Tropos Research Overview RWTH Aachen M Jarke and
![Speech Act Perspektive Action Workflow [Medina-Mora et al. 1992, Schäl 96] Speech Act Perspektive Action Workflow [Medina-Mora et al. 1992, Schäl 96]](https://slidetodoc.com/presentation_image_h2/e131c69014b9fadfd5d37cb1871dfd43/image-20.jpg)
- Slides: 38
Tropos Research Overview: RWTH Aachen M. Jarke and G. Lakemeyer RWTH Aachen Computer Science V TROPOS Workshop, Trento, November 15 -16, 2001
History of Aachen’s Approach DAIDA : Metadata linking IS development phases, development of Telos, first Concept. Base prototype (1988) COMPULOG : logical foundations of meta modeling, meta formula handling by partial evaluation (Jeusfeld 1992) NATURE/CREWS : application to perspective resolution in requirements engineering and business modeling (Nissen 1997, Peters 1997), extension to business cooperation (Kethers 2001) and warehoues/e-commerce (Quix 2002) RWTH Aachen Computer Science V TROPOS : dynamic modeling of social networks in coooperation with sociologists and entrepreneurs TROPOS Workshop, Trento, November 15 -16, 2001
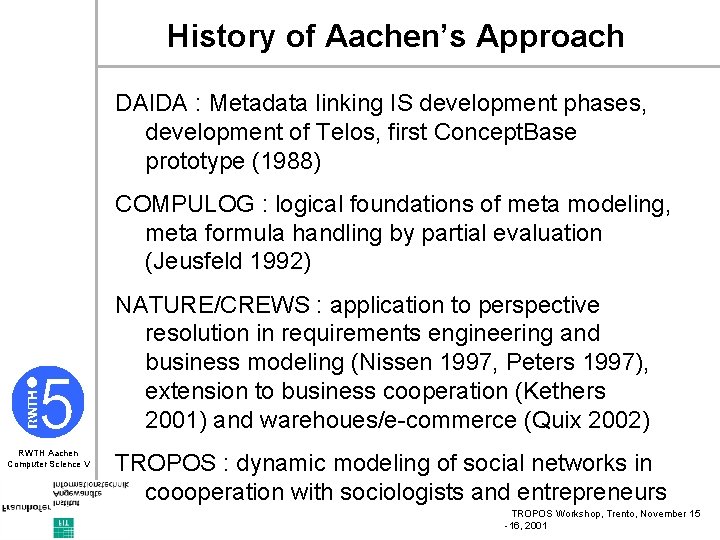
Multi-Perspective Cooperative Modeling : Metamodels as Goals common meta model entity relationship notation data flow notation viewpoint 1 viewpoint 2 For small processes [Nissen et al. ; IEEE i --> metaplan + repository formalizat Forn large processes [Rose, CACM 12/98] --> layout generation + synchroniza analysis common reality RWTH Aachen Computer Science V TROPOS Workshop, Trento, November 15 -16, 2001
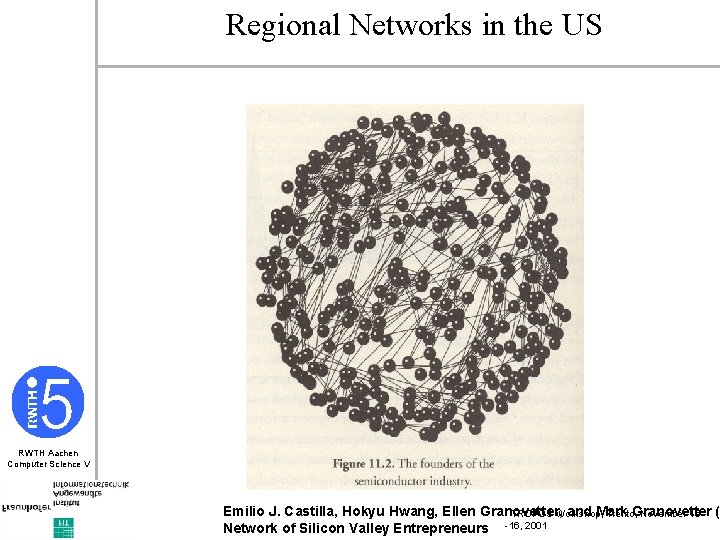
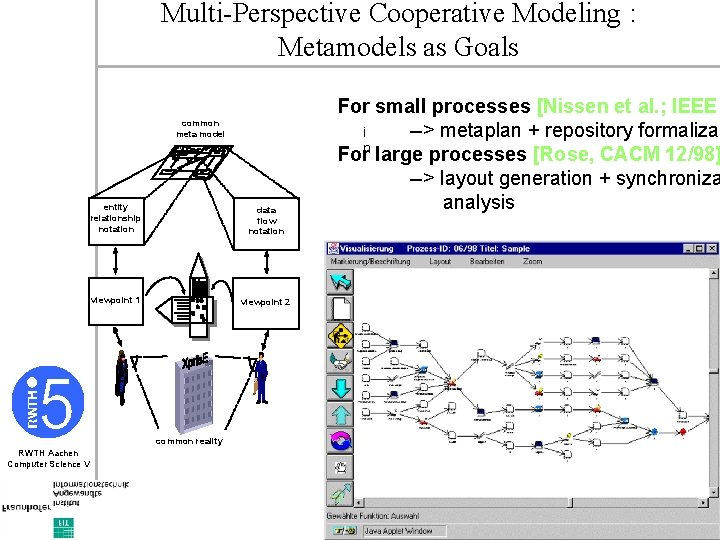
