UL 2050 National Industrial Security Systems 2011 Underwriters
- Slides: 55
UL 2050 National Industrial Security Systems © 2011 Underwriters Laboratories Inc.
Agenda • • • Introduction Fundamentals Monitoring Protection Services Transmission Methods and Alarm Installations
Introduction Module 1 © 2011 Underwriters Laboratories Inc.
Learning Objectives • After participation in this module, participants will be able to: • • Describe the Origin of Program Identify the Defining Security Documents Describe the Role of the CSO, CSA and the UL auditor Explain the Creation UL Standards
The Origin of the Program • • • Purpose Partnership Flexibility of Application • Rational • Cost Effective • Threat Appropriate
Documents Defining Security • National Industrial Security Systems , UL 2050 • National Industrial Security Systems Program • Operating Manual (NISPOM) • Director of Central Intelligence Directive, DCID 6/9 • Technical Specifications for Construction and Management of Sensitive Compartmented Information Facilities, ICS 705 -1 • Manual for Physical Security of Sensitive Conventional Arms, Ammunition, and Explosives (Do. D 5100. 76 -M) • Joint Air Force Army Navy Physical Security Manual 6/9 (JAFAN 6/9) 6
Role of the CSO/CSA • Define the Minimum Features of the IDS • Provide Prior Approval of Variables • Approve Security in Depth (SID) where • • applicable Confirm Clearances where Required Coordinate with Contractor and Alarm Company on non-technical IDS issues Coordinate with UL Representatives 7
Role of the UL Auditor • National Industrial Security Systems (CRZH) • To Audit Alarm Service Company’s that have requested UL Certificates for Compliance with UL 681 & UL 2050 • National Industrial Monitoring Station (CRZM) • To Audit Government Contractors or Central Stations that have established a Listing for Compliance with UL 2050 8
Conducting a Service Test • During business hours • Initiate a signal at an unoccupied area - Verification - Dispatch - Arrival of Investigator • After business hours (rarely done) • Initiate a signal with FSO/SSO • Initiate a telephone test - Dispatch - Arrival of Investigator 9
Fundamentals Module 2 © 2011 Underwriters Laboratories Inc.
Learning Objectives After participation in this module, participants will be able to: • Identify the responsibilities of the alarm service company • Identify the basic elements of service • Determine which paragraphs are affected by Security in • • Depth situations Identify features requiring prior approval Summarize the different types of monitoring provided
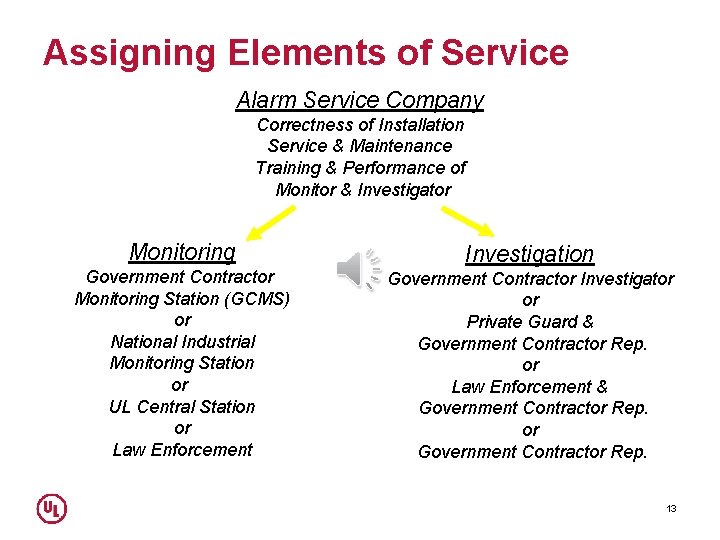
Who Is Responsible • 4. 3 of UL 2050 • Alarm Service Company may assign monitoring & investigation but retain responsibility for compliance • ASC may assign installation & service provided they supervise & verify correctness work completed • Alarm Service Company may assign maintenance, but only to personnel that work exclusively for the ASC Service Center 12
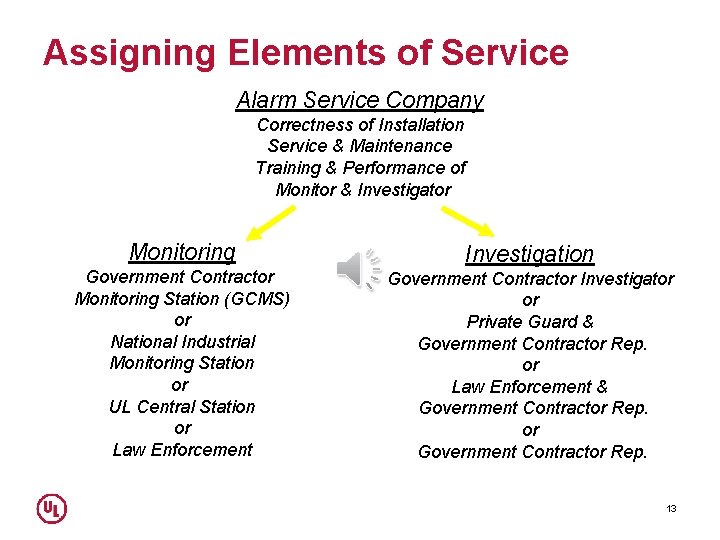
