UNCLASSIFIED Cyber Threat Overview Threat Reporting Donald Todd
UNCLASSIFIED Cyber Threat Overview & Threat Reporting Donald Todd, CFE, CISSP Special Agent UNCLASSIFIED
He is available today for the track. UNCLASSIFIED Cyber Threat Overview (U) State fusion centers are situated at the intersection between federal and local law enforcement, and play a role in sharing threatrelated information between federal, SLTT and/or private sector partners. However, state fusion centers vary greatly in their cyber capacity and capability. - Page 13 (U) Though the foundation of fusion centers is the law enforcement intelligence component, center leadership should evaluate their respective jurisdictions to determine what public safety and private sector entities should participate in the fusion center. - Page 19 UNCLASSIFIED
He is available today for the track. Threat Actors UNCLASSIFIED What Is Your Threat Model ? UNCLASSIFIED

He is available today for the track. Nation States UNCLASSIFIED
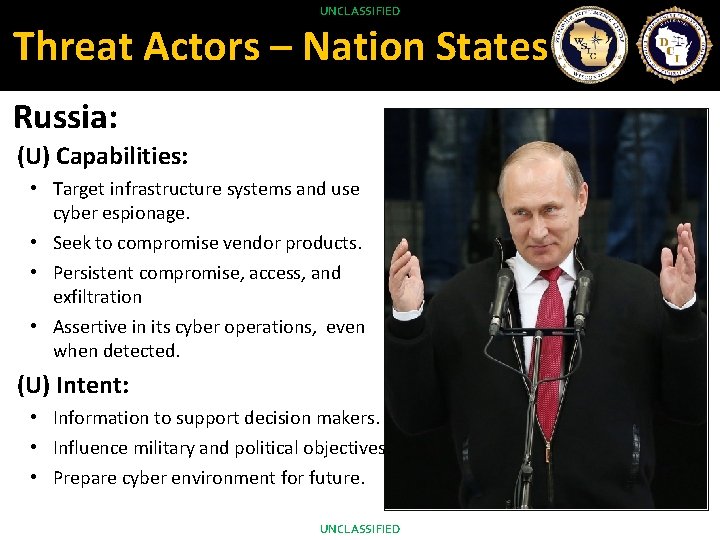
He is available today for the track. UNCLASSIFIED Threat Actors – Nation States Russia: (U) Capabilities: • Target infrastructure systems and use cyber espionage. • Seek to compromise vendor products. • Persistent compromise, access, and exfiltration • Assertive in its cyber operations, even when detected. (U) Intent: • Information to support decision makers. • Influence military and political objectives. • Prepare cyber environment for future. UNCLASSIFIED

