Unconditionally secure cryptosystems based on quantum cryptography Presented
Unconditionally secure cryptosystems based on quantum cryptography Presented by 吳憲政 1
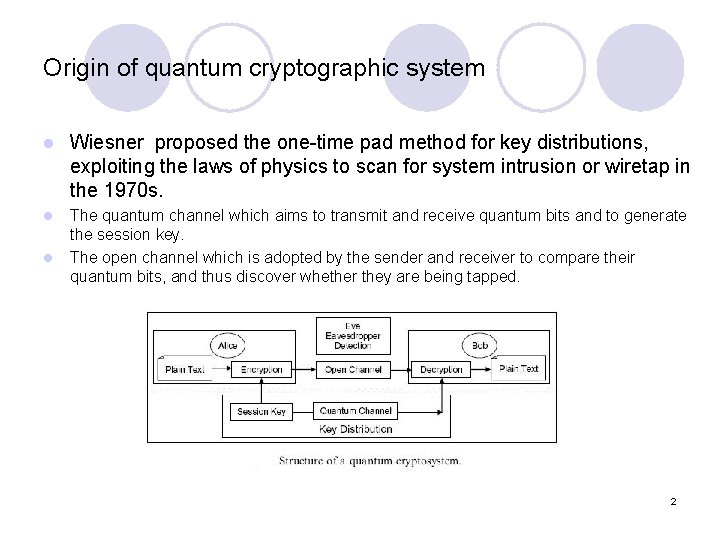
Origin of quantum cryptographic system l Wiesner proposed the one-time pad method for key distributions, exploiting the laws of physics to scan for system intrusion or wiretap in the 1970 s. l The quantum channel which aims to transmit and receive quantum bits and to generate the session key. The open channel which is adopted by the sender and receiver to compare their quantum bits, and thus discover whether they are being tapped. l 2
Two principles used in QKDPs l The QKDPs based on Heisenberg’s Uncertainty Principle -He noted the decoherence of wave function of the system while measuring the position of photons. l The QKDPs based on Bell’s Inequality -Very strong coherence or connection is observed when two quantum bits are in an entangled state. Measuring or modifying the state of one of the quantum bits determines the relative change in the rest of the quantum bit states within the entangled state. 3
