Understanding Microsofts Forefront Security Solution For Businesses Steve

Understanding Microsoft’s Forefront™ Security Solution For Businesses Steve Lamb Technical Security Advisor Microsoft Ltd http: //blogs. technet. com/steve_lamb mailto: //stephen. lamb@microsoft. com

Agenda Strategy Client Security Server Applications Network Edge Windows Networking Solutions

Microsoft’s Promises To You Enabling IT Pros & Development Teams across the IT Lifecycle
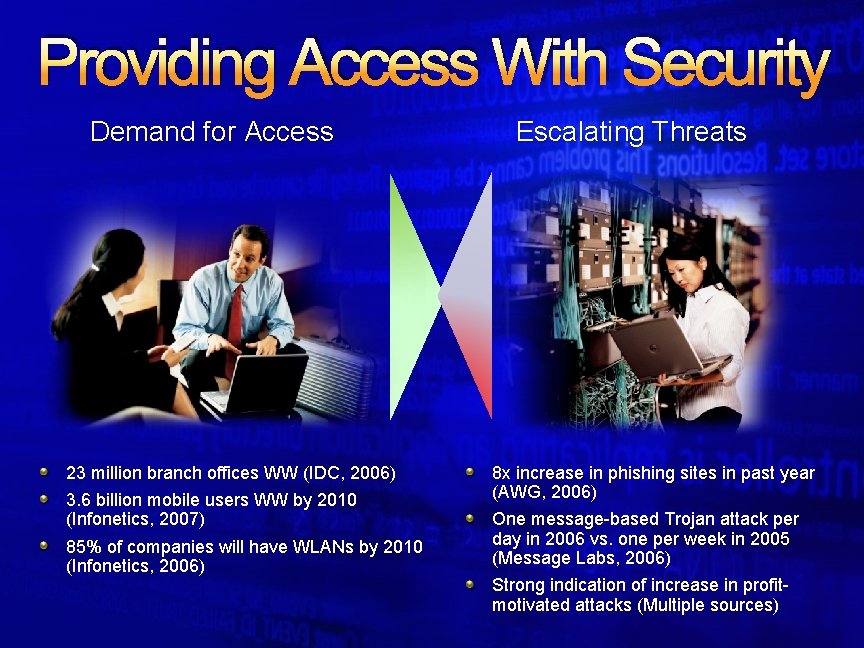
Providing Access With Security Demand for Access 23 million branch offices WW (IDC, 2006) 3. 6 billion mobile users WW by 2010 (Infonetics, 2007) 85% of companies will have WLANs by 2010 (Infonetics, 2006) Escalating Threats 8 x increase in phishing sites in past year (AWG, 2006) One message-based Trojan attack per day in 2006 vs. one per week in 2005 (Message Labs, 2006) Strong indication of increase in profitmotivated attacks (Multiple sources)
