UNCLASSIFIED ARCYBER The Next Battlefield UNCLASSIFIED OVERALL CLASSIFICATION
UNCLASSIFIED ARCYBER The Next Battlefield UNCLASSIFIED OVERALL CLASSIFICATION 10 December 2013
Cyberspace as a Domain UNCLASSIFIED CYBERSPACE: A global domain within the information environment consisting of the interdependent network of information technology infrastructures, including the Internet, telecommunications networks, computer systems, and embedded processors and controllers. (JP 1 -02) • Man-made domain – ever changing • Interdependent w/ traditional war-fighting domains. • Not special or separate – part of every unit’s Operating Environment • Physical, logical (virtual), and social characteristics • Instantaneous operational reach – global battlefield. Constant presence – evolves at the speed of code! UNCLASSIFIED 2
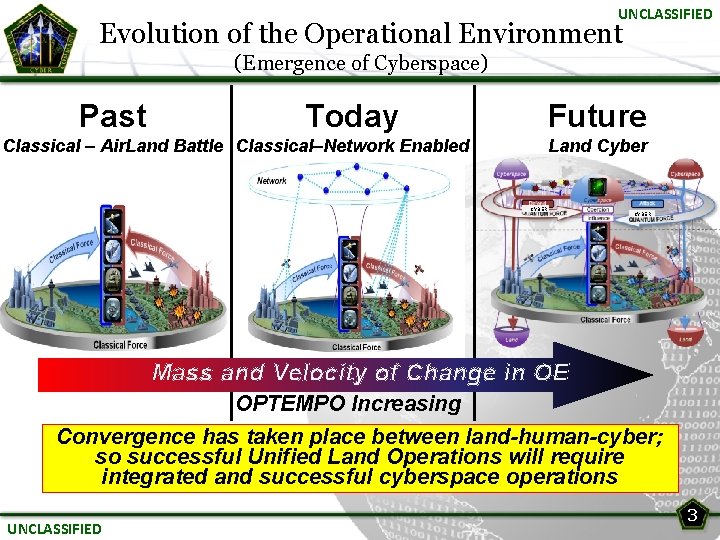
UNCLASSIFIED Evolution of the Operational Environment (Emergence of Cyberspace) Past Today Future Classical – Air. Land Battle Classical–Network Enabled Land Cyber CYBER Mass and Velocity of Change in OE OPTEMPO Increasing Convergence has taken place between land-human-cyber; so successful Unified Land Operations will require integrated and successful cyberspace operations UNCLASSIFIED 3
UNCLASSIFIED Threat…Contested Environment • Sophisticated, Growing and Evolving • Exploiting daily, Increasing disruption, Developing destruction capabilities • Current approach is not defendable or affordable – Limited Situation Awareness – Disparate Networks – Reactive Defense (Signature-based) – Compliance is our first line of defense Threats Developing Faster Than We Can Protect Against Them UNCLASSIFIED 4
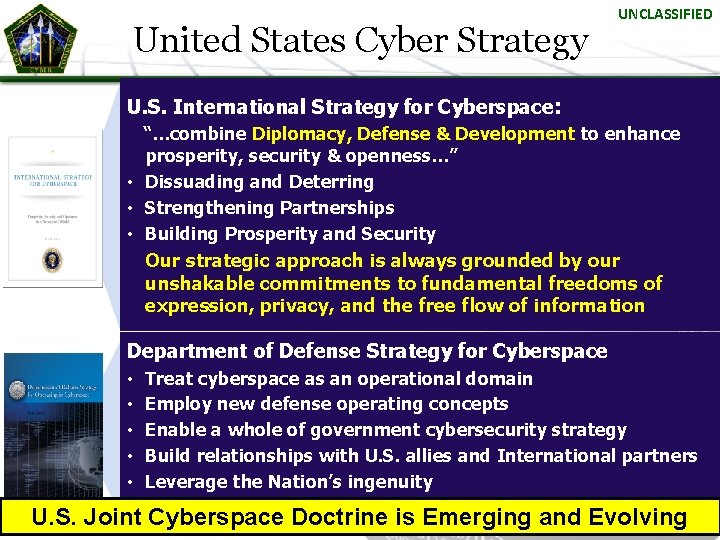
