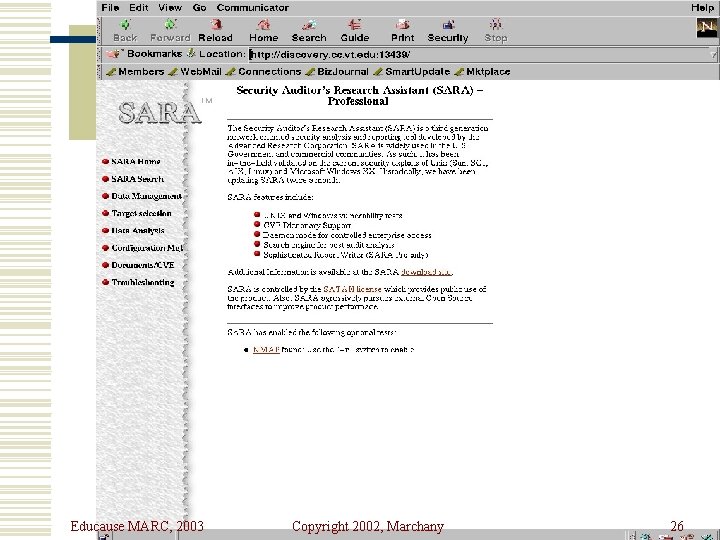
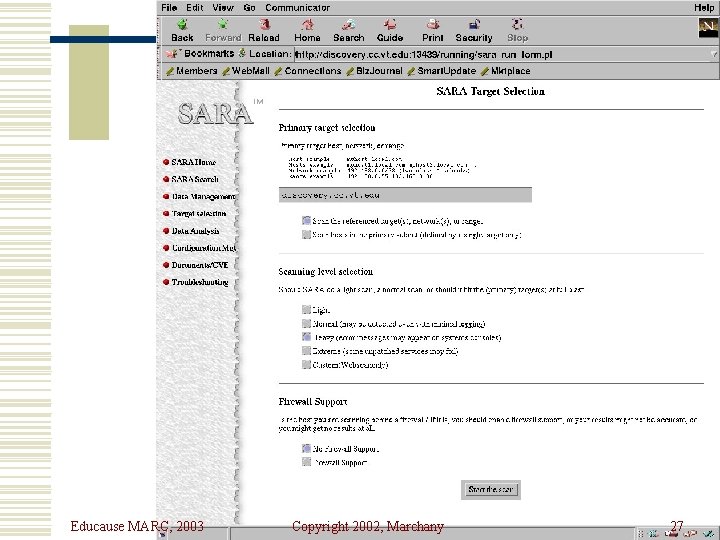
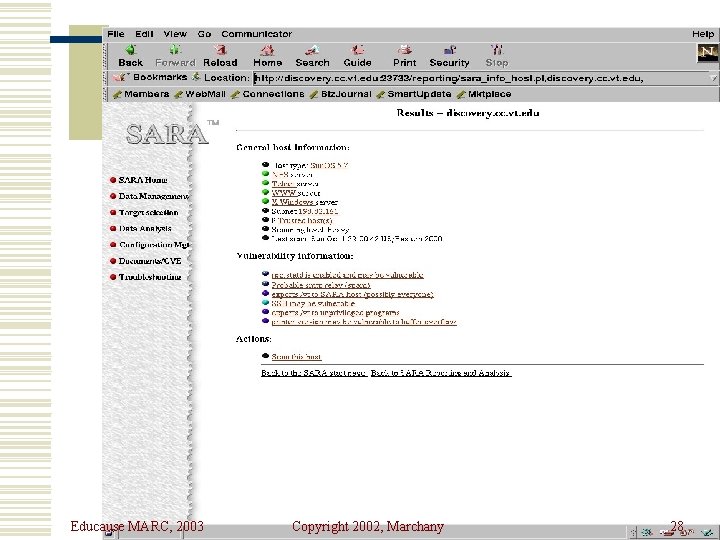
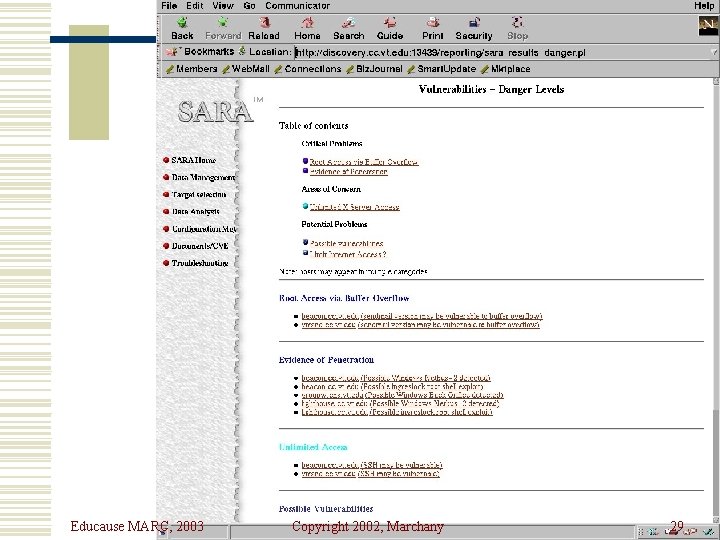
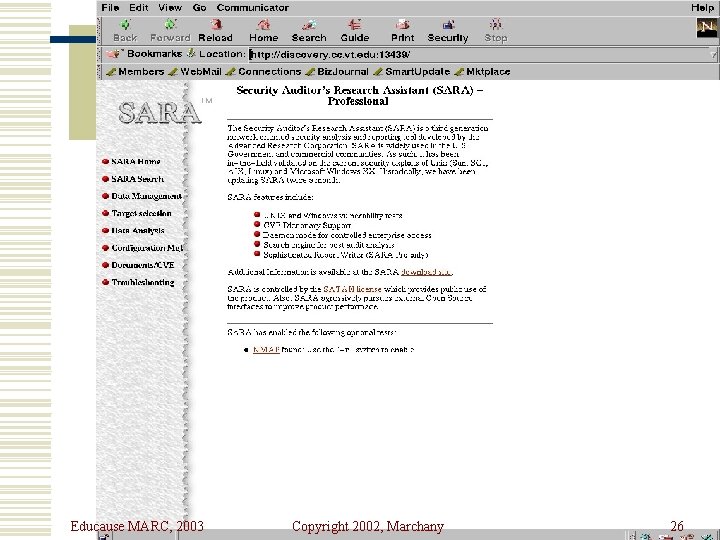
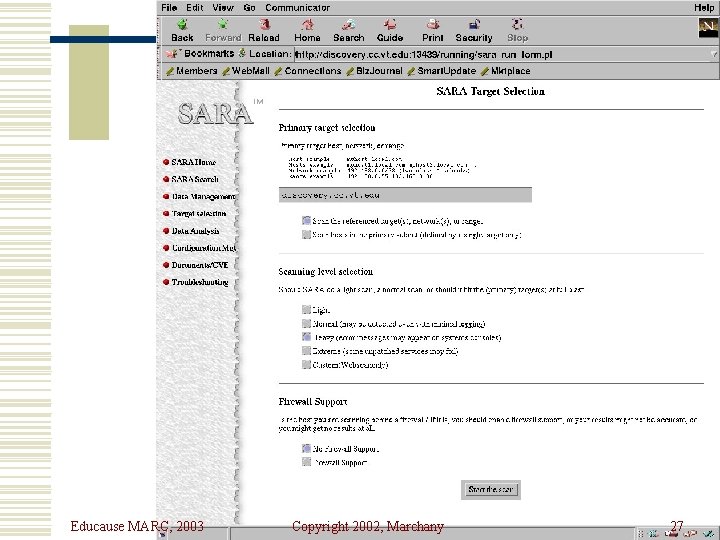
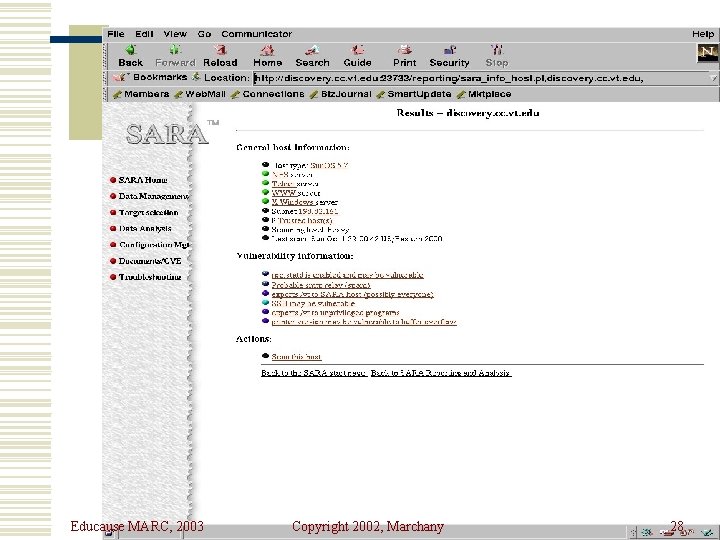
SARA w Security Auditor’s Research Assistant n www-arc. com/sara w Checks for SANS Top 10 Threats w Does Unix/Windows vulnerability tests w Has CVE dictionary support w Search engine for post audit analysis w Has a Report Writer Educause MARC, 2003 Copyright 2002, Marchany 25
Educause MARC, 2003 Copyright 2002, Marchany 26
Educause MARC, 2003 Copyright 2002, Marchany 27
Educause MARC, 2003 Copyright 2002, Marchany 28
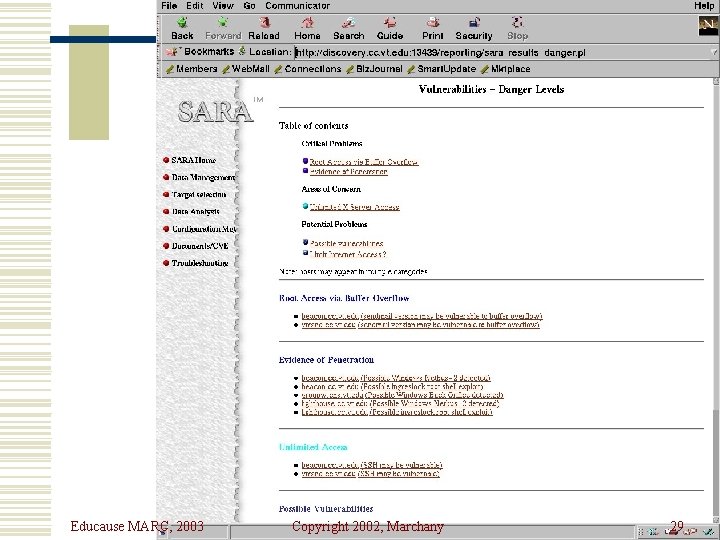
Educause MARC, 2003 Copyright 2002, Marchany 29
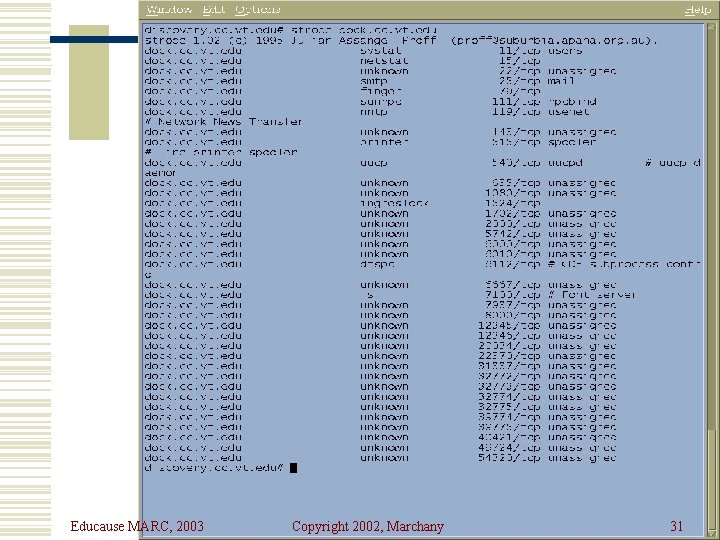
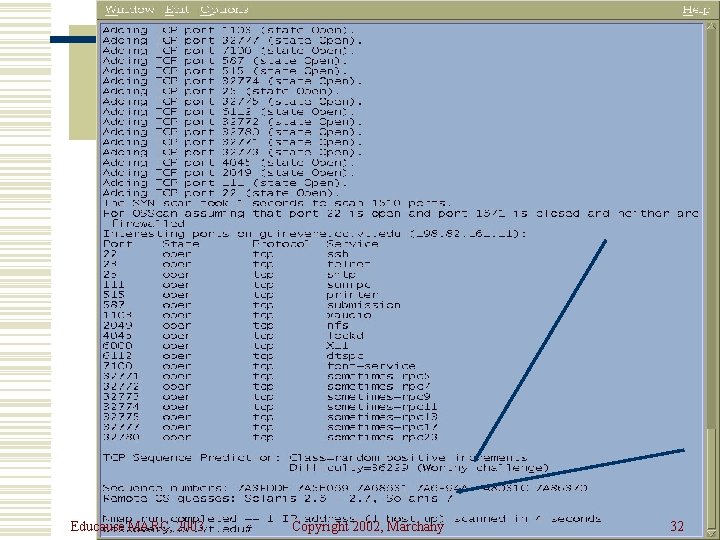
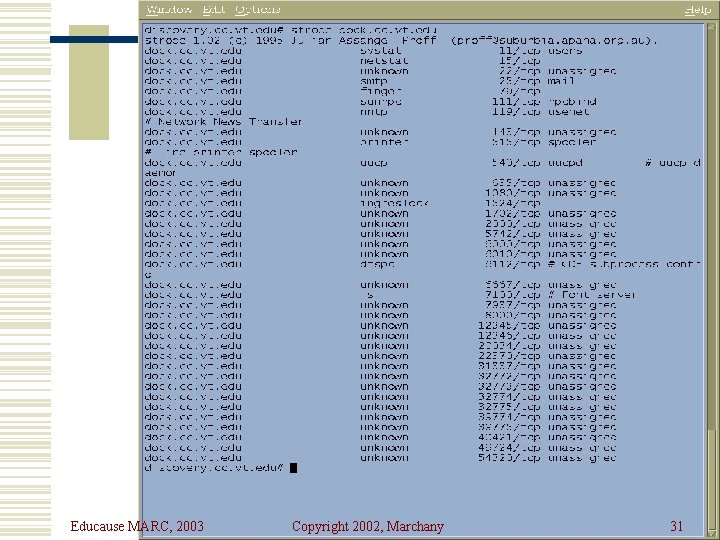
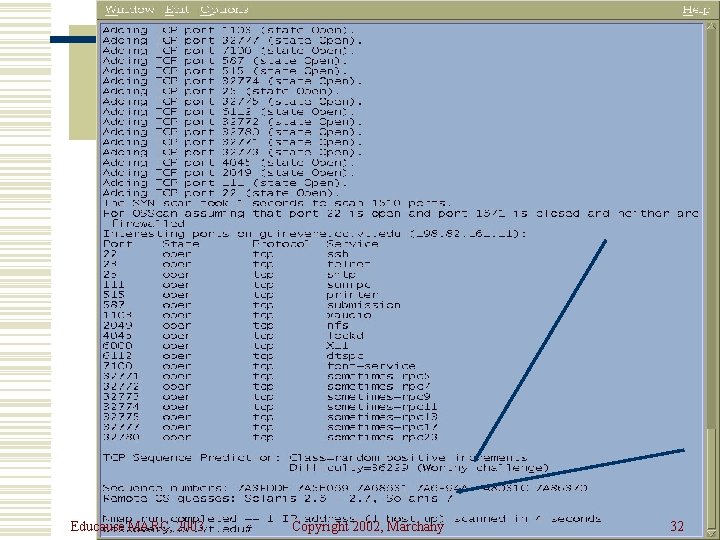
Port Scanning Tools w Strobe was one of the earliest port scanning tools. n Available from ciac. llnl. gov w Nmap is the more sophisticated grandson of strobe n Available from www. insecure. org Educause MARC, 2003 Copyright 2002, Marchany 30
Educause MARC, 2003 Copyright 2002, Marchany 31
Educause MARC, 2003 Copyright 2002, Marchany 32
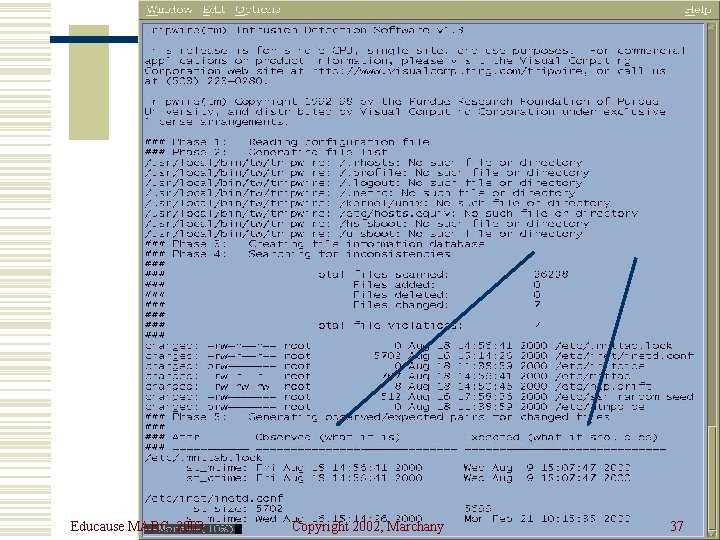
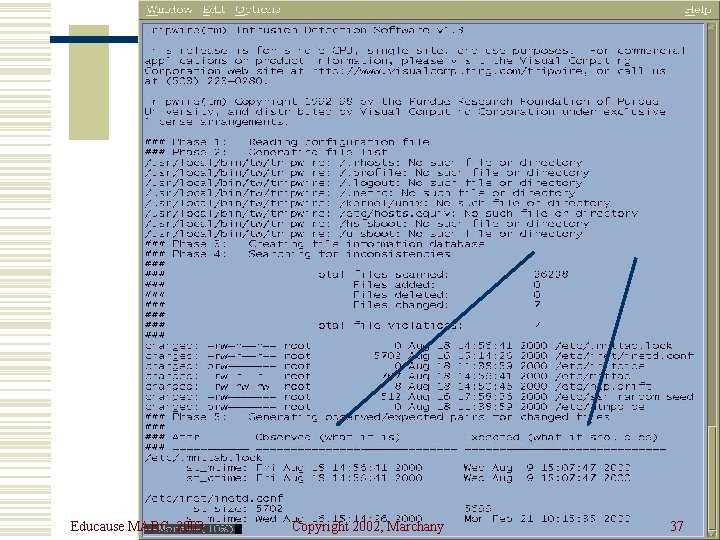
Tripwire w Available from www. tripwire. com w First of the file integrity checkers w Unix and NT versions available n Network capable versions available w Academic version is free. Commercial and NT versions are not. w Useful in finding trojan programs Educause MARC, 2003 Copyright 2002, Marchany 33
Tripwire w Generates a “signature” for each file based on checksums and other characteristics. w These signatures are stored in a database file that should be kept offline. w This is the baseline. Educause MARC, 2003 Copyright 2002, Marchany 34
Tripwire w To initialize the DB: tripwire –initialize w Update DB interactively: tripwire -interactive w Non-interactive DB update: tripwire – update <FN> Educause MARC, 2003 Copyright 2002, Marchany 35
Tripwire w Security Issues n n Need to protect the DB Need to protect the vulnerable executables w Advantages n Simple interface, good choice of crypto hash functions, good all-around tool w Disadvantages n Kernel mod attacks, initial tw. config takes some time to customize, NT version is good but costs $$$, no network security Educause MARC, 2003 Copyright 2002, Marchany 36
Educause MARC, 2003 Copyright 2002, Marchany 37
Personal Firewall Tools w These tools monitor connection attempts to your system and give you the option of allowing or denying the access w They log the connection attempt to standard log files w More valuable than real Firewall, IMHO. Educause MARC, 2003 Copyright 2002, Marchany 38