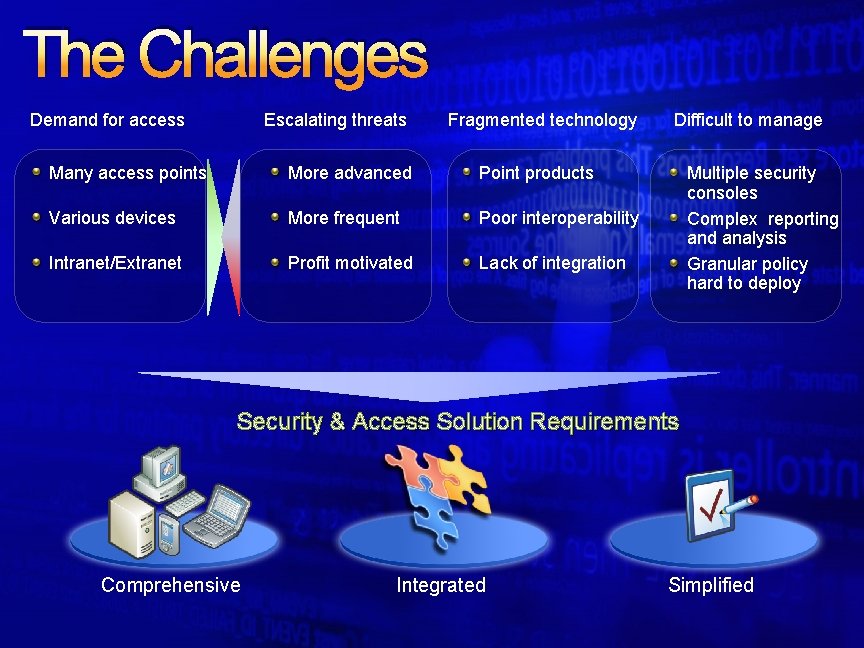
The Challenges Demand for access Escalating threats Fragmented technology Many access points More advanced Point products Various devices More frequent Poor interoperability Intranet/Extranet Profit motivated Lack of integration Difficult to manage Multiple security consoles Complex reporting and analysis Granular policy hard to deploy Security & Access Solution Requirements Comprehensive Integrated Simplified
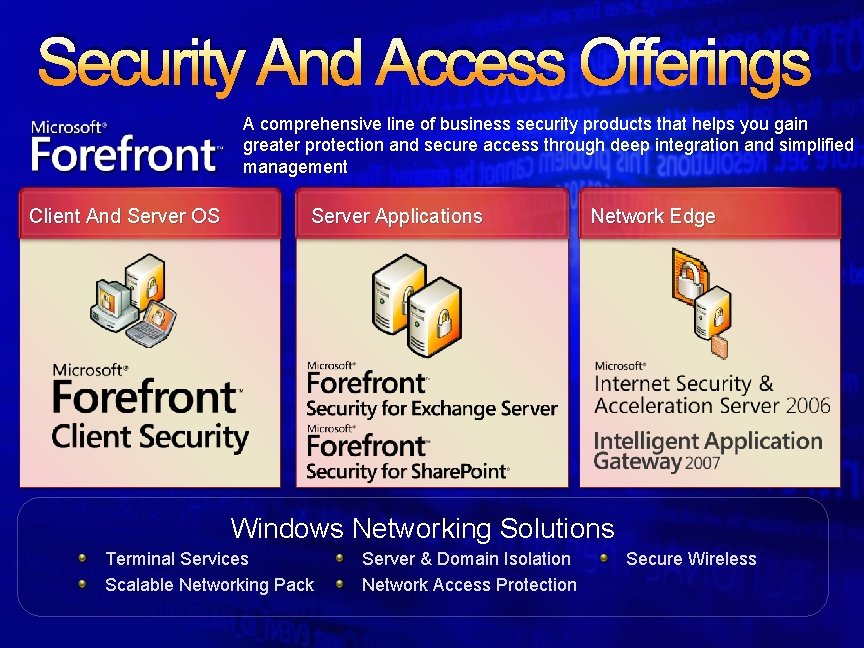
Security And Access Offerings A comprehensive line of business security products that helps you gain greater protection and secure access through deep integration and simplified management Client And Server OS Server Applications Network Edge