United States Cyber Strategy UNCLASSIFIED U. S. International Strategy for Cyberspace: “…combine Diplomacy, Defense & Development to enhance prosperity, security & openness…” • Dissuading and Deterring • Strengthening Partnerships • Building Prosperity and Security Our strategic approach is always grounded by our unshakable commitments to fundamental freedoms of expression, privacy, and the free flow of information Department of Defense Strategy for Cyberspace • • • Treat cyberspace as an operational domain Employ new defense operating concepts Enable a whole of government cybersecurity strategy Build relationships with U. S. allies and International partners Leverage the Nation’s ingenuity U. S. Joint Cyberspace Doctrine is Emerging and Evolving 5 UNCLASSIFIED
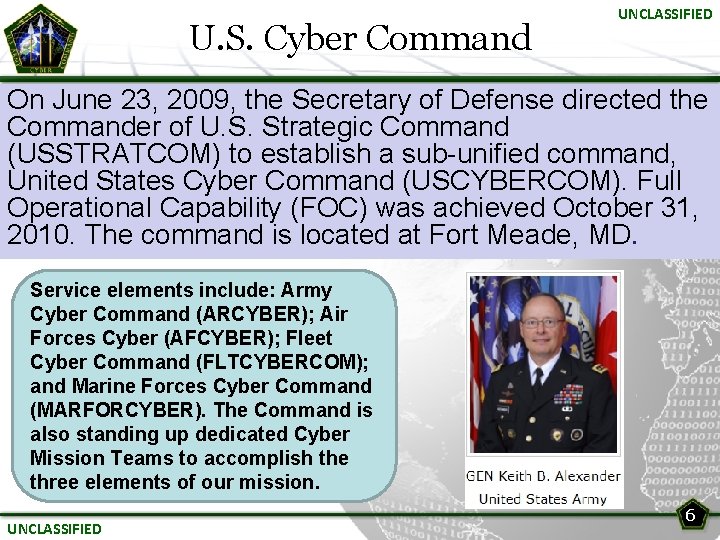
U. S. Cyber Command UNCLASSIFIED On June 23, 2009, the Secretary of Defense directed the Commander of U. S. Strategic Command (USSTRATCOM) to establish a sub-unified command, United States Cyber Command (USCYBERCOM). Full Operational Capability (FOC) was achieved October 31, 2010. The command is located at Fort Meade, MD. Service elements include: Army Cyber Command (ARCYBER); Air Forces Cyber (AFCYBER); Fleet Cyber Command (FLTCYBERCOM); and Marine Forces Cyber Command (MARFORCYBER). The Command is also standing up dedicated Cyber Mission Teams to accomplish the three elements of our mission. UNCLASSIFIED 6
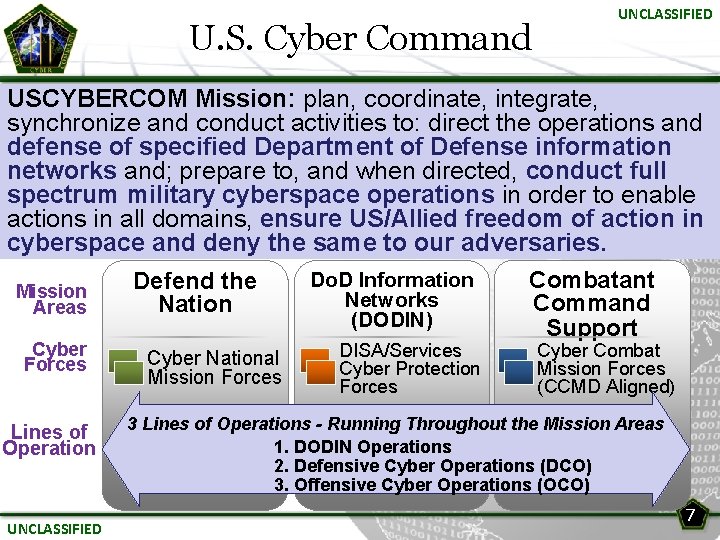
U. S. Cyber Command UNCLASSIFIED USCYBERCOM Mission: plan, coordinate, integrate, synchronize and conduct activities to: direct the operations and defense of specified Department of Defense information networks and; prepare to, and when directed, conduct full spectrum military cyberspace operations in order to enable actions in all domains, ensure US/Allied freedom of action in cyberspace