True Global Reach Single Source Compliance Security Compliance

True Global Reach. Single Source. Compliance. Security, Compliance, Value Recovery Global Reach, Source Security. Value. Single Recovery. 2016 -07 -21
”Kärt Barn har många namn” Dataserv AB TES-Amm TES Total Environmental Solution AB 2

Facts & History
About TES 4 • End to end IT lifecycle partner with global footprint • Compliant organization with long standing investment in meeting customer need locally, regionally and globally • Majority owned and backed by Navis Capital Partners with > US$6 Billion under mgt. • Over 1600 employees worldwide • • 2018 Group Revenues of over US$ 230 mil / EBITDA of US$ 20 mil Ability to invest in process, plant, systems and people • 25+ years experience in WEEE in Europe • Own WEEE scheme activities in UK, Germany, China, Australia & Italy since 2006 • 10+ years of providing B 2 B and B 2 C WEEE/UEEE programs in EU / APJ • In-house IT-system development capability
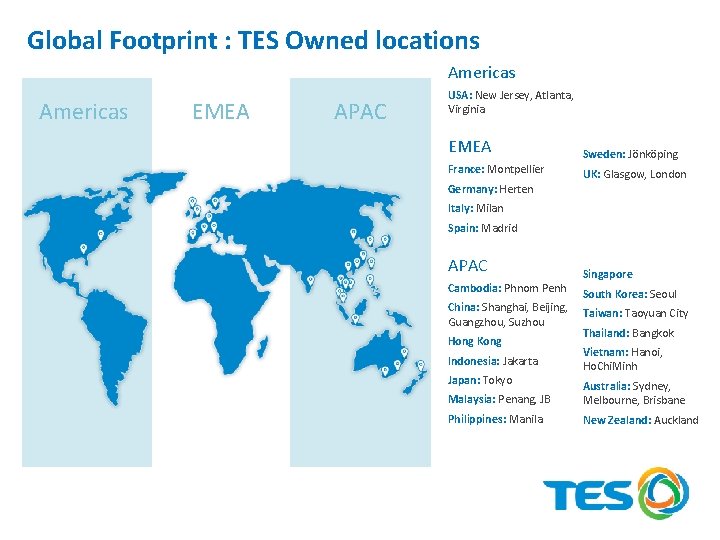
Global Footprint : TES Owned locations Americas EMEA APAC USA: New Jersey, Atlanta, Virginia EMEA Sweden: Jönköping France: Montpellier UK: Glasgow, London Germany: Herten Italy: Milan Spain: Madrid APAC Cambodia: Phnom Penh China: Shanghai, Beijing, Guangzhou, Suzhou Hong Kong Indonesia: Jakarta Japan: Tokyo Singapore South Korea: Seoul Taiwan: Taoyuan City Thailand: Bangkok Vietnam: Hanoi, Ho. Chi. Minh Malaysia: Penang, JB Australia: Sydney, Melbourne, Brisbane Philippines: Manila New Zealand: Auckland

Global Footprint: TES Partner locations Americas EMEA APAC Americas Argentina: Buenos Aires Costa Rica: San José Bolivia: Sucre Chile: Santiago Brazil: Sao Paulo Mexico: Mexico City Canada: Toronto Paraguay: Asunción Colombia: Bogota Uruguay: Montevideo EMEA Bulgaria: Sofia Croatia: Zagreb Cyprus: Nicosia Egypt: Cairo Greece: Athens Israel: Jerusalem Lithuania: Vilnius Poland: Warsaw Romania: Bucharest Serbia: Belgrade Slovakia: Bratislava Turkey: Ankara UAE: Abu Dhabi South Africa: Johannesburg APAC Laos: Vientiane Russia: Moscow Myanmar: Yangon Sri Lanka: Colombo India: Delhi, Bangalore, Chennai