Windows Networking Solutions Terminal Services Scalable Networking Pack Server & Domain Isolation Network Access Protection Secure Wireless
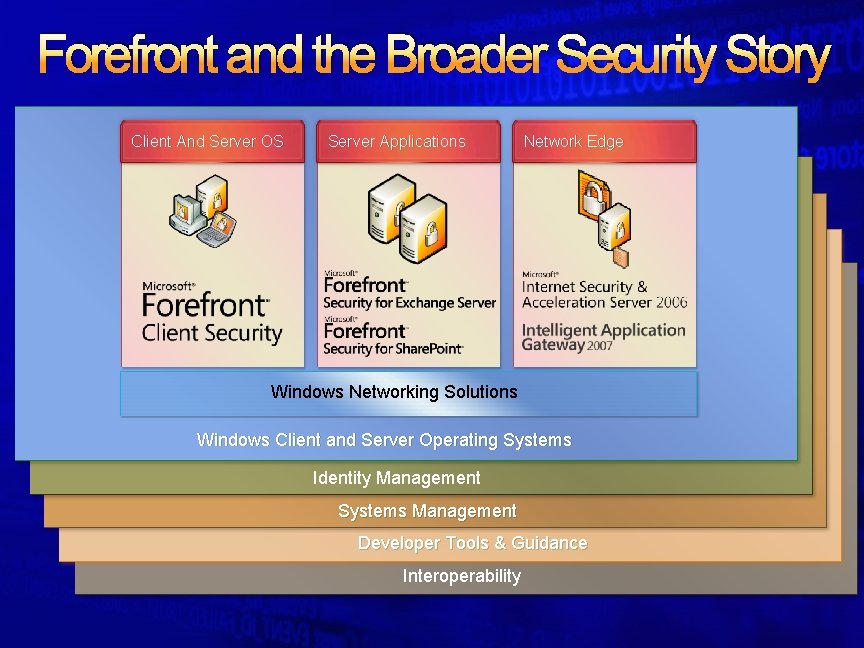
Forefront and the Broader Security Story Client And Server OS Server Applications Network Edge Windows Networking Solutions Windows Client and Server Operating Systems Identity Management Systems Management Developer Tools & Guidance Interoperability
Let’s take a closer look at…
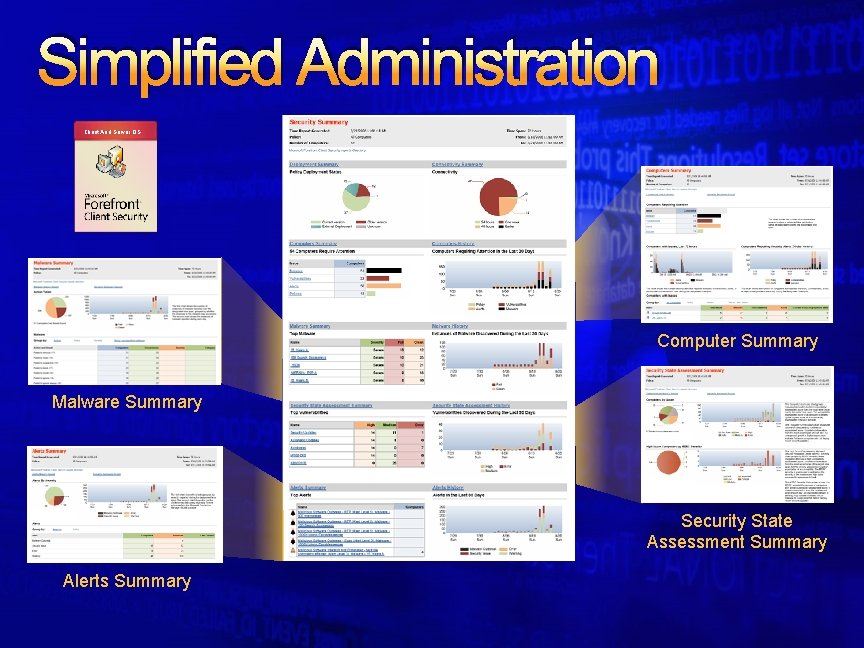
Simplified Administration Client And Server OS Computer Summary Malware Summary Security State Assessment Summary Alerts Summary
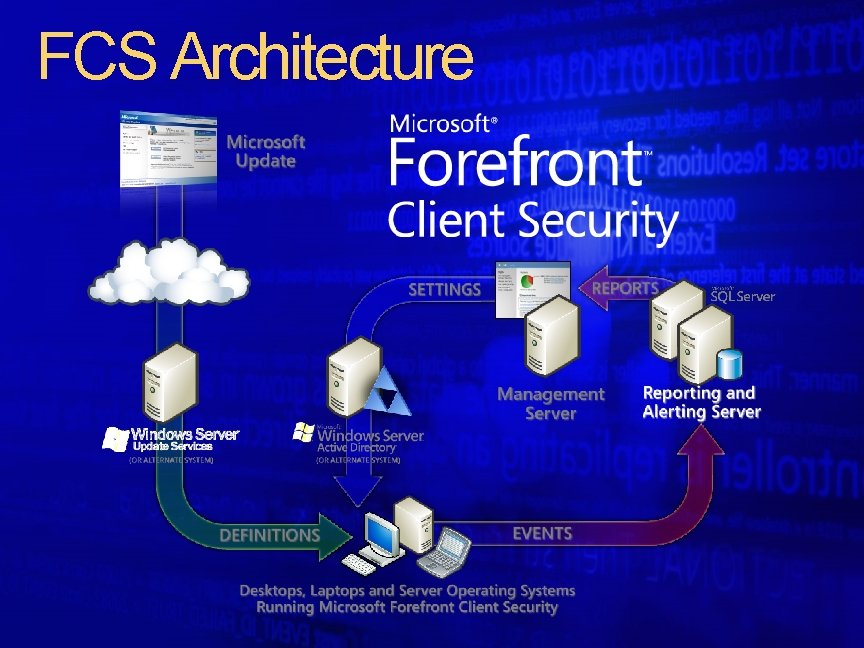
FCS Architecture
Let’s take a closer look at…
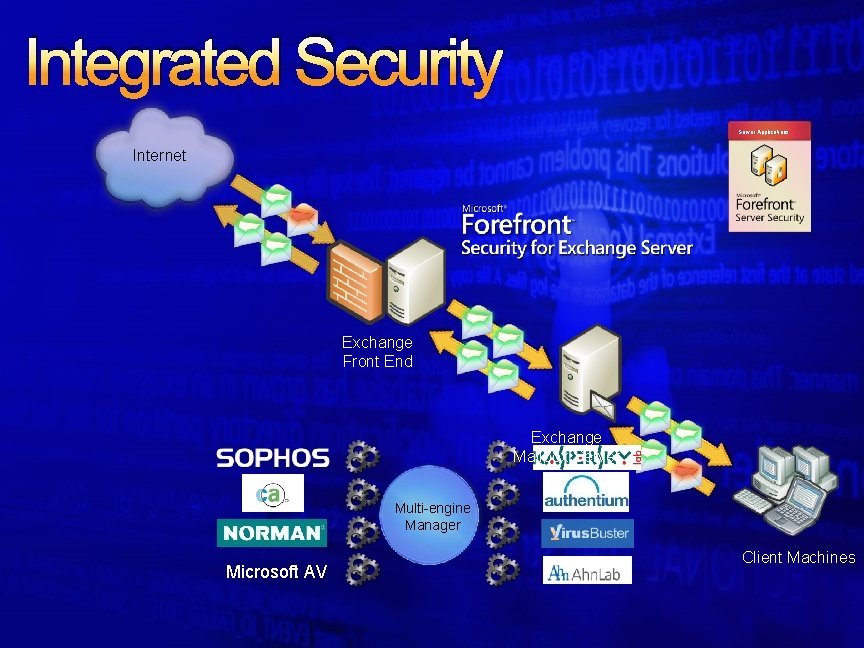
Integrated Security Server Applications Internet Exchange Front End Exchange Mailbox Server Multi-engine Manager Microsoft AV Client Machines
