U S Army Research Laboratory Army Netcentric Warfare
U. S. Army Research Laboratory Army Netcentric Warfare Dr John W. Gowens II Director Computational and Information Sciences Directorate
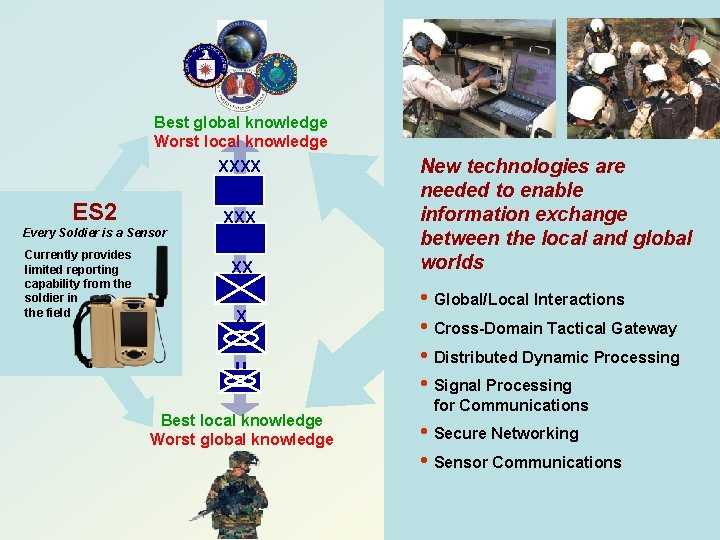
Best global knowledge Worst local knowledge XXXX ES 2 XXX Every Soldier is a Sensor Currently provides limited reporting capability from the soldier in the field XX X Best local knowledge Worst global knowledge New technologies are needed to enable information exchange between the local and global worlds • Global/Local Interactions • Cross-Domain Tactical Gateway • Distributed Dynamic Processing • Signal Processing for Communications • Secure Networking • Sensor Communications
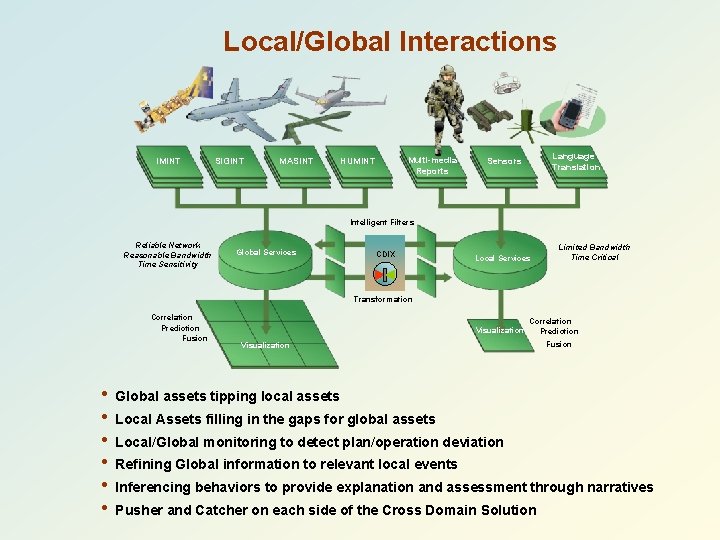
Local/Global Interactions IMINT SIGINT MASINT Multi-media Reports HUMINT Language Translation Sensors Intelligent Filters Reliable Network Reasonable Bandwidth Time Sensitivity Global Services CDIX Local Services Limited Bandwidth Time Critical Transformation Correlation Prediction Fusion • • • Visualization Correlation Prediction Visualization Fusion Global assets tipping local assets Local Assets filling in the gaps for global assets Local/Global monitoring to detect plan/operation deviation Refining Global information to relevant local events Inferencing behaviors to provide explanation and assessment through narratives Pusher and Catcher on each side of the Cross Domain Solution
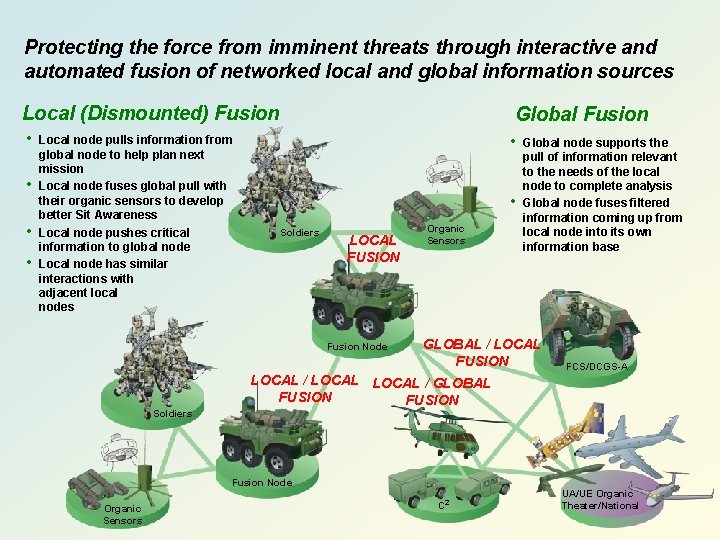
