True Random Number Generators Secure in a Changing
True Random Number Generators Secure in a Changing Environment Boaz Barak, Ronen Shaltiel, Eran Tromer Weizmann Institute, Israel
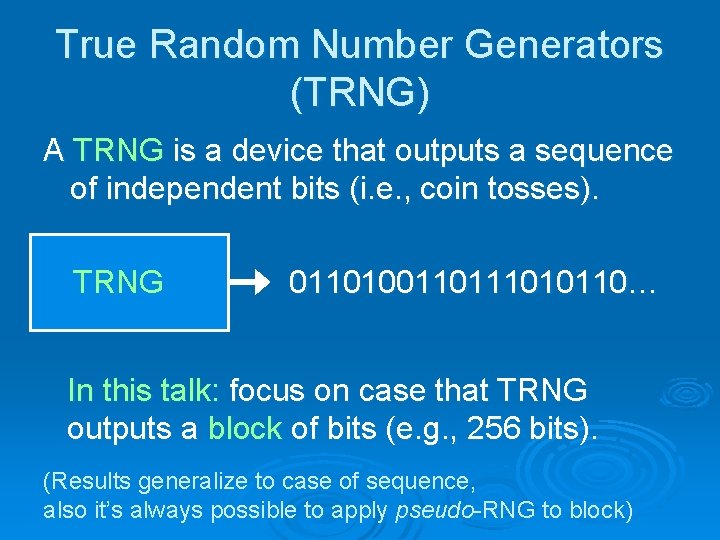
True Random Number Generators (TRNG) A TRNG is a device that outputs a sequence of independent bits (i. e. , coin tosses). TRNG 011010011010110… In this talk: focus on case that TRNG outputs a block of bits (e. g. , 256 bits). (Results generalize to case of sequence, also it’s always possible to apply pseudo-RNG to block)
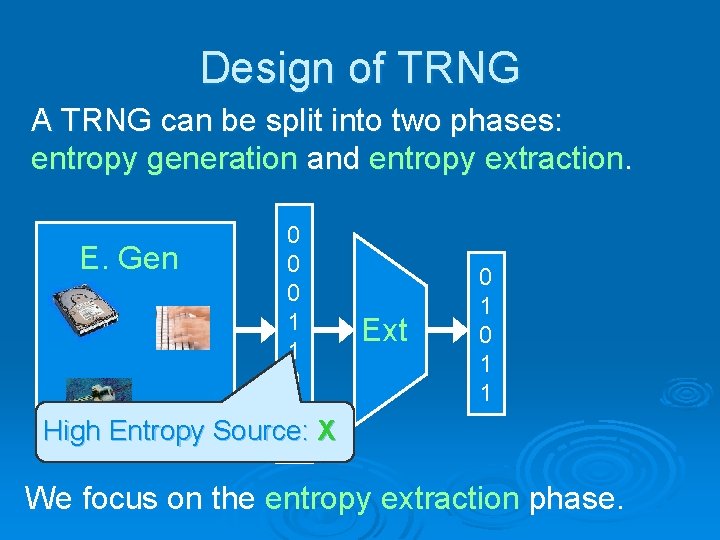
Design of TRNG A TRNG can be split into two phases: entropy generation and entropy extraction. 0 E. Gen 0 0 1 1 0 0 High Entropy Source: 1 X Ext 0 1 1 We focus on the entropy extraction phase.