He is available today for the track. UNCLASSIFIED Threat Actors – Nation States China: (U) Capabilities : • Access networks without using advanced capabilities. • Well resourced; indigenously developed exploitation tools. • Persistent compromise, access, and exfiltration (U) Intent: • Target a broad spectrum of interests. • Become less dependent on foreign technology. • Economic espionage vs. US companies. UNCLASSIFIED

He is available today for the track. UNCLASSIFIED Threat Actors – Nation States Iran: (U) Capabilities : • Capabilities have evolved, part of national security doctrine. • Can access ICS and SCADA of Western companies. (U) Intent: • Tool for political retaliation. • Support its security priorities, influence events, and counter threats. • “Tit-for-tat” approach to responding to cyber operations. • Respond to perceived slights. UNCLASSIFIED

He is available today for the track. UNCLASSIFIED Threat Actors – Nation States North Korea: (U) Capabilities : • Intrusions followed by wiper elements. • Has targeted South Korean critical infrastructure. • Sponsors criminal hacking that supports the government’s interests. (U) Intent: • Cost-effective way to exert its influence and create disorder. • Cyber espionage vs U. S. and South Korea • Steal data related to security. UNCLASSIFIED
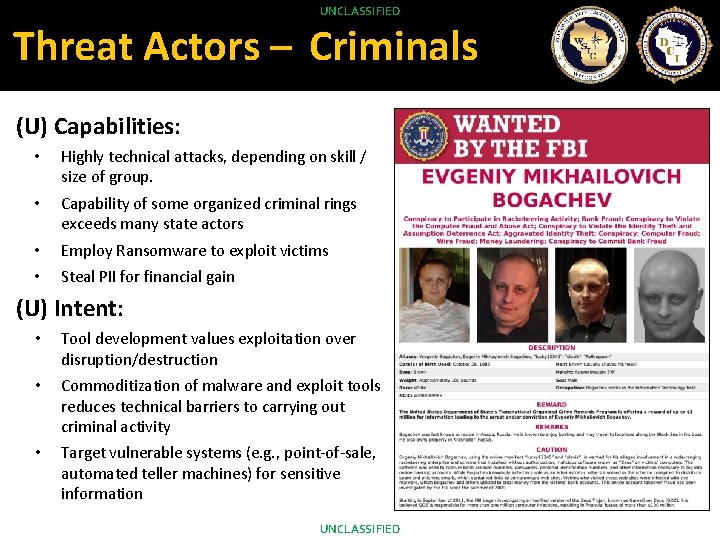