and deny the same to our adversaries. Do. D Information Combatant Defend the Mission Networks Command Nation Areas (DODIN) Support Cyber Forces Lines of Operation UNCLASSIFIED Cyber National Mission Forces DISA/Services Cyber Protection Forces Cyber Combat Mission Forces (CCMD Aligned) 3 Lines of Operations - Running Throughout the Mission Areas 1. DODIN Operations 2. Defensive Cyber Operations (DCO) 3. Offensive Cyber Operations (OCO) 7
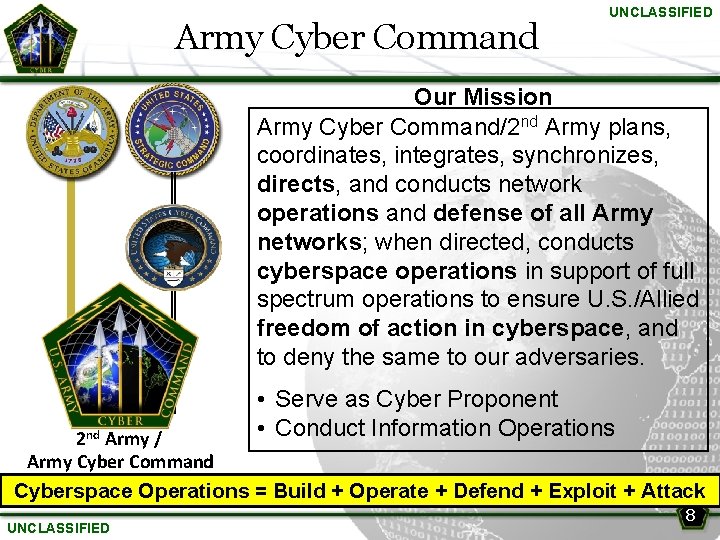
Army Cyber Command UNCLASSIFIED Our Mission Army Cyber Command/2 nd Army plans, coordinates, integrates, synchronizes, directs, and conducts network operations and defense of all Army networks; when directed, conducts cyberspace operations in support of full spectrum operations to ensure U. S. /Allied freedom of action in cyberspace, and to deny the same to our adversaries. 2 nd Army / Army Cyber Command • Serve as Cyber Proponent • Conduct Information Operations Cyberspace Operations = Build + Operate + Defend + Exploit + Attack UNCLASSIFIED 8
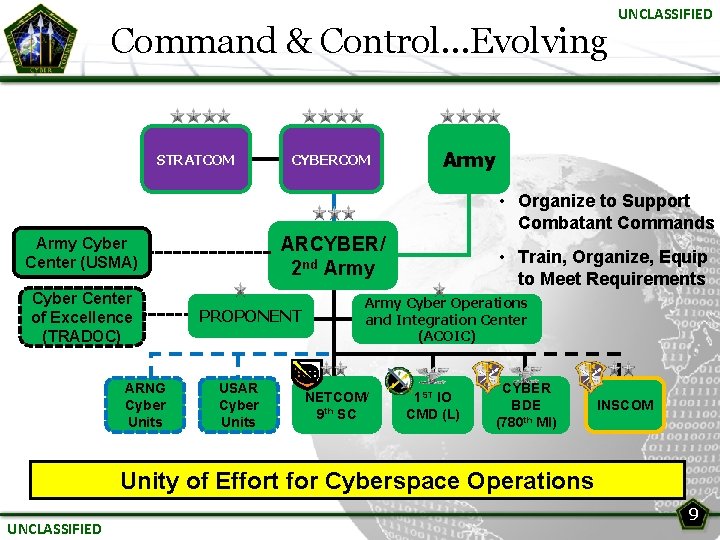
Command & Control…Evolving STRATCOM CYBERCOM UNCLASSIFIED Army • Organize to Support Combatant Commands ARCYBER/ 2 nd Army Cyber Center (USMA) Cyber Center of Excellence (TRADOC) ARNG Cyber Units PROPONENT USAR Cyber Units • Train, Organize, Equip to Meet Requirements Army Cyber Operations and Integration Center (ACOIC) NETCOM/ 9 th SC 1 ST IO CMD (L) CYBER BDE (780 th MI) INSCOM Unity of Effort for Cyberspace Operations UNCLASSIFIED 9
Army Cyber Command Roles UNCLASSIFIED Ø Defense of All Army Networks Ø Serves as Service Component to U. S. Cyber Command Ø Train, Organize and Equip Ø Provide Trained & Ready Forces Ø Build Joint Force Headquarters-Cyber capability Ø Integrate Cyberspace into Planning and Exercises Ø Cyber Education, Training and Leader Development Ø Build Partner Capacity Ø Conduct Information Ops for the Army Ø Support to Institutional Cyber Force Development UNCLASSIFIED 10