Regional Networks in the US RWTH Aachen Computer Science V Emilio J. Castilla, Hokyu Hwang, Ellen Granovetter, and Mark Granovetter ( TROPOS Workshop, Trento, November 15 -16, 2001 Network of Silicon Valley Entrepreneurs
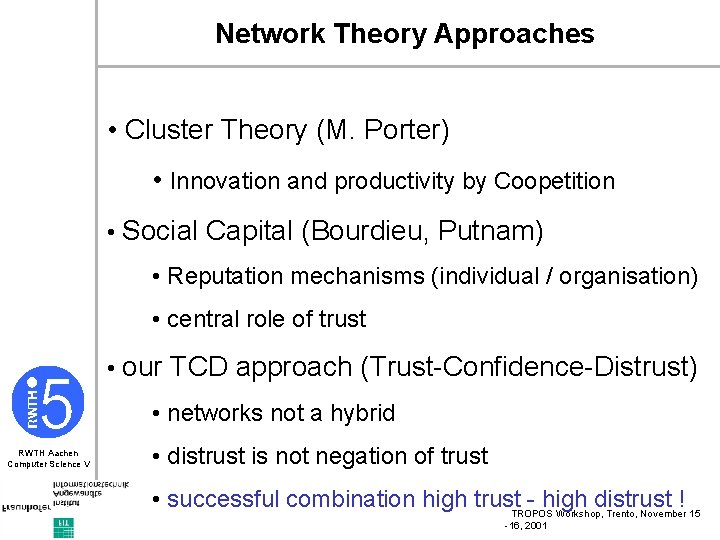
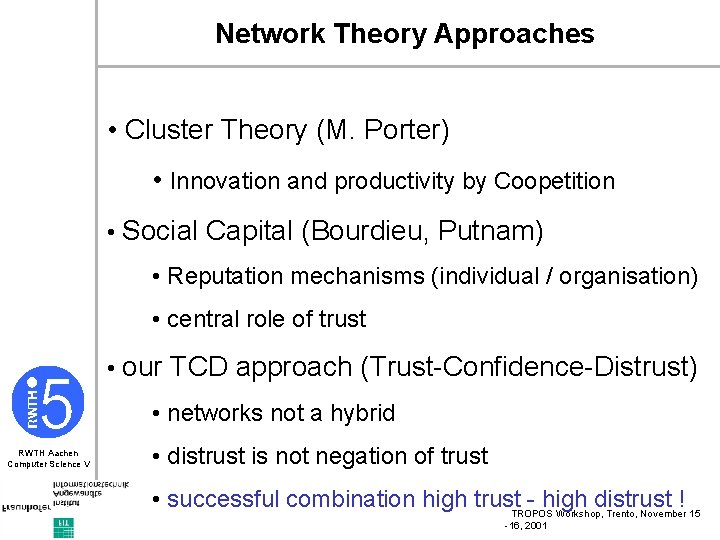
Network Theory Approaches • Cluster Theory (M. Porter) • Innovation and productivity by Coopetition • Social Capital (Bourdieu, Putnam) • Reputation mechanisms (individual / organisation) • central role of trust • our TCD approach (Trust-Confidence-Distrust) • networks not a hybrid RWTH Aachen Computer Science V • distrust is not negation of trust • successful combination high trust. TROPOS - high distrust ! Workshop, Trento, November 15 -16, 2001
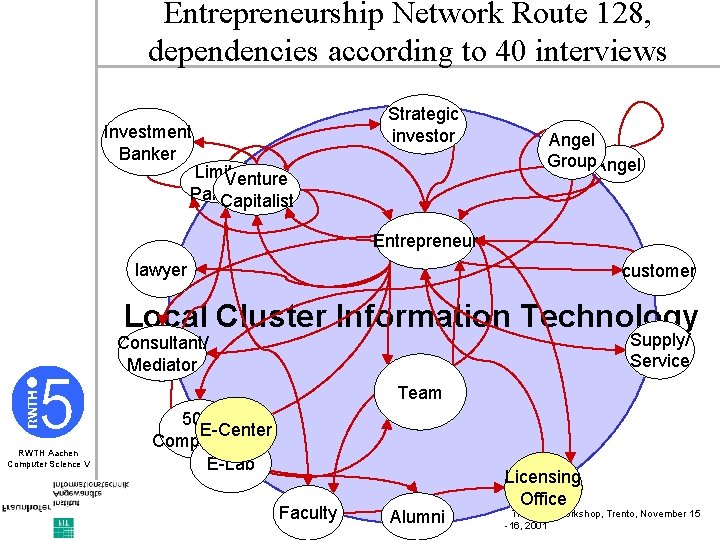
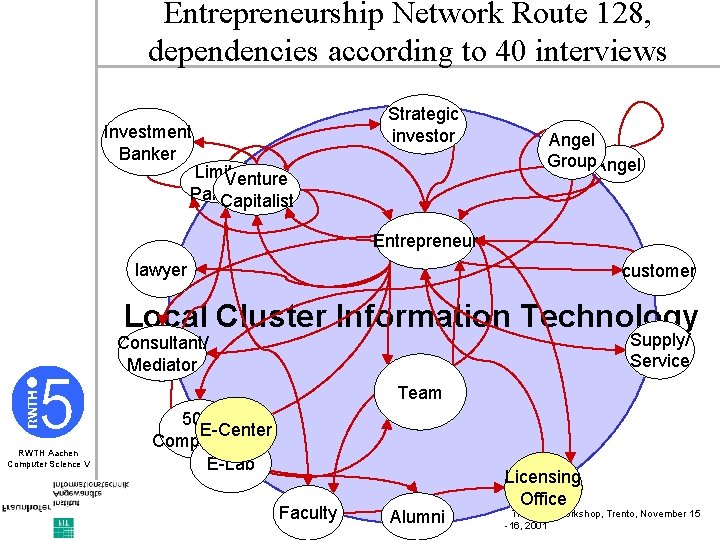
Entrepreneurship Network Route 128, dependencies according to 40 interviews Strategic investor Investment Banker Limited Venture Partners Capitalist Angel Group. Angel Entrepreneur lawyer customer Local Cluster Information Technology Supply/ Service Consultant/ Mediator Team RWTH Aachen Computer Science V 50 k. E-Center Competition E-Lab Faculty Alumni Licensing Office TROPOS Workshop, Trento, November 15 -16, 2001
Modeling Organisation Networks with Tropos: A Trust-Centered Approach M. Jarke and G. Lakemeyer Aachen University of Technology other contributors: RWTH Aachen Computer Science V L. Ellrich, C. Funken, M. Meister, Freiburg G. Gans, S. Kethers, R. Klamma, T. Vits, Aachen V. Wulf, Fraunhofer FITTROPOS Workshop, Trento, November 15 -16, 2001
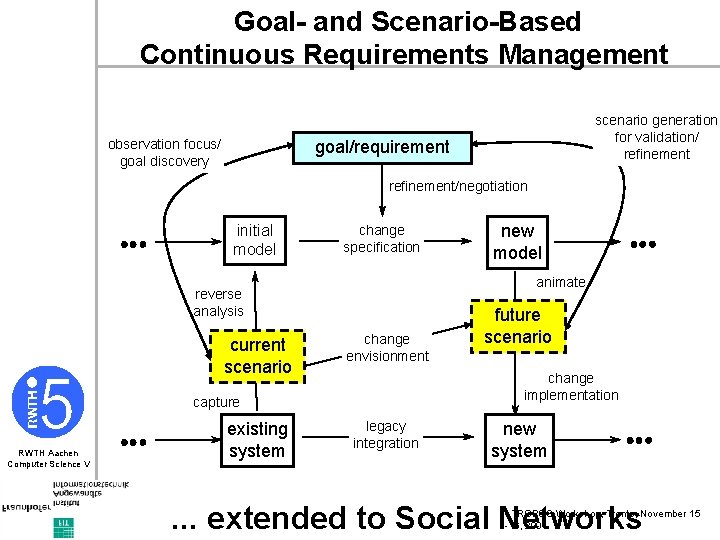
