Trust and the Public Key Infrastructure PKI Sangyoon
Trust and the Public Key Infrastructure (PKI) Sangyoon Oh Florida State University Computer Security Projects GS 5891 -01 Spring 2001 4/20/2001 Computer Security
Outlines n n n Security on Current Internet What is PKI? Structures and Models Weaknesses and Right PKI Trustworthiness in open network 4/20/2001 Computer Security 2
Security on Internet n n Internet is cloud of connection User is responsible for everything E-commerce and B 2 B grow rapidly Needs framework to exchange data and money securely and privately 4/20/2001 Computer Security 3
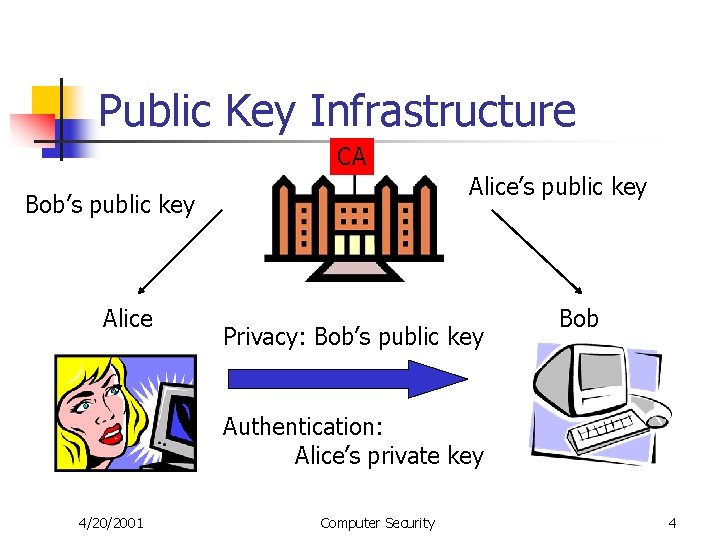
Public Key Infrastructure CA Alice’s public key Bob’s public key Alice Privacy: Bob’s public key Bob Authentication: Alice’s private key 4/20/2001 Computer Security 4
Structures and Models n n n Hierarchical structure: X. 509 Pretty Good Privacy Virtual Private Network n n n 4/20/2001 Secure connection over the phone line. Network service provider & Hardware vender Authentication, Encryption, Tunneling, Access Control Computer Security 5
Weakness n n Security is as strong as weakest link User computer is not safe: Private key Hacker use Root certificate RA (certificate content) - CA link is very weak. 4/20/2001 Computer Security 6
Right PKI n Choose the right structure n n B 2 B, B need Hierarchical structure: X. 509 Right Implementation n n 4/20/2001 Stochastic, security policy management prevent reliability failure and low level penatration Right Choice of PKI Structure prevent malicious attack Computer Security 7
Valuation of Trust (Thomas Beth, Malte Borcherding, Birgit Klein) n n n Direct and Recommended Trust Value Deriving Trust Relationships Combination of Trust Values Use: entrust task worth 100 unit, risk 49 unit. 4/20/2001 Computer Security 8
Secure communication in an unknown network (M. Burmester and Y. Desmedt) n n Structure of trust graph is not known except attacker Using query flood, get neighbor list. Label the vertexes Get a good approximation of the trust graph 4/20/2001 Computer Security 9
Reference n n n Which PKI (Public Key Infrastructure) is the right one? -Carlisle Adams, Mike Burmester, Yvo Desmedt (2000) Valuation of Trust in Open Networks -- Thomas Beth, Malte Borcherding, Birgit Klein (1994) Secure communication in an unknownnetwork using certificates. -- M. Burmester and Y. Desmedt. (1999) Ten Risks of PKI: What you’re not being told about Public Key Infrastructure. -- Carl Ellison, Bruce Schneier (2000) Security in Computing, 2 nd -- Charles P. Pfleeger 4/20/2001 Computer Security 10
Reference Con’t n n A Method for Obtaining Digital Signatures and Public-Key Cryptosystems. -- Rivest, R. L. , Shamir, A. , and Adleman, L. (1978). SPKI/SDSI 2. 0 A Simple Distributed Security Infrastructure -- Ronald L. Rivest (1997) Virtual Private Networks -- Cris Banson (1999) What is a VPN? -- Paul Ferguson, Geoff Huston (1998) 4/20/2001 Computer Security 11
- Slides: 11