Tugboat Captains Clinicians Both are in Harms Way
Tugboat Captains & Clinicians Both are in Harms Way Presented to: Internet 2 Conference Atlanta, GA - October 31, 2000 W. Holt Anderson, Executive Director NC Healthcare Information & Communications Alliance, Inc. (NCHICA)
Structure of Presentation • • • Implementing a Vision HIPAA Health. Key NC Projects Federal PKI Bridge The Tugboat Captain 2
Implementing a Vision • “Paperless, person-centered health records by 2010. ” • Adopted by the following organizations in NC: – – – – – Medical Society Nurses Association Hospital Assn. Health Information Management Assn. of Local Health Directors Assn. of Pharmacists Health Care Facilities Assn. For Health Care Quality Assn. For Hospice & End of Life Care 3
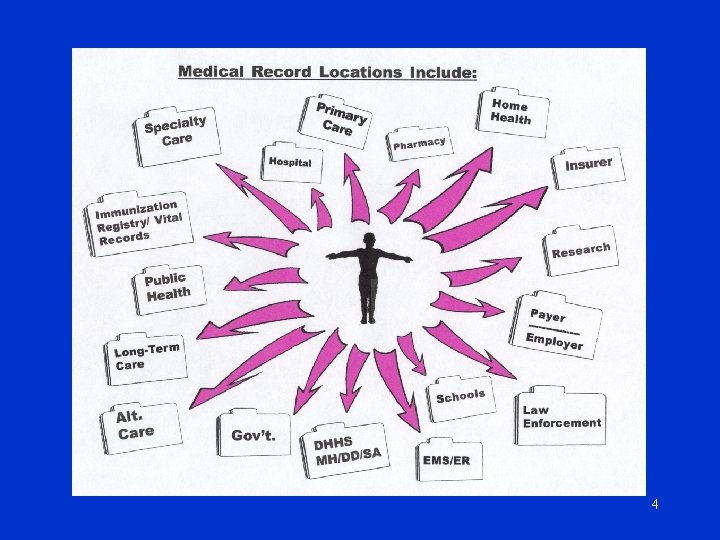
4
Definition - Health Record • A virtual digital record of an individual’s health information and all episodes of care • This record is maintained by multiple providers and shared when necessary for care of that individual (as allowed by patient consent and/or law) • NOT a central “master file”of information 5
Enhancing the Quality of Care • Preventing medical mishaps related to drug interactions, handwriting, allergies, transmissible diseases, etc. (Automated delivery of information) • Enhancing quality control through access to information 6
Death by Handwriting • Texas cardiologist – Prescribed 20 mg Isordil 4 X / day • Pharmacist – Filled 20 mg Plendil 4 X / hday = 80 mg / day – Normally Plendil taken max 10 mg / day • 42 -year old patient died of heart attack • Jury found MD and Pharmacist responsible and awarded $450 K to widow and three small children USA Today 10 -21 -99 7
Controlling and Reducing Costs Cost of paper records is said to be at least 25% of total health care costs. • Minimize space requirements • Reduce resources for filing, storage and retrieval of information • Improve access time • Less duplication 8
![HIPAA Health Insurance Portability & Accountability Act of 1996 [PL 104 -191] • Administrative HIPAA Health Insurance Portability & Accountability Act of 1996 [PL 104 -191] • Administrative](http://slidetodoc.com/presentation_image/64edb67a294b9e89ef0157e69040d8ec/image-9.jpg)
