TTS 1133 INTERNET ETHICS AND CYBER LAW CHAPTER
TTS 1133 : INTERNET ETHICS AND CYBER LAW CHAPTER THREE: Privacy
CONTENTS IT privacy protection and the law The right of privacy History of privacy protection – a case example Key privacy and anonymity issues ◦ Data encryption ◦ Consumer profiling ◦ Consumer data treatment – database and marketing ◦ Workplace monitoring ◦ Spamming ◦ Advanced surveillance technology Protecting privacy ◦ Awareness The cyber law and regulations
Introduction The use of information technology in business requires the balancing of the needs of those who use information about individuals against the right and desires. Handling information responsibly means understanding the following issues ◦ Ethics ◦ Personal privacy ◦ Threats to information ◦ Protection of information
Privacy – the right to left alone when you want to be, to have control over your own personal possessions, and not to be observed without your consent Dimensions of privacy ◦ Psychological: to have a sense of control ◦ Legal: to be able to protect yourself
What is Information Privacy? Information privacy is the ability of an individual or group to stop information about themselves from becoming known to people other than those they choose to give the information to. Privacy is sometimes related to anonymity although it is often most highly valued by people who are publicly known. Privacy can also be seen as an aspect of security—one in which there are trade-offs between the interests of one group and another can become particularly clear
Privacy and Employees Companies need information about their employees to run their business effectively As of March 2005, 60% of employers monitored employee e-mails 70% of Web traffic occurs during work hours 78% of employers reported abuse 60% employees admitted abuse
Privacy and Government Agencies About 2, 000 government agencies have databases with information on people Government agencies need information to operate effectively Whenever you are in contact with government agency, you leave behind information about yourself
Issues on Privacy A Canadian funeral home obtained the names and addresses of people diagnosed with cancer, and contacted a Montreal woman on the list about buying a burial plot and pre-paid funeral services. A candy company got hold of the names of people in a weight watchers program, and sent them chocolate bars in the mail. Part of a Toronto woman's medical record was printed on the back of real estate flyers which were delivered to hundreds of mailboxes. Participants in a medical research study on sickle cell anemia reported an increase in difficulties getting employment and insurance after they gave genetic samples to the researchers. Phone Busters National Call Centre reports that over 7, 600 Canadians had their identities stolen in 2002, with total losses of more than $8. 5 million.
Laws on Privacy Health Insurance Portability and Accountability Act (HIPAA) protects personal health information Financial Services Modernization Act requires that financial institutions protect personal customer information
Security And Employees Attacks on information and computer resources come from inside and outside the company Computer sabotage costs about $10 billion per year In general, employee misconduct is more costly than assaults from outside
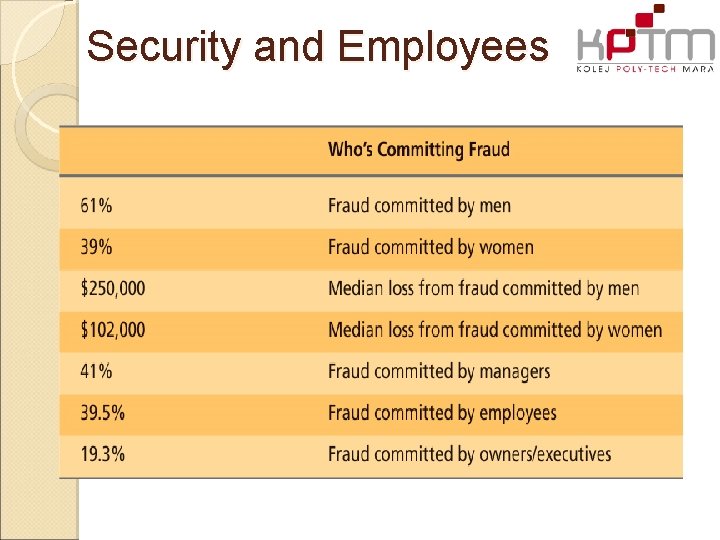
Security and Employees
IT Privacy & Protection In Malaysia, we have: Akta Komunikasi dan Multimedia 1998 merupakan satu Akta berkenaan undang -undang siber dan dibentuk sebagai satu rangkakerja bagi campurtangan kerajaan Malaysia dalam memantau industri komunikasi dan multimedia. Communications and Multimedia Act 1998 is an Act of cyber laws and established as a framework for the intervention of the government in monitoring communications and multimedia industry
Communications and Multimedia Act 1998 The activities and services controlled under this Act, ◦ Traditional broadcasting ◦ Telecommunications ◦ Online services, - including facilities and networks However, there is no provision in the Act that allow Internet censorship. Under the MSC Malaysia Bill Guarantees (MSC Malaysia Bill of Guarantees), the government pledged not to censor the Internet.
ACT - Related This Act is the cyber laws of the longest among the six cyber laws enacted in Malaysia so far. Apart from this Act, there another five related: ◦ ◦ ◦ Computer Crimes Act 1997. Digital Signature Act 1997. Telemedicine Act 1997. Copyright Amendment Act 1997. Malaysian Communications Council and Multimedia Act 1998.