Portsentry/TCP Wrappers w Available from www. psionic. com w TCP Wrappers available from ciac. llnl. gov and a ton of other sites w Any host that scans a list of “banned” ports is placed in an /etc/hosts. deny file w Need TCP Wrappers installed on the machine n Tcpwrappers logs attempts to connect to services Educause MARC, 2003 Copyright 2002, Marchany 39
TCP Wrappers w Everyone should buy Wietse Venema dinner for writing this tool. w Purpose n n Log network connections to a system Allow you to filter who connects to the system w Needs an inetd-like program to act as the dispatcher of network services Educause MARC, 2003 Copyright 2002, Marchany 40
TCP Wrappers Features w Allows you to monitor/filter incoming requests for SYSTAT, FINGER, FTP, TELNET, R-Commands, TFTP, TALK and other network services. w Provides access control to restrict what systems connect to what network daemons. w Provides some protection from host spoofing Educause MARC, 2003 Copyright 2002, Marchany 41
TCP Wrappers w Advantages n n n Logs and applies access controls to remote connections Lets you define which daemons are wrapped Does good reverse lookup on hosts w Disadvantages n n Ident service not reliable Only looks at network daemons spawned by inetd Doesn’t wrap ALL services (RPC) Could give a false sense of security Educause MARC, 2003 Copyright 2002, Marchany 42
Portsentry w Available from www. psionic. com w Monitors ports and performs an action when an attempt to access the port is made. w Usually access is denied to the probing systems. w Monitors TCP and UDP traffic. A little more flexible than TCP Wrappers Educause MARC, 2003 Copyright 2002, Marchany 43
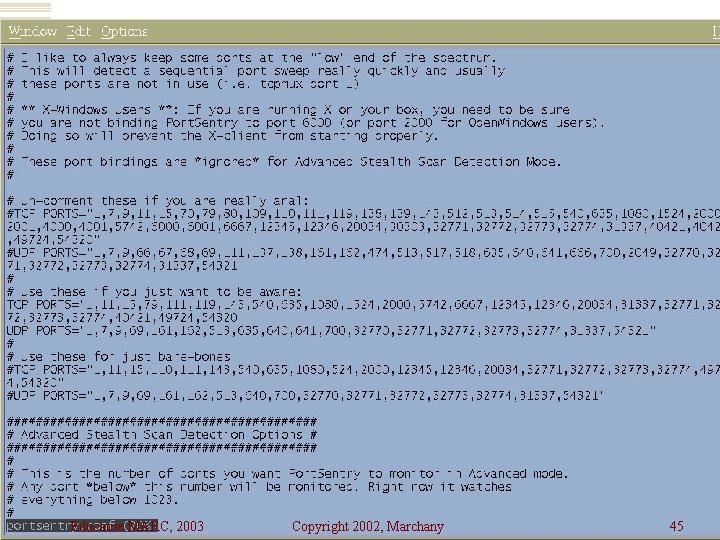
Portsentry Configuration Files w Portsentry. conf contains the list of ports to be monitored. w 3 levels of paranoia Educause MARC, 2003 Copyright 2002, Marchany 44
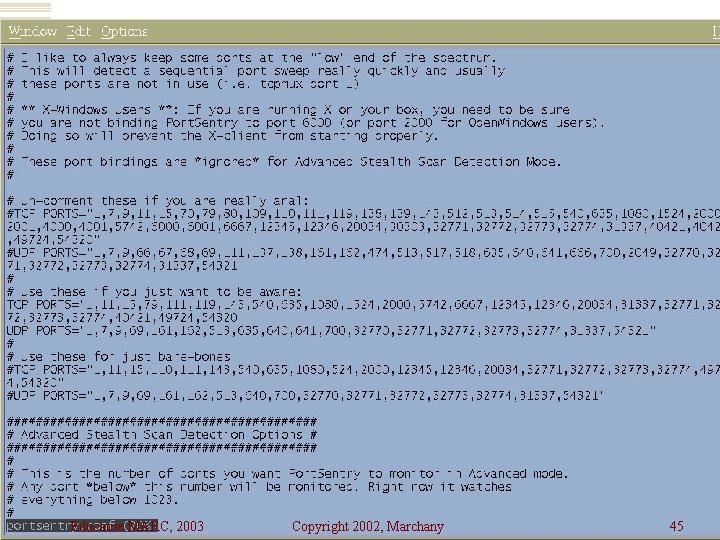
Educause MARC, 2003 Copyright 2002, Marchany 45
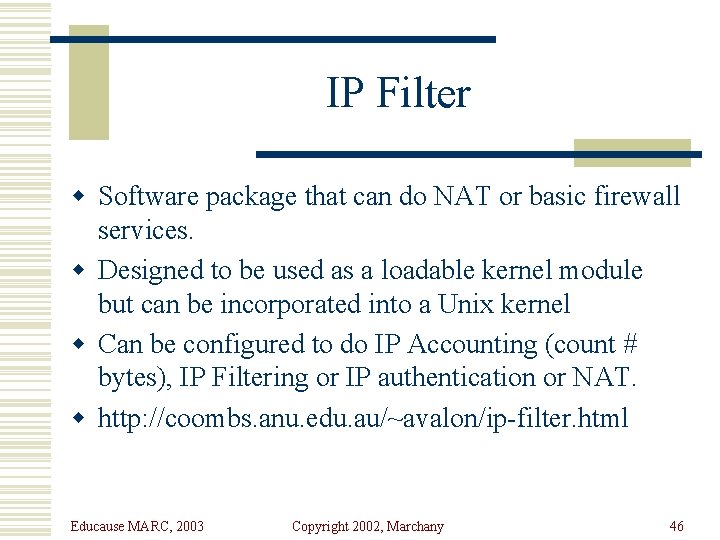
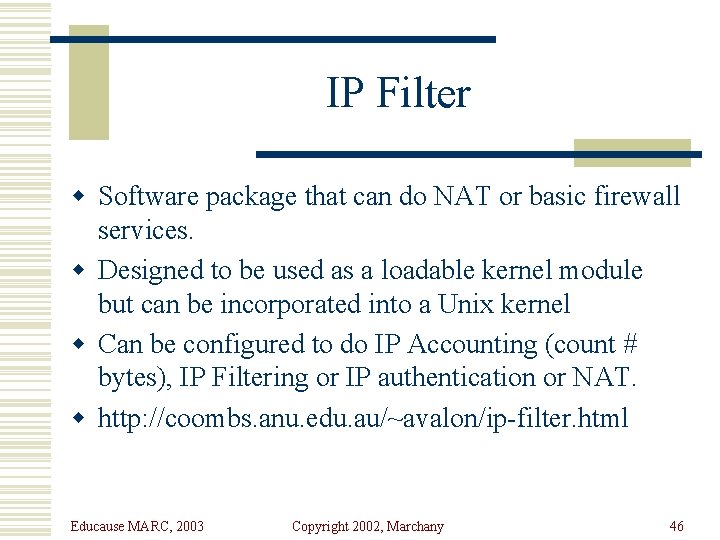
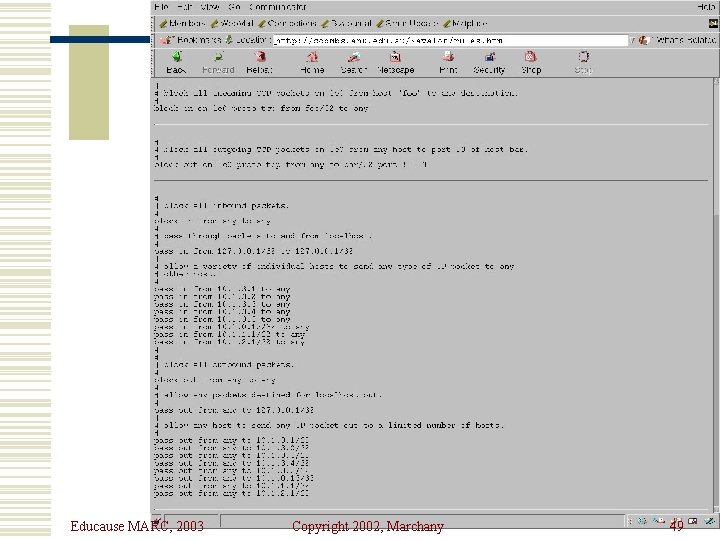
IP Filter w Software package that can do NAT or basic firewall services. w Designed to be used as a loadable kernel module but can be incorporated into a Unix kernel w Can be configured to do IP Accounting (count # bytes), IP Filtering or IP authentication or NAT. w http: //coombs. anu. edu. au/~avalon/ip-filter. html Educause MARC, 2003 Copyright 2002, Marchany 46
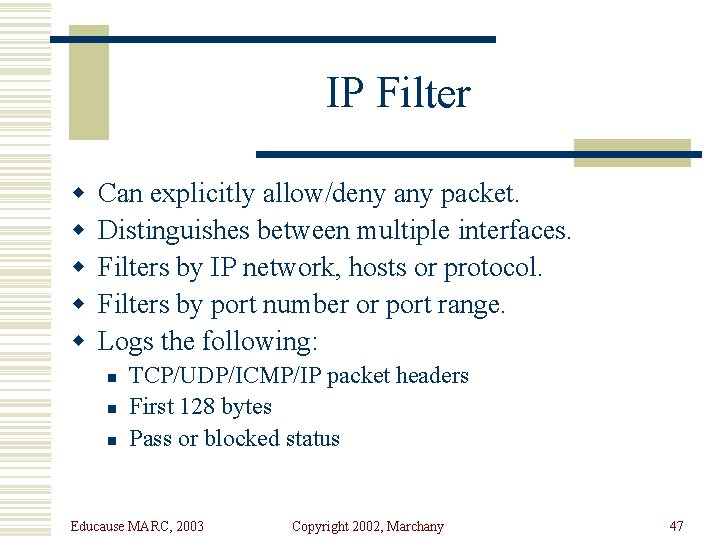
IP Filter w w w Can explicitly allow/deny any packet. Distinguishes between multiple interfaces. Filters by IP network, hosts or protocol. Filters by port number or port range. Logs the following: n n n TCP/UDP/ICMP/IP packet headers First 128 bytes Pass or blocked status Educause MARC, 2003 Copyright 2002, Marchany 47