Previous Constructions of Entropy Extraction Phase Ø Tailor-made design for a “nice” source X (Intel RNG, IBM-4758, … ) Ø Use cryptographic hash functions (PGP, Linux, Apache… )
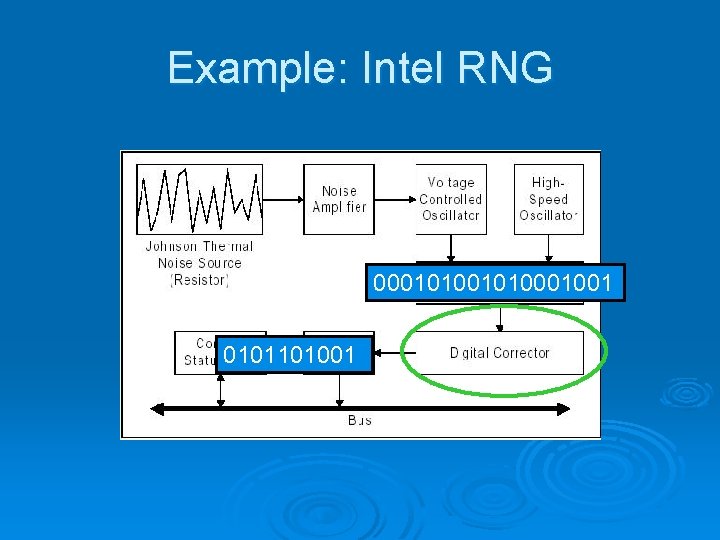
Example: Intel RNG 0001010001001 0101101001
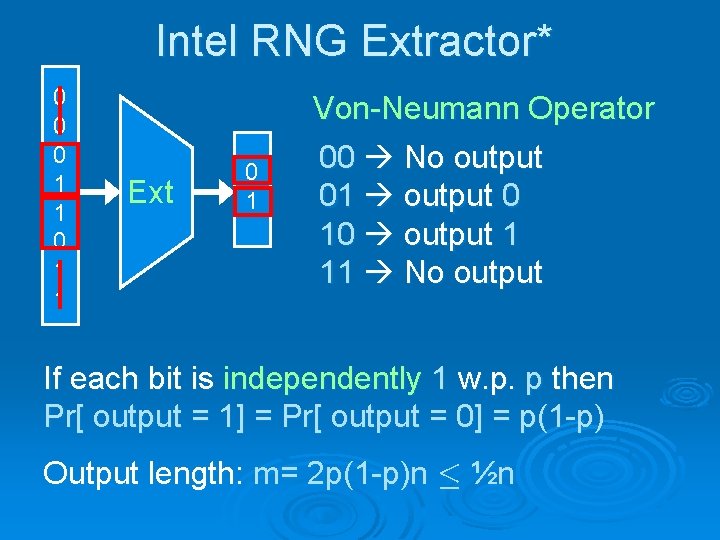
Intel RNG Extractor* 0 0 0 1 1 Ext 0 1 Von-Neumann Operator 00 No output 01 output 0 10 output 1 11 No output If each bit is independently 1 w. p. p then Pr[ output = 1] = Pr[ output = 0] = p(1 -p) Output length: m= 2 p(1 -p)n · ½n
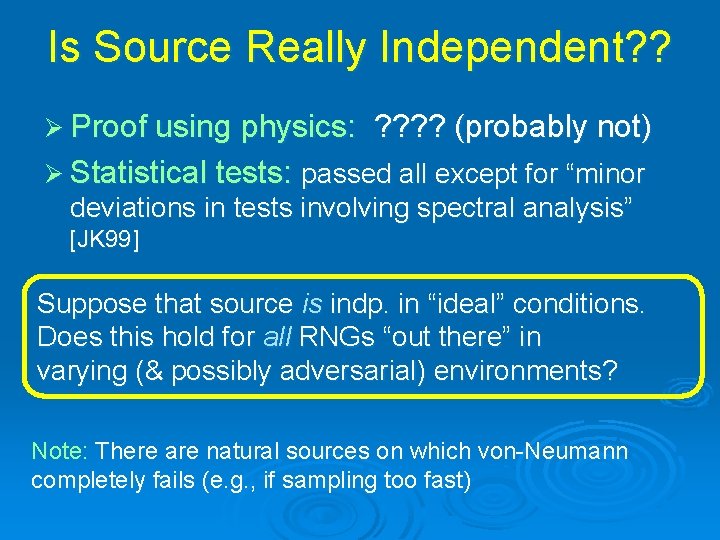
Is Source Really Independent? ? Ø Proof using physics: ? ? (probably not) Ø Statistical tests: passed all except for “minor deviations in tests involving spectral analysis” [JK 99] Suppose that source is indp. in “ideal” conditions. Does this hold for all RNGs “out there” in varying (& possibly adversarial) environments? Note: There are natural sources on which von-Neumann completely fails (e. g. , if sampling too fast)
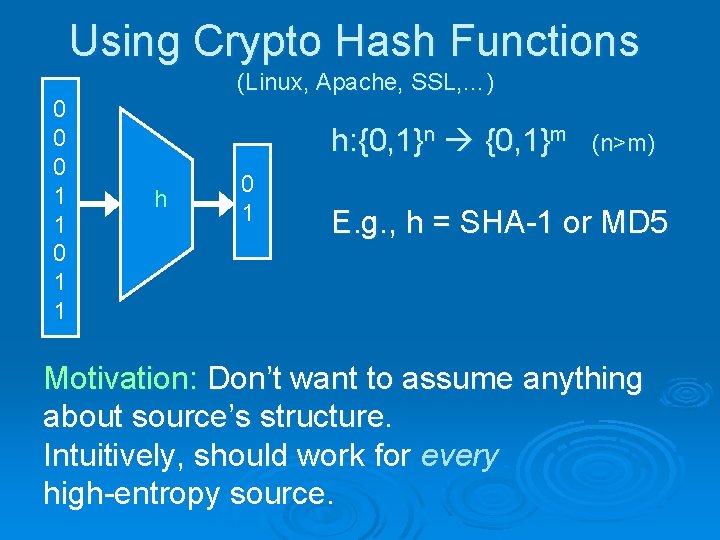
Using Crypto Hash Functions 0 0 0 1 1 (Linux, Apache, SSL, …) h: {0, 1}n {0, 1}m h 0 1 (n>m) E. g. , h = SHA-1 or MD 5 Motivation: Don’t want to assume anything about source’s structure. Intuitively, should work for every high-entropy source.
