Troubleshooting Direct Access Clients Step by Step Basic
Troubleshooting Direct. Access Clients Step by Step Basic troubleshooting steps are shown in order on the next slides to assist from basic misconfigurations to more advanced problems. These steps are to be used when you have one or more Direct. Access clients that cannot connect. Written by : Tom Daniels tomdan@outlook. com www. Direct. Access. Guide. com Version 1. 3
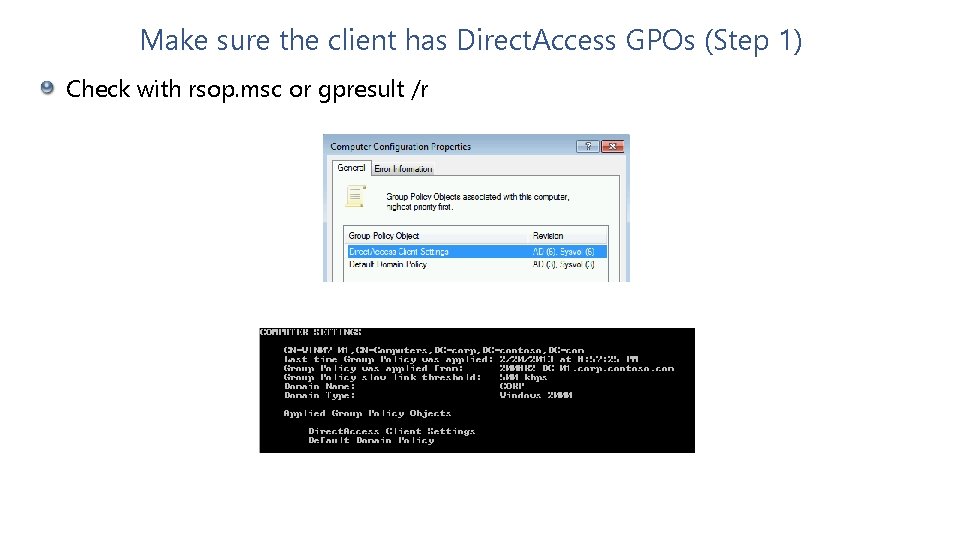
Make sure the client has Direct. Access GPOs (Step 1) Check with rsop. msc or gpresult /r
Make sure the client has Direct. Access GPOs (Step 1) This can occur when DA computer is not added to the security group or in the wrong OU not being targeted by the Direct. Access Client GPO If you’ve recently added the computer to a security group, it does require a reboot to pick up the new group membership. When in doubt, reboot the computer to ensure it has proper group membership
DA Client must think it’s on the Internet (Step 2) Check status of NCSI to make sure computer thinks it’s on the Internet