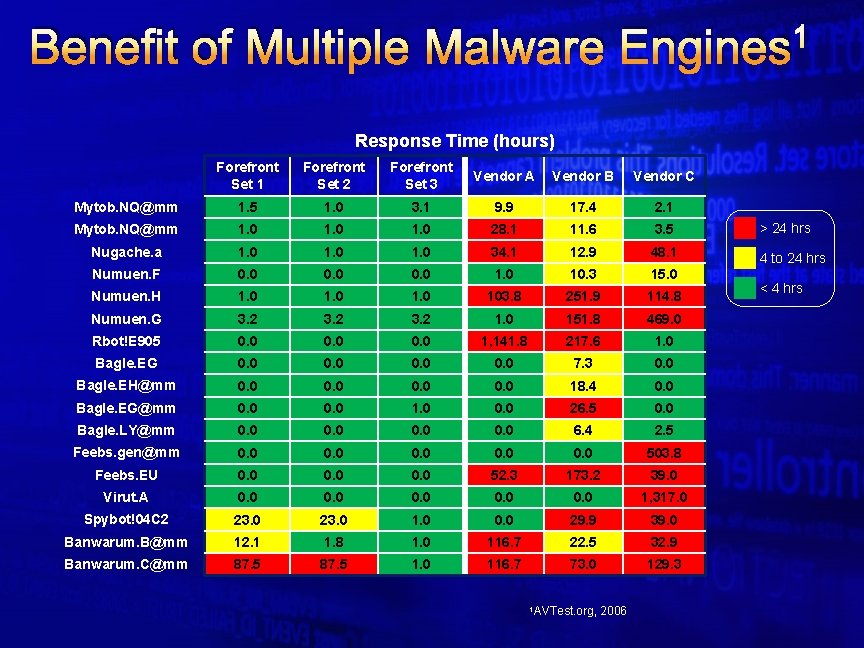
Benefit of Multiple Malware 1 Engines Response Time (hours) Forefront Set 1 Forefront Set 2 Forefront Set 3 Vendor A Vendor B Vendor C Mytob. NQ@mm 1. 5 1. 0 3. 1 9. 9 17. 4 2. 1 Mytob. NQ@mm 1. 0 28. 1 11. 6 3. 5 > 24 hrs Nugache. a 1. 0 34. 1 12. 9 48. 1 4 to 24 hrs Numuen. F 0. 0 10. 3 15. 0 Numuen. H 1. 0 103. 8 251. 9 114. 8 Numuen. G 3. 2 1. 0 151. 8 469. 0 Rbot!E 905 0. 0 1, 141. 8 217. 6 1. 0 Bagle. EG 0. 0 7. 3 0. 0 Bagle. EH@mm 0. 0 18. 4 0. 0 Bagle. EG@mm 0. 0 1. 0 0. 0 26. 5 0. 0 Bagle. LY@mm 0. 0 6. 4 2. 5 Feebs. gen@mm 0. 0 0. 0 503. 8 Feebs. EU 0. 0 52. 3 173. 2 39. 0 Virut. A 0. 0 0. 0 1, 317. 0 Spybot!04 C 2 23. 0 1. 0 0. 0 29. 9 39. 0 Banwarum. B@mm 12. 1 1. 8 1. 0 116. 7 22. 5 32. 9 Banwarum. C@mm 87. 5 1. 0 116. 7 73. 0 129. 3 1 AVTest. org, 2006 < 4 hrs