HIPAA Health Insurance Portability & Accountability Act of 1996 [PL 104 -191] • Administrative Simplification – – Electronic Transactions & Codes National Identifiers Security & Electronic Signatures Privacy • Generally expected to be implemented by end of 2002 • Civil Monetary & Criminal Penalties 9
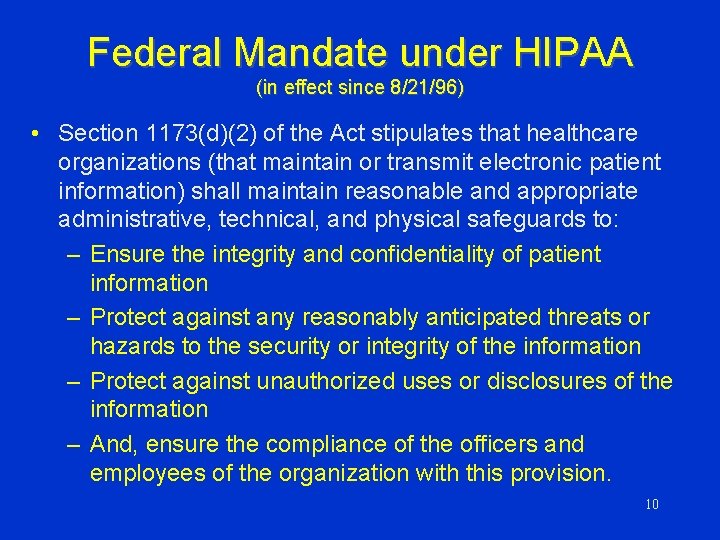
Federal Mandate under HIPAA (in effect since 8/21/96) • Section 1173(d)(2) of the Act stipulates that healthcare organizations (that maintain or transmit electronic patient information) shall maintain reasonable and appropriate administrative, technical, and physical safeguards to: – Ensure the integrity and confidentiality of patient information – Protect against any reasonably anticipated threats or hazards to the security or integrity of the information – Protect against unauthorized uses or disclosures of the information – And, ensure the compliance of the officers and employees of the organization with this provision. 10
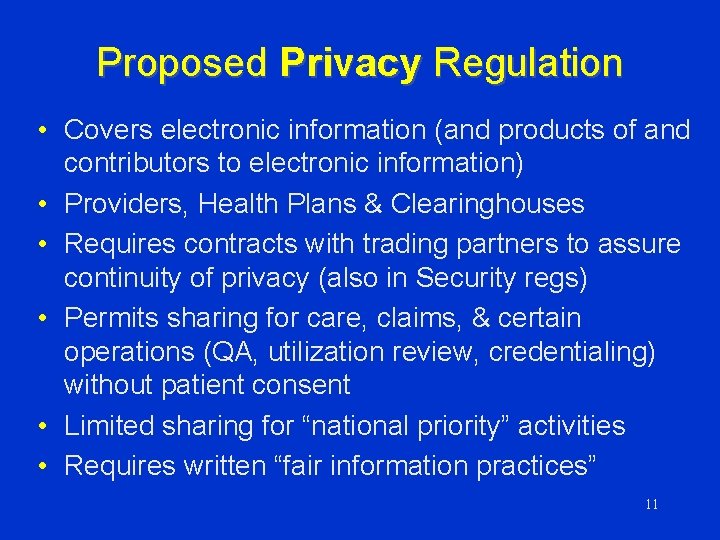
Proposed Privacy Regulation • Covers electronic information (and products of and contributors to electronic information) • Providers, Health Plans & Clearinghouses • Requires contracts with trading partners to assure continuity of privacy (also in Security regs) • Permits sharing for care, claims, & certain operations (QA, utilization review, credentialing) without patient consent • Limited sharing for “national priority” activities • Requires written “fair information practices” 11
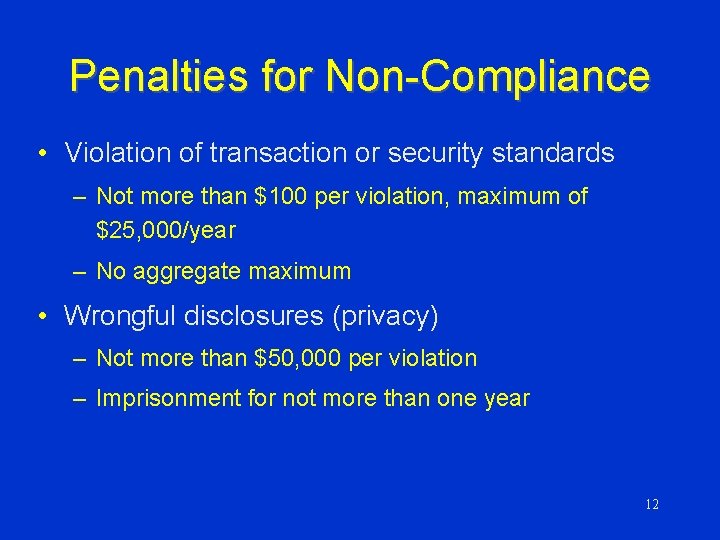
Penalties for Non-Compliance • Violation of transaction or security standards – Not more than $100 per violation, maximum of $25, 000/year – No aggregate maximum • Wrongful disclosures (privacy) – Not more than $50, 000 per violation – Imprisonment for not more than one year 12
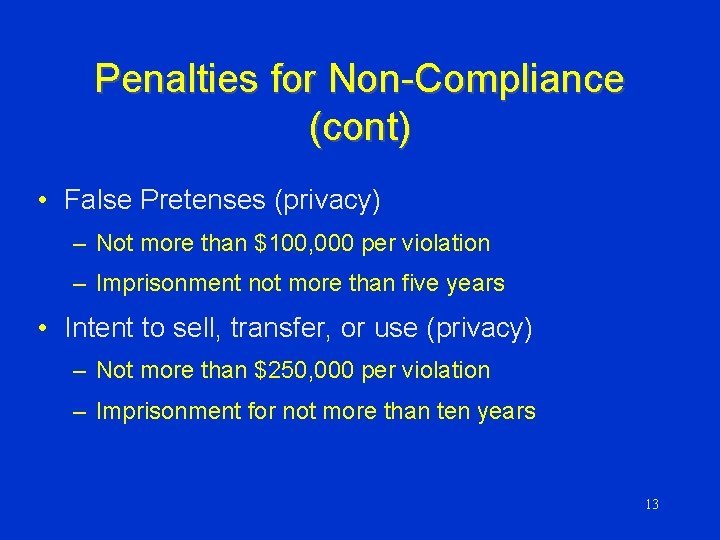
Penalties for Non-Compliance (cont) • False Pretenses (privacy) – Not more than $100, 000 per violation – Imprisonment not more than five years • Intent to sell, transfer, or use (privacy) – Not more than $250, 000 per violation – Imprisonment for not more than ten years 13