DA Client must think it’s on the Internet (Step 2) Windows OS uses Network Connectivity Status Indicator (NCSI) to determine Internet connectivity. Check icon to make sure it doesn’t have any warnings or errors Ensure NCSI in OS can reach www. msftncsi. com/ncsi. txt Some Internet connections require a proxy server Most public Internet connections have a splash page you need to logon to reach Internet resources
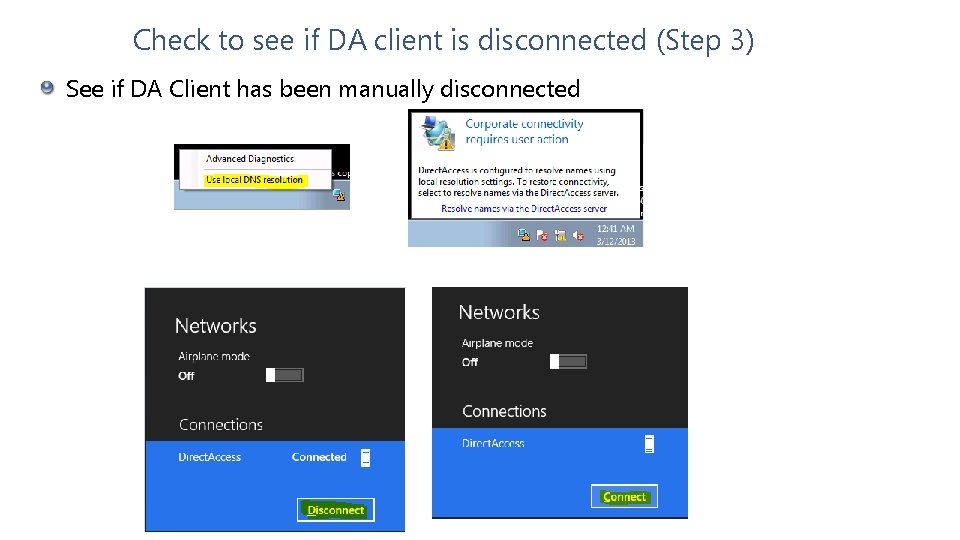
Check to see if DA client is disconnected (Step 3) See if DA Client has been manually disconnected

Check to see if DA client is disconnected (Step 3) It’s possible to manually disconnect a Direct. Access client by selecting “use local DNS resolution” with the Direct. Access Connectivity Assistant (DCA) on Windows 7 On Windows 8, the disconnect option can be selected on a Direct. Access connection to manually disconnect the Direct. Access client connection.
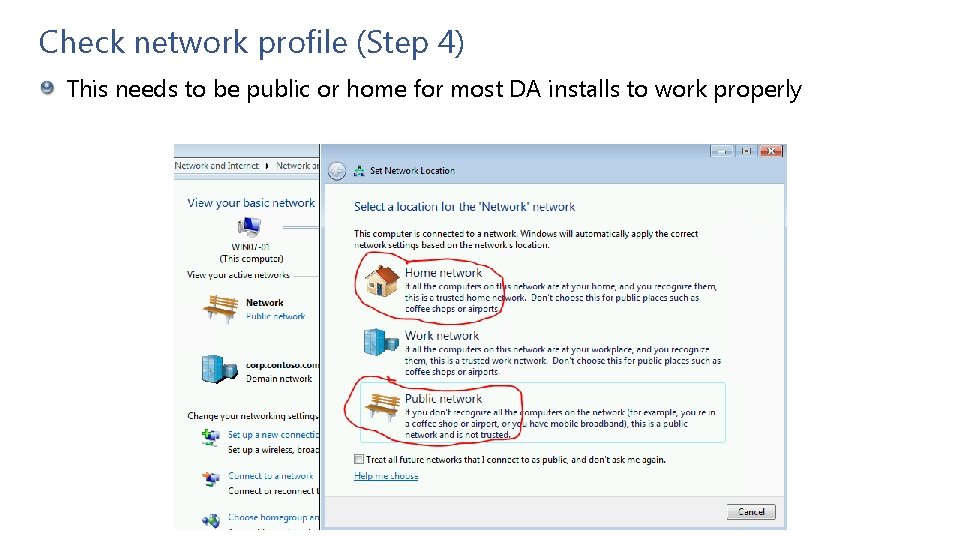
Check network profile (Step 4) This needs to be public or home for most DA installs to work properly
Check network profile (Step 4) This controls what firewall profile will apply Some environments disable the work firewall profile which can break Direct. Access if a user selects work when presented with a new network connection.