Computer Crime Act 1997 Computer Crimes Act 1997 was associated with offenses related to misuse of computers for the purpose of committing crimes. Under this act, unauthorized access or modify any program or data contained in a computer is wrong and punishable. This Act is effective to any crime committed outside of Malaysia even though the offense is committed by a person or from any place outside Malaysia as long as the computer, program or data is located in Malaysia or accessible, connected or used with a computer in Malaysia.
Digital Signature Act 1997 is a deed made to give confidence and encourage the public to conduct secure electronic transactions both locally and internationally. This Act into force on October 1, 1998. Under this act, providing a digital signature verification system to confirm the identity of the sender and verify that the message is sent. To enable the digital signature is certified, a certificate of authority must be obtained. Certificates will be sent with a message to confirm the message was correct as sent and received.
Telemedicine Act 1997 is an Act of Malaysia for the regulation and control of the practice of telemedicine, and for matters connected therewith. This Act is one of six cyber laws enacted in Malaysia so far. This Act is not enforceable, and subject to the discretion of the Minister of Health.
Data Encryption is the process of converting data (plaintext) into something that appears to be random and meaningless (ciphertext), which is difficult to decode without a secret key. Encryption is used to provide message confidentiality. Decryption is the reverse process which is transforming an encrypted message back into normal. Encipher, decipher, encode, decode is the same word for encryption and decryption.
TYPES OF ENCRYPTION Two main types of encryption: ◦ Asymmetric encryption (public-key encryption) ◦ Symmetric encryption (secret-key encryption). Encryption is the method to make sure that the message didn’t access by illegal person. 19
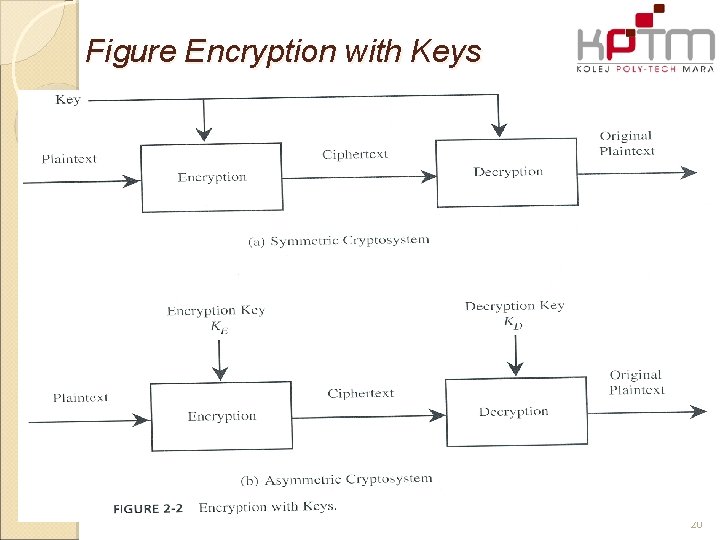
Figure Encryption with Keys 20
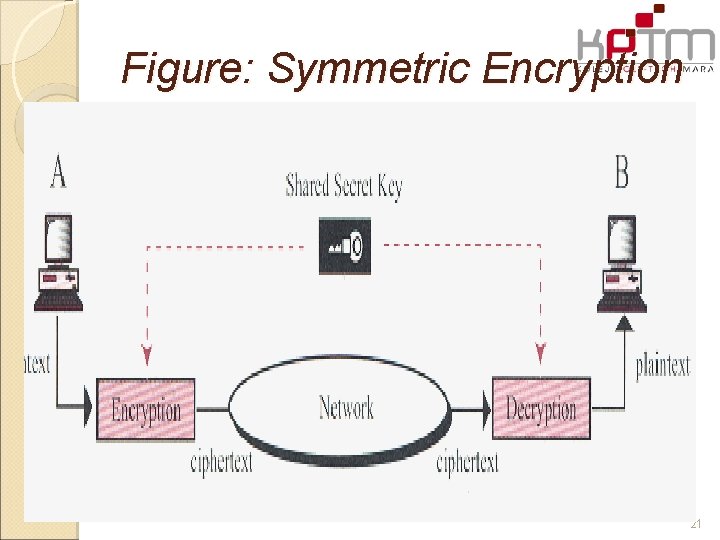
Figure: Symmetric Encryption 21
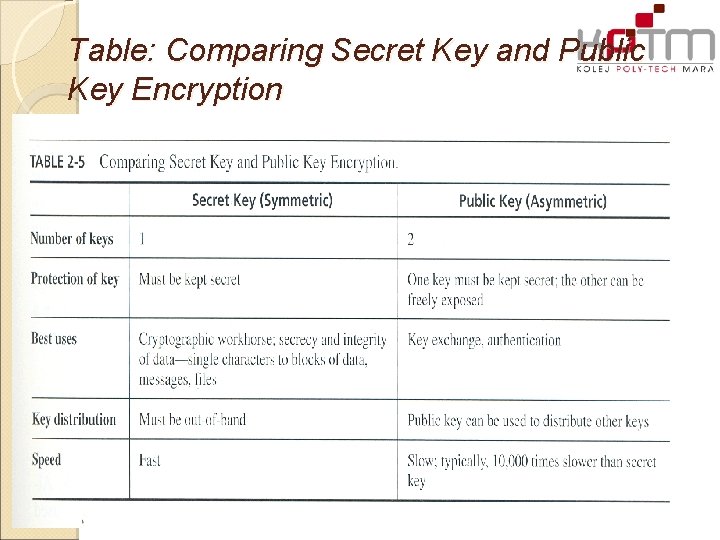
Table: Comparing Secret Key and Public Key Encryption 22