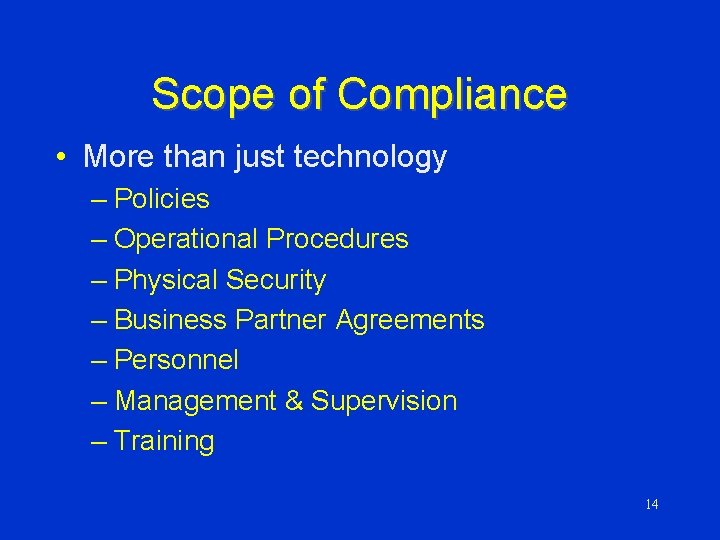
Scope of Compliance • More than just technology – Policies – Operational Procedures – Physical Security – Business Partner Agreements – Personnel – Management & Supervision – Training 14
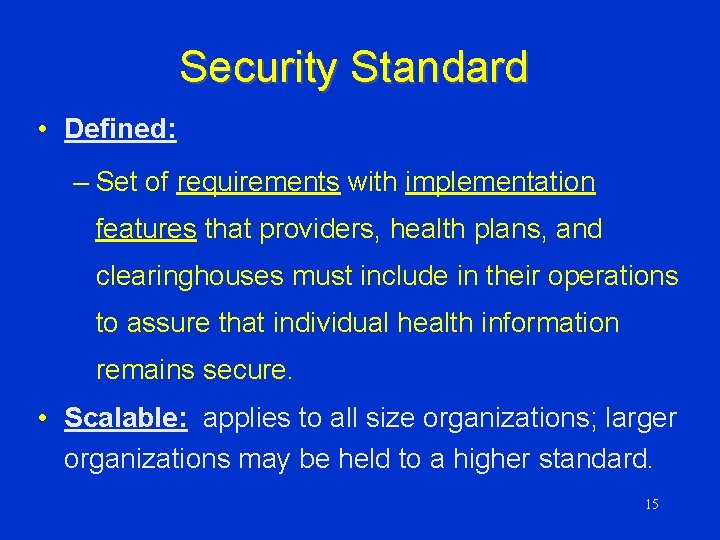
Security Standard • Defined: – Set of requirements with implementation features that providers, health plans, and clearinghouses must include in their operations to assure that individual health information remains secure. • Scalable: applies to all size organizations; larger organizations may be held to a higher standard. 15
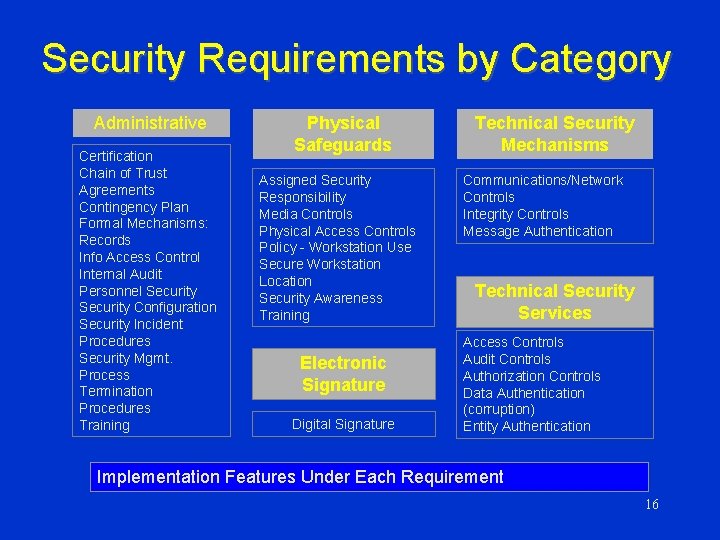
Security Requirements by Category Administrative Certification Chain of Trust Agreements Contingency Plan Formal Mechanisms: Records Info Access Control Internal Audit Personnel Security Configuration Security Incident Procedures Security Mgmt. Process Termination Procedures Training Physical Safeguards Assigned Security Responsibility Media Controls Physical Access Controls Policy - Workstation Use Secure Workstation Location Security Awareness Training Electronic Signature Digital Signature Technical Security Mechanisms Communications/Network Controls Integrity Controls Message Authentication Technical Security Services Access Controls Audit Controls Authorization Controls Data Authentication (corruption) Entity Authentication Implementation Features Under Each Requirement 16
Technical Security Mechanisms Objective: Ensure processes are in place to guard against unauthorized access to data that is transmitted over a communications network (intercept and interpret), and to protect systems from external access. 17
Communications--Open Network • Where the network is open (e. g. , shared data line, Internet, switched WAN), then the following must be in place: – Alarm (sense abnormal conditions) – Audit Trail – Entity Authentication – Event Reporting – Encryption is stated as “should be employed” 18