Portfolio

Customer requirements Business requirements: Services & Solutions: o o o o o Consulting Compliance Security Global Presence Value Recovery Reporting Clear Service Agreement (SOW, SLA, etc. ) Standardized, but flexible solutions System supported processes Managed Deployment Asset Recovery Onsite Data Destruction Return Solutions Part Management Environmental Compliant Recycling Data Sanitization Employee sales Take-Back / Trade-in Solutions How does your set-up look like?
”Kär tjänst har många namn” ITAD It Asset Disposal ARS Asset Recovery Services 9
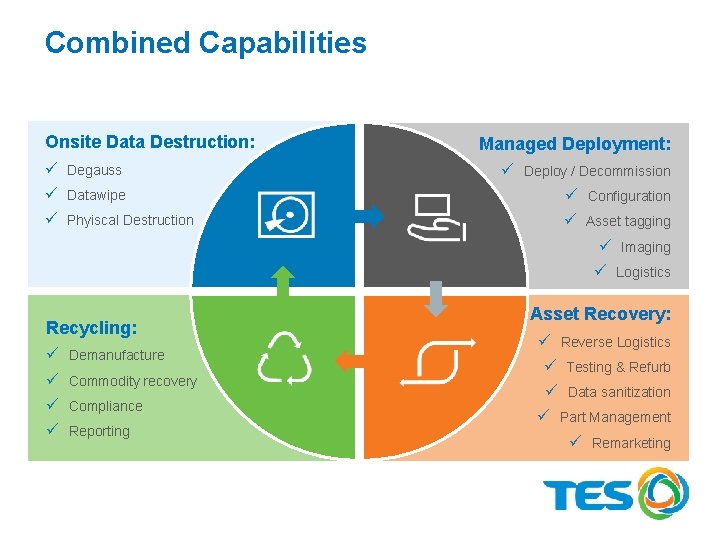
Combined Capabilities Onsite Data Destruction: ü Degauss ü Datawipe ü Phyiscal Destruction Recycling: ü Demanufacture ü Commodity recovery ü Compliance ü Reporting Managed Deployment: ü Deploy / Decommission ü Configuration ü Asset tagging ü Imaging ü Logistics Asset Recovery: ü Reverse Logistics ü Testing & Refurb ü Data sanitization ü Part Management ü Remarketing

Environmental & Legal Compliance

Global Compliance - Certifications Country ISO 14001 OHSAS 18001 ISO 9001 R 2 ISO 27001 France ● ● ● Germany ● ● Italy ● ● ● Spain ● ● ● South Africa ● ● ● Sweden ● ● ● UK ● ● USA ● Australia ISO 14001 OHSAS 18001 ISO 9001 R 2 Hong Kong ● ● ● India ● ● ● Indonesia ● ● Japan ● ● ● Malaysia ● ● ● Philippines ● ● ● Singapore ● ● ● South Korea ● ● ● ● Taiwan ● ● ● New Zealand ● ● Thailand ● ● ● China ● ● Vietnam ● ● ● Country ● ISO 27001 ● ● ●

Global Compliance

Security

Security, what comes to your mind? GDPR Employee Location Data security IT security Theft Privcacy 15

Security Management Global Security Team The Global Security Team is based in Singapore, and is responsible for maintaining high standards of security at all our facilities. The Chief Security Officer is part of the Executive Committee, and reports directly to the CEO. ISO 28000 TES has adopted ISO 28000: 2007 Security Management System for the Supply Chain. This provides a consistent framework for security management across the company. Our HQ in Singapore has received ISO 28000 certification, and the company is in the process of implementing this management system across all facilities globally. Security Risk Management The Global Security Team maintains an up-to-date security risk assessment of our operations. We encourage our clients to share information on threat and risk to make sure the security control measures in place are adequate. Our risk management practices are aligned with ISO 31000 Risk Management and HB 167 Security Risk Management.
Physical security TAPA Facility Security Requirements Our Singapore facilities have been certified to TAPA FSR “A” level. All other facilities are being brought up to TAPA standards. Access Control & Intrusion Alarm Systems Access to the TES-AMM warehouses and processing buildings is restricted, and is managed by an access control system. Loading bay roller shutters are closed when loading bays are not in use. All fire escape doors and external windows are secured and alarmed. All of our facilities are protected during non-operational hours by intrusion alarm systems. Procedures are in place for alarm response. Video Surveillance All our facilities have CCTV cameras and we retain CCTV recordings in each country for the maximum amount of days that is legally possible.
Physical security Security screening and inspections Every individual entering our warehouses or processing areas is subject to search. Selected facilities have installed millimetre wave scanners or walk-through metal detectors. Photography No photography or video recording is permitted in any of our warehouses or processing areas. Lockers are provided for visitors to leave their phones or cameras. Visitor Management All visitors and contractors arriving at our facilities are required to register, and are issued with a visitor badge. Visitors are escorted at all times whilst in our facilities. Audits and Inspections Our Global Security Team manages a program of security audits and inspections for all of our facilities. We also invite our customers to audit our facilities at any time.

