Trusted Computing and the Trusted Platform Module Bruce
Trusted Computing and the Trusted Platform Module Bruce Maggs (with some slides from Bryan Parno)
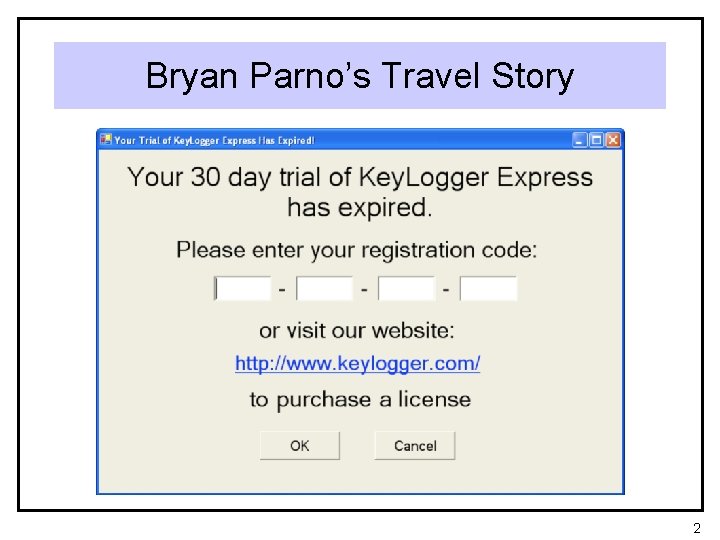
Bryan Parno’s Travel Story 2
Attestation • How can we know that a system that we would like to use has not been compromised? 3
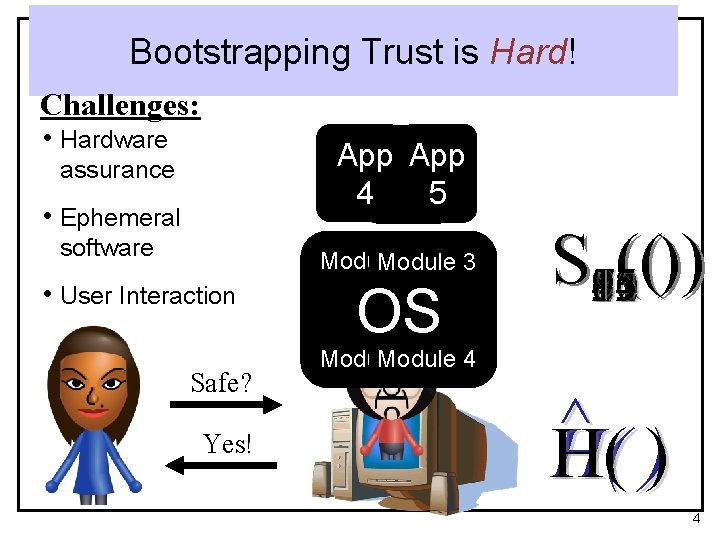
Bootstrapping Trust is Hard! Challenges: • Hardware App App 14 3 N 5 2 assurance • Ephemeral software Module 1 Module 3 • User Interaction Safe? Yes! OS S 15 ( ( ) ) 1 2 3 4 5 6 7 8 9 10 11 12 13 14 Module 2 4 ^ H( ) 4
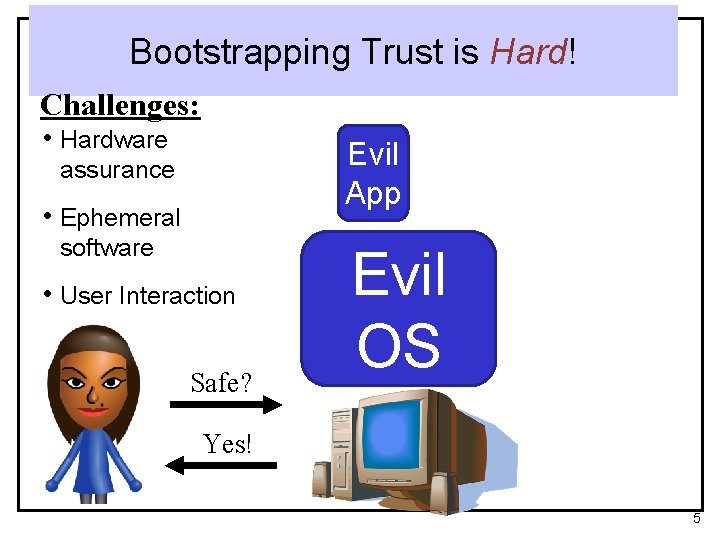
Bootstrapping Trust is Hard! Challenges: • Hardware Evil App assurance • Ephemeral software • User Interaction Safe? Evil OS Yes! 5
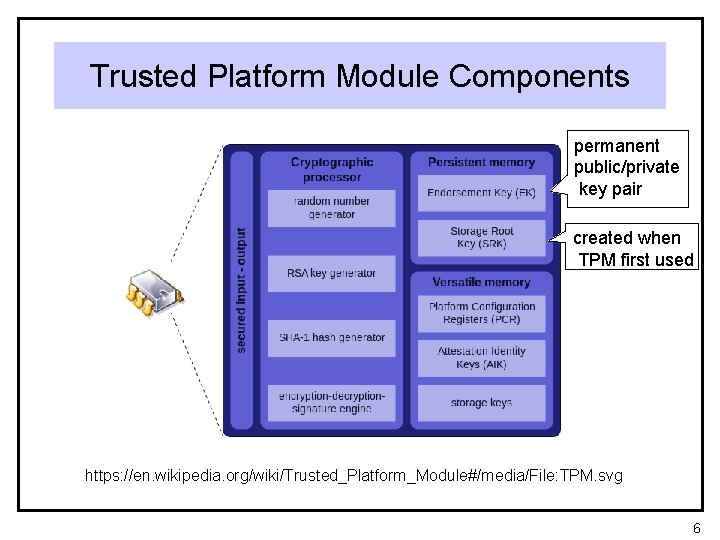
Trusted Platform Module Components permanent public/private key pair created when TPM first used https: //en. wikipedia. org/wiki/Trusted_Platform_Module#/media/File: TPM. svg 6
TPM Chip Often found in business-class laptops https: //en. wikipedia. org/wiki/Trusted_Platform_Module#/media/File: TPM_Asus. jpg 7

Caveat • The TPM is not 100% tamper proof! • Safe use requires physical security • In 2010 Christopher Tarnovsky extracted all keys from an Infineon TPM chip by • soaking the chip in acid to remove plastic • removing RF-shield wire mesh • probing with an extremely small needle 8
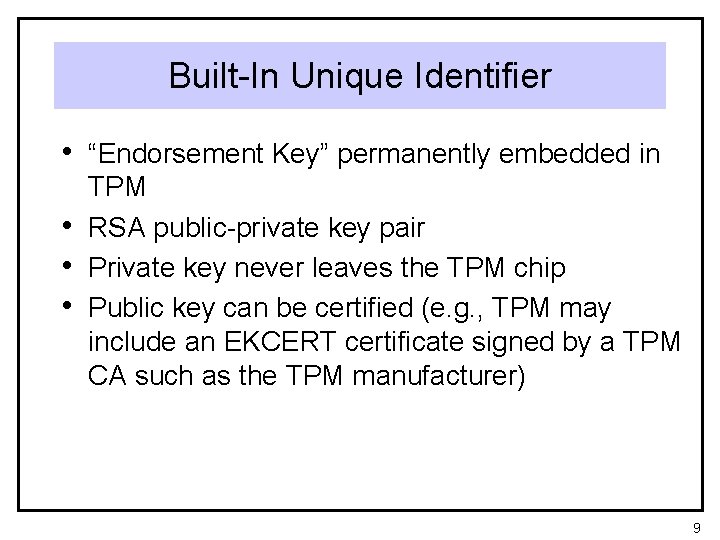