If You Use Electronic Signatures • Must have: – message integrity – non-repudiation – user authentication • May have: – ability to add attributes – continuity of signature capability – countersignature capability – independent verifiability – interoperability – multiple signatures – transportability 19
Health. Key Secure E-Health Solutions A Program funded by The Robert Wood Johnson Foundation 20
Health. Key Origins q Funded by $2. 5 million Robert Wood Johnson Foundation grant - Fall 1999 q Collaboration to advance the development of health information infrastructure q Market-driven, q Coordinated community-based approach pilot efforts in 5 states 21

Health. Key Participants Massachusetts Health Data Consortium (MHDC) q Minnesota Health Data Institute (MHDI) q North Carolina Healthcare Information and Communications Alliance (NCHICA) q Utah Health Information Network (UHIN) q Community Health Information Technology Alliance (CHITA) -- WA q 22
Health. Key Strategy q Identify interoperable, standards-based solutions to real business problems q Showcase pilot participants as leaders in testing evolving health information infrastructure q Identify approaches to achieve HIPAA compliance 23
$64, 000 Question Is PKI a valid infrastructure for the health industry? If so, what is the likely architectural model? 24
MN & NC to pilot Bridge CA q Developed by Mitretek for the Federal Dept of Treasury/GSA q Allows validation of digital certificates from multiple CAs q Aggressive timeframe - demo by Spring 2000 q Additional states/projects can tie in after pilot phase 25
q NCHICA PKI Projects – Rekmote access to immunization registry – Shared access to clinical info for Medicaid high-maintenance patients – Remote primary care provider access to neonatal/perinatal patient info – Remote primary care provider access to patient info for children with special needs – Access to emergency dept. database – Possible pharmacy application 26
q MHDI PKI Projects – Access to Immunization data – Transmit newborn screening results from MN Dept of Health – Provide secure access to Central Query Service for eligibility inquiries q Other States – Additional projects underway 27

Provider Access to Immunization Registry Securely PAi. RS
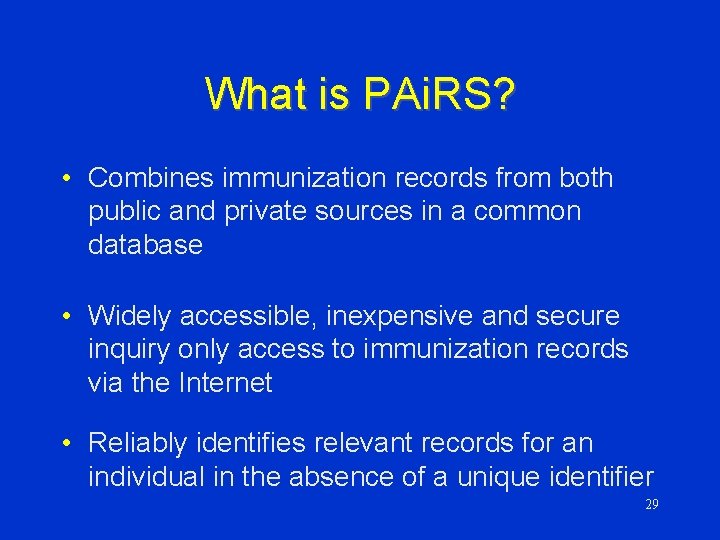