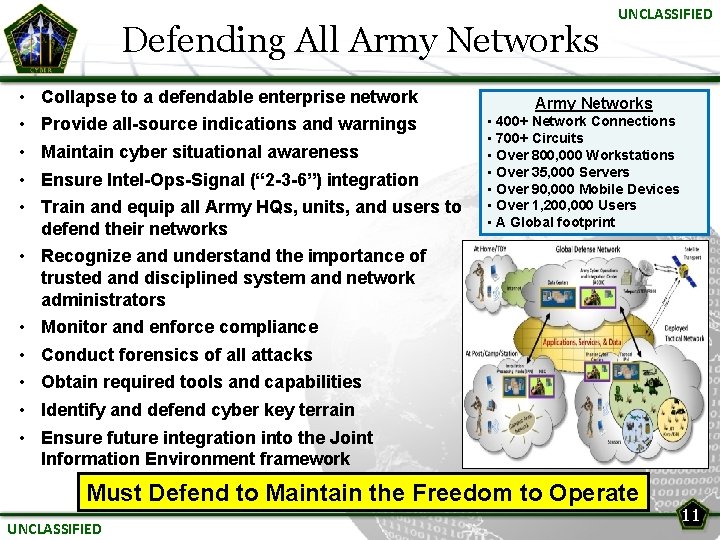
Defending All Army Networks • • • Collapse to a defendable enterprise network Provide all-source indications and warnings Maintain cyber situational awareness Ensure Intel-Ops-Signal (“ 2 -3 -6”) integration Train and equip all Army HQs, units, and users to defend their networks UNCLASSIFIED Army Networks • 400+ Network Connections • 700+ Circuits • Over 800, 000 Workstations • Over 35, 000 Servers • Over 90, 000 Mobile Devices • Over 1, 200, 000 Users • A Global footprint • Recognize and understand the importance of trusted and disciplined system and network administrators • Monitor and enforce compliance • Conduct forensics of all attacks • Obtain required tools and capabilities • Identify and defend cyber key terrain • Ensure future integration into the Joint Information Environment framework Must Defend to Maintain the Freedom to Operate UNCLASSIFIED 11
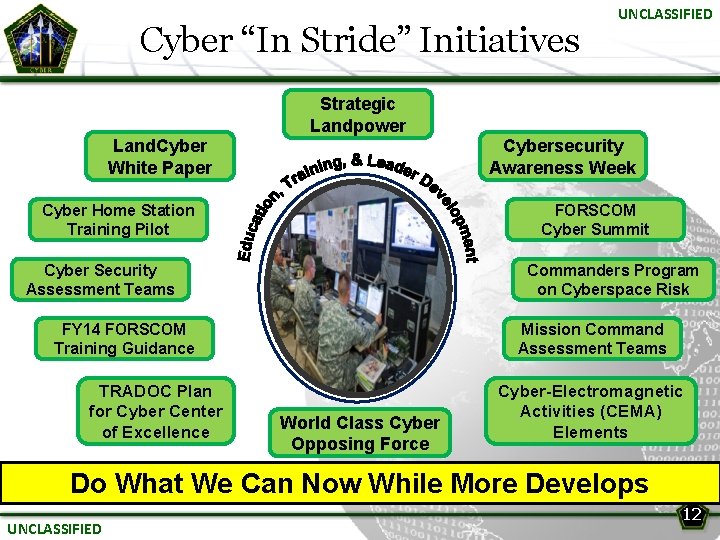
Cyber “In Stride” Initiatives UNCLASSIFIED Strategic Landpower Land. Cyber White Paper Cybersecurity Awareness Week Cyber Home Station Training Pilot FORSCOM Cyber Summit Cyber Security Assessment Teams Commanders Program on Cyberspace Risk FY 14 FORSCOM Training Guidance TRADOC Plan for Cyber Center of Excellence Mission Command Assessment Teams World Class Cyber Opposing Force Cyber-Electromagnetic Activities (CEMA) Elements Do What We Can Now While More Develops UNCLASSIFIED 12