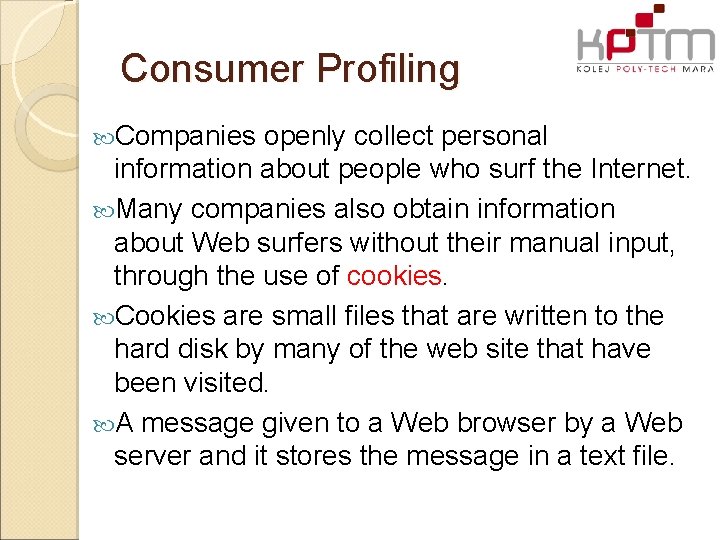
Consumer Profiling Companies openly collect personal information about people who surf the Internet. Many companies also obtain information about Web surfers without their manual input, through the use of cookies. Cookies are small files that are written to the hard disk by many of the web site that have been visited. A message given to a Web browser by a Web server and it stores the message in a text file.
COOKIES The main purpose of cookies is to identify users and possibly prepare customized Web pages for them. These are tokens that are attached to a user or program and change depending on the areas entered by the user or program. For example, online retail sites use cookies to implement shopping charts, which enable you to make selections on shopping activities. Several Internet and networks, such as Double. Click, use cookies to track user’s browsing actions across thousands of the most popular Internet sites. Prepared By: Razif Razali 24
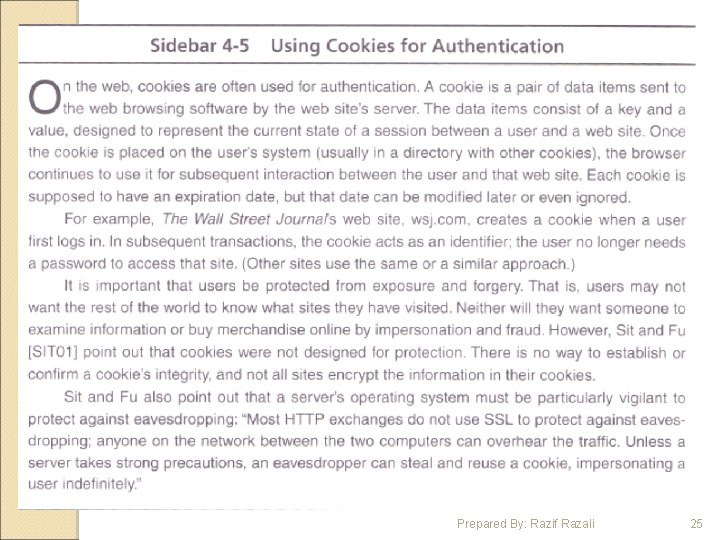
Prepared By: Razif Razali 25
SPAMMING Spam is the use of electronic messaging systems (including most broadcast media, digital delivery systems) to send unsolicited bulk messages indiscriminately. Some people define spam even more generally as any unsolicited e-mail. However, if a long-lost brother finds your e-mail address and sends you a message, this could hardly be called spam, even though it's unsolicited. Real spam is generally e-mail advertising for some product sent to a mailing list or newsgroup. People who create electronic spam are called spammers.
Protecting Privacy Steps in protecting privacy from the risks of computer technology is awareness of how: ◦ Technology works ◦ How it’s being used ◦ What the risks are? ◦ What tools are available? ◦ Unwanted uses of personal data.
Advanced Surveillance Technology Advance technology: ◦ Thermal imaging devices ◦ Surveillance cameras ◦ Face recognition Example: ◦ Police can use thermal imaging devices from outside a house to detect patterns of heat being generated from inside to find a marijuana in the house. ◦ The police department of Tampa, Florida placed 36 security cameras in the town and connected them to a powerful computer loaded with face recognition software.
- Slides: 28