Assigning Elements of Service Alarm Service Company Correctness of Installation Service & Maintenance Training & Performance of Monitor & Investigator Monitoring Government Contractor Monitoring Station (GCMS) or National Industrial Monitoring Station or UL Central Station or Law Enforcement Investigation Government Contractor Investigator or Private Guard & Government Contractor Rep. or Law Enforcement & Government Contractor Rep. or Government Contractor Rep. 13
Security In Depth • • • Reduces electrical supervision of remote equipment rooms when a GCMS is used (Does Not Apply When Areas Housing AA&E Are Monitored, DCID or ICS 705 -1 applies) Reduces standby power requirements when a GCMS is used (except SCIF’s and SAPF’s) Allows the use of an Extent 5 design of protection in closed areas (Does Not Apply to Areas Housing AA&E or When DCID applies) 14
Features Requiring Prior Approval • Use of Extent 5* vs. Extent 3 • *Extent 5 only applies to the NISPOM • Non Line Security Transmission • Use of Data Networks • Only Monitoring Alarm & Trouble Signals • Monitoring in a Law Enforcement Agency • Investigator Response Personnel • Response Times beyond 5 or 15 Minutes 15
Monitoring Module 3 © 2011 Underwriters Laboratories Inc.
Learning Objectives After participation in this module, participants will be able to: • • Describe a Government Contractor Monitoring Station (GCMS) Discuss the National Industrial Monitoring Station (NIMS) Identify the Listed Central Station characteristics provided Describe the requirements of Law Enforcement monitoring
Monitoring Types • Government Contractor Monitoring Station • National Industrial Monitoring Station • Commercial UL Central Station • Law-Enforcement Agency or Public Emergency Center © 2011 Underwriters Laboratories Inc.
Government Contractor Monitoring Station • Purpose - to monitor industrial security systems that are installed in the following areas: • Areas occupied by the government contractor that operates the GCMS • Areas occupied by a subcontractor • Areas occupied by other government contractors • • The station is verified & receivers are maintained by the ASC service center Can only monitor systems that are maintained by the ASC service center 19
Requirements for GCMS Facilities • • Physical protection Fire Protection Standby Lighting Clocks Power Supplies - Primary and Secondary Communication Circuits Personnel
Common Logs • • • Entry Logs Standby Lighting Tests Equipment Loads Generator Tests Battery/UPS Tests Training Logs
Alarm-Receiving equipment and Automation Systems (Sec. 6. 3) See Chart 20. 1 • Alarm-Receiving Equipment shall comply with one of the following Standards: Proprietary Burglar Alarm Units and Systems (UL 1076) Central Station Burglar Alarm Systems (UL 1610) Digital Alarm Communicator Systems Units (UL 1635) • Spare parts shall be available and shall be located where they can be put into service within 60 minutes (Applies to GCMS and NIMS) • Automation Systems shall comply with one of the following Standards: Central Station Burglar Alarm Systems (UL 1610) Central Station Automation Systems (UL 1981) • When an Automation System is used operators and supervisors shall be trained and tested monthly in the use of receivers other equipment and procedures in the event of an Automation System failure.