Managed Deployment Services

Managed Deployment Services • If your organisation is looking to deploy a new infrastructure or replace an aging one, TESAMM is able to offer a complete turn-key solution • Fully customisable to meet your specific requirements Efficient, dependable, hassle-free Solutioning Logistics Recovery Data Deletion Data Migration Planning & Execution Security Configuration Remarketing of used Devices Rollout Management Reverse Logistics Imaging Hardware Recycling Data Security
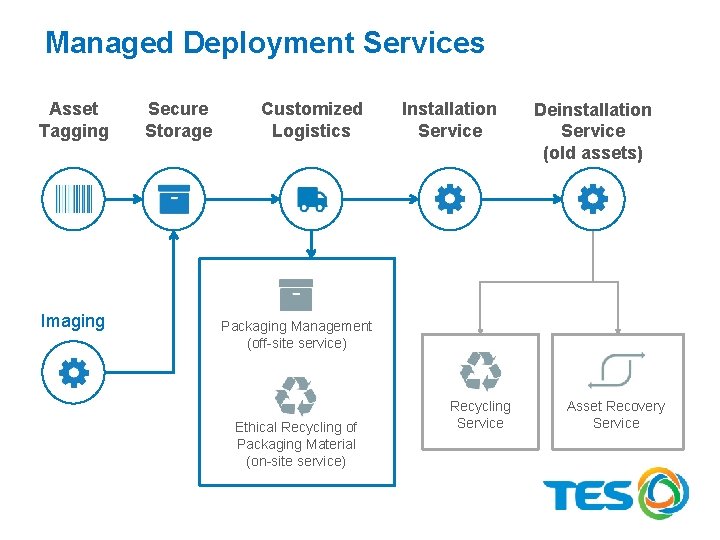
Managed Deployment Services Asset Tagging Imaging Secure Storage Customized Logistics Installation Service Deinstallation Service (old assets) Packaging Management (off-site service) Ethical Recycling of Packaging Material (on-site service) Recycling Service Asset Recovery Service

Asset Recovery Service

Asset Recovery Services • Asset Recovery describes the process of maximizing the value of unused or end of life assets • In the IT sector, ARS is usually achieved through an effective reuse or divestment of idle or redundant devices and parts Creation of Value
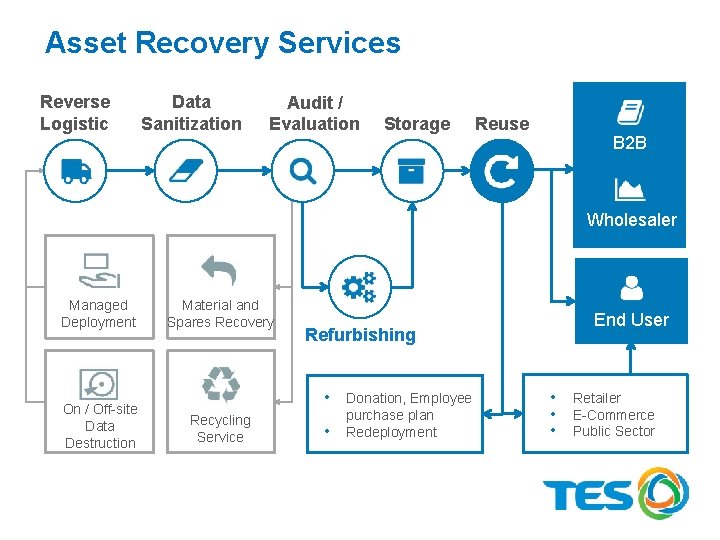
Asset Recovery Services Reverse Logistic s Data Sanitization Audit / Evaluation Storage Reuse B 2 B Wholesaler Managed Deployment On / Off-site Data Destruction Material and Spares Recovery Refurbishing • Donation, Employee Recycling Service • purchase plan Redeployment End User • Retailer • E-Commerce • Public Sector
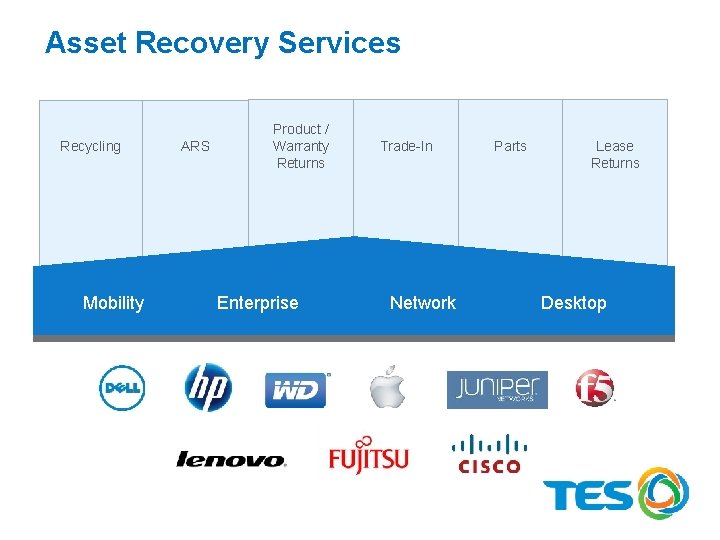
Asset Recovery Services Recycling Mobility ARS Product / Warranty Returns Enterprise Trade-In Network Parts Lease Returns Desktop