Built-In Unique Identifier • “Endorsement Key” permanently embedded in • • • TPM RSA public-private key pair Private key never leaves the TPM chip Public key can be certified (e. g. , TPM may include an EKCERT certificate signed by a TPM CA such as the TPM manufacturer) 9

Storage Root Key • Master “storage root key” (SRK) created • • when TPM first used Can be changed by clearing the TPM Protects TPM keys created by other applications 10
On-Chip Algorithms • • RSA key-pair generation RSA encryption/decryption RSA signing and signature checking Random number generation SHA-1 hashing Keyed-hash message authentication code (HMAC) (more on this later) NOT a crypto accelerator 11
Platform Configuration Registers (PCRs) • A TPM contains several 20 -byte PCRs • A PCR is initialized to zero at power on. • The only operation allowed on a PCR is to extend it: • val[PCR] = SHA 1(val[PCR] || newval) • At boot time, a TPM-enabled PC takes a series of measurements and stores them in PCRs (more on this later) 12
HMAC • Hash with two inputs: a key and a block • • of data Typically key is randomly generated and secret Key can be used (for example) to guarantee that the hash was freshly created 13

How HMAC can be used • TPM can hash contents of all storage on computer, or storage in certain places • Disks • Memory • Registers in the CPU • User can choose to execute only from known safe states 14

Applications • Protecting sensitive stored information • • from modification Trusted boot Attestation 15