National Industrial Monitoring Station • Purpose - to monitor industrial security systems installed in the following areas that are more than 4 hours away from the monitoring station: • Areas occupied by the government contractor that operates the NIMS • Areas occupied by a subcontractor • Areas occupied by other government contractors 23
A Listing is Required When • When the GCMS is not within the 4 hour service territory of the ASC service center to which the certificate was provided • The GCMS is maintained by a different ASC service center 24
Commercial UL Central Stations Provide • Monitoring of Alarm System • (operators & station may have to be cleared) • Processing of Signals & Creation of Records • Dispatching Investigators • Periodic Testing of Communication Links to Investigators 25
Law-Enforcement Agency or Public Emergency Center • Requires Prior Approval by CSO/CSA • Monitors System for Alarms & Trouble Conditions • Dispatches Investigators • Receivers are maintained by a UL Listed Alarm Service Company 26
Protection Service Module 4 © 2011 Underwriters Laboratories Inc.
Learning Objectives • After participation in this module, participants will be able to: • • Identify Signal processing requirements Explain Service Calls responsibilities Define Maintenance requirements Summarize record keeping responsibilities Describe Contracts and Training Describe Alarm transmission methods Design Alarm installations
Signal Processing in GCMS, NIMS, or a Central Station • Record each of the following types of signals • Openings & Closings • Alarms • Troubles • Maintain current lists of the following • Authorized operators of the system • Personnel to be notified of an alarm • The FSO/SSO • Service department personnel in the alarm service company that maintains the system 29
Alarms & Unauthorized Openings (Sec 12) • Contact-alarmed area • Verification-speak to authorized user • Late or None - During business hours - After business hours CALL FSO/SSO DISPATCH • Timely Verification - During business hours - After business hours CALL FSO/SSO REPORT TO FSO/SSO 30
Communication Channel Failures • Attempted Compromise (See Sec 13) • Treated as an Alarm if System is Armed • Treated as a Trouble if System is Disarmed • Disruption of Channel (See Sec 14) • Applies when Channel Serves More that 1 System - Contact Communication Provider - Contact FSO/SSO 31
Trouble Signals & Service Calls (Sec. 15) • Occupied or Checked Areas • Initiate repairs within 4 hours after facility opens the next day if: - Area is occupied by a person with authorized access OR - Area is checked by cleared personnel based on NISPOM • Not Occupied or Checked Areas • Initiate repairs within 4 hours 32
Maintenance (Sec. 16) • • • All systems at a government contractor’s facility and equipment in a GCMS shall be maintained in a complete functional condition. A thorough inspection, including operational tests shall be conducted on a 12 month basis by the Alarm Service Company. A record of these inspections and tests shall be maintained by the Alarm Service Company shall be available for review.
Records (Sec. 17) • • • Records shall be maintained for 12 months, except records for Special Access programs and Sensitive Compartmented information shall be maintained for 24 months. Records created in the monitoring center shall include openings, closings, alarm and trouble signals. Records shall be forwarded to or be available to the Alarm Service Company to which issued the Certificate for the protected system. Records for annual operational tests, periodic maintenance, service and both the Certificate Request form and Alarm description shall be kept throughout the life of the Certificate. Security in Depth recognition documentation shall be available for review. Service records shall include nature of service, date, time, name of service person, time of arrival and time which service was completed.