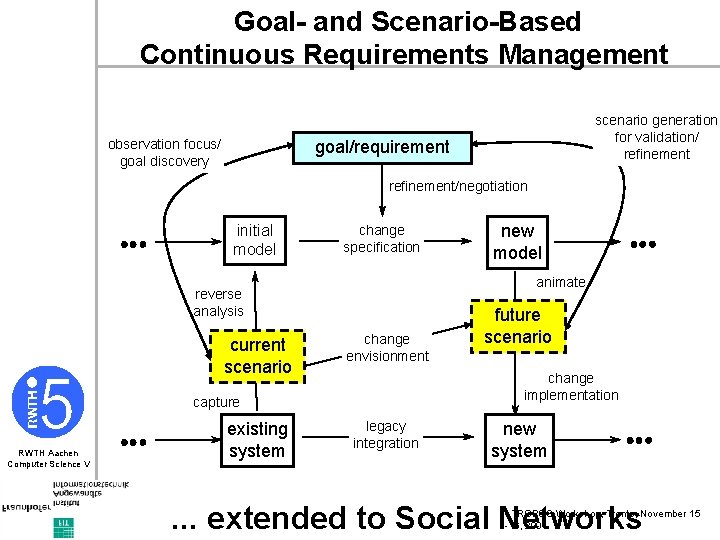
Goal- and Scenario-Based Continuous Requirements Management observation focus/ goal discovery scenario generation for validation/ refinement goal/requirement refinement/negotiation initial model change specification animate reverse analysis current scenario change envisionment RWTH Aachen Computer Science V future scenario change implementation capture existing system new model legacy integration new system . . . extended to Social Networks TROPOS Workshop, Trento, November 15 -16, 2001
Social Networks • an autonomous form of coordination that combines advantages of two traditional mechanisms • markets: flexibility, adaptive to competition • hierarchies: long duration cooperation • trusting cooperation of autonomous, but interdependent agents (here: organizations) • small-business B 2 B commerce, virtual org‘s RWTH Aachen Computer Science V • entrepreneurship networks TROPOS Workshop, Trento, November 15 -16, 2001
Overview 1. Role of Trust/Distrust in Agent Networks 2. A Multi-Perspective Modeling Approach 3. The Tropos(AC) Prototype 4. Conclusions RWTH Aachen Computer Science V TROPOS Workshop, Trento, November 15 -16, 2001
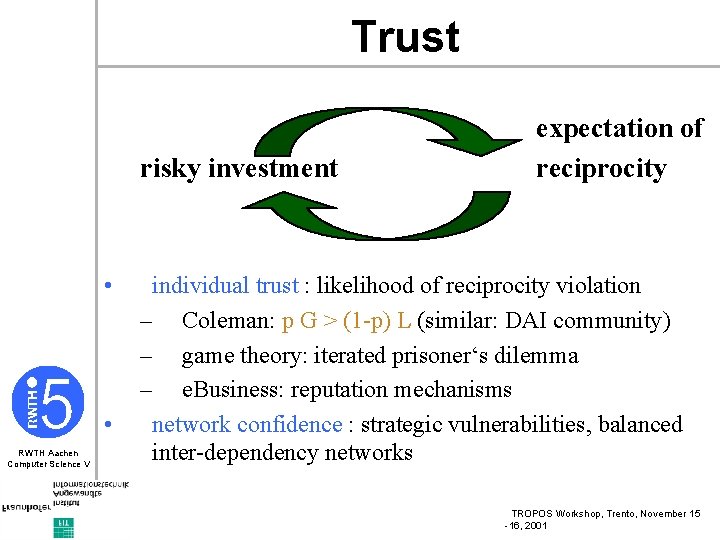
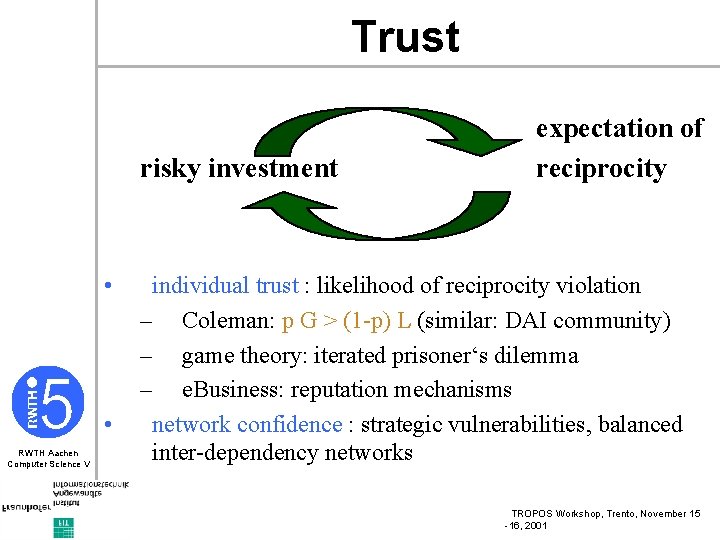
Trust risky investment • • RWTH Aachen Computer Science V expectation of reciprocity individual trust : likelihood of reciprocity violation – Coleman: p G > (1 -p) L (similar: DAI community) – game theory: iterated prisoner‘s dilemma – e. Business: reputation mechanisms network confidence : strategic vulnerabilities, balanced inter-dependency networks TROPOS Workshop, Trento, November 15 -16, 2001