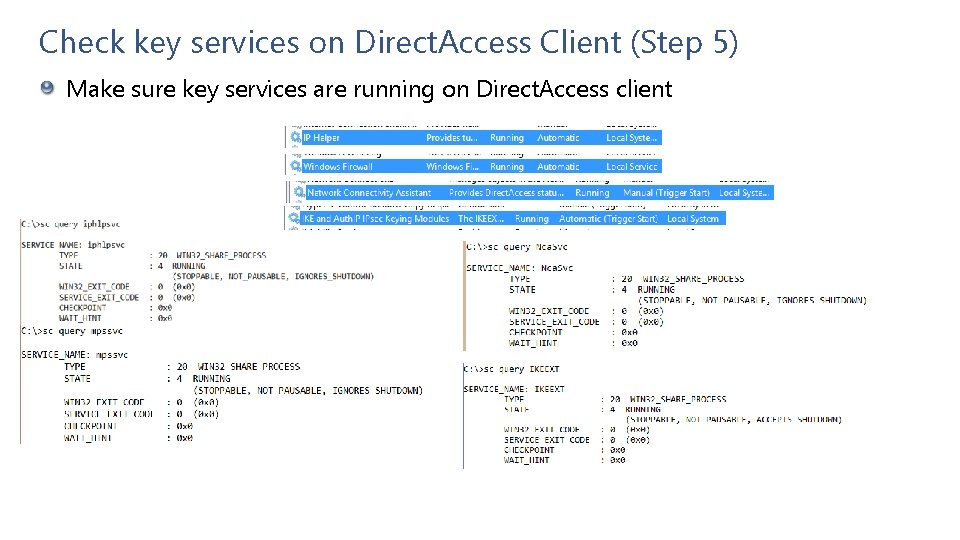
Check key services on Direct. Access Client (Step 5) Make sure key services are running on Direct. Access client
Check key services on Direct. Access Client (Step 5) IP Helper must be running in order for the IPv 6 transition adapters to load (Terero, 6 to 4, IP-HTTPS) The Windows Firewall service must also be running for the Direct. Access clients to negotiate IPsec correctly The IKE and Auth. IP IPsec Keying Modules service must be running in order for machines to properly communicate using IPsec which is required for Direct. Access The Network Connectivity Assistant is used on Windows 8+ systems to show Direct. Access Status
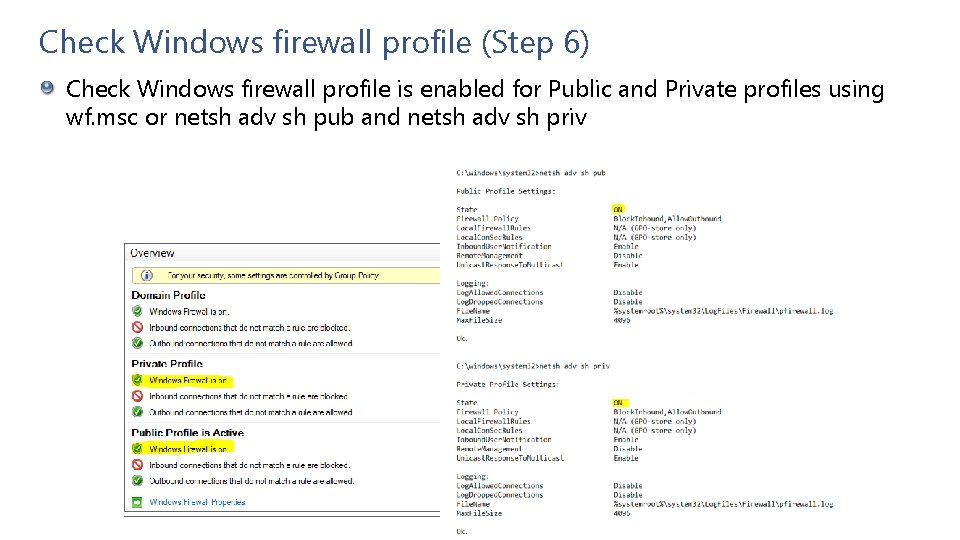
Check Windows firewall profile (Step 6) Check Windows firewall profile is enabled for Public and Private profiles using wf. msc or netsh adv sh pub and netsh adv sh priv
Check Windows firewall profile (Step 6) Not only does the Windows firewall service need to be running, the profile in the Windows Firewall for public and private needs to be enabled. If disabled, this will prevent IPsec from working correctly on the DA client.