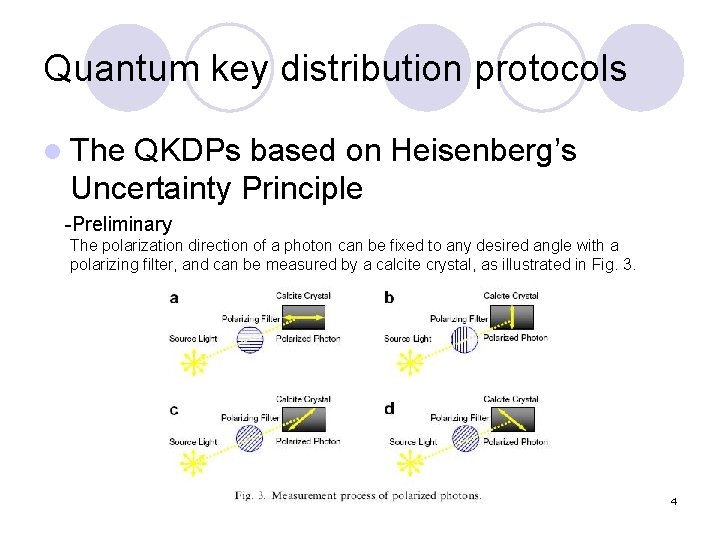
Quantum key distribution protocols l The QKDPs based on Heisenberg’s Uncertainty Principle -Preliminary The polarization direction of a photon can be fixed to any desired angle with a polarizing filter, and can be measured by a calcite crystal, as illustrated in Fig. 3. 4
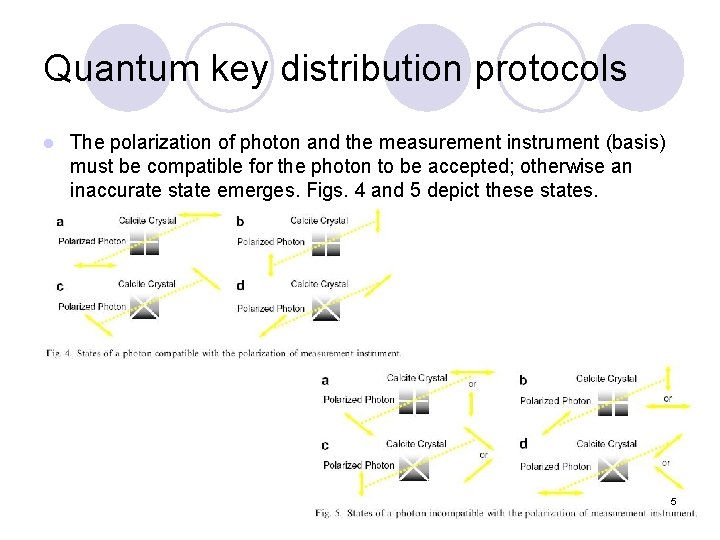
Quantum key distribution protocols l The polarization of photon and the measurement instrument (basis) must be compatible for the photon to be accepted; otherwise an inaccurate state emerges. Figs. 4 and 5 depict these states. 5
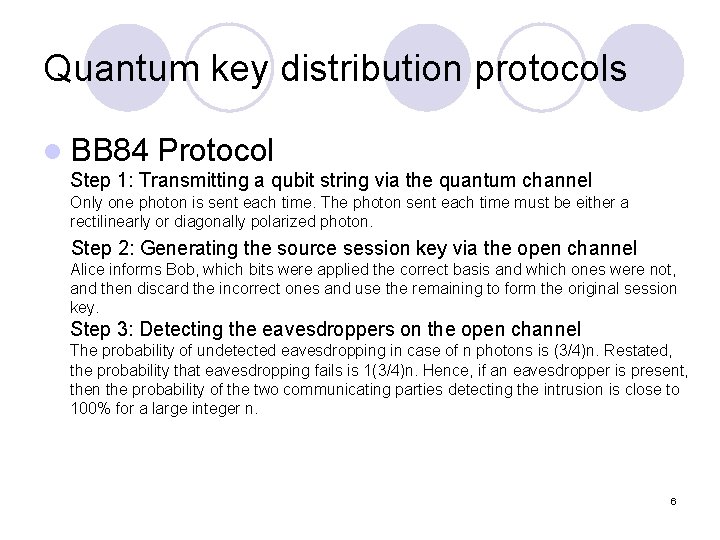
Quantum key distribution protocols l BB 84 Protocol Step 1: Transmitting a qubit string via the quantum channel Only one photon is sent each time. The photon sent each time must be either a rectilinearly or diagonally polarized photon. Step 2: Generating the source session key via the open channel Alice informs Bob, which bits were applied the correct basis and which