What is PAi. RS? • Combines immunization records from both public and private sources in a common database • Widely accessible, inexpensive and secure inquiry only access to immunization records via the Internet • Reliably identifies relevant records for an individual in the absence of a unique identifier 29
Current Project Status • Approximately 1. 5 million children (0 -18) and an associated 12 million vaccine doses • 28 pilot sites, 172 users • Over $1 million in in-kind contributions 30
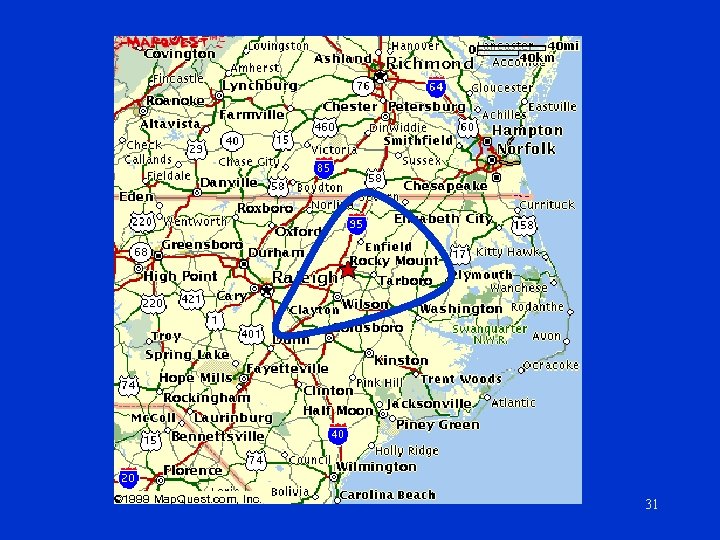
31
Challenges to Successful Implementation of PAi. RS: • • • Initiation of use Recognition of PAi. RS value Accessibility of computers Computer skills of nurses and physicians Busy practices with established service delivery methods • Security & Interoperability 32
Where do we go from here? • PAi. RS participation expansion • PKI for user authentication and security • Regional PAi. RS project - demonstration project to facilitate inter-state exchange of immunization information 33
NCEDD Project Description • 3 goals (putting down a railroad track) – select a standard data format (DEEDS) – demonstrate secure data exchange – statewide ED database for injury surveillance, EMS outcomes, best practice (NCEDD) 35
Use of NCEDD Data • Public Health Surveillance – Disasters, bioterrorism, reportable conditions • Research using hospital discharge dataset – Injury surveillance, Trends/impact of new facilities, HMO penetration, substance abuse indicators • Linkages- outcomes, episode of care – EMS – Trauma Registry – Hospital Database • Aggregate format – Oversight Committee of participating hospitals 36
NCEDD Security
Security/Access Concerns • Confidential data over Internet – Patient – Facility – Provider • Authentication of users - multiple organizations – Public health staff - SCHS, Epidemiology – STEER staff - Chapel Hill, Wilmington – Participant hospitals ? 38