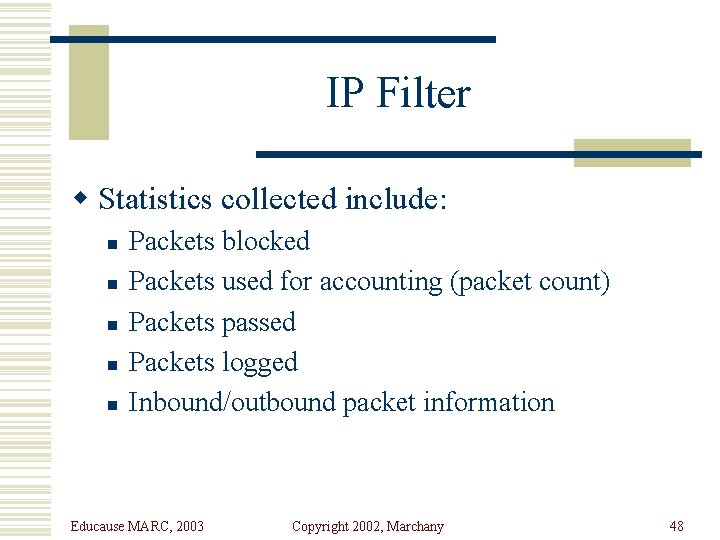
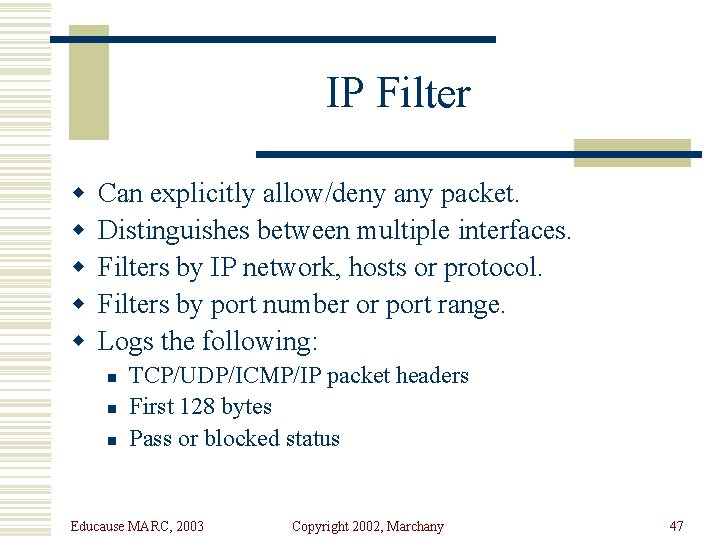
IP Filter w Statistics collected include: n n n Packets blocked Packets used for accounting (packet count) Packets passed Packets logged Inbound/outbound packet information Educause MARC, 2003 Copyright 2002, Marchany 48
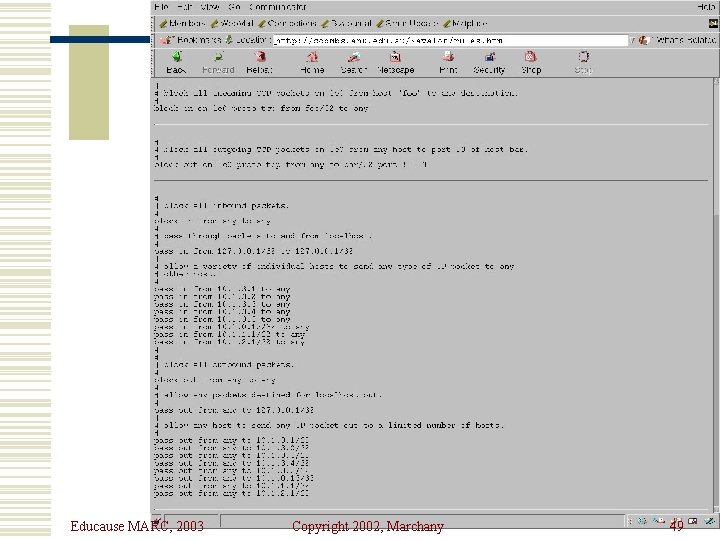
Educause MARC, 2003 Copyright 2002, Marchany 49
![IP Filter Log Format Jul 30 01 46 52 myhost vt edu ipmon147 ID IP Filter Log Format Jul 30 01: 46: 52 myhost. vt. edu ipmon[147]: [ID](https://slidetodoc.com/presentation_image_h2/250a20f9582bec6e90d74168b0e49b47/image-50.jpg)
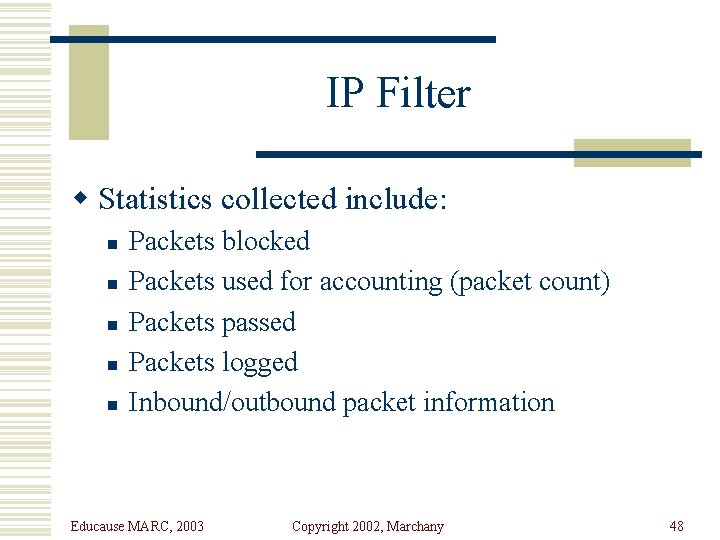
IP Filter Log Format Jul 30 01: 46: 52 myhost. vt. edu ipmon[147]: [ID 702911 local 0. warning] 01: 46: 52. 196772 hme 0 @0: 5 b 194. 143. 66. 126, 21 ->198. 82. 255, 21 PR tcp len 20 40 -S IN Jul 30 01: 47: 03 myhost. vt. edu ipmon[147]: [ID 702911 local 0. warning] 01: 47: 03. 269595 hme 0 @0: 5 b 194. 143. 66. 126, 21 ->198. 82. 255, 21 PR tcp len 20 40 -S IN Jul 30 05: 53: 51 myhost. vt. edu ipmon[147]: [ID 702911 local 0. warning] 05: 53: 50. 699235 hme 0 @0: 5 b 203. 90. 84. 163, 1781 ->198. 82. 255, 21 PR tcp len 20 60 -S IN Educause MARC, 2003 Copyright 2002, Marchany 50
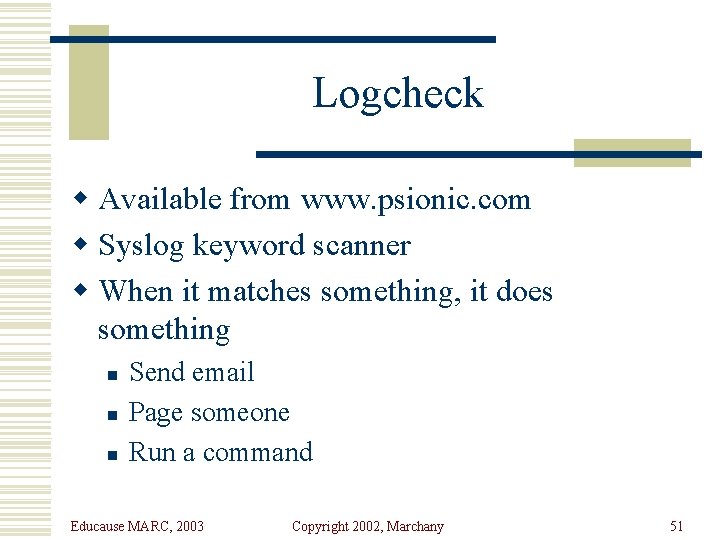
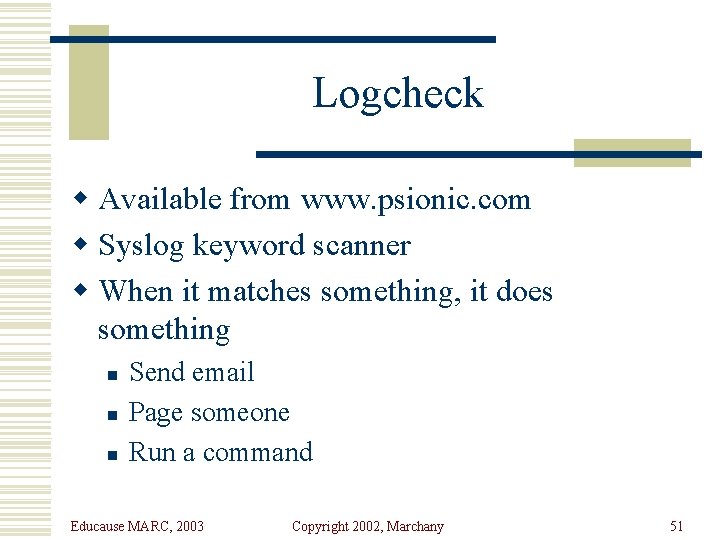
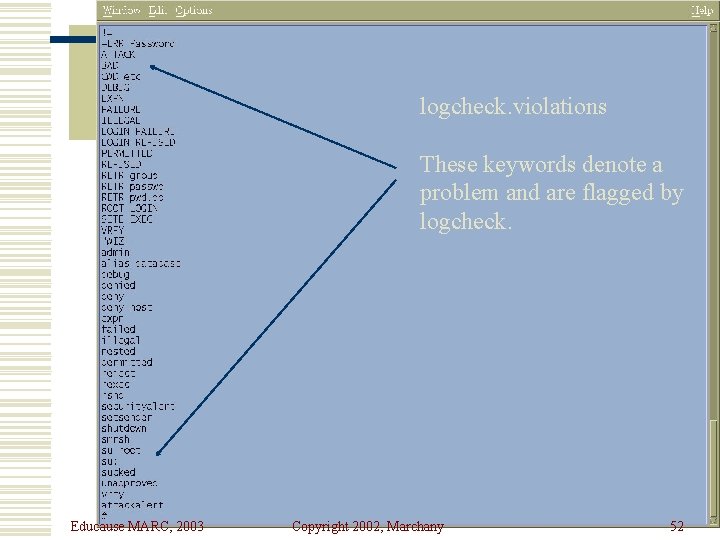
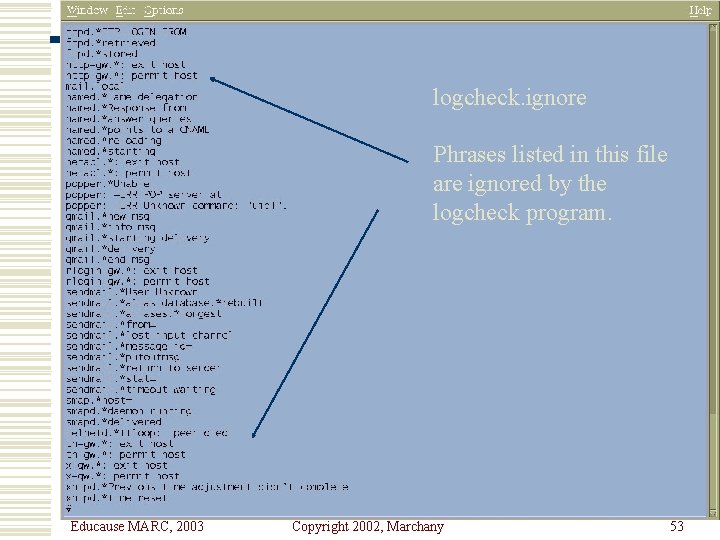
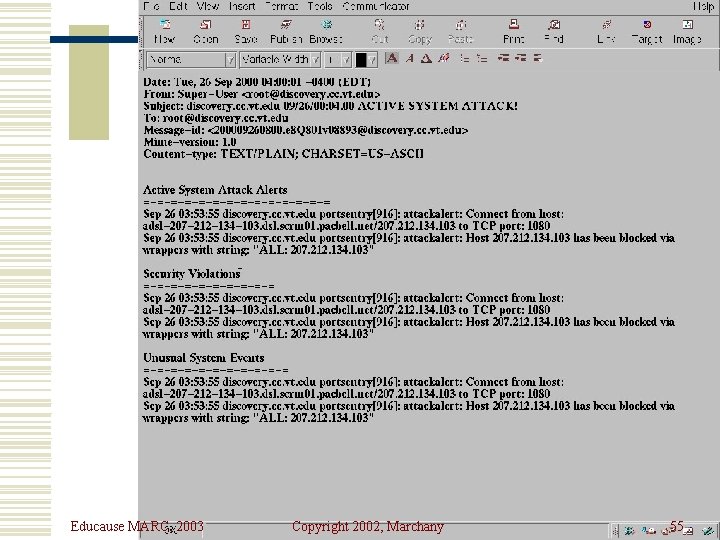
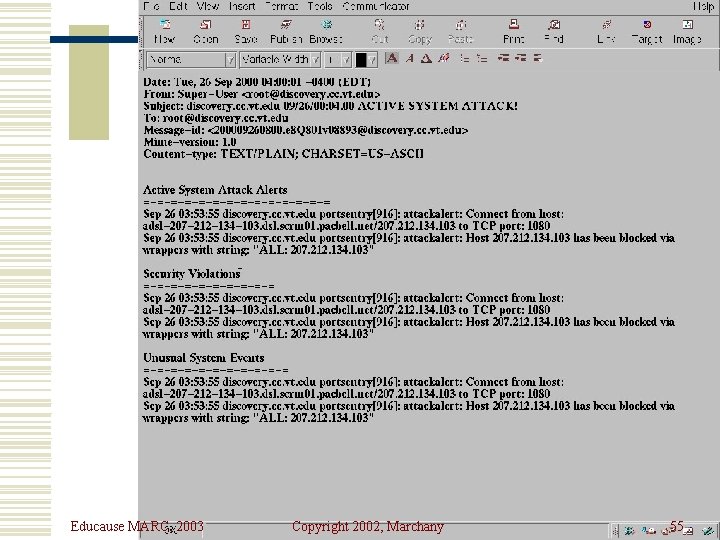
Logcheck w Available from www. psionic. com w Syslog keyword scanner w When it matches something, it does something n n n Send email Page someone Run a command Educause MARC, 2003 Copyright 2002, Marchany 51
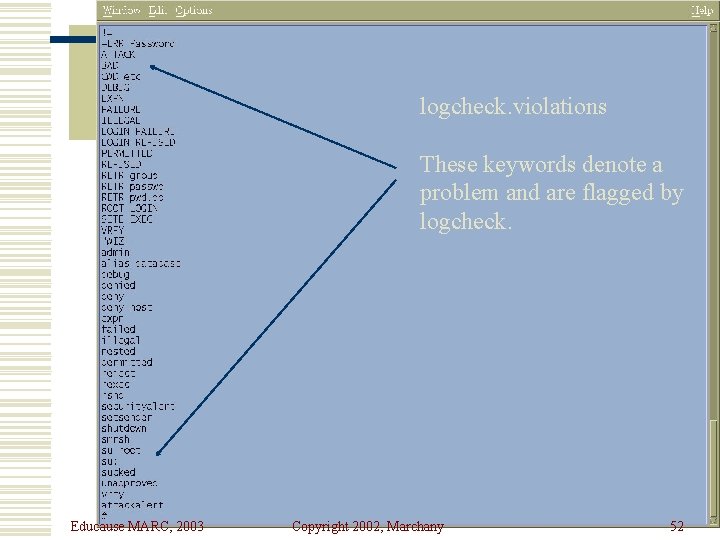
logcheck. violations These keywords denote a problem and are flagged by logcheck. Educause MARC, 2003 Copyright 2002, Marchany 52
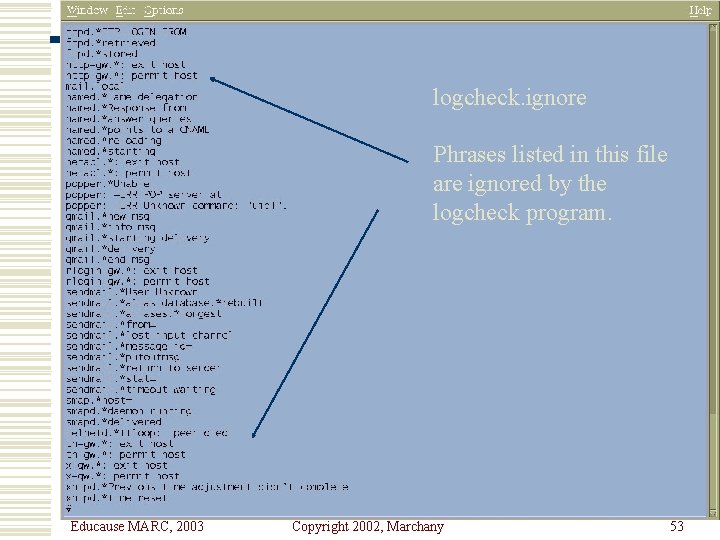
logcheck. ignore Phrases listed in this file are ignored by the logcheck program. Educause MARC, 2003 Copyright 2002, Marchany 53
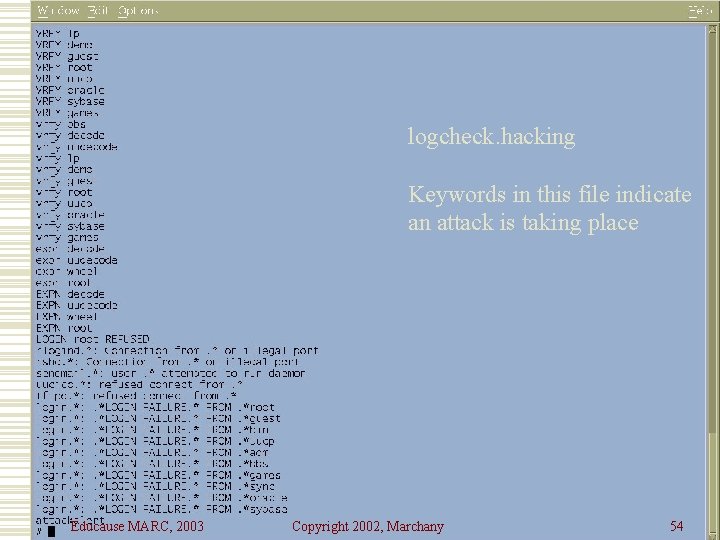
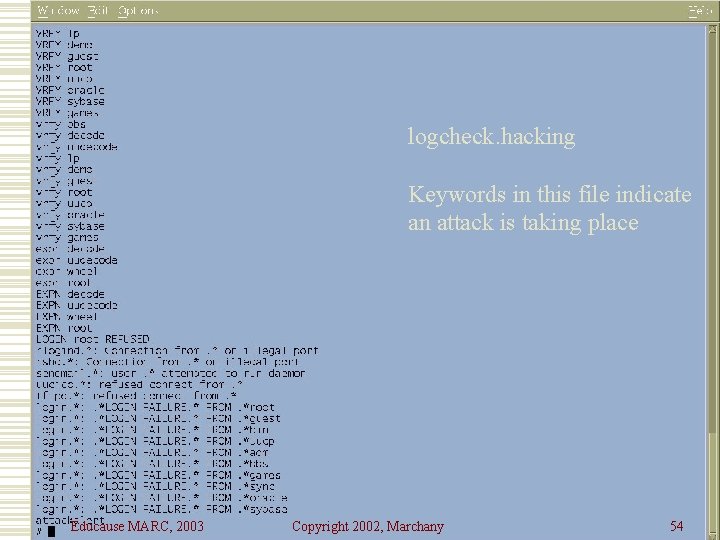
logcheck. hacking Keywords in this file indicate an attack is taking place Educause MARC, 2003 Copyright 2002, Marchany 54
Educause MARC, 2003 Copyright 2002, Marchany 55
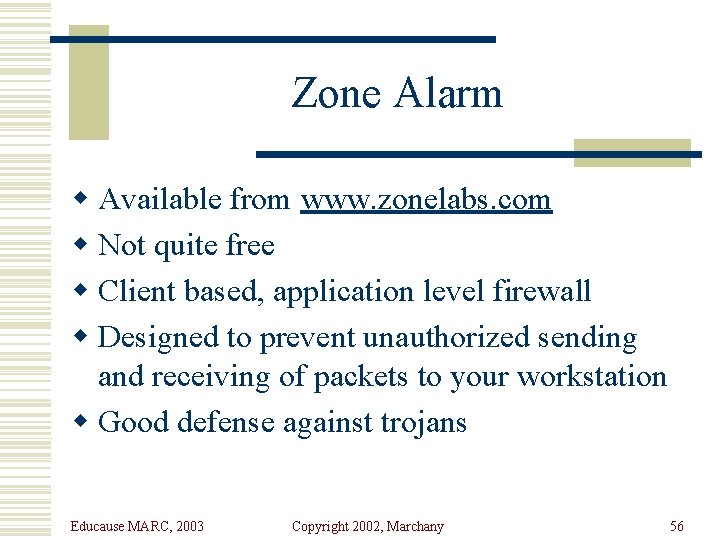
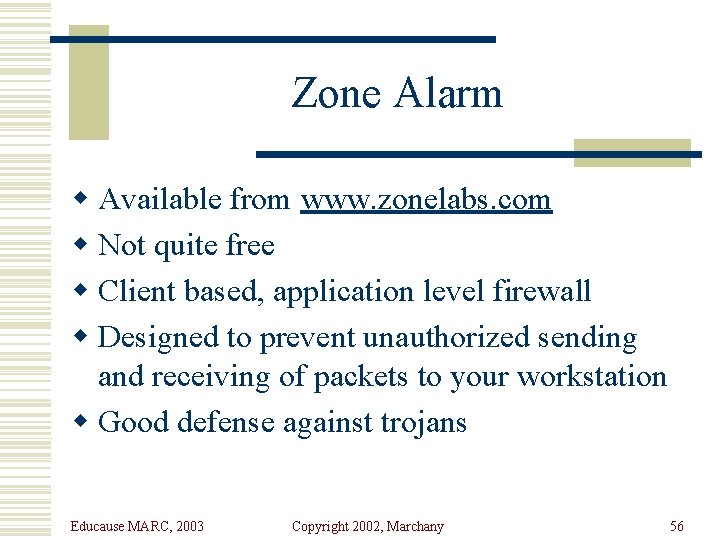
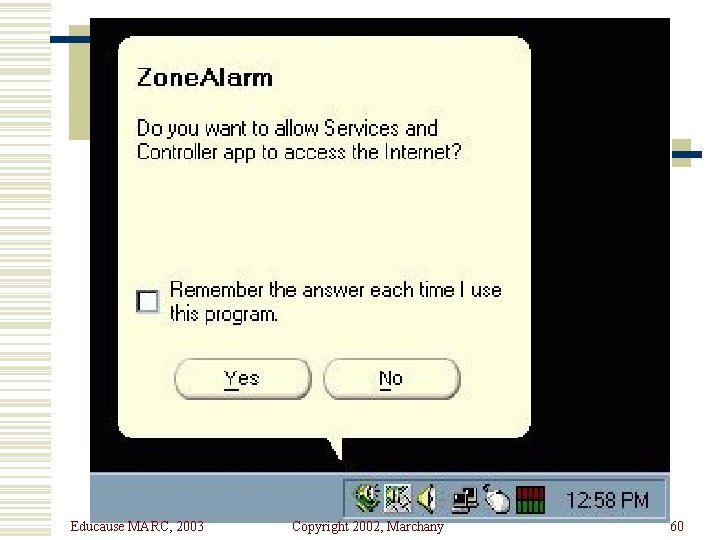
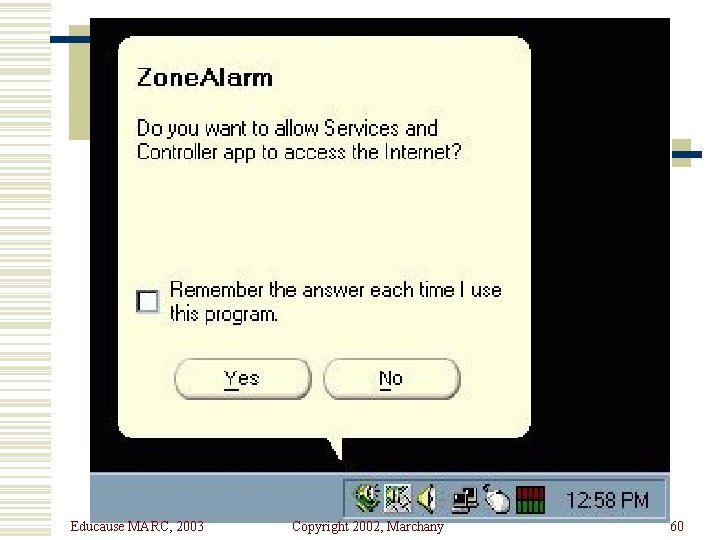
Zone Alarm w Available from www. zonelabs. com w Not quite free w Client based, application level firewall w Designed to prevent unauthorized sending and receiving of packets to your workstation w Good defense against trojans Educause MARC, 2003 Copyright 2002, Marchany 56
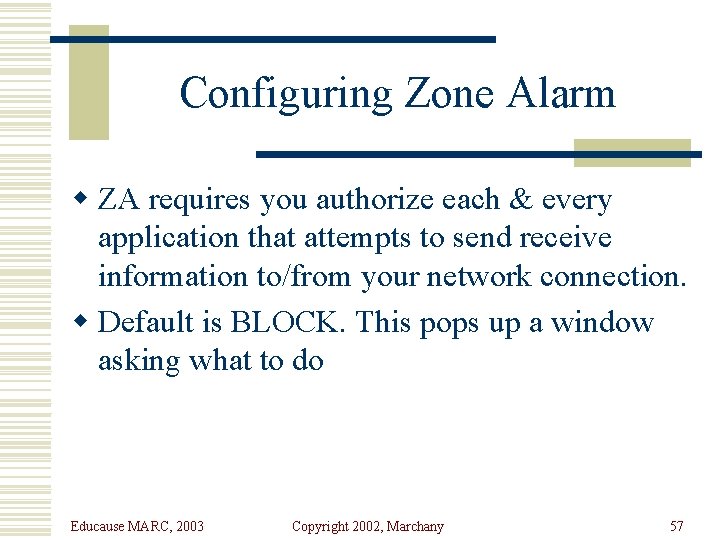
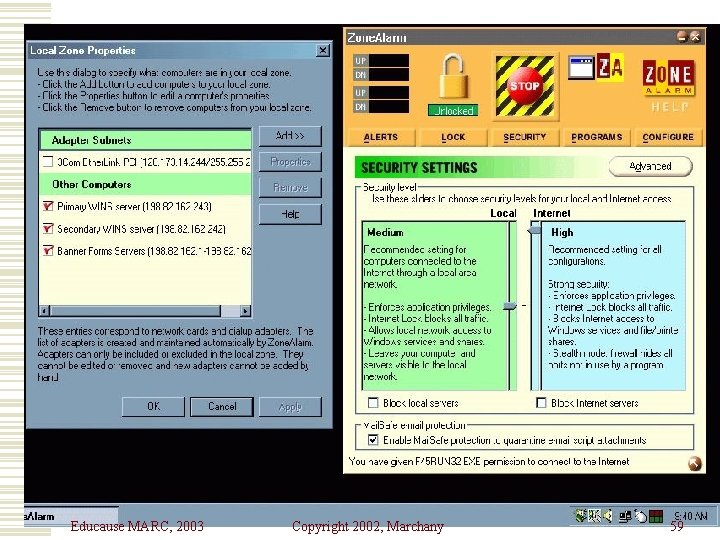