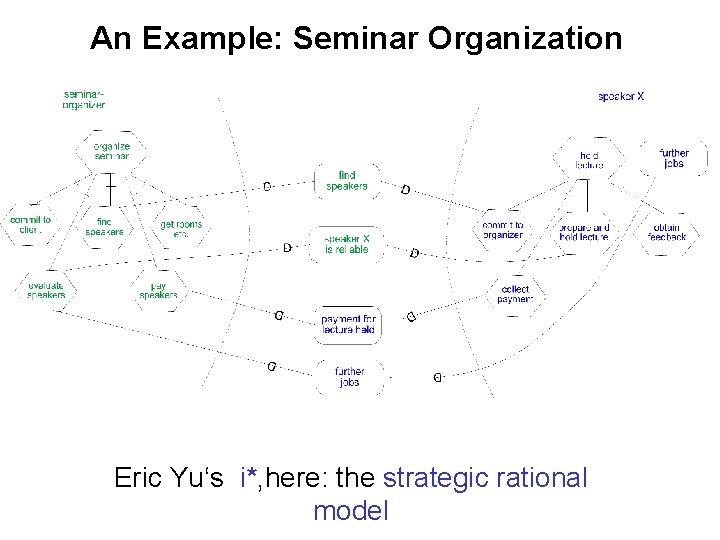
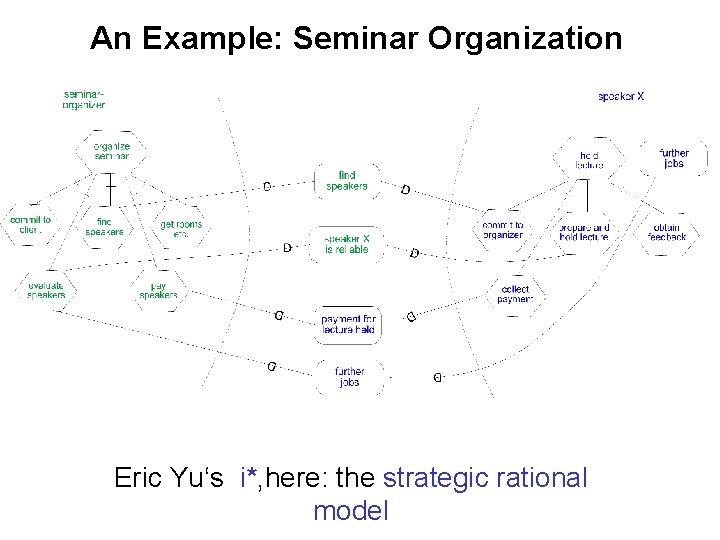
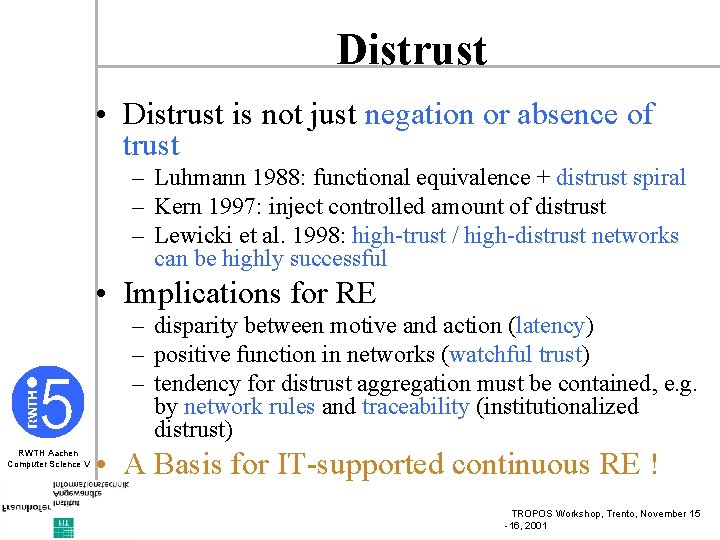
An Example: Seminar Organization Eric Yu‘s i*, here: the strategic rational model
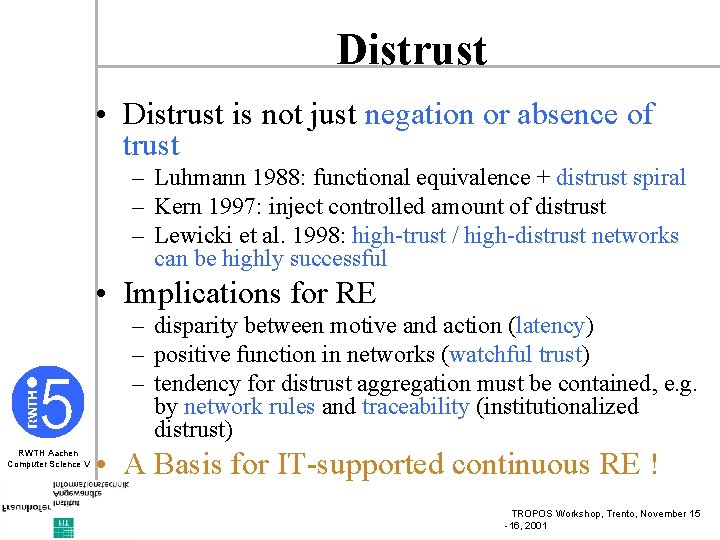
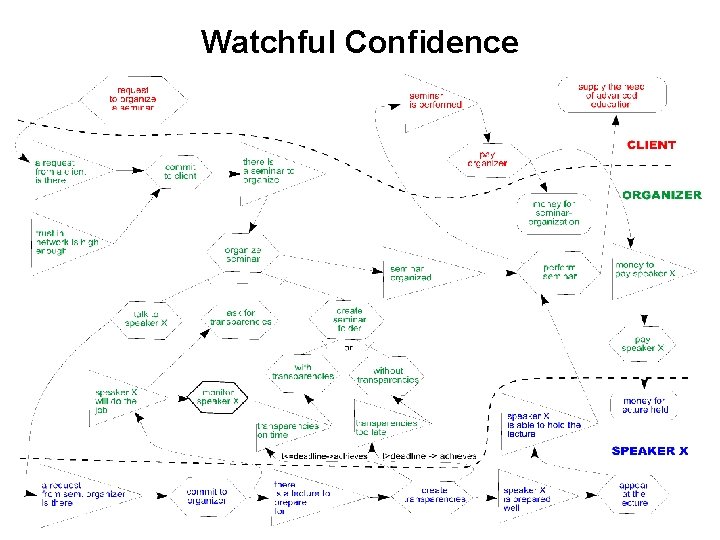
Distrust • Distrust is not just negation or absence of trust – Luhmann 1988: functional equivalence + distrust spiral – Kern 1997: inject controlled amount of distrust – Lewicki et al. 1998: high-trust / high-distrust networks can be highly successful • Implications for RE – disparity between motive and action (latency) – positive function in networks (watchful trust) – tendency for distrust aggregation must be contained, e. g. by network rules and traceability (institutionalized distrust) RWTH Aachen Computer Science V • A Basis for IT-supported continuous RE ! TROPOS Workshop, Trento, November 15 -16, 2001
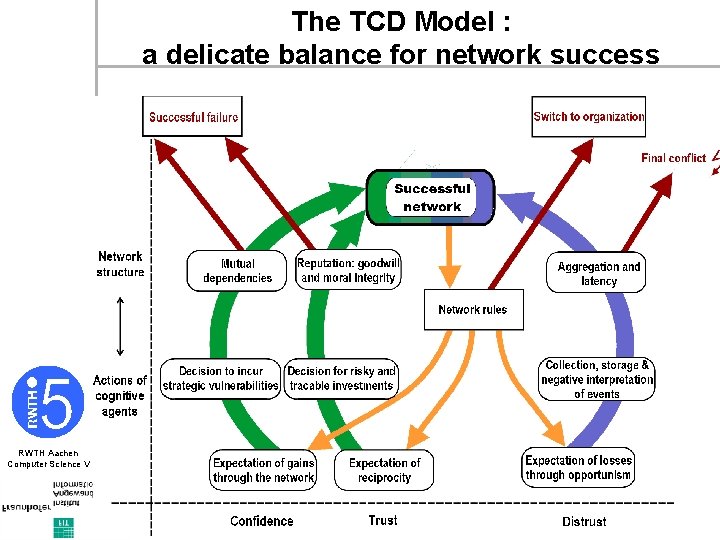
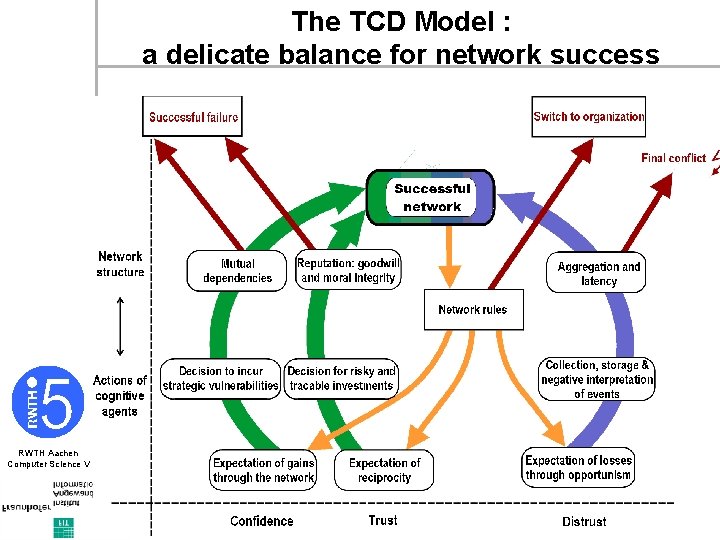
The TCD Model : a delicate balance for network success RWTH Aachen Computer Science V TROPOS Workshop, Trento, November 15 -16, 2001
Overview 1. Role of Trust/Distrust in Agent Networks 2. A Multi-Perspective Modeling Approach 3. The Tropos(AC) Prototype 4. Conclusions RWTH Aachen Computer Science V TROPOS Workshop, Trento, November 15 -16, 2001
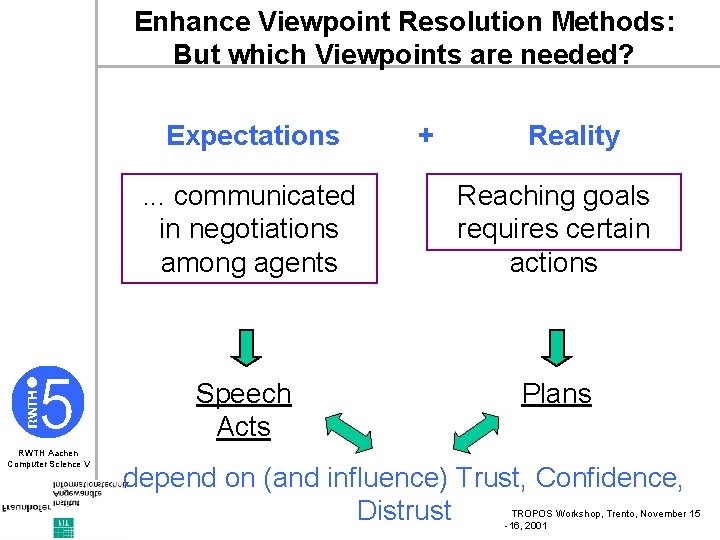
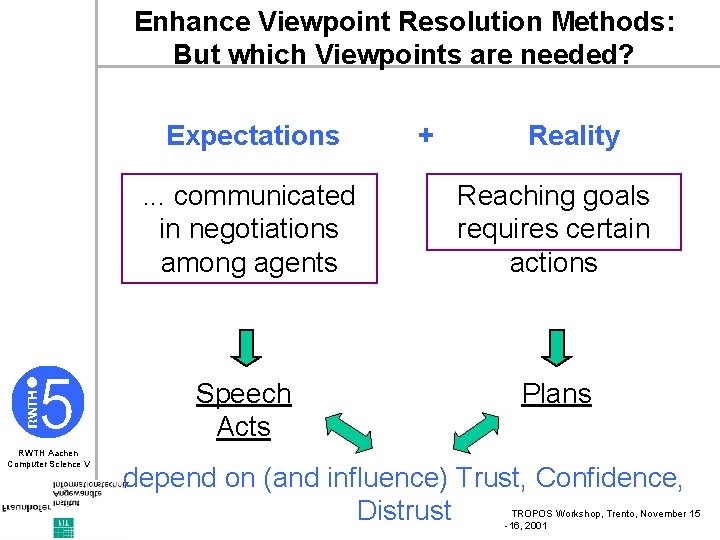
Enhance Viewpoint Resolution Methods: But which Viewpoints are needed? Expectations RWTH Aachen Computer Science V + Reality . . . communicated in negotiations among agents Reaching goals requires certain actions Speech Acts Plans depend on (and influence) Trust, Confidence, Distrust TROPOS Workshop, Trento, November 15 -16, 2001