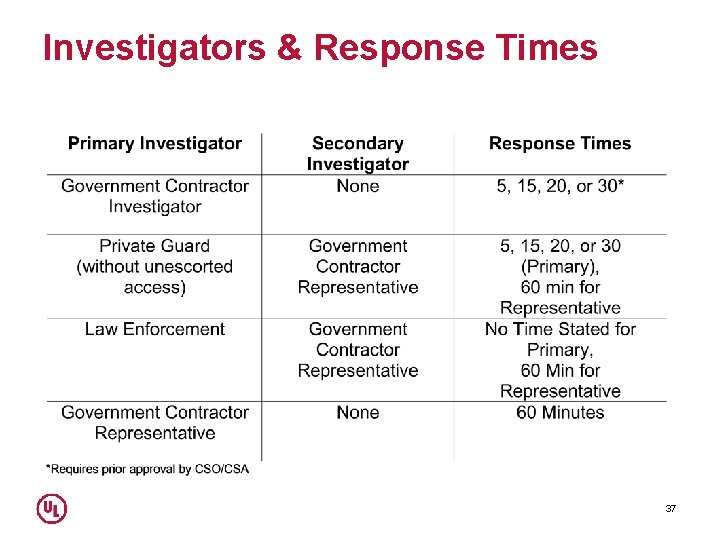
Investigators (Sec. 6. 17) • Government contractor investigators cleared & with unescorted access • Private guards without unescorted access and a representative of the government contractor • On-duty law-enforcement officer and a representative of the government contractor * • A representative of the government contractor having authorized access * *Requires Prior Approval by CSO/CSA 35
Details • If Government Contractor Representatives are used • 3 people shall be on call • The name & phone number of the FSO/SSO shall be maintained • The phone numbers shall be verified in writing every 90 days 36
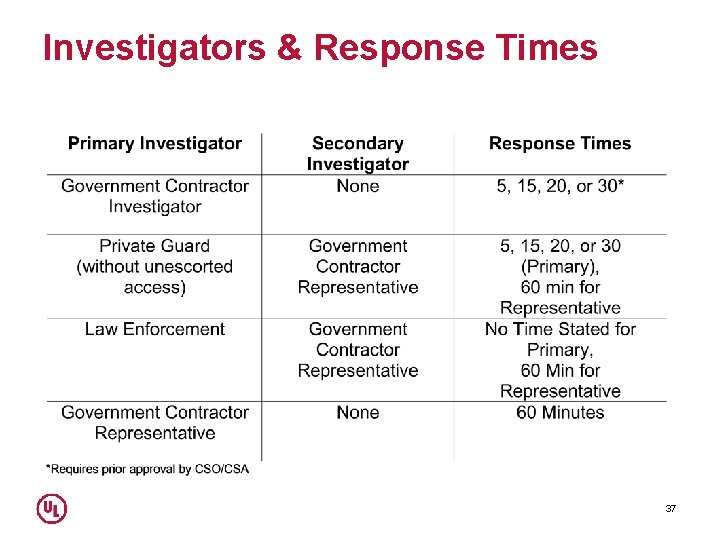
Investigators & Response Times 37
Contracts (Sec. 18) • When monitoring and investigation is assigned • 30 Day cancellation clause • DD 254 is required if monitoring or investigation is assigned to a central station and when NISPOM applies • Contracts do not relieve the Alarm Service Company from keeping the alarm and monitoring systems in compliance • Failure to uphold the contracts shall result in the cancellation of the Certificate 38
Training (Sec. 18) • The ASC is responsible to arrange for and or verify training of all those who are involved in monitoring, investigation and use of the alarm system. • Training shall be conducted annually or when there is a change • The ASC shall keep a record of the specific training and who was trained. 39
Transmission Methods and Alarm Installations Module 5 © 2011 Underwriters Laboratories Inc.
Learning Objectives After participation in this module. Participants will be to: • • • Describe transmission methods Discuss Signaling path configuration Explain manufacturer's installation instructions Discuss the security of a communications channel Identify the requirements of encryption Describe installations requirements © 2011 Underwriters Laboratories Inc.
Transmission Methods • Commonly used transmitters • • • Active Multiplex Data Network Digital Radios Line Security
Signaling Path Configurations • Single Path- 200 second check-in rate using a communicator with no dial up connection. • Dual Signal Path-360 second check-in rate on primary path and 24 -hour on secondary path. • Alternate Primary with Single Signal path-200 second check-in on either communication path. • Alternate Primary with Dual Signal path-360 second check-in rate on primary and alternate and 24 hour on second communication path.