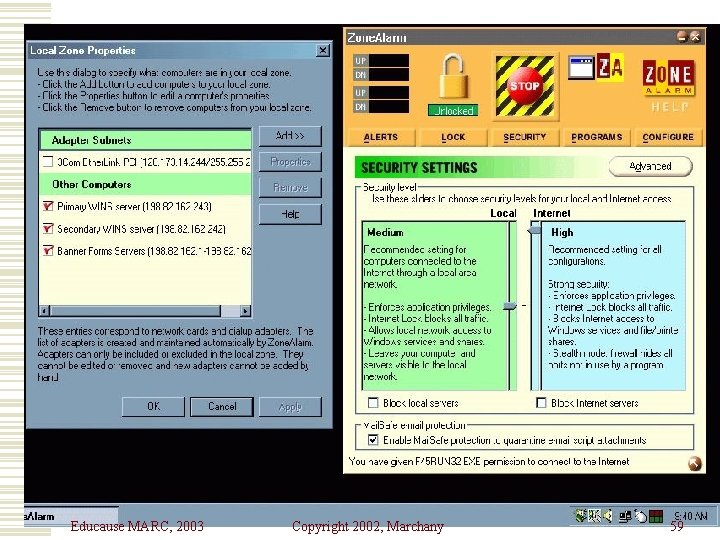
Configuring Zone Alarm w ZA requires you authorize each & every application that attempts to send receive information to/from your network connection. w Default is BLOCK. This pops up a window asking what to do Educause MARC, 2003 Copyright 2002, Marchany 57
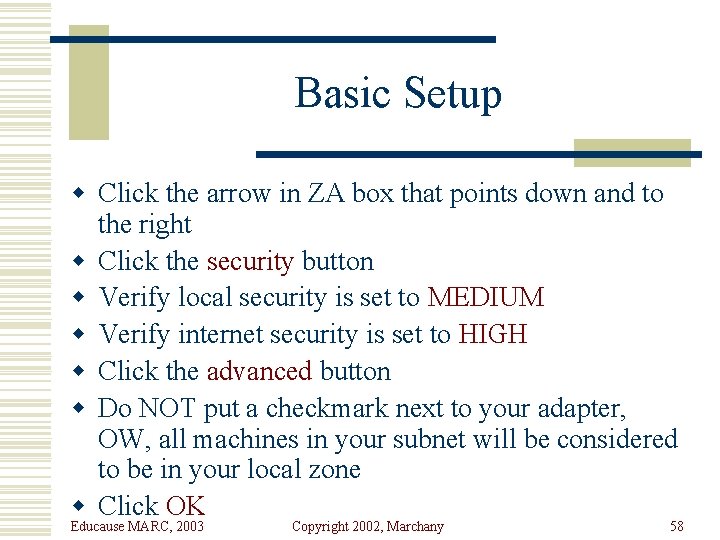
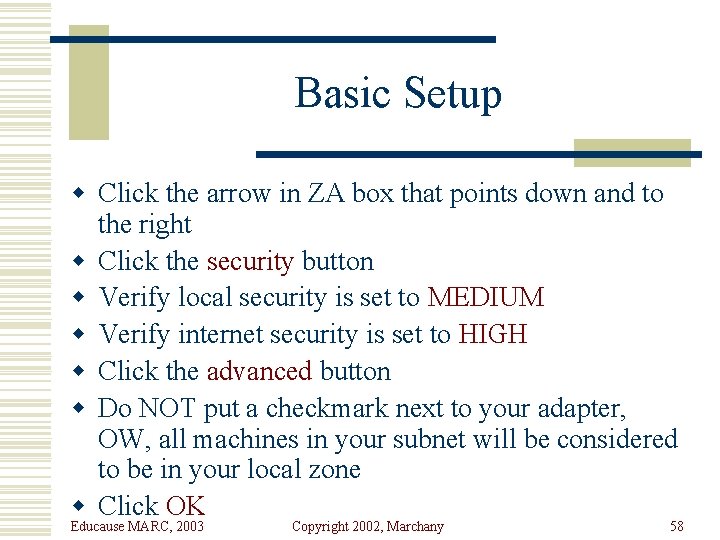
Basic Setup w Click the arrow in ZA box that points down and to the right w Click the security button w Verify local security is set to MEDIUM w Verify internet security is set to HIGH w Click the advanced button w Do NOT put a checkmark next to your adapter, OW, all machines in your subnet will be considered to be in your local zone w Click OK Educause MARC, 2003 Copyright 2002, Marchany 58
Educause MARC, 2003 Copyright 2002, Marchany 59
Educause MARC, 2003 Copyright 2002, Marchany 60
Educause MARC, 2003 Copyright 2002, Marchany 61
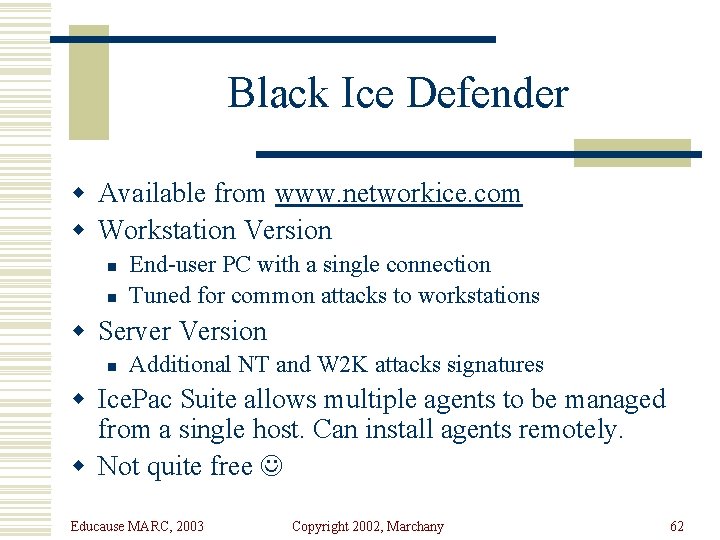
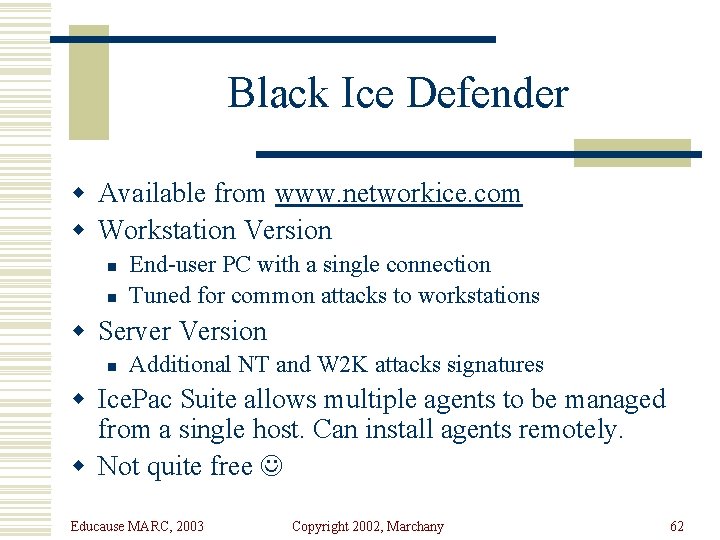
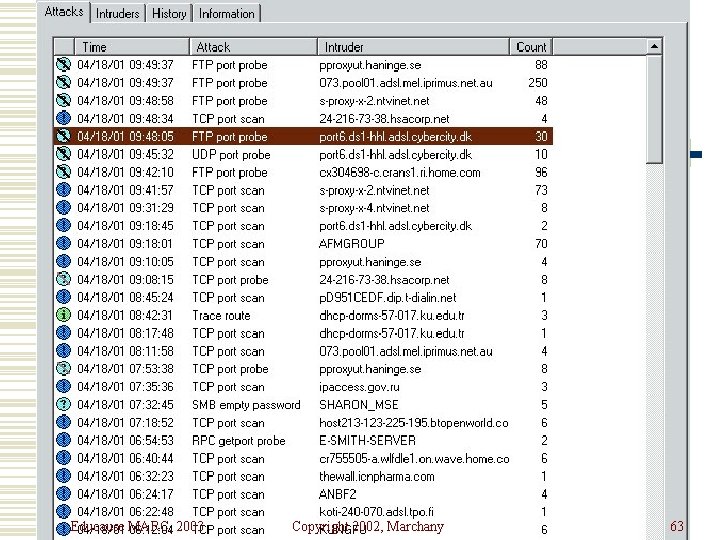
Black Ice Defender w Available from www. networkice. com w Workstation Version n n End-user PC with a single connection Tuned for common attacks to workstations w Server Version n Additional NT and W 2 K attacks signatures w Ice. Pac Suite allows multiple agents to be managed from a single host. Can install agents remotely. w Not quite free Educause MARC, 2003 Copyright 2002, Marchany 62
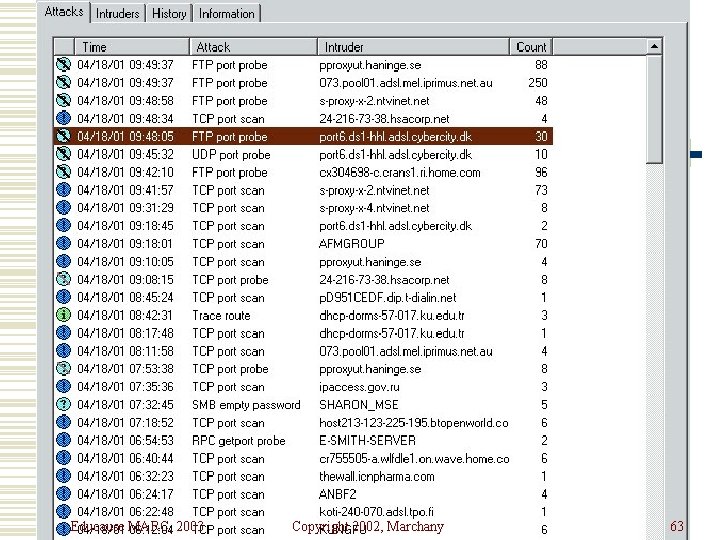
Educause MARC, 2003 Copyright 2002, Marchany 63
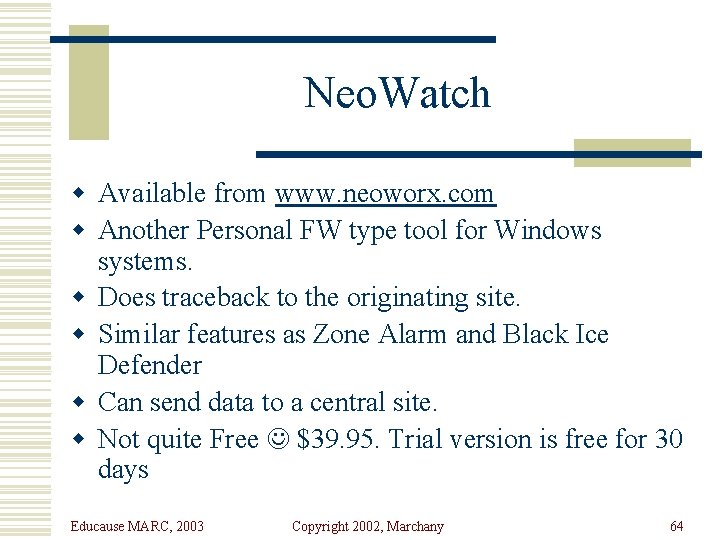
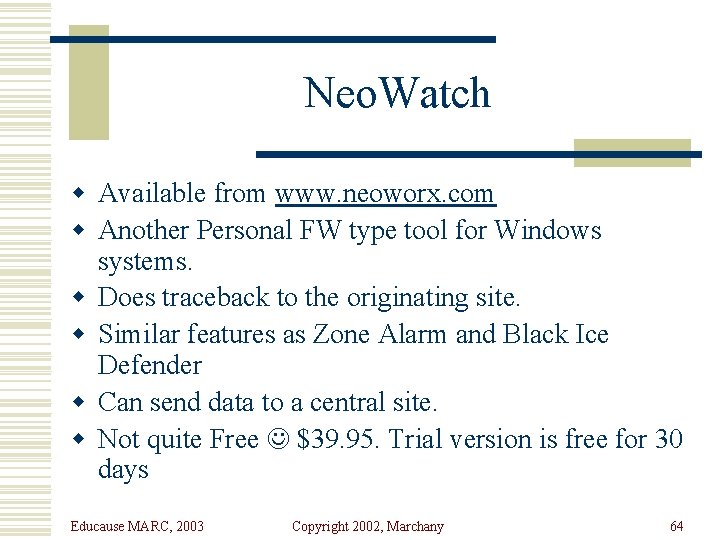
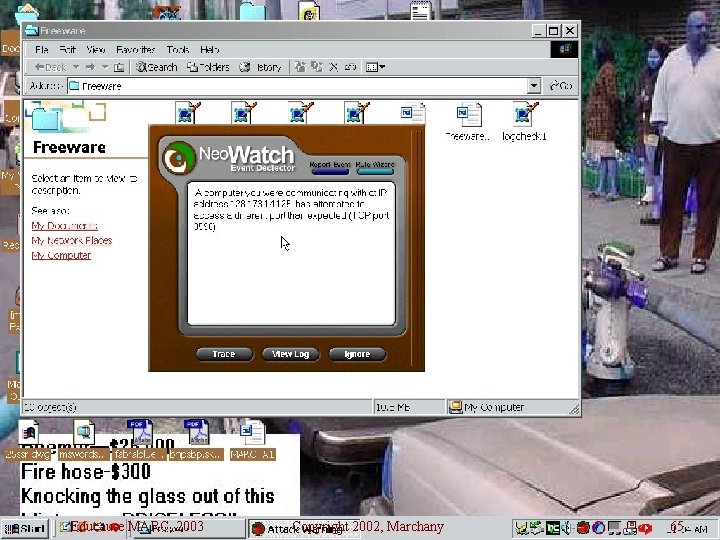
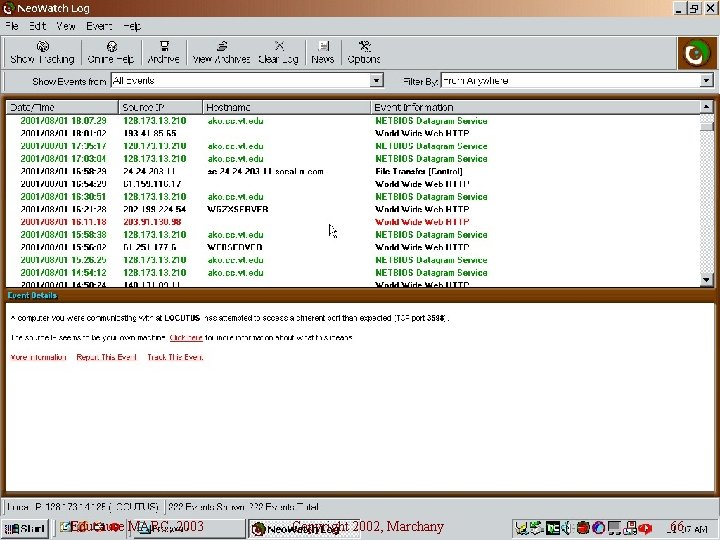
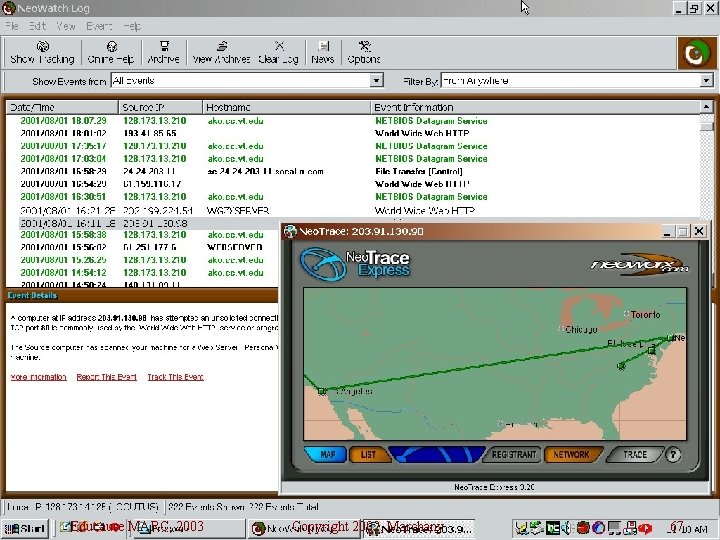
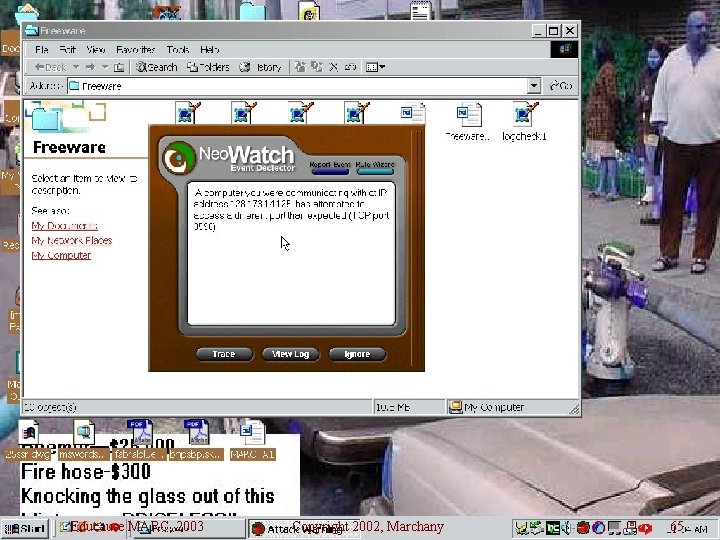
Neo. Watch w Available from www. neoworx. com w Another Personal FW type tool for Windows systems. w Does traceback to the originating site. w Similar features as Zone Alarm and Black Ice Defender w Can send data to a central site. w Not quite Free $39. 95. Trial version is free for 30 days Educause MARC, 2003 Copyright 2002, Marchany 64
Educause MARC, 2003 Copyright 2002, Marchany 65
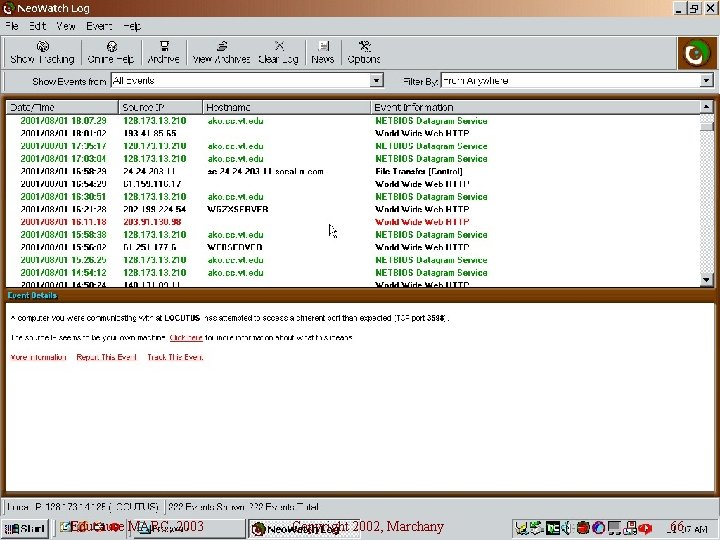
Educause MARC, 2003 Copyright 2002, Marchany 66
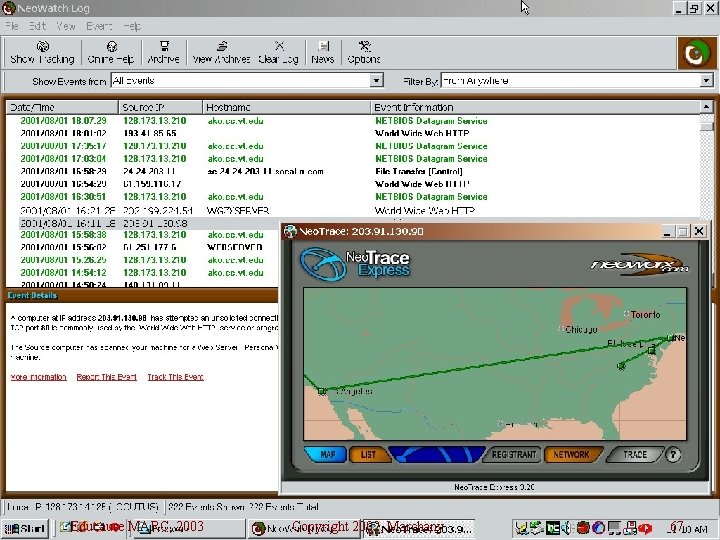
Educause MARC, 2003 Copyright 2002, Marchany 67
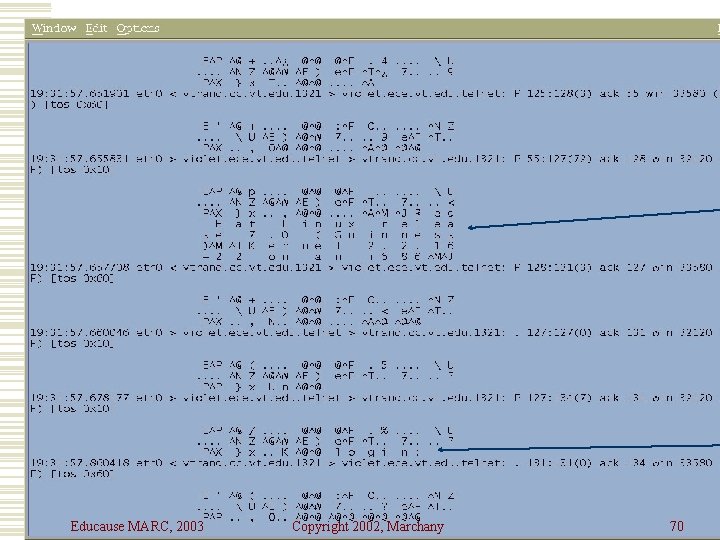
Sniffers: snoop, iptrace, tcpdump, snort w Some systems have builtin sniffers n n Solaris - snoop AIX - iptrace Linux - tcpdump NT/2000 - netwatch w Tcpdump is the generic sniffer for those systems with no builtin sniffer Educause MARC, 2003 Copyright 2002, Marchany 68
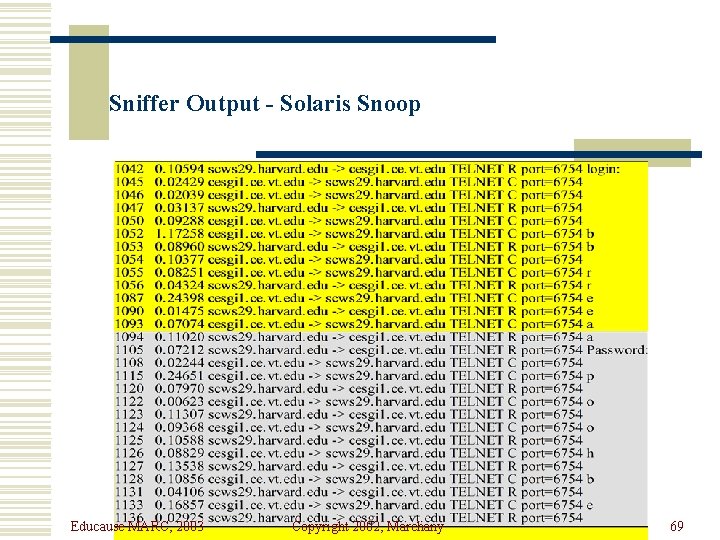
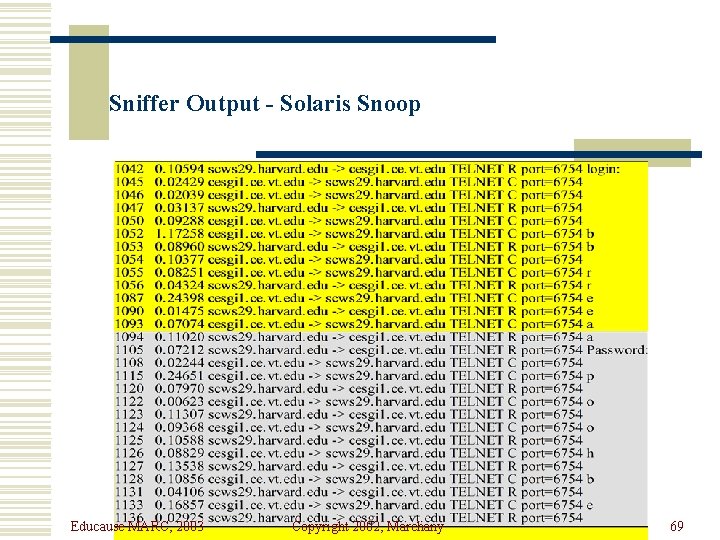
Sniffer Output - Solaris Snoop Educause MARC, 2003 Copyright 2002, Marchany 69
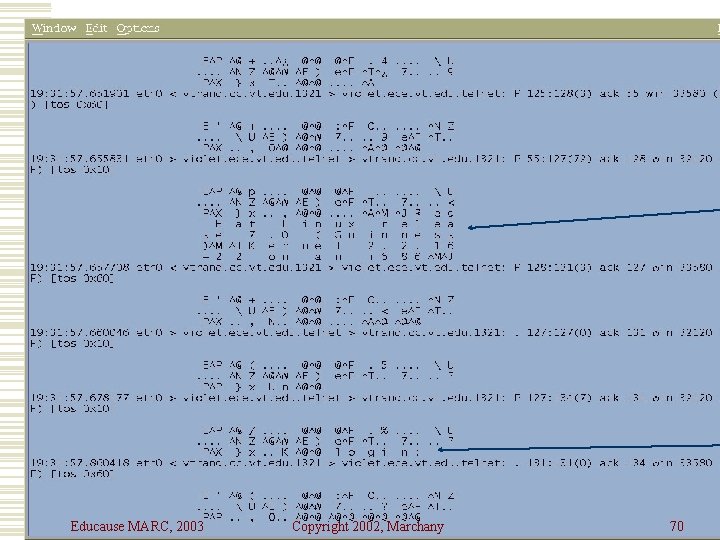