Let’s take a closer look at…
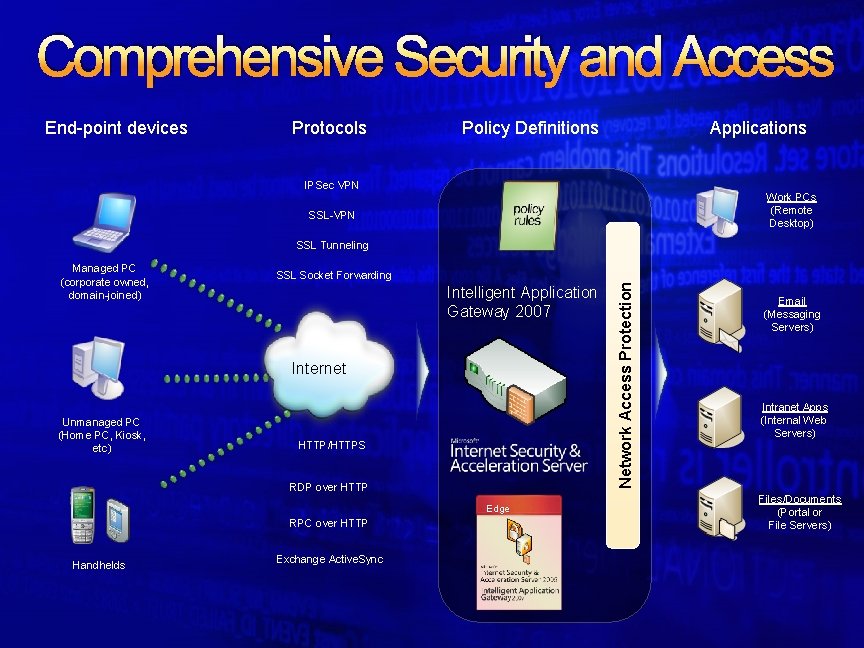
Comprehensive Security and Access End-point devices Protocols Policy Definitions Applications IPSec VPN Work PCs (Remote Desktop) SSL-VPN SSL Tunneling SSL Socket Forwarding Intelligent Application Gateway 2007 Internet Unmanaged PC (Home PC, Kiosk, etc) HTTP/HTTPS RDP over HTTP Edge RPC over HTTP Handhelds Exchange Active. Sync Network Access Protection Managed PC (corporate owned, domain-joined) Email (Messaging Servers) Intranet Apps (Internal Web Servers) Files/Documents (Portal or File Servers)
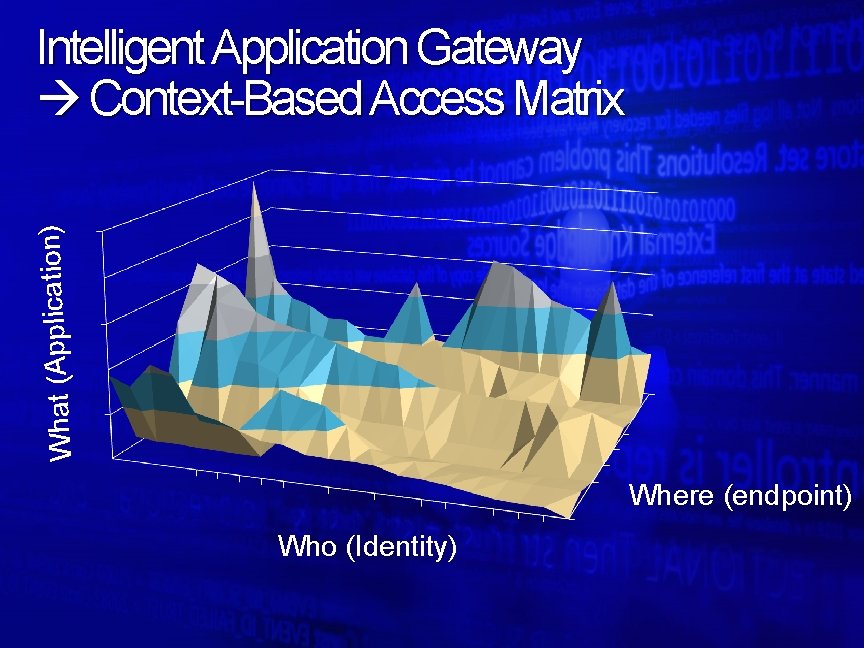
What (Application) Intelligent Application Gateway Context-Based Access Matrix Where (endpoint) Who (Identity)
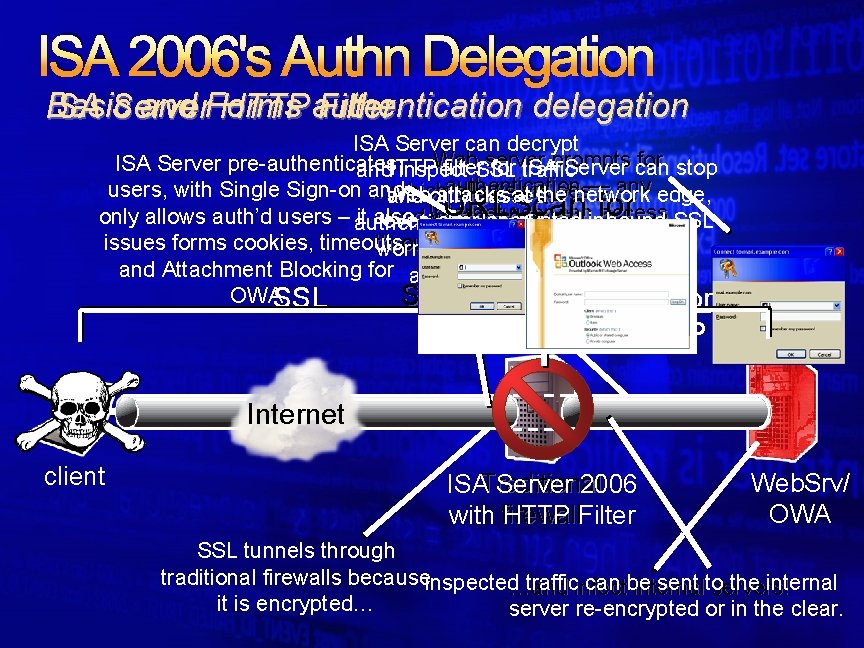
ISA 2006's Authn Delegation Basic and Forms authentication delegation ISA Server HTTP Filter ISA Server can decrypt Web server for stop ISA Server pre-authenticates HTTP filter. SSL for traffic ISAprompts Server can and inspect authentication — any edge, users, with Single Sign-on and …which allows Web attacks atviruses the network and only passes URLScan for Internet user can access SSL only allows auth’d users – authenticated it also and worms to pass even over encrypted traffic-no inbound this. Server prompt issues forms cookies, timeouts, through undetected… worms as they are ISA and Attachment Blocking for anonymous OWASSL SSL or HTTP Internet client ISATraditional Server 2006 with firewall HTTP Filter Web. Srv/ OWA SSL tunnels through traditional firewalls becauseinspected…and trafficinfect can be sent to the internal servers! it is encrypted… server re-encrypted or in the clear.