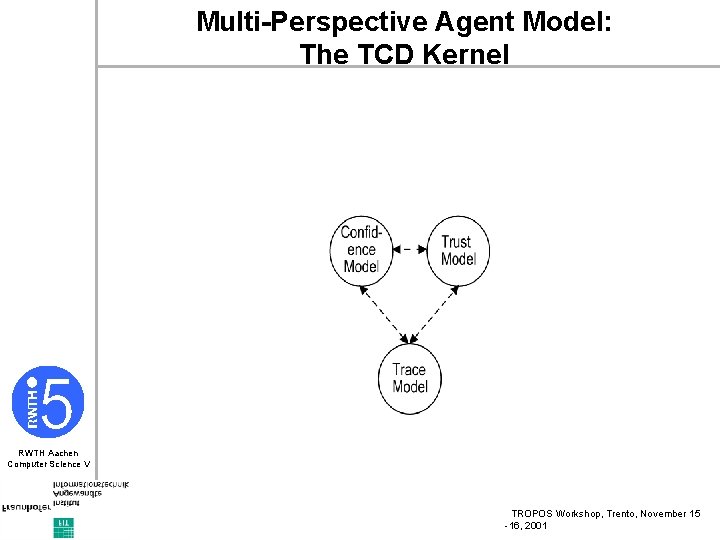
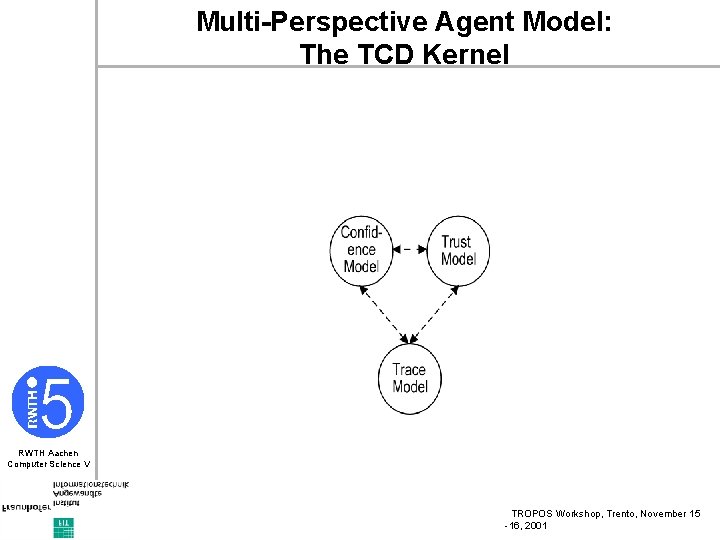
Multi-Perspective Agent Model: The TCD Kernel RWTH Aachen Computer Science V TROPOS Workshop, Trento, November 15 -16, 2001
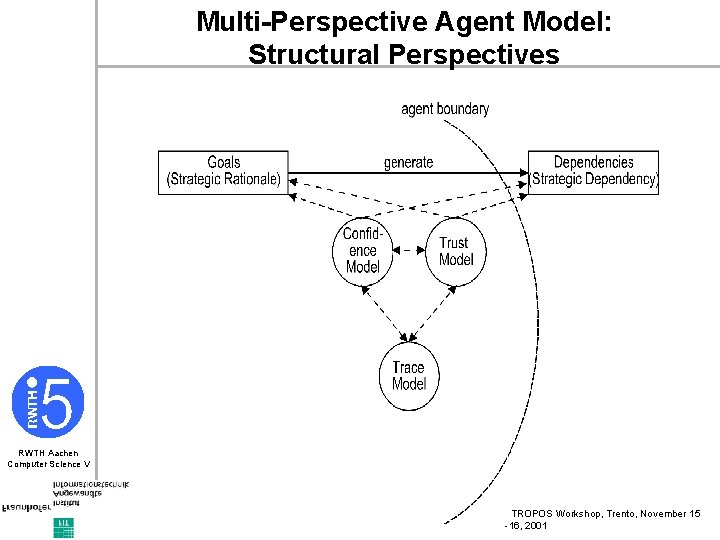
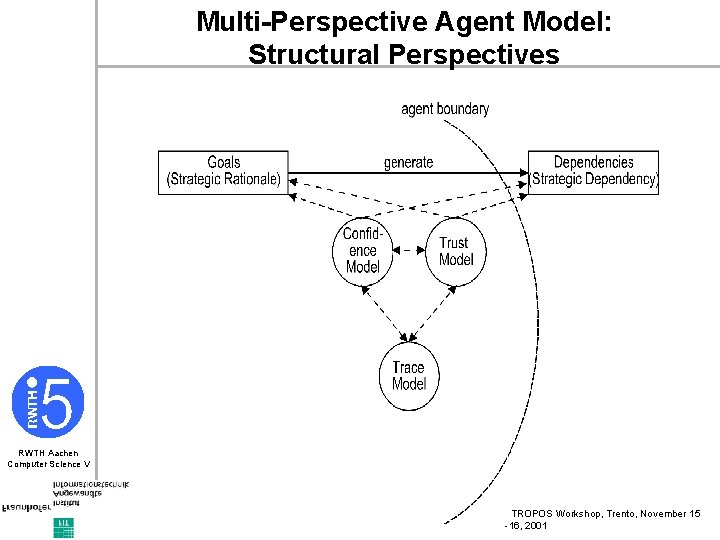
Multi-Perspective Agent Model: Structural Perspectives RWTH Aachen Computer Science V TROPOS Workshop, Trento, November 15 -16, 2001
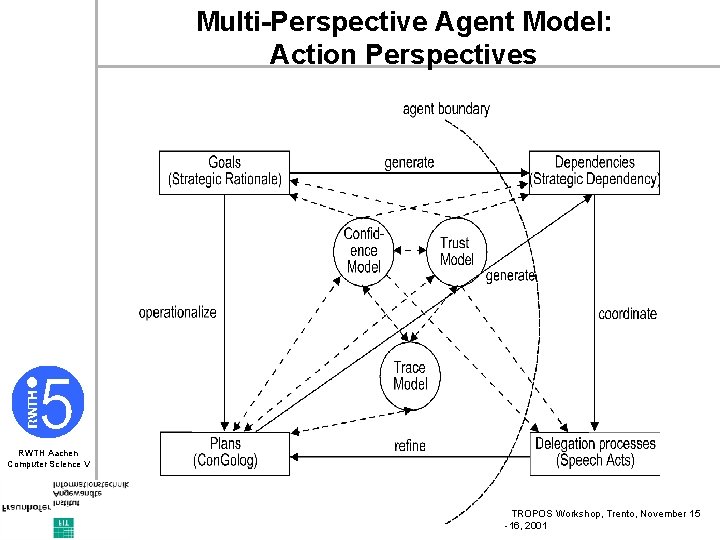
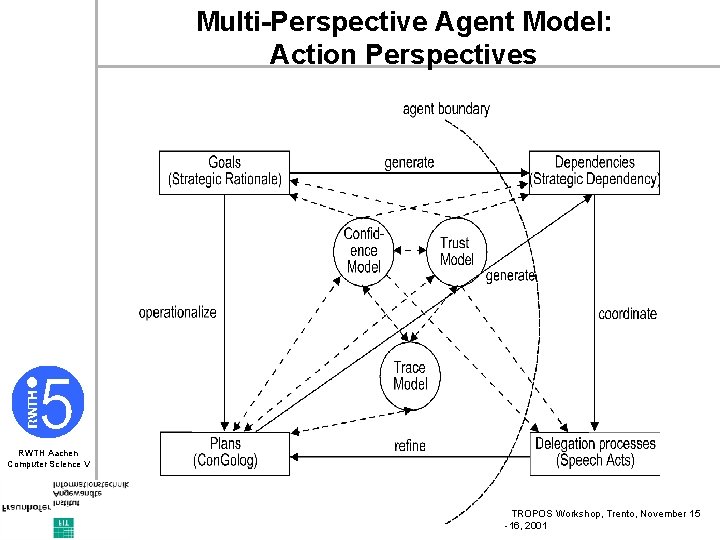
Multi-Perspective Agent Model: Action Perspectives RWTH Aachen Computer Science V TROPOS Workshop, Trento, November 15 -16, 2001
![Speech Act Perspektive Action Workflow MedinaMora et al 1992 Schäl 96 Speech Act Perspektive Action Workflow [Medina-Mora et al. 1992, Schäl 96]](https://slidetodoc.com/presentation_image_h2/e131c69014b9fadfd5d37cb1871dfd43/image-20.jpg)
Speech Act Perspektive Action Workflow [Medina-Mora et al. 1992, Schäl 96]
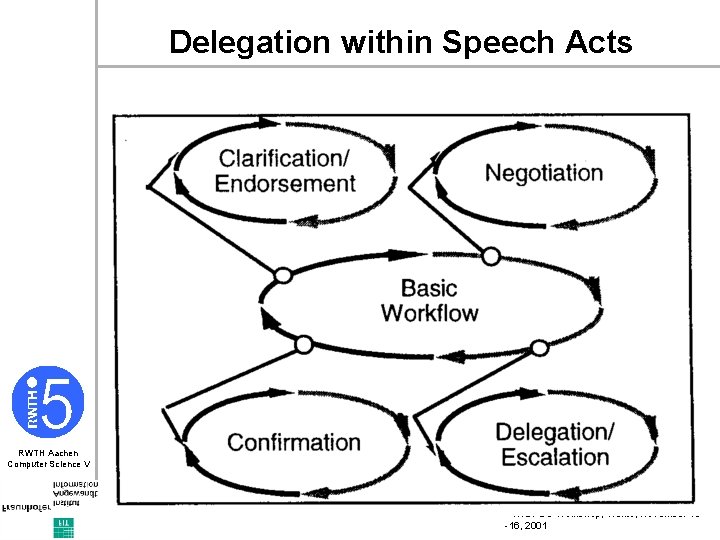
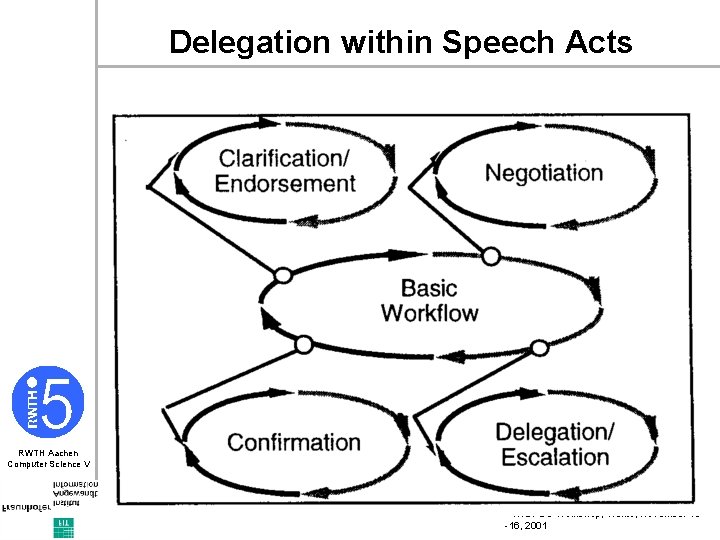
Delegation within Speech Acts RWTH Aachen Computer Science V TROPOS Workshop, Trento, November 15 -16, 2001
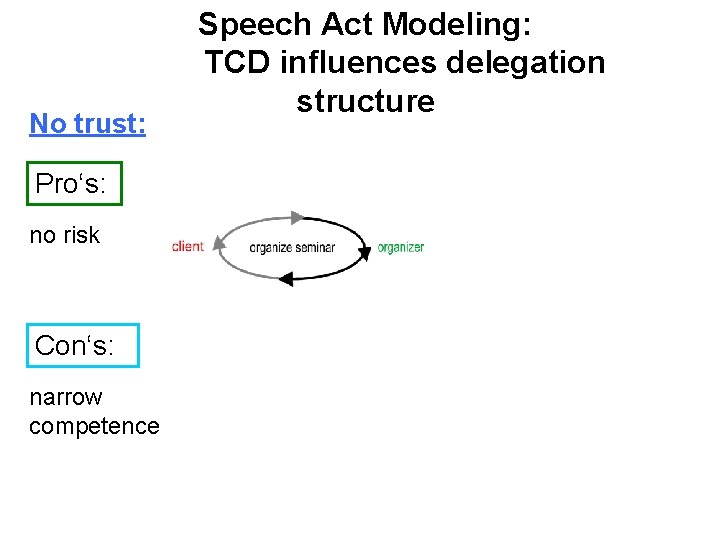
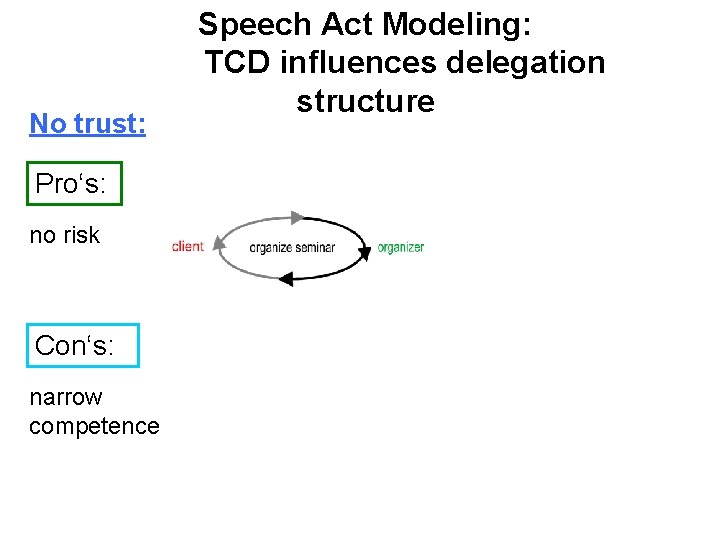
No trust: Pro‘s: no risk Con‘s: narrow competence Speech Act Modeling: TCD influences delegation structure
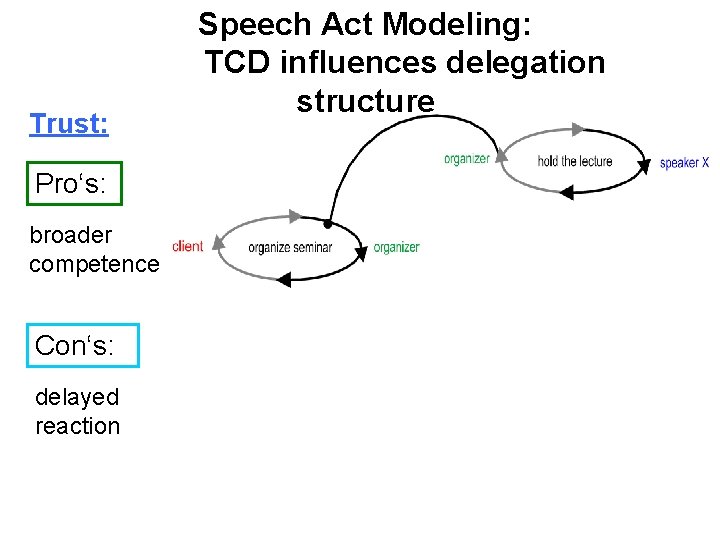
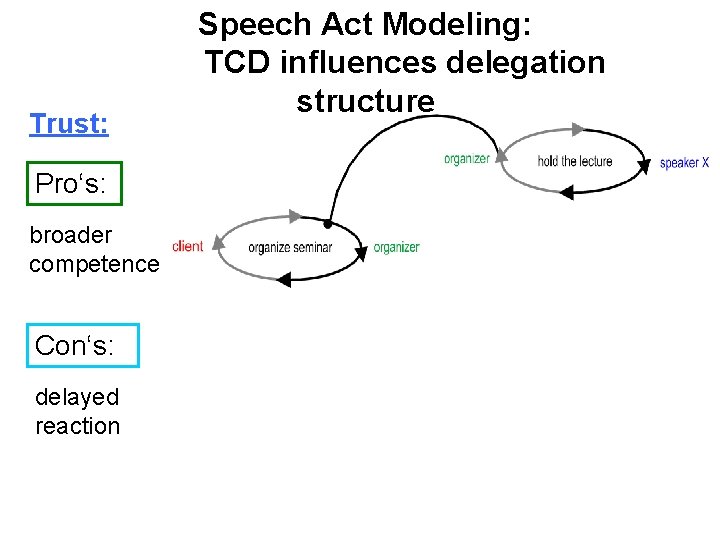
Trust: Pro‘s: broader competence Con‘s: delayed reaction Speech Act Modeling: TCD influences delegation structure