Tcpdump Example Educause MARC, 2003 Copyright 2002, Marchany 70
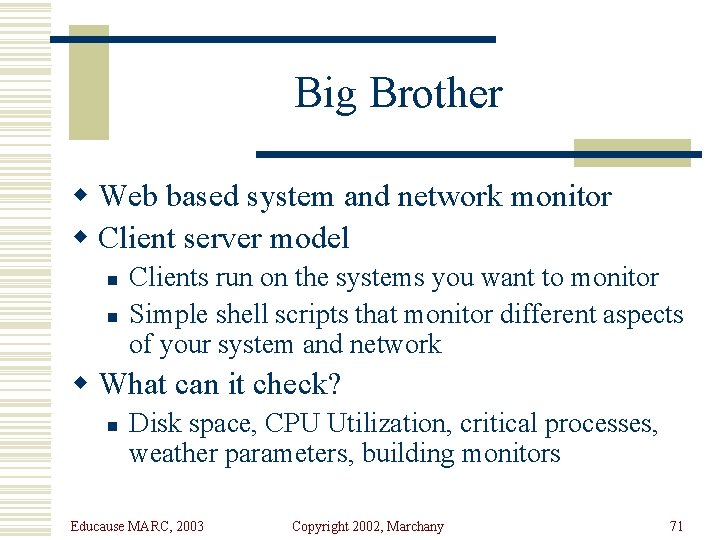
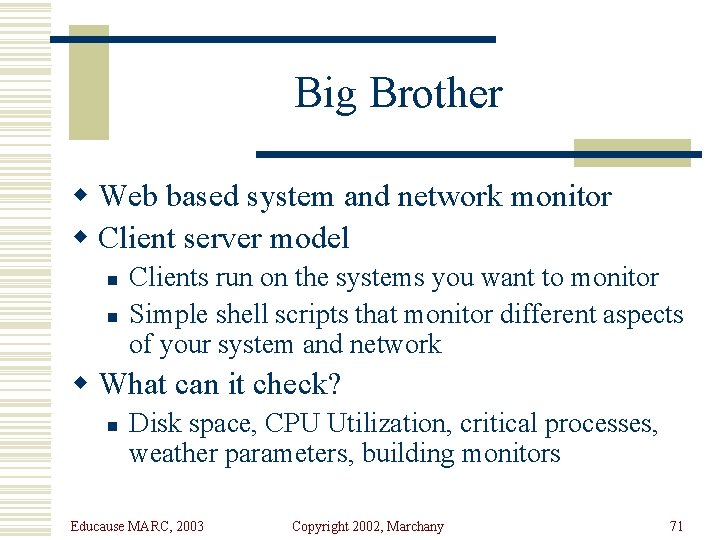
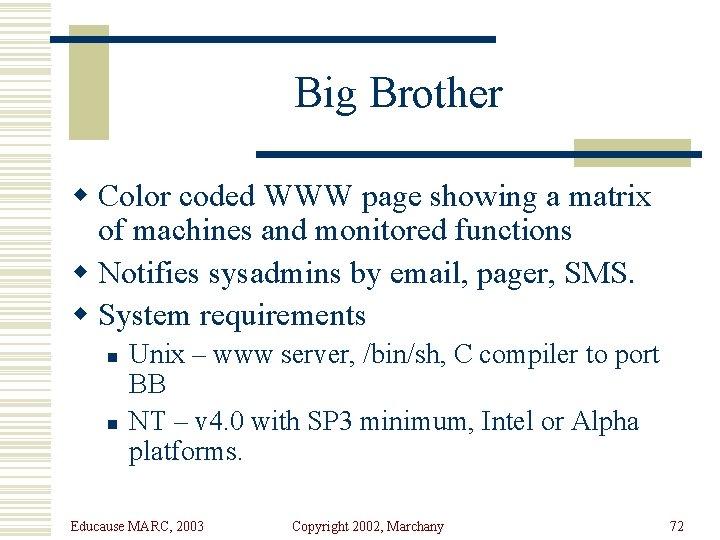
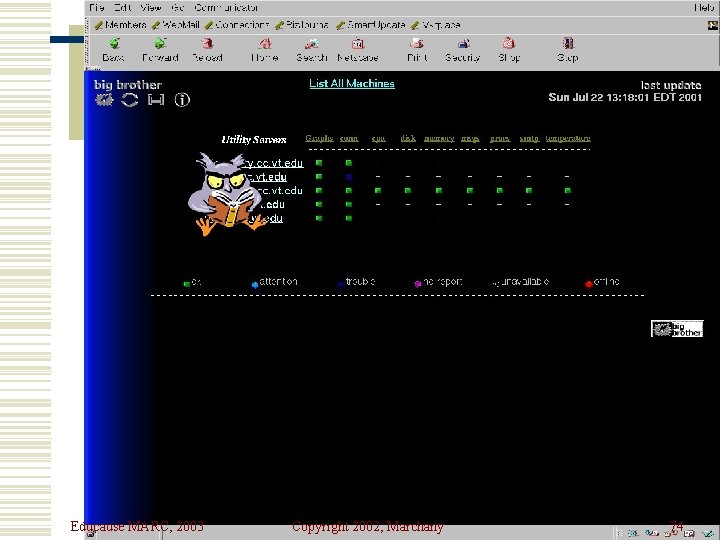
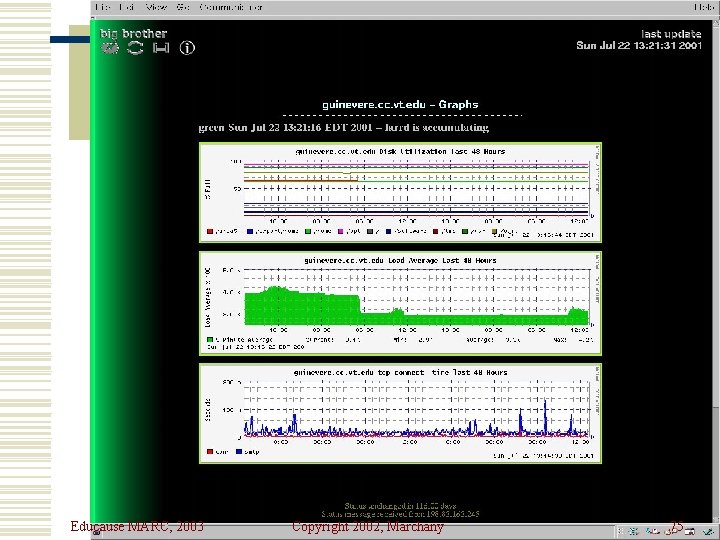
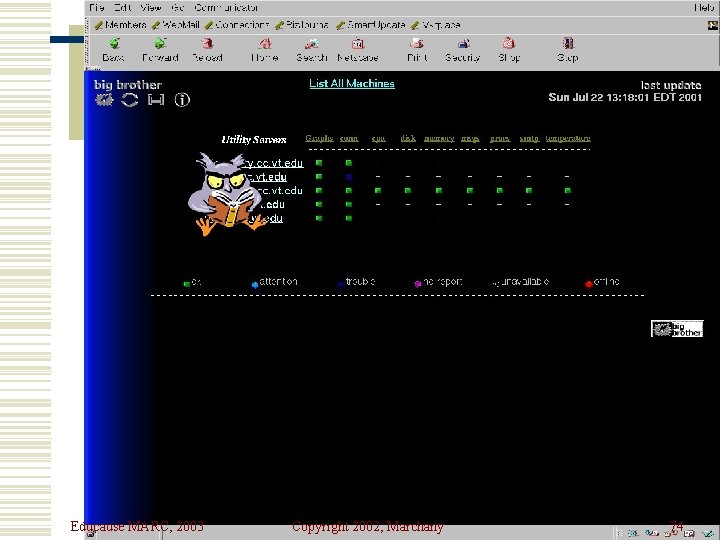
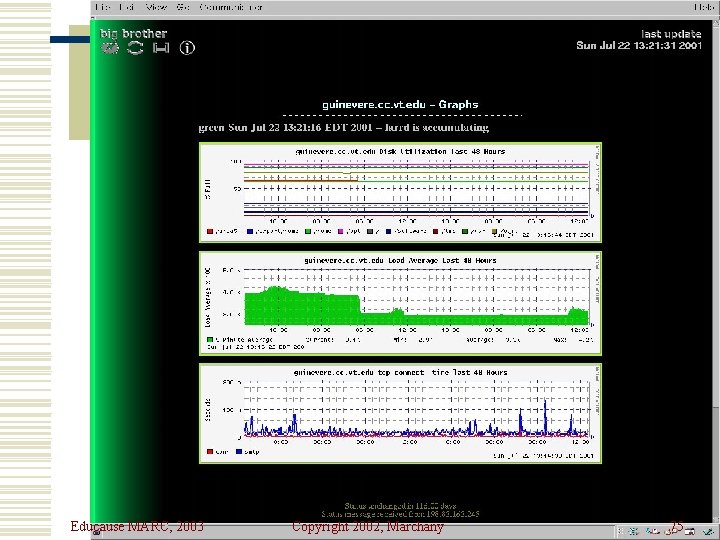
Big Brother w Web based system and network monitor w Client server model n n Clients run on the systems you want to monitor Simple shell scripts that monitor different aspects of your system and network w What can it check? n Disk space, CPU Utilization, critical processes, weather parameters, building monitors Educause MARC, 2003 Copyright 2002, Marchany 71
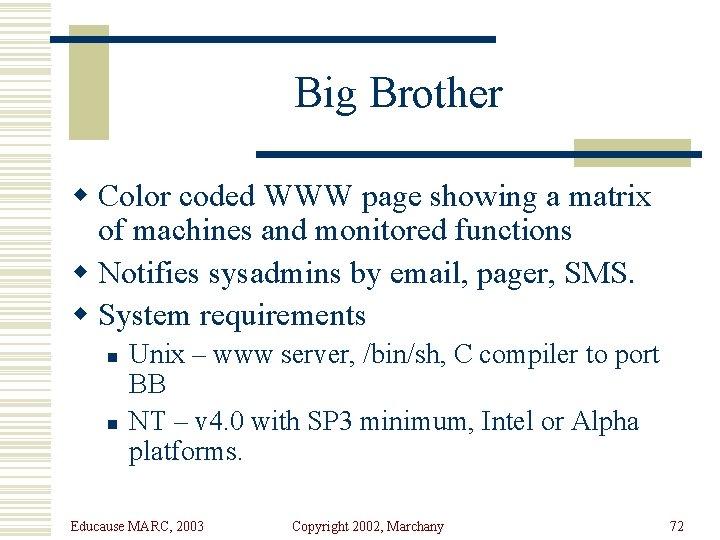
Big Brother w Color coded WWW page showing a matrix of machines and monitored functions w Notifies sysadmins by email, pager, SMS. w System requirements n n Unix – www server, /bin/sh, C compiler to port BB NT – v 4. 0 with SP 3 minimum, Intel or Alpha platforms. Educause MARC, 2003 Copyright 2002, Marchany 72
Educause MARC, 2003 Copyright 2002, Marchany 73
Educause MARC, 2003 Copyright 2002, Marchany 74
Educause MARC, 2003 Copyright 2002, Marchany 75
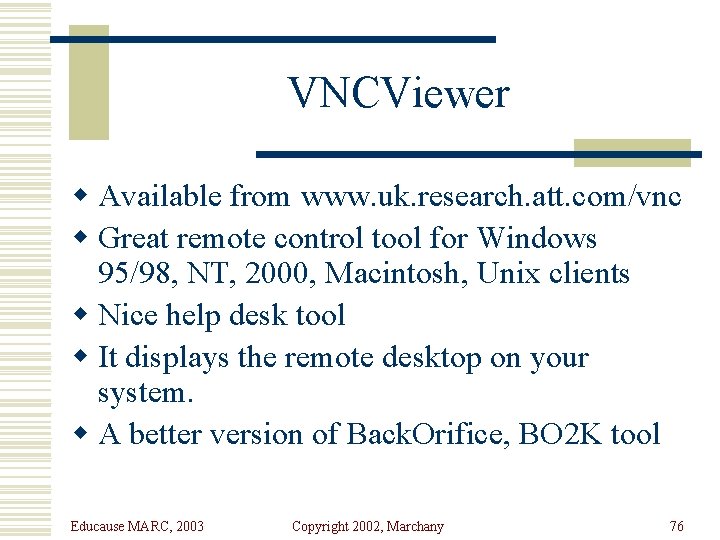
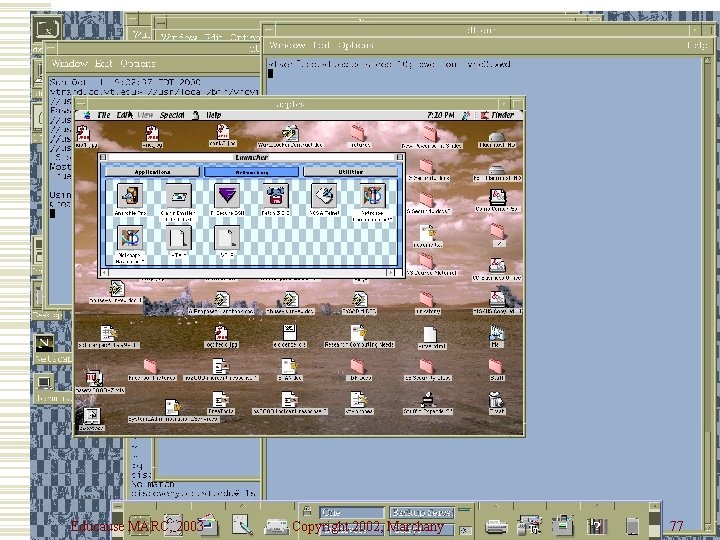
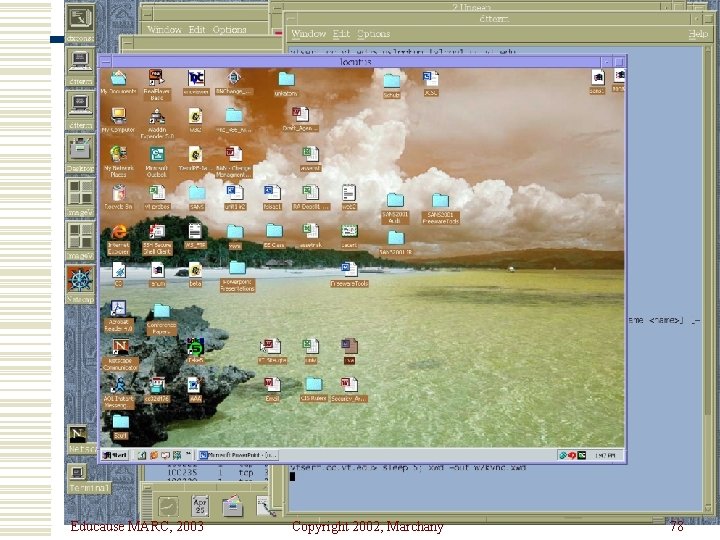
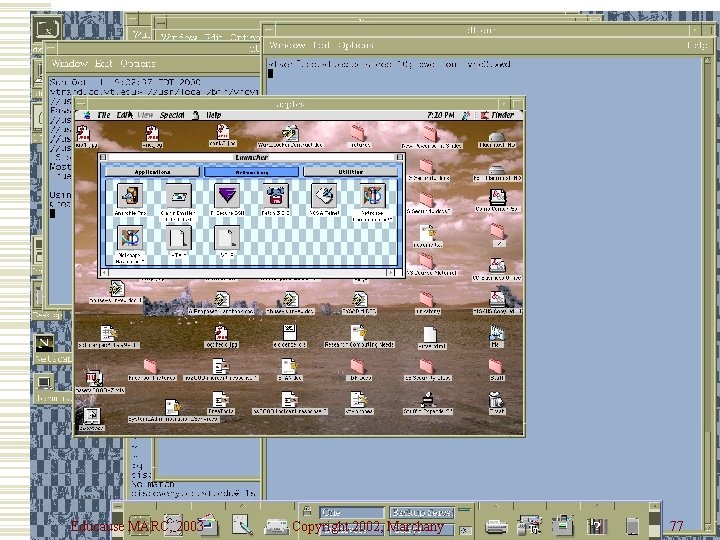
VNCViewer w Available from www. uk. research. att. com/vnc w Great remote control tool for Windows 95/98, NT, 2000, Macintosh, Unix clients w Nice help desk tool w It displays the remote desktop on your system. w A better version of Back. Orifice, BO 2 K tool Educause MARC, 2003 Copyright 2002, Marchany 76
Educause MARC, 2003 Copyright 2002, Marchany 77
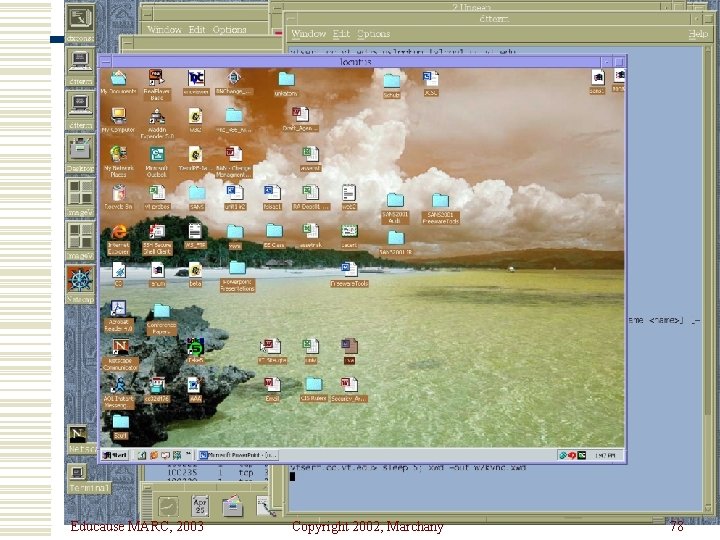
Educause MARC, 2003 Copyright 2002, Marchany 78
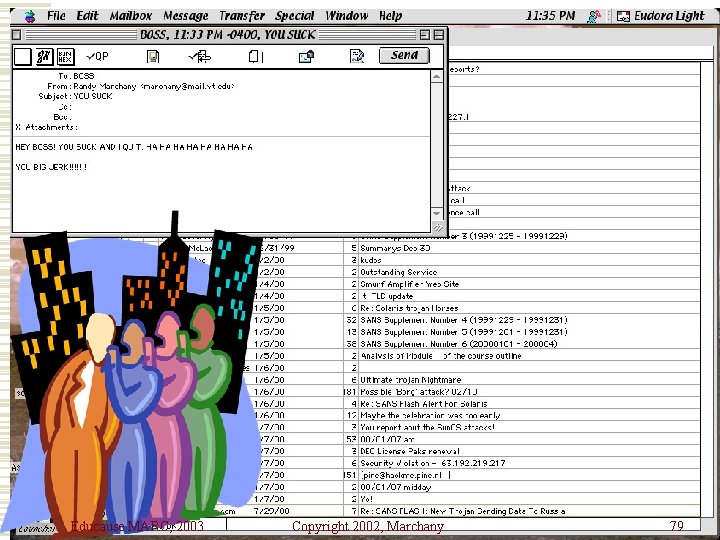
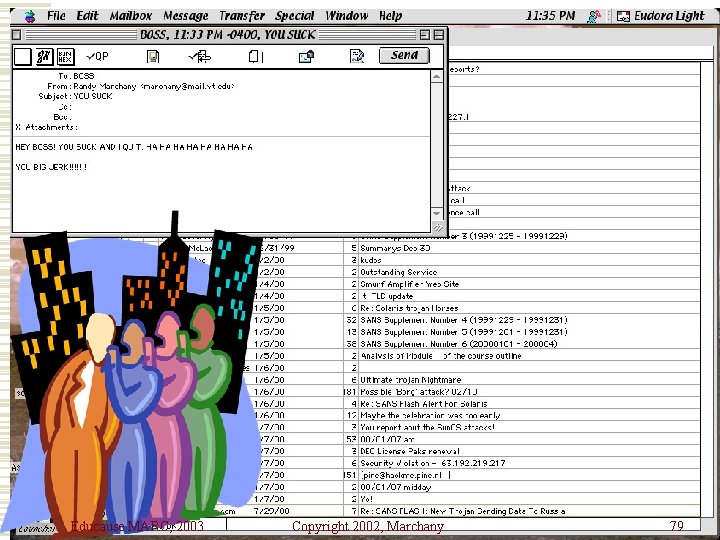
Educause MARC, 2003 Copyright 2002, Marchany 79
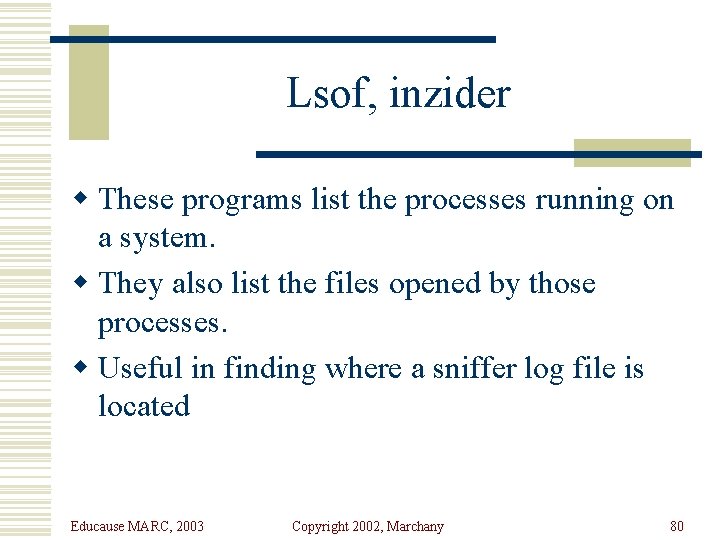
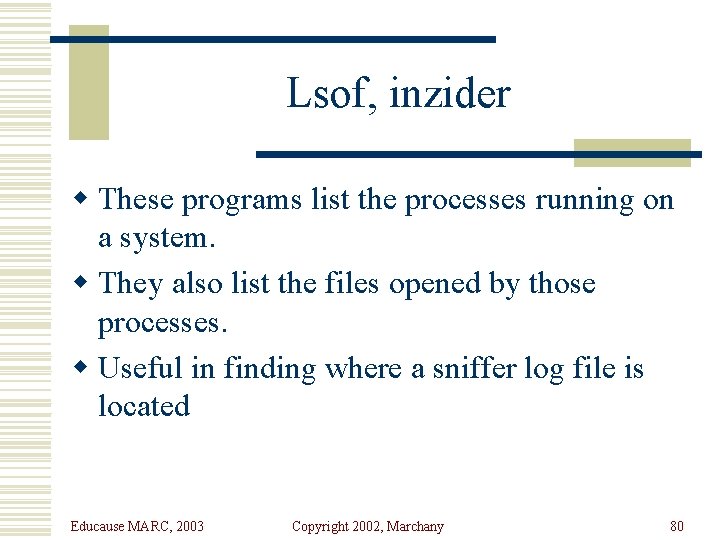
Lsof, inzider w These programs list the processes running on a system. w They also list the files opened by those processes. w Useful in finding where a sniffer log file is located Educause MARC, 2003 Copyright 2002, Marchany 80
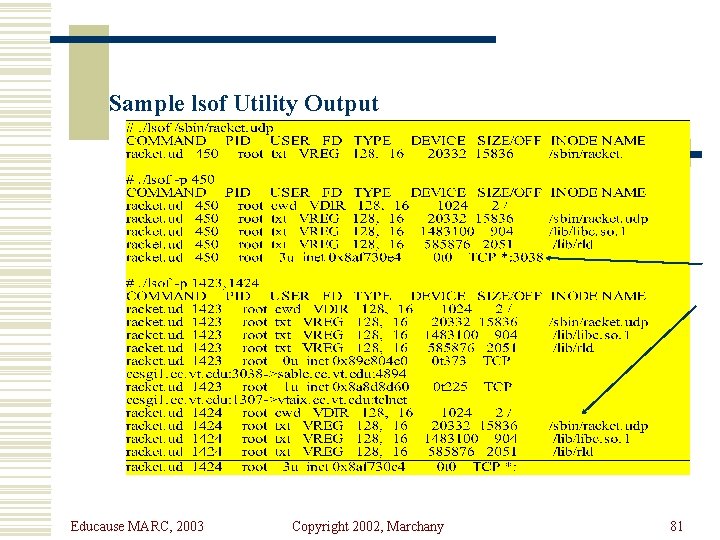
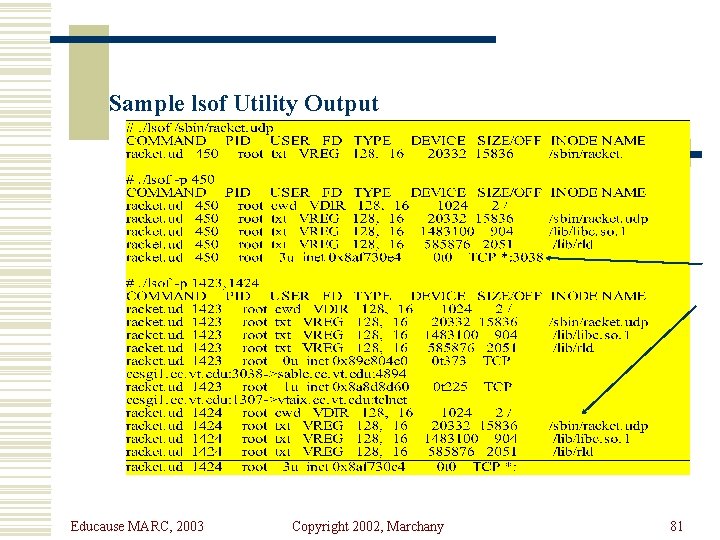
Sample lsof Utility Output Educause MARC, 2003 Copyright 2002, Marchany 81
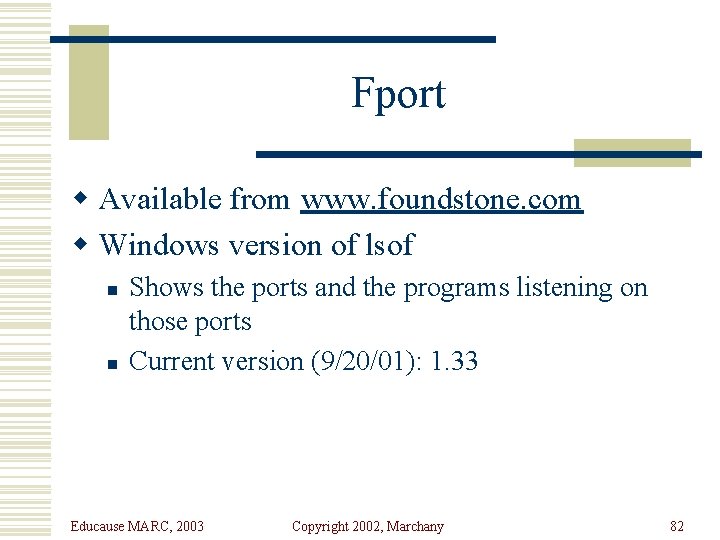
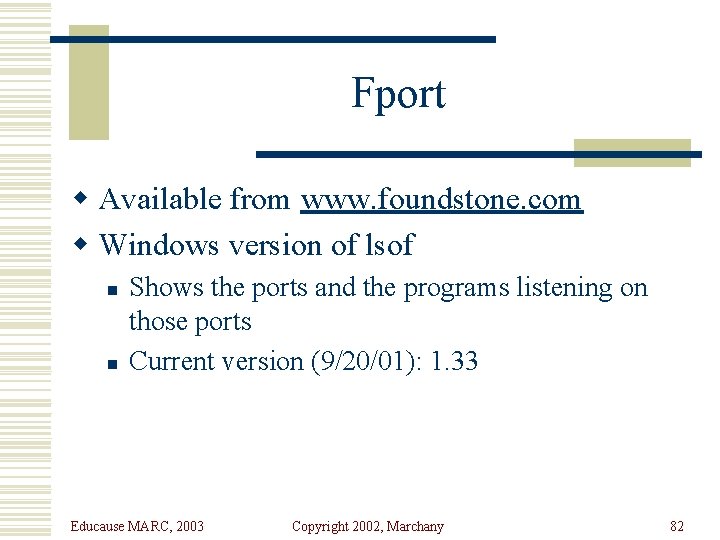
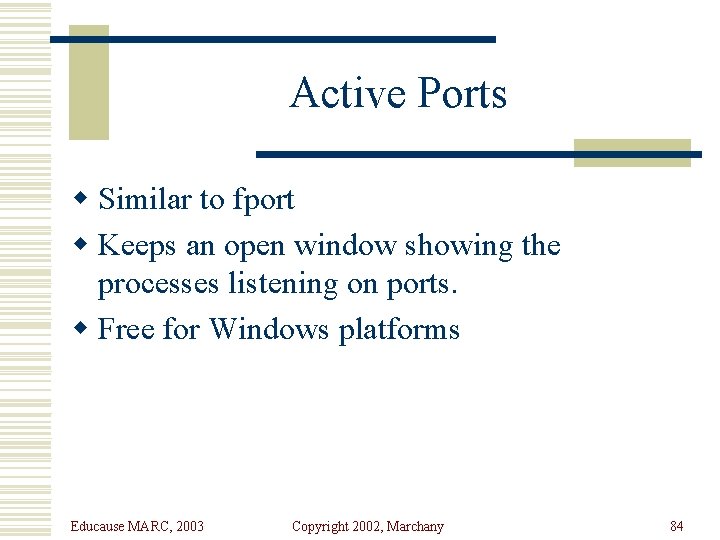
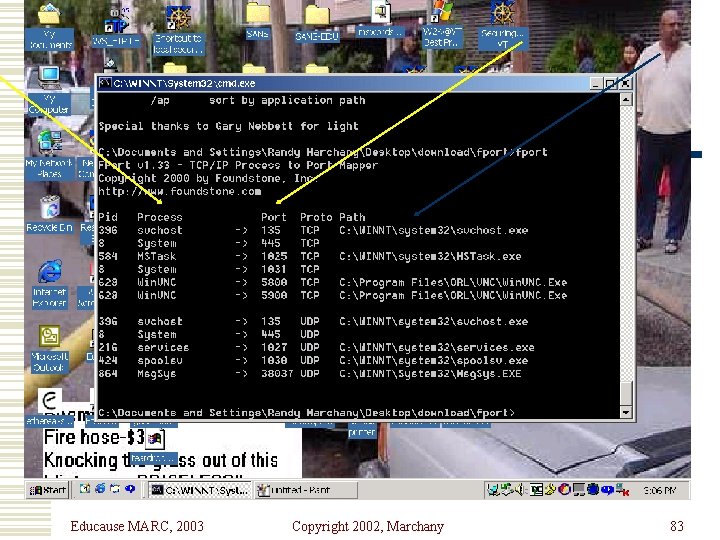
Fport w Available from www. foundstone. com w Windows version of lsof n n Shows the ports and the programs listening on those ports Current version (9/20/01): 1. 33 Educause MARC, 2003 Copyright 2002, Marchany 82
Educause MARC, 2003 Copyright 2002, Marchany 83