![TPM-Based Attestation Example [Gasser et al. ‘ 89], [Arbaugh et al. ‘ 97], [Sailer TPM-Based Attestation Example [Gasser et al. ‘ 89], [Arbaugh et al. ‘ 97], [Sailer](http://slidetodoc.com/presentation_image_h2/d98a2822619989ac96fc784ad420af84/image-16.jpg)
TPM-Based Attestation Example [Gasser et al. ‘ 89], [Arbaugh et al. ‘ 97], [Sailer et al. ‘ 04], [Marchesini et al. ‘ 04] Module BIOS OS Bootloader App App PCRs TPM KPriv 16
![Establishing Trust via a TPM [Gasser et al. ‘ 89], [Arbaugh et al. ‘ Establishing Trust via a TPM [Gasser et al. ‘ 89], [Arbaugh et al. ‘](http://slidetodoc.com/presentation_image_h2/d98a2822619989ac96fc784ad420af84/image-17.jpg)
Establishing Trust via a TPM [Gasser et al. ‘ 89], [Arbaugh et al. ‘ 97], [Sailer et al. ‘ 04], [Marchesini et al. ‘ 04] random # Module Accurate! Module K Module Bootloader Sign ( Module BIOS Bootloader Kpriv Guarantees actual TPM logs OS OS Pubp BIOS Bootloader BIOS Module AA p p. A ppp OS random # AA p p. A ppp p ) Guarantees freshness App App Guarantees real TPM PCRs TPM KPriv 17

Static Chain of Trust at Power-On • PCRs set to default values • Hardware instructs TPM to measure • • Authenticated Code Module (ACM) provided by manufacturer on motherboard, extend PCR 0 Processor runs ACM to measure BIOS, i. e. , software instructs TPM to extend PCR 0 with BIOS code extends PCR 4 with IPL (initial program loader) from master boot record 18