ones were not, and then discard the incorrect ones and use the remaining to form the original session key. Step 3: Detecting the eavesdroppers on the open channel The probability of undetected eavesdropping in case of n photons is (3/4)n. Restated, the probability that eavesdropping fails is 1(3/4)n. Hence, if an eavesdropper is present, then the probability of the two communicating parties detecting the intrusion is close to 100% for a large integer n. 6
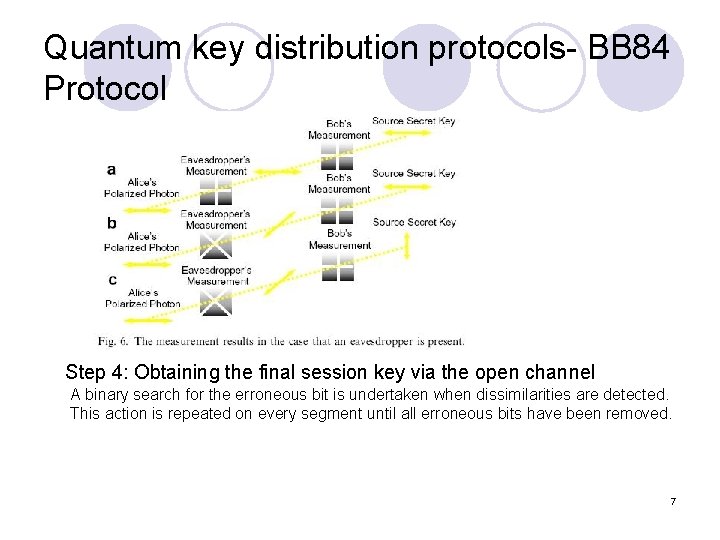
Quantum key distribution protocols- BB 84 Protocol Step 4: Obtaining the final session key via the open channel A binary search for the erroneous bit is undertaken when dissimilarities are detected. This action is repeated on every segment until all erroneous bits have been removed. 7
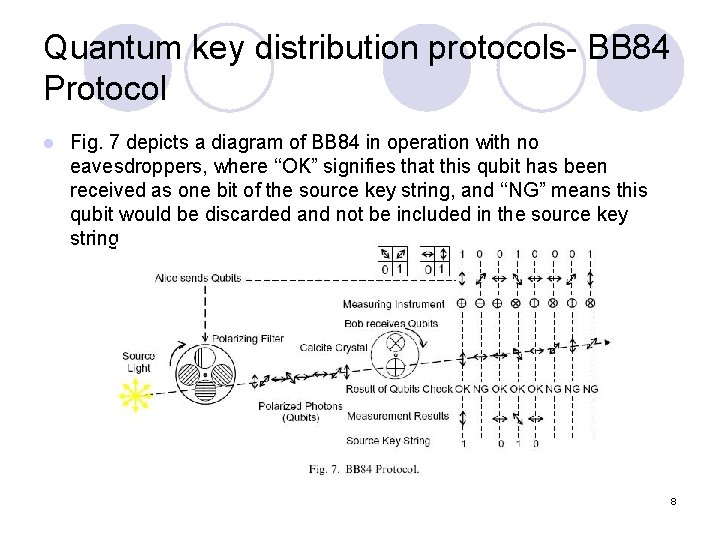
Quantum key distribution protocols- BB 84 Protocol l Fig. 7 depicts a diagram of BB 84 in operation with no eavesdroppers, where ‘‘OK” signifies that this qubit has been received as one bit of the source key string, and ‘‘NG” means this qubit would be discarded and not be included in the source key string. 8