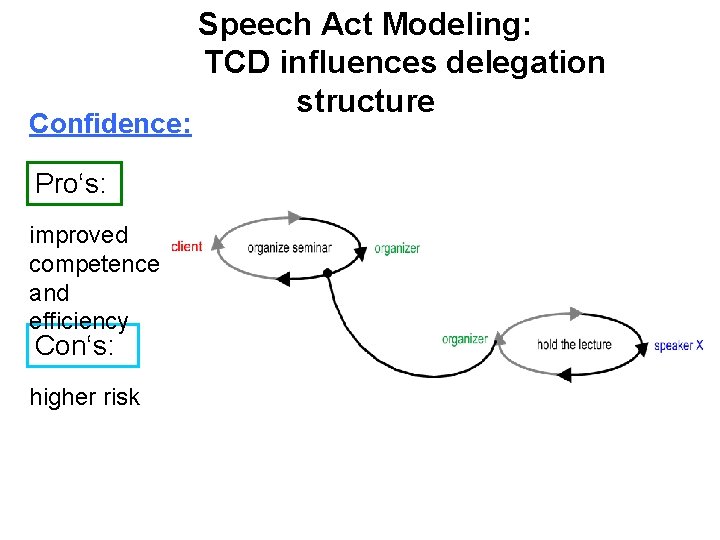
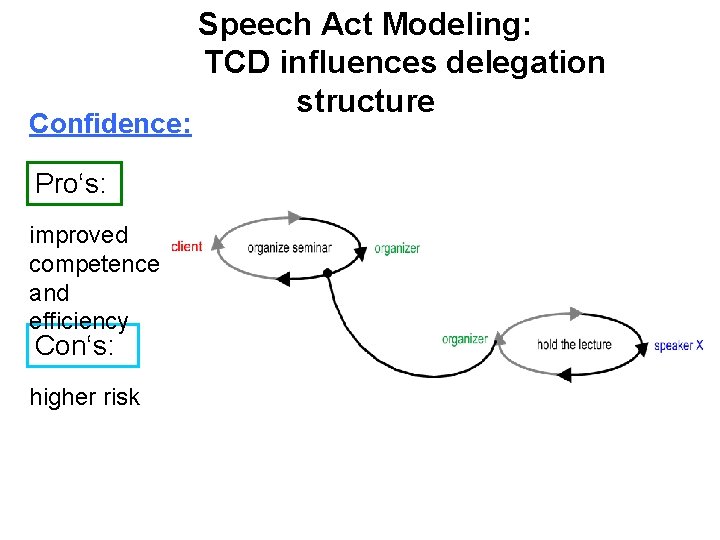
Confidence: Pro‘s: improved competence and efficiency Con‘s: higher risk Speech Act Modeling: TCD influences delegation structure
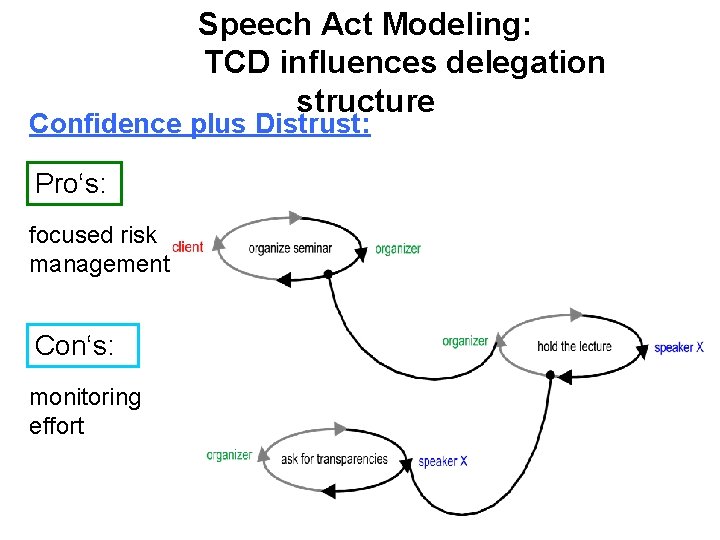
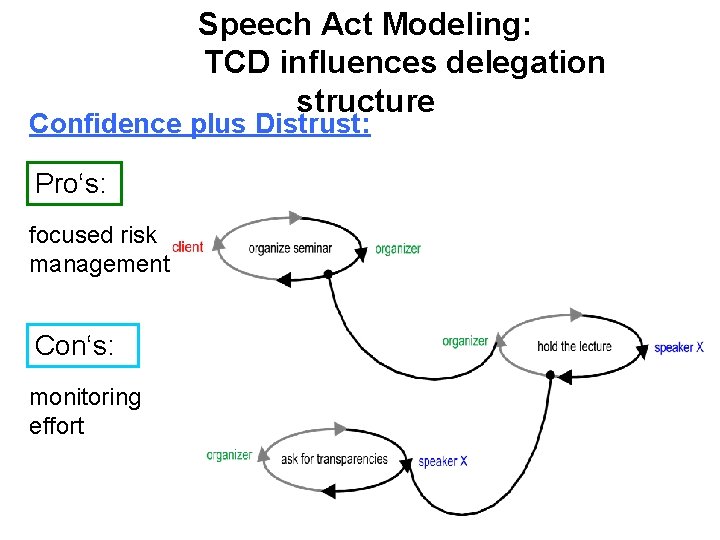
Speech Act Modeling: TCD influences delegation structure Confidence plus Distrust: Pro‘s: focused risk management Con‘s: monitoring effort
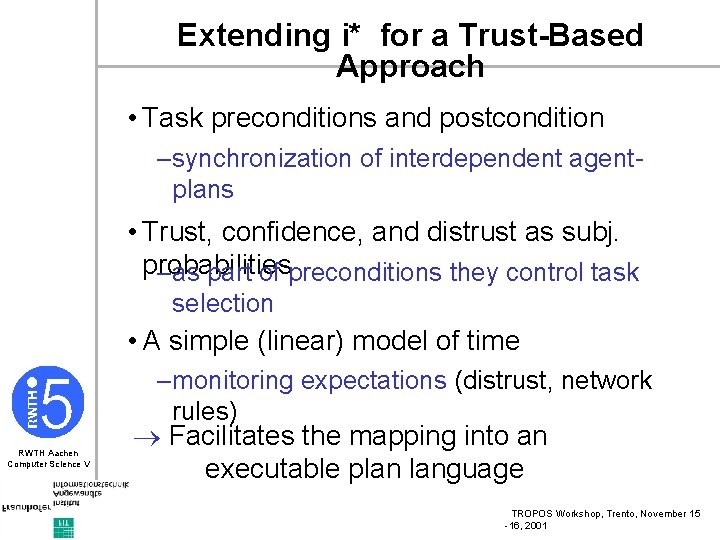
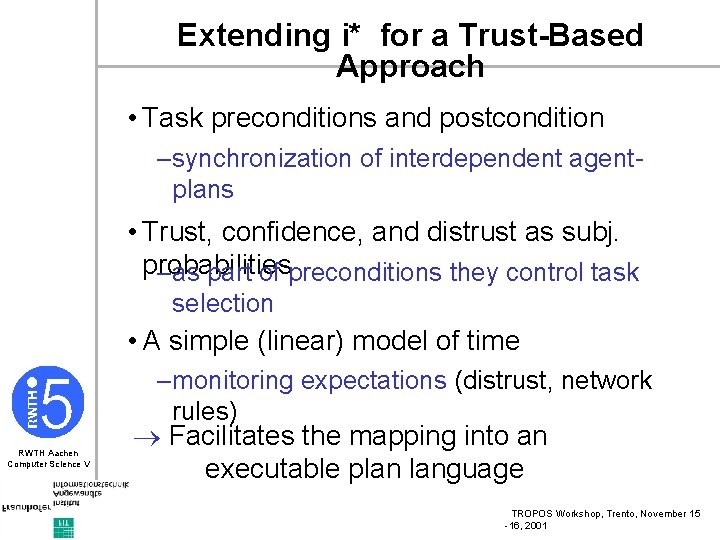
Extending i* for a Trust-Based Approach • Task preconditions and postcondition –synchronization of interdependent agentplans • Trust, confidence, and distrust as subj. probabilities –as part of preconditions they control task selection • A simple (linear) model of time –monitoring expectations (distrust, network rules) RWTH Aachen Computer Science V Facilitates the mapping into an executable plan language TROPOS Workshop, Trento, November 15 -16, 2001
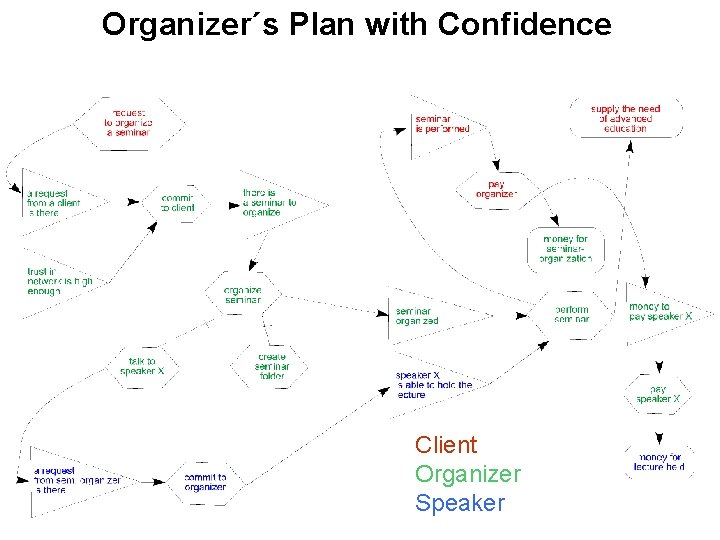
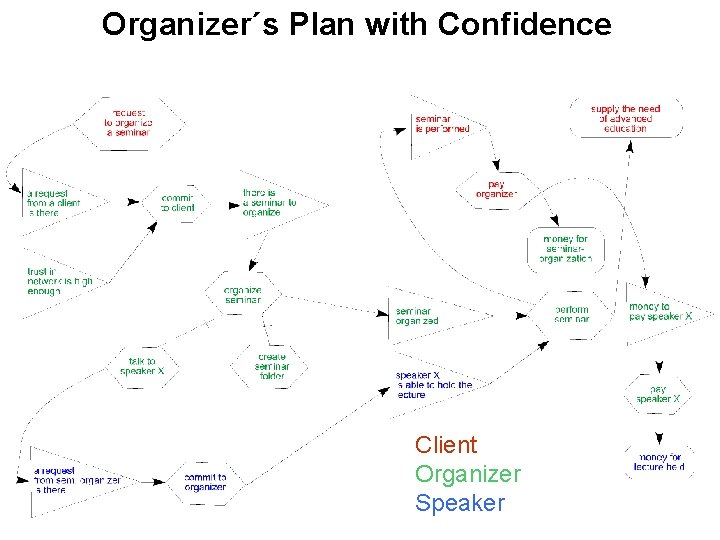
Organizer´s Plan with Confidence Client Organizer Speaker
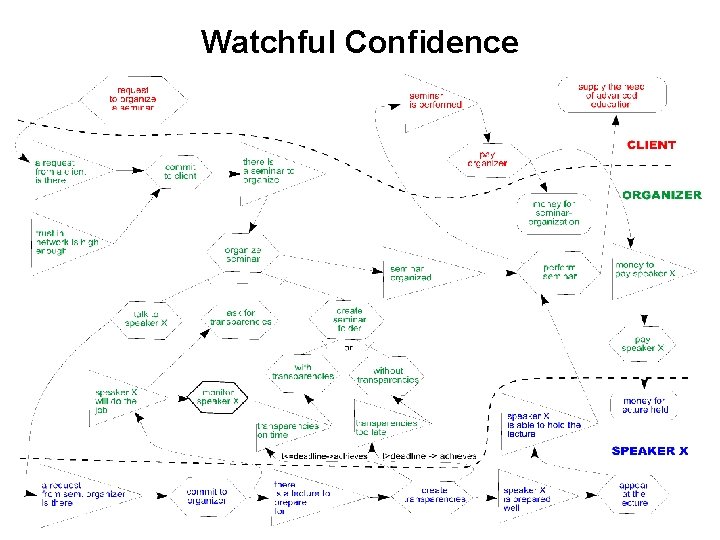
Watchful Confidence
Overview 1. Role of Trust/Distrust in Agent Networks 2. A Multi-Perspective Modeling Approach 3. The Tropos(AC) Prototype 4. Conclusions RWTH Aachen Computer Science V TROPOS Workshop, Trento, November 15 -16, 2001
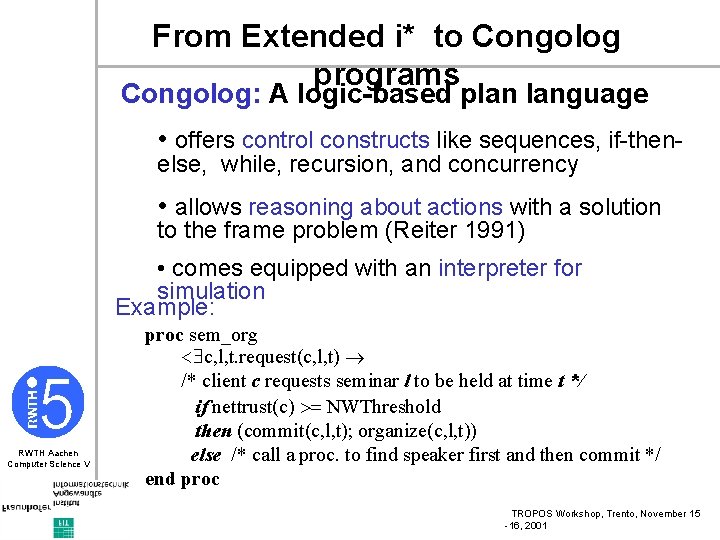
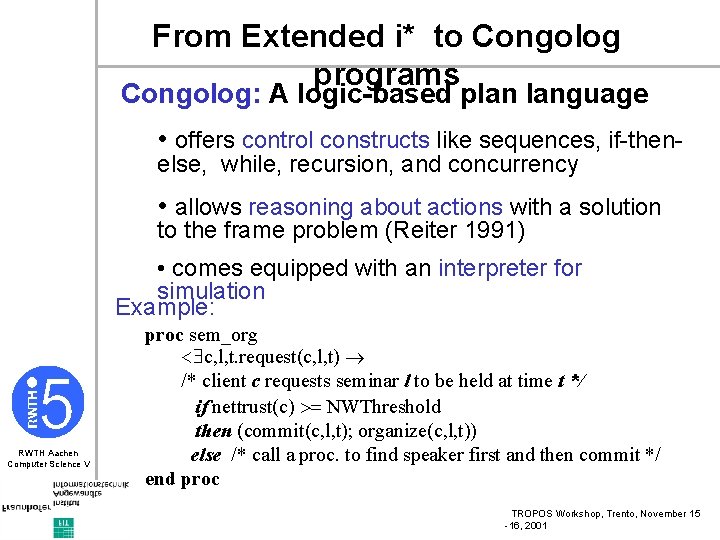