Dual Path Technology • Data Network, 2 -way RF or Other Transmitter • Digital Alarm Communicator Transmitter • 360 second check-in on primary path • 24 -Hours on Secondary path
Manufacturer's Installation Instructions • Instructions will indicate what equipment is Listed for. • What equipment is required for system installation. • How the equipment is to be installed. • Required transmission connections. • Programming instructions for required check-in rates. • Description of the operation, testing and maintenance • procedures. Identification of replacement parts by part number or manufacturer’s model number.
Security of Communication Channels • Communication paths from the alarmed area to the • • • monitoring center are as important as the installation Line Security The supervision against compromise using 2 way communication May be either Standard or Encrypted Non-Line Security - (Requires prior approval by CSO/CSA) The supervision of a single fault condition on the communication path Exists when there is 1 way communication 46
Security of Communication Channels • Transmission methods that provide Line Security Multiplex Transponders 2 Way Radio Data Networks • Transmission methods that do not provide Line Security: Digital Alarm Communicators 1 Way Radio 47
Requirements for Encryption • Certified by NIST • At least 128 Bit Encryption • Complying with FIPS 140 -2 OR FIPS-197 • Listed by UL as Line Security Equipment • Generally Required by the CSO/CSA When Data Networks are used • TABLE 48
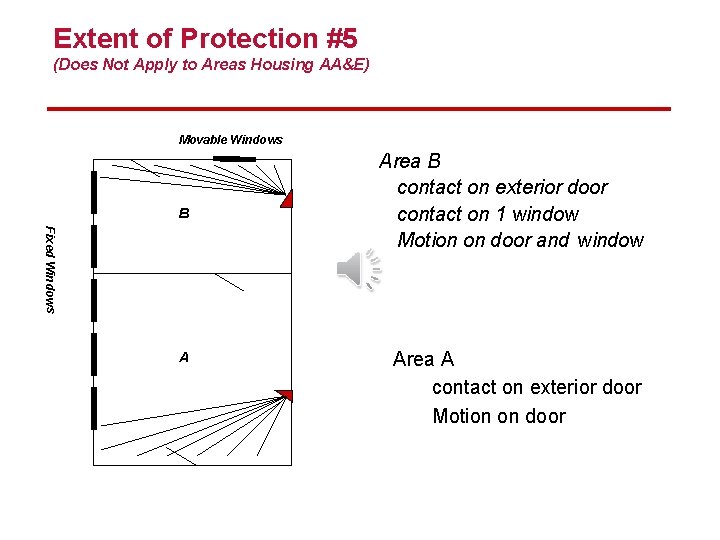
Alarm Installations (Sec. 22) • Installed in Closed Areas, SCIF’s or SAPF’s • Extent 3 • Extent 5 (Only Applies to Closed Areas under the NISPOM) • Extent 2 (Only Applies to Areas holding AA&E) • Installed in Vaults or on Container • Extent Partial • Extent Complete 49
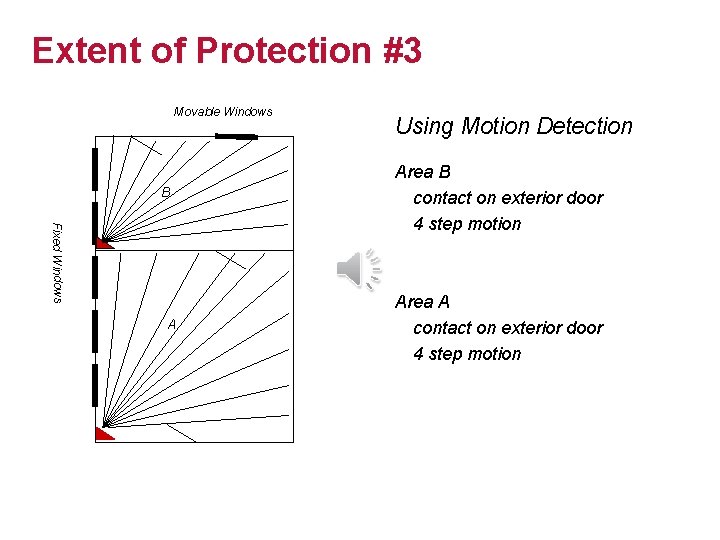
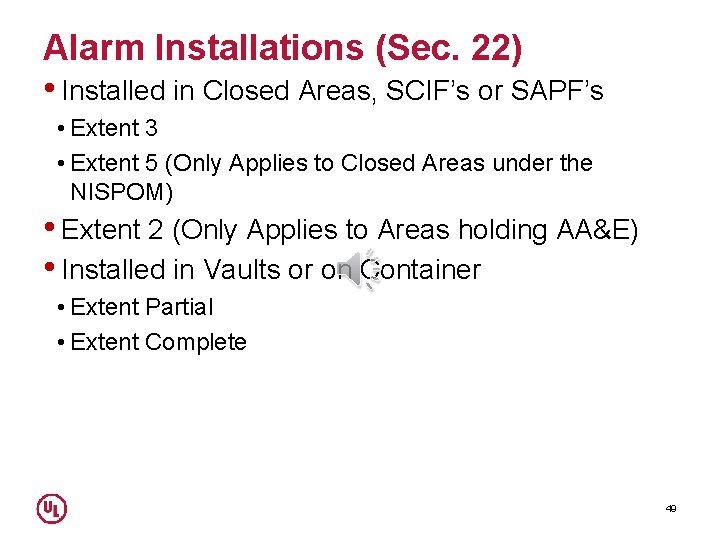
Extent of Protection #3 Movable Windows B Fixed Windows A Using Motion Detection Area B contact on exterior door 4 step motion Area A contact on exterior door 4 step motion
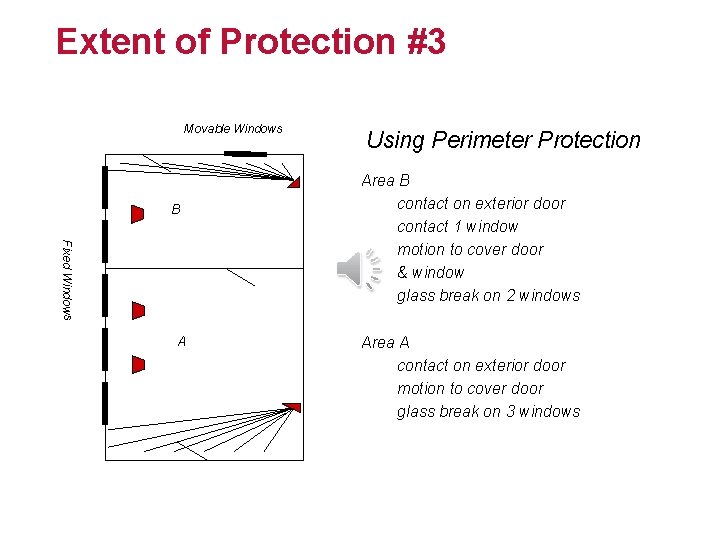
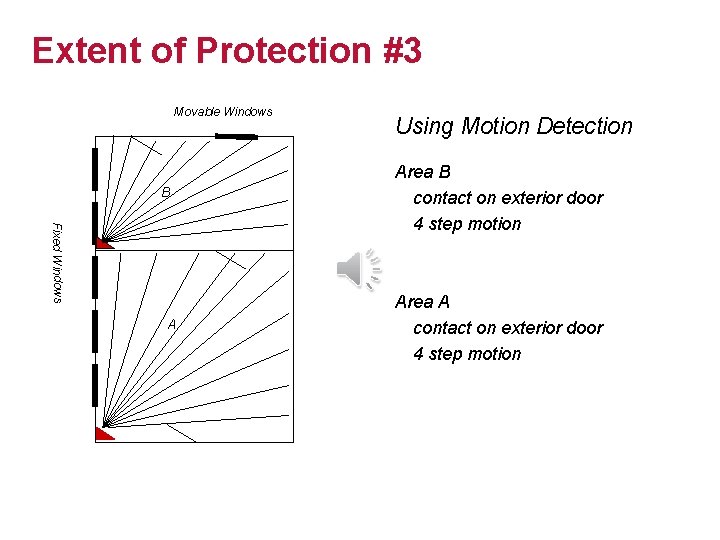
Extent of Protection #3 Movable Windows B Fixed Windows A Using Perimeter Protection Area B contact on exterior door contact 1 window motion to cover door & window glass break on 2 windows Area A contact on exterior door motion to cover door glass break on 3 windows