Protecting the force from imminent threats through interactive and automated fusion of networked local and global information sources Local (Dismounted) Fusion • • Local node pulls information from global node to help plan next mission Local node fuses global pull with their organic sensors to develop better Sit Awareness Local node pushes critical information to global node Local node has similar interactions with adjacent local nodes Global Fusion • • Soldiers LOCAL FUSION Fusion Node Soldiers Organic Sensors GLOBAL / LOCAL FUSION FCS/DCGS-A LOCAL / GLOBAL FUSION Fusion Node Organic Sensors Global node supports the pull of information relevant to the needs of the local node to complete analysis Global node fuses filtered information coming up from local node into its own information base C 2 UA/UE Organic Theater/National
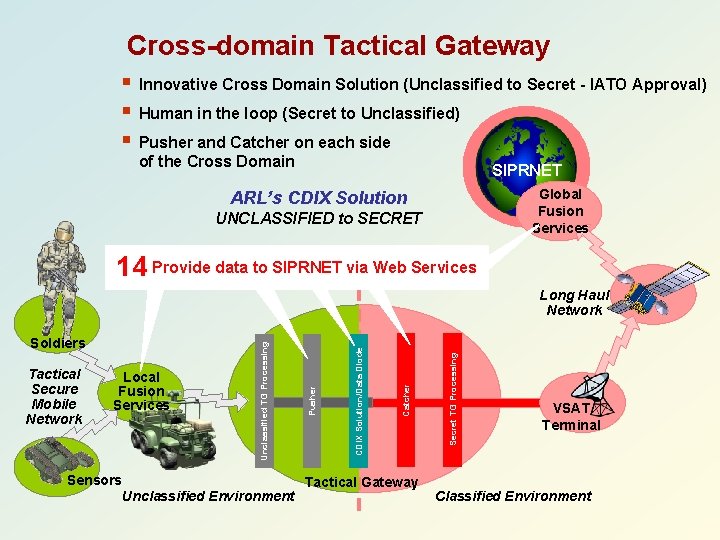
Cross-domain Tactical Gateway § § § Innovative Cross Domain Solution (Unclassified to Secret - IATO Approval) Human in the loop (Secret to Unclassified) Pusher and Catcher on each side of the Cross Domain SIPRNET Global Fusion Services ARL’s CDIX Solution UNCLASSIFIED to SECRET Provide data to SIPRNET via Web Services Digitally Detect Verify Detect Store sign Verify and unclass and sign and Apply for using reject screen unclassified meta using meta digital unclass malicious tags mobile SIPRNET mobile tags signature Do. D use code PKI cert Verify Transfer Store SIPRNET data across for digital boundary secret signature use 14 11 2 3 4 6 8 9 10 1 5 7 12 Digitally 13 Sensors Unclassified Environment Tactical Gateway Secret TG Processing Catcher Local Fusion Services CDIX Solution/Data Diode Tactical Secure Mobile Network Pusher Soldiers Unclassified TG Processing Long Haul Network VSAT Terminal Classified Environment
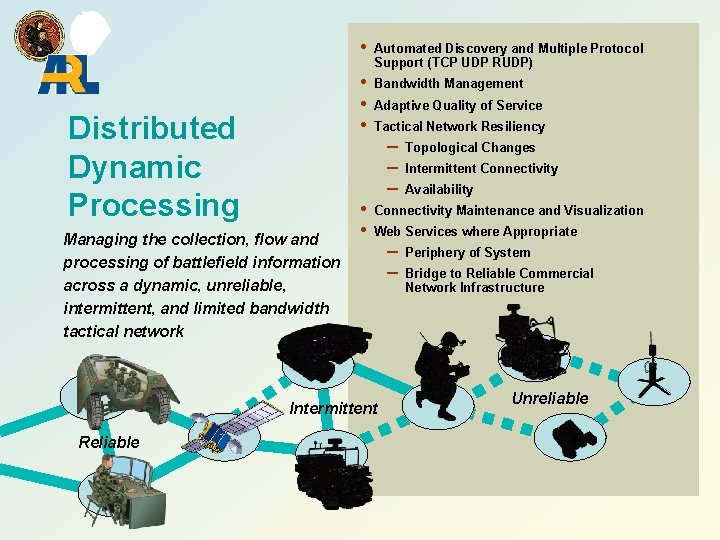