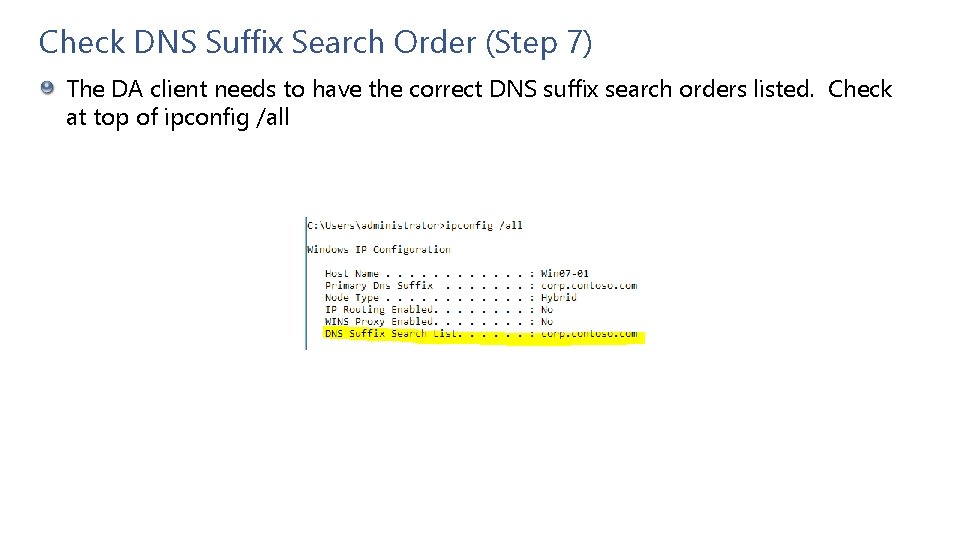
Check DNS Suffix Search Order (Step 7) The DA client needs to have the correct DNS suffix search orders listed. Check at top of ipconfig /all

Check DNS Suffix Search Order (Step 7) Most users expect to get to resources by short name. If the DNS Suffix search order is blank or not complete this can cause issues If you suspect a problem with the DNS Suffix search order, try to reach the same resources by FQDN instead and see if it works
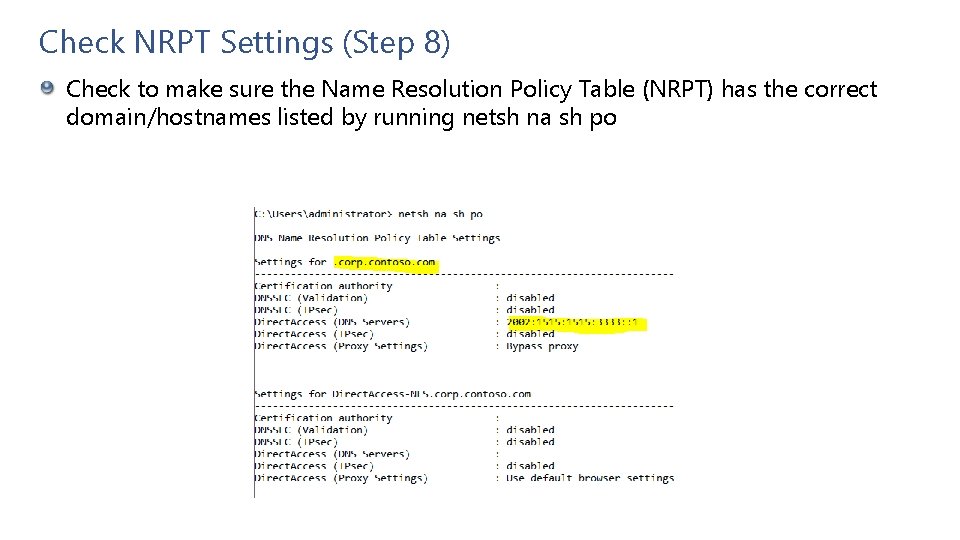
Check NRPT Settings (Step 8) Check to make sure the Name Resolution Policy Table (NRPT) has the correct domain/hostnames listed by running netsh na sh po
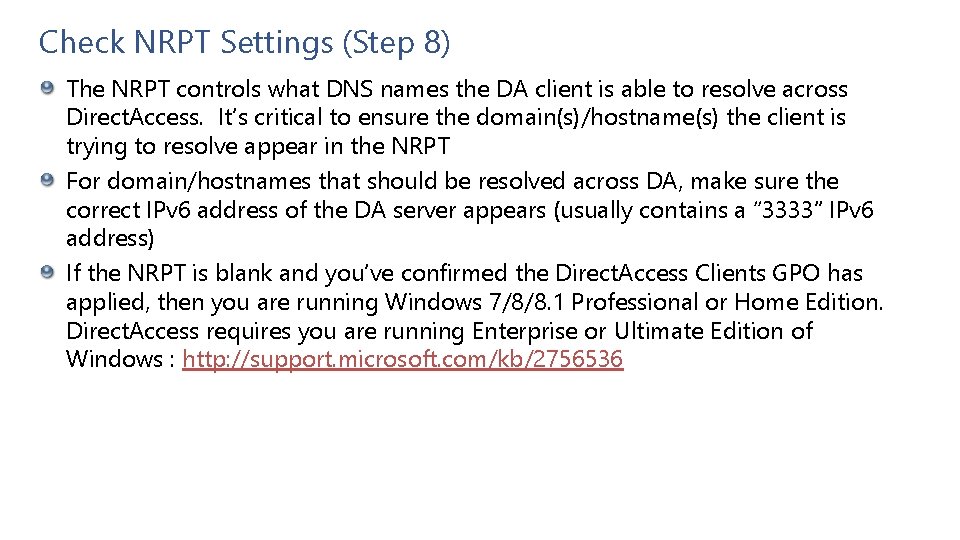
Check NRPT Settings (Step 8) The NRPT controls what DNS names the DA client is able to resolve across Direct. Access. It’s critical to ensure the domain(s)/hostname(s) the client is trying to resolve appear in the NRPT