Environmental Compliant Recycling
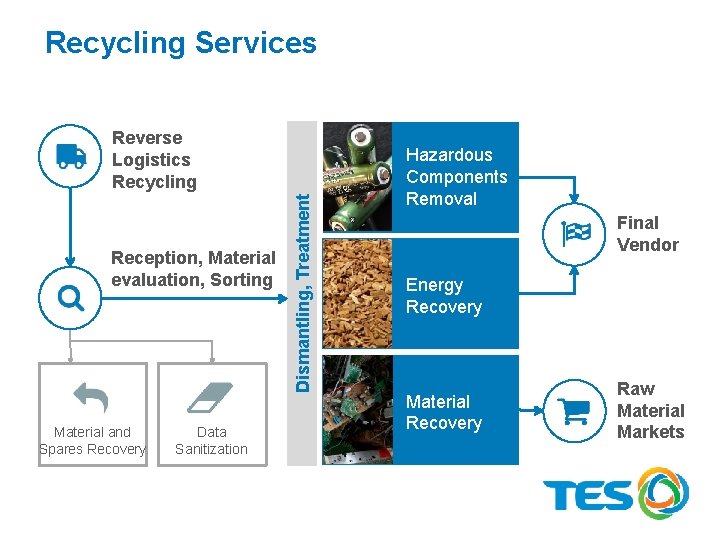
Recycling Services Reception, Material evaluation, Sorting Material and Spares Recovery Data Sanitization Dismantling, Treatment Reverse Logistics Recycling Hazardous Components Removal Final Vendor Energy Recovery Material Recovery Raw Material Markets
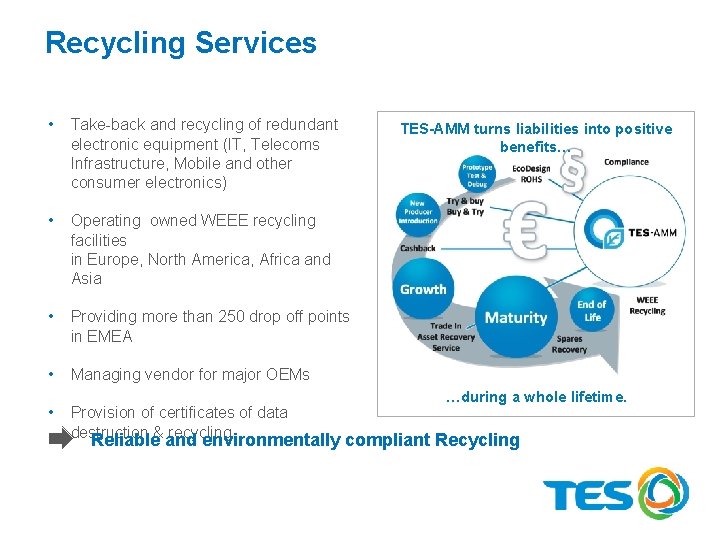
Recycling Services • Take-back and recycling of redundant electronic equipment (IT, Telecoms Infrastructure, Mobile and other consumer electronics) • Operating owned WEEE recycling facilities in Europe, North America, Africa and Asia • Providing more than 250 drop off points in EMEA • Managing vendor for major OEMs • Provision of certificates of data destruction & recycling TES-AMM turns liabilities into positive benefits… …during a whole lifetime. Reliable and environmentally compliant Recycling