Distributed Dynamic Processing Managing the collection, flow and processing of battlefield information across a dynamic, unreliable, intermittent, and limited bandwidth tactical network • Automated Discovery and Multiple Protocol Support (TCP UDP RUDP) • • • Bandwidth Management • • Adaptive Quality of Service Tactical Network Resiliency – – – Intermittent Connectivity Availability Connectivity Maintenance and Visualization Web Services where Appropriate Intermittent Reliable Topological Changes – – Periphery of System Bridge to Reliable Commercial Network Infrastructure Unreliable
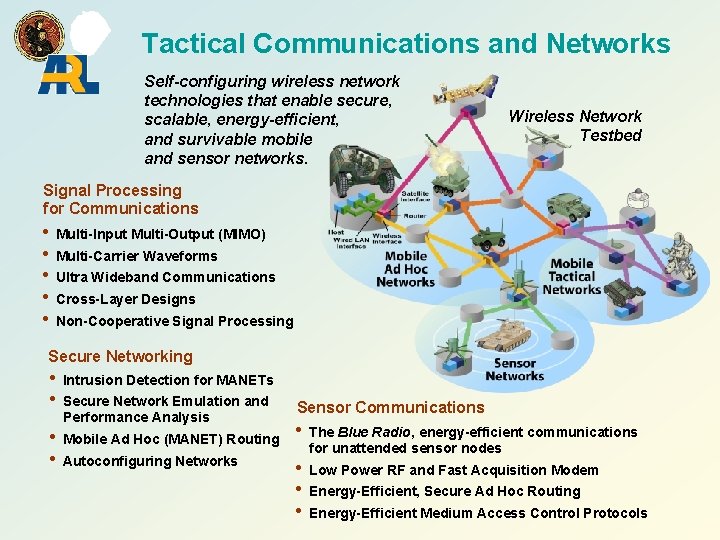
Tactical Communications and Networks Self-configuring wireless network technologies that enable secure, scalable, energy-efficient, and survivable mobile and sensor networks. Wireless Network Testbed Signal Processing for Communications • Multi-Input Multi-Output (MIMO) • Multi-Carrier Waveforms • Ultra Wideband Communications • Cross-Layer Designs • Non-Cooperative Signal Processing Secure Networking • Intrusion Detection for MANETs • Secure Network Emulation and Performance Analysis Sensor Communications Blue Radio, energy-efficient communications • Mobile Ad Hoc (MANET) Routing • The for unattended sensor nodes • Autoconfiguring Networks • Low Power RF and Fast Acquisition Modem • Energy-Efficient, Secure Ad Hoc Routing • Energy-Efficient Medium Access Control Protocols
Mobile Ad Hoc Networks
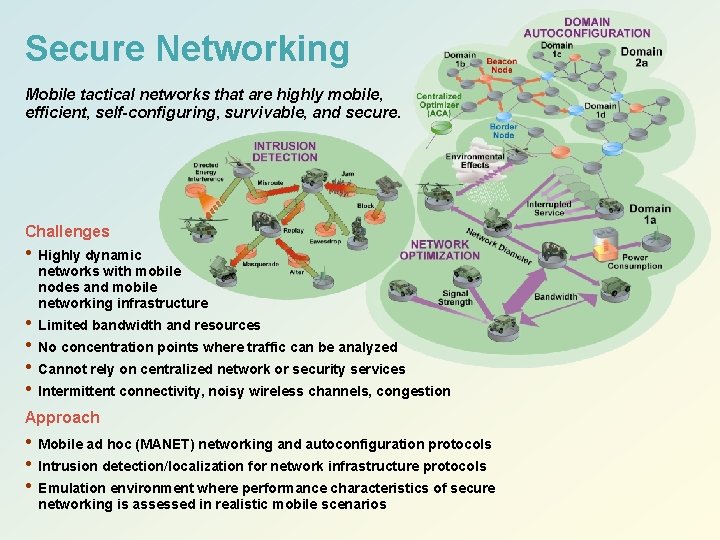
Secure Networking Mobile tactical networks that are highly mobile, efficient, self-configuring, survivable, and secure. Challenges • Highly dynamic networks with mobile nodes and mobile networking infrastructure • Limited bandwidth and resources • No concentration points where traffic can be