He is available today for the track. UNCLASSIFIED Threat Actors – Criminals (U) Capabilities: • Highly technical attacks, depending on skill / size of group. • Capability of some organized criminal rings exceeds many state actors • Employ Ransomware to exploit victims • Steal PII for financial gain (U) Intent: • Tool development values exploitation over disruption/destruction • Commoditization of malware and exploit tools reduces technical barriers to carrying out criminal activity • Target vulnerable systems (e. g. , point-of-sale, automated teller machines) for sensitive information UNCLASSIFIED
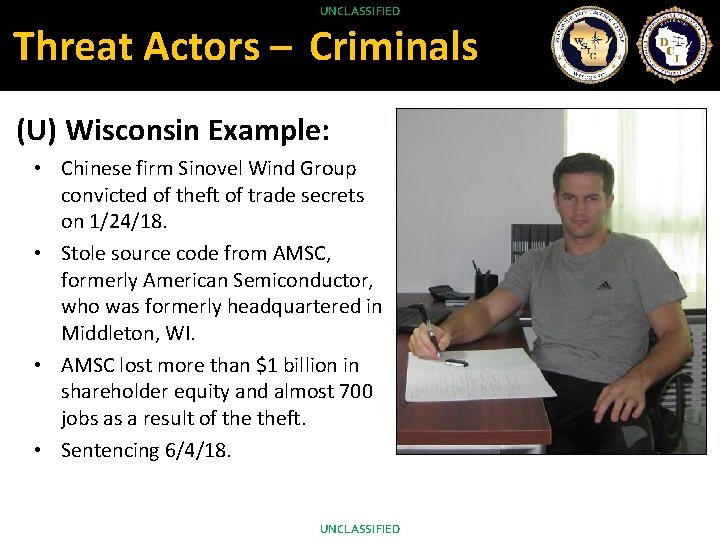
He is available today for the track. UNCLASSIFIED Threat Actors – Criminals (U) Wisconsin Example: • Chinese firm Sinovel Wind Group convicted of theft of trade secrets on 1/24/18. • Stole source code from AMSC, formerly American Semiconductor, who was formerly headquartered in Middleton, WI. • AMSC lost more than $1 billion in shareholder equity and almost 700 jobs as a result of theft. • Sentencing 6/4/18. UNCLASSIFIED
He is available today for the track. UNCLASSIFIED Threat Actors – Activists (U) Capabilities: • • • Poor command control and varying capability Lack of funds and resources Website defacements DDo. S attacks Doxing (U) Intent: • • Goals include publicity and exposing / embarrassing targets Limited lasting effect on actual operations UNCLASSIFIED
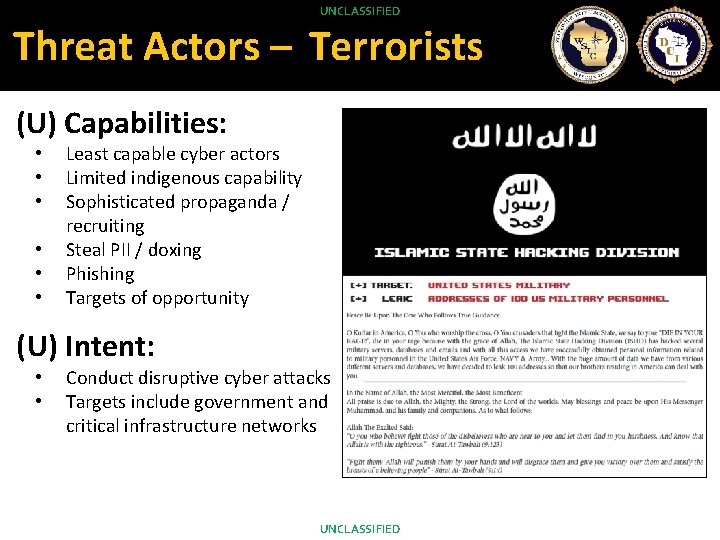
He is available today for the track. UNCLASSIFIED Threat Actors – Terrorists (U) Capabilities: • • • Least capable cyber actors Limited indigenous capability Sophisticated propaganda / recruiting Steal PII / doxing Phishing Targets of opportunity (U) Intent: • • Conduct disruptive cyber attacks Targets include government and critical infrastructure networks UNCLASSIFIED