Problems w/ using Crypto-hash Ø Relying on unproven properties of hash functions to obtain supposedly true random bits. Ø Assumptions are not even explicitly Not an explicit goal of either hash designers or cryptanalysts (In contrast to collision resistance) stated.
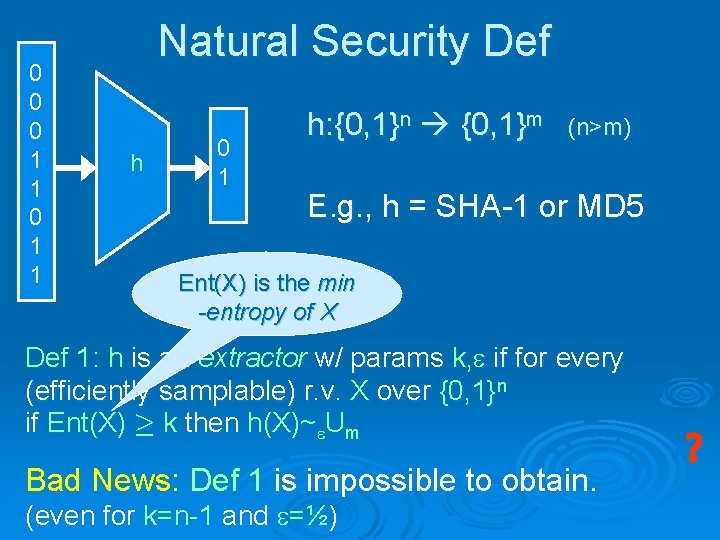
0 0 0 1 1 Natural Security Def h 0 1 h: {0, 1}n {0, 1}m (n>m) E. g. , h = SHA-1 or MD 5 Ent(X) is the min -entropy of X Def 1: h is an extractor w/ params k, if for every (efficiently samplable) r. v. X over {0, 1}n if Ent(X) ¸ k then h(X)~ Um Bad News: Def 1 is impossible to obtain. (even for k=n-1 and =½) ?
![Thm [NZ]: 8 efficiently computable h , 9 efficiently sampleable X s. t. 1) Thm [NZ]: 8 efficiently computable h , 9 efficiently sampleable X s. t. 1)](http://slidetodoc.com/presentation_image_h/94bb8bf266be5bddcf36ac4467d9f106/image-11.jpg)
Thm [NZ]: 8 efficiently computable h , 9 efficiently sampleable X s. t. 1) Ent(X) ¸ n-1 2) The first bit of h(X) is fixed. Proof: W. l. o. g Pr[h 1(Un)=0] ¸ ½. Sample X as follows: 1. Let x {0, 1}n 2. If h 1(x)=0, output x. Otherwise, goto 1 X is uniform over h 1 -1(0) – a set of size at least 2 n/2.