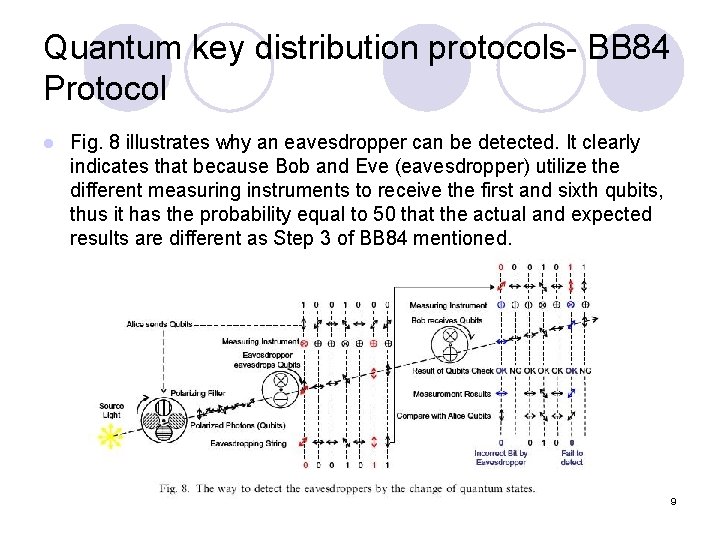
Quantum key distribution protocols- BB 84 Protocol l Fig. 8 illustrates why an eavesdropper can be detected. It clearly indicates that because Bob and Eve (eavesdropper) utilize the different measuring instruments to receive the first and sixth qubits, thus it has the probability equal to 50 that the actual and expected results are different as Step 3 of BB 84 mentioned. 9
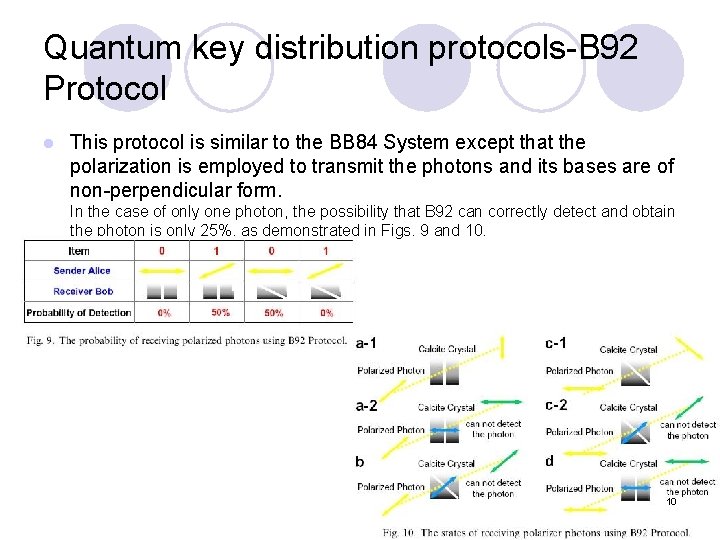
Quantum key distribution protocols-B 92 Protocol l This protocol is similar to the BB 84 System except that the polarization is employed to transmit the photons and its bases are of non-perpendicular form. In the case of only one photon, the possibility that B 92 can correctly detect and obtain the photon is only 25%, as demonstrated in Figs. 9 and 10. 10
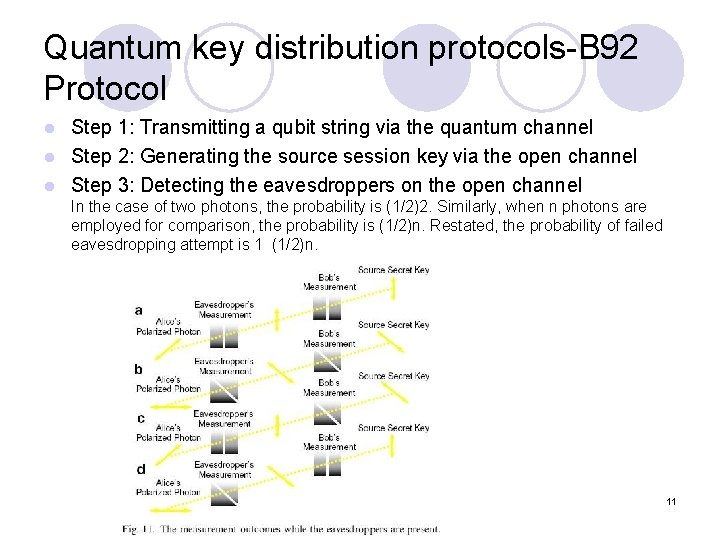