Dynamic Chain of Trust • OS invokes special security instruction, resetting • • • PCRs 17 -22 to default values Hardware measures SINIT ACM, also provided by hardware manufacturer SINIT ACM measures OS startup code (Measured Launch Environment MLE), extends PCR 18 Before running MLE, SINIT verifies that MLE and PCRs 0 -7 have known good values MLE measures OS, extends PCRs 19 -20 Before running OS, MLE compares PCRs 19 -20 to known good values 19
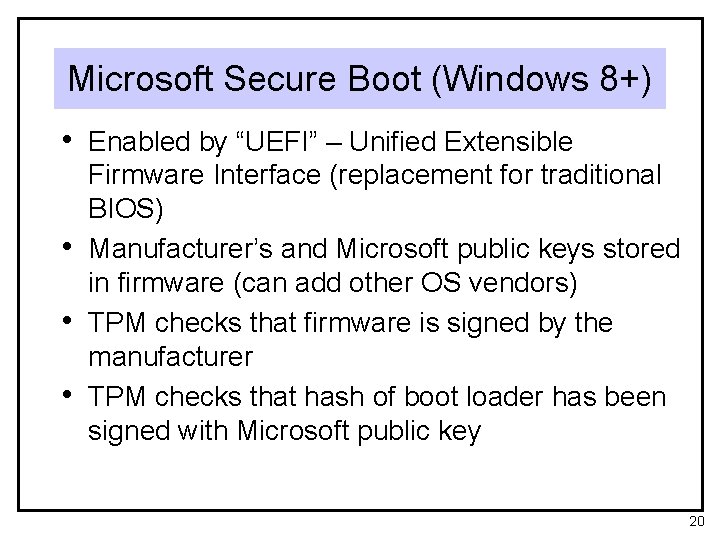
Microsoft Secure Boot (Windows 8+) • Enabled by “UEFI” – Unified Extensible • • • Firmware Interface (replacement for traditional BIOS) Manufacturer’s and Microsoft public keys stored in firmware (can add other OS vendors) TPM checks that firmware is signed by the manufacturer TPM checks that hash of boot loader has been signed with Microsoft public key 20
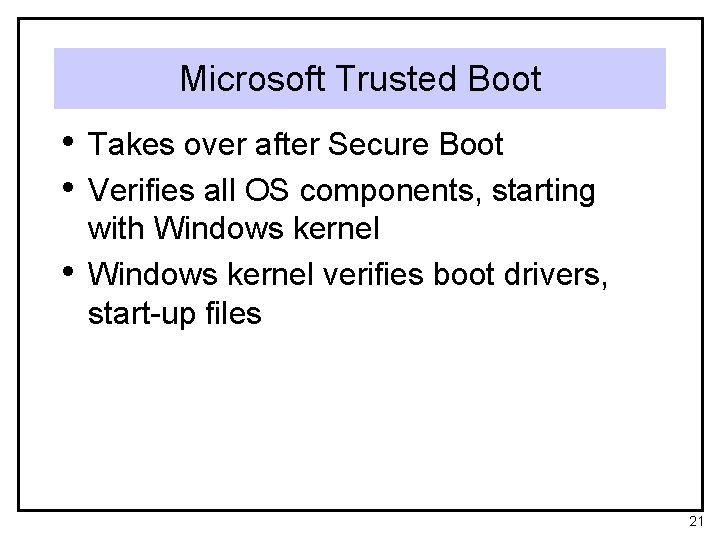
Microsoft Trusted Boot • Takes over after Secure Boot • Verifies all OS components, starting • with Windows kernel verifies boot drivers, start-up files 21
Microsoft Measured Boot • TPM signs measured boot log file • Remote attestation possible by transmitting signed boot log 22
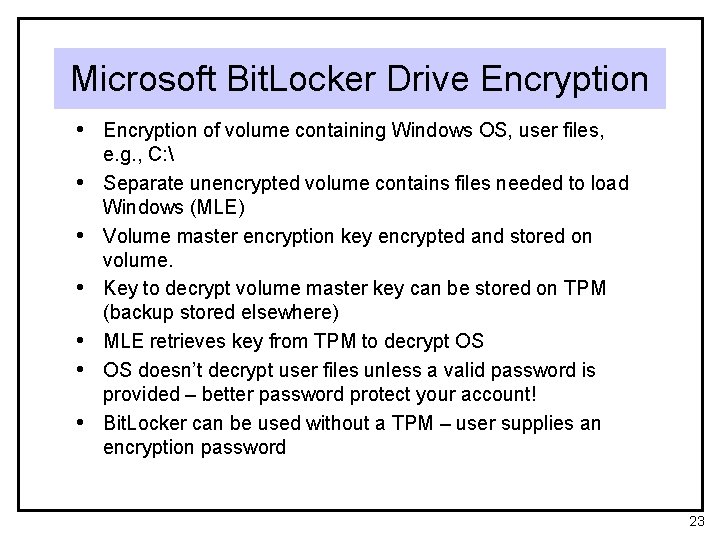