Our Contribution Ø We give an explicit model and definition for the entropy extraction problem. Ø We prove unconditionally that a known simple construction satisfies the definition. Ø We implemented and tested the above solution.
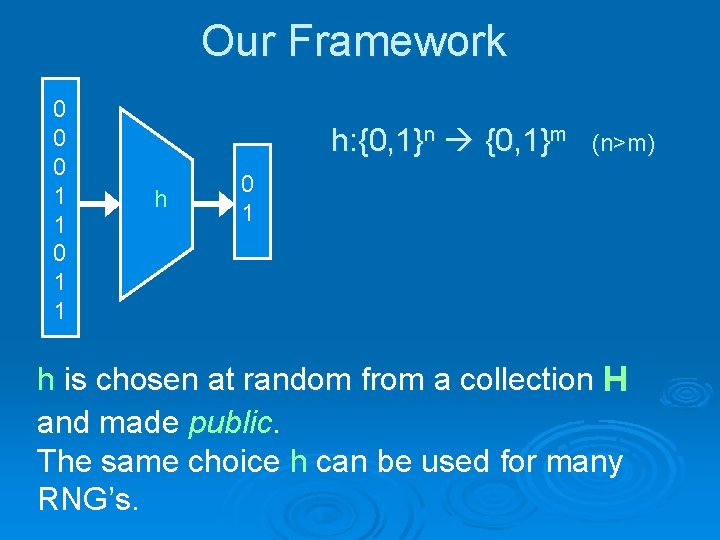
Our Framework 0 0 0 1 1 h: {0, 1}n {0, 1}m h (n>m) 0 1 h is chosen at random from a collection H and made public. The same choice h can be used for many RNG’s.
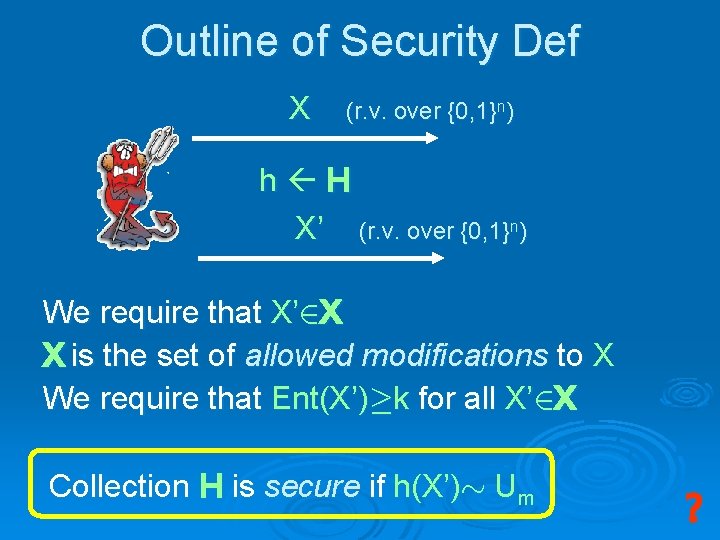
Outline of Security Def X (r. v. over {0, 1}n) h H X’ (r. v. over {0, 1}n) We require that X’ 2 X X is the set of allowed modifications to X We require that Ent(X’)¸k for all X’ 2 X Collection H is secure if h(X’)» Um ?