Quantum key distribution protocols-B 92 Protocol Step 1: Transmitting a qubit string via the quantum channel l Step 2: Generating the source session key via the open channel l Step 3: Detecting the eavesdroppers on the open channel l In the case of two photons, the probability is (1/2)2. Similarly, when n photons are employed for comparison, the probability is (1/2)n. Restated, the probability of failed eavesdropping attempt is 1 (1/2)n. 11
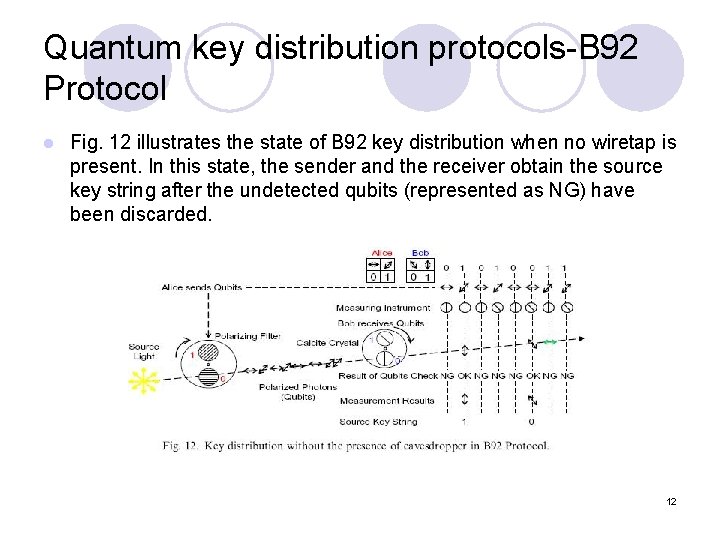
Quantum key distribution protocols-B 92 Protocol l Fig. 12 illustrates the state of B 92 key distribution when no wiretap is present. In this state, the sender and the receiver obtain the source key string after the undetected qubits (represented as NG) have been discarded. 12
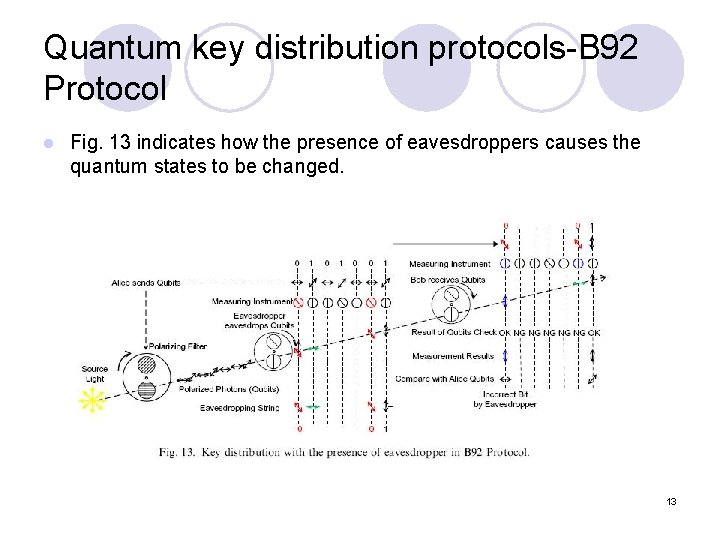
Quantum key distribution protocols-B 92 Protocol l Fig. 13 indicates how the presence of eavesdroppers causes the quantum states to be changed. 13
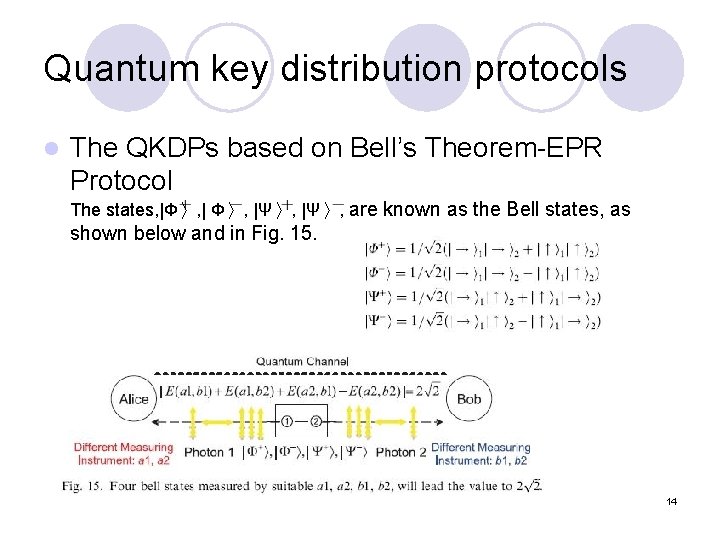
Quantum key distribution protocols l The QKDPs based on Bell’s Theorem-EPR Protocol The states, |Φ〉, |Ψ〉, are known as the Bell states, as shown below and in Fig. 15. 14