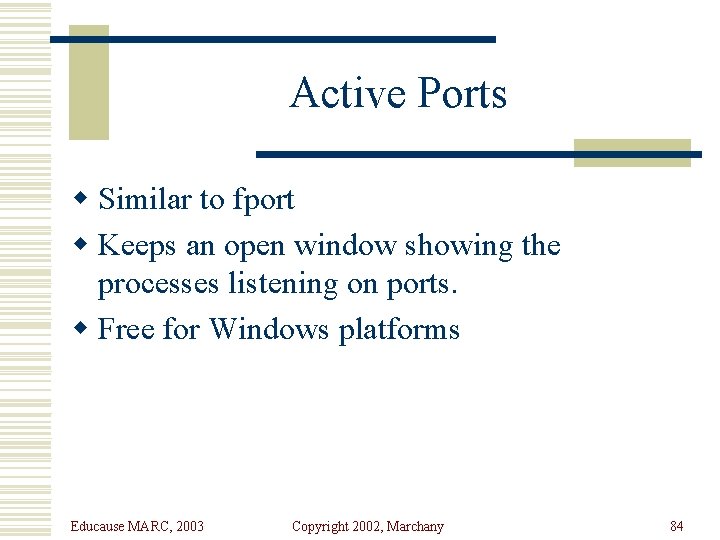
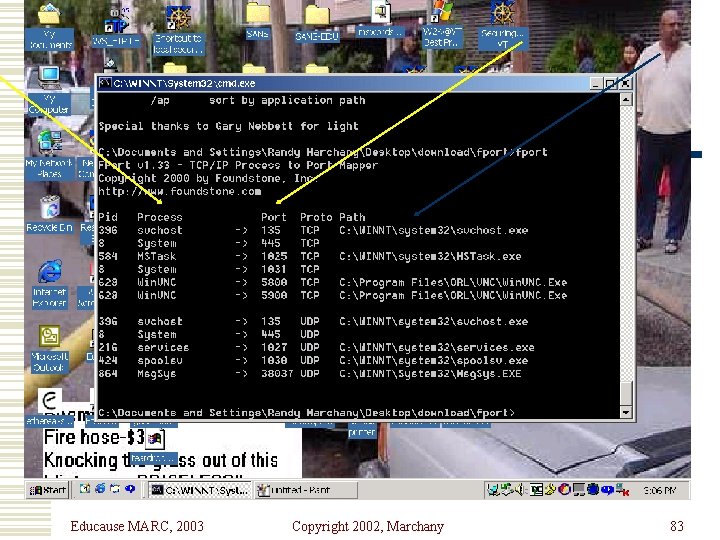
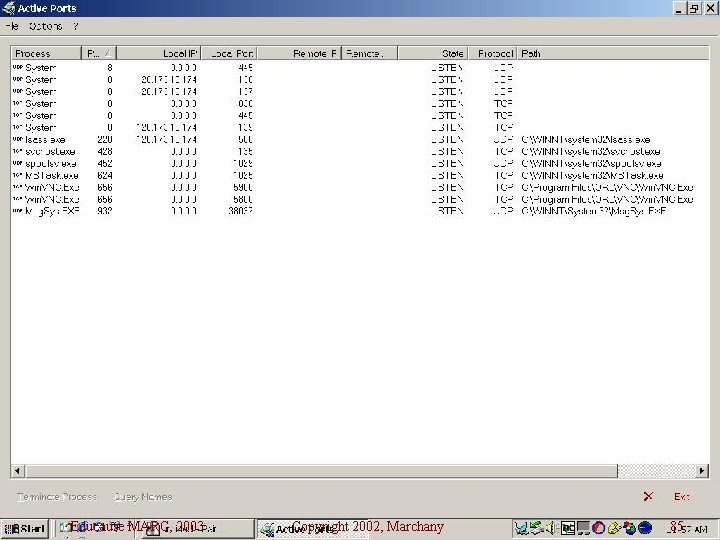
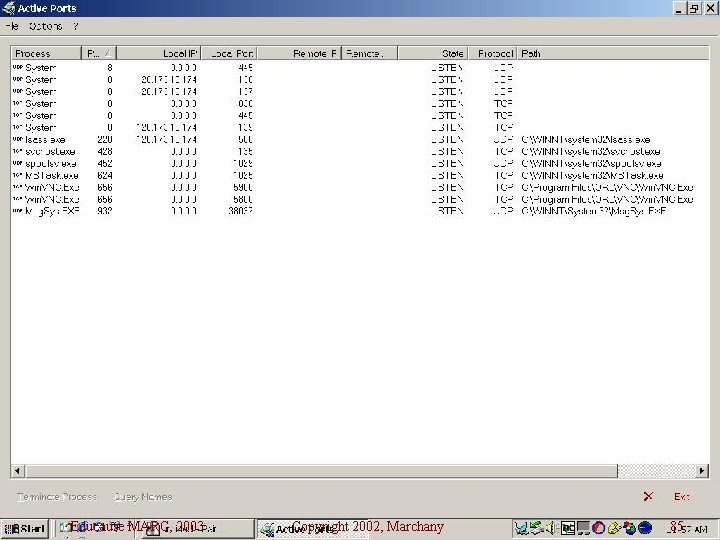
Active Ports w Similar to fport w Keeps an open window showing the processes listening on ports. w Free for Windows platforms Educause MARC, 2003 Copyright 2002, Marchany 84
Educause MARC, 2003 Copyright 2002, Marchany 85
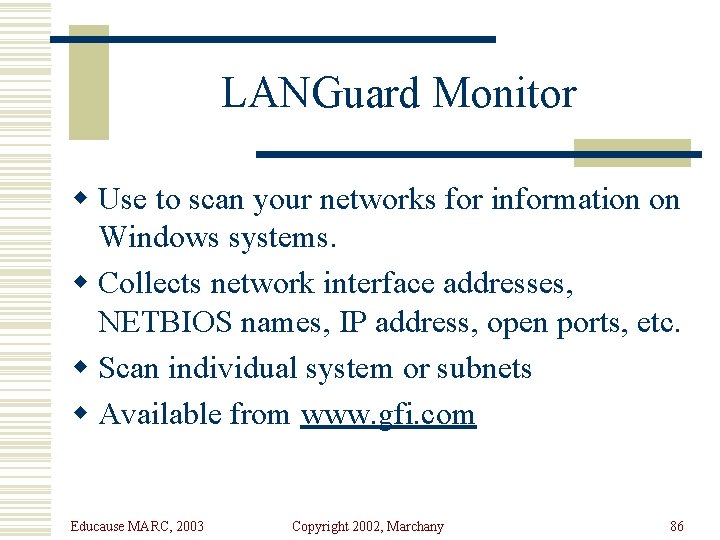
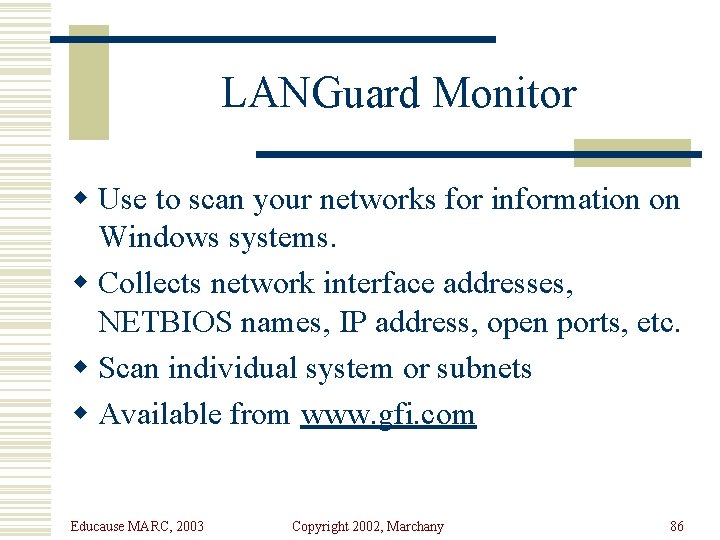
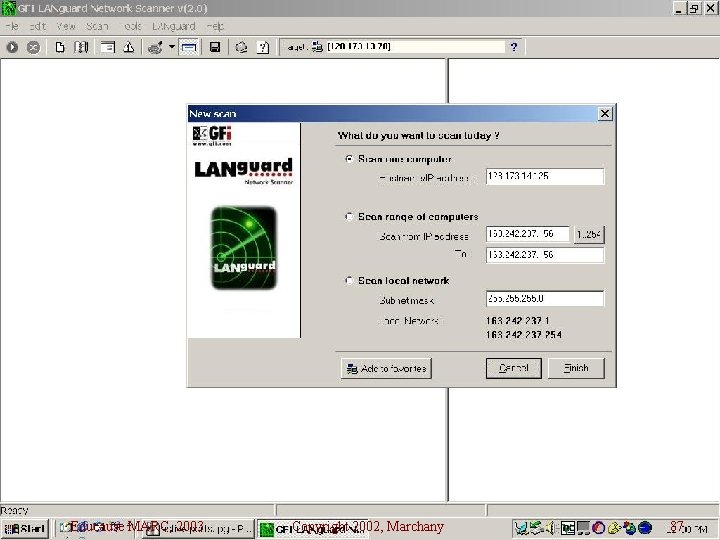
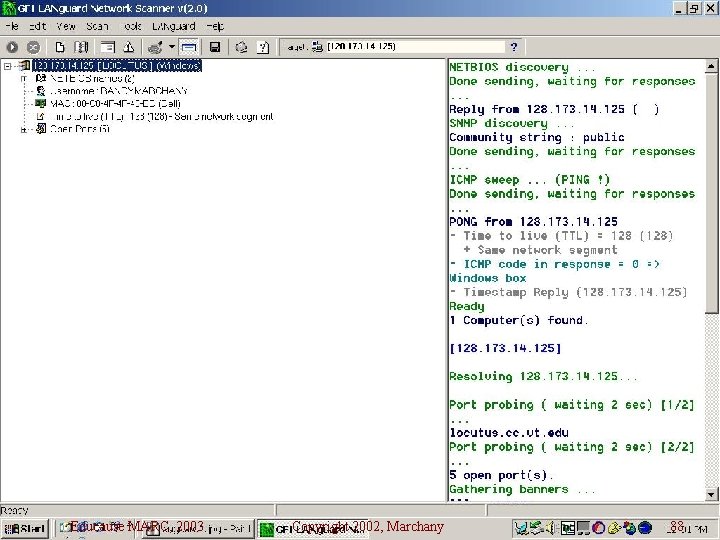
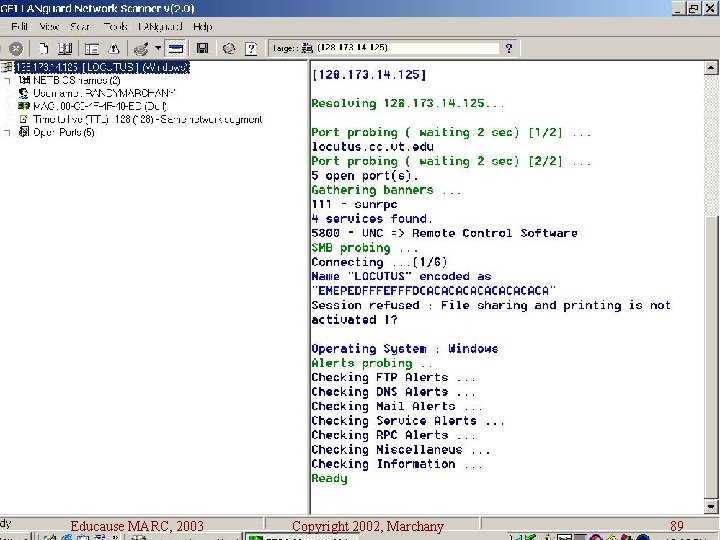
LANGuard Monitor w Use to scan your networks for information on Windows systems. w Collects network interface addresses, NETBIOS names, IP address, open ports, etc. w Scan individual system or subnets w Available from www. gfi. com Educause MARC, 2003 Copyright 2002, Marchany 86
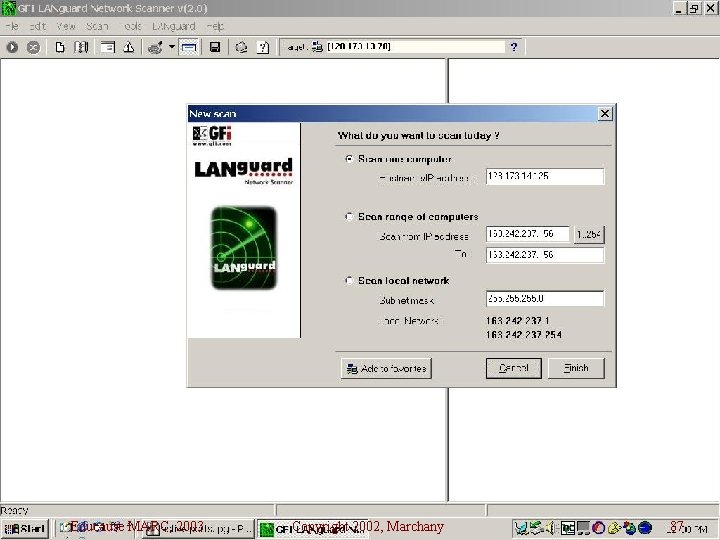
Educause MARC, 2003 Copyright 2002, Marchany 87
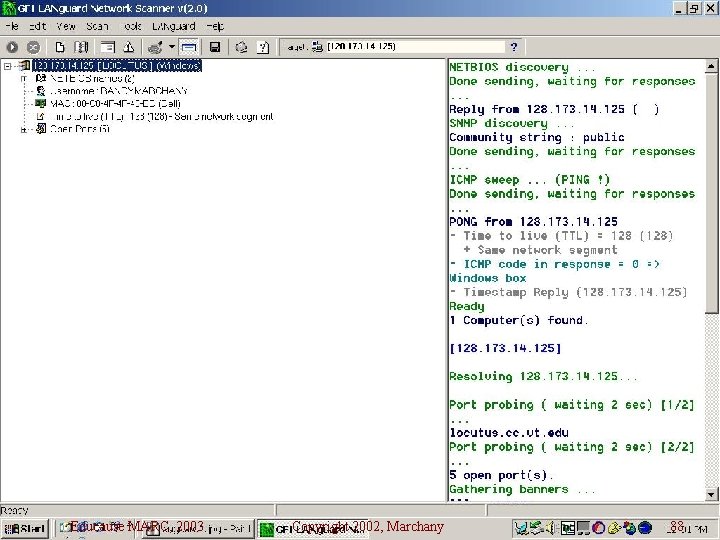
Educause MARC, 2003 Copyright 2002, Marchany 88
Educause MARC, 2003 Copyright 2002, Marchany 89
Sysadmin Tools w Sudo n n n Unix access control is all (root) or nothing (user). Some commands (backup, restore) are restricted to root but are really an OPER class command. You don’t want an operator to have root access but you want them to do backups. Sudo lets you set up this “pseudo” privilege scheme. Educause MARC, 2003 Copyright 2002, Marchany 90
Sudo w Sudo uses user identity and host to restrict the commands the user can run in “root” mode. w It is a restricted root shell. w User is prompted for a special password that allows them to run the command. Educause MARC, 2003 Copyright 2002, Marchany 91
Sudo w The sudoers files lists the commands, shells, hosts that a user can execute commands w Should always list the full path name for the commands w Notifies sysadmins if illegal uses of sudo is attempted. w Notifies sysadmins if user in sudoers tries to run a restricted command Educause MARC, 2003 Copyright 2002, Marchany 92
Proactive Password Tools w Most newer OS allow you to set password rules in config files. w Crack is still the best of the bunch. w Npasswd and passwd+ are two older but still effective tools. w Npasswd is a good tool for those who don’t want to spend a lot of time configuring a password checker w Passwd+ requires more configuration time. Educause MARC, 2003 Copyright 2002, Marchany 93
Crack w The first of the really good password crackers. Available on the net for the past 10 years. w Easy to customize. Works on non-shadow password files. Use a preprocessor to rebuild in old format or use NIS, NIS+ . Can be distributed among systems w http; //www. users. dircon. co. uk/~crypto/ w Crack Results Example Educause MARC, 2003 Copyright 2002, Marchany 94