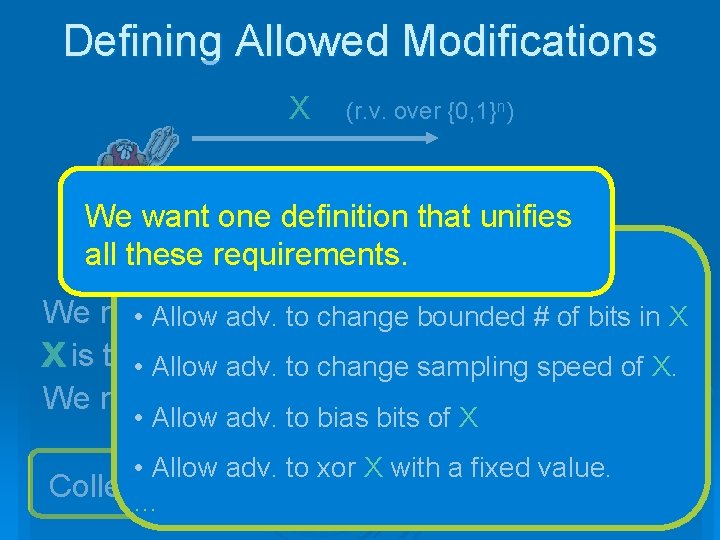
Defining Allowed Modifications X (r. v. over {0, 1}n) h H We want one definition that{0, 1} unifies n) X’ (r. v. over all these requirements. Possible choices: We require X • Allowthat adv. X’to 2 change bounded # of bits in X X is the • Allow set ofadv. allowed modifications to X of X. to change sampling speed We require that Ent(X’)¸k for all X’ 2 X • Allow adv. to bias bits of X • Allow adv. to xor X with a fixed value. Collection H is secure if h(X)» Um …
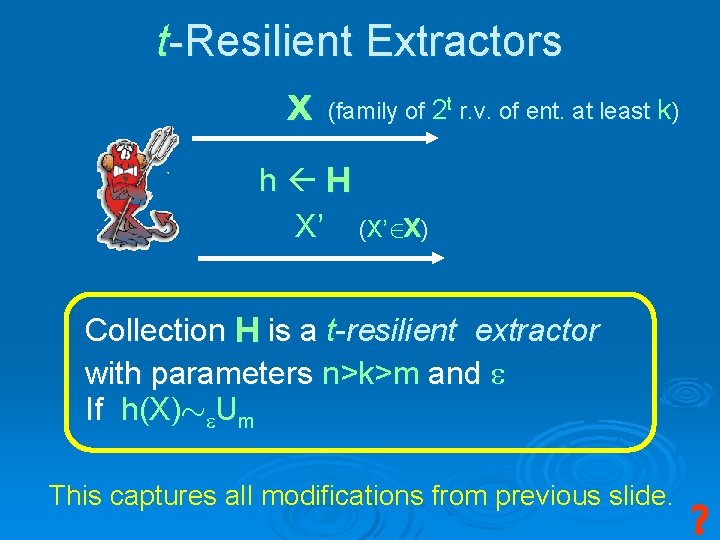
t-Resilient Extractors X (family of 2 t r. v. of ent. at least k) h H X’ (X’ 2 X) Collection H is a t-resilient extractor with parameters n>k>m and If h(X)» Um This captures all modifications from previous slide. ?
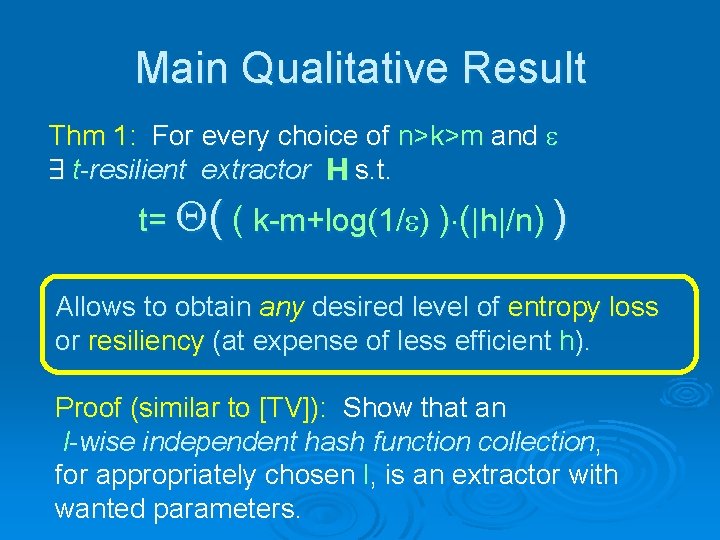
Main Qualitative Result Thm 1: For every choice of n>k>m and 9 t-resilient extractor H s. t. t= ( ( k-m+log(1/ ) )¢(|h|/n) ) Allows to obtain any desired level of entropy loss or resiliency (at expense of less efficient h). Proof (similar to [TV]): Show that an l-wise independent hash function collection, for appropriately chosen l, is an extractor with wanted parameters.