Evolving Doctrine UNCLASSIFIED • JP 3 -12 (Cyberspace Operations): ØCyberspace Operations are the employment of cyberspace capabilities where the primary purpose is to achieve objectives in or through cyberspace ØMost aspects of Joint Operations rely in part on cyberspace ØCommanders conduct cyberspace ops to retain freedom of maneuver in cyberspace and deny freedom of action to adversaries • FM 3 -38 (Cyber-Electromagnetic Activities): Activities leveraged to seize, retain, and exploit an advantage over adversaries and enemies in both cyberspace and the electromagnetic spectrum, while simultaneously denying and degrading adversary and enemy use of the same and protecting mission command systems UNCLASSIFIED 13
UNCLASSIFIED Army Cyber Training Vision: A team of elite, trusted and disciplined cyber warriors trained to operate and defend Army networks Individual Level • Increase individual cyber awareness (passwords, software updates, suspicious attachments); Begin with Initial Military Training • Certification is a first step…Every user has training requirements • Ensure leaders understand are capable of planning Cyber ops Unit Level • Train units for a degraded cyber environment • Seek opportunities to integrate and evaluate Cyber ops into planning, training, and exercises at all levels • Synchronization of Cyber ops with all other operations is imperative • Establish cyber OPFOR capability Service/Joint • Establish and meet Joint cyber training standards Making the US Army “Second to None” in Cyberspace… Training and Leader Development is the Key UNCLASSIFIED 14
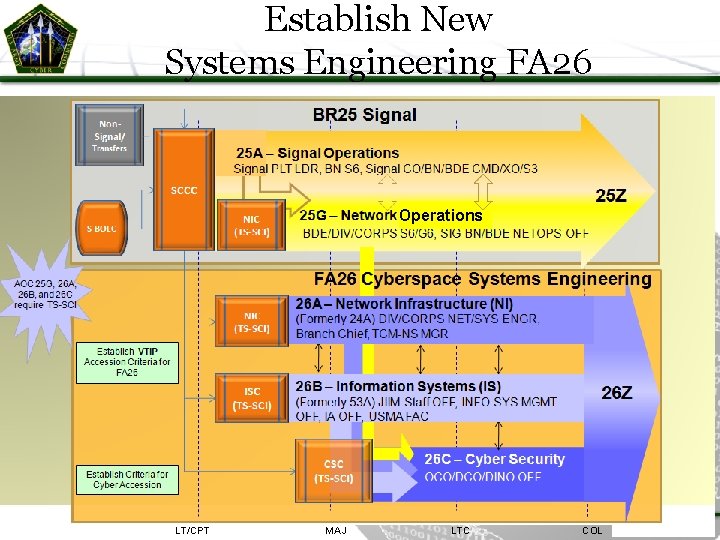
Establish New Systems Engineering FA 26 Operations LT/CPT MAJ LTC COL
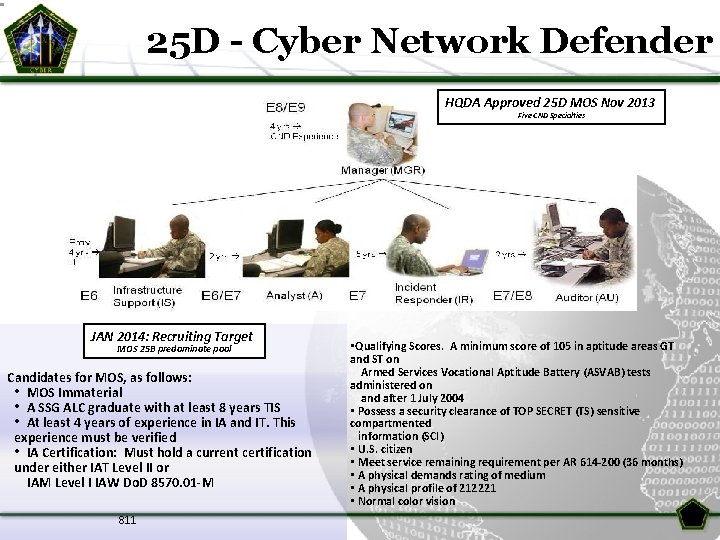