Data Sanitization

Data Sanitization • Protection of sensitive data through the use of approved data wiping software • Complying with current local, regional and global standards • All data, including the OS, are deleted beyond retrieval • Data wiping solution is fully integrated into the IT infrastructure • Secure data destruction (degaussing) if needed • Factory reset of devices in case data wiping is not possible using data wiping software
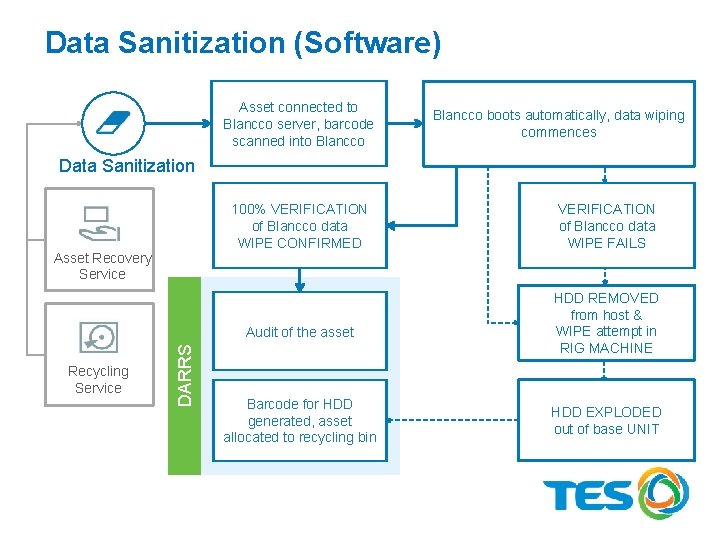
Data Sanitization (Software) Asset connected to Blancco server, barcode scanned into Blancco boots automatically, data wiping commences Data Sanitization 100% VERIFICATION of Blancco data WIPE CONFIRMED Asset Recovery Service Recycling Service DARRS Audit of the asset Barcode for HDD generated, asset allocated to recycling bin VERIFICATION of Blancco data WIPE FAILS HDD REMOVED from host & WIPE attempt in RIG MACHINE HDD EXPLODED out of base UNIT
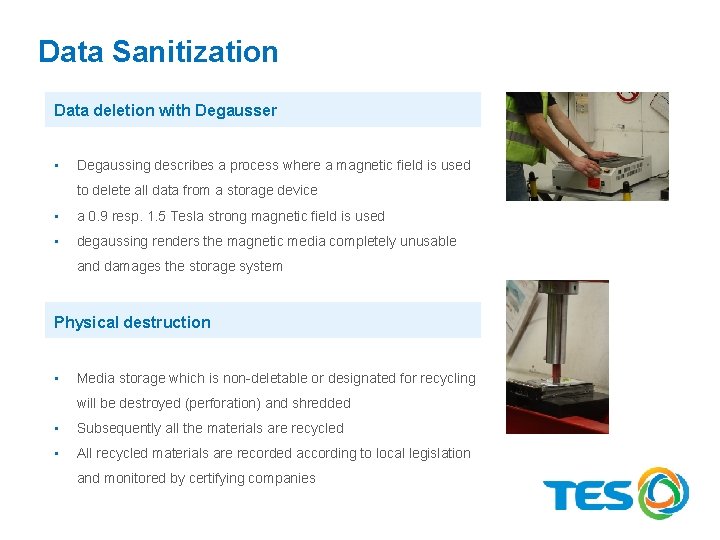
Data Sanitization Data deletion with Degausser • Degaussing describes a process where a magnetic field is used to delete all data from a storage device • a 0. 9 resp. 1. 5 Tesla strong magnetic field is used • degaussing renders the magnetic media completely unusable and damages the storage system Physical destruction • Media storage which is non-deletable or designated for recycling will be destroyed (perforation) and shredded • Subsequently all the materials are recycled • All recycled materials are recorded according to local legislation and monitored by certifying companies
Data Sanitization – current situation For the private sector as well as companies there are no mandatory regulations for data wipe available. The only known guidelines are e. g. ISO 27001 or occupational Group based ones which refer to the country specific guidelines (CESG, BSI and others). But these are only guidelines or recommendations (shall do) instead of mandatory regulations (must do). Ø There also no unique and mandatory classifications of security levels available. Ø In the following slides existing classifications, regulations and processes are displayed that are mainly in use.
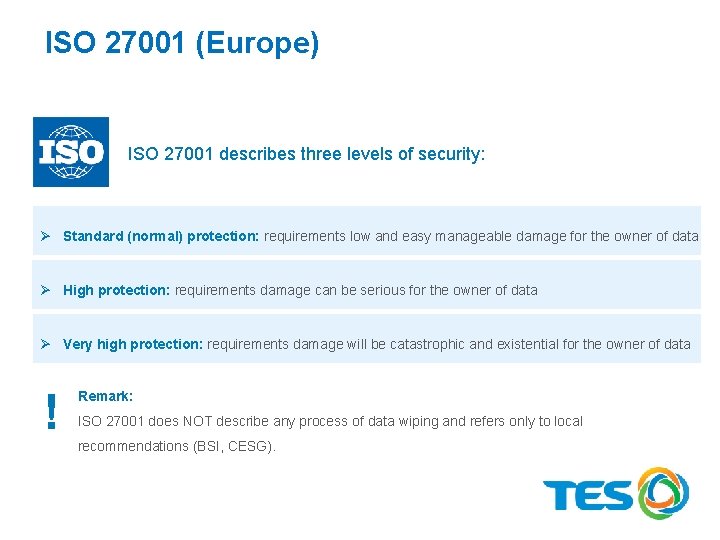
ISO 27001 (Europe) ISO 27001 describes three levels of security: Ø Standard (normal) protection: requirements low and easy manageable damage for the owner of data Ø High protection: requirements damage can be serious for the owner of data Ø Very high protection: requirements damage will be catastrophic and existential for the owner of data ! Remark: ISO 27001 does NOT describe any process of data wiping and refers only to local recommendations (BSI, CESG).