![Better Efficiency – Pairwise Indp. Hash Functions [CW] Thm: For every choice of n>k>m Better Efficiency – Pairwise Indp. Hash Functions [CW] Thm: For every choice of n>k>m](http://slidetodoc.com/presentation_image_h/94bb8bf266be5bddcf36ac4467d9f106/image-18.jpg)
Better Efficiency – Pairwise Indp. Hash Functions [CW] Thm: For every choice of n>k>m and if H: {0, 1}n {0, 1}m is a pairwise indp. collection then it is a t-resilient extractor where t= (k-m)/2 - 2 log(1/ ) - 1 H is pairwise indp. if for every distinct x 1, x 22{0, 1}n, if h H then the r. v. h(x 1) and h(x 2) are uniform and indp. random variables.
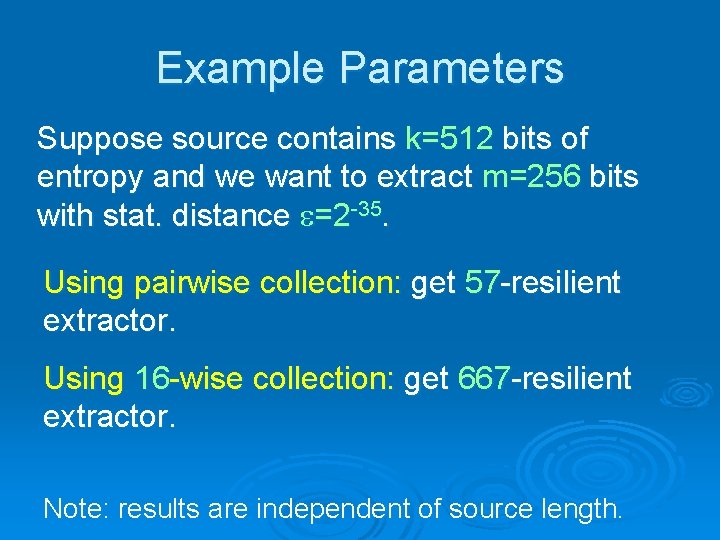
Example Parameters Suppose source contains k=512 bits of entropy and we want to extract m=256 bits with stat. distance =2 -35. Using pairwise collection: get 57 -resilient extractor. Using 16 -wise collection: get 667 -resilient extractor. Note: results are independent of source length.
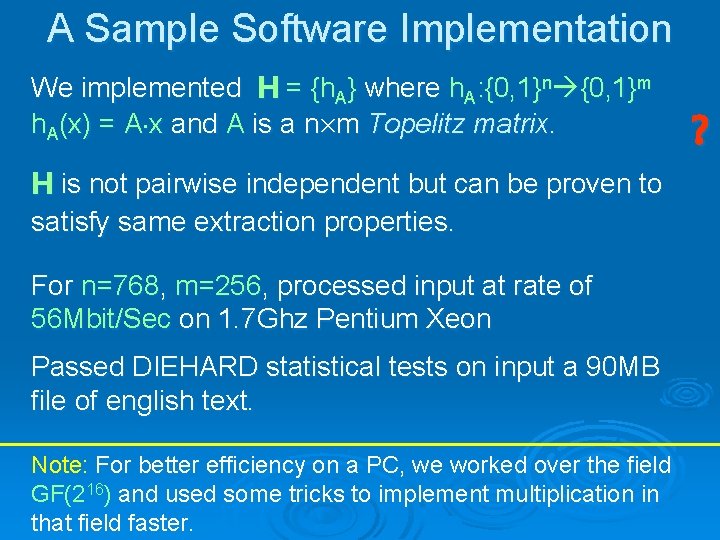
A Sample Software Implementation We implemented H = {h. A} where h. A: {0, 1}n {0, 1}m h. A(x) = A¢x and A is a n£m Topelitz matrix. H is not pairwise independent but can be proven to satisfy same extraction properties. For n=768, m=256, processed input at rate of 56 Mbit/Sec on 1. 7 Ghz Pentium Xeon Passed DIEHARD statistical tests on input a 90 MB file of english text. Note: For better efficiency on a PC, we worked over the field GF(216) and used some tricks to implement multiplication in that field faster. ?
- Slides: 20