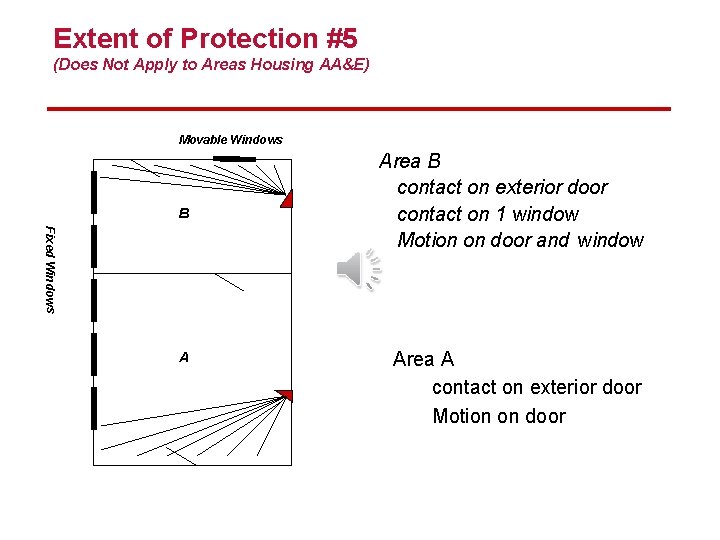
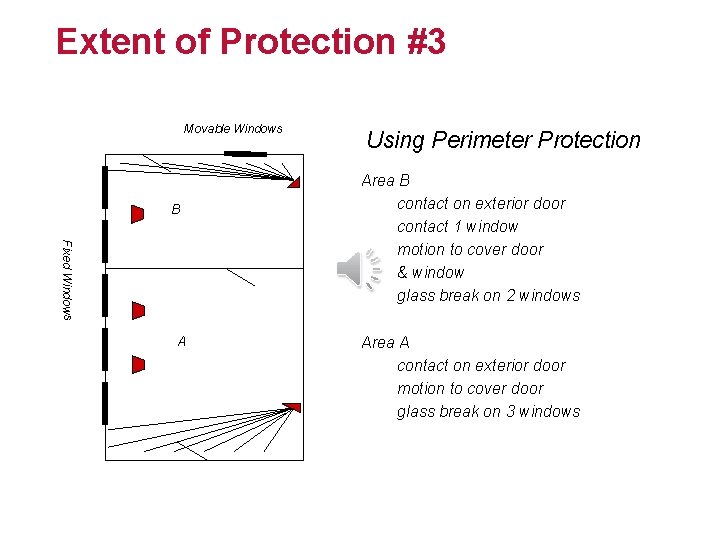
Extent of Protection #5 (Does Not Apply to Areas Housing AA&E) Movable Windows B Fixed Windows A Area B contact on exterior door contact on 1 window Motion on door and window Area A contact on exterior door Motion on door
Protection of Containers & Vaults • Extent Partial consists of a contact that is Listed for safe & vault applications on each door. One contact may be used on GSA approved containers. • Extent Complete consists of a contact that is Listed for safe & vault applications on each door. One contact may be used on GSA approved containers. In addition all exterior surfaces of the vault or container is protected with vibration sensors or proximity detectors. 53
Additional Alarm Installation Information • • Alarm Installations are based on Standard UL 681 Special Practices found in the US Government Manuals may apply and references to those can be found in UL 2050 Where motion sensors are required above ceiling or under floors, those sensor shall report independent of the UL 2050 Certificated system Some US Government Manuals may require Level I or Level II contact switches
End