For domain/hostnames that should be resolved across DA, make sure the correct IPv 6 address of the DA server appears (usually contains a “ 3333” IPv 6 address) If the NRPT is blank and you’ve confirmed the Direct. Access Clients GPO has applied, then you are running Windows 7/8/8. 1 Professional or Home Edition. Direct. Access requires you are running Enterprise or Ultimate Edition of Windows : http: //support. microsoft. com/kb/2756536
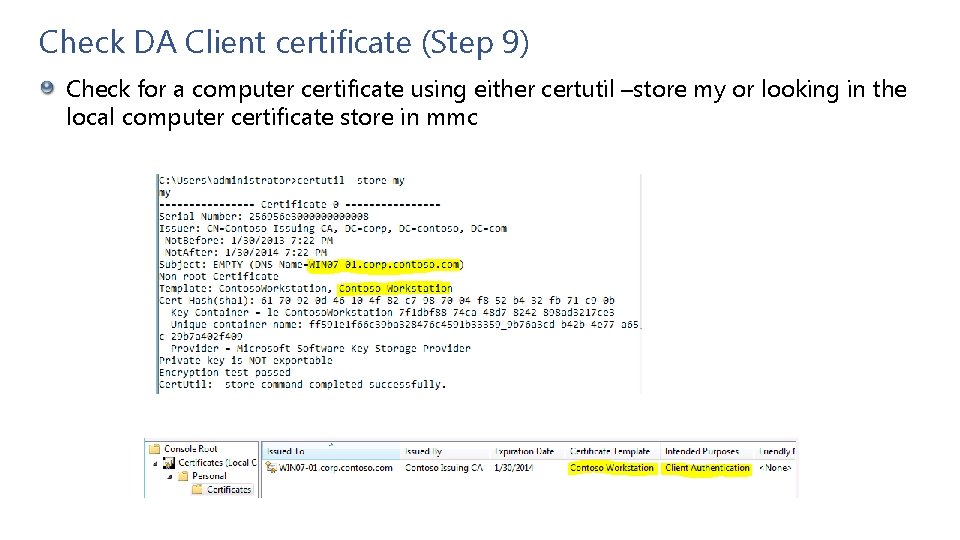
Check DA Client certificate (Step 9) Check for a computer certificate using either certutil –store my or looking in the local computer certificate store in mmc
Check DA Client certificate (Step 9) During most installs, a computer certificate is required especially if Windows 7 DA clients exist. Only exception is a Windows 8 only DA deployment which can use Kerberos. Check to make sure subject name of certificate matches the name of the computer Look