Let’s take a closer look at. . . Windows Networking Solutions - Core infrastructure
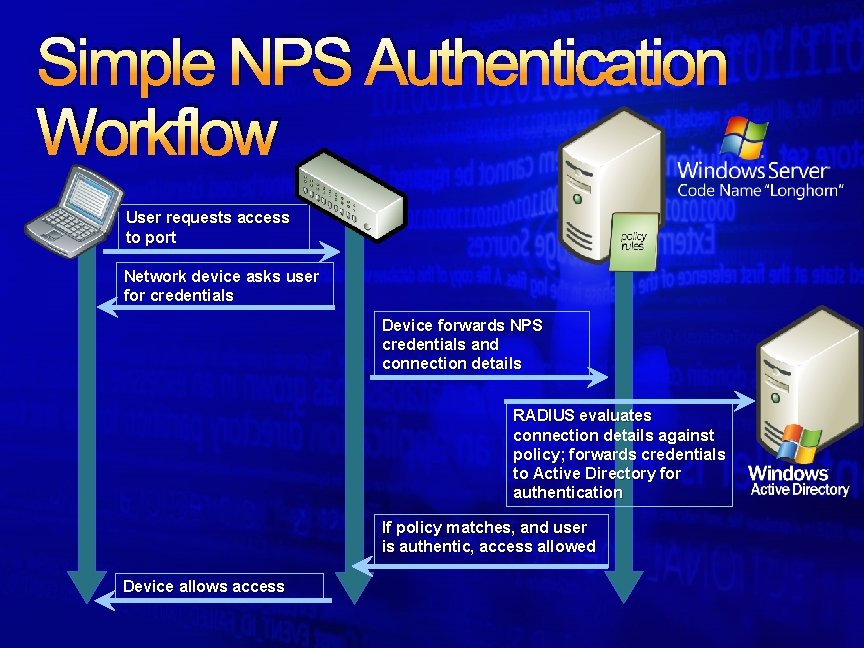
Simple NPS Authentication Workflow User requests access to port Network device asks user for credentials Device forwards NPS credentials and connection details RADIUS evaluates connection details against policy; forwards credentials to Active Directory for authentication If policy matches, and user is authentic, access allowed Device allows access
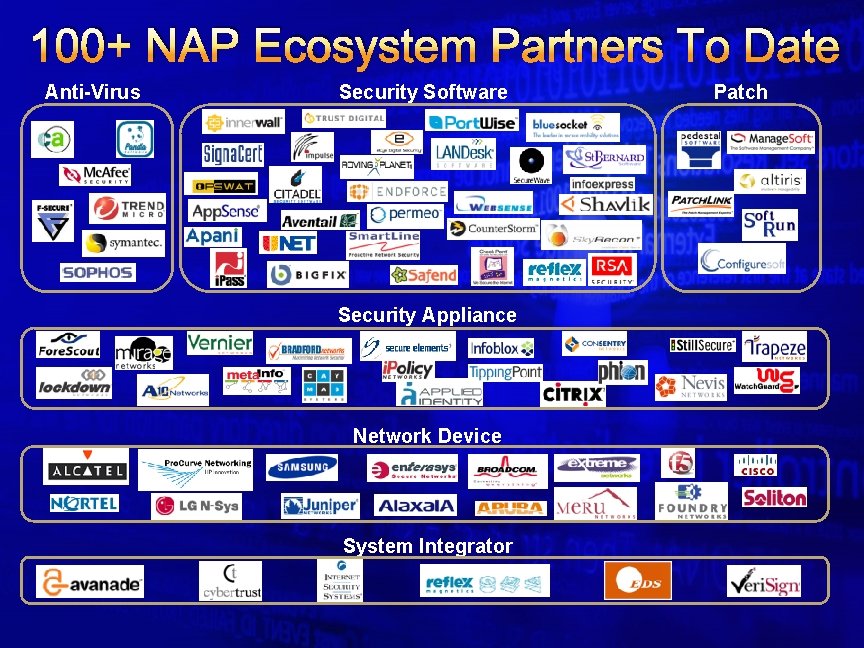
100+ NAP Ecosystem Partners To Date Anti-Virus Security Software Security Appliance Network Device System Integrator Patch
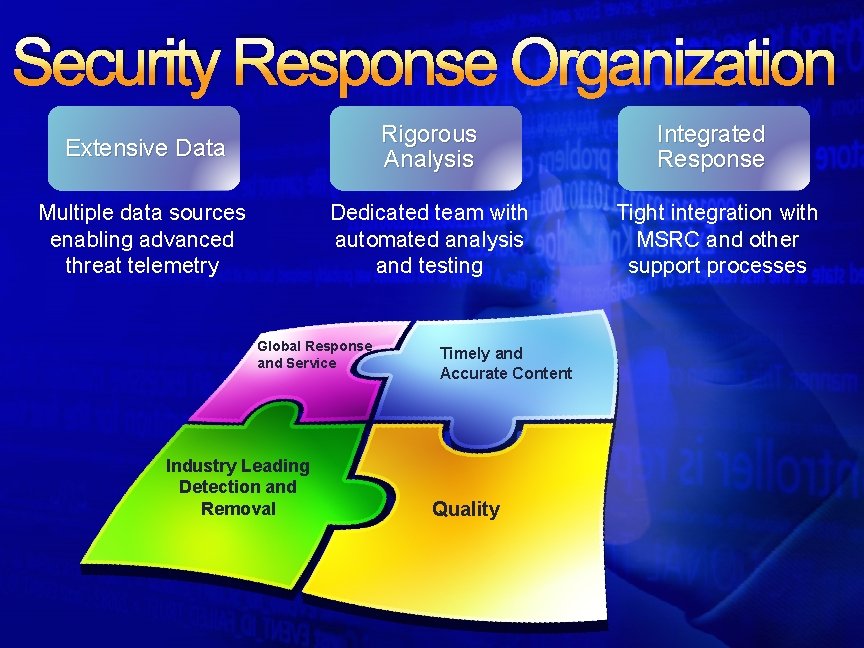
Security Response Organization Extensive Data Rigorous Analysis Integrated Response Multiple data sources enabling advanced threat telemetry Dedicated team with automated analysis and testing Tight integration with MSRC and other support processes Global Response and Service Industry Leading Detection and Removal Timely and Accurate Content Quality
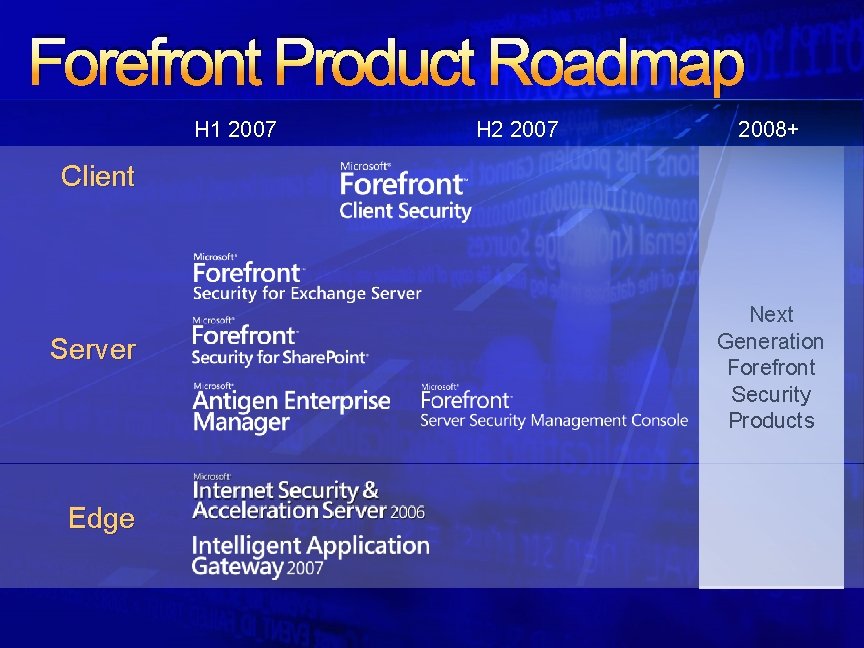
Forefront Product Roadmap H 1 2007 H 2 2007 2008+ Client Server Edge Next Generation Forefront Security Products