25 D - Cyber Network Defender HQDA Approved 25 D MOS Nov 2013 Five CND Specialties JAN 2014: Recruiting Target MOS 25 B predominate pool Candidates for MOS, as follows: • MOS Immaterial • A SSG ALC graduate with at least 8 years TIS • At least 4 years of experience in IA and IT. This experience must be verified • IA Certification: Must hold a current certification under either IAT Level II or IAM Level I IAW Do. D 8570. 01 -M 811 • Qualifying Scores. A minimum score of 105 in aptitude areas GT and ST on Armed Services Vocational Aptitude Battery (ASVAB) tests administered on and after 1 July 2004 • Possess a security clearance of TOP SECRET (TS) sensitive compartmented information (SCI) • U. S. citizen • Meet service remaining requirement per AR 614 -200 (36 months) • A physical demands rating of medium • A physical profile of 212221 • Normal color vision
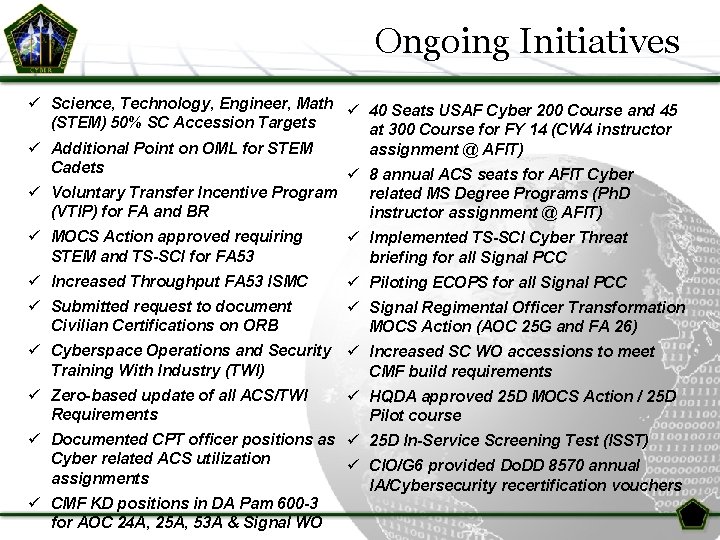
Ongoing Initiatives ü Science, Technology, Engineer, Math ü 40 Seats USAF Cyber 200 Course and 45 (STEM) 50% SC Accession Targets at 300 Course for FY 14 (CW 4 instructor ü Additional Point on OML for STEM assignment @ AFIT) Cadets ü 8 annual ACS seats for AFIT Cyber ü Voluntary Transfer Incentive Program (VTIP) for FA and BR related MS Degree Programs (Ph. D instructor assignment @ AFIT) ü MOCS Action approved requiring STEM and TS-SCI for FA 53 ü Implemented TS-SCI Cyber Threat briefing for all Signal PCC ü Increased Throughput FA 53 ISMC ü Piloting ECOPS for all Signal PCC ü Submitted request to document Civilian Certifications on ORB ü Signal Regimental Officer Transformation MOCS Action (AOC 25 G and FA 26) ü Cyberspace Operations and Security ü Increased SC WO accessions to meet Training With Industry (TWI) CMF build requirements ü Zero-based update of all ACS/TWI ü HQDA approved 25 D MOCS Action / 25 D Requirements Pilot course ü Documented CPT officer positions as ü 25 D In-Service Screening Test (ISST) Cyber related ACS utilization ü CIO/G 6 provided Do. DD 8570 annual assignments IA/Cybersecurity recertification vouchers ü CMF KD positions in DA Pam 600 -3 for AOC 24 A, 25 A, 53 A & Signal WO