analyzed • Cannot rely on centralized network or security services • Intermittent connectivity, noisy wireless channels, congestion Approach • Mobile ad hoc (MANET) networking and autoconfiguration protocols • Intrusion detection/localization for network infrastructure protocols • Emulation environment where performance characteristics of secure networking is assessed in realistic mobile scenarios
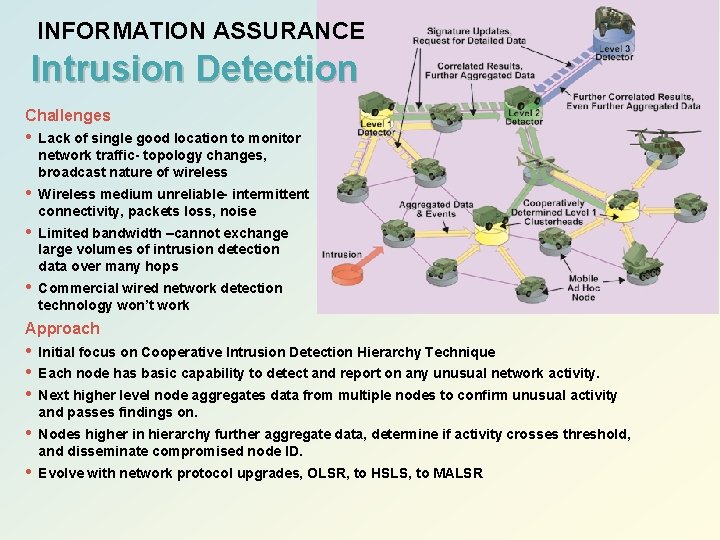
INFORMATION ASSURANCE Intrusion Detection Challenges • Lack of single good location to monitor network traffic- topology changes, broadcast nature of wireless • Wireless medium unreliable- intermittent connectivity, packets loss, noise • Limited bandwidth –cannot exchange large volumes of intrusion detection data over many hops • Commercial wired network detection technology won’t work Approach • • • Initial focus on Cooperative Intrusion Detection Hierarchy Technique • Nodes higher in hierarchy further aggregate data, determine if activity crosses threshold, and disseminate compromised node ID. • Evolve with network protocol upgrades, OLSR, to HSLS, to MALSR Each node has basic capability to detect and report on any unusual network activity. Next higher level node aggregates data from multiple nodes to confirm unusual activity and passes findings on.
Sensor Networks
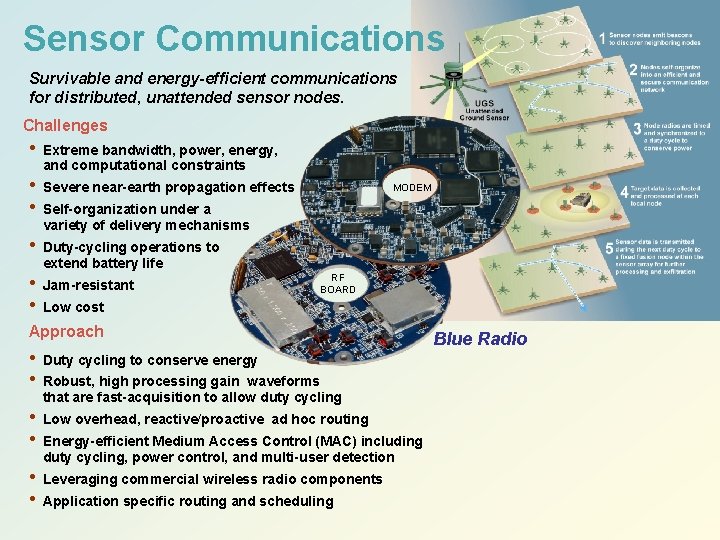
Sensor Communications Survivable and energy-efficient communications for distributed, unattended sensor nodes. Challenges • • • Extreme bandwidth, power, energy, and computational constraints Severe near-earth propagation effects MODEM Self-organization under a variety of delivery mechanisms Duty-cycling operations to extend battery