Summary Forefront delivers comprehensive, integrated and simplified protection and secure access for businesses New brand but proven, award-winning products Visit http: //www. microsoft. com/forefront Learn more about Forefront Download beta/evaluation software "Microsoft is one of the few vendors that can truly go endto-end (cloud-edge-serverclient) to make businesses more secure. " “Microsoft is poised to become the de facto leader in the e-mail security market. ” - Enterprise Strategy Group Eric Ogren, “At the Forefront of Microsoft Security”, Internet. News. com June 15, 2006 - Gartner—Peter Firstbrook & Arabella Hallwell, Gartner, “Magic Quadrant for EMail Security Boundary, 2006”

© 2007 Microsoft Corporation. All rights reserved. Microsoft, Windows Vista and other product names are or may be registered trademarks and/or trademarks in the U. S. and/or other countries. The information herein is for informational purposes only and represents the current view of Microsoft Corporation as of the date of this presentation. Because Microsoft must respond to changing market conditions, it should not be interpreted to be a commitment on the part of Microsoft, and Microsoft cannot guarantee the accuracy of any information provided after the date of this presentation. MICROSOFT MAKES NO WARRANTIES, EXPRESS, IMPLIED OR STATUTORY, AS TO THE INFORMATION IN THIS PRESENTATION.
- Slides: 24