npasswd w Uses ASCII dictionaries or DBM format dictionaries. If the password is in the dictionary, it’s rejected. Case and reversed word checks are done. w Does singlecase (Yes/No) checks n Allow passwords in one case. Default = No. w Does Control Character (Yes/No) checks. n Allows passwords with ASCII control characters in them. Default = Yes. w Does min/max length checks. Educause MARC, 2003 Copyright 2002, Marchany 95
npasswd w Checks for 3 sequential occurrences of the same character. This value can be modified. w Does illegal character check. (^C, ^D, ^G, ^J, ^M, ^O, ^Q, etc. w Good, quick easy tool to use. Educause MARC, 2003 Copyright 2002, Marchany 96
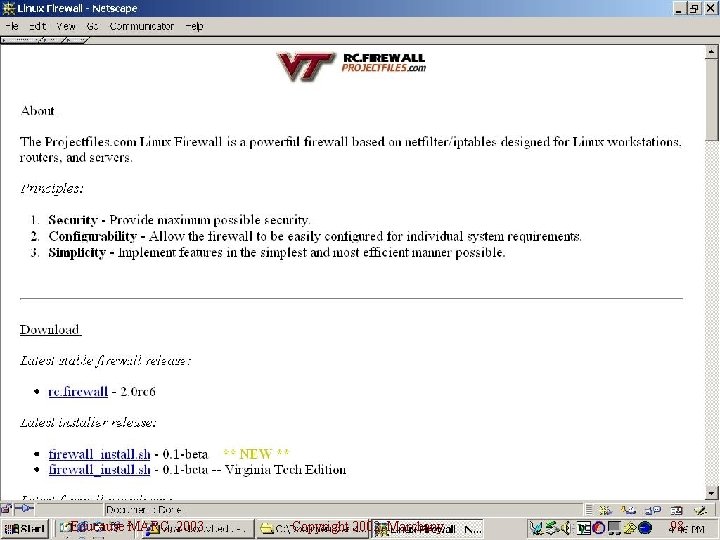
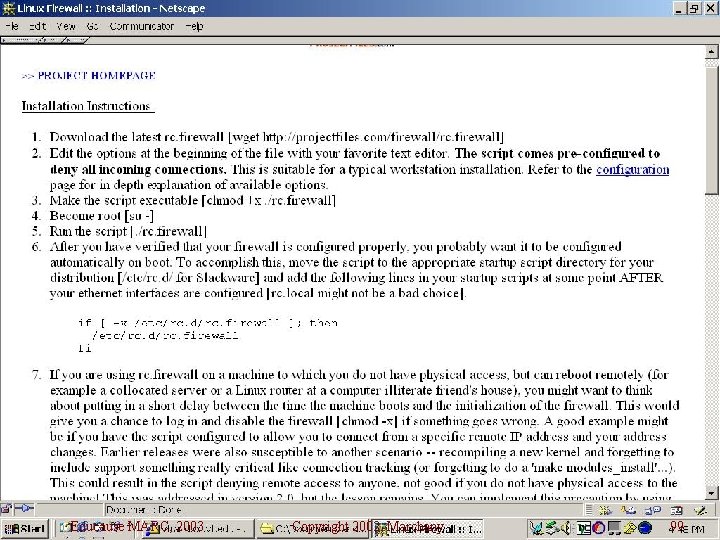
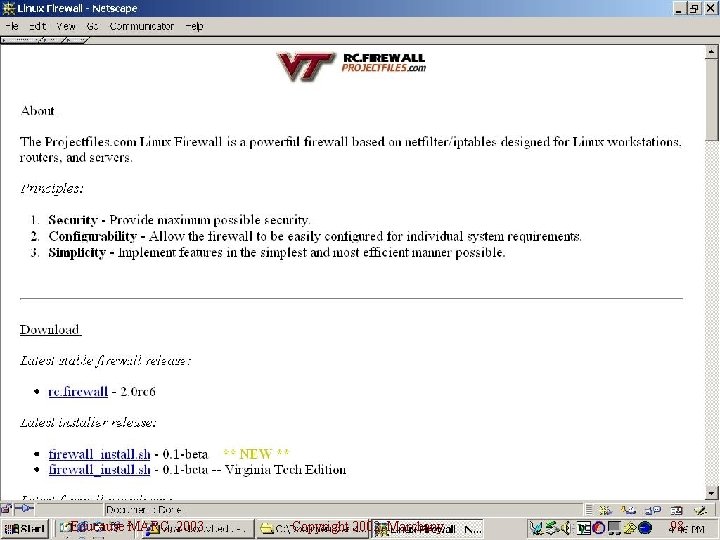
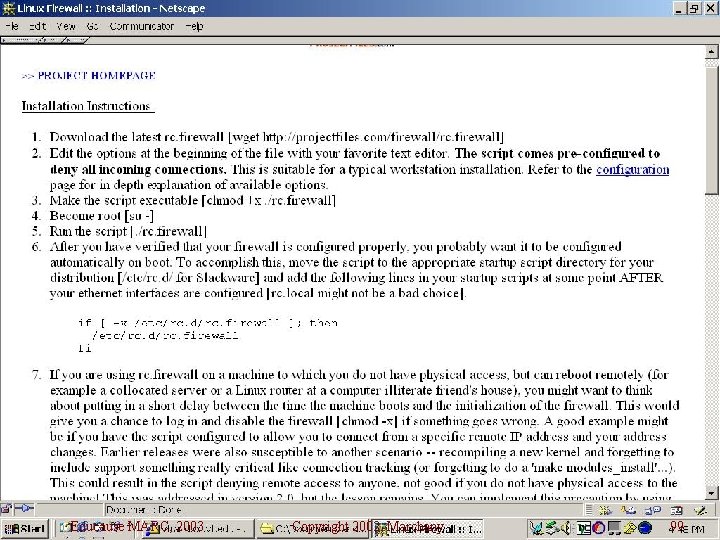
Home Grown Tools w Build specific packages for the tools n n n Preconfigured with your site information Easy to install (pkgadd, RPM) Put on a CD so you can configure the machines offline. Preconfigured Tripwire, SSH, IP Filters, lsof, l CIS Security Benchmark scripts l Other Firewall installation scripts l Educause MARC, 2003 Copyright 2002, Marchany 97
Educause MARC, 2003 Copyright 2002, Marchany 98
Educause MARC, 2003 Copyright 2002, Marchany 99
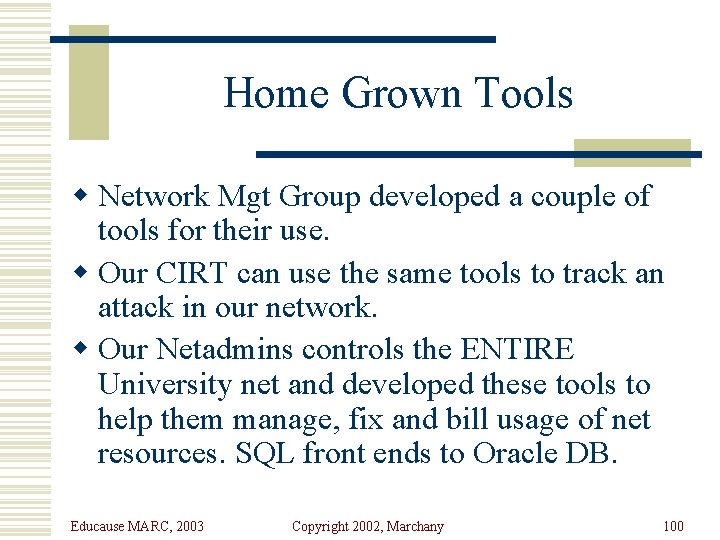
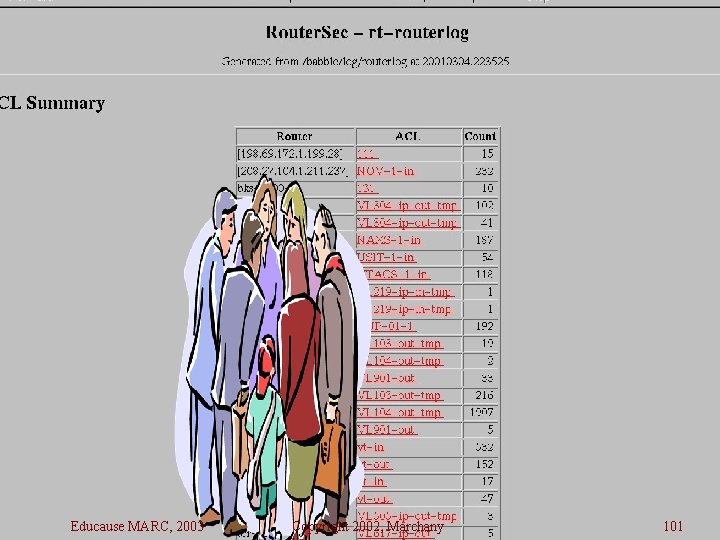
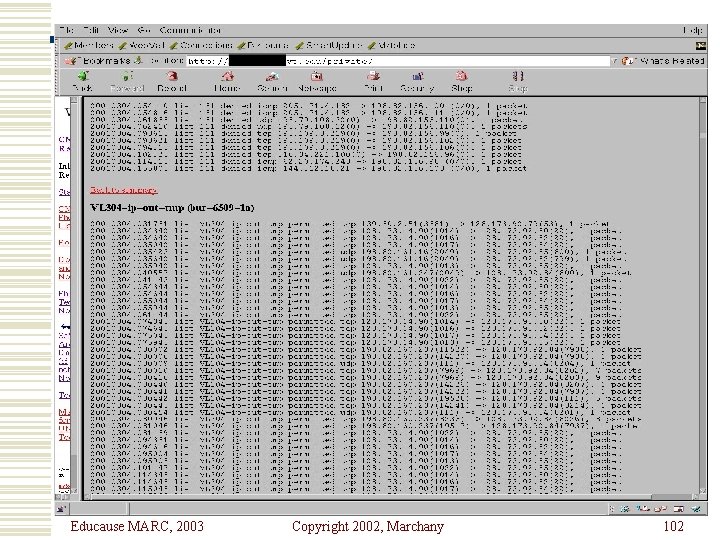
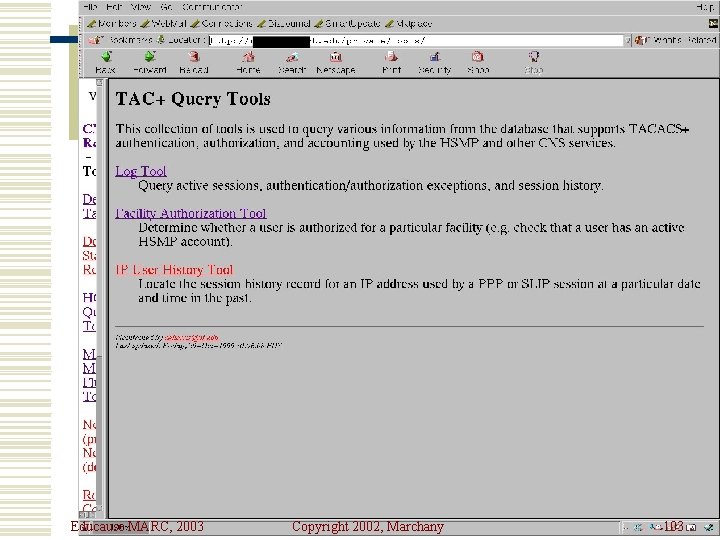
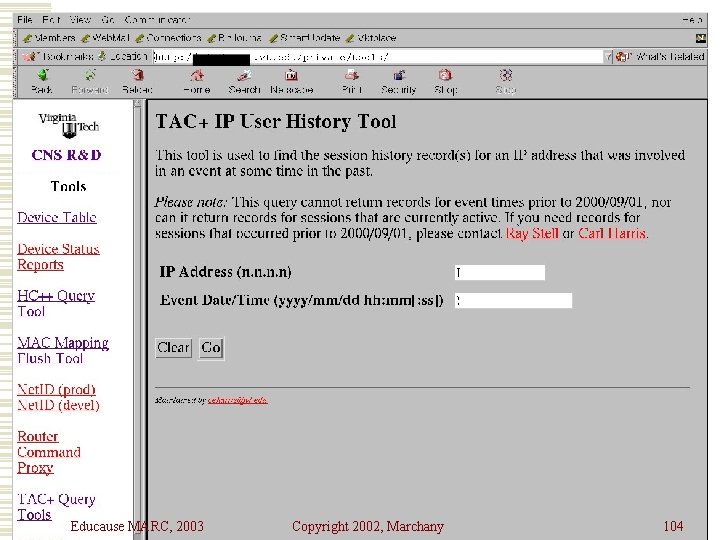
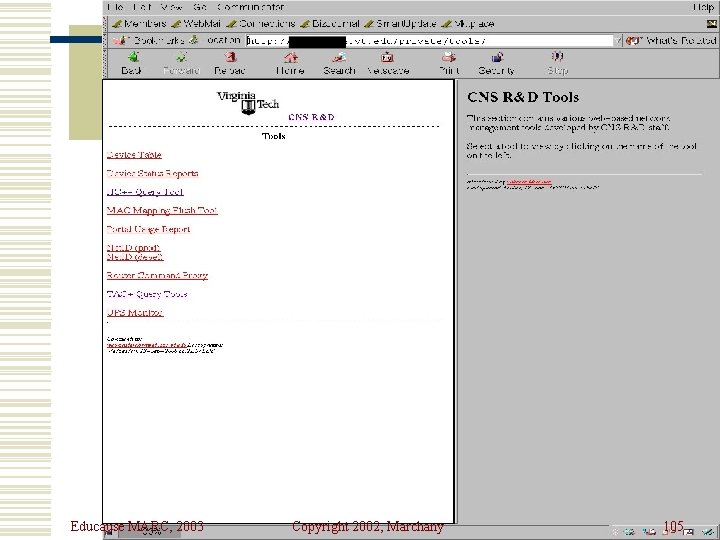
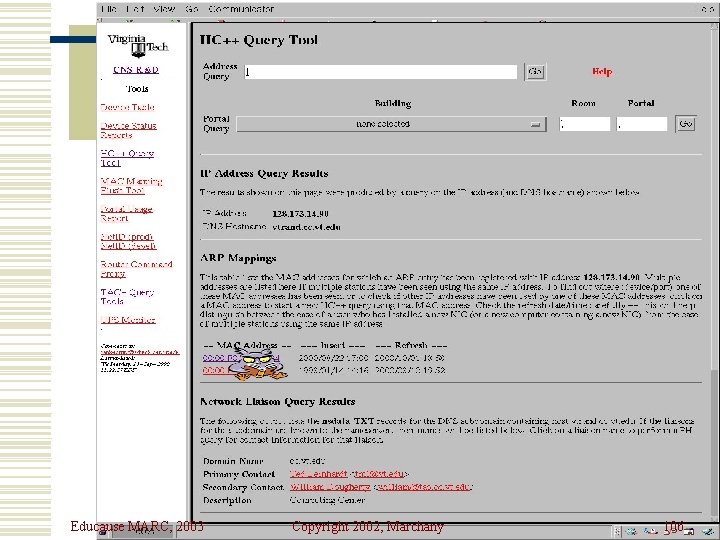
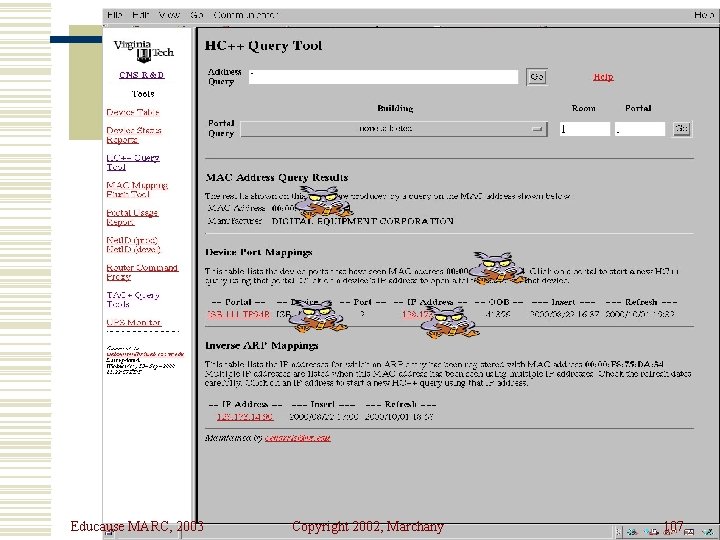
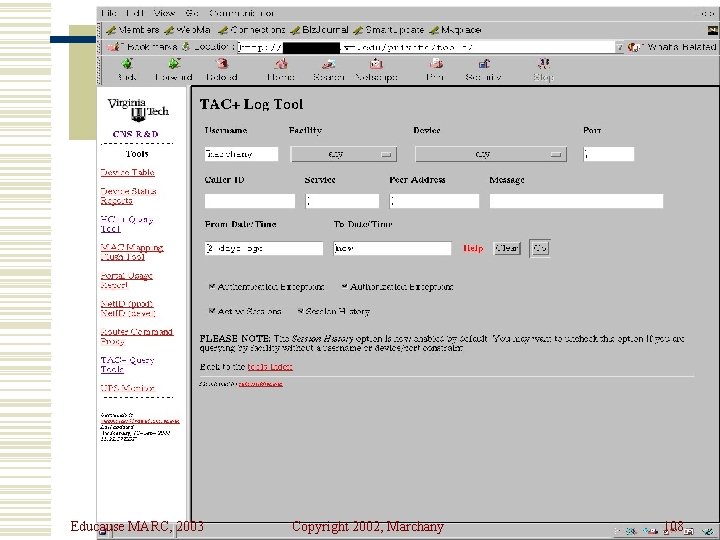
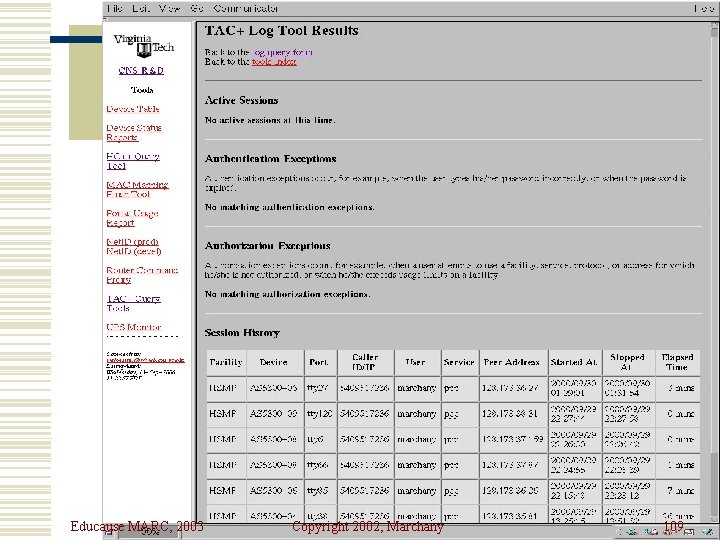
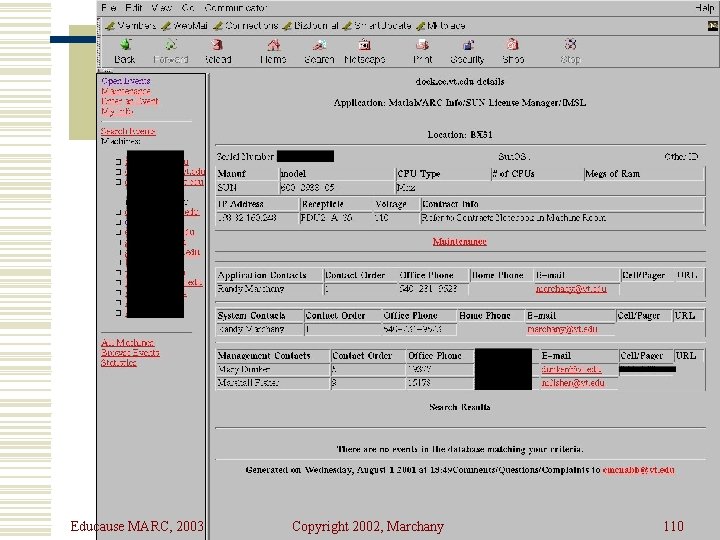
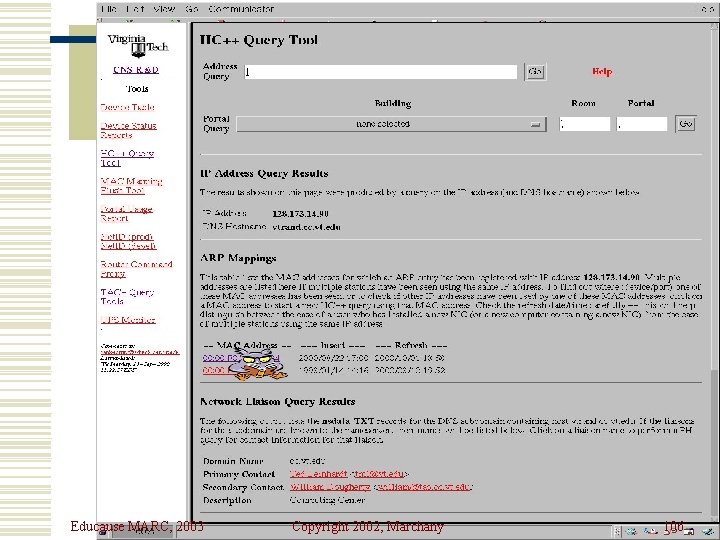
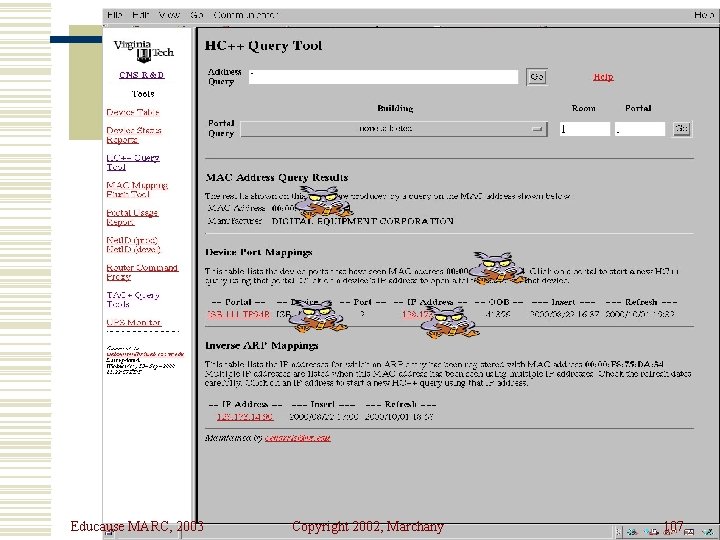
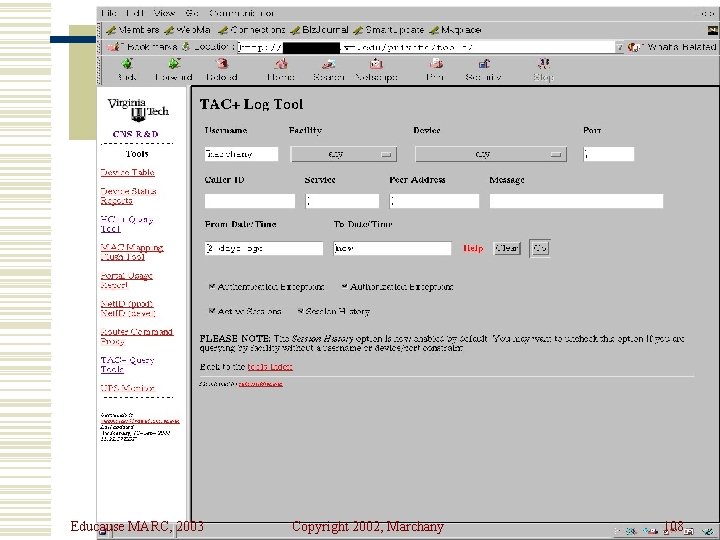
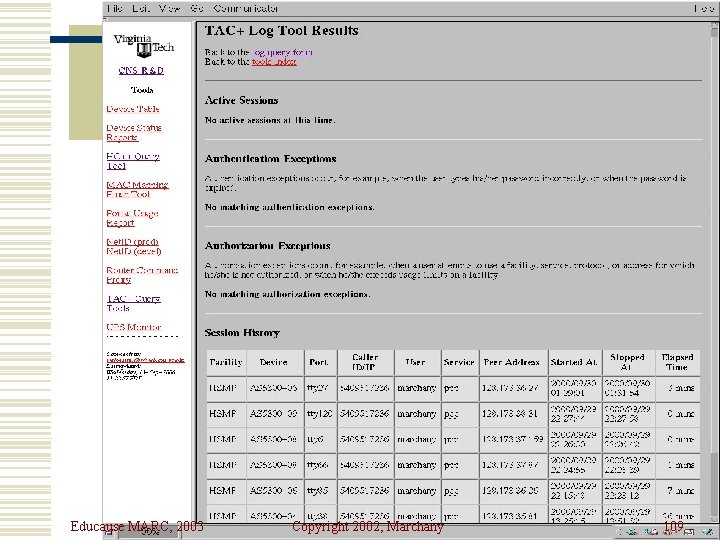
Home Grown Tools w Network Mgt Group developed a couple of tools for their use. w Our CIRT can use the same tools to track an attack in our network. w Our Netadmins controls the ENTIRE University net and developed these tools to help them manage, fix and bill usage of net resources. SQL front ends to Oracle DB. Educause MARC, 2003 Copyright 2002, Marchany 100
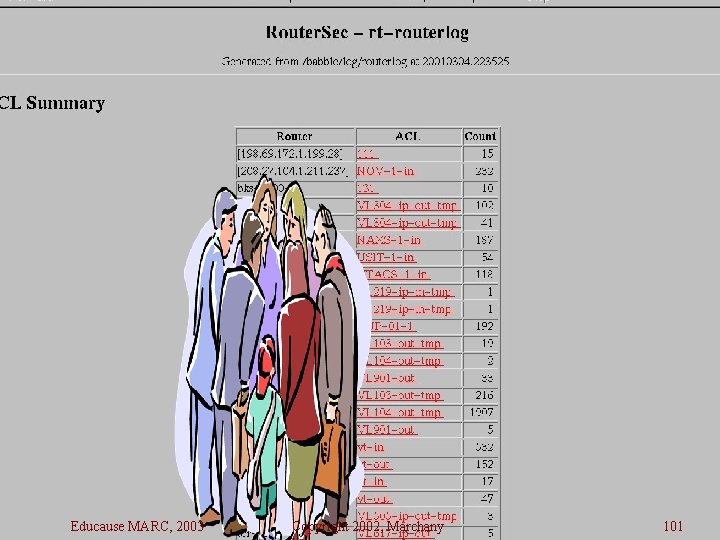
Educause MARC, 2003 Copyright 2002, Marchany 101
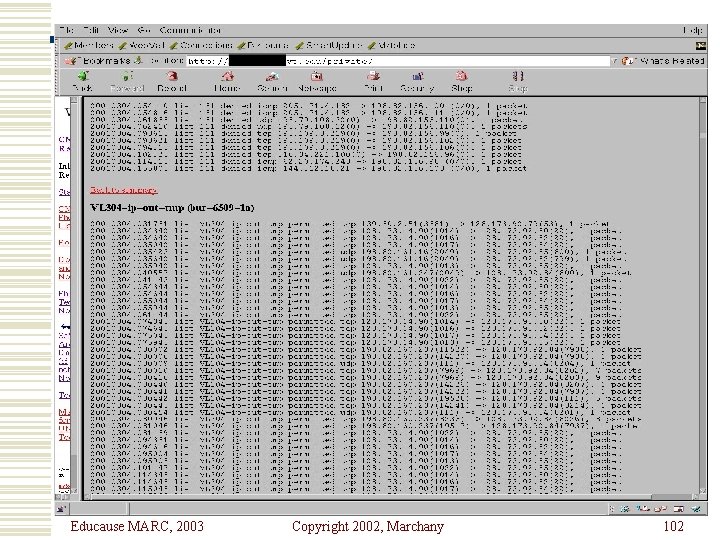
Educause MARC, 2003 Copyright 2002, Marchany 102
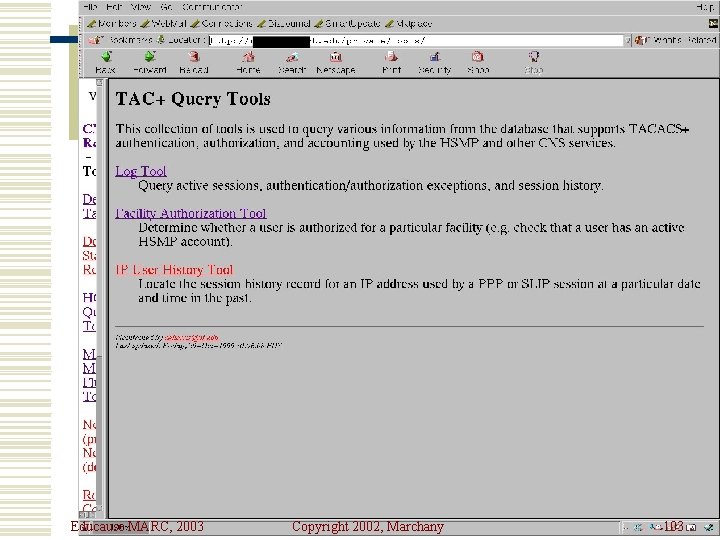
Educause MARC, 2003 Copyright 2002, Marchany 103
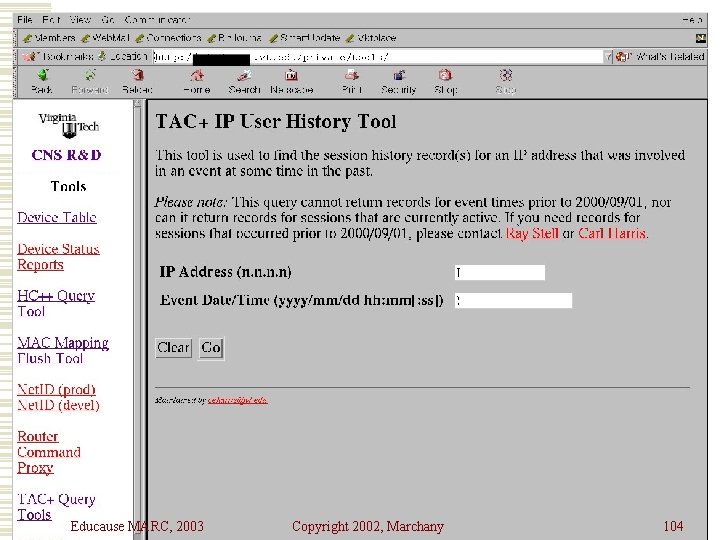
Educause MARC, 2003 Copyright 2002, Marchany 104
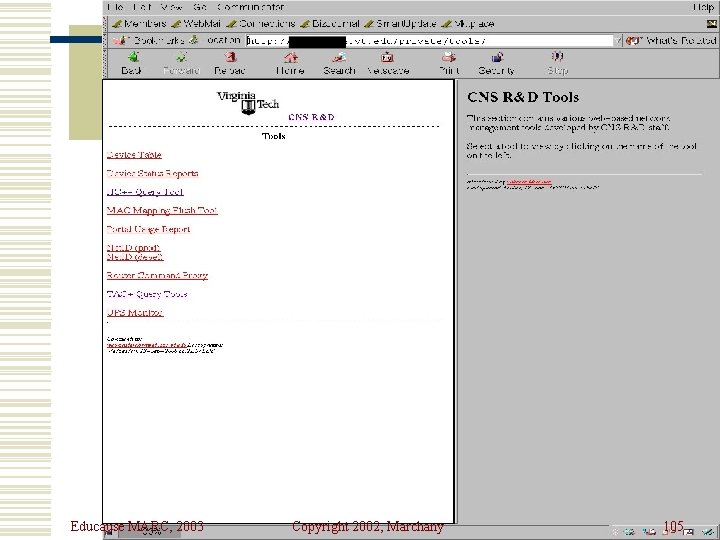
Educause MARC, 2003 Copyright 2002, Marchany 105
Educause MARC, 2003 Copyright 2002, Marchany 106
Educause MARC, 2003 Copyright 2002, Marchany 107
Educause MARC, 2003 Copyright 2002, Marchany 108