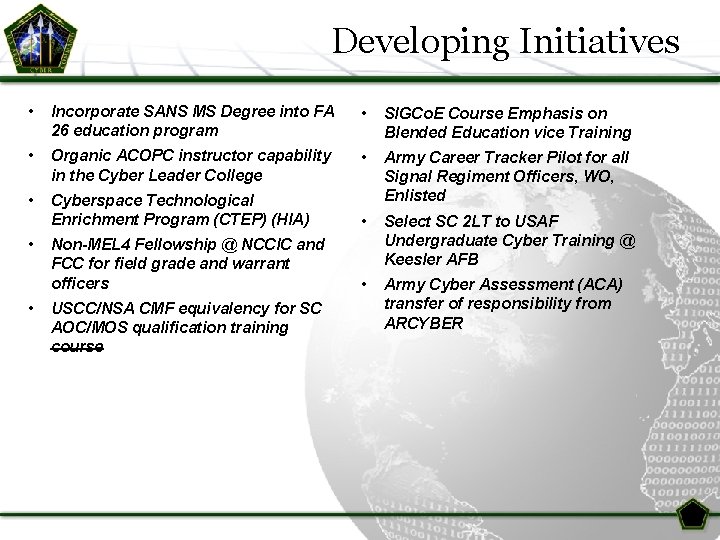
Developing Initiatives • Incorporate SANS MS Degree into FA 26 education program • SIGCo. E Course Emphasis on Blended Education vice Training • Organic ACOPC instructor capability in the Cyber Leader College • • Cyberspace Technological Enrichment Program (CTEP) (HIA) Army Career Tracker Pilot for all Signal Regiment Officers, WO, Enlisted • Non-MEL 4 Fellowship @ NCCIC and FCC for field grade and warrant officers Select SC 2 LT to USAF Undergraduate Cyber Training @ Keesler AFB • Army Cyber Assessment (ACA) transfer of responsibility from ARCYBER • • USCC/NSA CMF equivalency for SC AOC/MOS qualification training course
What We Must Do UNCLASSIFIED • Embrace cyberspace as a contested domain • Know the threat…. It is not random • Treat the Network as a weapon system • Enforce Compliance with Basic Standards and Discipline • Cyber security is not a given and remediation is expensive • This is leader’s business • Conduct Training and Leader Development • Make people the Centerpiece, not Technology Strong partnerships are critical to success UNCLASSIFIED 19
Cyber Warriors UNCLASSIFIED Vision: Professional team Ø Elite, trusted, precise, disciplined warriors Ø Culture of trust, respect, and dignity Who Ø Defend and operate all military networks Ø Provide dominant effects in cyberspace Ø Ensure Mission Command Ø Enable Unified Land Operations Ø Ensure a decisive advantage—Land Cyber The Key to Cyberspace Operations is People, not Technology UNCLASSIFIED 20
Questions UNCLASSIFIED “Transforming Cyberspace While at War… Can’t Afford Not To!” UNCLASSIFIED 21
- Slides: 21