CESG (UK) The CESG classification originally was developed for the public sector. For the private and company sector CESG equalizes the same three levels as ISO 27001 to the public classification < OFFICIAL > which contains the legacy levels PROTECTED RESTRICTED CONFIDENTIAL (Planned as base for a Europe-wide and for NATO classification. ) BSI / Grundschutzkatalog (Germany) BIS only names normal (high) and higher security and relates to the ISO 27001 classifications.

Do. D (US) The Do. D (5220. 22) manual originally was developed for the military, later on adapted to the public sector. Do. D (5220. 22) is often used as worldwide accepted standard. The Do. D (5220. 22) manual contains the US (military) classifications: CORE SECRETS TOP SECRET CONFIDENTIAL RESTRICTED SECRET
NIST (US) The new NIST standard describes two different levels of data wipe: < CLEAR > < PURGE > The NIST 800 -88 r 1 (12. 2014) contains the most precise instructions and classification of assets which can contain data and how to wipe them.

Onsite Data Destruction
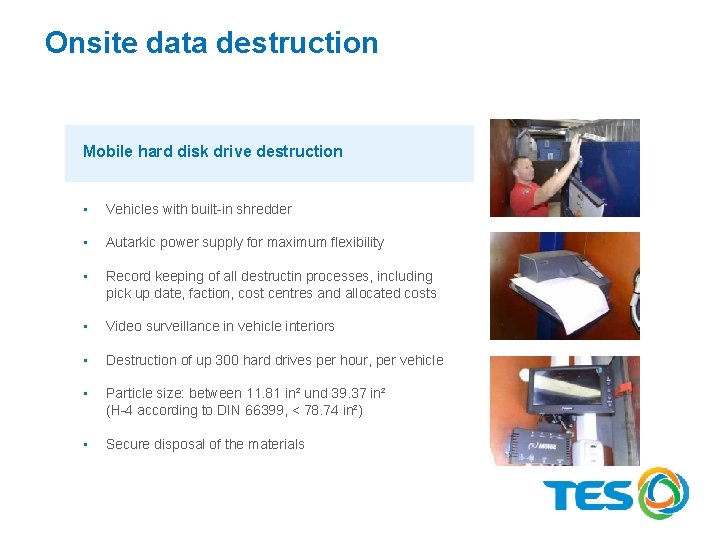
Onsite data destruction Mobile hard disk drive destruction • Vehicles with built-in shredder • Autarkic power supply for maximum flexibility • Record keeping of all destructin processes, including pick up date, faction, cost centres and allocated costs • Video surveillance in vehicle interiors • Destruction of up 300 hard drives per hour, per vehicle • Particle size: between 11. 81 in² und 39. 37 in² (H-4 according to DIN 66399, < 78. 74 in²) • Secure disposal of the materials
Links https: //www. tes-amm. com/services/ https: //youtu. be/4 p. DHFrm. C 4 kc 40

Thank you for your attention! Carl M. Ghatan General Manager Sweden Mobile: +46(0)73 546 89 20 Email: carl. ghatan@tes-amm. com Skype: cg-skype@dataserv. se www. tes-amm. com ISO 9001 l ISO 14001 l ISO 27001 l OHSAS 18001 l R 2 41
- Slides: 41