Educause MARC, 2003 Copyright 2002, Marchany 109
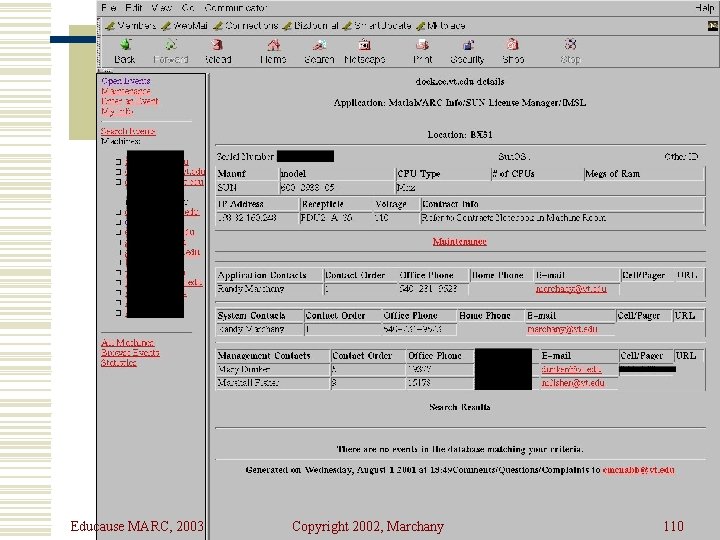
Educause MARC, 2003 Copyright 2002, Marchany 110
Using the Tools – A Strategy w Preparation w Detection w Containment w Eradication w Recovery w Followup Educause MARC, 2003 Copyright 2002, Marchany 111
Preparation w Unix Host Systems n Install TCP Wrappers, Portsentry, logcheck, tripwire, lsof, ipfilter w NT/2000 n Inzider, syslog converters w Network n n Ingress, egress filters in place Router logs in place Educause MARC, 2003 Copyright 2002, Marchany 112
Detection w Portsentry, TCP wrappers, Personal Firewall tools usually send the first alarm. w Network router filters may trigger an alarm as well. w Once an event is detected, reaction mechanisms are enabled Educause MARC, 2003 Copyright 2002, Marchany 113
Containment w Detection tools give the source IP address. w Router blocks may be enabled to prevent additional attacks. w HC++ tool used to isolate offending system w Portsentry or PFW tools prevent further access to the systems Educause MARC, 2003 Copyright 2002, Marchany 114
Eradication w HC++ tool used to shut off internal port. w Router blocks on external IP address. w Tripwire used to remove offending files. w Network backup software can be used to verify this. Why? Most network backup software does incremental backups so they can capture a newly installed file. Educause MARC, 2003 Copyright 2002, Marchany 115
Recovery w “Jumpstart” style OS installation w Network and regular backup software w File servers may limit the damage Educause MARC, 2003 Copyright 2002, Marchany 116
Followup w See what components worked. n n n Could additional scanning detect the holes? How fast did the reaction mechanisms work? Internal network tools work? Backup procedures work? What didn’t work? Why? How? Educause MARC, 2003 Copyright 2002, Marchany 117
Summary w There are some excellent freeware tools that will help you with sysadmin and security issues at your site. w Use these tools to gain experience in evaluating vendor tools. w A combination of vendor and freeware tools is desired w There are MORE tools out there. Educause MARC, 2003 Copyright 2002, Marchany 118
Where to Get the Tools w Http: //ciac. llnl. gov n TCP Wrappers, crack, tcpdump, lsof w Http: //www. wwdsi. com n SAINT w Http: //www. www-arc. com/sara n SARA w Http: //www. tripwire. com n tripwire Educause MARC, 2003 Copyright 2002, Marchany 119
Where to Get the Tools w Http: //www. psionic. com n Logcheck, portsentry w Http: //www. uk. research. att. com/vnc n VNCViewer w Http: //www. insecure. org n Nmap w Http: //www. ssh. org n SSH Educause MARC, 2003 Copyright 2002, Marchany 120
Where to Get the Tools w www. nessus. org n Nessus w http: //packetstormsecurity. com Educause MARC, 2003 Copyright 2002, Marchany 121