Federal PKI Approach (with thanks to Richard A. Guida, Chair, Federal PKI Steering Committee) • Establish Federal PKI Policy Authority • Develop/deploy Bridge CA using COTS – Four levels of assurance (emulate Canada) – Prototype early 2000, production mid 2000 • Deal with directory issues in parallel – Border directory concept; “White Pages” • Use ACES (Access Certs for Electronic Services) for public transactions 39
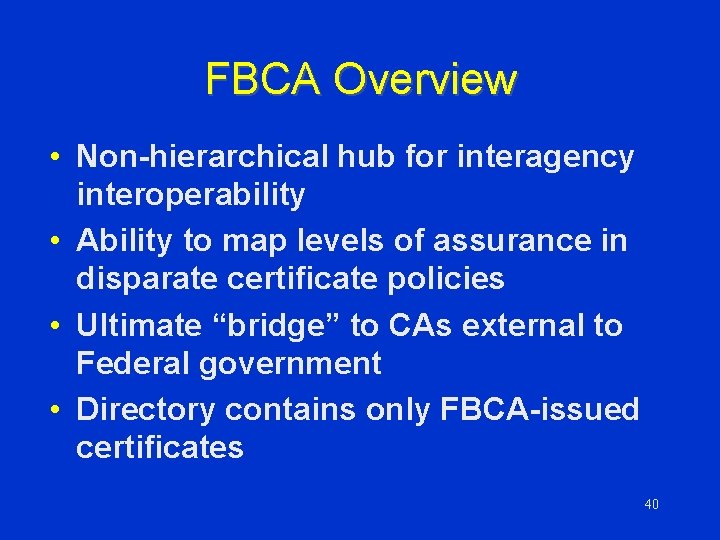
FBCA Overview • Non-hierarchical hub for interagency interoperability • Ability to map levels of assurance in disparate certificate policies • Ultimate “bridge” to CAs external to Federal government • Directory contains only FBCA-issued certificates 40
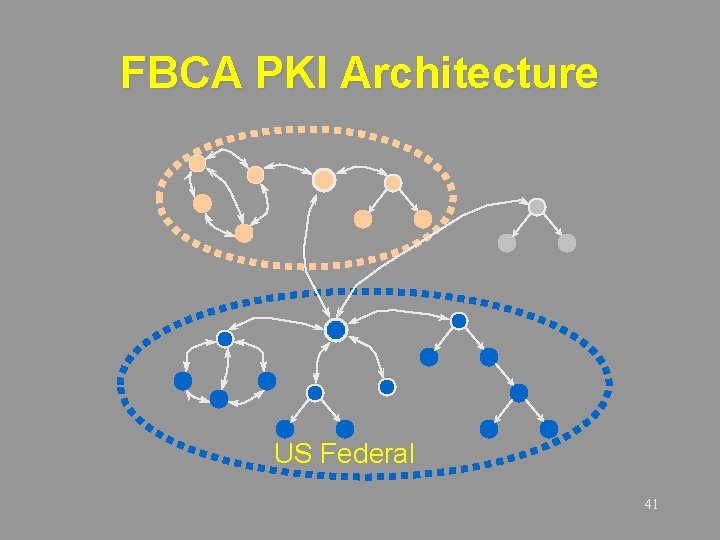
FBCA PKI Architecture US Federal 41
Potential Architectures • Multiple CAs within membrane, with single signing key • Single CA • Multiple CAs within membrane, crosscertified among themselves 42
Multiple CAs, Cross-certified • In essence, the “quark” model • Certificate path length may be +1 • Adding CAs within membrane should be straightforward albeit not necessarily easy • Requires solving inter-product interoperability issues within membrane rather than outside - which is good 43
Current Status • Decision: cross-certified CAs within membrane • Multiple vendor products: Initially Entrust and GTE for “prototype” FBCA • Migration from prototype to production FBCA will entail adding other CAs inside the membrane • GSA/FTS has responsibility to execute 44
PKI Use and Implementation Issues • Misunderstanding what it can and can’t do • Requiring legacy fixes to implement • Waiting for standards to stabilize • High cost - a yellow herring • Interoperability woes - a red herring • Legal trepidation - the brightest red herring 45
The Tugboat Captain TJ Hooper v. Northern Barge Company 60 F. 2 d 737 (2 d Cir. 1932) • Long Island Sound - storm comes up and tug loses barge • Plaintiff was barge owner • Plaintiff found negligent because Captain had no weather radio Rationale: to avoid negligence, keep up with technological innovations - they set the standard of care in the industry 46
The price of good navigation is eternal vigilance W. Holt Anderson, Executive Director NC Healthcare Information & Communications Alliance, Inc. www. nchica. org

Thank you ! www. nchica. org
- Slides: 48