Microsoft Bit. Locker Drive Encryption • Encryption of volume containing Windows OS, user files, • • • e. g. , C: Separate unencrypted volume contains files needed to load Windows (MLE) Volume master encryption key encrypted and stored on volume. Key to decrypt volume master key can be stored on TPM (backup stored elsewhere) MLE retrieves key from TPM to decrypt OS OS doesn’t decrypt user files unless a valid password is provided – better password protect your account! Bit. Locker can be used without a TPM – user supplies an encryption password 23
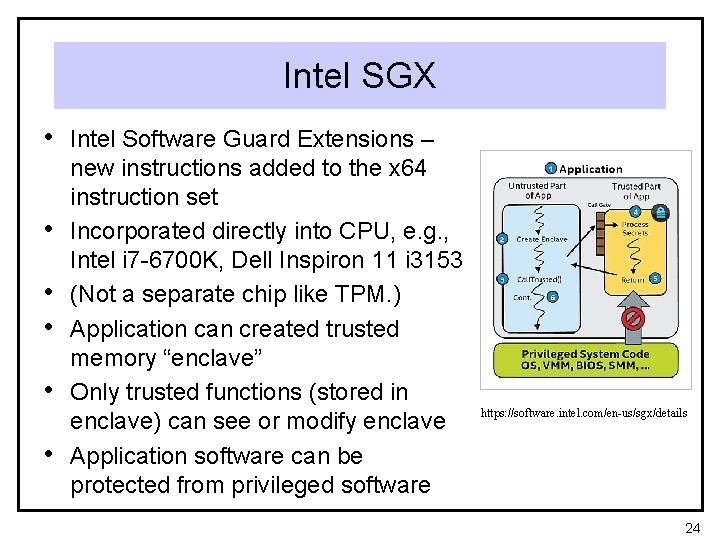
Intel SGX • Intel Software Guard Extensions – • • • new instructions added to the x 64 instruction set Incorporated directly into CPU, e. g. , Intel i 7 -6700 K, Dell Inspiron 11 i 3153 (Not a separate chip like TPM. ) Application can created trusted memory “enclave” Only trusted functions (stored in enclave) can see or modify enclave Application software can be protected from privileged software https: //software. intel. com/en-us/sgx/details 24
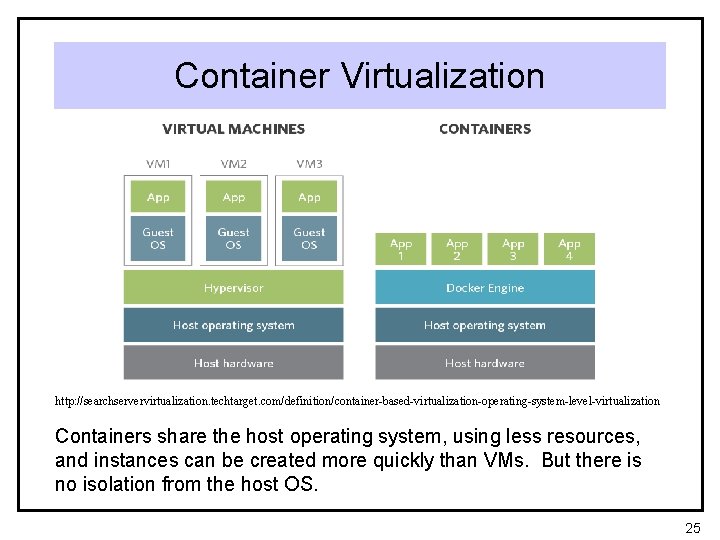
Container Virtualization http: //searchservervirtualization. techtarget. com/definition/container-based-virtualization-operating-system-level-virtualization Containers share the host operating system, using less resources, and instances can be created more quickly than VMs. But there is no isolation from the host OS. 25
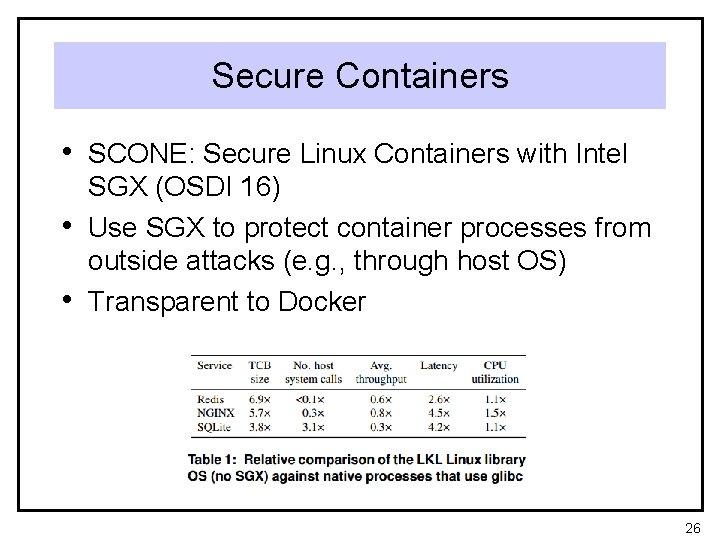
Secure Containers • SCONE: Secure Linux Containers with Intel • • SGX (OSDI 16) Use SGX to protect container processes from outside attacks (e. g. , through host OS) Transparent to Docker 26
- Slides: 26