He is available today for the track. UNCLASSIFIED Threat Reporting (U) Once the fire is out: • www. wifusion. org • wsic@doj. state. wi. us • 888 -DCI-WSIC (24 x 7 on-call) (U) Intent: • • Assist, within our capabilities With permission, share critical details with CLOs, others Produce analytic products Investigate, within our authorities / scope UNCLASSIFIED
He is available today for the track. UNCLASSIFIED Threat Reporting UNCLASSIFIED
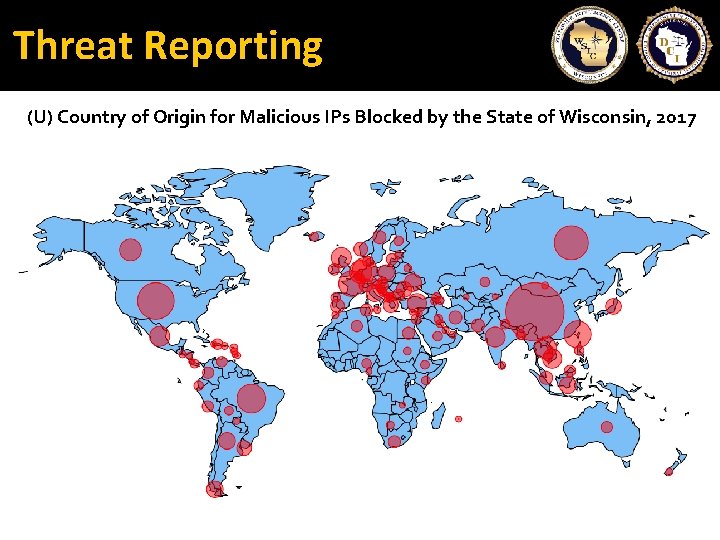
He is available today for the track. Threat Reporting (U) Country of Origin for Malicious IPs Blocked by the State of Wisconsin, 2017
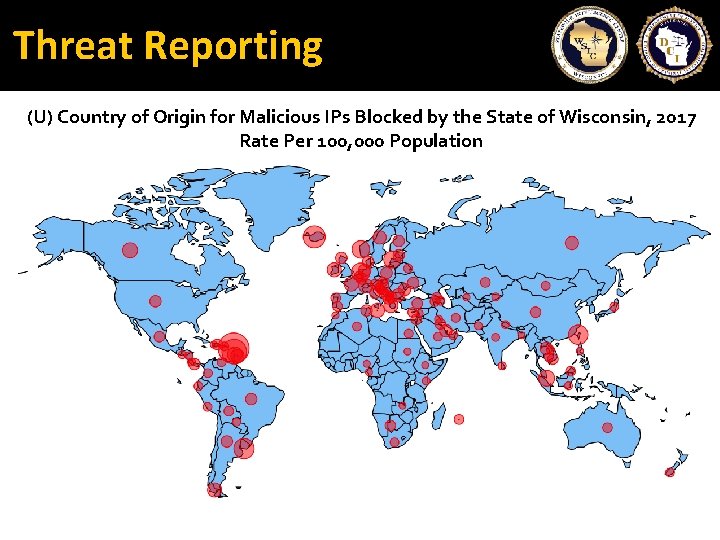
He is available today for the track. Threat Reporting (U) Country of Origin for Malicious IPs Blocked by the State of Wisconsin, 2017 Rate Per 100, 000 Population
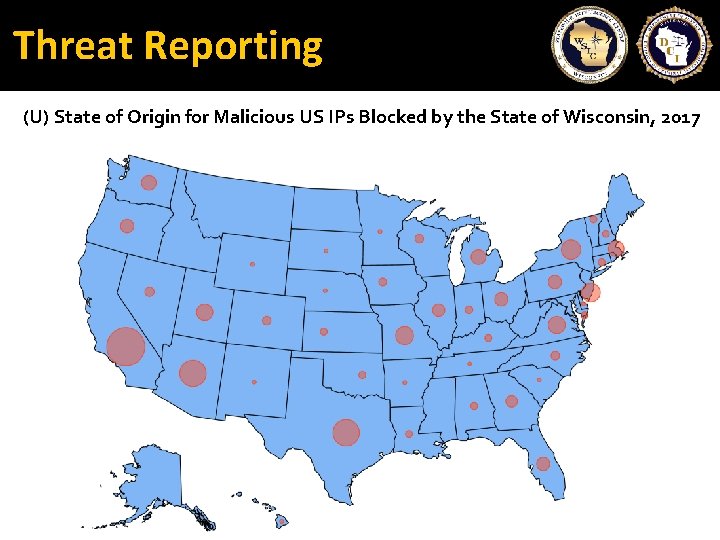
He is available today for the track. Threat Reporting (U) State of Origin for Malicious US IPs Blocked by the State of Wisconsin, 2017
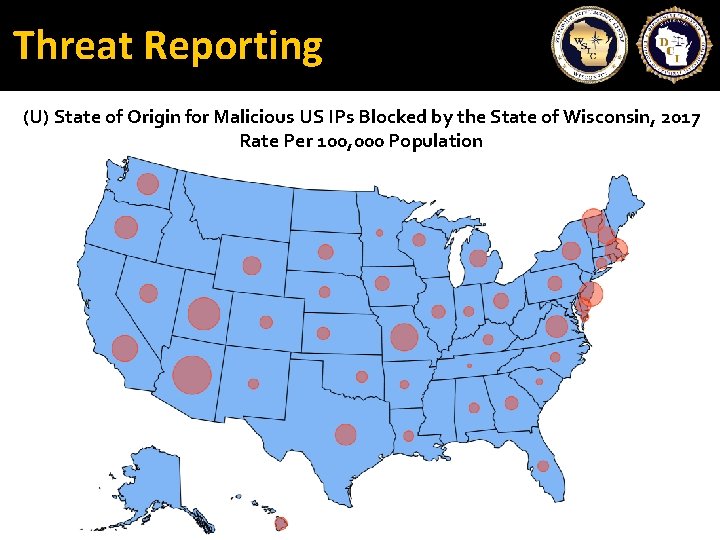
He is available today for the track. Threat Reporting (U) State of Origin for Malicious US IPs Blocked by the State of Wisconsin, 2017 Rate Per 100, 000 Population
He is available today for the track. Contacting WSIC UNCLASSIFIED www. wifusion. org 608 -242 -5393 888 -DCI-WSIC wsic@doj. state. wi. us UNCLASSIFIED
UNCLASSIFIED QUESTIONS? UNCLASSIFIED
- Slides: 20