life Jam-resistant RF BOARD Low cost Approach • • Duty cycling to conserve energy • • Low overhead, reactive/proactive ad hoc routing • • Robust, high processing gain waveforms that are fast-acquisition to allow duty cycling Energy-efficient Medium Access Control (MAC) including duty cycling, power control, and multi-user detection Leveraging commercial wireless radio components Application specific routing and scheduling Blue Radio
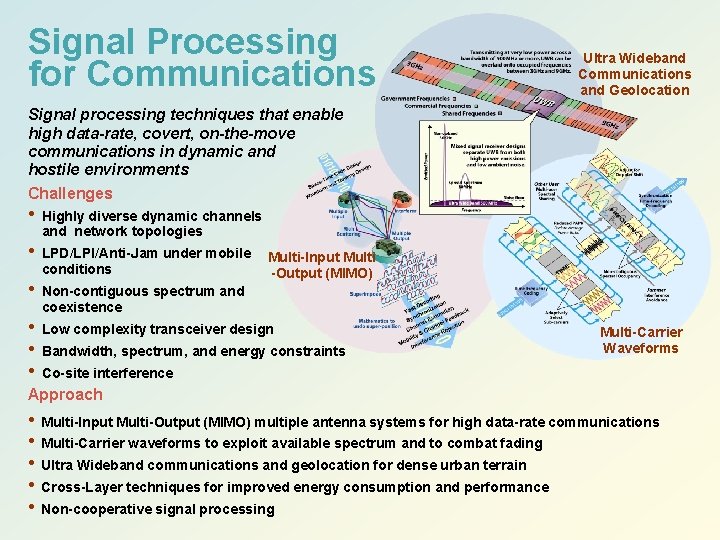
Signal Processing for Communications Ultra Wideband Communications and Geolocation Signal processing techniques that enable high data-rate, covert, on-the-move communications in dynamic and hostile environments Challenges • Highly diverse dynamic channels and network topologies • LPD/LPI/Anti-Jam under mobile conditions • Non-contiguous spectrum and Multi-Input Multi -Output (MIMO) coexistence • Low complexity transceiver design • Bandwidth, spectrum, and energy constraints • Co-site interference Multi-Carrier Waveforms Approach • Multi-Input Multi-Output (MIMO) multiple antenna systems for high data-rate communications • Multi-Carrier waveforms to exploit available spectrum and to combat fading • Ultra Wideband communications and geolocation for dense urban terrain • Cross-Layer techniques for improved energy consumption and performance • Non-cooperative signal processing
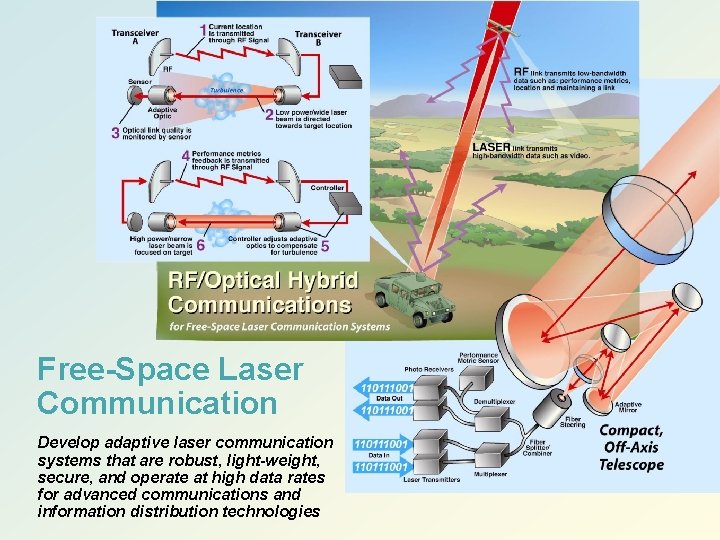
Free-Space Laser Communication Develop adaptive laser communication systems that are robust, light-weight, secure, and operate at high data rates for advanced communications and information distribution technologies

Army netcentric warfare depends on MANET technology for connectivity
- Slides: 15