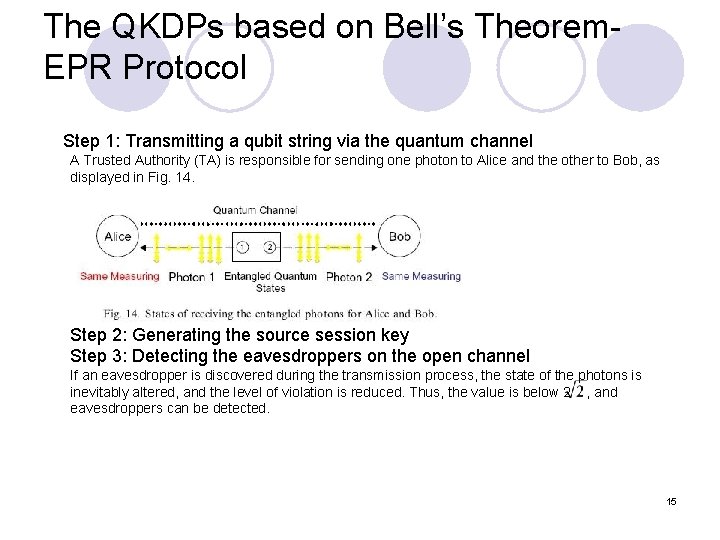
The QKDPs based on Bell’s Theorem. EPR Protocol Step 1: Transmitting a qubit string via the quantum channel A Trusted Authority (TA) is responsible for sending one photon to Alice and the other to Bob, as displayed in Fig. 14. Step 2: Generating the source session key Step 3: Detecting the eavesdroppers on the open channel If an eavesdropper is discovered during the transmission process, the state of the photons is inevitably altered, and the level of violation is reduced. Thus, the value is below 2 , and eavesdroppers can be detected. 15
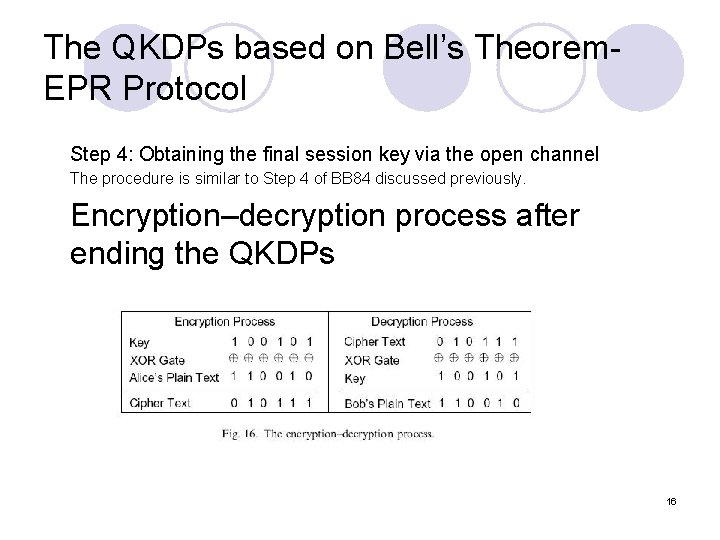
The QKDPs based on Bell’s Theorem. EPR Protocol Step 4: Obtaining the final session key via the open channel The procedure is similar to Step 4 of BB 84 discussed previously. Encryption–decryption process after ending the QKDPs 16
Conclusion l Although quantum cryptosystems are currently at the experimental stage and are unregulated, it can be employed to develop a strong information security software system. 17
l THANK YOU!! 18
- Slides: 18