at validity period, needs to be within this period Review Extended Key Usage (EKU) on certificate to ensure it lists at least Client Authentication Ensure the client certificate is not listed in the Certificate Revocation List (CRL)
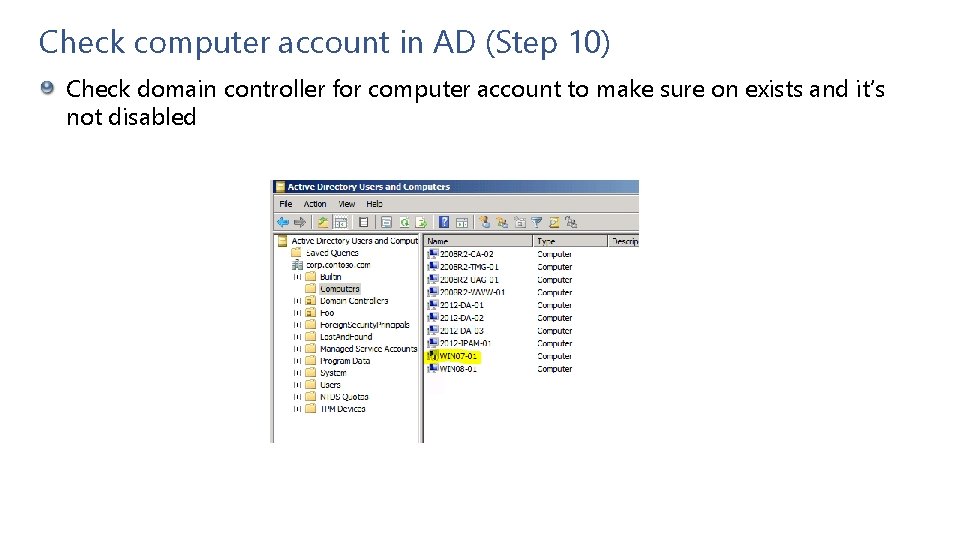
Check computer account in AD (Step 10) Check domain controller for computer account to make sure on exists and it’s not disabled
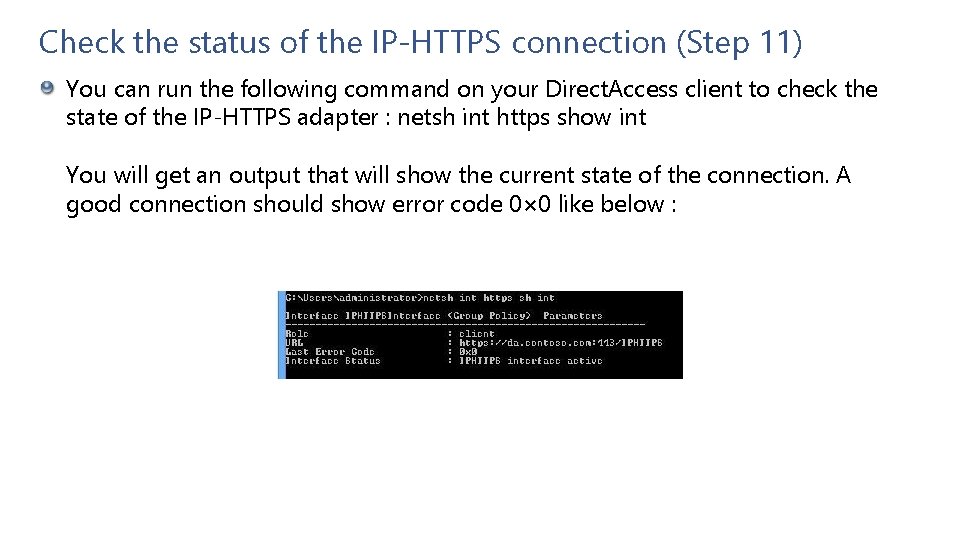
Check the status of the IP-HTTPS connection (Step 11) You can run the following command on your Direct. Access client to check the state of the IP-HTTPS adapter : netsh int https show int You will get an output that will show the current state of the connection. A good connection should show error code 0× 0 like below :
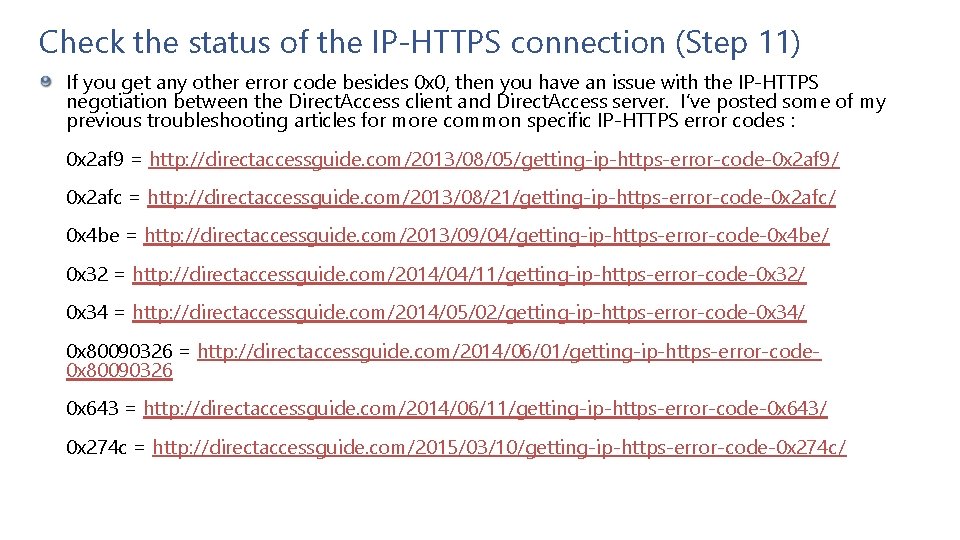
Check the status of the IP-HTTPS connection (Step 11) If you get any other error code besides 0 x 0, then you have an issue with the IP-HTTPS negotiation between the Direct. Access client and Direct. Access server. I’ve posted some of my previous troubleshooting articles for more common specific IP-HTTPS error codes : 0 x 2 af 9 = http: //directaccessguide. com/2013/08/05/getting-ip-https-error-code-0 x 2 af 9/ 0 x 2 afc = http: //directaccessguide. com/2013/08/21/getting-ip-https-error-code-0 x 2 afc/ 0 x 4 be = http: //directaccessguide. com/2013/09/04/getting-ip-https-error-code-0 x 4 be/ 0 x 32 = http: //directaccessguide. com/2014/04/11/getting-ip-https-error-code-0 x 32/ 0 x 34 = http: //directaccessguide. com/2014/05/02/getting-ip-https-error-code-0 x 34/ 0 x 80090326 = http: //directaccessguide. com/2014/06/01/getting-ip-https-error-code 0 x 80090326 0 x 643 = http: //directaccessguide. com/2014/06/11/getting-ip-https-error-code-0 x 643/ 0 x 274 c = http: //directaccessguide. com/2015/03/10/getting-ip-https-error-code-0 x 274 c/
- Slides: 22