From Extended i* to Congolog programs Congolog: A logic-based plan language • offers control constructs like sequences, if-thenelse, while, recursion, and concurrency • allows reasoning about actions with a solution to the frame problem (Reiter 1991) • comes equipped with an interpreter for simulation Example: RWTH Aachen Computer Science V proc sem_org < c, l, t. request(c, l, t) /* client c requests seminar l to be held at time t */ if nettrust(c) NWThreshold then (commit(c, l, t); organize(c, l, t)) else /* call a proc. to find speaker first and then commit */ end proc TROPOS Workshop, Trento, November 15 -16, 2001
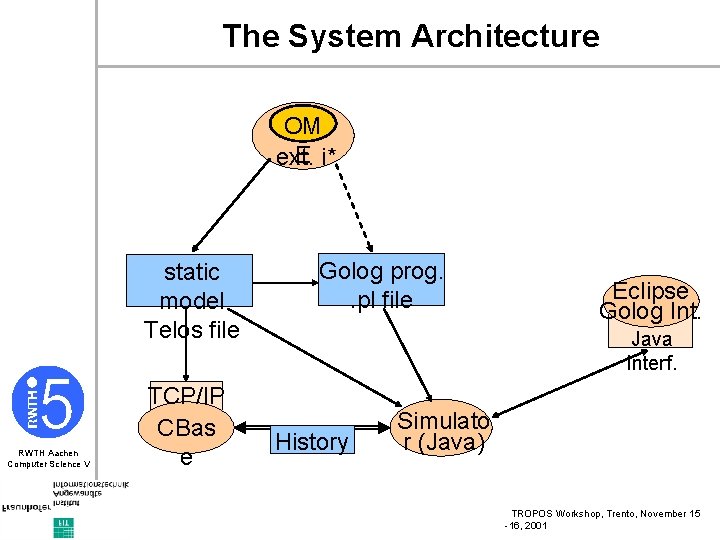
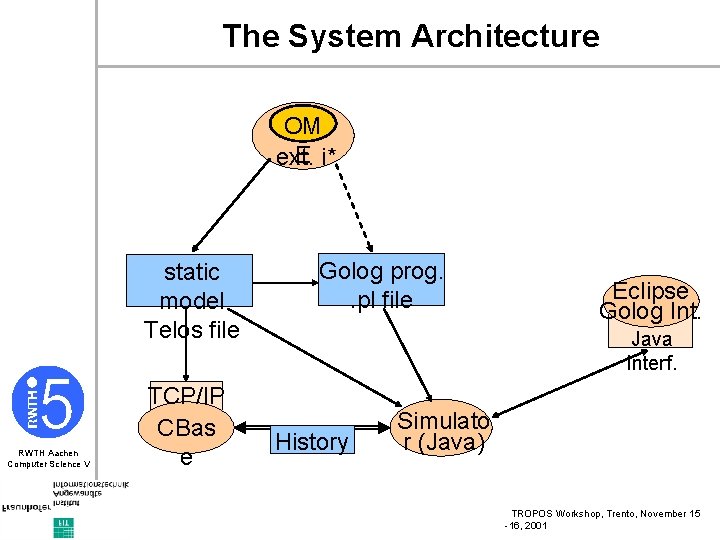
The System Architecture OM E i* ext. static model Telos file RWTH Aachen Computer Science V TCP/IP CBas e Golog prog. . pl file Eclipse Golog Int. Java Interf. History Simulato r (Java) TROPOS Workshop, Trento, November 15 -16, 2001
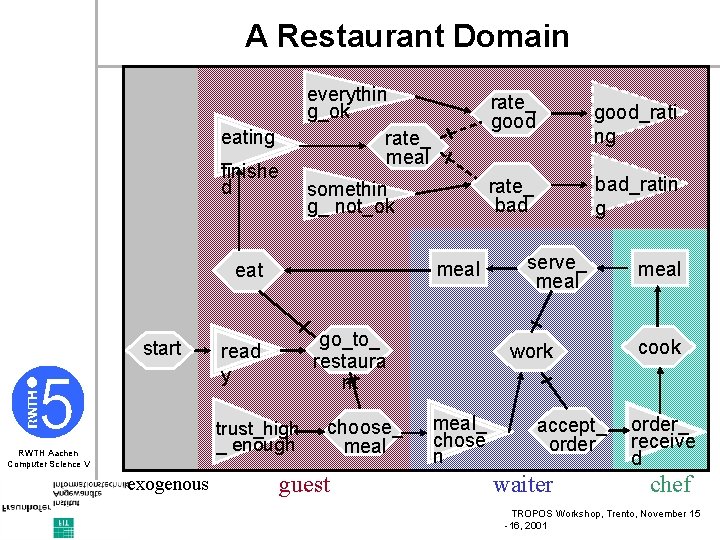
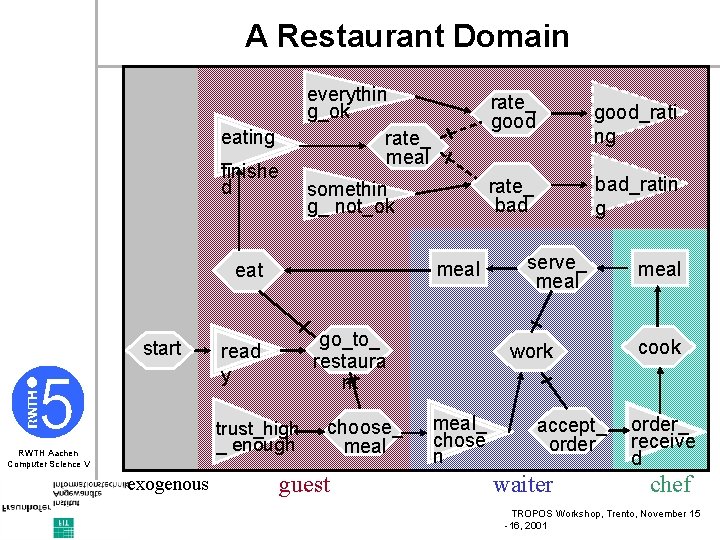
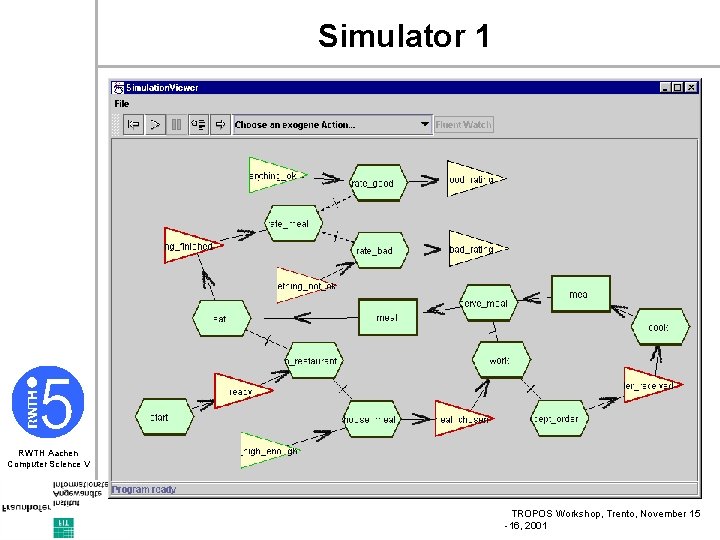
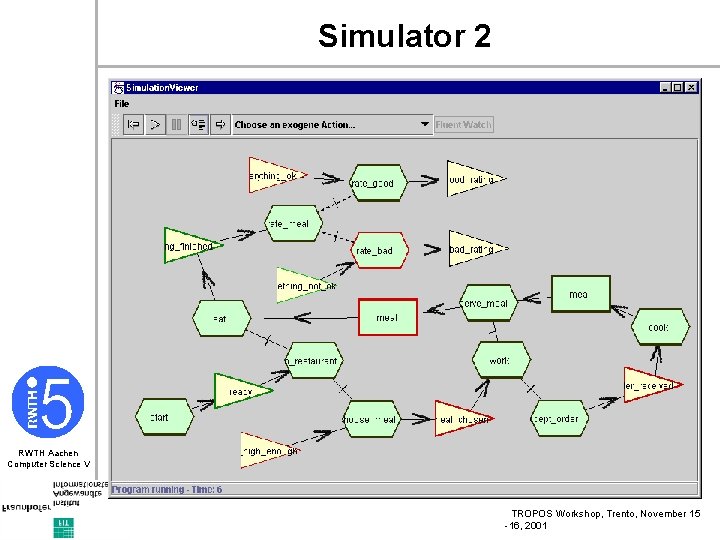
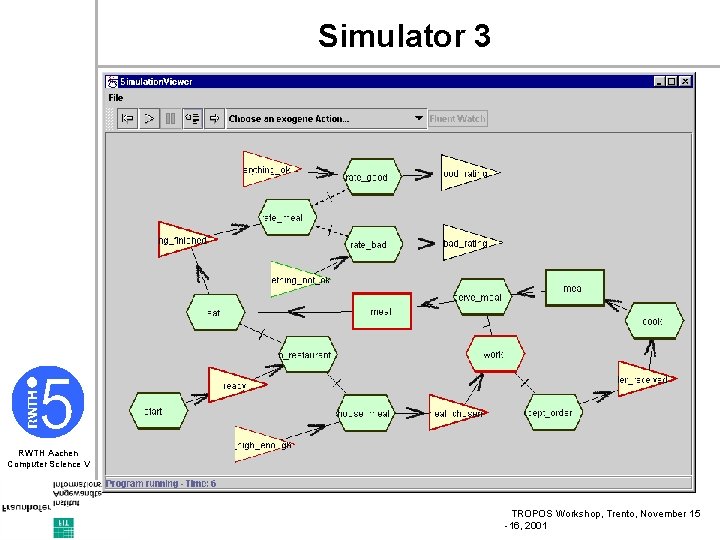
A Restaurant Domain eating _ finishe d everythin g_ok rate_ meal rate_ good_rati ng somethin g_ not_ok rate_ bad_ratin g meal eat start go_to_ restaura nt read y trust_high _ enough RWTH Aachen Computer Science V exogenous choose_ meal guest serve_ meal work meal_ chose n accept_ order waiter meal cook order_ receive d chef TROPOS Workshop, Trento, November 15 -16, 2001
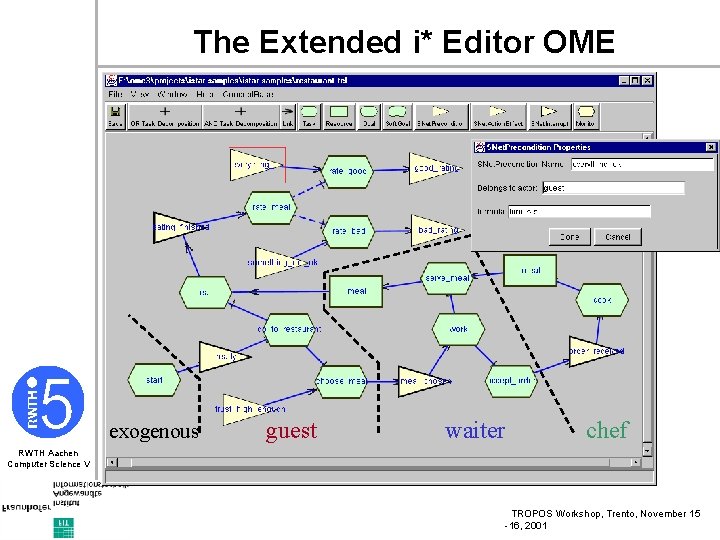
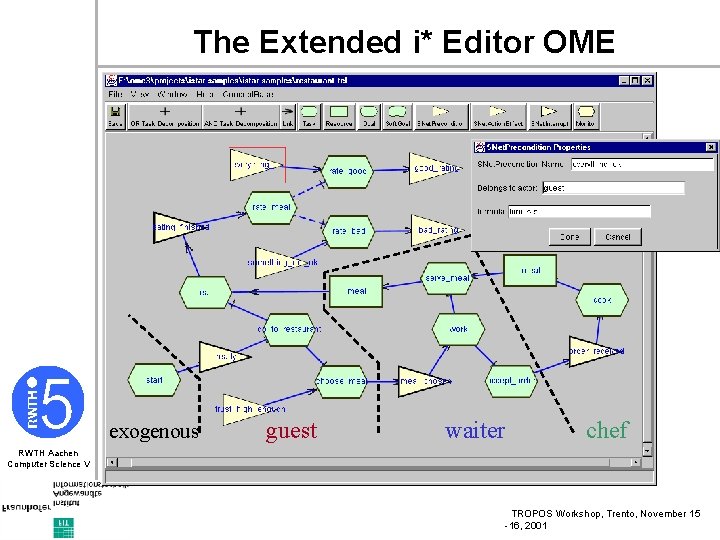
The Extended i* Editor OME exogenous guest waiter chef RWTH Aachen Computer Science V TROPOS Workshop, Trento, November 15 -16, 2001
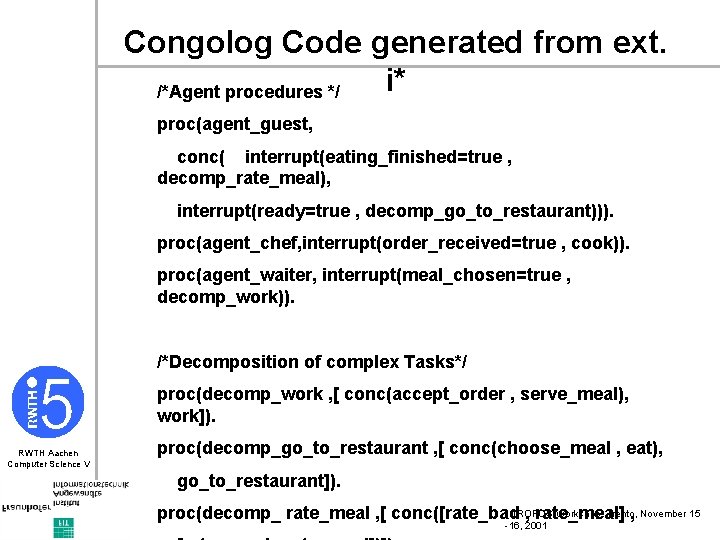
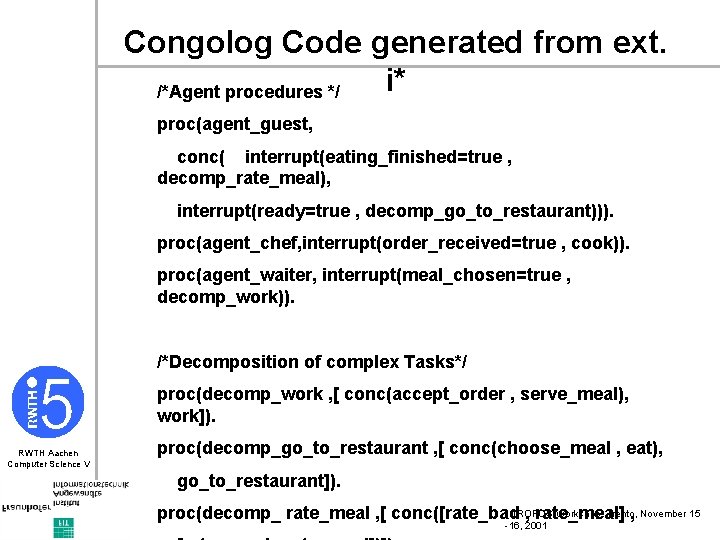
Congolog Code generated from ext. i* /*Agent procedures */ proc(agent_guest, conc( interrupt(eating_finished=true , decomp_rate_meal), interrupt(ready=true , decomp_go_to_restaurant))). proc(agent_chef, interrupt(order_received=true , cook)). proc(agent_waiter, interrupt(meal_chosen=true , decomp_work)). /*Decomposition of complex Tasks*/ proc(decomp_work , [ conc(accept_order , serve_meal), work]). RWTH Aachen Computer Science V proc(decomp_go_to_restaurant , [ conc(choose_meal , eat), go_to_restaurant]). TROPOS Workshop, Trento, proc(decomp_ rate_meal , [ conc([rate_bad , rate_meal] , November 15 -16, 2001
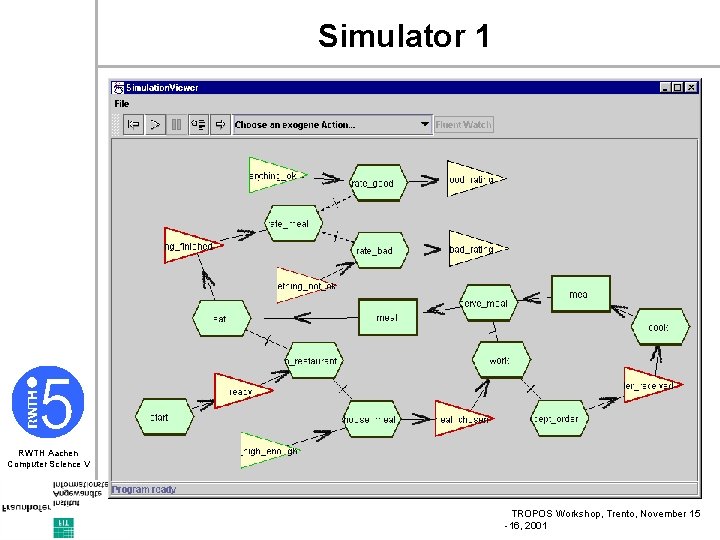
Simulator 1 RWTH Aachen Computer Science V TROPOS Workshop, Trento, November 15 -16, 2001
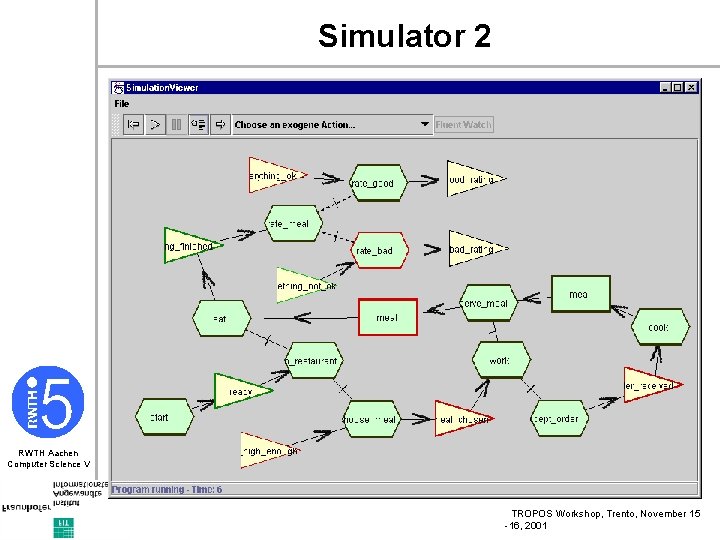
Simulator 2 RWTH Aachen Computer Science V TROPOS Workshop, Trento, November 15 -16, 2001
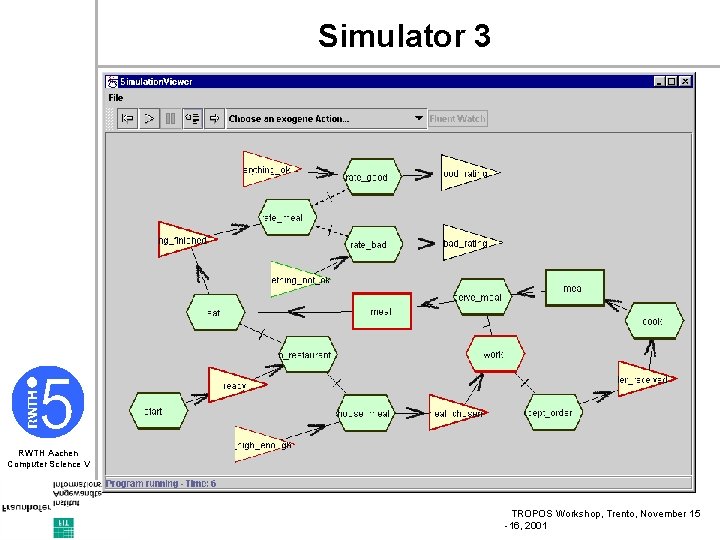
Simulator 3 RWTH Aachen Computer Science V TROPOS Workshop, Trento, November 15 -16, 2001
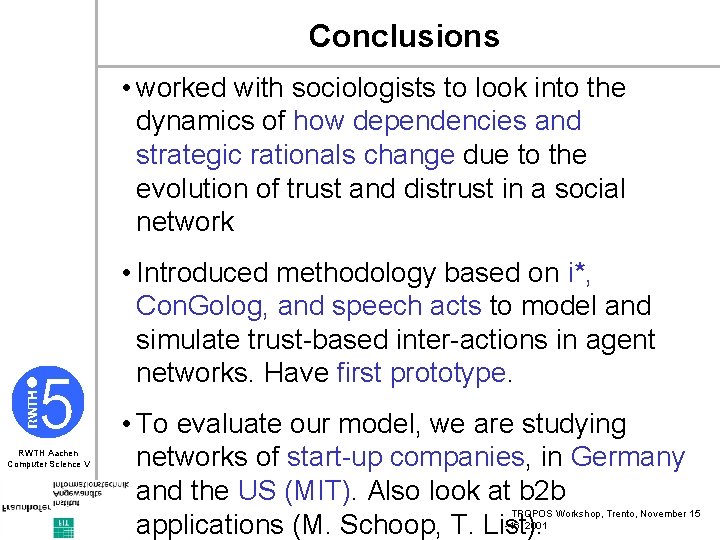
Conclusions • worked with sociologists to look into the dynamics of how dependencies and strategic rationals change due to the evolution of trust and distrust in a social network • Introduced methodology based on i*, Con. Golog, and speech acts to model and simulate trust-based inter-actions in agent networks. Have first prototype. RWTH Aachen Computer Science V • To evaluate our model, we are studying networks of start-up companies, in Germany and the US (MIT). Also look at b 2 b applications (M. Schoop, T. List). TROPOS Workshop, Trento, November 15 -16, 2001